Justice K.S. Puttaswamy (Retd.) and Another Vs. Union of India and Others

Home » Law Library Updates » Justice K.S. Puttaswamy (Retd.) and Another Vs. Union of India and Others
SUPREME COURT OF INDIA
BENCH: HON’BLE THE CHIEF JUSTICE, HON’BLE MR. JUSTICE A.K. SIKRI, HON’BLE MR. JUSTICE A.M. KHANWILKAR, HON’BLE DR. JUSTICE D.Y. CHANDRACHUD, HON’BLE MR. JUSTICE ASHOK BHUSHAN
Justice K.S. Puttaswamy (Retd.) and Another Vs. Union of India and Others
[Writ Petition (Civil) No. 494 of 2012] see below
A.K. SIKRI, J. (For Chief Justice, himself and A.M. Khanwilkar, J.)
Introduction and Preliminaries:
It is better to be unique than the best. Because, being the best makes you the number one, but being unique makes you the only one.
2) ‘Unique makes you the only one’ is the central message of Aadhaar, which is on the altar facing constitutional challenge in these petitions. ‘Aadhaar’ which means, in English, ‘foundation’ or ‘base’, has become the most talked about expression in recent years, not only in India but in many other countries and international bodies. A word from Hindi dictionary has assumed secondary significance. Today, mention of the word ‘Aadhaar’ would not lead a listener to the dictionary meaning of this word. Instead, every person on the very mentioning of this word ‘Aadhaar’ would associate it with the card that is issued to a person from where he/she can be identified.
It is described as an ‘Unique Identity’ and the authority which enrols a person and at whose behest the Aadhaar Card is issued is known as Unique Identification Authority of India (hereinafter referred to as ‘UIDAI’ or ‘Authority’). It is described as unique for various reasons. UIDAI claims that not only it is a foolproof method of identifying a person, it is also an instrument whereby a person can enter into any transaction without needing any other document in support.
It has become a symbol of digital economy and has enabled multiple avenues for a common man. Aadhaar scheme, which was conceptualised in the year 2006 and launched in the year 2009 with the creation of UIDAI, has secured the enrolment of almost 1.1 billion people in this country. Its use is spreading like wildfire, which is the result of robust and aggressive campaigning done by the Government, governmental agencies and other such bodies. In this way it has virtually become a household symbol. The Government boasts of multiple benefits of Aadhaar.
3) At the same time, the very scheme of Aadhaar and the architecture built thereupon has received scathing criticism from a section of the society. According to them, Aadhaar is a serious invasion into the right to privacy of persons and it has the tendency to lead to a surveillance state where each individual can be kept under surveillance by creating his/her life profile and movement as well on his/her use of Aadhaar. There has been no other subject matter in recent past which has evoked the kind of intensive and heated debate wherein both sides, for and against, argue so passionately in support of their respective conviction.
The petitioners in these petitions belong to the latter category who apprehend the totalitarian state if Aadhaar project is allowed to continue. They are demanding scrapping and demolition of the entire Aadhaar structure which, according to them, is anathema to the democratic principles and rule of law, which is the bedrock of the Indian Constitution. The petitioners have challenged the Aadhaar project which took off by way of administrative action in the year 2009. Even after Aadhaar got a shield of statutory cover, challenge persists as the very enactment known as Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Act, 2016 (hereinafter referred to as the ‘Aadhaar Act’) is challenged as constitutionally impermissible. The wide range of issues involved in this case is evident from the fact that it took almost four months for the parties to finish their arguments in these cases, and the Court witnessed highly skilled, suave, brilliant and intellectual advocacy, with the traces of passions as well.
4) The issue has generated heated public debate as well. Even outside the Court, there are groups advocating in favour of the Aadhaar scheme and those who are stoutly opposing the same. Interestingly, it is not only the commoners who belong to either of the two groups but intelligentsia is also equally divided. There have been number of articles, interviews for discourses in favour of or against Aadhaar. Those in favour see Aadhaar project as ushering the nation into a regime of good governance, advancing socio-economic rights, economic prosperity etc. and in the process they claim that it may make the nation a world leader. Mr. K.K. Venugopal, learned Attorney General for India, referred to the commendations by certain international bodies, including the World Bank.
We clarify that we have not been influenced by such views expressed either in favour or against Aadhaar. Those opposing Aadhaar are apprehensive that it may excessively intrude into the privacy of citizenry and has the tendency to create a totalitarian state, which would impinge upon the democratic and constitutional values. Some such opinions of various persons/bodies were referred to during the arguments. Notwithstanding the passions, emotions, annoyance, despair, ecstasy, euphoria, coupled with rhetoric, exhibited by both sides in equal measure during the arguments, this Court while giving its judgment on the issues involved is required to have a posture of calmness coupled with objective examination of the issues on the touchstone of the constitutional provisions.
5) Initiative in spearheading the attack on the Aadhaar structure was taken by the petitioners, namely, Justice K.S. Puttaswamy (Retd.) and Mr. Pravesh Khanna, by filing Writ Petition (Civil) No. 494 of 2012. At that time, Aadhaar scheme was not under legislative umbrella. In the writ petition the scheme has primarily been challenged on the ground that it violates fundamental rights of the innumerable citizens of India, namely, right to privacy falling under Article 21 of the Constitution of India. Few others joined the race by filing connected petitions. Series of orders were passed in this petition from time to time, some of which would be referred to by us at the appropriate stage. In 2016, with the passing of the Aadhaar Act, these very petitioners filed another writ petition challenging the vires of the Act. Here again, some more writ petitions have been filed with the same objective. All these writ petitions were clubbed together. There are number of interventions as well by various individuals, groups, NGOs, etc., some opposing the petitions and some supporting the Aadhaar scheme.
6) Before we go into the premise on which the attack is laid on the constitutional validity of the Aadhaar project and the Aadhaar Act, it would be apposite to take note of the events in chronological order that shaped the formulation, take off and implementation of the Aadhaar scheme.
7) On March 03, 2006, approval was given by the Department of Information Technology, Ministry of Communications and Information Technology, Government of India for the project titled ‘Unique Identification for BPL Families’ to be implemented by the National Informatics Centre (NIC) for over a period of twelve months. As a result, a Processes Committee was set up on July 03, 2006 to suggest the process for updation, modification, addition and deletion of data and fields from the core database to be created under the Unique Identification for BPL Families project. This Committee, on November 26, 2006, prepared a paper known as ‘Strategic Vision Unique Identification of Residents’. Based thereupon, the Empowered Group of Ministers (EGoM) was set up on December 04, 2006, to collate the National Population Register under the Citizenship Act, 1955 and the Unique Identification Number project of the Department of Information Technology. The EGoM was also empowered to look into the methodology and specific milestones for early and effective completion of projects and to take a final view on these projects. The EGoM was composed of the then Ministers of External Affairs, Home Affairs, Law, Panchayati Raj and Communications and Information Technology and the then Deputy Chairman, Planning Commission.
8) Various meetings on the Unique Identification (hereinafter referred to as ‘UID’) project were held from time to time. In the fourth meeting held on December 22, 2006, various aspects of proposed data elements and their formats were discussed. Thereafter, in its fifth meeting held on April 27, 2007, it was decided that the evolution of UID database would be in three stages in principle. The Committee further decided that linkage with major partner databases such as Household Survey of RD and the individual State Public Distribution System (PDS) databases should be taken up in a phased manner. On June 11, 2007, at the final stage of the project, a presentation on the UID project was made to the then Prime Minister by the Cabinet Secretary. The sixth meeting of the UID project was held on June 15, 2007. The Committee, inter alia, took the following decisions:
(i) The numbering format of 11 digits was approved.
(ii) The need for UID authority to be created by an executive order under the aegis of the Planning Commission was appreciated in order to ensure pan-departmental and neutral identity for the authority.
(iii) The proposal for creation of Central and State UIDs was approved.
(iv) Department of Information Technology (DIT) was directed to work out modalities for linkage with Election Commission and initiate discussions with MoRD and PDS for linkage. (v) In principle, approval of proposed sequence for phasing plan was granted.
9) In the seventh meeting held on August 30, 2007, the proposed administrative framework and structure of UID authority and manpower requirement, including financial implications, was discussed. It was decided that a detailed proposal based on the resource model be presented to the Committee for its ‘in principle’ approval. At this stage, EGoM convened its first meeting on November 27, 2007. At this meeting, a consensus emerged on the following points:
(i) There is a clear need for creating an identity related resident database, regardless of whether the database is created on a de novo collection of data or is based on an already existing data (such as the Election Commission’s Voter List).
(ii) Additionally, there is a critical need to create an institutional mechanism that would ‘own’ the database and be responsible for its maintenance and updating.
(iii) The next meeting is to consider topics relating to collating the National Population Register (NPR) and UID schemes, including methodology, effective implementation techniques, identification of the institutional mechanism stated above, and the time schedule for putting the scheme into operation. A series of meetings took place thereafter to work out the modalities of the programme. Certain issues were raised therein and to address those issues, a Committee of Secretaries was formed. The said Committee gave its recommendations which were discussed by EGoM. After approving the Aadhaar Scheme in principle, it instructed the Cabinet Secretary to convene a meeting to finalise the detailed organisational structure of the UID.
10) After considering the recommendation of the Cabinet Secretary, Notification No. A-43011/02/2009-Admn.I was issued on January 28, 2009 by the Government of India which constituted and notified the UIDAI as an attached office under the aegis of the Planning Commission. Consequent to the constitution of UIDAI, allocation of Rs.147.31 crores for Phase I of Aadhaar enrolments was approved by the Finance Minister on the recommendation of the Standing Committee on Finance. Demo-Official letter dated February 25, 2009, was sent by the Secretary, Planning Commission to all Chief Secretaries of 35 States/Union Territories apprising them of their roles and responsibilities of the States/Union Territories in implementation of UIDAI, such as appointment of the State/UT UID Commissioners, logistics support and coordination with various departments and State units. As they say, rest is history, which we recapitulate in brief hereinafter.
11) A core group was set up to advice and further the work related to UIDAI. Budgets were allocated to UIDAI to enable it to undertake its task. Staff was also allocated to it. Meetings of the core group took place from time to time. The core group, inter alia, decided that it was better to start with the electoral roll database of 2009 for undertaking the UIDAI project. The status of digitisation of PDS records, state-wise, was sought to be sent from the Department of Food and Public Distribution to the Standing Commission/UID.
This and other steps taken in this direction culminated in issuance of Notification dated July 02, 2009 whereby Mr. Nandan Nilekani was appointed as the Chairman of UIDAI for an initial tenure of five years in the rank and status of a Cabinet Minister. He assumed charge on July 24, 2009. Thereafter, the Prime Minister’s Council of UIDAI was constituted on July 30, 2009 which held its first meeting on August 12, 2009 where the Chairman of UIDAI made detailed representation on the broad strategy and approach of the proposed UID project.
One of the proposals was to provide a legislative framework for UID at the earliest so that it could have the legal sanction to perform its function. Some other Committees like the Biometrics Standard Committee, Demographic Data Standards and Verification Procedure Committee were set up as a support system to the project, which submitted their respective reports in December 2009. Even a Cabinet Committee on UID was constituted vide orders dated October 22, 2009 which was headed by the Prime Minister with the aim to cover all issues relating to UIDAI, including its organisation, policies, programmes, schemes, funding and methodology to be adopted for achieving its objectives.
12) The matter was addressed in the Seventeenth Finance Commission Report also which was tabled in the Parliament on February 25, 2010. In this report, the Finance Commission suggested targeting of subsidies through UIDAI. By April 2010, UIDAI came out with its Strategy Overview. This Overview describes the features, benefits, revenue model and timelines of the UIDAI project. Furthermore, it outlined the goal of the UID to serve as a universal proof of identity, allowing residents to prove their identities anywhere in the country. The project would give the Government a clear view of India’s population, enabling it to target and deliver services effectively, achieve greater returns on social investments and monitor money and resource flows across the country. It was felt that crucial to the achievement of this goal is the active participation of the central, state and local Governments as well as public and private sector entities. Only with their support will the project be able to realise a larger vision of inclusion and development in India.
13) A Cabinet Note bearing No. 4(4)/57/2010/CC-UIDAI for the Cabinet Committee on UIDAI was submitted on May 12, 2010. The Note outlined a brief background of UIDAI, proposed an approach for collection of demographic and biometric attributes of residents for the UID project and sought approval of the Cabinet Committee for adoption of the aforesaid approach and suggested that the same standards and processes be adhered to by the Registrar General of India for the NPR exercise and all other Registrars in the UID system. Rationale for inclusion of iris biometrics was also submitted with the aforesaid Cabinet Note to explain the need for capturing iris scans at the time of capturing biometric details.
14) By September 2010 enrolment process of Aadhaar began with the nationwide launch of the Aadhaar project. In December 2010, UIDAI came out with a report on enrolment process known as ‘UID Enrolment Proof-of-Concept Report’ studying enrolment proof-of-concept in three rural areas of Karnataka, Bihar and Andhra Pradesh published by the UIDAI. According to this report, ‘the biometric matching analysis of 40,000 people showed that the accuracy levels achieved by both iris and ten fingerprints were more than an order of magnitude better compared to using either of the two individually. The multi-modal enrolment was adequate to carry out de-duplication on a much larger scale, with reasonable expectations of extending it to all residents of India’.
15) Going by the recommendation of the Chairman of UIDAI for providing legislative framework to UIDAI, a Bill was introduced in the Rajya Sabha on December 03, 2010 known as ‘National Identification Authority of India Bill, 2010’. 16) Various other steps were taken to smoothen the process of enrolment. There were studies from time to time on the effectiveness of the enrolment process. Notifications/orders were also issued by the Reserve Bank of India stating that an Aadhaar letter would be recognised by Banks to open bank accounts for a resident. Similar Orders/Notifications were issued by other authorities as well. On the first anniversary of Aadhaar launch, which fell on September 29, 2011, announcement was made that 10 crores enrolments and generation of more than 3.75 crores of Aadhaar had taken place. Some of the reports submitted in due course of time, which are relevant for our purposes, are taken note of at this stage:
(i) Report of the Task Force on an Aadhaar-Enabled Unified Payment Infrastructure for the direct transfer of subsidies on Kerosene, LPG and Fertilizer.
(ii) In March 2012, Fingerprint Authentication Report was submitted to UIDAI. This Report showcased the high accuracy rates of using fingerprints to authenticate identities. The study conducted in the rural setting representing typical demography of the population established that it is technically possible to use fingerprint to authenticate a resident in 98.13% of the population. The accuracy of 96.5% can be achieved using one best finger and 99.3% can be achieved using two fingers. Further improvement is possible if the device specifications are tightened to include only the best devices and certain mechanical guide is used to aid proper placement of the finger. It was also demonstrated through benchmarking that the authentication infrastructure is able to sustain one million authentications per hour.
(iii) Fifty Third Report of the Standing Committee on Finance on the ‘Demands for Grants (2012-13)’ of the Ministry of Planning was presented to the Lok Sabha and Rajya Sabha on April 24, 2012. This Report summarises the objectives and financial implications of the UID scheme being implemented under the aegis of the Planning Commission.
(iv) Iris Authentication Accuracy Report was submitted to UIDAI on September 12, 2012. This Report based on an empirical study of 5833 residents demonstrated iris authentication to be viable in Indian context. With current level of device readiness for iris capture, it is capable of providing coverage for 99.67% of population with authentication accuracy of above 99.5%. Suggestions made in this document for the vendors, once implemented, will improve the rates further. The overall systems – network and software – have shown to meet desired requirements in real life condition. Finally, six different devices with variety of form and function are available to provide competitive vendor eco-system.
(v) Background Note on Introduction to Cash Transfers was prepared by the National Committee on Direct Cash Transfers in its first meeting on November 26, 2012. This Report outlines the advantages of cash transfers in the Indian context stating that a unique ID for all is a prerequisite for this purpose.
17) At this juncture, Writ Petition (Civil) No. 494 of 2012 was filed in which show-cause notice dated November 30, 2012 was issued by this Court. As pointed out above, this writ petition assailed Aadhaar scheme primarily on the ground that it violates right to privacy which is a facet of fundamental rights enshrined in Article 21 of the Constitution.
18) Counter affidavit thereto was filed by the Union of India as well as UIDAI. The stand taken by the respondents, inter alia, was that right to privacy is not a fundamental right, which was so held by the eight Judge Bench judgment in M.P. Sharma and 4 Others v. Satish Chandra Distt. Magistrate, Delhi and 4 Others1. This is notwithstanding the fact that thereafter in many judgments rendered by this Court, right to privacy was accepted as a facet of Article 21. Contention of the respondents, however, was that those judgments were contrary to the dicta laid down in M.P. Sharma and were, therefore, per in curium. The matter on this aspect was heard by a three Judge Bench and after hearing the parties, the Bench deemed it appropriate to make the reference to the Constitution Bench. A five Judge Bench was constituted, which after considering the matter, referred the same to a nine Judge Bench to resolve the controversy in an authoritative manner. The nine Judge Bench judgment has given an unanimous answer to the Reference with conclusive, unambiguous and emphatic determination that right to privacy is a part of fundamental rights which can be traced to Articles 14, 19 and 21 of the Constitution of India.
19) We may also record at this stage that in this petition certain interim orders were passed from time to time. We may give the gist of some of the relevant orders:
(a) Order dated September 23, 2013 (two Judge Bench)
“All the matters require to be heard finally. List all matters for final hearing after the Constitution Bench is over. In the meanwhile, no person should suffer for not getting the Aadhaar card in spite of the fact that some authority had issued a circular making it mandatory and when any person applies to get the Aadhaar card voluntarily, it may be checked whether that person is entitled for it under the law and it should not be given to any illegal immigrant.”
(b) Order dated November 26, 2013 (two Judge Bench)
“After hearing the matter at length, we are of the view that all the States and Union Territories have to be impleaded as respondents to give effective directions. In view thereof, notice be issued to all the States and Union Territories through standing counsel.
xx xx xx
Interim order to continue, in the meantime.”
(c) Order dated March 16, 2015 (three Judge Bench)
“In the meanwhile, it is brought to our notice that in certain quarters, Aadhaar identification is being insisted upon by the various authorities, we do not propose to go into the specific instances. Since Union of India is represented by learned Solicitor General and all the States are represented through their respective counsel, we expect that both the Union of India and States and all their functionaries should adhere to the order passed by this Court on 23rd September, 2013.”
(d) Order dated August 11, 2015 (three Judge Bench)
“Having considered the matter, we are of the view that the balance of interest would be best served, till the matter is finally decided by a larger Bench, if the Union of India or the UIDAI proceed in the following manner:
1. The Union of India shall give wide publicity in the electronic and print media including radio and television networks that it is not mandatory for a citizen to obtain an Aadhaar card.
2. The production of an Aadhaar card will not be condition for obtaining any benefits otherwise due to a citizen.
3. The Unique Identification Number or the Aadhaar card will not be used by the respondents for any purpose other than the PDS Scheme and in particular for the purpose of distribution of food grains, etc. and cooking fuel, such as kerosene. The Aadhaar card may also be used for the purpose of LPG Distribution Scheme.
4. The information about an individual obtained by the Unique Identification Authority of India while issuing an Aadhaar card shall not be used for any other purpose, save as above, except as may be directed by a Court for the purpose of criminal investigation.”
(d) Order dated October 15, 2015 (Constitution Bench)
“3. After hearing the learned Attorney General for India and other learned senior counsels, we are of the view that in paragraph 3 of the order dated 11.08.2015, if we add, apart from the other two Schemes, namely, P.D.S. Scheme and L.P.G. Distribution Scheme, the Schemes like The Mahatma Gandhi National Social Assistance Programme (Old Age Pensions, Widow Pensions, Disability Pensions), Prime Minister’s Jan Dhan Yojana (PMJDY) and Employees’ Provident Fund Organisation (EPFO) for the present, it would not dilute earlier order passed by this Court. Therefore, we now include the aforesaid Schemes apart from the other two Schemes that this Court has permitted in its earlier order dated 11.08.2015.
4. We impress upon the Union of India that it shall strictly follow all the earlier orders passed by this Court commencing from 23.09.2013.
5. We will also make it clear that the Aadhaar card scheme is purely voluntary and it cannot be made mandatory till the matter is finally decided by this Court one way or the other.”
(e) Order dated September 14, 2016 in WP (C) No. 686/2016
“Having regard to the facts and circumstances of the case, the material evidence available on record and the submissions made by learned senior counsel, we stay the operation and implementation of letters dated 14.07.2006 (i.e. Annexure P-5, P-6, P-7) for Pre-Matric Scholarship Scheme, Post-Matric Scholarship Scheme and Merit-cum- Means Scholarship Scheme to the extent they have made submission of Aadhaar mandatory and direct the Ministry of Electronics and Information Technology, Government of India, i.e. respondent No.2, to remove Aadhaar number as a mandatory condition for student registration form at the National Scholarship Portal of Ministry of Electronics and Information Technology, Government of India at the website…”
20) It is also relevant to point out that against an order passed by the High Court of Bombay at Panaji, in some criminal proceedings, wherein the Authority was directed to pass on biometric information on a person, UIDAI had filed Special Leave Petition (Criminal) No. 2524 of 2014 challenging the said order with the submission that such a direction for giving biometric information was contrary to the provisions of the Aadhaar Act and the Authority was not supposed to give such an information, which was confidential. In the said special leave petition, order dated March 24, 2014 was passed staying the operation of the orders of the Bombay High Court. This order reads as under: “Issue notice.
In addition to normal mode of service, dasti service, is permitted. Operation of the impugned order shall remain stayed. In the meanwhile, the present petitioner is restrained from transferring any biometric information of any person who has been allotted the Aadhaar number to any other agency without his consent in writing. More so, no person shall be deprived of any service for want of Aadhaar number in case he/she is otherwise eligible/entitled.
All the authorities are directed to modify their forms/circulars/likes so as to not compulsorily require the Aadhaar number in order to meet the requirement of the interim order passed by this Court forthwith. Tag and list the matter with main matter i.e. WP (C) No. 494 of 2012.” 21) Likewise, in Writ Petition (Civil) No. 1002 of 2017 titled Dr. Kalyan Menon Sen v. Union of India and Others, where constitutional validity of linking bank accounts and mobile phones with Aadhaar linkage was challenged, interim order was passed on November 03, 2017 extending the last date of linking to December 31, 2017 and February 06, 2018 respectively. This order was extended thereafter and continues to operate.
22) We would also like to refer to the order dated September 14, 2011 passed in People’s Union for Civil Liberties (PDS Matter) v. Union of India & Ors.2, wherein various directions were given to ensure effective implementation of the PDS Scheme and in the process to also undertake the exercise of eliminating the task and ghost ration cards. In the same manner, vide order dated March 16, 2012 it was noted that the Government had set up a task force under the Chairmanship of Mr. Nandan Nilekani to recommend, amongst others, an IT strategy for the PDS.
Mr. Nilekani was requested to suggest ways and means by which computerization process of the PDS can be expedited. Computerisation of PDS system was directed to be prepared and in this hue the process of computerisation with Aadhaar registration was also suggested. In the same very case above, which also pertained to providing night shelters to homeless destitute persons, some orders were passed on February 10, 20103 as well as on September 14, 20114.
23) Again, in the case of State of Kerala & Ors. v. President, Parent Teachers Association SNVUP School and Ors.5, where the Court was concerned with the problem of fake or bogus admissions, it was felt that instead of involving the Police in schools to prevent fake admissions, more appropriate method of verification would be Unique Identification (UID) card as means of verification.
Architecture of the Aadhaar Project and the Aadhaar Act:
24) Before adverting to the discussion on various issues that have been raised in these petitions, it would be apposite to first understand the structure of the Aadhaar Act and how it operates, having regard to various provisions contained therein. UIDAI was established in the year 2009 by an administrative order i.e. by resolution of the Govt. of India, Planning Commission, vide notification dated January 28, 2009. The object of the establishment of the said Authority was primarily to lay down policies to implement the Unique Identification Scheme (for short the ‘UIS’) of the Government, by which residents of India were to be provided unique identity number. The aim was to serve this as proof of identity, which is unique in nature, as each individual will have only one identity with no chance of duplication.
Another objective was that this number could be used for identification of beneficiaries for transfer of benefits, subsidies, services and other purposes. This was the primary reason, viz. to ensure correct identification of targeted beneficiaries for delivery of various subsidies, benefits, services, grants, wages and other social benefits schemes which are funded from the Consolidated Fund of India. It was felt that the identification of real and genuine beneficiaries had become a challenge for the Government. In the absence of a credible system to authenticate identity of beneficiaries, it was becoming difficult to ensure that the subsidies, benefits and services reach to intended beneficiaries.
As per the Government, failure to establish identity was proving to be major hindrance for the successful implementation of the welfare programmes and it was hitting hard the marginalised section of the society and, in particular, women, children, senior citizens, persons with disabilities, migrant unskilled and organised workers, and nomadic tribes. After the establishment of the Authority, vide the aforesaid notification, it started enrolling the residents of this country under the UIS. These residents also started using Aadhaar number allotted to them. It was found that over a period of time, the use of Aadhaar number had increased manifold. This necessitated ensuring security of the information contained in Aadhaar number as well as the information that generated as a result of the use of Aadhaar numbers. It was, thus, felt desirable to back the system with a Parliamentary enactment.
25) With this intention, the Aadhaar Bill was introduced with the following Introduction: “The Unique Identification Authority of India was established by a resolution of the Government of India in 2009. It was meant primarily to lay down policies and to implement the Unique Identification Scheme, by which residents of India were to be provided unique identity number.
This number wold serve as proof of identity and could be used for identification of beneficiaries for transfer of benefits, subsidies, services and other purposes. Later on, it was felt that the process of enrollment, authentication, security, confidentiality and use of Aadhaar related information be made statutory so as to facilitate the use of Aadhaar number for delivery of various benefits, subsidies and services, the expenditures of which were incurred from or receipts therefrom formed part of the Consolidated Fund of India. The Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Bill, 2016 inter alia, provides for establishment of Unique Identification Authority of India, issuance of Aadhaar number to individuals, maintenance and updating of information in the Central Identities Data Repository, issues pertaining to security, privacy and confidentiality of information as well as offences and penalties for contravention of relevant statutory provisions.”
26) After mentioning the reasons recorded above, Statement of Objects and Reasons for introducing the Bill also highlight the salient features thereof in the following manner:
“5. The Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Bill, 2016, inter alia, seeks to provide for-
(a) issue of Aadhaar numbers to individuals on providing his demographic and biometric information to the Unique Identification Authority of India;
(b) requiring Aadhaar numbers for identifying an individual for delivery of benefits, subsidies, and services the expenditure is incurred from or the receipt therefrom forms part of the Consolidated Fund of India;
(c) authentication of the Aadhaar number of an Aadhaar number holder in relation to his demographic and biometric information;
(d) establishment of the Unique Identification Authority of India consisting of a Chairperson, two Members and a Member-Secretary to perform functions in pursuance of the objectives above;
(e) maintenance and updating the information of individuals in the Central Identities Data Repository in such manner as may be specified by regulations;
(f) measures pertaining to security, privacy and confidentiality of information in possession or control of the Authority including information stored in the Central Identities Data Repository; and
(g) offences and penalties for contravention of relevant statutory provisions.”
27) The Bill having been passed by the Legislature, received the assent of the President on March 25, 2016 and, thus, became Act (18 of 2016). Preamble to this Act again emphasises the aim and objective which this Act seeks to achieve. It reads: “An Act to provide for, as a good governance, efficient, transparent, and targeted delivery of subsidies, benefits and services, the expenditure for which is incurred from the Consolidated Fund of India, to individuals residing in India through assigning of unique identity numbers to such individuals and for matters connected therewith or incidental thereto”
28) Section 2 of the Act provides certain definitions. Some of the definitions can be noted at this stage itself, while other relevant definitions would be mentioned at the appropriate stage.
“(a) “Aadhaar number” means an identification number issued to an individual under sub-section (3) of Section 3;
(b) “Aadhaar number holder” means an individual who has been issued an Aadhaar number under this Act;
(c) “authentication” means the process by which the Aadhaar number along with demographic information or biometric information of an individual is submitted to the Central Identities Data Repository for its verification and such Repository verifies the correctness, or the lack thereof, on the basis of information available with it;
(d) “authentication record” means the record of the time of authentication and identity of the requesting entity and the response provided by the Authority thereto;
xx xx xx
(f) “benefit” means any advantage, gift, reward, relief, or payment, in cash or kind, provided to an individual or a group of individuals and includes such other benefits as may be notified by the Central Government;
(g) “biometric information” means photograph, finger print, Iris scan, or such other biological attributes of an individual as may be specified by regulations;
(h) “Central Identities Data Repository” means a centralised database in one or more locations containing all Aadhaar numbers issued to Aadhaar number holders along with the corresponding demographic information and biometric information of such individuals and other information related thereto;
xx xx xx
(j) “core biometric information” means finger print, Iris scan, or such other biological attribute of an individual as may be specified by regulations;
(k) “demographic information” includes information relating to the name, date of birth, address and other relevant information of an individual, as may be specified by regulations for the purpose of issuing an Aadhaar number, but shall not include race, religion, caste, tribe, ethnicity, language, records of entitlement, income or medical history; (l) “enrolling agency” means an agency appointed by the Authority or a Registrar, as the case may be, for collecting demographic and biometric information of individuals under this Act;
(m) “enrollment” means the process, as may be specified by regulations, to collect demographic and biometric information from individuals by the enrolling agencies for the purpose of issuing Aadhaar numbers to such individuals under this Act;
(n) “identity information” in respect of an individual, includes his Aadhaar number, his biometric information and his demographic information;
xx xx xx
(r) “records of entitlement” means records of benefits, subsidies or services provided to, or availed by, any individual under any programme;
xx xx xx
(u) “requesting entity” means an agency or person that submits the Aadhaar number, and demographic information or biometric information, of an individual to the Central Identities Data Repository for authentication;
(v) “resident” means an individual who has resided in India for a period or periods amounting in all to one hundred and eighty-two days or more in the twelve months immediately preceding the date of application for enrolment;
(w) “service” means any provision, facility, utility or any other assistance provided in any form to an individual or a group of individuals and includes such other services as may be notified by the Central Government;
(x) “subsidy” means any form of aid, support, grant, subvention, or appropriation, in cash or kind, to an individual or a group of individuals and includes such other subsidies as may be notified by the Central Government.”
29) Chapter II of the Act deals with enrolment. Section 3 in this Chapter entitles every resident to obtain the Aadhaar number by submitting his demographic information and biometric information. As noted above, demographic information includes information relating to the name, date of birth, address and ‘other relevant information of an individual, as may be specified by regulations for the purpose of issuing an Aadhaar number’. Photograph, fingerprint, iris scan, ‘or such other biological attribute of an individual as may be specified by regulations’ are treated as biometric information. Sub-section (2) of Section 3 stipulates that the enrolling agency shall, at the time of enrolment, inform the individual undergoing enrolment of the following details in such manner as may be specified by regulations, namely:
(a) the manner in which the information shall be used;
(b) the nature of recipients with whom the information is intended to be shared during authentication; and
(c) the existence of a right to access information, the procedure for making requests for such access, and details of the person or department in-charge to whom such requests can be made.
30) Section 4, inter alia, provides that Aadhaar number issued to an individual shall not be reassigned to any individual. In this sense, it makes an Aadhaar number given to a particular individual ‘unique’. Section 5 delineates special measures for issuance of Aadhaar number to certain categories of persons and reads as under:
“5. Special measures for issuance of Aadhaar number to certain category of persons.- The Authority shall take special measures to issue Aadhaar number to women, children, senior citizens, persons with disability, unskilled and unorganised workers, nomadic tribes or to such other persons who do not have any permanent dwelling house and such other categories of individuals as may be specified by regulations.”
31) Section 6 enables the Authority to update demographic and biometric information of the Aadhaar number holders from time to time.
32) Chapter III deals with ‘authentication’, which has generated the maximum debate in these proceedings. Section 7 falling under this Chapter mandates that proof of Aadhaar number would be necessary for receipt of certain subsidies, benefits and services etc. meaning thereby for availing such subsidies, benefits and services, it would be necessary for the intended beneficiary to possess Aadhaar number. In case of an individual to whom no Aadhaar number has been assigned, he/she would be required to show that application for enrolment has been given.
Where the Aadhaar number is not assigned, proviso to Section 7 lays down that the individual shall be offered alternate and viable means of identification for delivery of subsidy, benefit or service. Section 8 deals with authentication of Aadhaar number and provides that on submission of request by any requesting entity, the Authority shall perform authentication of Aadhaar number. This authentication is in relation to biometric information or demographic information of an Aadhaar number holder. Before collecting identity information for the purpose of authentication, the requesting entity is to obtain consent of an individual and also to ensure that the identity information of that individual is only used for submission to the Central Identities Data Repository (CIDR) for authentication. Sections 7 and 8 read as under:
“7. Proof of Aadhaar number necessary for receipt of certain subsidies, benefits and services, etc.- The Central Government or, as the case may be, the State Government may, for the purpose of establishing identity of an individual as a condition for receipt of a subsidy, benefit or service for which the expenditure is incurred from, or the receipt therefrom forms part of, the Consolidated Fund of India, require that such individual undergo authentication, or furnish proof of possession of Aadhaar number or in the case of an individual to whom no Aadhaar number has been assigned, such individual makes an application for enrolment: Provided that if an Aadhaar number is not assigned to an individual, the individual shall be offered alternate and viable means of identification for delivery of the subsidy, benefit or service.
8. Authentication of Aadhaar number.-
(1) The Authority shall perform authentication of the Aadhaar number of an Aadhaar number holder submitted by any requesting entity, in relation to his biometric information or demographic information, subject to such conditions and on payment of such fees and in such manner as may be specified by regulations.
(2) A requesting entity shall-
(a) unless otherwise provided in this Act, obtain the consent of an individual before collecting his identity information for the purposes of authentication in such manner as may be specified by regulations; and
(b) ensure that the identity information of an individual is only used for submission to the Central Identities Data Repository for authentication.
(3) A requesting entity shall inform, in such manner as may be specified by regulations, the individual submitting his identity information for authentication, the following details with respect to authentication, namely-
(a) the nature of information that may be shared upon authentication;
(b) the uses to which the information received during authentication may be put by the requesting entity; and
(c) alternatives to submission of identity information to the requesting entity.
(4) The Authority shall respond to an authentication query with a positive, negative or any other appropriate response sharing such identity information excluding any core biometric information.”
33) Under Section 10, the Authority is given power to engage one or more entities to establish and maintain the CIDR and to perform any other functions as may be specified by regulations.
34) Chapter IV deals with the Establishment of the Authority. As per Section 11, the Central Government, by notification, shall establish an Authority to be known as the Unique Identification Authority of India. Notification dated July 12, 2016 was issued by the Central Government establishing the Authority. Other provisions in this Chapter deal with the composition of the Authority, qualifications for appointment of the Chairperson and Members of Authority; term of their office and their removal; and restrictions on their employment after cessation of office. It also provides for the functions of Chairperson as well as office of the Chief Executive Officer (CEO) and his functions and the meetings of the Authority etc. Powers and functions of the Authority are stipulated in Section 23.
35) Chapter V talks of grants to the Authority by the Central Government as well as accounts and audit and annual report of the Authority.
36) Chapter VI deals with the important aspects pertaining to ‘protection of information’. Section 28 of the Aadhaar Act puts an obligation on the Authority to ensure the security of identity information and authentication records of individuals. Likewise, Section 29 imposes certain restrictions on sharing information i.e. core biometric information collected or created under the Act or the identity information. The biometric information collected and stored in electronic form, in accordance with this Act and regulations made thereunder, is treated as ‘electronic record’ and ‘sensitive personal data or information’ by virtue of Section 30 of the Act. As these are very material and significant provisions of the Act, the same are reproduced verbatim in their entirety:
“28. Security and confidentiality of information.-
(1) The Authority shall ensure the security of identity information and authentication records of individuals.
(2) Subject to the provisions of this Act, the Authority shall ensure confidentiality of identity information and authentication records of individuals.
(3) The Authority shall take all necessary measures to ensure that the information in the possession or control of the Authority, including information stored in the Central Identities Data Repository, is secured and protected against access, use or disclosure not permitted under this Act or regulations made there under, and against accidental or intentional destruction, loss or damage.
(4) Without prejudice to sub-sections (1) and (2), the Authority shall-
(a) adopt and implement appropriate technical and organisational security measures;
(b) ensure that the agencies, consultants, advisors or other persons appointed or engaged for performing any function of the Authority under this Act, have in place appropriate technical and organisational security measures for the information; and
(c) ensure that the agreements or arrangements entered into with such agencies, consultants, advisors or other persons, impose obligations equivalent to those imposed on the Authority under this Act, and require such agencies, consultants, advisors and other persons to act only on instructions from the Authority.
29. Restriction on sharing information.-
(1) No core biometric information, collected or created under this Act, shall be-
(a) shared with anyone for any reason whatsoever; or
(b) used for any purpose other than generation of Aadhaar numbers and authentication under this Act.
(2) The identity information, other than core biometric information, collected or created under this Act may be shared only in accordance with the provisions of this Act and in such manner as may be specified by regulations.
(3) No identity information available with a requesting entity shall be-
(a) used for any purpose, other than that specified to the individual at the time of submitting any identity information for authentication; or
(b) disclosed further, except with the prior consent of the individual to whom such information relates.
(4) No Aadhaar number or core biometric information collected or created under this Act in respect of an Aadhaar number holder shall be published, displayed or posted publicly, except for the purposes as may be specified by regulations.
30. Biometric information deemed to be sensitive personal information.-
The biometric information collected and stored in electronic form, in accordance with this Act and regulations made thereunder, shall be deemed to be “electronic record” and “sensitive personal data or information”, and the provisions contained in the Information Technology Act, 2000 (21 of 2000) and the rules made thereunder shall apply to such information, in addition to, and to the extent not in derogation of the provisions of this Act.
Explanation.-For the purposes of this section, the expressions-
(a) “electronic form” shall have the same meaning as assigned to it in clause (r) of sub-section (1) of Section 2 of the Information Technology Act, 2000 (21 of 2000);
(b) “electronic record” shall have the same meaning as assigned to it in clause (t) of sub-section (1) of Section 2 of the Information Technology Act, 2000 (21 of 2000);
(c) “sensitive personal data or information” shall have the same meaning as assigned to it in clause (iii) of the Explanation to Section 43-A of the Information Technology Act, 2000 (21 of 2000).”
37) Section 32 provides that the Authority shall maintain authentication records in such manner and for such period as may be specified by regulations and enables every Aadhaar number holder to obtain his authentication record in such manner as may be specified by regulations.
This provision also puts an embargo upon the Authority to collect, keep or maintain any information about ‘purpose of authentication’. Section 33, however, creates an exception to the provisions of Section 28(ii) and
(v) as well as Section 29(ii) by stipulating that the information can be disclosed pursuant to an order of a court not inferior to that of a District Judge. It also carves out another exception in those cases where it becomes necessary to disclose the information in the interest of national security in pursuance of a direction of an officer not below the rank of Joint Secretary to the Government of India specially authorised in this behalf by an order of the Central Government.
38) Sections 34 to 47 in Chapter VII of the Act enumerate various kinds of offences and provide penalties for such offences. For our purposes, relevant Section is Section 37 which makes act of disclosing identity information as offence which is punishable with imprisonment for a term which may extend to three years or with a fine which may extend to ten thousand rupees. In the case of a company, this fine can extend to one lakh rupees. Likewise, Section 38 provides for penalty for unauthorised access to the CIDR. Penalties for tampering with data in CIDR (Section 39) and unauthorised use by requesting entity (Section 40) are also stipulated. Cognizance of offences under this Chapter can be taken by a court only on a complaint made by the Authority or any officer or person authorised by it.
39) Section 50 of the Act empowers the Central Government to issue directions to the Authority in writing from time to time and the Authority shall be bound to carry out such directions on questions of policy. Section 53 empowers the Central Government to make rules to carry out the provisions of the Act generally as well as the specific matters enumerated in sub-section (2) thereof. Section 54 empowers the Authority to make regulations consistent with the Act and Rules made thereunder, for carrying out the provisions of the Act and, in particular, the matters mentioned in sub-section (2). Such Rules and Regulations are to be laid before the Parliament, as provided in Section 55.
40) Section 57 provides that the Aadhaar Act would not prevent the use of Aadhaar number for establishing the identity of an individual for any purpose and reads as under:
“57. Act not to prevent use of Aadhaar number for other purposes under law.-
Nothing contained in this Act shall prevent the use of Aadhaar number for establishing the identity of an individual for any purpose, whether by the State or any body corporate or person, pursuant to any law, for the time being in force, or any contract to this effect: Provided that the use of Aadhaar number under this section shall be subject to the procedure and obligations under Section 8 and Chapter VI.”
41) If any difficulty arises in giving effect to the provisions of the Act, the Central Government is empowered to make provisions to remove those difficulties, provided that such provisions are not inconsistent with the provisions of the Act. Section 59, which is the last provision in the Act, is an attempt to save all the acts and actions of the Central Government under Notification dated January 28, 2009 vide which the Authority was established or the Department of Electronics and Information Technology under the Cabinet Secretariat Notification dated September 12, 2015. This provision is couched in the following language:
“59. Savings.-
Anything done or any action taken by the Central Government under the Resolution of the Government of India, Planning Commission bearing Notification Number A-43011/02/2009-Admin. I, dated the 28th January, 2009, or by the Department of Electronics and Information Technology under the Cabinet Secretariat Notification bearing Notification Number S.O. 2492(E), dated the 12th September, 2015, as the case may be, shall be deemed to have been validly done or taken under this Act.”
42) Regulations have been framed under the Act, namely,
(1) The Aadhaar (Enrolment and Update) Regulations, 2016;
(2) The Aadhaar (Authentication) Regulations, 2016;
(3) The Aadhaar (Data Security) Regulations, 2016; and
(4) The Aadhaar (Sharing of Information) Regulations, 2016. The relevant provisions in these Regulations are reproduced below:
“The Aadhaar (Enrolment and Update) Regulations, 2016
4. Demographic information required for enrolment. –
(1) The following demographic information shall be collected from all individuals undergoing enrolment (other than children below five years of age):
(i) Name;
(ii) Date of Birth;
(iii) Gender;
(iv) Residential Address.
(2) The following demographic information may also additionally be collected during enrolment, at the option of the individual undergoing enrolment:
(i) Mobile number
(ii) Email address
(3) In case of Introducer-based enrolment, the following additional information shall be collected:
(i) Introducer name;
(ii) Introducer’s Aadhaar number.
(4) In case of Head of Family based enrolment, the following additional information shall be collected:
(i) Name of Head of Family;
(ii) Relationship;
(iii) Head of Family’s Aadhaar number;
(iv) One modality of biometric information of the Head of Family.
(5) The standards of the above demographic information shall be as may be specified by the Authority for this purpose.
(6) The demographic information shall not include race, religion, caste, tribe, ethnicity, language, record of entitlement, income or medical history of the resident.
The Aadhaar (Authentication) Regulations, 2016
3. Types of Authentication.- There shall be two types of authentication facilities provided by the Authority, namely-
(i) Yes/No authentication facility, which may be carried out using any of the modes specified in regulation 4(2); and
(ii) e-KYC authentication facility, which may be carried out only using OTP and/ or biometric authentication modes as specified in regulation 4(2).
4. Modes of Authentication. –
(1) An authentication request shall be entertained by the Authority only upon a request sent by a requesting entity electronically in accordance with these regulations and conforming to the specifications laid down by the Authority.
(2) Authentication may be carried out through the following modes:
(a) Demographic authentication: The Aadhaar number and demographic information of the Aadhaar number holder obtained from the Aadhaar number holder is matched with the demographic information of the Aadhaar number holder in the CIDR.
(b) One-time pin based authentication: A One Time Pin (OTP), with limited time validity, is sent to the mobile number and/ or e-mail address of the Aadhaar number holder registered with the Authority, or generated by other appropriate means. The Aadhaar number holder shall provide this OTP along with his Aadhaar number during authentication and the same shall be matched with the OTP generated by the Authority.
(c) Biometric-based authentication: The Aadhaar number and biometric information submitted by an Aadhaar number holder are matched with the biometric information of the said Aadhaar number holder stored in the CIDR. This may be fingerprints-based or iris-based authentication or other biometric modalities based on biometric information stored in the CIDR.
(d) Multi-factor authentication: A combination of two or more of the above modes may be used for authentication.
(3) A requesting entity may choose suitable mode(s) of authentication from the modes specified in sub-regulation (2) for a particular service or business function as per its requirement, including multiple factor authentication for enhancing security. For the avoidance of doubt, it is clarified that e-KYC authentication shall only be carried out using OTP and/ or biometric authentication.
xx xx xx
7. Capturing of biometric information by requesting entity.-
(1) A requesting entity shall capture the biometric information of the Aadhaar number holder using certified biometric devices as per the processes and specifications laid down by the Authority.
(2) A requesting entity shall necessarily encrypt and secure the biometric data at the time of capture as per the specifications laid down by the Authority.
(3) For optimum results in capturing of biometric information, a requesting entity shall adopt the processes as may be specified by the Authority from time to time for this purpose.
xx xx xx
9. Process of sending authentication requests.-
(1) After collecting the Aadhaar number or any other identifier provided by the requesting entity which is mapped to Aadhaar number and necessary demographic and / or biometric information and/ or OTP from the Aadhaar number holder, the client application shall immediately package and encrypt these input parameters into PID block before any transmission, as per the specifications laid down by the Authority, and shall send it to server of the requesting entity using secure protocols as may be laid down by the Authority for this purpose.
(2) After validation, the server of a requesting entity shall pass the authentication request to the CIDR, through the server of the Authentication Service Agency as per the specifications laid down by the Authority. The authentication request shall be digitally signed by the requesting entity and/or by the Authentication Service Agency, as per the mutual agreement between them.
(3) Based on the mode of authentication request, the CIDR shall validate the input parameters against the data stored therein and return a digitally signed Yes or No authentication response, or a digitally signed e-KYC authentication response with encrypted e-KYC data, as the case may be, along with other technical details related to the authentication transaction.
(4) In all modes of authentication, the Aadhaar number is mandatory and is submitted along with the input parameters specified in sub-regulation (1) above such that authentication is always reduced to a 1:1 match.
(5) A requesting entity shall ensure that encryption of PID Block takes place at the time of capture on the authentication device as per the processes and specifications laid down by the Authority.
xx xx xx
18. Maintenance of logs by requesting entity. –
(1) A requesting entity shall maintain logs of the authentication transactions processed by it, containing the following transaction details, namely:-
(a) the Aadhaar number against which authentication is sought;
(b) specified parameters of authentication request submitted;
(c) specified parameters received as authentication response;
(d) the record of disclosure of information to the Aadhaar number holder at the time of authentication; and (e) record of consent of the Aadhaar number holder for authentication, but shall not, in any event, retain the PID information.
(2) The logs of authentication transactions shall be maintained by the requesting entity for a period of 2 (two) years, during which period an Aadhaar number holder shall have the right to access such logs, in accordance with the procedure as may be specified.
(3) Upon expiry of the period specified in sub-regulation (2), the logs shall be archived for a period of five years or the number of years as required by the laws or regulations governing the entity, whichever is later, and upon expiry of the said period, the logs shall be deleted except those records required to be retained by a court or required to be retained for any pending disputes.
(4) The requesting entity shall not share the authentication logs with any person other than the concerned Aadhaar number holder upon his request or for grievance redressal and resolution of disputes or with the Authority for audit purposes. The authentication logs shall not be used for any purpose other than stated in this sub-regulation.
(5) The requesting entity shall comply with all relevant laws, rules and regulations, including, but not limited to, the Information Technology Act, 2000 and the Evidence Act, 1872, for the storage of logs.
(6) The obligations relating to authentication logs as specified in this regulation shall continue to remain in force despite termination of appointment in accordance with these regulations.
xx xx xx
26. Storage and Maintenance of Authentication Transaction Data. –
(1) The Authority shall store and maintain authentication transaction data, which shall contain the following information:-
(a) authentication request data received including PID block;
(b) authentication response data sent;
(c) meta data related to the transaction;
(d) any authentication server side configurations as necessary Provided that the Authority shall not, in any case, store the purpose of authentication.
The Aadhaar (Data Security) Regulations, 2016
3. Measures for ensuring information security. –
(1) The Authority may specify an information security policy setting out inter alia the technical and organisational measures to be adopted by the Authority and its personnel, and also security measures to be adopted by agencies, advisors, consultants and other service providers engaged by the Authority, registrar, enrolling agency, requesting entities, and Authentication Service Agencies.
(2) Such information security policy may provide for:-
(a) identifying and maintaining an inventory of assets associated with the information and information processing facilities;
(b) implementing controls to prevent and detect any loss, damage, theft or compromise of the assets;
(c) allowing only controlled access to confidential information;
(d) implementing controls to detect and protect against virus/malwares;
(e) a change management process to ensure information security is maintained during changes;
(f) a patch management process to protect information systems from vulnerabilities and security risks;
(g) a robust monitoring process to identify unusual events and patterns that could impact security and performance of information systems and a proper reporting and mitigation process;
(h) encryption of data packets containing biometrics, and enabling decryption only in secured locations;
(i) partitioning of CIDR network into zones based on risk and trust;
(j) deploying necessary technical controls for protecting CIDR network;
(k) service continuity in case of a disaster; (l) monitoring of equipment, systems and networks;
(m) measures for fraud prevention and effective remedies in case of fraud;
(n) requirement of entering into non-disclosure agreements with the personnel;
(o) provisions for audit of internal systems and networks;
(p) restrictions on personnel relating to processes, systems and networks.
(q) inclusion of security and confidentiality obligations in the agreements or arrangements with the agencies, consultants, advisors or other persons engaged by the Authority.
(3) The Authority shall monitor compliance with the information security policy and other security requirements through internal audits or through independent agencies.
(4) The Authority shall designate an officer as Chief Information Security Officer for disseminating and monitoring the information security policy and other security-related programmes and initiatives of the Authority.
xx xx xx
5. Security obligations of service providers, etc. – The agencies, consultants, advisors and other service providers engaged by the Authority for discharging any function relating to its processes shall:
(a) ensure compliance with the information security policy specified by the Authority;
(b) periodically report compliance with the information security policy and contractual requirements, as required by the Authority;
(c) report promptly to the Authority any security incidents affecting the confidentiality, integrity and availability of information related to the Authority’s functions;
(d) ensure that records related to the Authority shall be protected from loss, destruction, falsification, unauthorised access and unauthorised release;
(e) ensure confidentiality obligations are maintained during the term and on termination of the agreement;
(f) ensure that appropriate security and confidentiality obligations are provided for in their agreements with their employees and staff members;
(g) ensure that the employees having physical access to CIDR data centers and logical access to CIDR data centers undergo necessary background checks;
(h) define the security perimeters holding sensitive information, and ensure only authorised individuals are allowed access to such areas to prevent any data leakage or misuse; and
(i) where they are involved in the handling of the biometric data, ensure that they use only those biometric devices which are certified by a certification body as identified by the Authority and ensure that appropriate systems are built to ensure security of the biometric data.
The Aadhaar (Sharing of Information) Regulations, 2016.
3. Sharing of information by the Authority. –
(1) Core biometric information collected by the Authority under the Act shall not be shared with anyone for any reason whatsoever.
(2) The demographic information and photograph of an individual collected by the Authority under the Act may be shared by the Authority with a requesting entity in response to an authentication request for e-KYC data pertaining to such individual, upon the requesting entity obtaining consent from the Aadhaar number holder for the authentication process, in accordance with the provisions of the Act and the Aadhaar (Authentication) Regulations, 2016.
(3) The Authority shall share authentication records of the Aadhaar number holder with him in accordance with regulation 28 of the Aadhaar (Authentication) Regulations, 2016.
(4) The Authority may share demographic information and photograph, and the authentication records of an Aadhaar number holder when required to do so in accordance with Section 33 of the Act.
xx xx xx
6. Restrictions on sharing, circulating or publishing of Aadhaar number. –
(1) The Aadhaar number of an individual shall not be published, displayed or posted publicly by any person or entity or agency.
(2) Any individual, entity or agency, which is in possession of Aadhaar number(s) of Aadhaar number holders, shall ensure security and confidentiality of the Aadhaar numbers and of any record or database containing the Aadhaar numbers.
(3) Without prejudice to sub-regulations (1) and (2), no entity, including a requesting entity, which is in possession of the Aadhaar number of an Aadhaar number holder, shall make public any database or record containing the Aadhaar numbers of individuals, unless the Aadhaar numbers have been redacted or blacked out through appropriate means, both in print and electronic form.
(4) No entity, including a requesting entity, shall require an individual to transmit his Aadhaar number over the Internet unless such transmission is secure and the Aadhaar number is transmitted in encrypted form except where transmission is required for correction of errors or redressal of grievances.
(5) No entity, including a requesting entity, shall retain Aadhaar numbers or any document or database containing Aadhaar numbers for longer than is necessary for the purpose specified to the Aadhaar number holder at the time of obtaining consent.”
43) To sum up broadly, the Authority is established under the Act as a statutory body which is given the task of developing the policy, procedure and system for issuing Aadhaar numbers to individuals and also to perform authentication thereof as per the provisions of the Act. For the purpose of enrolment and assigning Aadhaar numbers, enrolling agencies are recruited by the Authority. All the residents in India are eligible to obtain an Aadhaar number.
To enable a resident to get Aadhaar number, he is required to submit demographic as well as biometric information i.e., apart from giving information relating to name, date of birth and address, biometric information in the form of photograph, fingerprint, iris scan is also to be provided. Aadhaar number given to a particular person is treated as unique number as it cannot be reassigned to any other individual. Insofar as subsidies, benefits or services to be given by the Central Government or the State Government, as the case may be, is concerned, these Governments can mandate that receipt of these subsidies, benefits and services would be given only on furnishing proof of possession of Aadhaar number (or proof of making an application for enrolment, where Aadhaar number is not assigned). An added requirement is that such individual would undergo authentication at the time of receiving such benefits etc.
A particular institution/body from which the aforesaid subsidy, benefit or service is to be claimed by such an individual, the intended recipient would submit his Aadhaar number and is also required to give her biometric information to that agency. On receiving this information and for the purpose of its authentication, the said agency, known as Requesting Entity, would send the request to the Authority which shall perform the job of authentication of Aadhaar number. On confirming the identity of a person, the individual is entitled to receive subsidy, benefit or service. Aadhaar number is permitted to be used by the holder for other purposes as well.
44) In this whole process, any resident seeking to obtain an Aadhaar number is, in the first instance, required to submit her demographic information and biometric information at the time of enrolment. She, thus, parts with her photograph, fingerprint and iris scan at that stage by giving the same to the enrolling agency, which may be a private body/person. Likewise, every time when such Aadhaar holder intends to receive a subsidy, benefit or service and goes to specified/designated agency or person for that purpose, she would be giving her biometric information to that requesting entity, which, in turn, shall get the same authenticated from the Authority before providing a subsidy, benefit or service.
Whenever request is received for authentication by the Authority, record of such a request is kept and stored in the CIDR. At the same time, provisions for protection of such information/data have been made, as indicated above. Aadhaar number can also be used for purposes other than stated in the Act i.e. purposes other than provided under Section 7 of the Act, as mentioned in Section 57 of the Act, which permit the State or any body corporate or person, pursuant to any law, for the time being in force, or any contract to this effect, to use the Aadhaar number for establishing the identity of an individual. It can be used as a proof of identity, like other identity proofs such as PAN card, ration card, driving licence, passport etc.
45) Piercing into the aforesaid Aadhaar programme and its formation/structure under the Aadhaar Act, foundational arguments are that it is a grave risk to the rights and liberties of the citizens of this country which are secured by the Constitution of India. It militates against the constitutional abiding values and its foundational morality and has the potential to enable an intrusive state to become a surveillance state on the basis of information that is collected in respect of each individual by creation of a joint electronic mesh. In this manner, the Act strikes at the very privacy of each individual thereby offending the right to privacy which is elevated and given the status of fundamental right by tracing it to Articles 14, 19 and 21 of the Constitution of India by a nine Judge Bench judgment of this Court in K.S. Puttaswamy & Anr. v. Union of India & Ors.6. Most of the counsel appearing for different petitioners (though not all) conceded that there cannot be a serious dispute insofar as allotment of Aadhaar number, for the purpose of unique identification of the residents, is concerned.
However, apprehensions have been expressed about the manner in which the Scheme has been rolled out and implemented. The entire edifice of the aforesaid projection is based on the premise that it forces a person, who intends to enrol for Aadhaar, to part with his core information namely biometric information in the form of fingerprints and iris scan. These are to be given to the enrolment agency in the first instance which is a private body and, thus, there is risk of misuse of this vital information pertaining to an individual. Further, it is argued that the most delicate and fragile part, susceptible to misuse, is the authentication process which is to be carried out each time the holder of Aadhaar number wants to establish her identity.
At that stage, not only the individual parts with the biometric information again with the RE (which may again be a private agency as well), the purpose for which such a person approaches the RE would also be known i.e. the nature of transaction which is supposed to be undertaken by the said person at that time. Such information relating to different transactions of a person across the life of the citizen is connected to a central database. This record may enable the State to profile citizens, track their movements, assess their habits and silently influence their behaviour. Over a period of time, the profiling would enable the State to stifle dissent and influence political decision making. It may also enable the State to act as a surveillant state and there is a propensity for it to become a totalitarian state. It is stressed that at its core, Aadhaar alters the relationship between the citizen and the State.
It diminishes the status of the citizen. Rights freely exercised, liberties freely enjoyed, entitlements granted by the Constitution and laws are all made conditional, on a compulsory barter. The barter compels the citizen to give up her biometrics ‘voluntarily’, allow her biometrics and demographic information to be stored by the State and private operators and then used for a process termed ‘authentication’. To put it in nutshell, provisions of the Aadhaar Act are perceived by the petitioners as giving away of vital information about the residents to the State not only in the form of biometrics but also about the movement as well as varied kinds of transactions which a resident would enter into from time to time.
The threat is in the form of profiling the citizens by the State on the one hand and also misuse thereof by private agencies whether it is enrolling agency or requesting agency or even private bodies mentioned in Section 57 of the Act. In essence, it is stated that not only data of aforesaid nature is stored by the CIDR, which has the threat of being leaked, it can also be misused by non-State actors. In other words, it is sought to be highlighted that there is no assurance of any data protection at any level.
46) The respondents, on the other hand, have attempted to shake the very foundation of the aforesaid structure of the petitioners’ case. They argue that in the first instance, minimal biometric information of the applicant, who intends to have Aadhaar number, is obtained which is also stored in CIDR for the purpose of authentication.
Secondly, no other information is stored. It is emphasised that there is no data collection in respect of religion, caste, tribe, language records of entitlement, income or medical history of the applicant at the time of Aadhaar enrolment.
Thirdly, the Authority also claimed that the entire Aadhaar enrolment ecosystem is foolproof inasmuch as within few seconds of the biometrics having been collected by the enrolling agency, the said information gets transmitted the Authorities/CIDR, that too in an encrypted form, and goes out of the reach of the enrolling agency. Same is the situation at the time of authentication as biometric information does not remain with the requesting agency.
Fourthly, while undertaking the authentication process, the Authority simply matches the biometrics and no other information is received or stored in respect of purpose, location or nature or transaction etc. Therefore, the question of profiling does not arise at all. A powerpoint presentation was given by Dr. Ajay Bhushan Pandey, CEO of the Authority, in the Court, while explaining various nuances of the whole process. In this presentation, the enrolment process has been projected in the following manner:
Image 1
47) Insofar as Aadhaar authentication service is concerned, it was explained that the same is e-KYC wherein following process is involved:
Image 2
48) It was asserted with all vehemence that while doing the aforesaid authentication, no other information is collected or stored by the Authority/CIDR, specifically pointing that:
(a) The Authority does not collect purpose, location or details of transaction. Thus, it is purpose blind.
(b) The information collected as aforesaid remains in silos.
(c) Merging of silos is prohibited.
(d) The RE is provided answer only in Yes or No about the authentication of the person concerned.
(e) The authentication process is not exposed to the internet world.
(f) Security measures as per the provisions of Section 29(3) read with Section 38(g) as well as Regulation 17(1)(d) of the Authentication Regulations are strictly followed and adhere to. The Aadhaar Authentication Security has been described in the following manner:
Image 3
49) In this hue, the Authority has projected that the Aadhaar design takes full care of privacy and security of the persons. It is sought to be demonstrated by pointing out the following features:
(i) Privacy is ensured by the very design of Aadhaar which was conceived by the Authority from very inception and is now even incarnated in the Aadhaar Act because :
(a) it is backed by minimal data, federated databases, optimal ignorance; and
(b) there is no transaction/pooling data coupled with the fact that resident authorised access to identity data is available.
(ii) Aadhaar is designed for inclusion inasmuch as :
(a) there is flexibility of demographic data, multi-modal biometrics, and flexible processes;
(b) DDSVP Committee by Dr. V.N. Vittal, former CVC; and
(c) Biometric design and Standards Committee by Dr. Gairola, Former DG, NIC.
(iii) All security numbers are followed which can be seen from:
(a) PKI-2048 encryption from the time of capture,
(b) adoption of best-in-class security standards and practices, and
(c) strong audit and traceability as well as fraud detection.
50) It was explained that the security and data privacy is ensured in the following way:
(i) The data sent to ABIS is completely anonymised. The ABIS systems do not have access to resident’s demographic information as they are only sent biometric information of a resident with a reference number and asked to de-duplicate. The de-duplication result with the reference number is mapped back to the correct enrolment number by the Authorities own enrolment server.
(ii) The ABIS providers only provide their software and services. The data is stored in UIDAI storage and it never leaves the secure premises.
(iii) The ABIS providers do not store the biometric images (source). They only store template for the purpose of de- duplication (with reference number).
(iv) The encrypted enrolment packet sent by the enrolment client software to the CIDR is decrypted by the enrolment server but the decrypted packet is never stored.
(v) The original biometric images of fingerprints, iris and face are archived and stored offline. Hence, they cannot be accessed through an online network.
(vi) The biometric system provides high accuracy of over 99.86%. The mixed biometric have been adopted only t enhance the accuracy and to reduce the errors which may arise on account of some residents either not having biometrics or not having some particular biometric.
51) Above all, there is an oversight by Technology and Architecture Review Board (TARB) and Security Review Committee. This Board and Committee consists of very high profiled officers. The aforesaid security measures are shown by the Authority in the following manner:
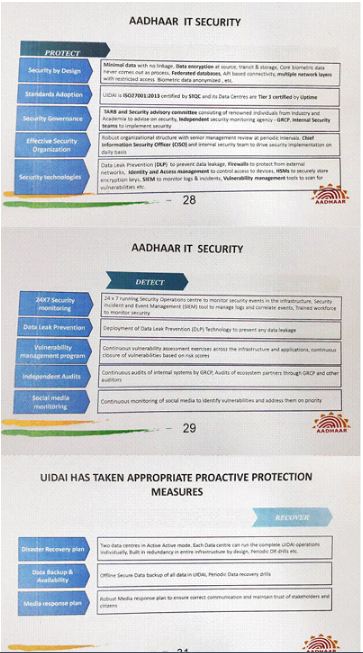
52) We may point out at this stage that to the powerpoint presentation by Dr. Pandey on the aforesaid lines, certain questions were put to him by Mr. Shyam Divan as well as Mr. Vishwanathan, senior advocates, and the answers thereto were given by Dr. Pandey. In order to have the complete picture, we will be well advised to reproduce these questions and their answers as well, which are as follows:
53) Questions and Answers to the queries raised by the petitioners in W.P. (C) No. 1056 of 2017 entitled ‘Nachiket Udupa & Anr. v. Union of India
(1) What are the figures for authentication failures, both at the national and state level? Please provide a breakup, between fingerprints and iris.
Ans.: UIDAI cannot provide authentication failure rates at the state level since it does not track the location of the authentication transactions. Authentication failure rate at national level is as below:
|
Modality |
Unique UID Participated |
Failed Unique ID |
Failed Percentage |
|
IRIS |
1,08,50,391 |
9,27,132 |
8.54% |
|
FINGER |
61,63,63,346 |
3,69,62,619 |
6.00% |
It must be stated that authentication failures do not mean exclusion or denial from subsidies, benefits or services since the requesting entities are obliged under the law to provide for exception handling mechanisms.
(2) In case a person who is claiming a biometric exception (e.g. a person suffering from leprosy) does not have a mobile phone number, or has not given it in the enrolment form, or if the phone number changes – how will her Aadhaar enrolment and subsequent authentication occur and under which provision of law? Ans.: Aadhaar enrolment is done for all residents, even of residents with leprosy. Biometric exception process is defined in the UIDAI resident enrolment process. In the case of a leprosy patient, who may not be able to do fingerprint authentication, iris authentication can be used for update (and add the mobile number).
This was the reason for multi-modal enrolment and authentication being selected for use in Aadhaar. Only in an unlikely scenario where both iris and fingerprint cannot be used for authentication, the mobile number is one of the methods for authentication. In cases where authentication through mobile number is not possible or feasible, the requesting entities have to provide their own exception and backup mechanism to ensure services to Aadhaar holders. As part of the exception handling mechanism, UIDAI has already implemented a digitally signed QR code into e-Aadhaar which allows agencies to verify the Aadhaar card in an off-line manner and trust the data (based on digital signature validation) without accessing e-KYC API service of UIDAI.
This is a simple off-line mechanism to quickly verify the legitimacy of the Aadhaar card. But, it does not ensure that the person holding the card is the owner of that Aadhaar number. It needs either manual check of photo against the face of the individual (like the way ID is verified at the entry of airports) or some form of electronic authentication using Aadhaar authentication API or agency specific authentication scheme. QR code based verification allows Aadhaar number holders to use their ID on a day-to-day purpose without using online e-KYC authentication. The verification through offline QR code can be used for those purposes or cases where proof of presence or proof of ownership of card is not required. The Aadhaar Act and Aadhaar
(Enrolment and Update)
Regulations, 2016 define special provision for enrolment of residents with biometric exception. Further, as per Regulation 14(i) of the Authentication Regulations, RE shall implement exception-handling mechanisms and backup identity authentication mechanisms to ensure seamless provision of authentication services to Aadhaar number holders. Accordingly, DBT Mission Cabinet Secretariat has issued a detailed circular dated December 19, 2017 regarding exception handling during use of Aadhaar in the benefit schemes of the Government.
(3) Are there any surprise checks, field studies done to check the authenticity of the exemption registers?
Ans.: As per Regulation 14(i) of the Authentication Regulations, this exception handling mechanism is to be implemented and monitored by the requesting entities and in case of the Government, their respective Ministries. Further, the DBT Mission Cabinet Secretariat had issued Circular dated December 19, 2017 on exception handling and audit of exceptions.
(4) Between the ages of 5-15 years, can a school, as an ‘introducer’, enrol a child without parental consent? Ans.: School officials, if permitted to act as ‘introducer’, can enrol only when there is a parental consent to enrol. The disclosure requirement as per Section 3(2) of the Aadhaar Act and the Aadhaar (Enrolment and Update) Regulations, 2016 (Schedule-I) is implemented through the enrolment form which is signed by the resident making it informed disclosure. In case of children, the consent form will be signed by the parent/guardian.
(5) Once a child attains the age of 18 years, is there any way for them to opt out or revoke consent? Ans.: It is not permissible under the Aadhaar Act. However, residents have the option of permanently locking their biometrics and only temporarily unlock it when needed for biometric authentication as per Regulation 11 of the Authentication Regulations.
(6) What is the status of the enrolments done by the 49,000 blacklisted enrolment operators? Please provide the number of enrolments done by them? Ans.: UIDAI has a policy to enforce the process guidelines and data quality check during the enrolment process. 100% of the enrolment done by operators undergoes a quality assurance check, wherein every enrolment passes through a human eye. Any Aadhaar enrolment found to be contrary to the UIDAI process, the enrolment itself gets rejected and Aadhaar is not generated. The resident is advised to re-enroll. Once an operator is blacklisted or suspended, further enrolments cannot be carried out by him during the time the order of blacklisting/suspension is valid.
(7) What are the total number of biometric De-duplication rejections that have taken place till date? In case an enrolment is rejected either for:
(a) duplicate enrolment and
(b) other technical reason under Regulation 14 of the Aadhaar Enrolment Regulations, what happens to the data packet that contains the stored biometric and demographic information?
Ans.: The total number of biometric de-duplication rejections that have taken place are 6.91 crores as on March 21, 2018. These figures do not pertain to the number of unique individuals who have been denied Aadhaar enrolment resulting in no Aadhaar issued to them. This figure merely pertains to the number of applications which have been identified by the Aadhaar de-duplication system as having matching biometrics to an existing Aadhaar number holder. The biometric de-duplication system is designed to identify as duplicate those cases where any one of the biometrics (ten fingers and two irises) match. However, very often it is found that all the biometrics match. It is highly improbable for the biometrics to match unless the same person has applied again.
There are a number of reasons why the same person might apply more than once. For instance, many individuals innocently apply for enrolment multiple times because of the delay in getting their Aadhaar cards due to postal delays, loss or destruction of their cards or confusion about how the system works. Each time one applies for Aadhaar, the system identifies her as a new enrolment but when it recognises that the individual’s biometrics match with already those in the database, thereafter further checks, including manual check through experienced personnels, are done.
After that exercise, if it is found that the person is already registered, it rejects the enrolment application. One of their main reasons for rejection is that multiple people would put their biometric details like fingerprints for Aadhaar generation either as a fraudulent exercise or by mistake, which also would get rejected. There were many fakes and frauds in the earlier systems and several reports have found that almost 50% of the subsidies were getting pilfered away by fakes and duplicates in the system.
Then, there would also be several such people who may have tried to defraud the Aadhaar enrolment system as well but failed get multiple Aadhaar numbers due to the stringent Aadhaar de-duplication process. Thus, the mere fact that 6.23 crore enrolments have been rejected as biometric duplicates does not mean that 6.23 crore people have been denied an Aadhaar number as has been alleged by the petitioners. Any genuine person who does not have an Aadhaar number and whose enrolment has been rejected can always apply again for enrolment.
It is worth noting that none of the deduplication rejects have come forward to lodge complaints either with the Authority or with the Government about denial of Aadhaar number. None of them have even approached any Court of law. Evidently, the genuine residents have got themselves re-enrolled and the rest are those who were trying to reach the Aadhaar system by fraudulent means. That explains why no one has approached a court of law complaining denial of Aadhaar number. All the enrolment packets received by UIDAI (accepted/rejected) are archived in the CIDR irrespective of its status.
(8) If the figure of rejection of enrolment packets was 8 crore, as on 2015, what is the total rejection figure for enrolment packets as on date? How many field studies/physical verification have been done to ensure that these persons (who have been rejected) are indeed “False or duplicate” enrolments?
Ans.: The total rejection figure for enrolment packets is 18.0 cr. as on March 26, 2018. These rejections are due to various technical reasons like:
(i) data quality reject such as address incomplete, name incomplete, use of expletives in names, address etc. photo is of object, photo of photo, age photo mismatch etc.; and
(ii) OSI validation reject such as operator / supervisor / introducer validation failed, operator / supervisor / introducer / Head of Family biometric validation failed etc. Those whose enrolments have been rejected for any reason and who do not have Aadhaar can re-enrol and obtain Aadhaar. Rejection of enrolments do not mean that the person will never be able to get Aadhaar.
(9) What does “any other appropriate response” under Section 8(4) of the Aadhaar Act include? Ans.: “Any other appropriate responses” includes e-KYC or limited e-KYC data. As per Regulation 3 of Authentication Regulations, UIDAI provides two types of authentication facilities, namely –
(i) Yes/No authentication facility; and
(ii) e-KYC authentication facility. In Yes/No authentication, UIDAI provides the response as Yes or No along with relevant error codes, if any. In e-KYC authentication, UIDAI provides the demographic data along with photograph and in case of mismatch/error, the relevant error codes.
54) Questions and Answers to the queries raised by the petitioners in W.P. (C) No. 829 of 2013 entitled ‘S.G. Vombatkere & Anr. v. Union of India
(1) Please confirm that no UIDAI official verifies the correctness of documents offered at the stage of enrolment/updating.
Ans.: As per UIDAI process, the verification of the documents is entrusted to the Registrar. For Verification based on Documents, the verifier present at the Enrolment Centre will verify the documents. Registrars/Enrolment agency must appoint personnel for the verification of documents.
(2) Please confirm that UIDAI does not know whether the documents shown at the time of enrolment/updating are genuine or false. Ans.: The answer is same as in (1) above.
(3) Please confirm: (a) UIDAI does not identify the persons it only matches the biometric information received at the time of authentication with its records and provides a Yes/No response; Ans.: Biometric authentication of an Aadhaar number holder is always performed as 1:1 biometric match against his/her Aadhaar number (identity) in CIDR. Based on the match, UIDAI provides Yes or No response. A “Yes” response means a positive identification of the Aadhaar number holder. Each enrolment is biometrically de-duplicated against all (1.2 billion) residents to issue the Aadhaar number (or Unique Identity).
(b) UIDAI takes no responsibility with respect to the correctness of the name, date of birth or address of the person enrolled. Ans.: The Name/Address/DOB are derived from the Proof of Identity (POI)/Proof of Address (POA) documents submitted during enrolments. The enrolment/update packet (encrypted) retains a scanned copy of the POI/POA documents used for the enrolment which can be reviewed in case of dispute. UIDAI maintains the update history of each Aadhaar number related to changes in name, address, date of birth etc.
(4) Please confirm:
(a) UIDAI takes no responsibility with respect to the correct identification of a person. Ans.: Please refer to Answer (1) above. Additionally, it may be stated that enrolment of Aadhaar is done through a resident enrolment process and verification of the POI/POA document is done against the acceptable documents, as per the UIDAI valid list of documents as provided in Schedule II and III Aadhaar (Enrolment and Update) Regulations, 2016 read with Regulation
10. UIDAI takes responsibility in creating and implementing standards, ensuring matching systems installed in CIDR work as they are designed to do, and providing options to Aadhaar holders in terms of controlling their identity (such as updating their data, locking their biometrics, etc.) and accessing their own authentication records. One of the key goals of Aadhaar is to issue a unique identity for the residents of India. Hence, each enrolment is biometrically de-duplicated against all (1.2 billion) residents to issue the Aadhaar number (or Unique Identity). Section 4 of Aadhaar lays down the properties of an Aadhaar number. Sub-section (3) of Section 4 reads as under:
“(3) An Aadhaar number, in physical or electronic form subject to authentication and other conditions, as may be specified by regulations, may be accepted as proof of identity of the Aadhaar number holder for any purpose.” The requesting entities are at liberty to use any or multiple of authentication mode available under Regulation 4 of Aadhaar (Authentication) Regulation, 2016 as per their requirements and needs of security etc. (b) The biometric authentication is based on a probabilistic match of the biometric captured during authentication and the record stored with CIDR. Ans.: Biometric authentication is based on 1:1 matching and, therefore, in that sense it is not probabilistic. If biometrics are captured it will lead to successful authentication. If biometrics are not well captured during authentication or an impostor tries authentication, it will lead to authentication failure. Aadhaar Proof of Concept studies show that a vast majority of residents (>98%) can successfully authenticate using biometric modalities such fingerprints and/or iris. However, the Aadhaar Act and Regulations provides that an Aadhaar number holder cannot be denied service due to the failure of Aadhaar authentication. Hence, all Aadhaar applications must implement exception processes. Possible methods to implement the exception process include:
(i) Family Based Authentication: Family based applications such as PDS or Health applications may allow authentication by family members to allow resident to avail services.
(ii) Alternate Modalities: Some applications may use different modalities for exception handling. Alternate modalities include:
(a) Iris Authentication
(b) OTP Authentication (if allowed by policy)
(iii) Biometric Fusion: UIDAI is introducing face authentication as secondary authentication factor to reduce the rate of authentication failures, especially for senior citizens. At this time, face authentication will be used only conjunction with another authentication factor such as finger/iris/OTP.
(a) Face + Finger Fusion
(b) Face + Iris Fusion (c) Face + OTP Fusion
(iv) Non Aadhaar Based Exception process: Applications may implement non-Aadhaar based exception process to ensure that no resident is denied service. Applications need to monitor the use of exceptions in their applications to prevent misuse of the exception process.
(v) Accordingly, DBT Mission Cabinet Secretariat had issued a detailed circular dated December 19, 2017 regarding use of Aadhaar in benefit schemes of Government – exception handling.
(5) Please confirm that with respect to individuals under 15 years and over 60 years of age, biometric authentication is likely to fail due to changes in/fading of biometrics such as fingerprints.
Ans.: Though there is no conclusive evidence to say that biometric authentication success is dependent upon age, slightly higher authentication failure rates have been observed only for fingerprints for senior citizens above the age of 70. A number of exception processes are provided in answer to Question 4(b) above to prevent denial of service for failure of authentication. Further, in case of any issue in biometric authentication, an Aadhaar number holder may update his/her biometric at any of the Aadhaar enrolment centres, which is also provided for in the Aadhaar Act.
(6) Please confirm that the reasons why over 49000 enrolment operators were blacklisted include:
(i) failure to verify documents presented;
(ii) failure to maintain records of documents submitted;
(iii) misuse of information submitted; and
(iv) aiding or abetting false enrolments?
Ans.: UIDAI has a policy to enforce the process guidelines and data quality check during the enrolment process. 100% of the enrolments done by operators undergoes a quality assurance check. If any Aadhaar enrolment is found to be not as per the UIDAI process, the enrolment itself gets rejected and Aadhaar is not generated. If such mistake by an operator crosses a threshold defined in the policy, the operator is blacklisted/ removed from the UIDAI ecosystem. As such, of the 49,000 operators who have been blacklisted/removed from the UIDAI eco-system, all the enrolments which were in violation of the process were rejected in the QA stage. Enrolment operators may be blacklisted for the following reasons:
illegally charging the resident for Aadhaar enrolment
poor demographic data quality
invalid biometric exceptions
other process malpractice
(7) Please confirm:
(a) At the stage of enrolment, there is no verification as to whether a person is an illegal immigrant.
(b) At the stage of enrolment, there is no verification about a person being resident in India for 182 days or more in the past 12 months.
(c) Foreign nationals may enrol and are issued Aadhaar numbers.
(d) Persons retain their Aadhaar number even after they cease to be resident. This is true of foreign nationals as well.
Ans.:
(a) At the time of enrolment, verification is done based upon documents provided by the resident. In case any violation of prescribed guidelines comes to light, the concerned Aadhaar is omitted/deactivated.
(b) This has been included through the enrolment form where resident undertakes and signs the disclosure: “Disclosure under Section 3(2) of the Aadhaar (Targeted Delivery of Financial And Other Subsidies, Benefits and Services) Act, 2016 I confirm that I have been residing in India for at least 182 days in the preceding 12 months & information (including biometrics) provided by me to the UIDAI is my own and is true, correct and accurate. I am aware that my information (including biometrics) will be used for generation of Aadhaar and authentication. I understand that my identity information (except core biometric) may be provided to an agency only with my consent during authentication or as per the provisions of the Aadhaar Act. I have a right to access my identity information (except core biometrics) following the procedure laid down by UIDAI.”
(c) Aadhaar is issued to the resident of India and the word ‘resident’ is defined in Section 2(v) of the Aadhaar Act. Aadhaar numbers may be issued to foreign nationals who are resident in India. Section 2(v) reads as under: ” ‘resident’ means an individual who has resided in India for a period or periods amounting in all to one hundred and eighty-two days or more in the twelve months immediately preceding the date of application for enrolment;” A foreign national fulfilling the above criteria is eligible for Aadhaar, provided he submits the acceptable POI/POA document as per the UIDAI valid list of documents.
(d) As per the Aadhaar Act, an Aadhaar number is issued to a resident who has been residing in India for at least 182 days in the preceding 12 months. An Aadhaar number is issued to an individual for life and may be omitted/deactivated in case of violation of prescribed guidelines only. Ineligibility of a person to retain an Aadhaar number owing to become non-resident may be treated as a ground for deactivation of Aadhaar number and Regulation 28(l)(f) of the Aadhaar Enrolment Regulations. This is in keeping with Section 31(1) and (3) of the Aadhaar Act wherein it is an obligation on an Aadhaar number holder to inform the UIDAI of changes in demographic information and for the Authority to make the necessary alteration.
(8) Please confirm the Points of Service (POS) biometric readers are capable of storing biometric information. Ans.: UIDAI has mandated use of Registered Devices (RD) for all authentication requests. With RDs, biometric data is signed within the device/RD service using the provider key to ensure it is indeed captured live. The device provider RD service encrypts the PID block before returning to the host application. This RD service encapsulates the biometric capture, signing and encryption of biometrics all within it. Therefore, introduction of RD in Aadhaar authentication system rules out any possibility of use of stored biometric and replay of biometrics captured from other source. Requesting entities are not legally allowed to store biometrics captured for Aadhaar authentication under Regulation 17(1)(a) of the Authentication Regulations.
(9) Referring to slide/page 13, please confirm that the architecture under the Aadhaar Act includes:
(i) authentication user agencies (e.g. Kerala Dairy Farmers Welfare Fund Board);
(ii) authentication service agencies (e.g. Airtel); and
(iii) CIDR. Ans.: UIDAI appoints Requesting Entities (AUA/KUA) and Authentication Service Agency (ASA) as per Regulation 12 of Authentication Regulations. List of Requesting Entitles (AUA/KUA) and Authentication Service Agency appointed by UIDAI is available on UIDAI’s website. An AUA/KUA can do authentication on behalf of other entities under Regulation 15 and Regulation 16.
(10) Please confirm that one or more entitles in the Aadhaar architecture described in the previous paragraph record the date and time of the authentication, the client IP, the device ID and purpose of authentication. Ans.: UIDAI does not ask requesting entities to maintain any logs related to IP address of the device, GPS coordinates of the device and purpose of authentication. However, AUAs like banks, telecom etc., in order to ensure that their systems are secure, frauds are managed, they may store additional information as per their requirement under their respective laws to secure their system. Section 32(3) of the Aadhaar Act specifically prevents the UIDAI from either by itself or through any entity under its control to keep or maintain any information about the purpose of authentication. Requesting entities are mandated to maintain following logs as per Regulation 18 of the Authentication Regulations.
These are:
(i) the Aadhaar number against which authentication is sought;
(ii) specified parameters of authentication request submitted;
(iii) specified parameters received as authentication response;
(iv) the record of disclosure of information to the Aadhaar number holder at the time of authentication; and
(v) record of consent of the Aadhaar number holder for authentication, but shall not, in any event, retain the PID information.
Further, even if a requesting entity captures any other data as per their own requirement, UIDAI will only audit the authentication logs maintained by the requesting entity as per Regulation 18(1) of the Authentication Regulations. ASAs are not permitted to maintain any logs related to IP address of the device, GPS coordinates of the device etc. ASAs are mandated to maintain logs as per Regulation 20 of the Authentication Regulations:
(i) identity of the requesting entity;
(ii) parameters of authentication request submitted; and
(iii) parameters received as authentication response. Provided that no Aadhaar number, PID information, device identity related data and e-KYC response data, where applicable, shall be retained.
(11) Referring to slide/page 7 and 14, please confirm that ‘traceability’ features enable UIDAI to track the specific device and its location from where each and every authentication takes place.
Ans.: UIDAI gets the AUA code, ASA code, unique device code, registered device code used for authentication. UIDAI does not get any information related to the IP address or the GPS location from where authentication is performed as these parameters are not part of authentication (v2.0) and e-KYC (v2.1) API UIDAI would only know from which device the authentication has happened, through which AUA/ASA etc.
This is what the slides meant by traceability. UIDAI does not receive any information about at what location the authentication device is deployed, its IP address and its operator and the purpose of authentication. Further, the UIDAI or any entity under its control is statutorily barred from collecting, keeping or maintaining any information about the purpose of authentication under Section 32(3) of the Aadhaar Act.
Summing up the Scheme:
55) The whole architecture of Aadhaar is devised to give unique identity to the citizens of this country. No doubt, a person can have various documents on the basis of which that individual can establish her identify. It may be in the form of a passport, Permanent Account Number (PAN) card, ration card and so on. For the purpose of enrolment itself number of documents are prescribed which an individual can produce on the basis of which Aadhaar card can be issued. Thus, such documents, in a way, are also proof of identity.
However, there is a fundamental difference between the Aadhaar card as a mean of identity and other documents through which identity can be established. Enrolment for Aadhaar card also requires giving of demographic information as well as biometric information which is in the form of iris and fingerprints. This process eliminates any chance of duplication. It is emphasised that an individual can manipulate the system by having more than one or even number of PAN cards, passports, ration cards etc.
When it comes to obtaining Aadhaar card, there is no possibility of obtaining duplicate card. Once the biometric information is stored and on that basis Aadhaar card is issued, it remains in the system with the Authority. Wherever there would be a second attempt for enrolling for Aadhaar and for this purpose same person gives his biometric information, it would immediately get matched with the same biometric information already in the system and the second request would stand rejected. It is for this reason the Aadhaar card is known as Unique Identification (UID). Such an identity is unparalleled.
56) There is, then, another purpose for having such a system of issuing unique identification cards in the form of Aadhaar card. A glimpse thereof is captured under the heading ‘Introduction’ above while mentioning how and under what circumstances the whole project was conceptualised. To put it tersely, in addition to enabling any resident to obtain such unique identification proof, it is also to empower marginalised section of the society, particularly those who are illiterate and living in abject poverty or without any shelter etc. It gives identity to such persons also. Moreover, with the aid of Aadhaar card, they can claim various privileges and benefits etc. which are actually meant for these people. Identity of a person has a significance for every individual in his/her life.
In a civilised society every individual, on taking birth, is given a name. Her place of birth and parentage also becomes important as she is known in the society and these demographic particulars also become important attribute of her personality. Throughout their lives, individuals are supposed to provide such information: be it admission in a school or college or at the time of taking job or engaging in any profession or business activity, etc. When all this information is available in one place, in the form of Aadhaar card, it not only becomes unique, it would also qualify as a document of empowerment. Added with this feature, when an individual knows that no other person can clone her, it assumes greater significance.
57) Thus, the scheme by itself can be treated as laudable when it comes to enabling an individual to seek Aadhaar number, more so, when it is voluntary in nature. Howsoever benevolent the scheme may be, it has to pass the muster of constitutionality. According to the petitioners, the very architecture of Aadhaar is unconstitutional on various grounds, glimpse whereof can be provided at this stage:
Gist of the challenge to the Aadhaar Scheme as well as the Act:
58) The petitioners accept that the case at hand is unique, simply because of the reason that the programme challenged here is itself without precedent. According to them, no democratic society has adopted a programme that is similar in its command and sweep. The case is about a new technology that the Government seeks to deploy and a new architecture of governance that it seeks to build on this technology. The petitioners are discrediting the Government’s claim that biometric technology employed and the Aadhaar Act is greatly beneficial. As per the petitioners, this is an inroad into the rights and liberties of the citizens which the Constitution of India guarantees. It is intrusive in nature. At its core, Aadhaar alters the relationship between the citizen and the State. It diminishes the status of the citizens. Rights freely exercised, liberties freely enjoyed, entitlements granted by the Constitution and laws are all made conditional, on a compulsory barter. The barter compels the citizens to give up their biometrics ‘voluntarily’, allow their biometrics and demographic information to be stored by the State and private operators and then used for a process termed ‘authentication’. According to them, by the very scheme of the Act and the way it operates, it has propensity to cause ‘civil death’ of an individual by simply switching of Aadhaar of that person. It is the submission of the petitioners that the Constitution balances rights of individuals against State interest. The Aadhaar completely upsets this balance and skews the relationship between the citizen and the State enabling the State to totally dominate the individual.
59) The challenge is directed at the constitutional validity of the following facets of Aadhaar:
(i) The Aadhaar programme that operated between January 28, 2009 until the bringing into force of the Aadhaar Act on July 12, 2016.
(ii) The Aadhaar Act (and alternatively certain provisions of that Act).
(iii) Elements of the Aadhaar project or programme that continues to operate, though not within the cover of the Aadhaar Act.
(iv) Specific Regulations framed under the Aadhaar Act, illustratively the Aadhaar (Authentication) Regulations, 2016.
(v) A set of subordinate legislation in the form of statutory rules/regulations including the Money Laundering (Amendment) Rules, 2017.
(vi) All notifications (nearly 139) issued under Section 7 of the Aadhaar Act (assuming the Act is upheld) insofar as they make Aadhaar mandatory for availing certain benefits/services/subsidies, including PDS, MGNREGA and social security pension.
(vii) Actions on the part of the authorities to make Aadhaar mandatory even where not covered by Section 7, inter alia: Actions by CBSE, NEET, JEE and UGC requirements for scholarship.
(viii) Specifically, actions on part of the Government mandating linking of mobile phones and Aadhaar vide DoT circular dated March 23, 2017.
(ix) Section 139AA of the Income Tax Act, 1961 insofar as it violates Article 21 by mandating linking Aadhaar to PAN and requiring Aadhaar linkage for filing returns.
60) Apart from the declaratory reliefs regarding ultra vires and certiorari to quash the provisions/actions enumerated above, there are certain other reliefs that are also sought, including:
(i) Suitable declarations regarding the physical autonomy of a person over her own body qua the Indian State.
(ii) Mandatory directions requiring the respondents to give an option to persons who are enrolled with the Aadhaar programme to opt out and to delete the data with suitable certification for compliance.
(iii) Mandatory directions to all concerned authorities that should the Aadhaar Act, etc. be upheld, nevertheless, every person must be entitled to avail services, benefits etc. through alternative means of identification. Negatively, nothing can be withheld from a citizen merely because he/she does not have an Aadhaar Card or does not wish to use their Aadhaar Card.
(iv) Mandatory directions consistent with the fundamental right to privacy and the right of a citizen to be let alone that no electronic trial or record of his/her authentication be maintained.
61) On the aforesaid premise, the petitioners point out following heads of challenge:
Surveillance:
62) The project creates the architecture for pervasive surveillance and unless the project is stopped, it will lead to an Orwellian State where every move of the citizen is constantly tracked and recorded by the State. The architecture of the project comprises a Central Identities Data Repository (CIDR) which stores and maintains authentication transaction data. The authentication record comprises the time of authentication and the identity of the requesting entity. Based on this architecture it is possible for the State to track down the location of the person seeking authentication. Since the requesting entity is also identified, the activity that the citizen is engaging in is also known.
Violation of Fundamental Right to Privacy:
63) The fundamental right to privacy is breached by the Aadhaar project and the Aadhaar Act in numerous ways. Following are the illustrations given by the petitioners:
(a) Between 2009-10 and July 2016 the project violated the right to privacy with respect to personal demographic as well as biometric information collected, stored and shared as there was no law authorising these actions.
(b) During both the pre-Act and post-Act periods, the project continues to violate the right to privacy by requiring individuals to part with demographic as well as biometric information to private enrolling agencies.
(c) By enabling private entities to use the Aadhaar authentication platform, the citizen’s right to informational privacy is violated inasmuch as the citizen is compelled to ‘report’ his/her actions to the State.
(d) Even where a person is availing of a subsidy, benefit or service from the State, mandatory authentication through the Aadhaar platform (without an option to the citizen to use an alternative mode of identification) violates the right to informational privacy.
(e) With Aadhaar being made compulsory for holding a bank account, operating a cell phone, having a valid PAN, holding mutual funds, securing admission to school, taking a board examination, etc. the citizen has no option but to obtain Aadhaar. Compelling the citizen to part with biometric information violates individual autonomy and dignity. (f) In a digital society an individual has the right to protect himself by controlling the dissemination of personal information, including biometric information. Compelling an individual to establish his identity by planting her biometric at multiple points of service violates privacy involving the person.
(g) The seeding of Aadhaar in distinct databases enables the content of information about an individual that is stored in different silos to be aggregated. This enables the State to build complete profiles of individuals violating privacy through the convergence of data.
Limited Government:
64) A fundamental feature of the Constitution is the sovereignty of the people with limited Government authority. The Constitution limits governmental authority in various ways, amongst them Fundamental Rights, the distribution of powers amongst organs of the State and the ultimate check by way of judicial review. The Aadhaar project is destructive of the limited Government. The Constitution is not about the power of the State, but about the limits on the power of the State. Post Aadhaar, the State will completely dominate the citizen and alter the relationship between citizen and the State. The features of a totalitarian state is seen from:
(a) A person cannot conduct routine activities such as operating a bank account, holding an investment in mutual funds, receiving government pension, receiving scholarship, receiving food rations, operating a mobile phone without the State knowing about these activities.
(b) The State can build a profile of the individual based on the trial of authentication from which the nature of the citizen’s activity can be determined.
(c) By disabling Aadhaar the State can cause civil death of the person.
(d) By making Aadhaar compulsory for other activities such as air travel, rail travel, directorship in companies, services and benefits extended by the State Governments and Municipal Corporations, etc. there will be virtually no zone of activity left where the citizen is not under the gaze of the State. This will have a chilling effect on the citizen.
(e) In such a society, there is little or no personal autonomy. The State is pervasive, and dignity of the individual stands extinguished.
(f) This is an inversion of the accountability in the Right to Information age: instead of the State being transparent to the citizen, it is the citizen who is rendered transparent to the State.
Impugned Act illegally passed as a ‘Money Bill’:
65) The Bill No. 47 of 2016 introduced in the Lok Sabha and which upon passage became the impugned Act was not a Money Bill in terms of Article 110 of the Constitution of India. Even though the object and purpose of the impugned legislation states that it is to be used for the delivery of subsidies, benefits and services, expenditure for which is incurred from the Consolidated Fund of India, the scope of the impugned Act is far beyond what is envisaged under Article 110.
Inasmuch as the impugned Act has not followed the constitutional procedure mandated for the passage of a law by disguising the statute as a ‘Money Bill’, there is no valid legislative process that has been followed in this case. The legislative process being colourable and since judicial review extends wherever Part III rights are violated, the Aadhaar Act is liable to be struck down.
Procedure followed violates Articles 14 and 21 of the Constitution:
66) The procedure adopted by the respondents, both pre-Act and post-Act, is arbitrary and in violation of Articles 14 and 21 of the Constitution because:
(a) There is no informed consent at the time of enrolment. Individuals are not told about crucial aspects such as potential misuse of the information, the commercial value of the information, the storage of information in a centralised database, that the information supplied could be used against the individual in criminal proceedings pursuant to a court order, there is no optout option, the entire enrolment process is conducted by private entities without any governmental supervision, etc.
(b) UIDAI has no direct relationship with the enrolling agency which collects sensitive personal information (biometric and demographic).
(c) The data collected and uploaded in to the CIDR is not verified by any Government official designated by the UIDAI. The data collected and stored lacks integrity.
(d) The procedure at the stage of enrolment and authentication enables the enrolling agency as well as the ‘requesting entity’ to capture, store and misuse/use the biometric as well as demographic information without the UIDAI having any control over such misuse/use.
Unreliability of Biometrics and Exclusion:
67) The foundation of the project, i.e. biometrics, is an unreliable and untested technology. Moreover, biometric exceptions severely erode reliability. The biometric authentication system works on a probabilistic model. Consequently, entitlements are reduced from certainty to a chance delivery where the biometrics match. Across the country several persons are losing out on their entitlements, for say food rations, because of a biometric mismatch resulting in them being excluded from various welfare schemes. The project is not an ‘identity’ project but an ‘identification’ exercise. Unless the biometrics work, a person in flesh and blood, does not exist for the State.
Illegal Object:
68) It is submitted before us that the objective of creating a single pervasive identification over time is itself illegal. There are several facets to the illegality and amongst them is the very negation of an individual citizen’s freedom to identify through different means. The coercive foundation of the impugned Act is in substance an illegal objective that renders the statute ultra vires Article 14 of the Constitution of India.
Democracy, Identity and Choice:
69) A citizen or resident in a democratic society has a choice to identify himself/herself through different modes in the course of his/her interactions generally in society as well as his/her interactions with the State. Mandating identification by only one highly intrusive mode is excessive, disproportionate and violates Articles 14, 19 and 21.
Children:
70) As per the petitioners, there is no justification to include children in the Aadhaar programme for various reasons.
71) It may also be recorded at this juncture itself that insofar as the Aadhaar Act is concerned, following provisions thereof are specifically attacked as unconstitutional:
(i) Section 2(c) and 2(d) – authentication and authentication record, read with Section 32
(ii) Section 2(h) read with Section 10 of CIDR
(iii) Section 2(l) read with Regulation 23 of the Aadhaar (Enrolment and Updates) Regulation – ‘enrolling agency’
(iv) Section 2
(v) – ‘resident’
(v) Section 3 – Aadhaar Number
(vi) Section 5 – Special treatment to children
(vii) Section 6 – Update of information
(viii) Section 7
(ix) Section 8
(x) Section 9
(xi) Chapter IV – Sections 11 to 23
(xii) Sections 23 and 54 – excessive delegation
(xiii) Section 23(2)(g) read with Chapter VI & VII – Regulations 27 to 32 of the Aadhaar (Enrolment and Update) Regulations, 2016
(xiv) Section 29 (xv) Section 33
(xvi) Section 47
(xvii) Section 48 – Power of Central Government to supersede UIDAI
(xviii) Section 57
(xix) Section 59
Some Introductory Remarks:
72) Before proceeding further, it would be necessary to state here the approach which we have adopted in dealing with various issues that are raised in these petitions. That may help in understanding the manner in which the matter is dealt with. This necessitates some introductory remarks:
(i) We may remark at this stage itself that many of the heads of challenge which are taken note of above are overlapping and, therefore, discussion on one aspect may provide substantial answers to the arguments advanced under the other head of challenge as well. Our endeavour, therefore, would be to eschew the repetitive discussion. However, our anxiety to bring clarity and also in order to have continuity of thought while discussing a particular head, may have led to some repetitions at different places. In any case, we would be dealing with the various heads of challenge, one by one, so as to cover the entire spectrum.
(ii) In order to have a smooth flow of discussion, we are going to formulate the questions which arise in all these petitions and then decide those issues. Since, number of advocates7 appeared on both sides, many of the arguments addressed by them were overlapping and repetitive. In this scenario, we deem it proper to collate the arguments of all the counsel and present the same while undertaking the discussion on each of the issues. Thus, in the process, we would not be referring to each counsel and her arguments.
We may, however, intend to place on record that all the counsel on both sides had taken the advocacy to its highest level by presenting all possible nuances of the complex issues involved. In the process, plethora of literature on such issues, including the law prevailing across the Globe was cited. We, therefore, place on record our appreciation of the sublime nature of lawyering in this case.
(iii) As pointed out above, many number of foreign judgments were cited during arguments. The history of this Court reflects that this Court has liberally accepted the good practices, rules of interpretation and norms of constitutional courts of other jurisdictions. In fact, in drafting Indian Constitution itself, the framing fathers had studied various foreign models and adopted provisions from different Constitutions after deep reflection. Constitutional influences of system prevailing in some of the countries on Indian Constitution can be summarised as under:
|
From UK |
– Parliamentary Type of Government |
|
|
– Cabinet System of Ministers – Bicameral Parliament – Lower House more powerful |
|
|
– Council of Minsters responsible to Lower House |
|
From US |
– Written Constitution – Executive head of State known as President and his being the Supreme Commander of the Armed Forces |
|
|
– Vice-President as the ex-officio Chairman of Rajya Sabha |
|
|
– Bill of Rights |
|
|
– Supreme Court |
|
|
– Provision of States |
|
|
– Independence of Judiciary and judicial review |
|
|
– Preamble – Removal of Supreme Court and High Court Judges |
|
From USSR |
– Fundamental Duties |
|
|
– Five Year Plan |
|
From Australia |
– Concurrent List |
|
|
– Language of the preamble |
|
|
– Provision regarding trade, commerce and intercourse |
|
From Japan |
– Law on which the Supreme Court function |
|
From Weimar Constitution of Germany |
– Suspension of Fundamental Rights during the emergency |
|
From Canada |
– Scheme of federation with a strong centre |
|
|
– Distribution of powers between the centre and the states and placing residuary powers with the centre |
|
From Ireland |
– Concept of Directive Principles of States Policy |
|
|
– Method of election of President |
|
|
– Nomination of members in the Rajya Sabha by the President |
It was, therefore, but natural to find out the manner in which particular provisions have been interpreted by the constitutional courts of the aforesaid countries. Case law of this Court would reflect this for interpreting the provisions relating to ‘Inter-State Trade, Commerce & Intercourse’. The case law of the Australian High Court is liberally referred as this Chapter is influenced by the provisions contained in the Australian Constitution. Likewise, for interpreting provisions of Part IX of the Constitution on ‘Relations between the Union and the States’ where Canadian model is followed, the judgments of Canadian Supreme Court have been cited by this Court from time to time.
Influence of U.S. Constitutionalism, tempered by the wish to preserve India’s own characteristics, while interpreting chapter relating to fundamental rights as well as power of judicial review is also discernible. A critical analysis of the various judgments of this Court, where foreign precedents are cited8, formulates four typologies of use, namely:
(a) Where the court relies on foreign precedents for guidance on general constitutional principles and when necessary to;
(b) Where the court frames the issue posed for adjudication and/or to formulate evaluative test and frameworks;
(c) To distinguish the country’s context from the foreign one9;
(d) To ‘read’ in the Constitution implied or unenumerated rights10. It can be said that though this Court has been liberally relying upon the judgments of the constitutional courts of other countries, particularly when it comes to human rights discourse, at the same time, in certain situations, note of caution is also added to give a message that the judgment of other jurisdiction cannot be relied blindly and it would depend as to whether a particular judgment will fit in Indian context or not. As a matter of fact, in Basheshar Nath, the Court discussed the doctrine of waiver in force in the United States and rejected it firmly stating that: :…the doctrine of waiver enunciated by some American Judges in construing the American Constitution cannot be introduced in our Constitution…We are not for the moment convinced that this theory has any relevancy in construing the fundamental rights conferred by Part III of the Constitution.”
On the contrary, in Romesh Thappar, the Court completely based its decision to strike down a law restricting the free circulation of newspapers on two US precedents, Ex parte Jackson11 and Lovell v. City of Griffin12, and affirmed that the protection of freedom of expression in India follows the maxim of Madison that the Court transposed from its quotation in Near v. Minnesota13, according to which ‘it is better to leave a few of its noxious branches to their luxuriant growth, than, by pruning them away, to injure the vigour of those yielding the proper fruits’. Likewise, the role of foreign precedents in a majority opinion is confirmed in the decision of His Holiness Kesavananda Bharati Sripadagalvaru which clarifies Parliament’s power to amend the Constitution.
At the same time, looking to the use of foreign precedents in this judgment, Justice S.M. Sikri (as His Lordship then was), dealing with the interpretation of Article 368 of the Constitution, first of all, highlighted that: “No other Constitution in the world is like ours. No other Constitution combines under its wings such diverse peoples, numbering now more than 550 millions [sic], with different languages and religions and in different stages of economic development, into one nation, and no other nation is faced with such vast socio-economic problems. After this premise, however, His Lordship accepts, in order to define what an ‘amendment’ is according to the Indian Constitution, the reasoning of Lord Greene in Bidie v. General Accident, Fire and Life Assurance Corporation14 and that of Justice Holmes in Towne v. Eisner15, which affirm that to understand a word it is necessary to understand the context in which it is inserted.
To strengthen this, James v. Commonwealth of Australia16 is also referred to. We have stated the trend in brief with a purpose. Number of judgments of U.K. Courts, German Supreme Court, European Commission of Human Rights (ECHR), U.S. Supreme Court etc. were cited. However, there is no similarity in approach by these Courts in deciding a particular issue by applying different principles, particularly when it comes to the issues of data protection and privacy.
In this backdrop, it becomes necessary, while referring to these judgments, to keep in mind the ethos, cultural background and vast socio-economic problems of this country and on that basis to accept a particular norm, or for that matter, to formulate a constitutional norm which is relevant in our context. That is the endeavour which is made by us. (iv) Many arguments of the petitioners relate to the working of the system. The petitioners had argued that the architecture of Aadhaar, by its very nature, is probabilistic and, therefore, it may result in exclusion, in many cases. Therefore, rather than extending subsidies, benefits and services to the section of society for which these are meant, it may have the tendency to exclude them from receiving such subsidies, benefits and services.
The respondents, on the other hand, have stated on affidavit that the attempt of the respondents would be to ensure that no individual who is eligible for such benefits etc. is deprived form receiving those benefits, even when in a particular case, it is found that on authentication, his fingerprints or iris are not matching and is resulting into failure. It was clarified that since Aadhaar project is an ongoing project, there may be some glitches in its working and there is a continuous attempt to make improvements in order to ensure that it becomes foolproof over a period of time.
We have eschewed detailed discussion in respect of those arguments, which may not have much relevance when judging the constitutional validity of the Act and the scheme. However, such arguments of exclusion etc. leading to violation of Articles 14 and 21 are dealt with at an appropriate stage. But the argument based on alleged inaccurate claims of savings by the Authority/Union of India in respect of certain programmes, like saving of USD 11 billion per annum due to the Aadhaar project, as well as savings in the implementation of the MGNREGA scheme, LPG subsidy, PDS savings need not detain us for long. Such rebuttals raised by the petitioners may have relevance insofar as working of the Act is concerned. That by itself cannot be a ground to invalidate the statute.
(v) As mentioned above, notwithstanding the passions and emotions evoked on both sides in equal measure, this Court has adopted a lambent approach while dealing with the issues raised, having a posture of calmness coupled with objective examination of the issues on the touchstone of the constitutional provisions. We are in the age of constitutional democracy, that too substantive and liberal democracy. Such a democracy is not based solely on the rule of people through their representatives which is known as “formal democracy”.
It also has other precepts like rule of law, human rights, independence of judiciary, separation of powers, etc. The framers of Indian Constitution duly recognized the aforesaid precepts of liberal and substantive democracy with rule of law as an important and fundamental pillar. At the same time, in the scheme of the Constitution, it is the judiciary which is assigned the role of upholding rule of law and protecting the Constitution and democracy. The essence of rule of law is to preclude arbitrary action. Dicey, who propounded the rule of law, gave distinct meaning to this concept and explained that it was based on three kindered features, which are as follows:
(i) absence of arbitrary powers on the part of authorities;
(ii) equality before law; and
(iii) the Constitution is part of the ordinary law of the land. There are three aspects of the rule of law, which are as follows:
(a) A formal aspect which means making the law rule.
(b) A jurisprudential or doctrinal aspect which is concerned with the minimal condition for the existence of law in society.
(c) A substantive aspect as per which the rule of law is concerned with properly balancing between the individual and society. When we talk of jurisprudential rule of law, it includes certain minimum requirements without which a legal system cannot exist and which distinguished a legal system from an automatic system where the leader imposes his will on everyone else. Professor Lon Fuller has described these requirements collectively as the ‘inner morality of law’. In addition to jurisprudential concept, which is important and an essential condition for the rule of law, the substantive concept of the rule of law is equally important and inseparable norm of the rule of law in real sense. It encompasses the ‘right conception’ of the rule of law propounded by Dworkin.
It means guaranteeing fundamental values of morality, justice, and human rights, with a proper balance between these and the other needs of the society. Justice Aharon Barak, former Chief Justice of Israel, has lucidly explained this facet of rule of law in the following manner: “The rule of law is not merely public order, the rule of law is social justice based on public order. The law exists to ensure proper social life. Social life, however, is not a goal in itself but a means to allow the individual to live in dignity and develop himself. The human being and human rights underlie this substantive perception of the rule of law, with a proper balance among the different rights and between human rights and the proper needs of society.
The substantive rule of law “is the rule of proper law, which balances the needs of society and the individual”. This is the rule of law that strikes a balance between society’s need for political independence, social equality, economic development, and internal order, on the one hand, and the needs of the individual, his personal liberty, and his human dignity on the other. The Judge must protect this rich concept of the rule of law.” The ‘rule of law’, which is a fine sonorous phrase, is dynamic and ever expanding and can be put alongside the brotherhood of man, human rights and human dignity. About the modern rule of law, Professor Garner observed:
“The concept in its modern dress meets a need that has been felt throughout the history of civilization, law is not sufficient in itself and it must serve some purpose. Man is a social animal, but to live in society he has had to fashion for himself and in his own interest the law and other instruments of government, and as a consequence those must to some extent limit his personal liberties. The problem is how to control those instruments of government in accordance with the Rule of Law and in the interest of the governed.” Likewise, the basic spirit of our Constitution is to provide each and every person of the nation equal opportunity to grow as a human being, irrespective of race, caste, religion, community and social status. Granville Austin while analyzing the functioning of Indian Constitution in first 50 years has described three distinguished strands of Indian Constitution:
(i) protecting national unity and integrity,
(ii) establishing the institution and spirit of democracy; and
(iii) fostering social reforms.
The strands are mutually dependent and inextricably intertwined in what he elegantly describes as a ‘seamless web’. And there cannot be social reforms till it is ensured that each and every citizen of this country is able to exploit his/her potentials to the maximum. The Constitution, although drafted by the Constituent Assembly, was meant for the people of India and that is why it is given by the people to themselves as expressed in the opening words “We the People…”. What is the most important gift to the common person given by this Constitution is “fundamental rights” which may be called human rights as well. Speaking for the vision of our founding fathers, in State of Karnataka & Anr. v. Shri Ranganatha Reddy & Anr.17, this Court speaking through Justice Krishna Iyer observed: “The social philosophy of the Constitution shapes creative judicial vision and orientation.
Our nation has, as its dynamic doctrine, economic democracy sans which political democracy is chimerical. We say so because our Constitution, in Parts III and IV and elsewhere, ensouls such a value system, and the debate in this case puts precisely this soul in peril….Our thesis is that the dialectics of social justice should not be missed if the synthesis of Parts III and Part IV is to influence State action and court pronouncements. Constitutional problems cannot be studied in a socio-economic vacuum, since socio-cultural changes are the source of the new values, and sloughing off old legal thought is part of the process the new equity- loaded legality. A judge is a social scientist in his role as constitutional invigilator and fails functionally if he forgets this dimension in his complex duties.”
In Dattatraya Govind Mahajan v. State of Maharashtra18 the spirit of our Constitution was explained thus: “Our Constitution is a tryst with destiny, preamble with lucent solemnity in the words ‘Justice – social, economic and political.’ The three great branches of Government, as creatures of the Constitution, must remember this promise in their fundamental role and forget it at their peril, for to do so will be a betrayal of chose high values and goals which this nation set for itself in its objective Resolution and whose elaborate summation appears in Part IV of the Paramount Parchment.
The history of our country’s struggle for independence was the story of a battle between the forces of socio-economic exploitation and the masses of deprived people of varying degrees and the Constitution sets the new sights of the nation…..Once we grasp the dharma of the Constitution, the new orientation of the karma of adjudication becomes clear. Our founding fathers, aware of our social realities, forged our fighting faith and integrating justice in its social, economic and political aspects. While contemplating the meaning of the Articles of the Organic Law, the Supreme Court shall not disown Social Justice.”
In National Human Rights Commission v. State of Arunachal Pradesh19, the Supreme Court explained it again, as under: “We are a country governed by the Rule of Law. Our Constitution confers certain rights on every human being and certain other rights on citizens. Every person is entitled to equality before the law and equal protection of the laws.” Looking the matter from this angle, when the judiciary is assigned the role of upholding the rule of law, the first function of the judiciary is to protect the democracy as well as the Constitution.
At the same time, second role of the Court, which is equally important, is to bridge the gap between the law and the society. In the process of undertaking this role, a third role, which is of equal significance also springs up. Judiciary is also to ensure that social and economic justice is meted out to the deserving lot by affirmative action of the State. Our attempt has been to strive the balancing of competing Constitutional norms. The complex issues are dealt with keeping in view this role of the Supreme Court as assigned by the Constitution; albeit within the constitutional norms.
Scope of Judicial Review:
73) The aforesaid discussion leads us to pick up and discuss another strand viz. the scope of judicial review in such matters.
74) Judicial review means the Supremacy of law. It is the power of the court to review the actions of the Legislature, the Executive and the Judiciary itself and to scrutinize the validity of any law or action. It has emerged as one of the most effective instruments of protecting and preserving the cherished freedoms in a constitutional democracy and upholding principles such as separation of powers and rule of law. The Judiciary, through judicial review, prevents the decisions of other branches from impinging on the constitutional values. The fundamental nature of the Constitution is that of a limiting document, it curtails the powers of majoritarianism from hijacking the State. The power of review is the shield which is placed in the hands of the most judiciaries of constitutional democracies to enable the protection of the supreme document.
75) In Binoy Viswam v. Union of India & Ors.20, scope of judicial review of legislative Act was described in the following manner:
“76. Under the Constitution, Supreme Court as well as High Courts are vested with the power of judicial review of not only administrative acts of the executive but legislative enactments passed by the legislature as well. This power is given to the High Courts under Article 226 of the Constitution and to the Supreme Court under Article 32 as well as Article 136 of the Constitution. At the same time, the parameters on which the power of judicial review of administrative act is to be undertaken are different from the parameters on which validity of legislative enactment is to be examined. No doubt, in exercises of its power of judicial review of legislative action, the Supreme Court, or for that matter, the High Courts can declare law passed by Parliament or the State Legislature as invalid. However, the power to strike down primary legislation enacted by the Union or the State Legislatures is on limited grounds.
Courts can strike down legislation either on the basis that it falls foul of federal distribution of powers or that it contravenes fundamental rights or other constitutional rights/provisions of the Constitution of India. No doubt, since the Supreme Court and the High Courts are treated as the ultimate arbiter in all matters involving interpretation of the Constitution, it is the courts which have the final say on questions relating to rights and whether such a right is violated or not. The basis of the aforesaid statement lies in Article 13(2) of the Constitution which proscribes the State from making “any law which takes away or abridges the right conferred by Part III”, enshrining fundamental rights. It categorically states that any law made in contravention thereof, to the extent of the contravention, be void.
77. We can also take note of Article 372 of the Constitution at this stage which applies to pre-constitutional laws. Article 372(1) reads as under:
“372. Continuance in force of existing laws and their adaptation.-
(1) Notwithstanding the repeal by this Constitution of the enactments referred to in Article 395 but subject to the other provisions of this Constitution, all the laws in force in the territory of India immediately before the commencement of this Constitution shall continue in force therein until altered or repealed or amended by a competent legislature or other competent authority.”
In the context of judicial review of legislation, this provision gives an indication that all laws enforced prior to the commencement of the Constitution can be tested for compliance with the provisions of the Constitution by courts. Such a power is recognised by this Court in Union of India v. SICOM Ltd. In that judgment, it was also held that since the term “laws”, as per Article 372, includes common law the power of judicial review of legislation, which is a part of common law applicable in India before the Constitution came into force, would continue to vest in the Indian courts.
78. …These contours of the judicial review are spelled out in the clear terms in Rakesh Kohli, and particularly in the following paragraphs: (SCC pp. 321-22 & 325-27, paras 16-17, 26-28 & 30) “16. The statute enacted by Parliament or a State Legislature cannot be declared unconstitutional lightly. The court must be able to hold beyond any iota of doubt that the violation of the constitutional provisions was so glaring that the legislative provision under challenge cannot stand. Sans flagrant violation of the constitutional provisions, the law made by Parliament or a State Legislature is not declared bad.
17. This Court has repeatedly stated that legislative enactment can be struck down by court only on two grounds, namely (i) that the appropriate legislature does not have the competence to make the law, and (ii) that it does not (sic) take away or abridge any of the fundamental rights enumerated in Part III of the Constitution or any other constitutional provisions. In McDowell and Co. while dealing with the challenge to an enactment based on Article 14, this Court stated in para 43 of the Report as follows: (SCC pp. 737-38) ’43. … A law made by Parliament or the legislature can be struck down by courts on two grounds and two grounds alone viz. (1) lack of legislative competence, and (2) violation of any of the fundamental rights guaranteed in Part III of the Constitution or of any other constitutional provision. There is no third ground. … if an enactment is challenged as violative of Article 14, it can be struck down only if it is found that it is violative of the equality clause/equal protection clause enshrined therein. Similarly, if an enactment is challenged as violative of any of the fundamental rights guaranteed by sub-clauses (a) to (g) of Article 19(1), it can be struck down only if it is found not saved by any of the clauses (2) to (6) of Article 19 and so on.
No enactment can be struck down by just saying that it is arbitrary or unreasonable. Some or the other constitutional infirmity has to be found before invalidating an Act. An enactment cannot be struck down on the ground that court thinks it unjustified. Parliament and the legislatures, composed as they are of the representatives of the people, are supposed to know and be aware of the needs of the people and what is good and bad for them. The court cannot sit in judgment over their wisdom.’
xx xx xx
26. In Mohd. Hanif Quareshi, the Constitution Bench further observed that there was always a presumption in favour of constitutionality of an enactment and the burden is upon him, who attacks it, to show that there has been a clear violation of the constitutional principles. It stated in para 15 of the Report as under: (AIR pp. 740-41)
’15. … The courts, it is accepted, must presume that the legislature understands and correctly appreciates the needs of its own people, that its laws are directed to problems made manifest by experience and that its discriminations are based on adequate grounds. It must be borne in mind that the legislature is free to recognise degrees of harm and may confine its restrictions to those cases where the need is deemed to be the clearest and finally that in order to sustain the presumption of constitutionality the court may take into consideration matters of common knowledge, matters of common report, the history of the times and may assume every state of facts which can be conceived existing at the time of legislation.’
27. The above legal position has been reiterated by a Constitution Bench of this Court in Mahant Moti Das v. S.P. Sahi.
28. In Hamdard Dawakhana v. Union of India, inter alia, while referring to the earlier two decisions, namely, Bengal Immunity Co. Ltd. and Mahant Moti Das, it was observed in para 8 of the Report as follows: (Hamdard Dawakhana case, AIR p. 559) ‘8. Therefore, when the constitutionality of an enactment is challenged on the ground of violation of any of the articles in Part III of the Constitution, the ascertainment of its true nature and character becomes necessary i.e. its subject-matter, the area in which it is intended to operate, its purport and intent have to be determined.
In order to do so it is legitimate to take into consideration all the factors such as history of the legislation, the purpose thereof, the surrounding circumstances and conditions, the mischief which it intended to suppress, the remedy for the disease which the legislature resolved to cure and the true reason for the remedy….’ In Hamdard Dawakhana, the Court also followed the statement of law in Mahant Moti Das and the two earlier decisions, namely, Charanjit Lal Chowdhury v. Union of India and State of Bombay v. F.N. Balsara and reiterated the principle that presumption was always in favour of constitutionality of an enactment.
xx xx xx
30. A well-known principle that in the field of taxation, the legislature enjoys a greater latitude for classification, has been noted by this Court in a long line of cases. Some of these decisions are Steelworth Ltd. v. State of Assam [Steelworth Ltd. v. State of Assam, 1962 Supp (2) SCR 589], Gopal Narain v. State of U.P. [Gopal Narain v. State of U.P., AIR 1964 SC 370], Ganga Sugar Corpn. Ltd. v. State of U.P. [Ganga Sugar Corpn. Ltd. v. State of U.P., (1980) 1 SCC 223 : 1980 SCC (Tax) 90], R.K. Garg v. Union of India [R.K. Garg v. Union of India, (1981) 4 SCC 675 : 1982 SCC (Tax) 30] and State of W.B. v. E.I.T.A. India Ltd. [State of W.B. v. E.I.T.A. India Ltd., (2003) 5 SCC 239]”
(emphasis in original)
xx xx xx
83. It is, thus, clear that in exercise of power of judicial review, the Indian courts are invested with powers to strike down primary legislation enacted by Parliament or the State Legislatures. However, while undertaking this exercise of judicial review, the same is to be done at three levels. In the first stage, the Court would examine as to whether impugned provision in a legislation is compatible with the fundamental rights or the constitutional provisions (substantive judicial review) or it falls foul of the federal distribution of powers (procedural judicial review). If it is not found to be so, no further exercise is needed as challenge would fail.
On the other hand, if it is found that legislature lacks competence as the subject legislated was not within the powers assigned in the List in Schedule VII, no further enquiry is needed and such a law is to be declared as ultra vires the Constitution. However, while undertaking substantive judicial review, if it is found that the impugned provision appears to be violative of fundamental rights or other constitutional rights, the Court reaches the second stage of review. At this second phase of enquiry, the Court is supposed to undertake the exercise as to whether the impugned provision can still be saved by reading it down so as to bring it in conformity with the constitutional provisions. If that is not achievable then the enquiry enters the third stage. If the offending portion of the statute is severable, it is severed and the Court strikes down the impugned provision declaring the same as unconstitutional.”
76) In support of the aforesaid proposition that an Act of the Parliament can be invalidated only on the aforesaid two grounds, passages from various judgments were extracted21. The Court also noted the observations from State of A.P. & Ors. v. MCDOWELL & Co. & Ors.22 wherein it was held that apart from the aforesaid two grounds, no third ground is available to validate any piece of legislation. In the process, it was further noted that in Rajbala & Ors. v. State of Haryana & Ors.23 (which followed MCDOWELL & Co. case), the Court held that a legislation cannot be declared unconstitutional on the ground that it is ‘arbitrary’ inasmuch as examining as to whether a particular Act is arbitrary or not implies a value judgment and courts do not examine the wisdom of legislative choices, and, therefore, cannot undertake this exercise.
77) The issue whether law can be declared unconstitutional on the ground of arbitrariness has received the attention of this Court in a Constitution Bench judgment in the case of Shayara Bano v. Union of India & Ors.24. R.F. Nariman and U.U. Lalit, JJ. discredited the ratio of the aforesaid judgments wherein the Court had held that a law cannot be declared unconstitutional on the ground that it is arbitrary. The Judges pointed out the larger Bench judgment in the case of Dr. K.R. Lakshmanan v. State of T.N. & Anr.25 and Maneka Gandhi v. Union of India & Anr.26 where ‘manifest arbitrariness’ is recognised as the third ground on which the legislative Act can be invalidated. Following discussion in this behalf is worthy of note:
“87. The thread of reasonableness runs through the entire fundamental rights chapter. What is manifestly arbitrary is obviously unreasonable and being contrary to the rule of law, would violate Article 14. Further, there is an apparent contradiction in the three-Judge Bench decision in McDowell [State of A.P. v. McDowell and Co., (1996) 3 SCC 709] when it is said that a constitutional challenge can succeed on the ground that a law is “disproportionate, excessive or unreasonable”, yet such challenge would fail on the very ground of the law being “unreasonable, unnecessary or unwarranted”.
The arbitrariness doctrine when applied to legislation obviously would not involve the latter challenge but would only involve a law being disproportionate, excessive or otherwise being manifestly unreasonable. All the aforesaid grounds, therefore, do not seek to differentiate between State action in its various forms, all of which are interdicted if they fall foul of the fundamental rights guaranteed to persons and citizens in Part III of the Constitution. 88. We only need to point out that even after McDowell [State of A.P. v. McDowell and Co., (1996) 3 SCC 709] , this Court has in fact negated statutory law on the ground of it being arbitrary and therefore violative of Article 14 of the Constitution of India. In Malpe Vishwanath Acharya v. State of Maharashtra [Malpe Vishwanath Acharya v. State of Maharashtra, (1998) 2 SCC 1] , this Court held that after passage of time, a law can become arbitrary, and, therefore, the freezing of rents at a 1940 market value under the Bombay Rent Act would be arbitrary and violative of Article 14 of the Constitution of India (see paras 8 to 15 and 31). xx xx xx
99. However, in State of Bihar v. Bihar Distillery Ltd. [State of Bihar v. Bihar Distillery Ltd., (1997) 2 SCC 453] , SCC at para 22, in State of M.P. v. Rakesh Kohli [State of M.P. v. Rakesh Kohli, (2012) 6 SCC 312 : (2012) 3 SCC (Civ) 481], SCC at paras 17 to 19, in Rajbala v. State of Haryana [Rajbala v. State of Haryana, (2016) 2 SCC 445], SCC at paras 53 to 65 and in Binoy Viswam v. Union of India [Binoy Viswam v. Union of India, (2017) 7 SCC 59], SCC at paras 80 to 82, McDowell [State of A.P. v. McDowell and Co., (1996) 3 SCC 709] was read as being an absolute bar to the use of “arbitrariness” as a tool to strike down legislation under Article 14. As has been noted by us earlier in this judgment, McDowell [State of A.P. v. McDowell and Co., (1996) 3 SCC 709] itself is per incuriam, not having noticed several judgments of Benches of equal or higher strength, its reasoning even otherwise being flawed. The judgments, following McDowell [State of A.P. v. McDowell and Co., (1996) 3 SCC 709] are, therefore, no longer good law.”
78) The historical development of the doctrine of arbitrariness has been noticed by the said Judges in Shayara Bano in detail. It would be suffice to reproduce paragraphs 67 to 69 of the said judgment as the discussion in these paras provide a sufficient guide as to how a doctrine of arbitrariness is to be applied while adjudging the constitutional validity of a legislation.
“67. We now come to the development of the doctrine of arbitrariness and its application to State action as a distinct doctrine on which State action may be struck down as being violative of the rule of law contained in Article 14. In a significant passage, Bhagwati, J., in E.P. Royappa v. State of T.N. stated: (SCC p. 38, para 85) “85. The last two grounds of challenge may be taken up together for consideration. Though we have formulated the third ground of challenge as a distinct and separate ground, it is really in substance and effect merely an aspect of the second ground based on violation of Articles 14 and 16. Article 16 embodies the fundamental guarantee that there shall be equality of opportunity for all citizens in matters relating to employment or appointment to any office under the State.
Though enacted as a distinct and independent fundamental right because of its great importance as a principle ensuring equality of opportunity in public employment which is so vital to the building up of the new classless egalitarian society envisaged in the Constitution, Article 16 is only an instance of the application of the concept of equality enshrined in Article 14. In other words, Article 14 is the genus while Article 16 is a species. Article 16 gives effect to the doctrine of equality in all matters relating to public employment. The basic principle which, therefore, informs both Articles 14 and 16 is equality and inhibition against discrimination. Now, what is the content and reach of this great equalising principle?
It is a founding faith, to use the words of Bose, J., “a way of life”, and it must not be subjected to a narrow pedantic or lexicographic approach. We cannot countenance any attempt to truncate its allembracing scope and meaning, for to do so would be to violate its activist magnitude. Equality is a dynamic concept with many aspects and dimensions and it cannot be “cribbed, cabined and confined” within traditional and doctrinaire limits. From a positivistic point of view, equality is antithetic to arbitrariness. In fact equality and arbitrariness are sworn enemies; one belongs to the rule of law in a republic while the other, to the whim and caprice of an absolute monarch. Where an act is arbitrary, it is implicit in it that it is unequal both according to political logic and constitutional law and is therefore violative of Article 14, and if it effects any matter relating to public employment, it is also violative of Article 16. Articles 14 and 16 strike at arbitrariness in State action and ensure fairness and equality of treatment.
They require that State action must be based on valid relevant principles applicable alike to all similarly situate and it must not be guided by any extraneous or irrelevant considerations because that would be denial of equality. Where the operative reason for State action, as distinguished from motive inducing from the antechamber of the mind, is not legitimate and relevant but is extraneous and outside the area of permissible considerations, it would amount to mala fide exercise of power and that is hit by Articles 14 and 16. Mala fide exercise of power and arbitrariness are different lethal radiations emanating from the same vice: in fact the latter comprehends the former. Both are inhibited by Articles 14 and 16.”
(emphasis supplied)
68. This was further fleshed out in Maneka Gandhi v. Union of India, where, after stating that various fundamental rights must be read together and must overlap and fertilise each other, Bhagwati, J., further amplified this doctrine as follows: (SCC pp. 283-84, para 7) “The nature and requirement of the procedure under Article 21 7. Now, the question immediately arises as to what is the requirement of Article 14: what is the content and reach of the great equalising principle enunciated in this article? There can be no doubt that it is a founding faith of the Constitution. It is indeed the pillar on which rests securely the foundation of our democratic republic. And, therefore, it must not be subjected to a narrow, pedantic or lexicographic approach.
No attempt should be made to truncate its all-embracing scope and meaning, for to do so would be to violate its activist magnitude. Equality is a dynamic concept with many aspects and dimensions and it cannot be imprisoned within traditional and doctrinaire limits. We must reiterate here what was pointed out by the majority in E.P. Royappa v. State of T.N. , namely, that: (SCC p. 38, para 85) ’85. … From a positivistic point of view, equality is antithetic to arbitrariness. In fact equality and arbitrariness are sworn enemies; one belongs to the rule of law in a republic, while the other, to the whim and caprice of an absolute monarch. Where an act is arbitrary, it is implicit in it that it is unequal both according to political logic and constitutional law and is therefore violative of Article 14….’ Article 14 strikes at arbitrariness in State action and ensures fairness and equality of treatment. The principle of reasonableness, which legally as well as philosophically, is an essential element of equality or non-arbitrariness pervades Article 14 like a brooding omnipresence and the procedure contemplated by Article 21 must answer the test of reasonableness in order to be in conformity with Article 14. It must be “right and just and fair” and not arbitrary, fanciful or oppressive; otherwise, it would be no procedure at all and the requirement of Article 21 would not be satisfied.”
(emphasis supplied)
69. This was further clarified in A.L. Kalra v. Project and Equipment Corpn., following Royappa and holding that arbitrariness is a doctrine distinct from discrimination. It was held: (A.L. Kalra case, SCC p. 328, para 19)
“19. … It thus appears well settled that Article 14 strikes at arbitrariness in executive/administrative action because any action that is arbitrary must necessarily involve the negation of equality. One need not confine the denial of equality to a comparative evaluation between two persons to arrive at a conclusion of discriminatory treatment. An action per se arbitrary itself denies equal of (sic) protection by law. The Constitution Bench pertinently observed in Ajay Hasia case and put the matter beyond controversy when it said: (SCC p. 741, para 16) ’16. … Wherever therefore, there is arbitrariness in State action whether it be of the legislature or of the executive or of an “authority” under Article 12, Article 14 immediately springs into action and strikes down such State action.’
This view was further elaborated and affirmed in D.S. Nakara v. Union of India . In Maneka Gandhi v. Union of India it was observed that Article 14 strikes at arbitrariness in State action and ensures fairness and equality of treatment. It is thus too late in the day to contend that an executive action shown to be arbitrary is not either judicially reviewable or within the reach of Article 14.” The same view was reiterated in Babita Prasad v. State of Bihar , SCC at p. 285, para 31.” This doctrine is, thus, treated as a facet of both Articles 14 and 21 of the Constitution.
79) We would like to record that we have proceeded on the premise that manifest arbitrariness also furnishes a ground on the basis on which a legislative enactment can be judicially reviewed. In the process, even the constitutional validity of Section 139AA of the Income Tax Act, 1961 is given a fresh look on the touchstone of this norm.
Explaining the doctrine/principles on which the cases are to be decided:
80) Our discussion up to this stage, which gives a glimpse of the attack to the Aadhaar scheme and the Aadhaar Act, spearheaded by the petitioners, would reveal that in the forefront is the right to privacy and that forms the main pillar on which the edifice of arguments is substantially constructed27. Inbuilt in this right to privacy is the right to live with dignity, which is a postulate of right to privacy. In the process, discussion leads to the issue of proportionality, viz. whether measures taken under the Aadhaar Act satisfy the doctrine of proportionality. We would, therefore, be well advised to explain these concepts, so that their application to the fact situation is undertaken with clear and stable norms in mind.
Contours of Right to Privacy:
81) It stands established, with conclusive determination of the nine Judge Bench judgment of this Court in K.S. Puttaswamy that right to privacy is a fundamental right. The majority judgment authored by Dr. D.Y. Chandrachud, J. (on behalf of three other Judges) and five concurring judgments of other five Judges have declared, in no uncertain terms and most authoritatively, right to privacy to be a fundamental right. This judgment also discusses in detail the scope and ambit of right to privacy. The relevant passages in this behalf have been reproduced above while taking note of the submissions of the learned counsel for the petitioners as well as respondents. One interesting phenomenon that is discerned from the respective submissions on either side is that both sides have placed strong reliance on different passages from this very judgment to support their respective stances. A close reading of this judgment brings about the following features:
(i) Privacy has always been a natural right: The correct position in this behalf has been established by a number of judgments starting from Gobind v. State of M.P.28 Various opinions conclude that:
(a) privacy is a concomitant of the right of the individual to exercise control over his or her personality.
(b) Privacy is the necessary condition precedent to the enjoyment of any of the guarantees in Part III.
(c) The fundamental right to privacy would cover at least three aspects –
(i) intrusion with an individual’s physical body,
(ii) informational privacy, and
(iii) privacy of choice.
(d) One aspect of privacy is the right to control the dissemination of personal information. And that every individual should have a right to be able to control exercise over his/her own life and image as portrayed in the world and to control commercial use of his/her identity. Following passages from different opinions reflect the aforesaid proposition:
Dr. D.Y. Chandrachud, J.:
42. Privacy is a concomitant of the right of the individual to exercise control over his or her personality. It finds an origin in the notion that there are certain rights which are natural to or inherent in a human being. Natural rights are inalienable because they are inseparable from the human personality. The human element in life is impossible to conceive without the existence of natural rights. In 1690, John Lockehad in his Second Treatise of Government observed that the lives, liberties and estates of individuals are as a matter of fundamental natural law, a private preserve.
The idea of a private preserve was to create barriers from outside interference. In 1765, William Blackstone in his Commentaries on the Laws of England spoke of a “natural liberty”. There were, in his view, absolute rights which were vested in the individual by the immutable laws of nature. These absolute rights were divided into rights of personal security, personal liberty and property. The right of personal security involved a legal and uninterrupted enjoyment of life, limbs, body, health and reputation by an individual.
xx xx xx
46. Natural rights are not bestowed by the State. They inhere in human beings because they are human. They exist equally in the individual irrespective of class or strata, gender or orientation.
xx xx xx
318. Life and personal liberty are inalienable rights. These are rights which are inseparable from a dignified human existence. The dignity of the individual, equality between human beings and the quest for liberty are the foundational pillars of the Indian Constitution.
S.A. Bobde, J. :
415. Therefore, privacy is the necessary condition precedent to the enjoyment of any of the guarantees in Part III. As a result, when it is claimed by rights bearers before constitutional courts, a right to privacy may be situated not only in Article 21, but also simultaneously in any of the other guarantees in Part III. In the current state of things, Articles 19(1), 20(3), 25, 28 and 29 are all rights helped up and made meaningful by the exercise of privacy. This is not an exhaustive list. Future developments in technology and social ordering may well reveal that there are yet more constitutional sites in which a privacy right inheres that are not at present evident to us.
R.F. Nariman, J. :
In the Indian context, a fundamental right to privacy would cover at least the following three aspects:
Privacy that involves the person i.e. when there is some invasion by the State of a person’s rights relatable to his physical body, such as the right to move freely;
Informational privacy which does not deal with a person’s body but deals with a person’s mind, and therefore recognises that an individual may have control over the dissemination of material that is personal to him. Unauthorised use of such information may, therefore lead to infringement of this right; and
The privacy of choice, which protects an individual’s autonomy over fundamental personal choices.
For instance, we can ground physical privacy or privacy relating to the body in Articles 19(1)(d) and (e) read with Article 21; ground personal information privacy under Article 21; and the privacy of choice in Articles 19(1)(a) to (c), 20(3), 21 and 25. The argument based on “privacy” being a vague and nebulous concept need not, therefore, detain us.
xx xx xx
532. The learned counsel for the petitioners also referred to another important aspect of the right to privacy. According to the learned counsel for the petitioner this right is a natural law right which is inalienable. Indeed, the reference order itself, in para 12, refers to this aspect of the fundamental right contained. It was, therefore, argued before us that given the international conventions referred to hereinabove and the fact that this right inheres in every individual by virtue of his being a human being, such right is not conferred by the Constitution but is only recognised and given the status of being fundamental. There is no doubt that the petitioners are correct in this submission. However, one important roadblock in the way needs to be got over.
533. In ADM, Jabalpur v. Shivakant Shukla, a Constitution Bench of this Court arrived at the conclusion (by majority) that Article 21 is the sole repository of all rights to life and personal liberty, and, when suspended, takes away those rights altogether. A remarkable dissent was that of Khanna, J. [ Khanna, J. was in line to be Chief Justice of India but was superseded because of this dissenting judgment. Nani Palkhivala in an article written on this great Judge’s supersession ended with a poignant sentence, “To the stature of such a man, the Chief Justiceship of India can add nothing.” Seervai, in his monumental treatise Constitutional Law of India had this to say:”53. If in this Appendix the dissenting judgment of Khanna, J. has not been considered in detail, it is not for lack of admiration for the judgment, or the courage which he showed in delivering it regardless of the cost and consequences to himself.
It cost him the Chief Justiceship of India, but it gained for him universal esteem not only for his courage but also for his inflexible judicial independence. If his judgment is not considered in detail it is because under the theory of precedents which we have adopted, a dissenting judgment, however valuable, does not lay down the law and the object of a critical examination of the majority judgments in this Appendix was to show that those judgments are untenable in law, productive of grave public mischief and ought to be overruled at the earliest opportunity.
The conclusion which Justice Khanna has reached on the effect of the suspension of Article 21 is correct. His reminder that the rule of law did not merely mean giving effect to an enacted law was timely, and was reinforced by his reference to the mass murders of millions of Jews in Nazi concentration camps under an enacted law. However, the legal analysis in this Chapter confirms his conclusion though on different grounds from those which he has given.” (at Appendix p. 2229).] The learned Judge held: (SCC pp. 747 & 751, paras 525 & 531) “525. The effect of the suspension of the right to move any court for the enforcement of the right conferred by Article 21, in my opinion, is that when a petition is filed in a court, the court would have to proceed upon the basis that no reliance can be placed upon that article for obtaining relief from the court during the period of emergency.
Question then arises as to whether the rule that no one shall be deprived of his life or personal liberty without the authority of law still survives during the period of emergency despite the Presidential Order suspending the right to move any court for the enforcement of the right contained in Article 21. The answer to this question is linked with the answer to the question as to whether Article 21 is the sole repository of the right to life and personal liberty. After giving the matter my earnest consideration, I am of the opinion that Article 21 cannot be considered to be the sole repository of the right to life and personal liberty.
The right to life and personal liberty is the most precious right of human beings in civilised societies governed by the rule of law. Many modern Constitutions incorporate certain fundamental rights, including the one relating to personal freedom. According to Blackstone, the absolute rights of Englishmen were the rights of personal security, personal liberty and private property. The American Declaration of Independence (1776) states that all men are created equal, and among their inalienable rights are life, liberty, and the pursuit of happiness.
The Second Amendment to the US Constitution refers inter alia to security of person, while the Fifth Amendment prohibits inter alia deprivation of life and liberty without due process, of law. The different Declarations of Human Rights and fundamental freedoms have all laid stress upon the sanctity of life and liberty. They have also given expression in varying words to the principle that no one shall be derived of his life or liberty without the authority of law. The International Commission of Jurists, which is affiliated to UNESCO, has been attempting with, considerable success to give material content to “the rule of law”, an expression used in the Universal Declaration of Human Rights.
One of its most notable achievements was the Declaration of Delhi, 1959. This resulted from a Congress held in New Delhi attended by jurists from more than 50 countries, and was based on a questionnaire circulated to 75,000 lawyers. “Respect for the supreme value of human personality” was stated to be the basis of all law (see p. 21 of the Constitutional and Administrative Law by O. Hood Phillips, 3rd Edn.).
xx xx xx 531. I am unable to subscribe to the view that when right to enforce the right under Article 21 is suspended, the result would be that there would be no remedy against deprivation of a person’s life or liberty by the State even though such deprivation is without the authority of law or even in flagrant violation of the provisions of law. The right not to be deprived of one’s life or liberty without the authority of law was not the creation of the Constitution. Such right existed before the Constitution came into force.
The fact that the Framers of the Constitution made an aspect of such right a part of the fundamental rights did not have the effect of exterminating the independent identity of such right and of making Article 21 to be the sole repository of that right. Its real effect was to ensure that a law under which a person can be deprived of his life or personal liberty should prescribe a procedure for such deprivation or, according to the dictum laid down by Mukherjea, J. in Gopalan case [A.K. Gopalan v. State of Madras, AIR 1950 SC 27 : 1950 SCR 88] , such law should be a valid law not violative of fundamental rights guaranteed by Part III of the Constitution. Recognition as fundamental right of one aspect of the preconstitutional right cannot have the effect of making things less favourable so far as the sanctity of life and personal liberty is concerned compared to the position if an aspect of such right had not been recognised as fundamental right because of the vulnerability of fundamental rights accruing from Article 359.
I am also unable to agree that in view of the Presidential Order in the matter of sanctity of life and liberty, things would be worse off compared to the state of law as it existed before the coming into force of the Constitution.”
(emphasis in original)
S.K. Kaul, J.:
574. I have had the benefit of reading the exhaustive and erudite opinions of Rohinton F. Nariman and Dr D.Y. Chandrachud, JJ. The conclusion is the same, answering the reference that privacy is not just a common law right, but a fundamental right falling in Part III of the Constitution of India. I agree with this conclusion as privacy is a primal, natural right which is inherent to an individual. However, I am tempted to set out my perspective on the issue of privacy as a right, which to my mind, is an important core of any individual existence.
xx xx xx
620. I had earlier adverted to an aspect of privacy – the right to control dissemination of personal information. The boundaries that people establish from others in society are not only physical but also informational. There are different kinds of boundaries in respect to different relations. Privacy assists in preventing awkward social situations and reducing social frictions. Most of the information about individuals can fall under the phrase “none of your business”. On information being shared voluntarily, the same may be said to be in confidence and any breach of confidentiality is a breach of the trust.
This is more so in the professional relationships such as with doctors and lawyers which requires an element of candour in disclosure of information. An individual has the right to control one’s life while submitting personal data for various facilities and services. It is but essential that the individual knows as to what the data is being used for with the ability to correct and amend it. The hallmark of freedom in a democracy is having the autonomy and control over our lives which becomes impossible, if important decisions are made in secret without our awareness or participation. [ Daniel Solove,
“10 Reasons Why Privacy Matters” published on 20-1-2014 “https://www.teachprivacy.com/10-reasonsprivacy- matters/”.]
xx xx xx
625. Every individual should have a right to be able to exercise control over his/her own life and image as portrayed to the world and to control commercial use of his/her identity. This also means that an individual may be permitted to prevent others from using his image, name and other aspects of his/her personal life and identity for commercial purposes without his/her consent. [ The Second Circuit’s decision in Haelan Laboratories Inc. v. Topps Chewing Gum Inc., 202 F 2d 866 (2d Cir 1953) penned by Jerome Frank, J. defined the right to publicity as “the right to grant the exclusive privilege of publishing his picture”.]”
xx xx xx
646. If the individual permits someone to enter the house it does not mean that others can enter the house. The only check and balance is that it should not harm the other individual or affect his or her rights. This applies both to the physical form and to technology. In an era where there are wide, varied, social and cultural norms and more so in a country like ours which prides itself on its diversity, privacy is one of the most important rights to be protected both against State and non-State actors and be recognised as a fundamental right. How it thereafter works out in its interplay with other fundamental rights and when such restrictions would become necessary would depend on the factual matrix of each case.
That it may give rise to more litigation can hardly be the reason not to recognise this important, natural, primordial right as a fundamental right.”
(ii) The sanctity of privacy lies in its functional relationship with dignity: Privacy ensures that a human being can lead a life of dignity by securing the inner recesses of the human personality from unwanted intrusions. While the legitimate expectation of privacy may vary from intimate zone to the private zone and from the private to the public arena, it is important to underscore that privacy is not lost or surrendered merely because the individual is in a public place. Further, privacy is a postulate of dignity itself. Also, privacy concerns arise when the State seeks to intrude into the body and the mind of the citizen. This aspect is discussed in the following manner:
Dr. D.Y. Chandrachud, J. :
127. The submission that recognising the right to privacy is an exercise which would require a constitutional amendment and cannot be a matter of judicial interpretation is not an acceptable doctrinal position. The argument assumes that the right to privacy is independent of the liberties guaranteed by Part III of the Constitution. There lies the error. The right to privacy is an element of human dignity. The sanctity of privacy lies in its functional relationship with dignity. Privacy ensures that a human being can lead a life of dignity by securing the inner recesses of the human personality from unwanted intrusion. Privacy recognises the autonomy of the individual and the right of every person to make essential choices which affect the course of life.
In doing so privacy recognises that living a life of dignity is essential for a human being to fulfill the liberties and freedoms which are the cornerstone of the Constitution. To recognise the value of privacy as a constitutional entitlement and interest is not to fashion a new fundamental right by a process of amendment through judicial fiat. Neither are the Judges nor is the process of judicial review entrusted with the constitutional responsibility to amend the Constitution. But judicial review certainly has the task before it of determining the nature and extent of the freedoms available to each person under the fabric of those constitutional guarantees which are protected. Courts have traditionally discharged that function and in the context of Article 21 itself, as we have already noted, a panoply of protections governing different facets of a dignified existence has been held to fall within the protection of Article 21.
xx xx xx
297. What, then, does privacy postulate? Privacy postulates the reservation of a private space for the individual, described as the right to be let alone. The concept is founded on the autonomy of the individual. The ability of an individual to make choices lies at the core of the human personality. The notion of privacy enables the individual to assert and control the human element which is inseparable from the personality of the individual. The inviolable nature of the human personality is manifested in the ability to make decisions on matters intimate to human life. The autonomy of the individual is associated over matters which can be kept private. These are concerns over which there is a legitimate expectation of privacy. The body and the mind are inseparable elements of the human personality.
The integrity of the body and the sanctity of the mind can exist on the foundation that each individual possesses an inalienable ability and right to preserve a private space in which the human personality can develop. Without the ability to make choices, the inviolability of the personality would be in doubt. Recognising a zone of privacy is but an acknowledgment that each individual must be entitled to chart and pursue the course of development of personality. Hence privacy is a postulate of human dignity itself. Thoughts and behavioural patterns which are intimate to an individual are entitled to a zone of privacy where one is free of social expectations. In that zone of privacy, an individual is not judged by others. Privacy enables each individual to take crucial decisions which find expression in the human personality.
It enables individuals to preserve their beliefs, thoughts, expressions, ideas, ideologies, preferences and choices against societal demands of homogeneity. Privacy is an intrinsic recognition of heterogeneity, of the right of the individual to be different and to stand against the tide of conformity in creating a zone of solitude. Privacy protects the individual from the searching glare of publicity in matters which are personal to his or her life. Privacy attaches to the person and not to the place where it is associated. Privacy constitutes the foundation of all liberty because it is in privacy that the individual can decide how liberty is best exercised. Individual dignity and privacy are inextricably linked in a pattern woven out of a thread of diversity into the fabric of a plural culture.
xx xx xx
322. Privacy is the constitutional core of human dignity. Privacy has both a normative and descriptive function. At a normative level privacy subserves those eternal values upon which the guarantees of life, liberty and freedom are founded. At a descriptive level, privacy postulates a bundle of entitlements and interests which lie at the foundation of ordered liberty.
323. Privacy includes at its core the preservation of personal intimacies, the sanctity of family life, marriage, procreation, the home and sexual orientation. Privacy also connotes a right to be left alone. Privacy safeguards individual autonomy and recognises the ability of the individual to control vital aspects of his or her life. Personal choices governing a way of life are intrinsic to privacy. Privacy protects heterogeneity and recognises the plurality and diversity of our culture. While the legitimate expectation of privacy may vary from the intimate zone to the private zone and from the private to the public arenas, it is important to underscore that privacy is not lost or surrendered merely because the individual is in a public place. Privacy attaches to the person since it is an essential facet of the dignity of the human being.
S.A. Bobde, J. :
407. Undoubtedly, privacy exists, as the foregoing demonstrates, as a verifiable fact in all civilised societies. But privacy does not stop at being merely a descriptive claim. It also embodies a normative one. The normative case for privacy is intuitively simple. Nature has clothed man, amongst other things, with dignity and liberty so that he may be free to do what he will consistent with the freedom of another and to develop his faculties to the fullest measure necessary to live in happiness and peace. The Constitution, through its Part III, enumerates many of these freedoms and their corresponding rights as fundamental rights. Privacy is an essential condition for the exercise of most of these freedoms. Ex facie, every right which is integral to the constitutional rights to dignity, life, personal liberty and freedom, as indeed the right to privacy is, must itself be regarded as a fundamental right.
408. Though he did not use the name of “privacy”, it is clear that it is what J.S. Mill took to be indispensable to the existence of the general reservoir of liberty that democracies are expected to reserve to their citizens. In the introduction to his seminal On Liberty (1859), he characterised freedom in the following way:
“This, then, is the appropriate region of human liberty. It comprises, first, the inward domain of consciousness; demanding liberty of conscience, in the most comprehensive sense; liberty of thought and feeling; absolute freedom of opinion and sentiment on all subjects, practical or speculative, scientific, moral, or theological. The liberty of expressing and publishing opinions may seem to fall under a different principle, since it belongs to that part of the conduct of an individual which concerns other people; but, being almost of as much importance as the liberty of thought itself, and resting in great part on the same reasons, is practically inseparable from it. Secondly, the principle requires liberty of tastes and pursuits; of framing the plan of our life to suit our own character; of doing as we like, subject to such consequences as may follow: without impediment from our fellow creatures, so long as what we do does not harm them, even though they should think our conduct foolish, perverse, or wrong.
Thirdly, from this liberty of each individual, follows the liberty, within the same limits, of combination among individuals; freedom to unite, for any purpose not involving harm to others: the persons combining being supposed to be of full age, and not forced or deceived. No society in which these liberties are not, on the whole, respected, is free, whatever may be its form of Government; and none is completely free in which they do not exist absolute and unqualified.
The only freedom which deserves the name, is that of pursuing our own good in our own way, so long as we do not attempt to deprive others of theirs, or impede their efforts to obtain it. Each is the proper guardian of his own health, whether bodily, or mental and spiritual. Mankind are greater gainers by suffering each other to live as seems good to themselves, than by compelling each to live as seems good to the rest. Though this doctrine is anything but new, and, to some persons, may have the air of a truism, there is no doctrine which stands more directly opposed to the general tendency of existing opinion and practice. Society has expended fully as much effort in the attempt (according to its lights) to compel people to conform to its notions of personal, as of social excellence.” [John Stuart Mill, On Liberty and Other Essays (Stefan Collini Edition, 1989) (1859)]
(emphasis supplied)
409. The first and natural home for a right to privacy is in Article 21 at the very heart of “personal liberty” and life itself. Liberty and privacy are integrally connected in a way that privacy is often the basic condition necessary for exercise of the right of personal liberty. There are innumerable activities which are virtually incapable of being performed at all and in many cases with dignity unless an individual is left alone or is otherwise empowered to ensure his or her privacy. Birth and death are events when privacy is required for ensuring dignity amongst all civilised people. Privacy is thus one of those rights “instrumentally required if one is to enjoy” [ Laurence H. Tribe and Michael C. Dorf, “Levels of Generality in the Definition of Rights”, 57 U CHI L REV 1057 (1990) at p. 1068.] rights specified and enumerated in the constitutional text.
410. This Court has endorsed the view that “life” must mean “something more than mere animal existence” [Munn v. Illinois, 1876 SCC OnLine US SC 4 : 24 L Ed 77 : 94 US 113 (1877) (Per Field, J.) as cited in Kharak Singh, (1964) 1 SCR 332 at pp. 347-48] on a number of occasions, beginning with the Constitution Bench in Sunil Batra (1) v. Delhi Admn. [Sunil Batra v. Delhi Admn., (1978) 4 SCC 494 : 1979 SCC (Cri) 155] Sunil Batra [Sunil Batra v. Delhi Admn., (1978) 4 SCC 494 : 1979 SCC (Cri) 155] connected this view of Article 21 to the constitutional value of dignity. In numerous cases, including Francis Coralie Mullin v. UT of Delhi [Francis Coralie Mullin v. UT of Delhi, (1981) 1 SCC 608 : 1981 SCC (Cri) 212] , this Court has viewed liberty as closely linked to dignity. Their relationship to the effect of taking into the protection of “life” the protection of “faculties of thinking and feeling”, and of temporary and permanent impairments to those faculties. In Francis Coralie Mullin[Francis Coralie Mullin v. UT of Delhi, (1981) 1 SCC 608 : 1981 SCC (Cri) 212] , Bhagwati, J. opined as follows: (SCC p. 618, para 7) “7. Now obviously, the right to life enshrined in Article 21 cannot be restricted to mere animal existence. It means something much more than just physical survival. In Kharak Singh v. State of U.P. [Kharak Singh v. State of U.P., AIR 1963 SC 1295 : (1963) 2 Cri LJ 329 : (1964) 1 SCR 332], Subba Rao, J. quoted with approval the following passage from the judgment of Field, J. in Munn v. Illinois [Munn v. Illinois, 1876 SCC OnLine US SC 4 : 24 L Ed 77 : 94 US 113 (1877)] to emphasise the quality of life covered by Article 21: (Kharak Singh case [Kharak Singh v. State of U.P., AIR 1963 SC 1295 : (1963) 2 Cri LJ 329 : (1964) 1 SCR 332] , AIR p. 1301, para 15) 15. …
“By the term “life” as here used something more is meant than mere animal existence. The inhibition against its deprivation extends to all those limbs and faculties by which life is enjoyed. The provision equally prohibits the mutilation of the body or amputation of an arm or leg or the putting out of an eye or the destruction of any other organ of the body through which the soul communicates with the outer world.” ‘ and this passage was again accepted as laying down the correct law by the Constitution Bench of this Court in the first Sunil Batra case [Sunil Batra v. Delhi Admn., (1978) 4 SCC 494 : 1979 SCC (Cri) 155].
Every limb or faculty through which life is enjoyed is thus protected by Article 21 and a fortiori, this would include the faculties of thinking and feeling. Now deprivation which is inhibited by Article 21 may be total or partial, neither any limb or faculty can be totally destroyed nor can it be partially damaged. Moreover it is every kind of deprivation that is hit by Article 21, whether such deprivation be permanent or temporary and, furthermore, deprivation is not an act which is complete once and for all: it is a continuing act and so long as it lasts, it must be in accordance with procedure established by law. It is therefore clear that any act which damages or injures or interferes with the use of, any limb or faculty of a person, either permanently or even temporarily, would be within the inhibition of Article 21.”
(emphasis supplied)
Privacy is, therefore, necessary in both its mental and physical aspects as an enabler of guaranteed freedoms. 411. It is difficult to see how dignity-whose constitutional significance is acknowledged both by the Preamble and by this Court in its exposition of Article 21, among other rights -can be assured to the individual without privacy. Both dignity and privacy are intimately intertwined and are natural conditions for the birth and death of individuals, and for many significant events in life between these events. Necessarily, then, the right to privacy is an integral part of both “life” and “personal liberty” under Article 21, and is intended to enable the rights bearer to develop her potential to the fullest extent made possible only in consonance with the constitutional values expressed in the Preamble as well as across Part III.
R.F. Nariman, J :
But most important of all is the cardinal value of fraternity which assures the dignity of the individual. [ In 1834, Jacques-Charles Dupont de l’Eure associated the three terms liberty, equality and fraternity together in the Revue Républicaine, which he edited, as follows:”Any man aspires to liberty, to equality, but he cannot achieve it without the assistance of other men, without fraternity.”Many of our decisions recognise human dignity as being an essential part of the fundamental rights chapter. For example, see Prem Shankar Shukla v. Delhi Admn., (1980) 3 SCC 526 at para 21, Francis Coralie Mullin v. UT of Delhi, (1981) 1 SCC 608 at paras 6, 7 and 8, Bandhua Mukti Morcha v. Union of India, (1984) 3 SCC 161 at para 10, Maharashtra University of Health Sciences v. Satchikitsa Prasarak Mandal, (2010) 3 SCC 786 at para 37, Shabnam v. Union of India, (2015) 6 SCC 702 at paras 12.4 and 14 and Jeeja Ghosh v. Union of India, (2016) 7 SCC 761 at para 37.] The dignity of the individual encompasses the right of the individual to develop to the full extent of his potential. And this development can only be if an individual has autonomy over fundamental personal choices and control over dissemination of personal information which may be infringed through an unauthorised use of such information.
It is clear that Article 21, more than any of the other articles in the fundamental rights chapter, reflects each of these constitutional values in full, and is to be read in consonance with these values and with the international covenants that we have referred to. In the ultimate analysis, the fundamental right to privacy, which has so many developing facets, can only be developed on a case-to-case basis. Depending upon the particular facet that is relied upon, either Article 21 by itself or in conjunction with other fundamental rights would get attracted.
S.K. Kaul, J. :
618. Rohinton F. Nariman, and Dr D.Y. Chandrachud, JJ., have emphasised the importance of the protection of privacy to ensure protection of liberty and dignity. I agree with them and seek to refer to some legal observations in this regard:
618.1. In Robertson and Nicol on Media Law [ Geoffrey Robertson, QC and Andrew Nicol, QC, Media Law, 5th Edn., p. 265.] it was observed: “Individuals have a psychological need to preserve an intrusion-free zone for their personality and family and suffer anguish and stress when that zone is violated. Democratic societies must protect privacy as part of their facilitation of individual freedom, and offer some legal support for the individual choice as to what aspects of intimate personal life the citizen is prepared to share with others. This freedom in other words springs from the same source as freedom of expression: a liberty that enhances individual life in a democratic community.”
618.2. Lord Nicholls and Lord Hoffmann in their opinion in Naomi Campbell case[Campbell v. MGN Ltd., (2004) 2 AC 457 : (2004) 2 WLR 1232 : (2004) UKHL 22 (HL)] recognised the importance of the protection of privacy. Lord Hoffman opined as under: (AC p. 472 H & 473 A-D, paras 50-51)
“50. What human rights law has done is to identify private information as something worth protecting as an aspect of human autonomy and dignity. And this recognition has raised inescapably the question of why it should be worth protecting against the state but not against a private person. There may of course be justifications for the publication of private information by private persons which would not be available to the state – I have particularly in mind the position of the media, to which I shall return in a moment – but I can see no logical ground for saying that a person should have less protection against a private individual than he would have against the state for the publication of personal information for which there is no justification. Nor, it appears, have any of the other Judges who have considered the matter.
51. The result of these developments has been a shift in the centre of gravity of the action for breach of confidence when it is used as a remedy for the unjustified publication of personal information. … Instead of the cause of action being based upon the duty of good faith applicable to confidential personal information and trade secrets alike, it focuses upon the protection of human autonomy and dignity – the right to control the dissemination of information about one’s private life and the right to the esteem and respect of other people.”
618.3. Lord Nicholls opined as under: (Naomi Campbell case [Campbell v. MGN Ltd., (2004) 2 AC 457 : (2004) 2 WLR 1232 : (2004) UKHL 22 (HL)] , AC p. 464 D-F, para 12)
“12. The present case concerns one aspect of invasion of privacy: wrongful disclosure of private information. The case involves the familiar competition between freedom of expression and respect for an individual’s privacy. Both are vitally important rights. Neither has precedence over the other. The importance of freedom of expression has been stressed often and eloquently, the importance of privacy less so. But it, too, lies at the heart of liberty in a modern state.
A proper degree of privacy is essential for the well-being and development of an individual. And restraints imposed on government to pry into the lives of the citizen go to the essence of a democratic state: see La Forest J. in R. v. Dyment [R. v. Dyment, 1988 SCC OnLine Can SC 86 : (1988) 2 SCR 417] , SCC OnLine Can SC para 17 : SCR p. 426.” 619. Privacy is also the key to freedom of thought. A person has a right to think. The thoughts are sometimes translated into speech but confined to the person to whom it is made. For example, one may want to criticise someone but not share the criticism with the world.
Chelameswar, J.:
372. History abounds with examples of attempts by Governments to shape the minds of subjects. In other words, conditioning the thought process by prescribing what to read or not to read; what forms of art alone are required to be appreciated leading to the conditioning of beliefs; interfering with the choice of people regarding the kind of literature, music or art which an individual would prefer to enjoy. [Stanleyv. Georgia, 1969 SCC OnLine US SC 78 : 22 L Ed 2d 542 : 394 US 557 (1969)”3. … that the mere private possession of obscene matter cannot constitutionally be made a crime.
***9. … State has no business telling a man, sitting alone in his own house, what books he may read or what films he may watch. Our whole constitutional heritage rebels at the thought of giving Government the power to control men’s minds.” (SCC OnLine US SC paras 3 & 9)] Such conditioning is sought to be achieved by screening the source of information or prescribing penalties for making choices which Governments do not approve. [Bijoe Emmanuel v. State of Kerala, (1986) 3 SCC 615] Insofar as religious beliefs are concerned, a good deal of the misery our species suffer owes its existence to and centres around competing claims of the right to propagate religion. Constitution of India protects the liberty of all subjects guaranteeing [“25. Freedom of conscience and free profession, practice and propagation of religion.-
(1) Subject to public order, morality and health and to the other provisions of this Part, all persons are equally entitled to freedom of conscience and the right freely to profess, practice and propagate religion.(2) Nothing in this article shall affect the operation of any existing law or prevent the State from making any law-
(a) regulating or restricting any economic, financial, political or other secular activity which may be associated with religious practice;
(b) providing for social welfare and reform or the throwing open of Hindu religious institutions of a public character to all classes and sections of Hindus.
Explanation I.-The wearing and carrying of kirpans shall be deemed to be included in the profession of the Sikh religion.
Explanation II.-In sub-clause
(b) of clause (2), the reference to Hindus shall be construed as including a reference to persons professing the Sikh, Jaina or Buddhist religion, and the reference to Hindu religious institutions shall be construed accordingly.”] the freedom of conscience and right to freely profess, practice and propagate religion. While the right to freely “profess, practice and propagate religion” may be a facet of free speech guaranteed under Article 19(1)(a), the freedom of the belief or faith in any religion is a matter of conscience falling within the zone of purely private thought process and is an aspect of liberty. There are areas other than religious beliefs which form part of the individual’s freedom of conscience such as political belief, etc. which form part of the liberty under Article 21.
373. Concerns of privacy arise when the State seeks to intrude into the body of subjects. [Skinner v. Oklahoma, 1942 SCC OnLine US SC 125 : 86 L Ed 1655 : 316 US 535 (1942)”20. There are limits to the extent to which a legislatively represented majority may conduct biological experiments at the expense of the dignity and personality and natural powers of a minority-even those who have been guilty of what the majority defines as crimes.” (SCC OnLine US SC para 20)-Jackson, J.] Corporeal punishments were not unknown to India, their abolition is of a recent vintage. Forced feeding of certain persons by the State raises concerns of privacy. An individual’s rights to refuse life prolonging medical treatment or terminate his life is another freedom which falls within the zone of the right to privacy. I am conscious of the fact that the issue is pending before this Court.
But in various other jurisdictions, there is a huge debate on those issues though it is still a grey area. [ For the legal debate in this area in US, See Chapter 15.11 of American Constitutional Law by Laurence H. Tribe, 2nd Edn.] A woman’s freedom of choice whether to bear a child or abort her pregnancy are areas which fall in the realm of privacy. Similarly, the freedom to choose either to work or not and the freedom to choose the nature of the work are areas of private decision-making process. The right to travel freely within the country or go abroad is an area falling within the right to privacy. The text of our Constitution recognised the freedom to travel throughout the country under Article 19(1)(d).
This Court has already recognised that such a right takes within its sweep the right to travel abroad. [Maneka Gandhi v. Union of India, (1978) 1 SCC 248] A person’s freedom to choose the place of his residence once again is a part of his right to privacy [Williams v. Fears, 1900 SCC OnLine US SC 211 : 45 L Ed 186 : 179 US 270 (1900)-“8. Undoubtedly the right of locomotion, the right to remove from one place to another according to inclination, is an attribute of personal liberty….” (SCC OnLine US SC para 8)] recognised by the Constitution of India under Article 19(1)(e) though the predominant purpose of enumerating the abovementioned two freedoms in Article 19(1) is to disable both the federal and State Governments from creating barriers which are incompatible with the federal nature of our country and its Constitution. The choice of appearance and apparel are also aspects of the right to privacy. The freedom of certain groups of subjects to determine their appearance and apparel (such as keeping long hair and wearing a turban) are protected not as a part of the right to privacy but as a part of their religious belief. Such a freedom need not necessarily be based on religious beliefs falling under Article 25.
Informational traces are also an area which is the subject-matter of huge debate in various jurisdictions falling within the realm of the right to privacy, such data is as personal as that of the choice of appearance and apparel. Telephone tappings and internet hacking by State, of personal data is another area which falls within the realm of privacy. The instant reference arises out of such an attempt by the Union of India to collect biometric data regarding all the residents of this country. The abovementioned are some of the areas where some interest of privacy exists. The examples given above indicate to some extent the nature and scope of the right to privacy.
374. I do not think that anybody in this country would like to have the officers of the State intruding into their homes or private property at will or soldiers quartered in their houses without their consent. I do not think that anybody would like to be told by the State as to what they should eat or how they should dress or whom they should be associated with either in their personal, social or political life. Freedom of social and political association is guaranteed to citizens under Article 19(1)(c). Personal association is still a doubtful area. [The High Court of A.P. held that Article 19(1) (c) would take within its sweep the matrimonial association in T. Sareetha v. T. Venkata Subbaiah, 1983 SCC OnLine AP 90 : AIR 1983 AP 356. However, this case was later overruled by this Court in Saroj Rani v. Sudarshan Kumar Chadha, (1984) 4 SCC 90 : AIR 1984 SC 1562.] The decision-making process regarding the freedom of association, freedoms of travel and residence are purely private and fall within the realm of the right to privacy. It is one of the most intimate decisions.
375. All liberal democracies believe that the State should not have unqualified authority to intrude into certain aspects of human life and that the authority should be limited by parameters constitutionally fixed. Fundamental rights are the only constitutional firewall to prevent State’s interference with those core freedoms constituting liberty of a human being. The right to privacy is certainly one of the core freedoms which is to be defended. It is part of liberty within the meaning of that expression in Article 21.
376. I am in complete agreement with the conclusions recorded by my learned Brothers in this regard.” (iii) Privacy is intrinsic to freedom, liberty and dignity: The right to privacy is inherent to the liberties guaranteed by Part-III of the Constitution and privacy is an element of human dignity. The fundamental right to privacy derives from Part-III of the Constitution and recognition of this right does not require a constitutional amendment. Privacy is more than merely a derivative constitutional right. It is the necessary basis of rights guaranteed in the text of the Constitution. Discussion in this behalf is captured in the following passages:
Dr. D.Y. Chandrachud, J. :
127. The submission that recognising the right to privacy is an exercise which would require a constitutional amendment and cannot be a matter of judicial interpretation is not an acceptable doctrinal position. The argument assumes that the right to privacy is independent of the liberties guaranteed by Part III of the Constitution. There lies the error. The right to privacy is an element of human dignity. The sanctity of privacy lies in its functional relationship with dignity. Privacy ensures that a human being can lead a life of dignity by securing the inner recesses of the human personality from unwanted intrusion. Privacy recognises the autonomy of the individual and the right of every person to make essential choices which affect the course of life. In doing so privacy recognises that living a life of dignity is essential for a human being to fulfill the liberties and freedoms which are the cornerstone of the Constitution.
To recognise the value of privacy as a constitutional entitlement and interest is not to fashion a new fundamental right by a process of amendment through judicial fiat. Neither are the Judges nor is the process of judicial review entrusted with the constitutional responsibility to amend the Constitution. But judicial review certainly has the task before it of determining the nature and extent of the freedoms available to each person under the fabric of those constitutional guarantees which are protected. Courts have traditionally discharged that function and in the context of Article 21 itself, as we have already noted, a panoply of protections governing different facets of a dignified existence has been held to fall within the protection of Article 21.
S.A. Bobde, J. :
416. There is nothing unusual in the judicial enumeration of one right on the basis of another under the Constitution. In the case of Article 21’s guarantee of “personal liberty”, this practice is only natural if Salmond’s formulation of liberty as “incipient rights” [ P.J. Fitzgerald, Salmond on Jurisprudence at p. 228.] is correct. By the process of enumeration, constitutional courts merely give a name and specify the core of guarantees already present in the residue of constitutional liberty. Over time, the Supreme Court has been able to imply by its interpretative process that several fundamental rights including the right to privacy emerge out of expressly stated fundamental rights. In Unni Krishnan, J.P. v. State of A.P. [Unni Krishnan, J.P. v. State of A.P., (1993) 1 SCC 645] , a Constitution Bench of this Court held that “several unenumerated rights fall within Article 21 since personal liberty is of widest amplitude” [Unni Krishnan, J.P. v. State of A.P., (1993) 1 SCC 645 at p. 669, para 29] on the way to affirming the existence of a right to education. It went on to supply the following indicative list of such rights, which included the right to privacy: (SCC pp. 669-70, para 30)
“30. The following rights are held to be covered under Article 21:
1. The right to go abroad. Satwant Singh v. D. Ramarathnam [Satwant Singh Sawhney v. D. Ramarathnam, (1967) 3 SCR 525 : AIR 1967 SC 1836] .
2. The right to privacy. Gobind v. State of M.P. [Gobind v. State of M.P., (1975) 2 SCC 148 : 1975 SCC (Cri) 468] In this case reliance was placed on the American decision in Griswold v. Connecticut [Griswold v. Connecticut, 1965 SCC OnLine US SC 124 : 14 L Ed 2d 510 : 85 S Ct 1678 : 381 US 479 (1965)] , US at p. 510.
3. The right against solitary confinement. Sunil Batra (1) v. Delhi Admn. [Sunil Batra v. Delhi Admn., (1978) 4 SCC 494 : 1979 SCC (Cri) 155] , SCC at p. 545.
4. The right against bar fetters. Charles Sobhraj v. Supt., Central Jail [Charles Sobraj v. Supt., Central Jail, (1978) 4 SCC 104 : 1978 SCC (Cri) 542].
5. The right to legal aid. M.H. Hoskot v. State of Maharashtra [M.H. Hoskot v. State of Maharashtra, (1978) 3 SCC 544 : 1978 SCC (Cri) 468].
6. The right to speedy trial. Hussainara Khatoon (1) v. State of Bihar[Hussainara Khatoon (1) v. State of Bihar, (1980) 1 SCC 81 : 1980 SCC (Cri) 23] .
7. The right against handcuffing. Prem Shankar v. Delhi Admn. [Prem Shankar Shukla v. Delhi Admn., (1980) 3 SCC 526 : 1980 SCC (Cri) 815]
8. The right against delayed execution. T.V. Vatheeswaran v. State of T.N. [T.V. Vatheeswaran v. State of T.N., (1983) 2 SCC 68 : 1983 SCC (Cri) 342]
9. The right against custodial violence. Sheela Barse v. State of Maharashtra [Sheela Barse v. State of Maharashtra, (1983) 2 SCC 96 : 1983 SCC (Cri) 353].
10. The right against public hanging. Attorney General of India v. Lachma Devi [Attorney General of India v. Lachma Devi, 1989 Supp (1) SCC 264 : 1989 SCC (Cri) 413].
11. Doctor’s assistance. Paramananda Katara v. Union of India [Parmanand Katara v. Union of India, (1989) 4 SCC 286 : 1989 SCC (Cri) 721].
12. Shelter. Santistar Builders v. Narayan Khimalal Totame [Shantistar Builders v. Narayan Khimalal Totame, (1990) 1 SCC 520] .”
In the case of privacy, the case for judicial enumeration is especially strong. It is no doubt a fair implication from Article 21, but also more. Privacy is a right or condition, “logically presupposed” [ Laurence H. Tribe And Michael C. Dorf, “Levels of Generality in the Definition of Rights”, 57 U CHI L REV 1057 (1990) at p. 1068.] by rights expressly recorded in the constitutional text, if they are to make sense. As a result, privacy is more than merely a derivative constitutional right. It is the necessary and unavoidable logical entailment of rights guaranteed in the text of the Constitution.
R.F. Nariman, J:
482. Shri Sundaram has argued that rights have to be traced directly to those expressly stated in the fundamental rights chapter of the Constitution for such rights to receive protection, and privacy is not one of them.
It will be noticed that the dignity of the individual is a cardinal value, which is expressed in the Preamble to the Constitution. Such dignity is not expressly stated as a right in the fundamental rights chapter, but has been read into the right to life and personal liberty. The right to live with dignity is expressly read into Article 21 by the judgment in Jolly George Varghesev. Bank of Cochin [Jolly George Varghese v. Bank of Cochin, (1980) 2 SCC 360] , at para 10. Similarly, the right against bar fetters and handcuffing being integral to an individual’s dignity was read into Article 21 by the judgment in Sunil Batra v. Delhi Admn. [Sunil Batra v. Delhi Admn., (1978) 4 SCC 494 : 1979 SCC (Cri) 155] , at paras 192, 197-B, 234 and 241 and Prem Shankar Shukla v. Delhi Admn. [Prem Shankar Shukla v. Delhi Admn., (1980) 3 SCC 526 : 1980 SCC (Cri) 815] , at paras 21 and 22. It is too late in the day to canvas that a fundamental right must be traceable to express language in Part III of the Constitution.
As will be pointed out later in this judgment, a Constitution has to be read in such a way that words deliver up principles that are to be followed and if this is kept in mind, it is clear that the concept of privacy is contained not merely in personal liberty, but also in the dignity of the individual.”
(iv) Privacy has both positive and negative content: The negative content restrains the State from committing an intrusion upon the life and personal liberty of a citizen. Its positive content imposes an obligation on the State to take all necessary measures to protect the privacy of the individual.
Dr. D.Y. Chandrachud, J.:
326. Privacy has both positive and negative content. The negative content restrains the State from committing an intrusion upon the life and personal liberty of a citizen. Its positive content imposes an obligation on the State to take all necessary measures to protect the privacy of the individual.”
(v) Informational Privacy is a facet of right to privacy: The old adage that ‘knowledge is power’ has stark implications for the position of individual where data is ubiquitous, an allencompassing presence. Every transaction of an individual user leaves electronic tracks without her knowledge. Individually these information silos may seem inconsequential. In aggregation, information provides a picture of the beings. The challenges which big data poses to privacy emanate from both State and non-State entities.
This proposition is described in the following manner:
Dr. D.Y. Chandrachud, J.:
300. Ours is an age of information. Information is knowledge. The old adage that “knowledge is power” has stark implications for the position of the individual where data is ubiquitous, an all-encompassing presence. Technology has made life fundamentally interconnected. The internet has become all-pervasive as individuals spend more and more time online each day of their lives. Individuals connect with others and use the internet as a means of communication.
The internet is used to carry on business and to buy goods and services. Individuals browse the web in search of information, to send e-mails, use instant messaging services and to download movies. Online purchases have become an efficient substitute for the daily visit to the neighbouring store. Online banking has redefined relationships between bankers and customers. Online trading has created a new platform for the market in securities. Online music has refashioned the radio. Online books have opened up a new universe for the bibliophile. The old-fashioned travel agent has been rendered redundant by web portals which provide everything from restaurants to rest houses, airline tickets to art galleries, museum tickets to music shows. These are but a few of the reasons people access the internet each day of their lives.
Yet every transaction of an individual user and every site that she visits, leaves electronic tracks generally without her knowledge. These electronic tracks contain powerful means of information which provide knowledge of the sort of person that the user is and her interests [See Francois Nawrot, Katarzyna Syska and Przemyslaw Switalski, “Horizontal Application of Fundamental Rights – Right to Privacy on the Internet”, 9th Annual European Constitutionalism Seminar (May 2010), University of Warsaw, available at “http://en.zpc.wpia.uw.edu.pl/wpcontent/ uploads/2010/04/9_Horizontal_Application_of_Fun damental_Rights.pdf”.] .
Individually, these information silos may seem inconsequential. In aggregation, they disclose the nature of the personality: food habits, language, health, hobbies, sexual preferences, friendships, ways of dress and political affiliation. In aggregation, information provides a picture of the being: of things which matter and those that do not, of things to be disclosed and those best hidden.
xx xx xx
304. Data mining processes together with knowledge discovery can be combined to create facts about individuals. Metadata and the internet of things have the ability to redefine human existence in ways which are yet fully to be perceived. This, as Christina Moniodis states in her illuminating article, results in the creation of new knowledge about individuals; something which even she or he did not possess. This poses serious issues for the Court. In an age of rapidly evolving technology it is impossible for a Judge to conceive of all the possible uses of information or its consequences: “… The creation of new knowledge complicates data privacy law as it involves information the individual did not possess and could not disclose, knowingly or otherwise. In addition, as our State becomes an “information State” through increasing reliance on information-such that information is described as the “lifeblood that sustains political, social, and business decisions.
It becomes impossible to conceptualize all of the possible uses of information and resulting harms. Such a situation poses a challenge for courts who are effectively asked to anticipate and remedy invisible, evolving harms.” [ Christina P. Moniodis, “Moving from Nixon to NASA: Privacy’s Second Strand – A Right to Informational Privacy”, Yale Journal of Law and Technology (2012), Vol. 15 (1), at p. 154.] The contemporary age has been aptly regarded as “an era of ubiquitous dataveillance, or the systematic monitoring of citizen’s communications or actions through the use of information technology” [Yvonne McDermott, “Conceptualizing the Right to Data Protection in an Era of Big Data”, Big Data and Society (2017), at p. 1.] .
It is also an age of “big data” or the collection of data sets. These data sets are capable of being searched; they have linkages with other data sets; and are marked by their exhaustive scope and the permanency of collection. [Id, at pp. 1 and 4.] The challenges which big data poses to privacy interests emanate from State and non-State entities. Users of wearable devices and social media networks may not conceive of themselves as having volunteered data but their activities of use and engagement result in the generation of vast amounts of data about individual lifestyles, choices and preferences. Yvonne McDermott speaks about the quantified self in eloquent terms:
“… The rise in the so-called ‘quantified self’, or the self-tracking of biological, environmental, physical, or behavioural information through tracking devices, Internet-of-things devices, social network data and other means (?Swan.2013) may result in information being gathered not just about the individual user, but about people around them as well. Thus, a solely consent-based model does not entirely ensure the protection of one’s data, especially when data collected for one purpose can be repurposed for another.” [Id, at p. 4.]
xx xx xx
328. Informational privacy is a facet of the right to privacy. The dangers to privacy in an age of information can originate not only from the State but from non-State actors as well. We commend to the Union Government the need to examine and put into place a robust regime for data protection. The creation of such a regime requires a careful and sensitive balance between individual interests and legitimate concerns of the State. The legitimate aims of the State would include for instance protecting national security, preventing and investigating crime, encouraging innovation and the spread of knowledge, and preventing the dissipation of social welfare benefits.
These are matters of policy to be considered by the Union Government while designing a carefully structured regime for the protection of the data. Since the Union Government has informed the Court that it has constituted a Committee chaired by Hon’ble Shri Justice B.N. Srikrishna, former Judge of this Court, for that purpose, the matter shall be dealt with appropriately by the Union Government having due regard to what has been set out in this judgment.
S.K. Kaul, J.:
585. The growth and development of technology has created new instruments for the possible invasion of privacy by the State, including through surveillance, profiling and data collection and processing. Surveillance is not new, but technology has permitted surveillance in ways that are unimaginable. Edward Snowden shocked the world with his disclosures about global surveillance. States are utilising technology in the most imaginative ways particularly in view of increasing global terrorist attacks and heightened public safety concerns.
One such technique being adopted by the States is “profiling”. The European Union Regulation of 2016 [ Regulation No. (EU) 2016/679 of the European Parliament and of the Council of 27-4- 2016 on the protection of natural persons with regard to the processing of personal data and on the free movement of such data, and repealing Directive No. 95/46/EC (General Data Protection Regulation).] on data privacy defines “profiling” as any form of automated processing of personal data consisting of the use of personal data to evaluate certain personal aspects relating to a natural person, in particular to analyse or predict aspects concerning that natural person’s performance at work, economic situation, health, personal preferences, interests, reliability, behaviour, location or movements [ Regulation No. (EU) 2016/679 of the European Parliament and of the Council of 27-4-2016 on the protection of natural persons with regard to the processing of personal data and on the free movement of such data, and repealing Directive No. 95/46/EC (General Data Protection Regulation).] . Such profiling can result in discrimination based on religion, ethnicity and caste. However, “profiling” can also be used to further public interest and for the benefit of national security.
586. The security environment, not only in our country, but throughout the world makes the safety of persons and the State a matter to be balanced against this right to privacy.
587. The capacity of non-State actors to invade the home and privacy has also been enhanced. Technological development has facilitated journalism that is more intrusive than ever before.
588. Further, in this digital age, individuals are constantly generating valuable data which can be used by non-State actors to track their moves, choices and preferences. Data is generated not just by active sharing of information, but also passively, with every click on the “world wide web”. We are stated to be creating an equal amount of information every other day, as humanity created from the beginning of recorded history to the year 2003 – enabled by the “world wide web”. [ Michael L. Rustad, SannaKulevska, “Reconceptualizing the right to be forgotten to enable transatlantic data flow”, (2015) 28 Harv JL & Tech 349.]
589. Recently, it was pointed out that ” “Uber”, the world’s largest taxi company, owns no vehicles. “Facebook”, the world’s most popular media owner, creates no content. “Alibaba”, the most valuable retailer, has no inventory. And “Airbnb”, the world’s largest accommodation provider, owns no real estate.
Something interesting is happening.” [ Tom Goodwin “The Battle is for Customer Interface”, <https://techcrunch.com/2015/03/03/in-the-age-ofdisintermediation- the-battle-is-all-for-the-customerinterface/>.] “Uber” knows our whereabouts and the places we frequent. “Facebook” at the least, knows who we are friends with. “Alibaba” knows our shopping habits. “Airbnb” knows where we are travelling to. Social network providers, search engines, e-mail service providers, messaging applications are all further examples of non-State actors that have extensive knowledge of our movements, financial transactions, conversations – both personal and professional, health, mental state, interest, travel locations, fares and shopping habits. As we move towards becoming a digital economy and increase our reliance on internetbased services, we are creating deeper and deeper digital footprints – passively and actively.
590. These digital footprints and extensive data can be analysed computationally to reveal patterns, trends, and associations, especially relating to human behaviour and interactions and hence, is valuable information. This is the age of “big data”. The advancement in technology has created not just new forms of data, but also new methods of analysing the data and has led to the discovery of new uses for data. The algorithms are more effective and the computational power has magnified exponentially. A large number of people would like to keep such search history private, but it rarely remains private, and is collected, sold and analysed for purposes such as targeted advertising. of course, “big data” can also be used to further public interest. There may be cases where collection and processing of big data is legitimate and proportionate, despite being invasive of privacy otherwise.
591. Knowledge about a person gives a power over that person. The personal data collected is capable of effecting representations, influencing decision-making processes and shaping behaviour. It can be used as a tool to exercise control over us like the “big brother” State exercised. This can have a stultifying effect on the expression of dissent and difference of opinion, which no democracy can afford.
592. Thus, there is an unprecedented need for regulation regarding the extent to which such information can be stored, processed and used by non-State actors. There is also a need for protection of such information from the State. Our Government was successful in compelling Blackberry to give to it the ability to intercept data sent over Blackberry devices. While such interception may be desirable and permissible in order to ensure national security, it cannot be unregulated. [ Kadhim Shubber, “Blackberry gives Indian Government ability to intercept messages” published by Wired on 11-7-2013 <http://www.wired.co.uk/article/blackberry-india>.]
593. The concept of “invasion of privacy” is not the early conventional thought process of “poking ones nose in another person’s affairs”. It is not so simplistic. In today’s world, privacy is a limit on the Government’s power as well as the power of private sector entities. [ Daniel Solove, “10 Reasons Why Privacy Matters” published on 20-1-2014 <https://www.teachprivacy.com/10-reasons-privacymatters/>.]
594. George Orwell created a fictional State in Nineteen Eighty-Four. Today, it can be a reality. The technological development today can enable not only the State, but also big corporations and private entities to be the “big brother”.
xx xx xx
629. The right of an individual to exercise control over his personal data and to be able to control his/her own life would also encompass his right to control his existence on the internet. Needless to say that this would not be an absolute right. The existence of such a right does not imply that a criminal can obliterate his past, but that there are variant degrees of mistakes, small and big, and it cannot be said that a person should be profiled to the nth extent for all and sundry to know.
630. A high school teacher was fired after posting on her Facebook page that she was “so not looking forward to another [school] year” since the school district’s residents were “arrogant and snobby”.
A flight attendant was fired for posting suggestive photos of herself in the company’s uniform. [ Patricia Sánchez Abril, “Blurred Boundaries: Social Media Privacy and the Twenty-First-Century Employee”, 49 Am Bus LJ 63 at p. 69 (2012).] In the predigital era, such incidents would have never occurred. People could then make mistakes and embarrass themselves, with the comfort that the information will be typically forgotten over time.
631. The impact of the digital age results in information on the internet being permanent. Humans forget, but the internet does not forget and does not let humans forget. Any endeavour to remove information from the internet does not result in its absolute obliteration.
The footprints remain. It is thus, said that in the digital world preservation is the norm and forgetting a struggle [ Ravi Antani,
“THE RESISTANCE of MEMORY : COULD THE EUROPEAN UNION’S RIGHT TO BE FORGOTTEN EXIST IN THE UNITED STATES?”, 30 Berkeley Tech LJ 1173 (2015).] .
632. The technology results almost in a sort of a permanent storage in some way or the other making it difficult to begin life again giving up past mistakes. People are not static, they change and grow through their lives. They evolve. They make mistakes. But they are entitled to re-invent themselves and reform and correct their mistakes. It is privacy which nurtures this ability and removes the shackles of unadvisable things which may have been done in the past.
633. Children around the world create perpetual digital footprints on social network websites on a 24/7 basis as they learn their “ABCs”: Apple, Bluetooth and chat followed by download, e-mail, Facebook, Google, Hotmail and Instagram. [ Michael L. Rustad, SannaKulevska, “Reconceptualizing the right to be forgotten to enable transatlantic data flow”, (2015) 28 Harv JL & Tech 349.] They should not be subjected to the consequences of their childish mistakes and naivety, their entire life. Privacy of children will require special protection not just in the context of the virtual world, but also the real world.
634. People change and an individual should be able to determine the path of his life and not be stuck only on a path of which he/she treaded initially. An individual should have the capacity to change his/her beliefs and evolve as a person. Individuals should not live in fear that the views they expressed will forever be associated with them and thus refrain from expressing themselves.
635. Whereas this right to control dissemination of personal information in the physical and virtual space should not amount to a right of total eraser of history, this right, as a part of the larger right to privacy, has to be balanced against other fundamental rights like the freedom of expression, or freedom of media, fundamental to a democratic society.
636. Thus, the European Union Regulation of 2016 [Regulation No. (EU) 2016/679 of the European Parliament and of the Council of 27-4-2016 on the protection of natural persons with regard to the processing of personal data and on the free movement of such data, and repealing Directive No. 95/46/EC (General Data Protection Regulation).] has recognised what has been termed as “the right to be forgotten”. This does not mean that all aspects of earlier existence are to be obliterated, as some may have a social ramification. If we were to recognise a similar right, it would only mean that an individual who is no longer desirous of his personal data to be processed or stored, should be able to remove it from the system where the personal data/information is no longer necessary, relevant, or is incorrect and serves no legitimate interest.
Such a right cannot be exercised where the information/data is necessary, for exercising the right of freedom of expression and information, for compliance with legal obligations, for the performance of a task carried out in public interest, on the grounds of public interest in the area of public health, for archiving purposes in the public interest, scientific or historical research purposes or statistical purposes, or for the establishment, exercise or defence of legal claims. Such justifications would be valid in all cases of breach of privacy, including breaches of data privacy.”
(vi) Right to privacy cannot be impinged without a just, fair and reasonable law: It has to fulfill the test of proportionality i.e. (i) existence of a law; (ii) must serve a legitimate State aim; and (iii) proportionality.
“Dr. D.Y. Chandrachud, J. :
310. While it intervenes to protect legitimate State interests, the State must nevertheless put into place a robust regime that ensures the fulfilment of a threefold requirement. These three requirements apply to all restraints on privacy (not just informational privacy). They emanate from the procedural and content-based mandate of Article 21. The first requirement that there must be a law in existence to justify an encroachment on privacy is an express requirement of Article 21. For, no person can be deprived of his life or personal liberty except in accordance with the procedure established by law.
The existence of law is an essential requirement. Second, the requirement of a need, in terms of a legitimate State aim, ensures that the nature and content of the law which imposes the restriction falls within the zone of reasonableness mandated by Article 14, which is a guarantee against arbitrary State action. The pursuit of a legitimate State aim ensures that the law does not suffer from manifest arbitrariness. Legitimacy, as a postulate, involves a value judgment. Judicial review does not reappreciate or second guess the value judgment of the legislature but is for deciding whether the aim which is sought to be pursued suffers from palpable or manifest arbitrariness.
The third requirement ensures that the means which are adopted by the legislature are proportional to the object and needs sought to be fulfilled by the law. Proportionality is an essential facet of the guarantee against arbitrary State action because it ensures that the nature and quality of the encroachment on the right is not disproportionate to the purpose of the law. Hence, the threefold requirement for a valid law arises out of the mutual interdependence between the fundamental guarantees against arbitrariness on the one hand and the protection of life and personal liberty, on the other. The right to privacy, which is an intrinsic part of the right to life and liberty, and the freedoms embodied in Part III is subject to the same restraints which apply to those freedoms.
311. Apart from national security, the State may have justifiable reasons for the collection and storage of data. In a social welfare State, the Government embarks upon programmes which provide benefits to impoverished and marginalised sections of society. There is a vital State interest in ensuring that scarce public resources are not dissipated by the diversion of resources to persons who do not qualify as recipients. Allocation of resources for human development is coupled with a legitimate concern that the utilisation of resources should not be siphoned away for extraneous purposes.
Data mining with the object of ensuring that resources are properly deployed to legitimate beneficiaries is a valid ground for the State to insist on the collection of authentic data. But, the data which the State has collected has to be utilised for legitimate purposes of the State and ought not to be utilised unauthorisedly for extraneous purposes. This will ensure that the legitimate concerns of the State are duly safeguarded while, at the same time, protecting privacy concerns. Prevention and investigation of crime and protection of the revenue are among the legitimate aims of the State. Digital platforms are a vital tool of ensuring good governance in a social welfare State. Information technology-legitimately deployed is a powerful enabler in the spread of innovation and knowledge.
312. A distinction has been made in contemporary literature between anonymity on one hand and privacy on the other. [See in this connection, Jeffrey M. Skopek, “Reasonable Expectations of Anonymity”, Virginia Law Review (2015), Vol. 101, at pp. 691-762.] Both anonymity and privacy prevent others from gaining access to pieces of personal information yet they do so in opposite ways. Privacy involves hiding information whereas anonymity involves hiding what makes it personal. An unauthorised parting of the medical records of an individual which have been furnished to a hospital will amount to an invasion of privacy. On the other hand, the State may assert a legitimate interest in analysing data borne from hospital records to understand and deal with a public health epidemic such as malaria or dengue to obviate a serious impact on the population. If the State preserves the anonymity of the individual it could legitimately assert a valid State interest in the preservation of public health to design appropriate policy interventions on the basis of the data available to it.
313. Privacy has been held to be an intrinsic element of the right to life and personal liberty under Article 21 and as a constitutional value which is embodied in the fundamental freedoms embedded in Part III of the Constitution. Like the right to life and liberty, privacy is not absolute. The limitations which operate on the right to life and personal liberty would operate on the right to privacy. Any curtailment or deprivation of that right would have to take place under a regime of law. The procedure established by law must be fair, just and reasonable. The law which provides for the curtailment of the right must also be subject to constitutional safeguards.
xx xx xx
325. Like other rights which form part of the fundamental freedoms protected by Part III, including the right to life and personal liberty under Article 21, privacy is not an absolute right. A law which encroaches upon privacy will have to withstand the touchstone of permissible restrictions on fundamental rights. In the context of Article 21 an invasion of privacy must be justified on the basis of a law which stipulates a procedure which is fair, just and reasonable. The law must also be valid with reference to the encroachment on life and personal liberty under Article 21.
An invasion of life or personal liberty must meet the threefold requirement of
(i) legality, which postulates the existence of law;
(ii) need, defined in terms of a legitimate State aim; and
(iii) proportionality which ensures a rational nexus between the objects and the means adopted to achieve them.
S.A. Bobde, J. :
426. There is no doubt that privacy is integral to the several fundamental rights recognised by Part III of the Constitution and must be regarded as a fundamental right itself. The relationship between the right to privacy and the particular fundamental right (or rights) involved would depend on the action interdicted by a particular law. At a minimum, since privacy is always integrated with personal liberty, the constitutionality of the law which is alleged to have invaded into a rights bearer’s privacy must be tested by the same standards by which a law which invades personal liberty under Article 21 is liable to be tested. Under Article 21, the standard test at present is the rationality review expressed in Maneka Gandhi case [Maneka Gandhi v. Union of India, (1978) 1 SCC 248] .
This requires that any procedure by which the State interferes with an Article 21 right to be “fair, just and reasonable, not fanciful, oppressive or arbitrary” [Maneka Gandhi v. Union of India, (1978) 1 SCC 248 at p. 323, para 48].
R.F. Nariman, J. :
526. But this is not to say that such a right is absolute. This right is subject to reasonable regulations made by the State to protect legitimate State interests or public interest. However, when it comes to restrictions on this right, the drill of various articles to which the right relates must be scrupulously followed.
For example, if the restraint on privacy is over fundamental personal choices that an individual is to make, State action can be restrained under Article 21 read with Article 14 if it is arbitrary and unreasonable; and under Article 21 read with Article 19(1) (a) only if it relates to the subjects mentioned in Article 19(2) and the tests laid down by this Court for such legislation or subordinate legislation to pass muster under the said article. Each of the tests evolved by this Court, qua legislation or executive action, under Article 21 read with Article 14; or Article 21 read with Article 19(1)(a) in the aforesaid examples must be met in order that State action pass muster. In the ultimate analysis, the balancing act that is to be carried out between individual, societal and State interests must be left to the training and expertise of the judicial mind.
S.K. Kaul, J. :
638. The concerns expressed on behalf of the petitioners arising from the possibility of the State infringing the right to privacy can be met by the test suggested for limiting the discretion of the State:
“(i) The action must be sanctioned by law;
(ii) The proposed action must be necessary in a democratic society for a legitimate aim;
(iii) The extent of such interference must be proportionate to the need for such interference;
(iv) There must be procedural guarantees against abuse of such interference.”
Chelameswar, J.:
377. It goes without saying that no legal right can be absolute. Every right has limitations. This aspect of the matter is conceded at the Bar. Therefore, even a fundamental right to privacy has limitations. The limitations are to be identified on case-to-case basis depending upon the nature of the privacy interest claimed. There are different standards of review to test infractions of fundamental rights. While the concept of reasonableness overarches Part III, it operates differently across Articles (even if only slightly differently across some of them).
Having emphatically interpreted the Constitution’s liberty guarantee to contain a fundamental right to privacy, it is necessary for me to outline the manner in which such a right to privacy can be limited. I only do this to indicate the direction of the debate as the nature of limitation is not at issue here.
378. To begin with, the options canvassed for limiting the right to privacy include an Article 14 type reasonableness enquiry [A challenge under Article 14 can be made if there is an unreasonable classification and/or if the impugned measure is arbitrary.
The classification is unreasonable if there is no intelligible differentia justifying the classification and if the classification has no rational nexus with the objective sought to be achieved. Arbitrariness, which was first explained at para 85 of E.P. Royappa v. State of T.N., (1974) 4 SCC 3 : 1974 SCC (L&S) 165 : AIR 1974 SC 555, is very simply the lack of any reasoning.] ; limitation as per the express provisions of Article 19; a just, fair and reasonable basis (that is, substantive due process) for limitation per Article 21; and finally, a just, fair and reasonable standard per Article 21 plus the amorphous standard of “compelling State interest”.
The last of these four options is the highest standard of scrutiny [ A tiered level of scrutiny was indicated in what came to be known as the most famous footnote in constitutional law, that is, fn 4 in United States v. Carolene Products Co., 1938 SCC OnLine US SC 93 : 82 L Ed 1234 : 304 US 144 (1938). Depending on the graveness of the right at stake, the court adopts a correspondingly rigorous standard of scrutiny.] that a court can adopt. It is from this menu that a standard of review for limiting the right to privacy needs to be chosen.
379. At the very outset, if a privacy claim specifically flows only from one of the expressly enumerated provisions under Article 19, then the standard of review would be as expressly provided under Article 19. However, the possibility of a privacy claim being entirely traceable to rights other than Article 21 is bleak. Without discounting that possibility, it needs to be noted that Article 21 is the bedrock of the privacy guarantee. If the spirit of liberty permeates every claim of privacy, it is difficult, if not impossible, to imagine that any standard of limitation other than the one under Article 21 applies. It is for this reason that I will restrict the available options to the latter two from the above described four.
380. The just, fair and reasonable standard of review under Article 21 needs no elaboration. It has also most commonly been used in cases dealing with a privacy claim hitherto. [District Registrar and Collector v. Canara Bank, (2005) 1 SCC 496 : AIR 2005 SC 186] , [State of Maharashtra v. Bharat Shanti Lal Shah, (2008) 13 SCC 5] Gobind [Gobind v. State of M.P., (1975) 2 SCC 148 : 1975 SCC (Cri) 468] resorted to the compelling State interest standard in addition to the Article 21 reasonableness enquiry. From the United States, where the terminology of “compelling State interest” originated, a strict standard of scrutiny comprises two things-a “compelling State interest” and a requirement of “narrow tailoring” (narrow tailoring means that the law must be narrowly framed to achieve the objective).
As a term, “compelling State interest” does not have definite contours in the US. Hence, it is critical that this standard be adopted with some clarity as to when and in what types of privacy claimsit is to be used. Only in privacy claims which deserve the strictest scrutiny is the standard of compelling State interest to be used. As for others, the just, fair and reasonable standard under Article 21 will apply. When the compelling State interest standard is to be employed, must depend upon the context of concrete cases. However, this discussion sets the ground rules within which a limitation for the right to privacy is to be found.”
82) In view of the aforesaid detailed discussion in all the opinions penned by six Hon’ble Judges, it stands established, without any pale of doubt, that privacy has now been treated as part of fundamental rights. The Court has held, in no uncertain terms, that privacy has always been a natural right which gives an individual freedom to exercise control over his or her personality. The judgment further affirms three aspects of the fundamental right to privacy, namely:
(i) intrusion with an individual’s physical body;
(ii) informational privacy; and
(iii) privacy of choice.
83) As succinctly put by Nariman, J. first aspect involves the person himself/herself and guards a person’s rights relatable to his/her physical body thereby controlling the uncalled invasion by the State. Insofar as the second aspect, namely, informational privacy is concerned, it does not deal with a person’s body but deals with a person’s mind. In this manner, it protects a person by giving her control over the dissemination of material that is personal to her and disallowing unauthorised use of such information by the State.
Third aspect of privacy relates to individual’s autonomy by protecting her fundamental personal choices. These aspects have functional connection and relationship with dignity. In this sense, privacy is a postulate of human dignity itself. Human dignity has a constitutional value and its significance is acknowledged by the Preamble. Further, by catena of judgments, human dignity is treated as a fundamental right and as a facet not only of Article 21 but that of right to equality (Article 14) and also part of bouquet of freedoms stipulated in Article 19.
Therefore, privacy as a right is intrinsic of freedom, liberty and dignity. Viewed in this manner, one can trace positive and negative contents of privacy. The negative content restricts the State from committing an intrusion upon the life and personal liberty of a citizen. Its positive content imposes an obligation on the State to take all necessary measures to protect the privacy of the individual. 84) A brief summation of the judgment on privacy would indicate that privacy is treated as fundamental right. It is predicated on the basis that privacy is a postulate of dignity and the concept of dignity can be traced to the preamble of the Constitution as well as Article 21 thereof.
Further, privacy is considered as a subset of personal liberty thereby accepting the minority opinion in Kharak Singh v. State of U.P. & Ors.29 Another significant jurisprudential development of this judgment is that right to privacy as a fundamental right is not limited to Article 21. On the contrary, privacy resonates through the entirety of Part III of the Constitution which pertains to fundamental rights and, in particular, Articles 14, 19 and 21. Privacy is also recognised as a natural right which inheres in individuals and is, thus, inalienable. In developing the aforesaid concepts, the Court has been receptive to the principles in international law and international instruments.
It is a recognition of the fact that certain human rights cannot be confined within the bounds of geographical location of a nation but have universal application. In the process, the Court accepts the concept of universalisation of human rights, including the right to privacy as a human right and the good practices in developing and understanding such rights in other countries have been welcomed. In this hue, it can also be remarked that comparative law has played a very significant role in shaping the aforesaid judgment on privacy in Indian context, notwithstanding the fact that such comparative law has only a persuasive value.
85) The whole process of reasoning contained in different opinions of the Hon’ble Judges would, thus, reflect that the argument that it is difficult to precisely define the common denominator of privacy, was rejected. While doing so, the Court referred to various approaches in formulating privacy30. An astute and sagacious analysis of the judgment by the Centre for Internet and Society brings about the following approaches which contributed to formulating the following right to privacy:
(a) Classifying privacy on the basis of ‘harms’, thereby adopting the approach conceptualised by Daniel Solove. In his book, Understanding Privacy31, Daniel Solove makes a case for privacy being a family resemblance concept.
(b) Classifying privacy on the basis of ‘interests’: Gary Bostwick’s taxonomy of privacy is among the most prominent amongst the scholarship that sub-areas within the right to privacy protect different ‘interests’ or ‘justifications’. This taxonomy is adopted in Chelameswar, J.’s definition of ‘privacy’ and includes the three interests of privacy of repose, privacy of sanctuary and privacy of intimate decision. Repose is the ‘right to be let alone’, sanctuary is the interest which prevents others from knowing, seeing and hearing thus keeping information within the private zone, and finally, privacy of intimate decision protects the freedom to act autonomously.
(c) Classifying privacy as an ‘aggregation of rights’: This approach in classifying privacy as a right, as highlighted above, is not limited to one particular provision in the Chapter of Fundamental Rights under the Constitution but is associated with amalgam of different but connected rights. In formulating this principle, the Court has referred to scholars like Roger Clarke, Anita Allen etc. It has led to the recognition of private spaces or zones as protected under the right to privacy (thereby extending the ambit and scope of spatial privacy), informational privacy and decisional autonomy.
86) The important question that arises, which is directly involved in these cases, is: What is the scope of the right to privacy and in what circumstances such a right can be limited?
87) Concededly, fundamental rights are not absolute. The Constitution itself permits State to impose reasonable restrictions on these rights under certain circumstances. Thus, extent and scope of the right to privacy and how and when it can be limited by the State actions is also to be discerned. As noted above, Nariman, J. has led the path by observing that “when it comes to restrictions on this right, the drill of various Articles to which the right relates must be scrupulously followed”.
Therefore, examination has to be from the point of view of Articles 14, 19 and 21 for the reason that right to privacy is treated as having intimate connection to various rights in Part III and is not merely related to Article 21. Looked from this angle, the action of the State will have to be tested on the touchstone of Article 14. This judgment clarifies that the ‘classification’ test adopted earlier has to be expanded and instead the law/action is to be tested on the ground of ‘manifest arbitrariness’. This aspect has already been discussed in detail under the caption ‘Scope of Judicial Review’ above. When it comes to examining the ‘restrictions’ as per the provisions of Article 19 of the Constitution, the judgment proceeds to clarify that a law which impacts dignity and liberty under Article 21, as well as having chilling effects on free speech which is protected by Article 19(1)(a), must satisfy the standards of judicial review under both provisions. Therefore, such restriction must satisfy the test of judicial review under:
(i) one of the eight grounds mentioned under Article 19(2); and
(ii) the restriction should be reasonable.
This Court has applied multiple standards to determine reasonableness, including proximity, arbitrariness, and proportionality. Further, the reasonable restrictions must be in the interests of:
(i) the sovereignty and integrity of India,
(ii) the security of the State,
(iii) friendly relations with foreign States,
(iv) public order,
(v) decency or morality or
(vi) in relation to contempt of court,
(vii) defamation or
(viii) incitement to an offence.
88) The judgment further lays down that in the context of Article 21, the test to be applied while examining a particular provision is the ‘just, fair and reasonable test’ thereby bringing notion of proportionality.
89) The petitioners have sought to build their case on the aforesaid parameters of privacy and have submitted that this right of privacy, which is now recognised as a fundamental right, stands violated by the very fabric contained in the scheme of Aadhaar.
It is sought to be highlighted that the data which is collected by the State, particularly with the authentication of each transaction entered into by an individual, can be assimilated to construct a profile of such an individual and it particularly violates informational privacy. No doubt, there can be reasonable restrictions on this right, which is conceded by the petitioners. It is, however, argued that right to privacy cannot be impinged without a just, fair and reasonable law. Therefore, in the first instance, any intrusion into the privacy of a person has to be backed by a law. Further, such a law, to be valid, has to pass the test of legitimate aim which it should serve and also proportionality i.e. proportionate to the need for such interference. Not only this, the law in question must also provide procedural guarantees against abuse of such interference.
90) At the same time, it can also be deduced from the reading of the aforesaid judgment that the reasonable expectation of privacy may vary from the intimate zone to the private zone and from the private zone to the public arena. Further, privacy is not lost or surrendered merely because the individual is in a public place. For example, if a person was to post on Facebook vital information about himself, the same being in public domain, he would not be entitled to claim privacy right. This aspect is highlighted by some of the Hon’ble Judges as under: Dr. D.Y. Chandrachud, J.:
“297. What, then, does privacy postulate? Privacy postulates the reservation of a private space for the individual, described as the right to be let alone. The concept is founded on the autonomy of the individual. The ability of an individual to make choices lies at the core of the human personality. The notion of privacy enables the individual to assert and control the human element which is inseparable from the personality of the individual. The inviolable nature of the human personality is manifested in the ability to make decisions on matters intimate to human life. The autonomy of the individual is associated over matters which can be kept private. These are concerns over which there is a legitimate expectation of privacy. The body and the mind are inseparable elements of the human personality.
The integrity of the body and the sanctity of the mind can exist on the foundation that each individual possesses an inalienable ability and right to preserve a private space in which the human personality can develop. Without the ability to make choices, the inviolability of the personality would be in doubt. Recognising a zone of privacy is but an acknowledgment that each individual must be entitled to chart and pursue the course of development of personality. Hence privacy is a postulate of human dignity itself. Thoughts and behavioural patterns which are intimate to an individual are entitled to a zone of privacy where one is free of social expectations. In that zone of privacy, an individual is not judged by others. Privacy enables each individual to take crucial decisions which find expression in the human personality.
It enables individuals to preserve their beliefs, thoughts, expressions, ideas, ideologies, preferences and choices against societal demands of homogeneity. Privacy is an intrinsic recognition of heterogeneity, of the right of the individual to be different and to stand against the tide of conformity in creating a zone of solitude. Privacy protects the individual from the searching glare of publicity in matters which are personal to his or her life. Privacy attaches to the person and not to the place where it is associated. Privacy constitutes the foundation of all liberty because it is in privacy that the individual can decide how liberty is best exercised. Individual dignity and privacy are inextricably linked in a pattern woven out of a thread of diversity into the fabric of a plural culture.
xx xx xx
299. Privacy represents the core of the human personality and recognises the ability of each individual to make choices and to take decisions governing matters intimate and personal. Yet, it is necessary to acknowledge that individuals live in communities and work in communities. Their personalities affect and, in turn are shaped by their social environment. The individual is not a hermit. The lives of individuals are as much a social phenomenon.
In their interactions with others, individuals are constantly engaged in behavioural patterns and in relationships impacting on the rest of society. Equally, the life of the individual is being consistently shaped by cultural and social values imbibed from living in the community. This state of flux which represents a constant evolution of individual personhood in the relationship with the rest of society provides the rationale for reserving to the individual a zone of repose. The lives which individuals lead as members of society engender a reasonable expectation of privacy.
The notion of a reasonable expectation of privacy has elements both of a subjective and objective nature. Privacy at a subjective level is a reflection of those areas where an individual desires to be left alone. On an objective plane, privacy is defined by those constitutional values which shape the content of the protected zone where the individual ought to be left alone. The notion that there must exist a reasonable expectation of privacy ensures that while on the one hand, the individual has a protected zone of privacy, yet on the other, the exercise of individual choices is subject to the rights of others to lead orderly lives.
For instance, an individual who possesses a plot of land may decide to build upon it subject to zoning regulations. If the building byelaws define the area upon which construction can be raised or the height of the boundary wall around the property, the right to privacy of the individual is conditioned by regulations designed to protect the interests of the community in planned spaces. Hence while the individual is entitled to a zone of privacy, its extent is based not only on the subjective expectation of the individual but on an objective principle which defines a reasonable expectation.
xx xx xx
307. The sphere of privacy stretches at one end to those intimate matters to which a reasonable expectation of privacy may attach. It expresses a right to be left alone. A broader connotation which has emerged in academic literature of a comparatively recent origin is related to the protection of one’s identity. Data protection relates closely with the latter sphere. Data such as medical information would be a category to which a reasonable expectation of privacy attaches. There may be other data which falls outside the reasonable expectation paradigm. Apart from safeguarding privacy, data protection regimes seek to protect the autonomy of the individual.
This is evident from the emphasis in the European data protection regime on the centrality of consent. Related to the issue of consent is the requirement of transparency which requires a disclosure by the data recipient of information pertaining to data transfer and use.” S.A. Bobde, J: “421. Shri Rakesh Dwivedi, appearing for the State of Gujarat, while referring to several judgments of the Supreme Court of the United States, submitted that only those privacy claims which involve a “reasonable expectation of privacy” be recognised as protected by the fundamental right. It is not necessary for the purpose of this case to deal with the particular instances of privacy claims which are to be recognised as implicating a fundamental right. Indeed, it would be premature to do so. The scope and ambit of a constitutional protection of privacy can only be revealed to us on a case-by-case basis.”
91) Though Nariman, J. did not subscribe to the aforesaid view in totality, however, His Lordship has also given an example that if a person has to post on Facebook vital information, the same being in public domain, she would not be entitled to the claim of privacy right.
92) We would also like to reproduce following discussion, in the opinion authored by Nariman, J., giving the guidance as to how a law has to be tested when it is challenged on the ground that it violates the fundamental right to privacy: “…Statutory provisions that deal with aspects of privacy would continue to be tested on the ground that they would violate the fundamental right to privacy, and would not be struck down, if it is found on a balancing test that the social or public interest and the reasonableness of the restrictions would outweigh the particular aspect of privacy claimed. If this is so, then statutes which would enable the State to contractually obtain information about persons would pass muster in given circumstances, provided they safeguard the individual right to privacy as well.
A simple example would suffice. If a person was to paste on Facebook vital information about himself/herself, such information, being in the public domain, could not possibly be claimed as a privacy right after such disclosure. But, in pursuance of a statutory requirement, if certain details need to be given for the statutory purpose concerned, then such details would certainly affect the right to privacy, but would on a balance, pass muster as the State action concerned has sufficient inbuilt safeguards to protect this right- viz. the fact that such information cannot be disseminated to anyone else, save on compelling grounds of public interest.”
93) One important comment which needs to be made at this stage relates to the standard of judicial review while examining the validity of a particular law that allegedly infringes right to privacy. The question is as to whether the Court is to apply ‘strict scrutiny’ standard or the ‘just, fair and reasonableness’ standard. In the privacy judgment, different observations are made by different Hon’ble Judges and the aforesaid aspect is not determined authoritatively, may be for the reason that the Bench was deciding the reference on the issue as to whether right to privacy is a fundamental right or not and, in the process, it was called upon to decide the specific questions referred to it. We have dealt with this aspect at the appropriate stage.
Principles of Human Dignity:
94) While undertaking the analysis of the judgment in K.S. Puttaswamy, we have mentioned that one of the attributes laid down therein is that the sanctity of privacy lies in its functional relationship with dignity. Privacy is the constitutional core of human dignity. In the context of Aadhaar scheme how the concept of human dignity is to be applied assumes significance.
95) In Common Cause v. Union of India32, the concept of human dignity has been explained in much detail33. The concept of human dignity developed in the said judgment was general in nature which is based on right to autonomy and right of choice and it has become a constitutional value. In the last 40 years or so, this Court has given many landmark judgments wherein concept of human dignity is recognised as an attribute of fundamental rights. In the earlier years, though the meaning and scope of human dignity by itself was not expanded, this exercise has been undertaken in last few years. Earlier judgments have mentioned that human dignity is the intrinsic value of every human being and, in the process, a person’s autonomy as an attribute of dignity stands recognised. The judgments rendered in the last few years have attempted to provide jurisprudential basis to the concept of human dignity itself.
96) In National Legal Services Authority v. Union of India & Ors.34 while recognising the right of transgenders of self determination of their sex, the Court explained the contours of human dignity in the following words:
“106. The basic principle of the dignity and freedom of the individual is common to all nations, particularly those having democratic set up. Democracy requires us to respect and develop the free spirit of human being which is responsible for all progress in human history. Democracy is also a method by which we attempt to raise the living standard of the people and to give opportunities to every person to develop his/her personality.
It is founded on peaceful co-existence and cooperative living. If democracy is based on the recognition of the individuality and dignity of man, as a fortiori we have to recognize the right of a human being to choose his sex/gender identity which is integral to his/her personality and is one of the most basic aspect of self-determination, dignity and freedom. In fact, there is a growing recognition that the true measure of development of a nation is not economic growth; it is human dignity.
107. More than 225 years ago, Immanuel Kant propounded the doctrine of free will, namely, the free willing individual as a natural law ideal. Without going into the detailed analysis of his aforesaid theory of justice (as we are not concerned with the analysis of his jurisprudence) what we want to point out is his emphasis on the “freedom” of human volition. The concepts of volition and freedom are “pure”, that is not drawn from experience. They are independent of any particular body of moral or legal rules. They are presuppositions of all such rules, valid and necessary for all of them.
108. Over a period of time, two divergent interpretations of the Kantian criterion of justice came to be discussed. One trend was an increasing stress on the maximum of individual freedom of action as the end of law. This may not be accepted and was criticised by the protagonist of “hedonist utilitarianism”, notably Bentham. This school of thought laid emphasis on the welfare of the society rather than an individual by propounding the principle of maximum of happiness to most of the people. Fortunately, in the instant case, there is no such dichotomy between the individual freedom/liberty we are discussing, as against public good. On the contrary, granting the right to choose gender leads to public good.
The second tendency of the Kantian criterion of justice was found in reinterpreting “freedom” in terms not merely of absence of restraint but in terms of attainment of individual perfection. It is this latter trend with which we are concerned in the present case and this holds good even today. As pointed out above, after the Second World War, in the form of the UN Charter and thereafter there is more emphasis on the attainment of individual perfection. In that united sense at least there is a revival of the natural law theory of justice. Blackstone, in the opening pages in his “Vattelian Fashion” said that the principal aim of society “is to protect individuals in the enjoyment of those absolute rights which were vested in them by the immutable laws of nature….”
97) Thus, right of choice and right of self determination were accepted as facets of human dignity. It was also emphasised that in certain cases, like the case at hand (that of transgenders), recognition of this aspect of human dignity would yield happiness to the individuals and, at the same time, also be in public good.
98) Advancement in conceptualising the doctrine of human dignity took place in the case of Shabnam v. Union of India & Ors.35 wherein this Court has gone to the extent of protecting certain rights of death convicts by holding that they cannot be executed till they exhaust all available constitutional and statutory remedies. In the process, the Court held as under: “
“15. This right to human dignity has many elements. First and foremost, human dignity is the dignity of each human being ‘as a human being’. Another element, which needs to be highlighted, in the context of the present case, is that human dignity is infringed if a person’s life, physical or mental welfare is harmed. It is in this sense torture, humiliation, forced labour, etc. all infringe on human dignity. It is in this context many rights of the accused derive from his dignity as a human being.
These may include the presumption that every person is innocent until proven guilty; the right of the accused to a fair trial as well as speedy trial; right of legal aid, all part of human dignity. Even after conviction, when a person is spending prison life, allowing humane conditions in jail is part of human dignity. Prisons reforms or Jail reforms measures to make convicts a reformed person so that they are able to lead normal life and assimilate in the society, after serving the jail term, are motivated by human dignity jurisprudence.
16. In fact, this principle of human dignity has been used frequently by Courts in the context of considering the death penalty itself. Way back in the year 1972, the United States Supreme Court kept in mind this aspect in the case of Furman v. Georgia 408 US 238 (1972). The Court, speaking through Brennan, J., while considering the application of Eighth Amendment’s prohibition on cruel and unusual punishments, summed up the previous jurisprudence on the Amendment as ‘prohibit(ing) the infliction of uncivilized and inhuman punishments. The State, even as it punishes, must treat its members with respect for their intrinsic worth as human beings. A punishment is ‘cruel and unusual’, therefore, if it does not comport with human dignity’.
In Gregg v. Georgia 428 US 153 (1976), that very Court, again through Brennan, J., considered that ‘the fatal constitutional infirmity in the punishment of death is that it treats “members of the human race as non-humans, as objects to be toyed with an discarded. (It is), thus, inconsistent with the fundamental premise of the clause that even the vilest criminal remains a human being possessed of common human dignity’. The Canadian Supreme Court, the Hungarian Constitutional Court and the South African Supreme Court have gone to the extent of holding that capital punishment constitutes a serious impairment of human dignity and imposes a limitation on the essential content of the fundamental rights to life and human dignity and on that touchstone declaring that dignity as unconstitutional.”
99) Next judgment in this line of cases would be that of Jeeja Ghosh & Another v. Union of India & Ors.36 wherein the Court, while expanding the jurisprudential basis, outlined three models of dignity which have been discussed by us above. These were referred to while explaining the normative role of human dignity, alongside, in the following manner:
“37. The rights that are guaranteed to differently-abled persons under the 1995 Act, are founded on the sound principle of human dignity which is the core value of human right and is treated as a significant facet of right to life and liberty. Such a right, now treated as human right of the persons who are disabled, has it roots in Article 21 of the Constitution. Jurisprudentially, three types of models for determining the content of the constitutional value of human dignity are recognised.
These are:
(i) Theological Models,
(ii) Philosophical Models, and
(iii) Constitutional Models. Legal scholars were called upon to determine the theological basis of human dignity as a constitutional value and as a constitutional right. Philosophers also came out with their views justifying human dignity as core human value. Legal understanding is influenced by theological and philosophical views, though these two are not identical. Aquinas and Kant discussed the jurisprudential aspects of human dignity based on the aforesaid philosophies. Over a period of time, human dignity has found its way through constitutionalism, whether written or unwritten.
Even right to equality is interpreted based on the value of human dignity. Insofar as India is concerned, we are not even required to take shelter under theological or philosophical theories. We have a written Constitution which guarantees human rights that are contained in Part III with the caption “Fundamental Rights”. One such right enshrined in Article 21 is right to life and liberty. Right to life is given a purposeful meaning by this Court to include right to live with dignity. It is the purposive interpretation which has been adopted by this Court to give a content of the right to human dignity as the fulfilment of the constitutional value enshrined in Article 21. Thus, human dignity is a constitutional value and a constitutional goal. What are the dimensions of constitutional value of human dignity?
It is beautifully illustrated by Aharon Barak (former Chief Justice of the Supreme Court of Israel) in the following manner: “The constitutional value of human dignity has a central normative role. Human dignity as a constitutional value is the factor that unites the human rights into one whole. It ensures the normative unity of human rights. This normative unity is expressed in the three ways: first, the value of human dignity serves as a normative basis for constitutional rights set out in the Constitution; second, it serves as an interpretative principle for determining the scope of constitutional rights, including the right to human dignity; third, the value of human dignity has an important role in determining the proportionality of a statute limiting a constitutional right.”
38. All the three goals of human dignity as a constitutional value are expanded by the author in a scholarly manner. Some of the excerpts thereof, are reproduced below which give a glimpse of these goals: “The first role of human dignity as a constitutional value is expressed in the approach that it comprises the foundation for all of the constitutional rights. Human dignity is the central argument for the existence of human rights.
It is the rationale for them all. It is the justification for the existence of rights. According to Christoph Enders, it is the constitutional value that determines that every person has the right to have rights… The second role of human dignity as a constitutional value is to provide meaning to the norms of the legal system. According to purposive interpretation, all of the provisions of the Constitution, and particularly all of the rights in the constitutional bill of rights, are interpreted in light of human dignity… Lastly, human dignity as a constitutional value influences the development of the common law. Indeed, where common law is recognised, Judges have the duty to develop it, and if necessary, modify it, so that it expresses constitutional values, including the constitutional value of human dignity.
To the extent that common law determines rights and duties between individuals, it might limit the human dignity of one individual and protect the human dignity of the other.” 100) The concept was developed and expanded further in K.S. Puttaswamy. The Court held that privacy postulates the reservation of a private space for an individual, described as the right to be let alone, as a concept founded on autonomy of the individual. In this way, right to privacy has been treated as a postulate of human dignity itself. While defining so, the Court also remarked as under:
“298. Privacy of the individual is an essential aspect of dignity. Dignity has both an intrinsic and instrumental value. As an intrinsic value, human dignity is an entitlement or a constitutionally protected interest in itself. In its instrumental facet, dignity and freedom are inseparably intertwined, each being a facilitative tool to achieve the other. The ability of the individual to protect a zone of privacy enables the realisation of the full value of life and liberty… The family, marriage, procreation and sexual orientation are all integral to the dignity of the individual. Above all, the privacy of the individual recognises an inviolable right to determine how freedom shall be exercised…”
101) This concept of dignity took a leap forwarded in the case of Common Cause v. Union of India37 pertaining to passive euthanasia. Though this right was earlier recognised in Aruna Ramachandra Shanbaug v. Union of India & Ors.38, a totally new dimension was given to this right, based on freedom of choice which is to be given to an individual accepting his dignity. There were four concurring opinions. In one of the opinions39, the aspects of dignity are succinctly brought out in the following manner: “154. Dignity of an individual has been internationally recognised as an important facet of human rights in the year 1948 itself with the enactment of the Universal Declaration of Human Rights. Human dignity not only finds place in the Preamble of this important document but also in Article 1 of the same. It is well known that the principles set out in UDHR are of paramount importance and are given utmost weightage while interpreting human rights all over the world. The first and foremost responsibility fixed upon the State is the protection of human dignity without which any other right would fall apart. Justice Brennan in his book The Constitution of the United States: Contemporary Ratification has referred to the Constitution as “a sparkling vision of the supremacy of the human dignity of every individual”. 155. In fact, in Christine Goodwin v. United Kingdom the European Court of Human Rights, speaking in the context of the Convention for the Protection of Human Rights and Fundamental Freedoms, has gone to the extent of stating that “the very essence of the Convention is respect for human dignity and human freedom”. In the South African case of S. v. Makwanyane, O’Regan, J. stated in the Constitutional Court that “without dignity, human life is substantially diminished”.
xx xx xx
157. The concept and value of dignity requires further elaboration since we are treating it as an inextricable facet of right to life that respects all human rights that a person enjoys. Life is basically self-assertion. In the life of a person, conflict and dilemma are expected to be normal phenomena. Oliver Wendell Holmes, in one of his addresses, quoted a line from a Latin poet who had uttered the message, “Death plucks my ear and says, Live- I am coming”. That is the significance of living. But when a patient really does not know if he/she is living till death visits him/her and there is constant suffering without any hope of living, should one be allowed to wait?
Should she/he be cursed to die as life gradually ebbs out from her/his being? Should she/he live because of innovative medical technology or, for that matter, should he/she continue to live with the support system as people around him/her think that science in its progressive invention may bring about an innovative method of cure? To put it differently, should he/she be “Guinea pig” for some kind of experiment? The answer has to be an emphatic “No” because such futile waiting mars the pristine concept of life, corrodes the essence of dignity and erodes the fact of eventual choice which is pivotal to privacy.
xx xx xx
159. In Mehmood Nayyar Azam v. State of Chhattisgarh, a two-Judge Bench held thus: (SCC p. 6, para 1) “1. … Albert Schweitzer, highlighting on Glory of Life, pronounced with conviction and humility, “the reverence of life offers me my fundamental principle on morality”. The aforesaid expression may appear to be an individualistic expression of a great personality, but, when it is understood in the complete sense, it really denotes, in its conceptual essentiality, and connotes, in its macrocosm, the fundamental perception of a thinker about the respect that life commands.
The reverence of life is insegregably associated with the dignity of a human being who is basically divine, not servile. A human personality is endowed with potential infinity and it blossoms when dignity is sustained. The sustenance of such dignity has to be the superlative concern of every sensitive soul. The essence of dignity can never be treated as a momentary spark of light or, for that matter, “a brief candle”, or “a hollow bubble”. The spark of life gets more resplendent when man is treated with dignity sans humiliation, for every man is expected to lead an honourable life which is a splendid gift of “creative intelligence”.”
xx xx xx
166. The purpose of saying so is only to highlight that the law must take cognizance of the changing society and march in consonance with the developing concepts. The need of the present has to be served with the interpretative process of law. However, it is to be seen how much strength and sanction can be drawn from the Constitution to consummate the changing ideology and convert it into a reality. The immediate needs are required to be addressed through the process of interpretation by the Court unless the same totally falls outside the constitutional framework or the constitutional interpretation fails to recognise such dynamism.
The Constitution Bench in Gian Kaur [Gian Kaur v. State of Punjab, (1996) 2 SCC 648 : 1996 SCC (Cri) 374] , as stated earlier, distinguishes attempt to suicide and abetment of suicide from acceleration of the process of natural death which has commenced. The authorities, we have noted from other jurisdictions, have observed the distinctions between the administration of lethal injection or certain medicines to cause painless death and non-administration of certain treatment which can prolong the life in cases where the process of dying that has commenced is not reversible or withdrawal of the treatment that has been given to the patient because of the absolute absence of possibility of saving the life.
To explicate, the first part relates to an overt act whereas the second one would come within the sphere of informed consent and authorised omission. The omission of such a nature will not invite any criminal liability if such action is guided by certain safeguards. The concept is based on non-prolongation of life where there is no cure for the state the patient is in and he, under no circumstances, would have liked to have such a degrading state. The words “no cure” have to be understood to convey that the patient remains in the same state of pain and suffering or the dying process is delayed by means of taking recourse to modern medical technology.
It is a state where the treating physicians and the family members know fully well that the treatment is administered only to procrastinate the continuum of breath of the individual and the patient is not even aware that he is breathing. Life is measured by artificial heartbeats and the patient has to go through this undignified state which is imposed on him. The dignity of life is denied to him as there is no other choice but to suffer an avoidable protracted treatment thereby thus indubitably casting a cloud and creating a dent in his right to live with dignity and face death with dignity, which is a preserved concept of bodily autonomy and right to privacy. In such a stage, he has no old memories or any future hopes but he is in a state of misery which nobody ever desires to have.
Some may also silently think that death, the inevitable factum of life, cannot be invited. To meet such situations, the Court has a duty to interpret Article 21 in a further dynamic manner and it has to be stated without any trace of doubt that the right to life with dignity has to include the smoothening of the process of dying when the person is in a vegetative state or is living exclusively by the administration of artificial aid that prolongs the life by arresting the dignified and inevitable process of dying. Here, the issue of choice also comes in. Thus analysed, we are disposed to think that such a right would come within the ambit of Article 21 of the Constitution.” 102) In the other opinion40, four facets of euthanasia were discussed, namely:
(i) philosophy of euthanasia,
(ii) morality of euthanasia,
(iii) dignity in euthanasia, and
(iv) economics of euthanasia.
While discussing dignity in euthanasia, the three models of dignity, namely, theological, philosophical and constitutional model, were highlighted. Thereafter, postulates of dignity have been explained in the following manner:
“292. Aharon Barak, former Chief Justice of the Supreme Court of Israel, attributes two roles to the concept of human dignity as a constitutional value, which are:
292.1. Human dignity lays a foundation for all the human rights as it is the central argument for the existence of human rights.
292.2. Human dignity as a constitutional value provides meaning to the norms of the legal system. In the process, one can discern that the principle of purposive interpretation exhorts us to interpret all the rights given by the Constitution, in the light of the human dignity. In this sense, human dignity influences the purposive interpretation of the Constitution. Not only this, it also influences the interpretation of every sub-constitutional norm in the legal system. Moreover, human dignity as a constitutional value also influences the development of the common law.
xx xx xx
295. Dworkin, being a philosopher-jurist, was aware of the idea of a Constitution and of a constitutional right to human dignity. In his book, Taking Rights Seriously, he noted that everyone who takes rights seriously must give an answer to the question why human rights vis-à-vis the State exist. According to him, in order to give such an answer one must accept, as a minimum, the idea of human dignity. As he writes: “Human dignity … associated with Kant, but defended by philosophers of different schools, supposes that there are ways of treating a man that are inconsistent with recognising him as a full member of the human community, and holds that such treatment is profoundly unjust.”
296. In his Book, Is Democracy Possible Here?42 Dworkin develops two principles about the concept of human dignity. First principle regards the intrinsic value of every person viz. every person has a special objective value which value is not only important to that person alone but success or failure of the lives of every person is important to all of us. The second principle, according to Dworkin, is that of personal responsibility. According to this principle, every person has the responsibility for success in his own life and, therefore, he must use his discretion regarding the way of life that will be successful from his point of view. Thus, Dworkin’s jurisprudence of human dignity is founded on the aforesaid two principles which, together, not only define the basis but the conditions for human dignity. Dworkin went on to develop and expand these principles in his book, Justice for Hedgehogs (2011)43.
297. When speaking of rights, it is impossible to envisage it without dignity. In his pioneering and all-inclusive Justice for Hedgehogs, he proffered an approach where respect for human dignity, entails two requirements; first, selfrespect i.e. taking the objective importance of one’s own life seriously; this represents the free will of the person, his capacity to think for himself and to control his own life and second, authenticity i.e. accepting a “special, personal responsibility for identifying what counts as success” in one’s own life and for creating that life “through a coherent narrative” that one has chosen44. According to Dworkin, these principles form the fundamental criteria supervising what we should do in order to live well.45
They further explicate the rights that individuals have against their political community,46 and they provide a rationale for the moral duties we owe to others. This notion of dignity, which Dworkin gives utmost importance to, is indispensable to any civilised society. It is what is constitutionally recognised in our country and for good reason. Living well is a moral responsibility of individuals; it is a continuing process that is not a static condition of character but a mode that an individual constantly endeavours to imbibe. A life lived without dignity, is not a life lived at all for living well implies a conception of human dignity which Dworkin interprets includes ideals of self-respect and authenticity.”
103) In summation, it can be said that the concept of human dignity dates back to thousands of years. Historically, human dignity, as a concept, found its origin in different religions which is held to be an important component of their theological approach. Jurists have given this approach as ‘theological model’ of dignity. It is primarily based on the premise that human beings are the creation of God and cannot be treated as mere material beings. Human identity is more ethical than spiritual because man is creation of God; harm to a human being is harm to God. God, thus, wishes to grant human being recognition, dignity and authority. It is also religious belief that God is rational and determines his goals for himself. Likewise, human being created by God too is rational and determines his own goal. Therefore, man has freedom of will. A couple of centuries ago, philosophical approach was given to the conception of human dignity. This sphere was headed by German Philosopher Immanuel Kant whose moral theory is divided into two parts: ethics and right. According to Kant, a person acts ethically when he acts by force of a duty that a rational agent self-legislates onto his own will. Thus, he talked of free will of the human being.
For Kant, ethics include duties of oneself (for example – to develop one’s talents) and to others (for example – to contribute to their happiness). This ability is the human dignity of man. Philosophical approach, thus, is metaethical one, which is a journey from ‘human being’ and ‘remaining human’. This is explained by Professor Upendra Baxi as the relationship between ‘self’, ‘others’ and ‘society’. In this philosophical sense, dignity is ‘respect’ for an individual person based on the principle of freedom and capacity of making choices and a good or just social order is one which respects dignity via assuring ‘contexts’ and ‘conditions’ as the ‘source of free and informed choice’.
To put it philosophically, each individual has a right to live her life the way she wants, without any subjugation. One can rule others, but then it is never noble. It is immoral because the other is not a means to you, the other is an end to herself. Kant also maintains that to use the other as a means is the basic immoral act. Everything else that is immoral is immoral because of this, so this should be the criterion: Are you using the other as a means? Someone has put this remarkably in the following words: “Alexander the Great is not noble, only Gautam the Buddha is noble, for the simple reason that Buddha has no rule over others but he is a matter of himself. There is no part of his being which is not in tune with him. He has come to attain absolute harmony. There is no conflict in him, there is a reign of absolute peace. And his consciousness is supreme, nothing is above it – no instinct, no intellect, nothing is higher than his consciousness.”
104) Historically, a transition has taken place into the idea of dignity by transforming the amalgam of theological approach (man as creation of God deserving dignity) and philosophical approach based on morality, by elevating human dignity as a constitutional norm attaching constitutional value to it. It is a transition from ‘respect’ to ‘right’ by making respect as enforceable right. The manner in which it has happened in India has been traced above.
105) From the aforesaid discussion, it follows that dignity as a jurisprudential concept has now been well defined by this Court. Its essential ingredients can be summarised as under: The basic principle of dignity and freedom of the individual is an attribute of natural law which becomes the right of all individuals in a constitutional democracy. Dignity has a central normative role as well as constitutional value. This normative role is performed in three ways:
First, it becomes basis for constitutional rights;
Second, it serves as an interpretative principle for determining the scope of constitutional rights; and,
Third, it determines the proportionality of a statute limiting a constitutional right. Thus, if an enactment puts limitation on a constitutional right and such limitation is disproportionate, such a statute can be held to be unconstitutional by applying the doctrine of proportionality.
106) As per Dworkin, there are two principles about the concept of human dignity. First principle regards an ‘intrinsic value’ of every person, namely, every person has a special objective value, which value is not only important to that person alone but success or failure of the lives of every person is important to all of us. It can also be described as self respect which represents the free will of the person, her capacity to think for herself and to control her own life. The second principle is that of ‘personal responsibility’, which means every person has the responsibility for success in her own life and, therefore, she must use her discretion regarding the way of life that will be successful from her point of view.
107) Sum total of this exposition is well defined by Professor Baxi by explaining that as per the aforesaid view, dignity is to be treated as ’empowerment’ which makes a triple demand in the name of ‘respect’ for human dignity, namely:
(i) respect for one’s capacity as an agent to make one’s own free choices;
(ii) respect for the choices so made; and
(iii) respect for one’s need to have a context and conditions in which one can operate as a source of free and informed choice.
108) In this entire formulation, ‘respect’ for an individual is the fulcrum, which is based on the principle of freedom and capacity to make choices and a good or just social order is one which respects dignity via assuring ‘contexts’ and ‘conditions’ as the ‘source of free and informed choice’.
109) The aforesaid discourse on the concept of human dignity is from an individual point of view. That is the emphasis of the petitioners as well. That would be one side of the coin. A very important feature which the present case has brought into focus is another dimension of human dignity, namely, in the form of ‘common good’ or ‘public good’. Thus, our endeavour here is to give richer and more nuanced understanding to the concept of human dignity. Here, dignity is not limited to an individual and is to be seen in an individualistic way. A reflection on this facet of human dignity was stated in National Legal Services Authority (Transgenders’ case), which can be discerned from the following discussion:
“103. A corollary of this development is that while so long the negative language of Article 21 and use of the word “deprived” was supposed to impose upon the State the negative duty not to interfere with the life or liberty of an individual without the sanction of law, the width and amplitude of this provision has now imposed a positive obligation (Vincent Panikurlangara v. Union of India) upon the State to take steps for ensuring to the individual a better enjoyment of his life and dignity e.g.:
(i) Maintenance and improvement of public health (Vincent Panikurlangara v. Union of India).
(ii) Elimination of water and air pollution (M.C. Mehta v. Union of India).
(iii) Improvement of means of communication (State of H.P. v. Umed Ram Sharma).
(iv) Rehabilitation of bonded labourers (Bandhua Mukti Morcha v. Union of India).
(v) Providing human conditions in prisons (Sher Singh v. State of Punjab) and protective homes (Sheela Barse v. Union of India).
(vi) Providing hygienic condition in a slaughterhouse (Buffalo Traders Welfare Assn. v. Maneka Gandhi). 104. The common golden thread which passes through all these pronouncements is that Article 21 guarantees enjoyment of life by all citizens of this country with dignity, viewing this human right in terms of human development. 105. The concepts of justice social, economic and political, equality of status and of opportunity and of assuring dignity of the individual incorporated in the Preamble, clearly recognise the right of one and all amongst the citizens of these basic essentials designed to flower the citizen’s personality to its fullest. The concept of equality helps the citizens in reaching their highest potential. Thus, the emphasis is on the development of an individual in all respects.”
110) Christopher McCrudden, an Oxford Academic, in his article ‘Human Dignity and Judicial Interpretation of Human Rights’ traces the evolution of concept of human dignity. In substance, his analysis is that in the early stages of social evolution, human dignity was understood as a concept associated with ‘status’. Only those individuals were considered worthy of respect who enjoyed a certain status within the social construct.
Though one finds statements about dignity of humans as human beings on account of the human being the highest creation of God and his possession of mind and the power of reason in the Oration of Marcus Tullius Cicero, a Roman Politician and Philosopher (63 BC), and in the works of Pico della 47 Published in the European Journal of International Law on September 01, 2008 Mirandola, a Reformation Humanist (1486) ‘On the dignity of man’, yet there existed human beings who were not considered as human beings. There were slaves who were treated at par with animals.
111) Kant expounded the theory that humans should be treated as an end in themselves and not merely as a means to an end with ability to choose their destiny. Emphasis was laid on the intrinsic worth of the human being. Based on this philosophy emerged the initial declaration of rights. Kant wrote thus: “Humanity itself is a dignity; for a human being cannot be used merely as a means by any human being (…) but must always be used at the same time as an end. It is just in this that his dignity (personality) consists, by which he raises himself above all other beings in the world that are not human beings and yet can be used, and so overall things.”
112) Charles Bernard Renouvier, a French Philosopher, said:
“Republic is a State which best reconciles dignity of individual with dignity of everyone.”
113) Dignity extended to all citizens involves the idea of communitarism. A little earlier in 1798, Friedrich Schiller, a German poet of freedom and philosophy, brought out the connection between dignity and social condition in his work “Wurde des Menschen”. He said “(g)ive him food and shelter; when you have covered his nakedness, dignity will follow by itself.” It was during the period that abolition of slavery became an important political agenda. Slavery was considered as an affront to human dignity.
114) The Universal Declaration of Human Rights (UDHR) recorded in the Preamble recognition of the inherent dignity and of the equal and inalienable rights of all members of the human family as the foundation of freedom, justice and peace. It included freedom from fear and want as amongst the highest aspirations of the common people.
This is of course subject to resources of each State. But the realisation is contemplated through national effort and international cooperation. Evidently, the UDHR adopts a substantive or communitarian concept of human dignity. The realisation of intrinsic worth of every human being, as a member of society through national efforts as an indispensable condition has been recognised as an important human right. Truly speaking, this is directed towards the deprived, downtrodden and have nots.
115) We, therefore, have to keep in mind humanistic concept of human dignity which is to be accorded to a particular segment of the society and, in fact, a large segment. Their human dignity is based on the socio-economic rights that are read in to the fundamental rights, as already discussed above.
116) When we read socio-economic rights into human dignity, the community approach also assumes importance along with individualistic approach to human dignity. It has now been well recognised that at its core, human dignity contains three elements, namely, intrinsic value, autonomy and community value. These are known as core values of human dignity. These three elements can assist in structuring legal reasoning and justifying judicial choices in ‘hard cases’. It has to be borne in mind that human dignity is a constitutional principle, rather than free standing fundamental rights. Insofar as intrinsic value is concerned, here human dignity is linked to the nature of being. We may give brief description of these three contents of the idea of human dignity as below:
(I) Intrinsic Value:
The uniqueness of human kind is the product of a combination of inherent traits and features – including intelligence, sensibility, and the ability to communicate – that give humans a special status in the world, distinct from other species.48 The intrinsic value of all individuals results in two basic postulates: anti-utilitarian and anti-authoritarian. The former consists of the formulation of Kant’s categorical imperative that every individual is an end in him or herself, not a means for collective goals or the purposes of others. The latter is synthesized in the idea that the State exists for the individual, not the other way around. As for its legal implications, intrinsic value is the origin of a set of fundamental rights. The first of these rights is the right to life, a basic precondition for the enjoyment of any other right.
A second right directly related to the intrinsic value of each and every individual is equality before and under the law. All individuals are of equal value and, therefore, deserve equal respect and concern. This means not being discriminated against due to race, colour, ethnic or national origin, sex, age or mental capacity (the right to non-discrimination), as well as respect for cultural, religious, or linguistic diversity (the right to recognition). Human dignity fulfills only part of the content of the idea of equality, and in many situations it may be acceptable to differentiate among people. In the contemporary world, this is particularly at issue in cases involving affirmative action and the rights of religious minorities. Intrinsic value also leads to the right to integrity, both physical and mental.
The right to physical integrity includes the prohibition of torture, slave labour, and degrading treatment or punishment. Discussions on life imprisonment, interrogation techniques, and prison conditions take place within the scope of this right. The right to mental integrity comprises the right to personal honour and image and includes the right to privacy.
(II) Autonomy:
Autonomy is the ethical element of human dignity. It is the foundation of the free will of individuals, which entitles them to pursue the ideals of living well and having a good life in their own ways. The central notion is that of self-determination: An autonomous person establishes the rules that will govern his or her life. Kantian conception of autonomy is the will governed by the moral law (moral autonomy). Here, we are concerned with personal autonomy, which is value neutral and means the free exercise of the will according to one’s own values, interests, and desires. Autonomy requires the fulfillment of certain conditions, such as reason (the mental capacity to make informed decisions), independence (the absence of coercion, manipulation and severe want), and choice (the actual existence of alternatives).
Autonomy, thus, is the ability to make personal decisions and choices in life based on one’s conception of the good, without ndue external influences. As for its legal implications, autonomy underlies a set of fundamental rights associated with democratic constitutionalism, including basic freedoms (private autonomy) and the right of political participation (public autonomy). It would be pertinent to emphasise here that with the rise of the welfare state, many countries in the world (and that includes India) also consider a fundamental right to minimum living conditions (the existential minimum) in the balancing that results into effective autonomy. Thus, there are three facets of autonomy, namely: private autonomy, public autonomy and the existential minimum. Insofar as the last component is concerned, it is also referred to as social minimum or the basic right to the provision of adequate living conditions has its roots in right to equality as well. In fact, equality, in a substantive sense, and especially autonomy (both private and public), are dependent on the fact that individuals are “free from want,” meaning that their essential needs are satisfied.
To be free, equal, and capable of exercising responsible citizenship, individuals must pass minimum thresholds of well-being, without which autonomy is a mere fiction. This requires access to some essential utilities, such as basic education and health care services, as well as some elementary necessities, such as food, water, clothing, and shelter. The existential minimum, therefore, is the core content of social and economic rights. This concept of minimum social right is protected by the Court, time and again.
(III) Community Value:
This element of human dignity as community value relates to the social dimension of dignity. The contours of human dignity are shaped by the relationship of the individual with others, as well as with the world around him. English poet John Donne expresses the same sentiments when he says ‘no man is an island, entire of itself’49.
The individual, thus, lives within himself, within a community, and within a state. His personal autonomy is constrained by the values, rights, and morals of people who are just as free and equal as him, as well as by coercive regulation. Robert Post identified three distinct forms of social order: community (a “shared world of common faith and fate”), management (the instrumental organization of social life through law to achieve specific objectives), and democracy (an arrangement that embodies the purpose of individual and collective self-determination. These three forms of social order presuppose and depend on each other, but are also in constant tension. Dignity as a community value, therefore, emphasises the role of the state and community in establishing collective goals and restrictions on individual freedoms and rights on behalf of a certain idea of the good life. The relevant question here is in what circumstances and to what degree should these actions be regarded as legitimate in a constitutional democracy?
The liberal predicament that the state must be neutral with regard to different conceptions of the good in a plural society is not incompatible, of course, with limitation resulting from the necessary coexistence of different views and potentially conflicting rights. Such interferences, however, must be justified on grounds of a legitimate idea of justice, an “overlapping consensus”50 that can be shared by most individuals and groups. Whenever such tension arises, the task of balancing is to be achieved by the Courts. We would like to highlight one more significant feature which the issues involved in the present case bring about. It is the balancing of two facets of dignity of the same individual.
Whereas, on the one hand, right of personal autonomy is a part of dignity (and right to privacy), another part of dignity of the same individual is to lead a dignified life as well (which is again a facet of Article 21 of the Constitution). Therefore, in a scenario where the State is coming out with welfare schemes, which strive at giving dignified life in harmony with human dignity and in the process some aspect of autonomy is sacrificed, the balancing of the two becomes an important task which is to be achieved by the Courts. For, there cannot be undue intrusion into the autonomy on the pretext of conferment of economic benefits.
Precisely, this very exercise of balancing is undertaken by the Court in resolving the complex issues raised in the petitions.
Doctrine of Proportionality:
117) As noted above, whenever challenge is laid to an action of the State on the ground that it violates the right to privacy, the action of the State is to be tested on the following parameters:
(a) the action must be sanctioned by law;
(b) the proposed action must be necessary in a democratic society for a legitimate aim; and
(c) the extent of such interference must be proportionate to the need for such interference. 118) Doctrine of proportionality was explained by the Constitution Bench judgment of this Court in Modern Dental College and Research Centre & Ors. v. State of Madhya Pradesh & Ors.51. In the first instance, therefore, it would be apt to reproduce the said discussion:
“60. …Thus, while examining as to whether the impugned provisions of the statute and rules amount to reasonable restrictions and are brought out in the interest of the general public, the exercise that is required to be undertaken is the balancing of fundamental right to carry on occupation on the one hand and the restrictions imposed on the other hand. This is what is known as “doctrine of proportionality”. Jurisprudentially, “proportionality” can be defined as the set of rules determining the necessary and sufficient conditions for limitation of a constitutionally protected right by a law to be constitutionally permissible. According to Aharon Barak (former Chief Justice, Supreme Court of Israel), there are four sub-components of proportionality which need to be satisfied [Aharon Barak, Proportionality: Constitutional Rights and Their Limitation (Cambridge University Press 2012)], a limitation of a constitutional right will be constitutionally permissible if:
(i) it is designated for a proper purpose;
(ii) the measures undertaken to effectuate such a limitation are rationally connected to the fulfilment of that purpose;
(iii) the measures undertaken are necessary in that there are no alternative measures that may similarly achieve that same purpose with a lesser degree of limitation; and finally
(iv) there needs to be a proper relation (“proportionality stricto sensu” or “balancing”) between the importance of achieving the proper purpose and the social importance of preventing the limitation on the constitutional right.
61. Modern theory of constitutional rights draws a fundamental distinction between the scope of the constitutional rights, and the extent of its protection. Insofar as the scope of constitutional rights is concerned, it marks the outer boundaries of the said rights and defines its contents. The extent of its protection prescribes the limitations on the exercises of the rights within its scope.
In that sense, it defines the justification for limitations that can be imposed on such a right.
62. It is now almost accepted that there are no absolute constitutional rights [ Though, debate on this vexed issue still continues and some constitutional experts claim that there are certain rights, albeit very few, which can still be treated as “absolute”.
Examples given are:(a) Right to human dignity which is inviolable,(b) Right not to be subjected to torture or to inhuman or degrading treatment or punishment. Even in respect of such rights, there is a thinking that in larger public interest, the extent of their protection can be diminished. However, so far such attempts of the States have been thwarted by the judiciary.] and all such rights are related. As per the analysis of Aharon Barak [Aharon Barak, Proportionality: Constitutional Rights and Their Limitation (Cambridge University Press 2012).] , two key elements in developing the modern constitutional theory of recognising positive constitutional rights along with its limitations are the notions of democracy and the rule of law.
Thus, the requirement of proportional limitations of constitutional rights by a subconstitutional law i.e. the statute, is derived from an interpretation of the notion of democracy itself. Insofar as the Indian Constitution is concerned, democracy is treated as the basic feature of the Constitution and is specifically accorded a constitutional status that is recognised in the Preamble of the Constitution itself. It is also unerringly accepted that this notion of democracy includes human rights which is the cornerstone of Indian democracy. Once we accept the aforesaid theory (and there cannot be any denial thereof), as a fortiori, it has also to be accepted that democracy is based on a balance between constitutional rights and the public interests. In fact, such a provision in Article 19 itself on the one hand guarantees some certain freedoms in clause (1) of Article 19 and at the same time empowers the State to impose reasonable restrictions on those freedoms in public interest. This notion accepts the modern constitutional theory that the constitutional rights are related.
This relativity means that a constitutional licence to limit those rights is granted where such a limitation will be justified to protect public interest or the rights of others. This phenomenon- of both the right and its limitation in the Constitution- exemplifies the inherent tension between democracy’s two fundamental elements. On the one hand is the right’s element, which constitutes a fundamental component of substantive democracy; on the other hand is the people element, limiting those very rights through their representatives. These two constitute a fundamental component of the notion of democracy, though this time in its formal aspect. How can this tension be resolved? The answer is that this tension is not resolved by eliminating the “losing” facet from the Constitution. Rather, the tension is resolved by way of a proper balancing of the competing principles. This is one of the expressions of the multi-faceted nature of democracy. Indeed, the inherent tension between democracy’s different facets is a “constructive tension”.
It enables each facet to develop while harmoniously coexisting with the others. The best way to achieve this peaceful coexistence is through balancing between the competing interests. Such balancing enables each facet to develop alongside the other facets, not in their place. This tension between the two fundamental aspects- rights on the one hand and its limitation on the other hand- is to be resolved by balancing the two so that they harmoniously coexist with each other. This balancing is to be done keeping in mind the relative social values of each competitive aspects when considered in proper context.
63. In this direction, the next question that arises is as to what criteria is to be adopted for a proper balance between the two facets viz. the rights and limitations imposed upon it by a statute.
Here comes the concept of “proportionality”, which is a proper criterion. To put it pithily, when a law limits a constitutional right, such a limitation is constitutional if it is proportional. The law imposing restrictions will be treated as proportional if it is meant to achieve a proper purpose, and if the measures taken to achieve such a purpose are rationally connected to the purpose, and such measures are necessary. This essence of doctrine of proportionality is beautifully captured by Dickson, C.J. of Canada in R. v. Oakes [R. v. Oakes, (1986) 1 SCR 103 (Can SC)] , in the following words (at p. 138): ‘To establish that a limit is reasonable and demonstrably justified in a free and democratic society, two central criteria must be satisfied.
First, the objective, which the measures, responsible for a limit on a Charter right or freedom are designed to serve, must be “of” sufficient importance to warrant overriding a constitutional protected right or freedom … Second … the party invoking Section 1 must show that the means chosen are reasonable and demonstrably justified. This involves “a form of proportionality test…” Although the nature of the proportionality test will vary depending on the circumstances, in each case courts will be required to balance the interests of society with those of individuals and groups.
There are, in my view, three important components of a proportionality test. First, the measures adopted must be … rationally connected to the objective. Second, the means … should impair “as little as possible” the right or freedom in question … Third, there must be a proportionality between the effects of the measures which are responsible for limiting the Charter right or freedom, and the objective which has been identified as of “sufficient importance”. The more severe the deleterious effects of a measure, the more important the objective must be if the measure is to be reasonable and demonstrably justified in a free and democratic society.’
64. The exercise which, therefore, is to be taken is to find out as to whether the limitation of constitutional rights is for a purpose that is reasonable and necessary in a democratic society and such an exercise involves the weighing up of competitive values, and ultimately an assessment based on proportionality i.e. balancing of different interests.
65. We may unhesitatingly remark that this doctrine of proportionality, explained hereinabove in brief, is enshrined in Article 19 itself when we read clause (1) along with clause (6) thereof. While defining as to what constitutes a reasonable restriction, this Court in a plethora of judgments has held that the expression “reasonable restriction” seeks to strike a balance between the freedom guaranteed by any of the sub-clauses of clause (1) of Article 19 and the social control permitted by any of the clauses (2) to (6).
It is held that the expression “reasonable” connotes that the limitation imposed on a person in the enjoyment of the right should not be arbitrary or of an excessive nature beyond what is required in the interests of public. Further, in order to be reasonable, the restriction must have a reasonable relation to the object which the legislation seeks to achieve, and must not go in excess of that object (see P.P. Enterprises v. Union of India).
At the same time, reasonableness of a restriction has to be determined in an objective manner and from the standpoint of the interests of the general public and not from the point of view of the persons upon whom the restrictions are imposed or upon abstract considerations (see Mohd. Hanif Quareshi v. State of Bihar). In M.R.F. Ltd. v. State of Kerala, this Court held that in examining the reasonableness of a statutory provision one has to keep in mind the following factors:
(1) The directive principles of State policy.
(2) Restrictions must not be arbitrary or of an excessive nature so as to go beyond the requirement of the interest of the general public.
(3) In order to judge the reasonableness of the restrictions, no abstract or general pattern or a fixed principle can be laid down so as to be of universal application and the same will vary from case to case as also with regard to changing conditions, values of human life, social philosophy of the Constitution, prevailing conditions and the surrounding circumstances.
(4) A just balance has to be struck between the restrictions imposed and the social control envisaged by Article 19(6).
(5) Prevailing social values as also social needs which are intended to be satisfied by the restrictions.
(6) There must be a direct and proximate nexus or reasonable connection between the restrictions imposed and the object sought to be achieved. If there is a direct nexus between the restrictions, and the object of the Act, then a strong presumption in favour of the constitutionality of the Act will naturally arise.”
(emphasis in original)
119) We may note at this stage that there is a growing awareness of the practical importance of the principle of proportionality for rights adjudication and it has sparked a wave of academic scholarship as well. The first integrates the doctrine of proportionality into a broader theoretical framework. It is propounded by Robert Alexy, premised on the theory of rights as principles and optimisation requirements52. For Alexy, all norms are either rules or principles.
Constitutional rights are principles, which means that they must be realised to the greatest extent factually and legally possible. For Alexy, the principle of proportionality follows logically from the nature of constitutional rights as principles. On the other hand, Mattias Kumm presented his theory of rights adjudication as Socratic contestation, with proportionality principle at its centre. As per Kumm, proportionality is the doctrinal tool which allows Judges to assess the reasonableness or plausibility, of a policy and thus to determine whether it survives Socratic contestation53. Recently, Kai Moller has proposed another theory, which is an autonomybased theory of what he calls ‘the global model of constitutional rights’, at the core of which lies the obligation of the State to take the autonomy interests of every person adequately into account54. In this process, his understanding of autonomy leads to one consequence, viz., there will often be conflicts of autonomy interests, which have to be resolved in line with each agent’s status as an equal. Here, the proportionality principle becomes the doctrinal tool which guides Judges through the process of resolving those conflicts. One thing is clear from the above, i.e. jurisprudential explanations of proportionality principle. There may be some differences about the approach on the application of proportionality doctrine, it is certain that proportionality has become the lingua franca of judicial systems across borders, concerning the circumstances under which it is appropriate to limit fundamental rights.
120) The proportionality test which is stated in the aforesaid judgment, accepting Justice Barak’s conceptualisation, essentially takes the version which is used by the German Federal Constitutional Court and is also accepted by most theorists of proportionality. According to this test, a measure restricting a right must, first, serve a legitimate goal (legitimate goal stage); it must, secondly, be a suitable means of furthering this goal (suitability or rational connection stage); thirdly, there must not be any less restrictive but equally effective alternative (necessity stage); and fourthly, the measure must not have a disproportionate impact on the right-holder (balancing stage).
121) Many issues arise while undertaking the exercise of proportionality inquiry. At legitimate goal stage, question arises as to what does it mean to speak of the goal of a policy, and what does it mean to require a goal to be legitimate?55 With regard to the suitability and necessity stages, some of the open issues are how to deal with empirical uncertainty: should this lead to wideranging deference to the elected branches?56 At the balancing stage, we have to ask the question of what it means to say that a right is ‘balanced’ against a competing right or public interest. One remarkable feature of the German test is that it tends to push most of the important issues into the last stage, viz., the balancing stage. At the legitimate goal stage, any goal that is legitimate will be accepted. At the suitability stage, even a marginal contribution to the achievement of the goal will suffice. At the necessity stage, it is very rare for a policy to fail because less restrictive alternatives normally come with some disadvantage and cannot, therefore, be considered equally effective. Thus, the balancing stage dominates the legal analysis and is usually determinative of the outcome.
122) In contrast, Canadian Supreme Court has chartered different course while using proportionality test. R. v. Oakes57 (popularly known as Oakes test), has held that the objective must be ‘of sufficient importance to warrant overriding a constitutionally protected right or freedom’; there must be a rational connection between measure and objective; the means must ‘impair “as little as possible” the right or freedom in question’; and finally, ‘there must be a proportionality between the effects of the measures which are responsible for limiting the Charter right or freedom, and the objective which has been identified as of “sufficient importance”‘.
Under this test, arguably more issues are addressed at the earlier stages. Instead of accepting any legitimate goal, Oakes requires a goal ‘of sufficient importance to warrant overriding a constitutionally protected right or freedom’. And the minimal impairment test is different from the German necessity test both in the way in which it is formulated (there is no requirement that the less restrictive measure be equally effective) and in the way it is applied in practice: the Canadian Supreme Court tends to resolve cases at that stage and not, as the German Federal Constitutional Court, at the balancing stage.
123) There is a great debate as to which out of the aforesaid two approaches is a better approach. Some jurists are of the view that the proper application of the German test leads to a practice of constitutional review with two connected problems: first, as pointed about above, usually almost all the moral work is done at the balancing stage, arguably rendering the earlier stages largely useless and throwing doubt on the truth of the popular argument that proportionality is a valuable doctrine partly because it structures the analysis of rights issues in a meaningful way.
Secondly, the balancing act at the final stage is often carried out in an impressionistic fashion which seems to be largely unguided by principle and thus opens the door for subjective, arbitrary and unpredictable judgments encroaching on what ought to be the proper domain of the democratic legislature.
These concerns can, however, be addressed. According to Bilchitz58, first concern can be addressed by focusing on the necessity stage of the test. He takes issue with both the German test – according to which almost all policies are necessary because any alternative policy will usually have some disadvantage which means that it cannot be considered equally effective – and the Canadian minimal impairment test – which, taken seriously, narrows down the range of constitutionally acceptable policies far too much: ‘minimal Writ impairment’ can be read as insisting that only one measure could pass constitutional scrutiny, namely the measure which impairs the right least.59
So the alternatives seem to be either to construct the necessity (minimal impairment) test as filtering out almost nothing or to allow only one policy, thus rendering the elected branches partly superfluous. In order to preserve a meaningful but not unduly strict role for the necessity stage, Bilchitz proposes the following inquiry. First, a range of possible alternatives to the measure employed by the Government must be identified. Secondly, the effectiveness of these measures must be determined individually; the test here is not whether each respective measure realises the governmental objective to the same extent, but rather whether it realises it in a ‘real and substantial manner’.
Thirdly, the impact of the respective measures on the right at stake must be determined. Finally, an overall judgment must be made as to whether in light of the findings of the previous steps, there exists an alternative which is preferable; and this judgment will go beyond the strict meansends assessment favoured by Grimm and the German version of the proportionality test; it will also require a form of balancing to be carried out at the necessity stage.
124) Insofar as second problem in German test is concerned, it can be taken care of by avoiding ‘ad-hoc balancing’ and instead proceeding on some ‘bright-line rules’ i.e. by doing the act of balancing on the basis of some established rule or by creating a sound rule. We may point out that whereas Chandrachud, J. has formulated the test of ‘legitimate state interest’, other two of the Judges, namely, Chelameswar and Sapre, JJ. have used the test of ‘compelling state interest’ and not ‘legitimate state interest’. On the other hand, S.K. Kaul, J. has held that the test to be applied is whether the law satisfies ‘public interest’. Nariman, J., on the other hand, pointed out that the Right to Information Act, 2005 has provided for personal information being disclosed to third parties subject to ‘larger public interest’ being satisfied.
If this test is applied, the result is that one would be entitled to invoke ‘large public interest’ in lieu of ‘legitimate state aim’ or ‘legitimate state interest’, as a permissible restriction on a claim to privacy of an individual – a more lenient test. However, since judgment of Chandrachud, J. is on behalf of himself and three other Judges and S.K. Kaul, J. has also virtually adopted the same test, we can safely adopt the test of ‘legitimate state interest’ as the majority opinion, instead of applying the test of ‘compelling state interest’.
125) In Modern Dental College & Research Centre, four sub components or proportionality which need to be satisfied were taken note of.
These are:
(a) A measure restricting a right must have a legitimate goal (legitimate goal stage).
(b) It must be a suitable means of furthering this goal (suitability or rationale connection stage).
(c) There must not be any less restrictive but equally effective alternative (necessity stage). (d) The measure must not have a disproportionate impact on the right holder (balancing stage). 126) This has been approved in K.S. Puttaswamy as well. Therefore, the aforesaid stages of proportionality can be looked into and discussed. of course, while undertaking this exercise it has also to be seen that the legitimate goal must be of sufficient importance to warrant overriding a constitutionally protected right or freedom and also that such a right impairs freedom as little as possible.
This Court, in its earlier judgments, applied German approach while applying proportionality test to the case at hand. We would like to proceed on that very basis which, however, is tempered with more nuanced approach as suggested by Bilchitz. This, in fact, is the amalgam of German and Canadian approach. We feel that the stages, as mentioned in Modern Dental College & Research Centre and recapitulated above, would be the safe method in undertaking this exercise, with focus on the parameters as suggested by Bilchitz, as this projects an ideal approach that need to be adopted. Issues:
127) After setting the tone of the case, it is now time to specify the precise issues which are involved that need to be decided in these matters:
(1) Whether the Aadhaar Project creates or has tendency to create surveillance state and is, thus, unconstitutional on this ground?
(a) What is the magnitude of protection that needs to be accorded to collection, storage and usage of biometric data?
(b) Whether the Aadhaar Act and Rules provide such protection, including in respect of data minimisation, purpose limitation, time period for data retention and data protection and security?
(2) Whether the Aadhaar Act violates right to privacy and is unconstitutional on this ground? {This issue is considered in the context of Sections 7 and 8 of the Aadhaar Act. Incidental issue of ‘Exclusion’ is also considered here}
(3) Whether children can be brought within the sweep of Sections 7 and 8 of the Aadhaar Act?
(4) Whether the following provisions of the Aadhaar Act and Regulations suffer from the vice of unconstitutionality:
(i) Sections 2(c) and 2(d) read with Section 32
(ii) Section 2(h) read with Section 10 of CIDR
(iii) Section 2(l) read with Regulation 23
(iv) Section 2(v)
(v) Section 3
(vi) Section 5
(vii) Section 6
(viii) Section 8 (ix) Section 9
(x) Sections 11 to 23
(xi) Sections 23 and 54
(xii) Section 23(2)(g) read with Chapter VI & VII – Regulations 27 to 32
(xiii) Section 29
(xiv) Section 33
(xv) Section 47
(xvi) Section 48
(xvii) Section 57
(xviii) Section 59
(5) Whether the Aadhaar Act defies the concept of Limited Government, Good Governance and Constitutional Trust?
(6) Whether the Aadhaar Act could be passed as ‘Money Bill’ within the meaning of Article 110 of the Constitution?
(7) Whether Section 139AA of the Income Tax Act, 1961 is violative of right to privacy and is, therefore, unconstitutional?
(8) Whether Rule 9(a)(17) of the Prevention of Money Laundering (Maintenance of Records) Rules, 2005 and the notifications issued thereunder, which mandate linking of Aadhaar with bank accounts, are unconstitutional?
(9) Whether Circular dated March 23, 2017 issued by the Department of Telecommunications mandating linking of mobile number with Aadhaar is illegal and unconstitutional?
(10) Whether certain actions of the respondents are in contravention of the interim orders passed by the Court, if so, the effect thereof?
128) We now proceed to discuss the arguments on these grounds, as advanced by the petitioners, reply thereto and our conclusions thereupon. Surveillance: Whether the Aadhaar Project creates or has tendency to create surveillance state and is, thus, unconstitutional on this ground? Education took us from thumb impression to signature Technology has taken us from signature to thumb impression, again
129) It may be remarked at the outset that the argument of surveillance draws sustenance, to a larger extent, from privacy rights as well. Therefore, the arguments which were addressed under this caption have traces of privacy also. However, these are discussed in the context of surveillance state argument.
130) It was submitted that Aadhaar project creates the architecture of a ‘cradle to grave’ surveillance state and society. This means that it enables the State to profile citizens, track their movements, assess their habits and silently influence their behaviour throughout their lives.
Over time, the profiling enables the State to stifle dissent and influence political decision making. The architecture of the project comprises a Central Identities Data Repository which stores and maintains authentication transaction data. The authentication record comprises the time of authentication and the identity of the requesting entity. The UIDAI and the Authentication Service Agency (ASA) is permitted to store this authentication record for 2 + 5 years (as per Regulations 20 and 26/27 of the Authentication Regulations). Based on this architecture it is possible for the State to track down the location of the person seeking authentication. Since the requesting entity is also identified, the activity that the citizen is engaging in is also known. (Sections 2(d), 2(h), 8, 10, 32 of the Act read with Regulations 18, 20, 26 of the Aadhaar (Authentication) Regulation, 2016).
131) According to the petitioners, the Authority has the following information (according to the document on technical specification of Aadhaar registered devices published by the Authority in February 2017) – Aadhaar number, name of Aadhaar holder, whether authentication failed or was successful, reason for such failure, requesting entities’ Internet Protocol (IP) address, date and time of authentication, device ID and its unique ID of authentication device which can be used to locate the individual.
132) Authentication of Aadhaar number enables tracking, tagging and profiling of individuals as the IP Address of the authentication device gives an idea of its geographical location (determinable within the range of 2 kilometres), country, city, region, pin code/zip code). Mr. Divan submits that an individual is on an electronic leash, tethered to a central data repository that has the architecture to track all activities of an individual.
The Aadhaar Act creates a database of all Indian residents and citizens with their core biometric information, demographic information and meta data. In light of the enormous potential of information, concentration of information in a single entity, i.e., the Authority, enabling easier access to aggregated information puts the State in a position to wield enormous power. Given that with advancements in technology, such information can affect every aspect of an individual’s personal, professional, religious and social life, such power is a threat to individual freedoms guaranteed under Articles 19(1)(a) to 19(1)(g) of the Constitution and other fundamental rights guaranteed under Article 21 (Right to informational privacy) and Article 25 of the Constitution.
It was submitted that the Aadhaar Act treats the entire populace of the country as potential criminals ignoring the necessity to balance the State’s mandate of protection against crime with the right to personal bodily integrity which is envisaged under Article 21 read with Article 20(3) of the Constitution. It does not require the collection of data to have a nexus with a crime. Mr. Sibal submits that in the decision in Selvi & Ors. v. State of Karnataka60, this Court has held: “The theory of interrelationship of rights mandates that the right against self-incrimination should also be read as a component of “personal liberty” under Article 21. Hence, our understanding of the “right to privacy” should account for its intersection with Article 20(3)”
133) It is argued that the Aadhaar Act, therefore, violates the right to protection from self-incrimination, and the right to privacy and personal dignity/bodily integrity under Article 20(3) and Article 21.
134) It was argued that the Constitution of India repudiates mass surveillance as enabled by Aadhaar and the project ought to be struck down on this ground alone. There is no question of balancing or justification in case of a surveillance architecture.
135) Passages from various judgments were quoted in an attempt to establish that surveillance causes interference with right to privacy, life and liberty. From Kharak Singh v. State of U.P.61, dissenting opinion of Subba Rao, J. (which has been upheld in K.S. Puttaswamy) was relied upon. With respect to how surveillance constricts right to life and liberty, His Lordship held that: “Now let us consider the scope of Article 21. The expression “life” used in that Article cannot be confined only to the taking away of life, i.e., causing death. In Munn v. Illinois (1), Field, J., defined “life” in the following words:
“Something more than mere animal existence. The inhibition against its deprivation extends to all those limbs and faculties by which life is enjoyed. The provision equally prohibits the mutilation of the body by the amputation of an arm or leg, or the putting out of an eye, or the destruction of any other organ of the body through which the soul communicates with the outer world. The expression “‘liberty” is given a very wide meaning in America. It takes in all the freedoms. In Bolling v. Sharpe (2), the Supreme Court of America observed that the said expression was not confined to mere freedom from bodily restraint and that liberty under law extended to the full range of conduct which the individual was free to pursue.
But this absolute right to liberty was regulated to protect other social interests by the State exercising its powers such as police power, the power of eminent domain, the power of taxation etc. The proper exercise of the power which is called the due process of law is controlled by the Supreme Court of America. In India the word “liberty” has been qualified by the word “Personal”, indicating thereby that it is confined only to the liberty of the person. The other aspects of the liberty have been provided for in other Articles of the Constitution
xx xx xx
It is true our Constitution does not expressly declare a right to privacy as a fundamental right, but the said right is an essential ingredient of personal liberty. Every democratic country sanctifies domestic life; it is expected to give him rest, physical happiness, peace of mind and security. In the last resort, a person’s house, where he lives with his family, is his “castle”; it is his rampart against encroachment on his personal liberty. The pregnant words of that famous Judge, Frankfurter J., in Wolf v. Colorado [[1949] 238 US 25] pointing out the importance of the security of one’s privacy against arbitrary intrusion by the police, could have no less application to an Indian home as to an American one.
If physical restraints on a person’s movements affect his personal liberty, physical encroachments on his private life would affect it in a larger degree. Indeed, nothing is more deleterious to a man’s physical happiness and health than a calculated interference with his privacy. We would, therefore, define the right of personal liberty in Article 21 as a right of an individual to be free from restrictions or encroachments on his person, whether those restrictions or encroachments are directly imposed or indirectly brought about by calculated measures.
xx xx xx
The freedom of movement in clause (d) of Article 19 therefore must be a movement in a free country i.e. in a country where he can do whatever he likes, speak to whomsoever he wants, meet people of his own choice without any apprehension, subject of course to the law of social control. The petitioner under the shadow of surveillance is certainly deprived of this freedom. He can move physically, but he cannot do so freely, for all his activities are watched and noted. The shroud of surveillance cast upon him perforce engender inhibitions in him and he cannot act freely as he would like to do. “
136) In the case of District Registrar and Collector, Hyderabad and Anr. v. Canara Bank and Ors.62, this Court struck down provisions of a legislation on grounds that it was too intrusive of citizens’ right to privacy. The case involved an evaluation of the Andhra Pradesh Stamp Act which authorized the collector to delegate “any person” to enter any premises in order to search for and impound any document that was found to be improperly stamped. After an exhaustive analysis of privacy laws across the world, and in India, the Court held that in the absence of any safeguards as to probable or reasonable cause or reasonable basis, this provision was violative of the constitutionally guaranteed right to privacy “both of the house and of the person”.
The Court held: “The A.P. amendment permits inspection being carried out by the Collector by having access to the documents which are in private custody i.e. custody other than that of a public officer. It is clear that this provision empowers invasion of the home of the person in whose possession the documents ‘tending’ to or leading to the various facts stated in sec. 73 are in existence and sec. 73 being one without any safeguards as to probable or reasonable cause or reasonable basis or materials violates the right to privacy both of the house and of the person. We have already referred to R. Rajagopal’s case wherein the learned judges have held that the right to personal liberty also means the life free from encroachments unsustainable in law and such right flowing from Article 21 of the Constitution.”
137) Reference was made to the U.S Supreme Court case of U.S. v. Jones63 where the court held that installing a Global Positioning System (GPS) tracking device on a vehicle and using the device to monitor the vehicle’s movements constitutes an unlawful search under the Fourth Amendment. Sotomayor, J. in her concurring judgment observed that Fourth Amendment search and seizure is not only concerned with physical trespassory intrusions on property but also non-physical violation of privacy that society recognizes as reasonable. She notes that GPS data can reveal an entire profile of a person simply by knowing the places she visits and that the Government can mine this data in the future:
“With increasing regularity, the Government will be capable of duplicating the monitoring undertaken in this case by enlisting factory or owner-installed vehicle tracking devises or GPS enabled smart-phones … In cases of electronic or other novel modes of surveillance that do not depend upon a physical invasion on property, the trespassory test may provide little guidance.
xx xx xx
GPS monitoring generates a precise, comprehensive record of a person’s public movements that reflects a wealth of detail about her familial, political, professional, religious, and sexual associations … disclosed GPS data will be trips to the psychiatrist, plastic surgeon, abortion clinic, AIDS treatment centre, strip club, criminal defence attorney … Government can store such records and efficiently mine them for information years into the future… awareness that the government may be watching chills associational and expressive freedom … it may alter the relationship between citizen and government in a way that is inimical to democratic society.
xx xx xx
I would not assume that all information voluntarily disclosed to some member of the public for a limited purpose is, for that reason alone, disentitled to Fourth Amendment protection … (“Privacy is not a discrete commodity, possessed absolutely or not at all. Those who disclose certain facts to a bank or phone company for a limited business purpose need not assume that this information will be released to other persons for other purposes”) … (“[W]hat [a person] seeks to preserve as private, even in an area accessible to the public, may be constitutionally protected”).”
138) The judgment of the ECtHR in Zakharov v. Russia64 was also referred to where the ECtHR examined an application claiming violation of Article 8 of the Convention (right to respect for private and family life) alleging that the mobile operators had permitted unrestricted interception of all telephone communications by the security services without prior judicial authorisation, under the prevailing national law. The Court observed that:
“Mr Zakharov was entitled to claim to be a victim of a violation of the European Convention, even though he was unable to allege that he had been the subject of a concrete measure of surveillance. Given the secret nature of the surveillance measures provided for by the legislation, their broad scope (affecting all users of mobile telephone communications) and the lack of effective means to challenge them at national level… Russian law did not meet the “quality of law” requirement and was incapable of keeping the interception of communications to what was “necessary in a democratic society”. There had accordingly been a violation of Article 8 of the Convention… existence of arbitrary and abusive surveillance practices, which appear to be due to inadequate safeguards provided by law”.
139) The Court held that any interference with the right to privacy under Article 8 can only be justified under Article 8(2) if it is in accordance with law, pursues one or more legitimate aims and is necessary in a democratic society to achieve such aim. “In accordance with the law” requires the impugned measure both to have some basis in domestic law and to be compatible with the rule of law, which is expressly mentioned in the Preamble to the Convention and inherent in the object and purpose of Article 8.
The law must, thus, meet quality requirements: it must be accessible to the person concerned and foreseeable as to its effects. With respect to foreseeability of surveillance, the court held: “Foreseeability in the special context of secret measures of surveillance, such as the interception of communications, cannot mean that an individual should be able to foresee when the authorities are likely to intercept his communications so that he can adapt his conduct accordingly. However, especially where a power vested in the executive is exercised in secret, the risks of arbitrariness are evident. It is therefore essential to have clear, detailed rules on interception of telephone conversations, especially as the technology available for use is continually becoming more sophisticated.
The domestic law must be sufficiently clear to give citizens an adequate indication as to the circumstances in which and the conditions on which public authorities are empowered to resort to any such measures.
xx xx xx
Since the implementation in practice of measures of secret surveillance of communications is not open to scrutiny by the individuals concerned or the public at large, it would be contrary to the rule of law for the discretion granted to the executive or to a judge to be expressed in terms of an unfettered power. Consequently, the law must indicate the scope of any such discretion conferred on the competent authorities and the manner of its exercise with sufficient clarity to give the individual adequate protection against arbitrary interference.”
140) The Court observed that the following minimum safeguards that should be set out in law in order to avoid abuses of power for surveillance are: the nature of offences which may give rise to an interception order; a definition of the categories of people liable to have their telephones tapped; a limit on the duration of telephone tapping; the procedure to be followed for examining, using and storing the data obtained; the precautions to be taken when communicating the data to other parties; and the circumstances in which recordings may or must be erased or destroyed.
141) For establishing if the measures were “necessary in a democratic society” in pursuit of a legitimate aim, the Court observed: “When balancing the interest of the respondent State in protecting its national security through secret surveillance measures against the seriousness of the interference with an applicant’s right to respect for his or her private life, the national authorities enjoy a certain margin of appreciation in choosing the means for achieving the legitimate aim of protecting national security. However, this margin is subject to European supervision embracing both legislation and decisions applying it.
In view of the risk that a system of secret surveillance set up to protect national security may undermine or even destroy democracy under the cloak of defending it, the Court must be satisfied that there are adequate and effective guarantees against abuse. The assessment depends on all the circumstances of the case, such as the nature, scope and duration of the possible measures, the grounds required for ordering them, the authorities competent to authorise, carry out and supervise them, and the kind of remedy provided by the national law. The Court has to determine whether the procedures for supervising the ordering and implementation of the restrictive measures are such as to keep the “interference” to what is “necessary in a democratic society”.”
142) Two other cases of violation of Article of the European Convention of Human Rights were cited, namely Digital Rights Ireland Ltd. v. Minister for Communication, Marine and Natural Resources65 and S and Marper v. United Kingdom66. In Digital Ireland, the European Parliament and the Council of the European Union adopted Directive 2006/24/EC (Directive), which regulated Internet Service Providers’ storage of telecommunications data. It could be used to retain data generated or processed in connection with the provision of publicly available electronic communications services or of public communications network for the purpose of fighting serious crime in the European Union (EU).
The data included data necessary to trace and identify the source of communication and its destination, to identify the date, time duration, type of communication, IP address, telephone number and other fields. The European Court of Justice (ECJ) evaluated the compatibility of the Directive with Articles 7 and 8 of the Charter of Fundamental Rights of the European Union and declared the Directive to be invalid. According to the ECJ, the Directive interfered with the right to respect for private life under Article 7 and with the right to the protection of personal data under Article 8. It allowed very precise conclusion to be drawn concerning the private lives of the persons whose data had been retained, such as habits of everyday life, permanent or temporary places of residence, daily and other movements, activities carried out, social relationships and so on. The invasion of right was not proportionate to the legitimate aim pursued.
143) In S and Marper, the storing of DNA profiles and cellular samples of any person arrested in the United Kingdom was challenged before the ECtHR. Even if the individual was never charged, if criminal proceedings were discontinued, or if the person was later acquitted of any crime, their DNA profile could nevertheless be kept permanently on record. It held that there had been a violation of Article 8 of the ECHR. Fingerprints, DNA profiles and cellular samples, constituted personal data and their retention was capable of affecting private life of an individual. Retention of such data without consent, thus, constitutes violation of Article 8 as they relate to identified and identifiable individuals.
The Court held that invasion of privacy was not “necessary in a democratic society as it did not fulfill any pressing social need. The blanket and indiscriminate nature of retention of data was excessive and did not strike a balance between private and public interest.
144) The respondents, on the other hand, rebutted the arguments of the petitioners that the architecture of the Aadhaar Act enables State surveillance. It was submitted that bare minimal information was obtained from the individual who enrolled for Aadhaar. Insofar as demographic information is concerned, it included name, date of birth, address, gender, mobile number and email address. The latter two are optional and meant for transmitting relevant information to the AMH and for One Time Password (OTP) based authentication. This information was in respect of an individual and is always in public domain. Section 2(k) of the Aadhaar Act specifically provides that regulations cannot include race, religion, caste, tribe, ethnicity, language, records of entitlement, income or medical history. Therefore, sensitive information specifically stands excluded.
This specific exclusion, in the context, ensures that the scope of including additional demographic information is very narrow and limited. It was also argued that even the biometric information was limited to the fingerprints and iris scan, which is considered to be the core biometric information. Such information is, again, frequently utilised globally to ascertain the identity of a person. The argument was, thus, that the information gathered was noninvasive and non-intrusive identity information.
145) It was also argued that the very scheme of the Aadhaar and the manner in which it operates excludes every possibility of data profiling and, therefore, the question of State surveillance would not arise. The powerpoint presentation which was given by Dr. Pandey, as has been stated above, was referred to, on the basis of which it was argued that the Aadhaar design takes full care of security of persons.
146) It was also argued by the respondents that identity information data resides in the CIDR which is not in the control of the Government or the police force. The Authority is a body constituted as a body corporate having perpetual succession and a common seal. It is regulated by substantive and procedural checks to protect the identity information and authentication record. This information cannot be published, displayed or posted publicly. It does not have the authority to carry out surveillance. The State Governments and the police forces cannot obtain the information contained in the CIDR or the authentication records except in two situations contemplated by Section 33 – (i) When the District Judge orders so after giving an opportunity of hearing to the authority (even in this situation core biometric information will not be shared; and (ii) in the interest of National Security where a Joint Secretary or a superior officer of the Government of India specially authorizes in this behalf, and in this case every direction is reviewed by an oversight committee chaired by the Cabinet Secretary. Further, this direction is limited for three months and extendable by a further period of 3 months.
147) It was submitted that surveillance, if at all, can only be carried out by unauthorised use of CIDR information, despite its statutory prohibition and punitive injunctions or by other means such as physical surveillance. That is, however, an illegal surveillance. The architecture of the Act does not allow surveillance. It was submitted that the petitioners have not made out a case of surveillance by the Authority but points out a mere possibility of surveillance.
148) We may reiterate that the argument of surveillance also has the reflections of privacy and in fact the argument is structured on the basis that the vital information which would be available with the Government can be utilised to create the profiling of individuals and retention of such information in the hands of the respondents is a risky affair which may enable the State to do the surveillance of any individual it wants.
149) Insofar as the aspect of privacy of individual is concerned, that would be dealt with in detail while addressing that issue. To segregate issue of surveillance from privacy, we are focusing the discussion to the aspect whether there is sufficient data available with the respondents which may facilitate the profiling and misuse thereof or whether there are sufficient safeguards to ward off the same. In the process, we would be discussing the issues pertaining to data protection as well. At the same time, there would be some overlapping of discussion inasmuch as it will have to be seen as to the collection, storage and use of biometric data satisfies the proportionality principle.
150) It is clear that the argument of the petitioners is that on the basis of the data available with the Authority, there can be a profiling of an individual which may make the surveillance state. And such a mass surveillance is not permitted by the Constitution of India. The entire foofaraw about the Aadhaar architecture is the socalled enormous information that would be available to the Government on using Aadhaar card by residents. Two issues arise from the respective arguments of the parties:
(a) whether the architecture of the Aadhaar project enables the Sate to create a regime of surveillance?; and
(b) whether there are adequate provisions for data protection?
151) Insofar as issue (a) above is concerned, after going through the various aspects of the Aadhaar project, the provisions of the Aadhaar Act and the manner in which it operates, it is difficult to accept the argument of the petitioners. The respondents have explained that the enrolment and authentication processes are strongly regulated so that data is secure. The enrolment agency, which collects the biometric and demographic of the individuals during enrolment, is appointed either by UIDAI or by a Registrar [Section 2(s)]. The Registrars are appointed through MoUs or agreements for enrolment and are to abide by a code of conduct and processes, policies and guidelines issued by the Authority.
They are responsible for the process of enrolment. Categories of persons eligible for appointment are limited by the Regulations. The agency employs a certified supervisor, an operator and a verifier under Enrolment and Update Regulations. Registrars and the enrolling agencies are obliged to use the software provided or authorized by UIDAI for enrolment purpose. The standard software has security features as specified by the Authority. All equipment used is as per the specification issued by the Authority. The Registrars are prohibited from using the information collected for any purpose other than uploading the information to CIDR. Sub-contracting of enrolment function is not allowed.
The Code of Conduct contains specific directions for following the confidentiality, privacy and security protocols and submission of periodic reports of enrolment. Not only there are directions prohibiting manipulation and fraudulent practices but the Act contains penal provisions for such violations in Chapter VII of the Regulations. The enrolment agencies are empanelled by the Authority. They are given an enrolling agency code using which the Registrar can onboard such agency to the CIDR. The enrolment data is uploaded to the Central Identities Data Repository (CIDR) certified equipment and software with a digital signature of the Registrar/enrolling agency. The data is encrypted immediately upon capture.
The decryption key is with the UIDAI solely. Section 2(ze) of the Information Technology Act, 2000 (hereinafter referred to as the ‘IT Act’) which defines ‘secure systems’ and Section 2(w) of the Act, which defines ‘intermediaries’ apply to the process. Authentication only becomes available through the Authentication Service Agency (ASA). They are regulated by the Aadhaar (Authentication) Regulations, 2016. Their role and responsibilities are provided by Regulation 19 of the Authentication Regulations. They are to use certified devices. The equipment or software has to be duly registered with or approved or certified by the Authority/agency. The systems and operations are audited by information system auditor.
The requesting entities pass the encrypted data to the CIDR through the ASA and the response (Yes/No authentication or e-KYC information) also takes the same route back. The server of the ASA has to perform basic compliance and completeness checks on the authentication data packet before forwarding it to the CIDR. The Act prohibits sharing and disclosure of core biometric data under Section 8 and 29. Other identity information is shared with requesting entity (AUAs and KUAs) only for the limited purpose of authentication. The data is transferred from the requesting entity to the ASA to the CIDR in an encrypted manner through a leased line circuitry using secure Protocols (Regulation 9 of the Authentication Regulations).
The storage of data templates is in safely located servers with no public internet inlet/outlet, and offline storage of original encrypted data (PID blocks). There are safety and security provisions such as audit by Information Systems Auditor. Requesting entities are appointed through agreement. They can enter into agreement with sub-AUA or sub-KUA with permission of the UIDAI. Whatever identity information is obtained by the requesting entity is based on a specific consent of the Aadhaar number holder. The e-KYC data shared with the requesting entity can only be after prior consent of the Aadhaar holder. Such data cannot be shared and has to be stored in encrypted form.
The biometric information used is not permitted to be stored. Only the logs of authentication transactions are maintained for a short period. Full identity information is never transmitted back to the requesting entity. There is a statutory bar from sharing biometric information (Section 29(1)(a)/Section 29(4)). Data centres of ASA, requesting entities and CIDR should be within the territory of India. There are various other provisions for monitoring, auditing, inspection, limits on data sharing, data protection, punishments etc., grievance redressal mechanism, suspension and termination of services, etc. so that all actions the entities involved in the process are regulated. Regulation 3(i) & (j) of Aadhaar (Data Security) Regulation, 2016 enables partitioning of CIDR network into zones based on risk and trust and other security measures. CIDR being a computer resource is notified to be a “Protected System” under Section 70 of the IT Act by the Central Government on December 11, 2015.
Anyone trying to unlawfully gain access into this system is liable to be punished with 10 years imprisonment and fine. The storage involves end to end encryption, logical partitioning, firewalling and anonymisation of decrypted biometric data. Breaches of penalty are made punitive by Chapter VII of the Act. Biometric information is deemed to be an “electronic record”, and “Sensitive personal data or information” under the IT Act. There are further guards under the Aadhaar (Data Security) Regulations, 2016.
152) That apart, we have recorded in detail the powerpoint presentation that was given by Dr. Ajay Bhushan Pandey, CEO of the Authority, which brings out the following salient features:
(a) During the enrolment process, minimal biometric data in the form of iris and fingerprints is collected. The Authority does not collect purpose, location or details of transaction. Thus, it is purpose blind. The information collected, as aforesaid, remains in silos. Merging of silos is prohibited. The requesting agency is provided answer only in ‘Yes’ or ‘No’ about the authentication of the person concerned. The authentication process is not exposed to the Internet world. Security measures, as per the provisions of Section 29(3) read with Section 38(g) as well as Regulation 17(1)(d) of the Authentication Regulations are strictly followed and adhered to.
(b) There are sufficient authentication security measures taken as well, as demonstrated in Slides 14, 28 and 29 of the presentation.
(c) The Authority has sufficient defence mechanism, as explained in Slide 30. It has even taken appropriate protection measures as demonstrated in Slide 31.
(d) There is an oversight by Technology and Architecture Review Board (TARB) and Security Review Committee.
(e) During authentication no information about the nature of transaction etc. is obtained.
(f) The Authority has mandated use of Registered Devices (RD) for all authentication requests. With these, biometric data is signed within the device/RD service using the provider key to ensure it is indeed captured live. The device provider RD service encrypts the PID block before returning to the host application. This RD service encapsulates the biometric capture, signing and encryption of biometrics all within it. Therefore, introduction of RD in Aadhaar authentication system rules out any possibility of use of stored biometric and replay of biometrics captured from other source. Requesting entities are not legally allowed to store biometrics captured for Aadhaar authentication under Regulation 17(1)(a) of the Authentication Regulations.
(g) The Authority gets the AUA code, ASA code, unique device code, registered device code used for authentication. It does not get any information related to the IP address or the GPS location from where authentication is performed as these parameters are not part of authentication (v2.0) and e-KYC (v2.1) API. The Authority would only know from which device the authentication has happened, through which AUA/ASA etc. It does not receive any information about at what location the authentication device is deployed, its IP address and its operator and the purpose of authentication. Further, the authority or any entity under its control is statutorily barred from collecting, keeping or maintaining any information about the purpose of authentication under Section 32(3) of the Aadhaar Act.
153) After going through the Aadhaar structure, as demonstrated by the respondents in the powerpoint presentation from the provisions of the Aadhaar Act and the machinery which the Authority has created for data protection, we are of the view that it is very difficult to create profile of a person simply on the basis of biometric and demographic information stored in CIDR. Insofar as authentication is concerned, the respondents rightly pointed out that there are sufficient safeguard mechanisms. To recapitulate, it was specifically submitted that there were security technologies in place (slide 28 of Dr. Pandey’s presentation), 24/7 security monitoring, data leak prevention, vulnerability management programme and independent audits (slide 29) as well as the Authority’s defence mechanism (slide 30). It was further pointed out that the Authority has taken appropriate proactive protection measures, which included disaster recovery plan, data backup and availability and media response plan (slide 31).
The respondents also pointed out that all security principles are followed inasmuch as: (a) there is PKI-2048 encryption from the time of capture, meaning thereby, as soon as data is given at the time of enrolment, there is an end to end encryption thereof and it is transmitted to the Authority in encrypted form. The said encryption is almost foolproof and it is virtually impossible to decipher the same; (b) adoption of best-in-class security standards and practices; and (c) strong audit and traceability as well as fraud detection. Above all, there is an oversight of Technology and Architecture Review Board (TARB) and Security Review Committee. This Board and Committee consist of very high profiled officers. Therefore, the Act has endeavoured to provide safeguards67.
154) Issue (b) relates to data protection. According to the petitioners there is no data protection and there is a likelihood of misuse of data/personal information of the individuals.
155) The question to be determined is whether the safeguards provided for the protection of personal biometric data in the Aadhaar Act and Rules are sufficient. The crucial tasks that the Court needs to undertake are –
(i) to discuss the significance of data in the world of technology and its impact;
(ii) to determine the magnitude of protection that should be accorded to collection, storage and use of sensitive biometric data, so that they can qualify as proportionate; and
(iii) to determine whether the Aadhaar Act and Rules provide such data protection, thereby obviating any possibility of surveillance.
(i) Significance of Data:
156) Alvin Toffler in his illuminating article titled ‘What will our future be like?’ has presented mind boggling ideas. Toffler traces the transition – from agriculture society to industry society to knowledge based society. If we go back to the beginnings of time, agriculture was the prime source and the entire mankind was based on agriculture. 350 years later with the invention of steam engines came the industrialized age and now what we are living through is the third gigantic wave, which is way more powerful than industrialized age. An age that is based on knowledge. Toffler emphasises that in today’s society the only thing that leads to creation of wealth is knowledge.
Unlike the past wherein economics was described as the science of the allocation of scarce resources, today we are primarily dependent on knowledge and that is not a scarce resource. Times are changing, we can no longer trust the straight line projection. His view is that we are going from a society which is more and more uniform to a highly de-massified society. Knowledge is power. We are in the era of information. Probably what Toffler is hinting is that access to this vast reservoir of information is available in digital world. Information is available online, at the touch of a button. With this, however, we usher into the regime of data.
157) In a recent speech by Mr. Benjamin Netanyahu, Prime Minister of Israel, while talking about innovation and entrepreneurship, he brought out an interesting phenomena in the world of free market principles, i.e. in the era of globalisation, in the following words: “Look at the ten leading companies in 2006, five energy companies, one IT company Microsoft and a mere ten years later, in 2016, a blink of an eye, in historical terms, its completely reversed, five IT companies one energy company left. The true wealth is in innovation – you know these companies – Apple, Google, Microsoft, Amazon, Facebook.”
158) He adds by making a significant statement as the reason behind this change: “…there is a reason something is going on, it’s a great change – you want to hear a jargan – it’s a one sentence, this is a terrible sentence, but I have no other way to say, it’s a confluence of big data, connectivity and artificial intelligence. Ok, you get that? You know what that does – it revolutionises old industries and it creates entirely new industries, so here is an old industry that Israel was always great in – Agriculture. We are always good in agriculture but now we have precision agriculture. You know what that is? See that drone in the sky is connected to a big database and there is sensor at the field and in the field there is drip irrigation and drip fertilization and now we can target with this technology the water that we give, the fertilizer that we give down to the individual plant that needs it. That’s precision agriculture, that’s Israel. Unbelievable.”
159) This brings us to the world of data – big data. It has its own advantages of tremendous nature. It is making life of people easier. People can connect with each other even when they are located at places far away from each other. Not only they can converse with each other but can even see each other while talking. There is a wealth of information available on different networks to which they can easily access and satisfy their quest for knowledge within seconds by getting an answer. People can move from one place to the other with the aid of Global Positioning System (GPS).
They can hear music and watch movies on their handy gadgets, including smart cellphones. We are in the age of digital economy which has enabled multiple avenues for a common man. Internet access is becoming cheaper by the day, which can be accessed not only through the medium of desktop computers or laptops and even other handy gadgets like smart phones. Electronic transactions like online shopping, bill payments, movie/train/air ticket bookings, funds transfer, e-wallet payments, online banking and online insurance etc. are happening with extreme ease at the touch of a finger. Such tasks can be undertaken sitting in drawing rooms. Even while travelling from one place to the other in their car, they can indulge in all the aforesaid activities. In that sense, technology has made their life so easy.
160) However, there is another side to do as well, like any coin which has two sides. The use of such technologies is at the cost of giving away personal information, which is in the realm of privacy. In order to connect with such technologies and avail their benefits, the users are parting with their biometric information like fingerprints and iris as well as demographic information like their names, parentage, family members, their age, even personal information like their sex, blood group or even the ailments they are suffering from. Not only this, use of aforesaid facilities on net or any portal like Apple, Google, Facebook etc. involves tracking their movements, including the nature of activities, like the kind of shopping, the places from where shopping is done, the actual money spent thereon, the nature of movies watched etc.
All this data is there with the companies in respect of its users which may even turn into metadata. In fact, cases after cases are reported where such data of users is parted with various purposes. Interestingly, for using such facilities, people knowingly and willingly, are ready to part with their vital personal information. Every transaction on a digital platform is linked with some form of sensitive personal information. It can be an individual’s user name, password, account number, PAN number, biometric details, e-mail ID, debit/credit card number, CVV number and transaction OTP etc.
161) These have raised concerns about the privacy and protection of data, which has become a matter of great concern. Problem is not limited to data localisation but has become extra-territorial. There are issues of cross-border transfers of personal data, regulation whereof is again a big challenge with which various opinions are grappling. There are even talks of convergence of regulatory regime in this behalf so that uniform approach is adopted in providing a legal ecosystem to regulate cross-border data transfer. Asian Business Law Institute (ABLI), in collaboration with Singapore Academy of Law (SAL) has, after undertaking in-depth study, compiled 14 country reports in their respective jurisdictions on the regulation of cross-border data transfer and data localisation in Asia.
162) In the aforesaid scenario, interesting issue is posed by the respondents, viz., when so much personal information about people is already available in public domain, how can there be an expectancy of data privacy. That aspect is dealt with while discussing the issue of privacy. Here, we are concerned with data protection under Aadhaar that is available with the State. As pointed out above, even in respect of private players, the data protection has become a matter of serious concern. When it comes to the State or the instrumentality of the State, the matter has to be taken with all seriousness, on the touchstone of constitutionalism and the concept of limited Government.
(ii) Law on Data Protection:
163) In order to determine this aspect, i.e. the nature and magnitude of data protection that is required to enable legal collection and use of biometric data, reliance can be placed on –
(a) various existing legislations – both in India and across the world; and
(b) case law including the judgment in K.S. Puttaswamy.
(a) Legislation in India:
(i) Information Technology Act, 2000 The only existing legislation covering data protection related to biometric information are Section 43A and Section 72A of the IT Act and the Information Technology (Reasonable Security Practices and Procedures and Sensitive Personal Data or Information) Rules, 2011 (hereinafter “Sensitive Personal Data Rules”). Although the IT Act and Rules do not determine the constitutionality of use of biometric data and information by the Aadhaar Act and Rules, they are instructive in determining the safeguards that must be taken to collect biometric information68.
164) Following are the provisions which cover biometric information under the IT Act: Section 43A of the IT Act attaches liability to a body corporate, which is possessing, handling and dealing with any ‘sensitive personal information or data’ and is negligent in implementing and maintaining reasonable security practices resulting in wrongful loss or wrongful gain to any person. ‘Sensitive personal information or data’ is defined under Rule 3 of the Sensitive Personal Data Rules to include information relating to biometric data. Section 43A reads as follows:
“43A. Compensation for failure to protect data. -Where a body corporate, possessing, dealing or handling any sensitive personal data or information in a computer resource which it owns, controls or operates, is negligent in implementing and maintaining reasonable security practices and procedures and thereby causes wrongful loss or wrongful gain to any person, such body corporate shall be liable to pay damages by way of compensation to the person so affected.
Explanation. -For the purposes of this section,-
(i) “body corporate” means any company and includes a firm, sole proprietorship or other association of individuals engaged in commercial or professional activities;
(ii) “reasonable security practices and procedures” means security practices and procedures designed to protect such information from unauthorised access, damage, use, modification, disclosure or impairment, as may be specified in an agreement between the parties or as may be specified in any law for the time being in force and in the absence of such agreement or any law, such reasonable security practices and procedures, as may be prescribed by the Central Government in consultation with such professional bodies or associations as it may deem fit;
(iii) “sensitive personal data or information” means such personal information as may be prescribed by the Central Government in consultation with such professional bodies or associations as it may deem fit.]”
165) Similarly, Section 72A of the IT Act makes intentional disclosure of ‘personal information’ obtained under a contract, without consent of the parties concerned and in breach of a lawful contract, punishable with imprisonment and fine. Rule 2(i) of the Sensitive Personal Data Rules define “personal information” to mean any information that relates to a natural person, which, either directly or indirectly, in combination with other information available or likely to be available with a body corporate, is capable of identifying such person. Thus, biometrics will form a part of “personal information”.
The Section reads as under- “72A. Punishment for disclosure of information in breach of lawful contract – Save as otherwise provided in this Act or any other law for the time being in force, any person including an intermediary who, while providing services under the terms of lawful contract, has secured access to any material containing personal information about another person, with the intent to cause or knowing that he is likely to cause wrongful loss or wrongful gain discloses, without the consent of the person concerned, or in breach of a lawful contract, such material to any other person, shall be punished with imprisonment for a term which may extend to three years, or with fine which may extend to five lakh rupees, or with both.”
166) The Sensitive Personal Data Rules provide for additional requirements on commercial and business entities (body corporates as defined under Section 43A of the IT Act) relating to the collection and disclosure of sensitive personal data (including biometric information). The crucial requirements, which are 567 indicative of the principles for data protection that India adheres to, inter alia include:
(i) The body corporate or any person who on behalf of body corporate collects, receives, possesses, stores, deals or handle information of provider of information, shall provide a privacy policy for handling of or dealing in personal information including sensitive personal data or information and ensure that the same are available for view.
(ii) Body corporate or any person on its behalf shall obtain consent in writing from the provider of the sensitive personal data or information regarding purpose of usage before collection of such information.
(iii) Body corporate or any person on its behalf shall not collect sensitive personal data or information unless –
(a) the information is collected for a lawful purpose connected with a function or activity of the body corporate or any person on its behalf; and
(b) the collection of the sensitive personal data or information is considered necessary for that purpose (iv) The person concerned has the knowledge of –
(a) the fact that the information is being collected;
(b) the purpose for which the information is being collected;
(c) the intended recipients of the information; and
(d) name and address of the agency collecting and retaining the information.
(v) Body corporate or any person on its behalf holding sensitive personal data or information shall not retain that information for longer than is required for the purposes for which the information may lawfully be used or is otherwise required under any other law for the time being in force.
(vi) Information collected shall be used for the purpose for which it has been collected.
(vii) Body corporate or any person on its behalf shall, prior to the collection of information, including sensitive personal data or information, provide an option to the provider of the information to not to provide the data or information sought to be collected.
(viii) Body corporate shall address any discrepancies and grievances of their provider of the information with respect to processing of information in a time bound manner.
(ix) Disclosure of sensitive personal data or information by body corporate to any third party shall require prior permission from the provider of such information, who has provided such information under lawful contract or otherwise, unless such disclosure has been agreed to in the contract between the body corporate and provider of information, or where the disclosure is necessary for compliance of a legal obligation.
(x) A body corporate or a person on its behalf shall comply with reasonable security practices and procedure i.e. implement such security practices and standards and have a comprehensive documented information security programme and information security policies that contain managerial, technical, operational and physical security control measures that are commensurate with the information assets being protected with the nature of business.
In the event of an information security breach, the body corporate or a person on its behalf shall be required to demonstrate, as and when called upon to do so by the agency mandated under the law, that they have implemented security control measures as per their documented information security programme and information security policies. The above substantive and procedural safeguards are required for legal collection, storage and use of biometric information under the IT Act. They indicate the rigour with which such processes need to be carried out.
Position in other countries:
(a) EUGDPR (European Union General Data Protection Regulation)69 EUGDPR which was enacted by the EU in 2016 came into force on May 25, 2018 replacing the Data Protection Directive of 1995. It is an exhaustive and comprehensive legal framework that is aimed at protection of natural persons from the processing of personal data and their right to informational privacy. It deals with all kinds of processing of personal data while delineating rights of data subjects and obligations of data processors in detail. The following fundamental principles of data collection, processing, storage and use reflect the proportionality principle underpinning the EUGDPR –
(i) the personal data shall be processed lawfully, fairly, and in a transparent manner in relation to the data subject (principle of lawfulness, fairness, and transparency);
(ii) the personal data must be collected for specified, explicit, and legitimate purposes (principle of purpose limitation);
(iii) processing must also be adequate, relevant, and limited to what is necessary (principle of data minimization) as well as accurate and, where necessary, kept up to date (principle of accuracy);
(iv) data is to be kept in a form that permits identification of data subjects for no longer than is necessary for the purposes for which the personal data are processed (principle of storage limitation);
(v) data processing must be secure (principle of integrity and confidentiality); and
(vi) data controller is to be held responsible (principle of accountability).
167) The EUGDPR under Article 9 prohibits the collection of biometric data unless except in few circumstances which include (but are not limited to) –
(a) there is an explicit consent by the party whose data is being collected. The consent should be freely given, which is clearly distinguishable in an intelligible and easily accessible form, using clear and plain language. This consent can be withdrawn at any time without affecting the actions prior to the withdrawal; (b) processing is necessary for the purposes of carrying out the obligations and exercising specific rights of the controller or of the data subject in the field of employment and social security and social protection law;
(c) processing relates to personal data which is manifestly made public by the data subject; and
(d) processing is necessary for reasons of substantial public interest, and it shall be proportionate to the aim pursued, respect the essence of the right to data protection and provide for suitable and specific measures to safeguard the fundamental rights and the interests of the data subject.
168) The Regulation also institutes rights of the data subject (the person whose data is collected), subject to exceptions, which include the data subject’s right of access to information about the purpose of collection of data, details of data controller and subsequent use and transfer of data, the data subject’s right to rectification of data, right to erasure or right to be forgotten, the data subject’s right to restriction of processing, the right to be informed, the right to data portability and the data subject’s right to object to illegitimate use of data.
(b) Biometric Privacy Act in the United States of America
169) Some States in the United States of America have laws regulating collection and use of biometric information. Illinois has passed Biometric Information Privacy Act (740 ILCS 14/1 or BIPA) in 2008. Texas has also codified the law for capture of use of biometric identifier (Tex. Bus. & Com. Code Ann. §503.001) in 2009. The Governor of the Washington State signed into law House Bill 1493 (“H.B. 1493”) on May 16, 2017, which sets forth requirements for businesses who collect and use biometric identifiers for commercial purposes. BIPA, Illinois, for example makes it unlawful for private entities to collect, store, or use biometric information, such as retina/iris scans, voice scans, face scans, or fingerprints, without first obtaining individual consent for such activities. BIPA also requires that covered entities take specific precautions to secure the information.
(b) Case Laws:
170) In K.S. Puttaswamy’s judgment, all the Judges highlighted the importance of informational privacy in the age of easy access, transfer, storage and mining of data. The means of aggregation and analysis of data of individuals through various tools are explained. Chandrachud, J. observed that with the increasing ubiquity of electronic devices, information can be accessed, stored and disseminated without notice to the individual. Metadata and data mining make the individual’s personal information subject to private companies and the state. In this background, His Lordship discusses the necessity of a data protection regime for safeguarding privacy and protecting the autonomy of the individual. The following observations in the conclusion of the judgment are worth quoting:
“328. Informational privacy is a facet of the right to privacy. The dangers to privacy in an age of information can originate not only from the state but from non-state actors as well. We commend to the Union Government the need to examine and put into place a robust regime for data protection. The creation of such a regime requires a careful and sensitive balance between individual interests and legitimate concerns of the state. The legitimate aims of the state would include for instance protecting national security, preventing and investigating crime, encouraging innovation and the spread of knowledge, and preventing the dissipation of social welfare benefits. These are matters of policy to be considered by the Union government while designing a carefully structured regime for the protection of the data. Since the Union government has informed the Court that it has constituted a Committee chaired by Hon’ble Shri Justice B N Srikrishna, former Judge of this Court, for that purpose, the matter shall be dealt with appropriately by the Union government having due regard to what has been set out in this judgment.”
171) S.K. Kaul, J. cited the European Union General Data Protection Regulations70 to highlight the importance of data protection and the circumstances in which restrictions on the right to privacy may be justifiable subject to the principle of proportionality. These include balance against other fundamental rights, legitimate national security interest, public interest including scientific or historical research purposes or statistical purposes, criminal offences, tax purposes, etc.
172) There are numerous case laws – both American and European – presented by the petitioners and the respondents with respect to the collection, storage and use of biometric data which have been taken note of above. They are illustrative of the method and safeguards required to satisfy the proportionality principle while dealing with biometric data. The first set of cases cited by the petitioners are cases from European Human Rights Courts.
173) The European Human Rights legislations have both explicitly and through case laws recognized the right to informational privacy and data protection. The EU Charter of Fundamental Rights states in Article 7 that ‘everyone has the right to respect for his or her private and family life, home and communications’ and in Article 8 it grants a fundamental right to protection of personal data. The first article of the EU Charter affirms the right to respect and protection of human dignity. The ECHR also recognises the right to respect for private and family life, home and his correspondence which have been read to include protection of right to control over personal biometric information.
174) As pointed out above as well, a prominent case which addresses the question of storage of biometric data, i.e. whether storage and retention of DNA samples and fingerprints violates Article 8 of the ECHR, is S and Marper71. In this case, the storing of DNA profiles and cellular samples of any person arrested in the United Kingdom was challenged before the ECtHR. Even if the individual was never charged or if criminal proceedings were discontinued or if the person was later acquitted of any crime, their DNA profile could nevertheless be kept permanently on record without their consent.
175) In a unanimous verdict, the seventeen-judge bench held that there had been a violation of Article 8 of the ECHR. Fingerprints, DNA profiles and cellular samples, constituted personal data and their retention was capable of affecting private life of an individual. The retention of such data without consent, thus, constitutes violation of Article 8 as they relate to identified and identifiable individuals. It held that: “84. …fingerprints objectively contain unique information about the individual concerned allowing his or her identification with precision in a wide range of circumstances. They are thus capable of affecting his or her private life and retention of this information without the consent of the individual concerned cannot be regarded as neutral or insignificant.”
176) It articulated the proportionality principle in the following words:
“101. An interference will be considered “necessary in a democratic society” for a legitimate aim if it answers a “pressing social need” and, in particular, if it is proportionate to the legitimate aim pursued and if the reasons adduced by the national authorities to justify it are “relevant and sufficient
xx xx xx
The protection of personal data is of fundamental importance to a person’s enjoyment of his or her right to respect for private and family life, as guaranteed by Article 8 of the Convention. The domestic law must afford appropriate safeguards to prevent any such use of personal data as may be inconsistent with the guarantees of this Article. The need for such safeguards is all the greater where the protection of personal data undergoing automatic processing is concerned, not least when such data are used for police purposes. The domestic law should notably ensure that such data are relevant and not excessive in relation to the purposes for which they are stored; and preserved in a form which permits identification of the data subjects for no longer than is required for the purpose for which those data are stored … The domestic law must also afford adequate guarantees that retained personal data was efficiently protected from misuse and abuse.”
177) The issue in the case according to the Court was whether the retention of the fingerprints and DNA data of the applicants, as persons who had been suspected but not convicted of certain criminal offences, was justified under Article 8 of the Convention.
178) The Court held that such invasion of privacy was not proportionate as it was not “necessary in a democratic society” as it did not fulfill any pressing social need. The blanket and indiscriminate nature of retention of data was excessive and did not strike a balance between private and public interest.
It held:
“125. the blanket and indiscriminate nature of the powers of retention of the fingerprints, cellular samples and DNA profiles of persons suspected but not convicted of offences, as applied in the case of the present applicants, fails to strike a fair balance between the competing public and private interests and that the respondent State has overstepped any acceptable margin of appreciation in this regard.
Accordingly, the retention at issue constitutes a disproportionate interference with the applicants’ right to respect for private life and cannot be regarded as necessary in a democratic society. This conclusion obviates the need for the Court to consider the applicants’ criticism regarding the adequacy of certain particular safeguards, such as too broad an access to the personal data concerned and insufficient protection against the misuse or abuse of such data.”
179) The two crucial aspects of the case that need to be kept in mind are – First, in that case, the fingerprints were collected for criminal purposes and without the consent of the individual to whom the fingerprints belonged. Second, the fingerprints were to be stored indefinitely without the consent of the individual and that the individual did not have an option to seek deletion. These aspects were vital for the Court to decide that the retention violated the citizen’s right to privacy.
180) Similarly, in the Digital Ireland case72, the European Parliament and the Council of the European Union adopted Directive 2006/24/EC (Directive), which regulated Internet Service Providers’ storage of telecommunications data. It could be used to retain data which was generated or processed in connection with the provision of publicly available electronic communications services or of public communications network, for the purpose of fighting serious crime in the European Union. The data included data necessary to trace and identify the source of communication and its destination, to identify the date, time duration, type of communication, IP address, telephone number and other fields. The Court of Justice of European Court (CJEU) evaluated the compatibility of the Directive with Articles 7 and 8 of the Charter and declared the Directive to be invalid.
181) According to the CJEU, the Directive interfered with the right to respect for private life under Article 7 and with the right to the protection of personal data under Article 8 of the Charter of Fundamental Rights of the European Union. It allowed very precise conclusion to be drawn concerning the private lives of the persons whose data had been retained, such as habits of everyday life, permanent or temporary places of residence, daily and other movements, activities carried out, social relationships and so on. The invasion of right was not proportionate to the legitimate aim pursued for the following reasons:
(i) Absence of limitation of data retention pertaining to a particular time period and/or a particular geographical zone and/or to a circle of particular persons likely to be involved.
(ii) Absence of objective criterion, substantive and procedural conditions to determine the limits of access of the competent national authorities to the data and their subsequent use for the purposes of prevention, detection or criminal prosecutions. There was no prior review carried out by a court or by an independent administrative body whose decision sought to limit access to the data and their use to what is strictly necessary for attaining the objective pursued.
(iii) Absence of distinction being made between the categories of data collected based on their possible usefulness.
(iv) Period of retention i.e. 6 months was very long being not based on an objective criterion.
(v) Absence of rules to protect data retained against the risk of abuse and against any unlawful access and use of that data.
(vi) Directive does not require the data in question to be retained within the European Union.
182) In Tele2 Sverige AB vs. Post-och telestyrelsen73, the CJEU was seized with the issue as to whether in light of Digital Rights Ireland, a national law which required a provider of electronic communications services to retain meta-data (name, address, telephone number and IP address) regarding users/subscribers for the purpose of fighting crime was contrary to Article 7, 8 and 11 of the EU Charter. The CJEU struck down the provision allowing collection of such meta data on grounds of lack of purpose limitation, data differentiation, data protection, prior review by a court or administrative authority and consent, amongst other grounds. It held: “103. While the effectiveness of the fight against serious crime, in particular organised crime and terrorism (…) cannot in itself justify that national legislation providing for the general and indiscriminate retention of all traffic and location data should be considered to be necessary for the purposes of that fight.
xx xx xx
105. Second, national legislation (…) provides for no differentiation, limitation or exception according to the objective pursued. It is comprehensive in that it affects all persons using electronic communication services, even though those persons are not, even indirectly, in a situation that is liable to give rise to criminal proceedings. It therefore applies even to persons for whom there is no evidence capable of suggesting that their conduct might have a link, even an indirect or remote one, with serious criminal offences. Further, it does not provide for any exception, and consequently it applies even to persons whose communications are subject, according to rules of national law, to the obligation of professional secrecy.
xx xx xx
if it is to be ensured that data retention is limited to what is strictly necessary, it must be observed that, while those conditions may vary according to the nature of the measures taken for the purposes of prevention, investigation, detection and prosecution of serious crime, the retention of data must continue nonetheless to meet objective criteria, that establish a connection between the data to be retained and the objective pursued. In particular, such conditions must be shown to be such as actually to circumscribe, in practice, the extent of that measure and, thus, the public affected.”
183) With respect to measures for data security and data protection the court held :
“122. Those provisions require those providers to take appropriate technical and organisational measures to ensure the effective protection of retained data against risks of misuse and against any unlawful access to that data. Given the quantity of retained data, the sensitivity of that data and the risk of unlawful access to it, the providers of electronic communications services must, in order to ensure the full integrity and confidentiality of that data, guarantee a particularly high level of protection and security by means of appropriate technical and organisational measures. In particular, the national legislation must make provision for the data to be retained within the European Union and for the irreversible destruction of the data at the end of the data retention period.”
184) In BVerfG74, the German Constitutional Court rendered on March 02, 2010 a decision by which provisions of the data retention legislation adopted for, inter alia, the prevention of crime were rendered void because of lack of criteria for rendering the data retention proportional.
185) In Maximillian Schrems v. Data Protection Commissioner75, the CJEU struck down the transatlantic US-EU Safe Harbor agreement that enabled companies to transfer data from Europe to the United States on the ground that there was not an adequate level of safeguard to protect the data. It held that the U.S. authorities could access the data beyond what was strictly necessary and proportionate to the protection of national security. The subject had no administrative or judicial means of accessing, rectifying or erasing their data.
186) In Szabo and Vissy v. Hungary76, the ECtHR held unanimously that there had been a violation of Article 8 (right to respect for private and family life, the home and correspondence) of the European Convention on Human Rights. The case concerned Hungarian legislation on secret anti-terrorist surveillance introduced in 2011. The court held that the legislation in question did not have sufficient safeguards to avoid abuse. Notably, the scope of the measures could include virtually anyone in Hungary, with new technologies enabling the Government to intercept masses of data easily concerning even persons outside the original range of operation. Furthermore, the ordering of such measures was taking place entirely within the realm of the executive and without an assessment of whether interception of communications was strictly necessary. There were no effective remedial measures in place, let alone judicial ones. The court held:
“77. … Rule of law implies, inter alia, that an interference by the executive authorities with an individual right should be subject to an effective control which should normally be assured by the judiciary, at least in the last resort…”
187) Thus, it is evident from various case laws cited above, that data collection, usage and storage (including biometric data) in Europe requires adherence to the principles of consent, purpose and storage limitation, data differentiation, data exception, data minimization, substantive and procedural fairness and safeguards, transparency, data protection and security. Only by such strict observance of the above principles can the State successfully discharge the burden of proportionality while affecting the privacy rights of its citizens.
188) The jurisprudence with respect to collection, use and retention of biometric information in the United States differs from the EU. In the US context, there is no comprehensive data protection regime. This is because of the federal system of American government, there are multiple levels of law enforcement-federal, state, and local. Different states have differing standards for informational privacy. Moreover, the U.S. has a sectoral approach to privacy, i.e. laws and regulations related to data differ in different sectors such as health sector or student sector. In most cases, however, the Fourth Amendment which prohibits “unreasonable searches and seizures” by the government has been read by courts to envisage various levels data protection.
189) At this juncture, we are not entering the debate as to whether the jurisprudence developed in United States is to be preferred or E.U. approach would be more suitable. Fact remains that importance to data protection in processing the data of the citizens is an accepted norm.
190) Observance of this fundamental principle is necessary to prevent a disproportionate infringement of the Fundamental Right of Privacy of a citizen. The question which now needs to be addressed is whether the Aadhaar Act and Rules incorporate these principles of data protection. We have already taken note of the provisions in the Act, which relate to data protection. However, a detailed analysis of the provisions of the Act needs to be undertaken for this purpose having regard to the principles that have emerged from case law in other jurisdiction and noted in paragraph 187 above.
Data Minimisation:
191) The petitioners have argued that the Act enables data collection indiscriminately regarding all aspects of a person (biometrics, demographic details, authentication records, meta-data related to transaction) even though such data has no nexus to the purported object of subsidies, thus violating the principle of data minimization. The data collected is sufficient to indicate religion, class, social status, income, education and intimate personal details. Under Section 32 of the Act, authentication records are stored in the central database in the manner prescribed under the Regulations. Regulation 26 of the Authentication Regulations requires UIDAI to store “authentication transaction data” consisting of:
(a) authentication request data received including PID block;
(b) authentication response data sent;
(c) meta data related to the transaction; and
(d) any authentication server side configurations as necessary. The authentication record affords access to information that can be used and analyzed to systematically track or profile an individual and her activities.
192) As per the respondents, Aadhaar involves minimal identity information for effective authentication. Four types of information collected for providing Aadhaar:
(i) Mandatory demographic information comprising name, date of birth, address and gender [Section 2(k) read with Regulation 4(1) of the Aadhaar (Enrolment and Update) Regulations, 2016];
(ii) Optional demographic information [Section 2(k) read with Regulation 4(2) of the Aadhaar (Enrolment and Update) Regulations, 2016];
(iii) Non-core biometric information comprising photograph;
(iv) Core biometric information comprising finger print and iris scan.
193) Demographic information, both mandatory and optional, and photographs does not raise a reasonable expectation of privacy under Article 21 unless under special circumstances such as juveniles in conflict of law or a rape victim’s identity. Today, all global ID cards contain photographs for identification alongwith address, date of birth, gender etc. The demographic information is readily provided by individuals globally for disclosing identity while relating with others and while seeking benefits whether provided by government or by private entities, be it registration for citizenship, elections, passports, marriage or enrolment in educational institutions.
Email ids and phone numbers are also available in public domain, For example in telephone directories. Aadhaar Act only uses demographic information which are not sensitive and where no reasonable expectation of privacy exists – name, date of birth, address, gender, mobile number and e mail address. Section 2(k) specifically provides that Regulations cannot include race, religion, caste, tribe, ethnicity, language, records of entitlement, income or medical history. Thus, sensitive information specifically stand excluded.
194) We find that Section 32 (3) of the Aadhaar Act specifically prohibits the authority from collecting, storing or maintaining, either directly or indirectly any information about the purpose of authentication. The proviso to Regulation 26 of Authentication Regulations is also to the same effect.
195) Thus, the principle of data minimization is largely followed.
196) With this, we advert to some other provisions, challenge whereof is based on threat to security of the data. These are Section 2(c), Section 2(g) and Section 2(h) read with Section 10 of the Aadhaar Act. Section 2(c) pertains to authentication. It is a process by which Aadhaar number along with demographic information or biometric information of an individual is submitted to the CIDR for its verification. On submission thereof, the CIDR verifies the correctness or lack of it. CIDR is defined in Section 2(h). Section 10 lays down that the Authority may engage one or more entities to establish or maintain the CIDR and to perform any other functions as may be specified by regulations.
197) Insofar as authentication process is concerned, that has already been taken note of above. The manner in which it is explained by the respondent authority, that may not pose much of a problem. As noted earlier, while seeking authentication, neither the location of the person whoso identity is to be verified nor the purpose for which authentication of such identity is needed, comes to the knowledge of the Authority and, therefore, such data collected by the Authority.
Therefore, the threat to real time surveillance and profiling may be far-fetched. The respondents have explained that Section 2(d) defines “authentication record” to mean the record of the time of authentication, identity of the RE and the response provided by the authority”, Regulation 26 (a) to (d) does not go beyond the scope of Section 2(d). None of the four clauses of Regulation 26 entitle the authority to store data about the purpose for which authentication is being done.
The device can therefore only tell the authority the identity of the RE, the PID, the time and nature of response, the code of the device and the authentication server side configurations. Identity of the RE does not include details of the organization which is seeking authentication as an RE provides authentication service to large number of government organizations who have agreements with it. Such a mechanism preventing the authority from tracking the nature of activity for which the authentication was required. To illustrate nic.in is an RE which provides authentication service to large number of Government organisations who have agreements with it. The authentication record would only contain information about the identity about the RE. It will give information only about the RE (nic.in) and not about the organisation which is requiring authentication through the RE. In most cases the authentication is one time.
Mr. Dwivedi has also explained that yet again, there may be organisations, which have branches in different part of India. Assuming Apollo Hospital (although in fact it is not an RE) has five branches in India. If Apollo Hospital seeks authentication as an RE, the authentication record will merely tell the identity of Apollo Hospital and its device code, but it will not indicate which branch of Apollo was seeking authentication and from which part of the country. Further, assuming that the Indira Gandhi International Airport is an RE and there is requirement of authentication at the point of entry and/or exit. All that the record will show that the ANH has entered the airport at a particular time but it will not show by which plane he is flying and to what destination. At the time of exit, it will only show that the person has exited the airport at a particular time. It will not show from which flight he has arrived and from which destination and at what time he has arrived or with whom he travelled.
198) However, other apprehension of the petitioners is that storing of data for a period of seven years as per Regulations 20 and 26/27 of the Aadhaar (Authentication) Regulations, 2016 is too long a period. We may reproduce Regulations 26 and 27 of the Aadhaar (Authentication) Regulations, 2016 hereunder:
“26. Storage and Maintenance of Authentication Transaction Data –
(1) The Authority shall store and maintain authentication transaction data, which shall contain the following information:-
(a) authentication request data received including PID block;
(b) authentication response data sent;
(c) meta data related to the transaction;
(d) any authentication server side configurations as necessary: Provided that the Authority shall not, in any case, store the purpose of authentication.
27. Duration of storage –
(1) Authentication transaction data shall be retained by the Authority for a period of 6 months, and thereafter archived for a period of five years.
(2) Upon expiry of the period of five years specified in subregulation (1), the authentication transaction data shall be deleted except when such authentication transaction data are required to be maintained by a court or in connection with any pending dispute.”
199) It is also submitted that Section 10 which authorises the Authority to engage one or more entities, which may be private entities, to establish and maintain CIDR is a serious threat to privacy and it even amounts to compromise on national sovereignty and security. Insofar as first argument is concerned, there appears to be some force in that. If authentication is the only purpose, we fail to understand why this authentication record is needed to be kept for a period of 2+5 years. No satisfactory explanation in this behalf was given.
200) Insofar as information regarding metadata is concerned, we may note that the respondents distinguished between three types of meta-data :technical, business and process metadata. Process metadata describes the results of various operations such as logs key data, start time, end time, CPU seconds used, disk reads, disk writes, and rows processed. This data is valuable for purposes of authenticating transaction, troubleshooting , security, compliance and monitoring and improving performance. They submit that the metadata contemplated under this Regulation is Process metadata.
201) However, metadata is not defined in the Aadhaar Act. In common parlance, it is understood as information about data, example whereof was given by Mr. Sibal that the text of a message exchanged between two persons would be the data itself. However, surrounding circumstances like when the message was sent; from whom and to whom the message was sent; and location from which the message was sent would include meta data.
As noted above, Mr. Dwivedi had tried to explain it away by stating that there are three types of meta data, namely, technical, business and process meta data. According to him, meta data under the Aadhaar Act refers to only process meta data. In support, he had referred to Section 2(d) of the Aadhaar Act which defines ‘authentication record’ to mean the record of the time of authentication, identity of requesting entity and the response provided by the Authority. He, thus, submitted that Regulation 26 would not go beyond Section 2(d). However, aforesaid explanation that meta data refers to process data only does not find specific mention. There is, thus, need to amend Regulation 26 to restrict it to process meta data, and to exclude other type of meta data specifically.
Purpose Limitation:
202) As per the petitioners, there is no purpose limitation. Identity information collected for one purpose under the Act can be used for any other (new) purpose. Definition of “benefit” (Section 2(f)) and “service” (Section 2(w)) and “subsidy” (Section 2(x)), to which the personal data collected is supposed to be applied is not identifiable. It is open to the executive to notify that any advantage, gift, reward, relief, payment, provision, facility, utility or any other assistance aid, support, grant subvention, or appropriation may be made conditional on Aadhaar Authentication. Moreover, under Section 57, the State, a body corporate or any person can avail authentication facility and access information under CIDR. This creates an open ended and unspecified set of laws and contracts for which Aadhaar can be used and defeats the principle of informed consent at the time of enrolment and purpose limitation.
203) Respondents controvert the aforesaid submission by arguing that there is purpose limitation under the Aadhaar Act as purpose of use of biometric data in the CIDR is limited to authentication for identification. The Aadhaar holder is made aware of such use of the Aadhaar card at the time of enrolment. The enrolling agency is obliged under the Enrolment Regulations to inform the individual about the manner in which the information shall be used, the nature of recipients with whom the information is to be shared during authentication; and the existence of a right to access information, the procedure for making request for such access and details of the person/ department to whom request can be made. This information to individual is the basis for his consent for enrolment.
204) As per the respondents, Section 57 is not an enabling provision which allows Aadhaar to be used for purposes other than Section 7, but is a limiting provision. It limits its use by State, Body Corporate or a person by requiring it to be sanctioned by any law in force or any contract and making the use subject to the proviso to Section 57. The proviso requires the use of Aadhaar under this Section to be subject to procedure and obligations under Section 8 and Chapter VI of penalties. Section 8(2)(a) requires Requesting Entities (RE) (parties authorized to carry out authentication under Section 57) to obtain the consent of an individual before collecting her identity information for the purposes of authentication in such manner as may be specified by regulations.
Section 8(3) enables this consent to be informed consent by requiring that an individual submitting her identity information for authentication shall be informed of the nature and the use of the information that may be shared upon authentication and the alternatives to submission of identity information to the requesting entity. This aspect is discussed in detail at a later stage, as it touches upon privacy aspects as well. Suffice it is to mention here that we have found some portion of Section 57 as offending and declared that unconstitutional. Insofar as Sections 2(f), (w) and (x) are concerned, these provisions are discussed at a later stage77. We would like to mention here that we have read down these provisions. The aforesaid measure would subserve the purpose limitation as well.
Time Period for Data Retention:
205) We have touched upon this aspect hereinabove. According to petitioners, the data is allowed to be retained for an unreasonable long period of time. Regulation 27 of the Authentication Regulations requires the UIDAI to retain the “authentication transaction data” (which includes the meta data) for a period of 6 months and to archive the same for a period of 5 years thereafter. Regulation 18(3) and 20(3) allow Requesting entities (RE) and Authentication Service Agencies to retain the authentication logs for a period of 2 years and then archive them for 5 years. It is required to be deleted only after 7 years unless retained by a court.
The right of the citizen to erasure of data or right to be forgotten is severely affected by such regulation. There is no provision to delete the biometric information in any eventuality once a person is enrolled. We do not find any reason for archiving the authentication transaction data for a period of five years. Retention of this data for a period of six months is more than sufficient after which it needs to be deleted except when such authentication transaction data are required to be maintained by a Court or in connection with any pending dispute. Regulations 26 and 27 shall, therefore, be amended accordingly.
Data Protection and Security:
206) Petitioners argued that there are not enough safeguards for data protection and security in the Act. Section 28 of the Act which addresses security and confidentiality of information is vague and fails to lay down any standard of data security or prescribe any cogent measures which are to be taken to prevent data breaches. Section 54 empowers UIDAI to make regulations related to various data management processes, security protocol and other technology safeguards. The Aadhaar (Data Security) Regulations, 2016 passed by UIDAI under Section 54, vest in the authority a discretion to specify “an information security policy” (Regulation 3).
This leads to excessive delegation. Alternatively, it has not been subject to parliamentary oversight which Regulations under Section 54 require. Further, the CIDR central database, unlike the ASAs and REs (under Authentication Regulation 22(1)), are not required to be located in data centres. The personal data is accessible by private entities such as AUAs and KUAs and other private entities such as banks, insurance companies and telecom service providers. There have been numerous data breaches in the Aadhaar system. These establish its vulnerability. There are not enough safeguards from data hack and data leak. The data is being used by private parties to build comprehensive databases containing information and profiles of individuals. Thus the project also lacks transparency of data and its use.
207) The Respondents contend that strong measures for data protection and security, taken at all stages of data collection, transfer, storage and use. After deliberating over respective contentions, we are of the opinion that the following explanation furnished by the respondents on various facets ensures data protection and security to a considerable extent:
(a) CIDR
208) Regulation 3(i) & (j) of Aadhaar (Data Security) Regulation 2016 enables partitioning of CIDR network into zones based on risk and trust and other security measures. CIDR being a computer resource is notified to be a “Protected System” under Section 70 of the IT Act, 2000 by the Central Government on 11.12.2015. Anyone trying to unlawfully gain access into this system is liable to be punished with 10 years imprisonment and fine. The storage involves end to end encryption, logical partitioning, firewalling and anonymisation of decrypted biometric data. Breaches of penalty are made punitive by Chapter VII of the Act. Biometric information is deemed to be an “electronic record”, and “Sensitive personal data or information” under the IT Act, 2000. There are further guards under The Aadhaar (Data Security ) Regulation, 2016.
(b) Requesting Entities (AUA and KUA)
209) Other identity information is shared with Requesting Entity (AUAs and KUAs) only for the limited purpose of authentication. The data is transferred from the RE to the ASA (Authentication Service Agency) to the CIDR in an encrypted manner through a leased line circuitry using secure Protocols (Regulation 9 of the Authentication Regulations). The storage of data templates is in safely located servers with no public internet inlet/outlet, and offline storage of original encrypted data (PID blocks). There are safety and security provisions such as audit by Information Systems Auditor. REs are appointed through agreement. REs can enter into agreement with sub-AUA or sub-KUA with permission of the of UIDAI.
Whatever identity information is obtained by the requesting entity is based on a specific consent of the Aadhaar number holder. The e-KYC data shared with the RE can only be after prior consent of the Aadhaar holder. Such data cannot be shared and has to be stored in encrypted form. The biometric information used is not permitted to be stored only the logs of authentication transactions are maintained for a short period. Full identity information is never transmitted back to RE. There is a statutory bar from sharing Biometric information [Section 29(1)(a)/ Section 29(4)]. The Data centres of ASA, REs and CIDR should be within the territory of India.
(c) Enrolment Agencies and Registrars
210) The enrolment and Authentication processes are strongly regulated so that data is secure. The Enrolment agency, which collects the biometric and demographic of the individuals during enrolment, is appointed either by UIDAI or by a Registrar [Section 2(s)]. The registrar are appointed through MoUs or agreements for enrolment and are to abide by a code of conduct and processes, policies and guidelines issued by the authority. They are responsible for the process of enrolment. Categories of persons eligible for appointment are limited by the Regulations. The agency employees a certified supervisor, an operator and a verifier under Enrolment and Update Regulations. Registrars, enrolling agencies are obliged to use the software provided or authorized by UIDAI for enrolment purpose.
The standard software has security features as specified by Authority. All equipment used are as per the specification issued by the authority. The Registrars are prohibited from using the information collected for any purpose other than uploading the information to CIDR. Sub-contracting of enrolment function is not allowed. The Code of Conduct contains specific directions for following the confidentiality, privacy and security protocols and submission of periodic reports of enrolment. Not only there are directions prohibiting manipulation and fraudulent practices but the Act contains penal provisions for such violations in Chapter VII of the Regulations.
The enrolment agencies are empanelled by the authority. They are given an enrolling agency code using which the Registrar can onboard such agency to the CIDR. The enrolment data is uploaded to the Central Identities Data Repository (CIDR) certified equipment and software with a digital signature of the registrar/enrolling agency. The data is encrypted immediately upon capture. The decryption key is with the UIDAI solely. Section 2(ze) of the IT Act, which defines ‘secure systems’ and Section 2(w) of the Act, which defines ‘intermediaries’ apply to the process.
(d) Authentication Service Agency
211) Authentication only becomes available through the Authentication Service Agency (ASA). They are regulated by the Aadhaar (Authentication) Regulations, 2016. Their role and responsibilities are provided by Authentication Regulation 19. They are to use certified devices, equipment, or software are duly registered with or approved or certified by the Authority/agency. The systems and operations are audited by information system auditor. The REs pass the encrypted data to the CIDR through the ASA and the response (Yes/No authentication or e-KYC information) also takes the same route back. The server of the ASA has to perform basic compliance and completeness checks on the authentication data packet before forwarding it to the CIDR.
(e) Hacking
212) As far as hacking is concerned, the respondents submit that the authority has involved adequate firewalling and other safety features. The biometric data stored in the CIDR is stored offline. Only templates are online. So far there has been no incidence of hacking. However, the authority is conscious of the hackers and it constantly updates itself to safe guard the data. It may, however, be mentioned that of late certain reports have appeared in newspapers to the effect that some people could hack the website of CIDR, though it is emphatically denied by the UIDAI. Since there are only newspapers reports to this effect which appeared after the conclusion of hearing in these cases and, therefore, parties could not be heard on this aspect, we leave this aspect of the matter at that with a hope that CIDR would find out the ways and means to curb any such tendency.
(f) Biometric Solution Providers
213) With respect to foreign companies owning software, Respondents submit that UIDAI has entered into licensing agreements with foreign biometric solution providers (BSP) for software. Even thought the source code of the software are retained by the BSP as it constitutes their Intellectual property, the data in the server rooms is secure as the software operates automatically and the biometric data is stored offline. There is no opportunity available to BSP to extract data as they have no access to it.
Substantive, Procedural or Judicial Safeguards:
214) Another grievance of the petitioners is that the Act lacks any substantive, procedural or judicial safeguards against misuse of individual data. Section 23(2)(k) which allows sharing information of Aadhaar holders, in such manner as may be specified by regulations. This means individual’s identity information can be shared with the government. This may include demographic and core biometric information, include aspects such as DNA profiles, handwriting, voice-print etc., (in the future). Subsequent linkage with various state and non-state actors that interact with such individual may enable UIDAI to share greater information. The police can easily gain access to all biometric information, bank accounts of the individual, all mobile phones, and meta data associated with any associated linkages, information relating to all mutual funds, policies etc., information relating to travel by air or by rail by such person and so on.
215) In other cases of collection of information of this kind under other laws, there are exhaustive legal procedures. For example, Section 73 of the Indian Evidence Act, 1872 which allows the taking of handwriting samples only if necessary “for the purposes of any (specific ) investigation”, or in order to compare writing or signature that appears in relation to the facts of a particular case. Section 53 of the CrPC allows medical examination of a person arrested on a charge of committing an offence if reasonable grounds exist for believing that an examination of his person will afford evidence as to the commission of the offence. Similarly provisions in various other statutes such as of the Foreign Exchange Regulation Act, 1973 (Sections 34-48); the Prevention of Money-Laundering Act, 2002 (Sections 17-19); the Narcotic Drugs and Psychotropic Substances Act, 1985 (Sections 41-42) and the Customs Act, 1962 (Chapter 13) which allow for search, seizure or even arrest, and thereby provide access to personal information also bear a nexus with a particular crime under investigation.
216) As per the petitioners, the Investigating Agency can presently access fingerprints, only limited to cases of citizens who were arrested on the reasonable basis of having committed a crime, or were convicted of a crime, as per provisions of the Identification of Prisoners Act. In all such circumstances, not only are there adequate safeguards- such as permission from the Magistrate that collection is necessary for the purpose of investigation, but persons accused of an offence presently can claim protection under Article 20(3), thereby making it incumbent upon the investigating agency to obtain such information in accordance with law, as described above. Further, unlike the Aadhaar Act, present day criminal statutes contain provisions for destruction of some kinds of core biometric data obtained [Section 7 of the Identification of Prisoners Act, 1920]. No such safeguards exist under the Aadhaar Act.
217) It is also argued that Section 33(2), which permits disclosure of identity information and authentication records under direction of an officer not below the rank of Jt. Secretary to Central Government in the interest of national security, has no provision for judicial review. The Oversight Committee does not have a judicial member.
218) Respondents submitted that Section 29 of the Aadhaar Act provides protection against disclosure of core biometric information. The biometric information cannot shared with anyone for any reason whatsoever; or used for any purpose other than generation of Aadhaar numbers and authentication under this Act. Section 8 ensure that the during authentication, biometric information of an individual is only used for submission to the Central Identities Data Repository
219) We are of the view that most of the apprehensions of the petitioners stand assuaged with the treatment which is given by us to some of the provisions. Some of these are already discussed above and some provisions are debated in the next issue. Summary thereof, however, can be given hereunder:
(a) Authentication records are not to be kept beyond a period of six months, as stipulated in Regulation 27(1) of the Authentication Regulations. This provision which permits records to be archived for a period of five years is held to be bad in law.
(b) Metabase relating to transaction, as provided in Regulation 26 of the aforesaid Regulations in the present form, is held to be impermissible, which needs suitable amendment.
(c) Section 33 of the Aadhaar Act is read down by clarifying that an individual, whose information is sought to be released, shall be afforded an opportunity of hearing.
(d) Insofar as Section 33(2) of the Act in the present form is concerned, the same is struck down.
(e) That portion of Section 57 of the Aadhaar Act which enables body corporate and individual to seek authentication is held to be unconstitutional.
(f) We have also impressed upon the respondents, as the discussion hereinafter would reveal, to bring out a robust data protection regime in the form of an enactment on the basis of Justice B.N. Srikrishna (Retd.) Committee Report with necessary modifications thereto as may be deemed appropriate.
220) With the removal of the aforesaid provisions from the statute and the Rules, coupled with the statement of the Authority on affidavit that there is no record of any transactions carried out by the individuals which is even known (and, therefore, no question of the same being retained by the Authority), most of the apprehensions of the petitioners are taken care of. At the same time, we may remind ourselves of the judgment in G. Sundarrajan v. Union of India & Ors.78. In that case, the Court noted the safety and security risk in the setting up of the nuclear power plant in the backdrop of Fukushima disaster and Bhopal Gas tragedy. Yet, keeping in view the importance of generation of nuclear energy, the Court observed that a balance should be struck between production of nuclear energy which was of extreme importance for the economic growth, alleviation of poverty, generation of employment, and the smaller violation to right to life under Article 21.
It took note of the opinion of experts committee and observed that ‘adequate safety measure’ have been taken. It noted huge expenditure of money running into crores and observed ‘apprehension however legitimate it may be, cannot override the justification of the project. Nobody on this earth can predict what would happen in future and to a larger extent we have to leave it to the destiny. But once the justification test is satisfied, the apprehension test is bound to fail. Apprehension is something we anticipate with anxiety or fear, a fearful anticipation, which may vary from person to person’.
The Court also held that ‘nuclear power plant is being established not to negate right to life but to protect the right to life guaranteed under Article 21 of the Constitution. No doubt, the Court took a view that this interest of people needed to be respected for their human dignity which was divinity. However, it was also stressed that generation of nuclear energy was a nuclear necessity and the project was for larger public benefit and consequently, individual interest or smaller public interest must yield. In such a situation, necessity for ‘adequate care, caution, and monitoring at every stage’ and ‘constant vigil’ was emphasised. Safety and security was read into Article 21. Acknowledging that proportionality of risk may not be ‘zero’, regard being had to the nature’s unpredictability, the Court ruled that all efforts must be made to avoid disaster by observing the highest degree of constant alertness. In the directions of the Court, it was observed that ‘maintaining safety is an ongoing process not only at the design level but also during the operation’. In the present case as well, we have come to the conclusion that Aadhaar Act is a beneficial legislation which is aimed at empowering millions of people in this country. The justification of this project has been taken note of in detail, which the subsequent discussion shall also demonstrate. In such a scenario only on apprehension, the project cannot be shelved. At the same time, data protection and data safety is also to be ensured to avoid even the remote possibility of data profiling or data leakage.
221) Notwithstanding the statutory provision discussed above, we are of the view that there is a need for a proper legislative mechanism for data protection. The Government is not unmindful of this essential requirement. During the arguments it was stated by Mr. K.K. Venugopal, learned Attorney General, that an expert committee heading by Justice B.N. Srikrishna (Retd.) was constituted which was looking into the matter. The said Committee has since given its report.
222) In this behalf, it may be worthwhile to mention that one of the first comprehensive reports on data protection and informational privacy was prepared by the Group of Experts79 constituted by the Planning Commission of India under the Chairmanship of Retd. Justice A.P. Shah, which submitted a report on 16 October, 2012. The five salient features of this report were expected to serve as a conceptual foundation for legislation protecting privacy. The framework suggested by the expert group was based on five salient features:
(i) Technological neutrality and interoperability with international standards;
(ii) Multi-Dimensional privacy;
(iii) Horizontal applicability to state and non-state entities;
(iv) Conformity with privacy principles; and
(v) A co-regulatory enforcement regime.
223) The Union Government, on 31 July 2017, had constituted a committee chaired by Retd.Justice B N Srikrishna, former Judge of the Supreme Court of India to review data protection norms in the country and to make recommendations. The Committee recently released its report and the first draft of the Personal Data Protection Bill, 2018 which comprehensively addresses the processing of personal data where such data has been collected, disclosed, shared or otherwise processed within the territory of India. The bill has incorporated provisions and principles from the Europe’s General Data Protection Regulation (EUGDPR).
224) The Draft Bill replaces the traditional concepts of data controller i.e. the entity which processes data and data subject i.e. the natural person whose data is being collected, with data ‘fiduciary’ and data ‘principal’. It aims to create a trust-based relationship between the two.
225) The Bill largely incorporates data protection principles from the EUGDPR and EU data protection jurisprudence, including fair and reasonable processing of data, purpose limitation, collection limitation, lawful processing, storage limitation, data quality and accountability. The Draft bill and the report cull out rights and obligations of the data fiduciary and data controller respectively. These rights include the right to access and correction, the right to data portability and right to be forgotten – a right to prevent or restrict disclosure of personal data by a fiduciary. Most importantly, consent has been given a crucial status in the draft data protection law. Thus, a primary basis for processing of personal data must be individual consent. This consent is required to be free, informed, specific, clear and, in an important addition, capable of being withdrawn. The Authority under the Bill is obligated and empowered to ensure protection of data from misuse and compromise.
226) Processing of biometric data, classified as ‘Sensitive Personal Data’ (SPD), by the data fiduciary mandates additional safeguards (mentioned under Chapter IV of the Bill). For example, the data fiduciary is required to undertake Data Protection Impact Assessment under the provisions of the Bill. The Draft Bill allows processing of biometric data for the exercise of any function of the State authorised by law for the provision of any service or benefit to the data principal. Special provisions to protect sensitive and personal data of children also exist. For example, Data fiduciaries shall be barred from profiling, tracking, or behavioural monitoring of, or targeted advertising directed at, children and undertaking any other processing of personal data that can cause significant harm to the child.
227) For security of data and protection of breach, the Draft Bill has separate provisions which require use of methods such as deidentification and encryption and other steps necessary to protect the integrity of personal data and to prevent misuse, unauthorised access to, modification, disclosure or destruction of personal data. The data fiduciary is required to immediately notify the Authority of any personal data breach relating to any personal data processed by the data fiduciary where such breach is likely to cause harm to any data principal. It also incorporates a provision for Grievance Redressal.
228) The Draft Bill creates several exceptions and exemptions for processing data by the State. These are situations where rights and obligations of data principals and data fiduciaries may not apply in totality. Such situations include national security, prevention of crime, allocation of resources for human development, protection of revenue, etc. The committee asserts that such exceptions have been envisaged in the Puttaswamy judgement as legitimate interests of the state and satisfy the proportionality test.
229) The Srikrishna Committee Report and the Draft Data Protection Bill are the first articulation of a data protection law in our country. They have incorporated many of the progressive data protection principles inspired by the EUGDPR. There may be indeed be scope for further fine tuning of this law through a consultative process, however, we are not far away from a comprehensive data protection regime which entrenches informational and data privacy within our laws and legal system. We hope that there would be a robust statutory regime in place in near future.
230) The aforesaid discussion leads us to hold that the protection that there is going to be a surveillance state created by the Aadhaar project is not well founded, and in any case, taken care of by the diffluence exercise carried out with the striking down certain offending provisions in their present form.
Privacy:
Whether Aadhaar Act violates right to privacy and is unconstitutional on this ground? (This issue is considered in the context of Section 7 and Section 8 of the Act.)
231) The petitioners submit that right to privacy and dignity and individual autonomy have been established by various cases. In Gobind v. State of M.P.80, this Court held: “the significance of man’s spiritual nature, of his feelings and of his intellect and that only a part of the pain, pleasure, satisfaction of life can be found in material things and therefore they must be deemed to have conferred upon the individual as against the Government, a sphere where he should be let alone.
xx xx xx
24. Any right to privacy must encompass and protect the personal intimacies of the home, the family, marriage, motherhood, procreation and child rearing. This catalogue approach to the question is obviously not as instructive as it does not give analytical picture of the distinctive characteristics of the right of privacy. Perhaps, the only suggestion that can be offered as unifying principle underlying the concept has been the assertion that a claimed right must be a fundamental right implicit in the concept of ordered liberty.
25. Rights and freedoms of citizens are set forth in the Constitution in order to guarantee that the individual, his personality, and those things stamped with his personality shall be free from official interference except where a reasonable basis for intrusion exists. “Liberty against Government” a phrase coined by Professor Corwin expresses this idea forcefully. In this sense, many of the fundamental rights of citizens can be described as contributing to the right to privacy.
26. As Ely says: “There is nothing to prevent one from using the word ‘privacy’ to mean the freedom to live one’s life without governmental interference. But the Court obviously does not so use the term. Nor could it, for such a right is at stake in every case.”
232) To recapitulate briefly, the judgment of K.S. Puttaswamy has affirmed the following –
(i) privacy has always been a natural right, and the correct position has been established by a number of judgments starting from Gobind. Privacy is a concomitant of the right of the individual to exercise control over his or her personality. Equally, privacy is the necessary condition precedent to the enjoyment of any of the guarantees in Part III.
The fundamental right to privacy would cover at least three aspects-
(i) intrusion with an individual’s physical body,
(ii) informational privacy and
(iii) privacy of choice. Further, one aspect of privacy is the right to control the dissemination of personal information.
Every individual should have a right to be able to control exercise over his/her own life and image as portrayed in the world and to control commercial use of his/her identity.
(ii) The sanctity of privacy lies in its functional relationship with dignity. Privacy ensures that a human being can lead a life of dignity by securing the inner recesses of the human personality from unwanted intrusions. While the legitimate expectation of privacy may vary from intimate zone to the private zone and from the private to the public arena, it is important to underscore that privacy is not lost or surrendered merely because the individual is in a public place. Privacy is a postulate of dignity itself. Privacy concerns arise when the State seeks to intrude into the body and the mind of the citizen.
(iii) Privacy as intrinsic to freedom, liberty and dignity. The right to privacy is inherent to the liberties guaranteed by Part-III of the Constitution and privacy is an element of human dignity. The fundamental right to privacy derives from Part-III of the Constitution and recognition of this right does not require a constitutional amendment. Privacy is more than merely a derivative constitutional right. It is the necessary basis of rights guaranteed in the text of the Constitution.
(iv) Privacy has both positive and negative content. The negative content restrains the State from committing an intrusion upon the life and personal liberty of a citizen. Its positive content imposes an obligation on the State to take all necessary measures to protect the privacy of the individual.
(v) Informational Privacy is a facet of right to privacy. The old adage that ‘knowledge is power’ has stark implications for the position of individual where data is ubiquitous, an all encompassing presence. Every transaction of an individual user leaves electronic tracks, without her knowledge. Individually these information silos may seem inconsequential. In aggregation, information provides a picture of the beings. The challenges which big data poses to privacy emanate from both State and non-State entities.
(vi) Right to privacy cannot be impinged without a just, fair and reasonable law.
It has to fulfil the test of proportionality i.e.
(i) existence of a law
(ii) must serve a legitimate State aim and
(iii) proportionate.
233) We have also remarked, in paragraph 85 above, the taxonomy of privacy, namely, on the basis of ‘harms’, ‘interest’ and ‘aggregation of rights’. We have also discussed the scope of right to privacy with reference to the cases at hand and the circumstances in which such a right can be limited. In the process, we have also taken note of the passage from the judgment rendered by Nariman, J. in K.S. Puttaswamy stating the manner in which law has to be tested when it is challenged on the ground that it violates the fundamental right to privacy. Keeping in mind all these considerations and parameters, we proceed to deal with the argument on right to privacy.
234) It is argued that the Aadhaar project, during the pre-Act period (2009/10 – July, 2016), violated the Right to Privacy with respect to personal demographic as well as biometric information collected, stored and shared as there was no law authorizing these actions. In a digital society an individual has the right to protect herself by controlling the dissemination of such personal information. Compelling an individual to establish her identity by planting her biometric at multiple points of service violates privacy involving the person. The seeding of Aadhaar in distinct data bases enables the content of information about an individual that is stored in different silos to be aggregated. This enables the State to build complete profiles of individuals violating privacy through the convergence of data.
235) It is also contended that the citizen’s right to informational privacy is violated by authentication under the Aadhaar Act inasmuch as the citizen is compelled to ‘report’ her actions to the State. Even where a person is availing of a subsidy, benefit or service from the State under Section 7 of the Act, mandatory authentication through the Aadhaar platform (without an option to the citizen to use an alternative mode of identification) violates the right to informational privacy. An individual’s rights and entitlements cannot be made dependent upon an invasion of his or her bodily integrity and his or her private information which the individual may not be willing to share with the State. The bargain underlying section 7 is an unconscionable, unconstitutional bargain. Section 7 is against the constitutional morality contained in both Part III as well the Part IV of the Constitution of India.
236) It was also highlighted that today the fastest growing businesses are network orchestrators, the likes of Facebook and Uber, which recreate a network of peers in which participants interact and share value in creation. The most important assets for these network orchestrators is information. Although, individuals share information with these entities, such information is scattered, not concentrated in a single authority or aggregated. If information, collected in different silos is aggregated and centralized, it can afford easy access to a person’s complete profile, including her social groups, proclivities, habits, inclinations, tastes etc. The entity that holds the key to such information would then be in an extremely powerful position, especially if such entity is the State. Since informational privacy is a part of Right to Privacy, it had to be saved. The peittioners pointed out that the significance of information being aggregated was noted by Hon’ble Court in K.S. Puttaswamy as follows:
“300 …Yet every transaction of an individual user and every site that she visits, leaves electronic tracks generally without her knowledge. These electronic tracks contain powerful means of information which provide knowledge of the sort of person that the user is and her interests. Individually, these information silos may seem inconsequential. In aggregation, they disclose the nature of the personality: food habits, language, health, hobbies, sexual preferences, friendships, ways of dress and political affiliation. In aggregation, information provides a picture of the being: of things which matter and those that don’t, of things to be disclosed and those best hidden…
xx xx xx
305. Daniel J Solove deals with the problem of “aggregation”. Businesses and governments often aggregate a variety of information fragments, including pieces of information which may not be viewed as private in isolation to create a detailed portrait of personalities and behaviour of individuals. Yet, it is now a universally accepted fact that information and data flow are “increasingly central to social and economic ordering”. Individuals are identified with reference to tax records, voting eligibility, and government-provided entitlements. There is what is now described as “‘veillant panoptic assemblage’, where data gathered through the ordinary citizen’s veillance practices finds its way to state surveillance mechanisms, through the corporations that hold that data.”
237) It was further argued that test of proportionality was not satisfied as the extent of information collected is not proportionate to the ‘compelling interest of the State’. Various judgments were citied where the principle of proportionality has been established by this court. In Chairman, All India Railway Recruitment Board v. K Shyam Kumar and others81, this Court held as follows:
“37. …Proportionality requires the court to judge whether action taken was really needed as well as whether it was within the range of courses of action which could reasonably be followed. Proportionality is more concerned with the aims and intention of the decision-maker and whether the decision-maker has achieved more or less the correct balance or equilibrium. The court entrusted with the task of judicial review has examine whether decision taken by the authority is proportionate i.e. well balanced and harmonious, to this extent the court may indulge in a merit review and if the court finds that the decision is proportionate, it seldom interferes with the decision taken and if it finds that the decision is disproportionate i.e. if the court feels that it is not well balanced or harmonious and does not stand to reason it may tend to interfere.”
238) Attention was also drawn to the judgment in Modern Dental College & Research Centre, wherein this Court established the four-limb test of proportionality. It was argued that Aadhaar failed to meet the test laid down therein.
239) According to the petitioners, there is no compelling state interest for State to know the details of the location and time of using Aadhaar authentication. Likewise, there are various other methods available for identification. Submission was that one of the objects of the Aadhaar project is to ensure targeted delivery in the disbursement of government subsidies benefits and services in India. Identification for this purpose can be carried out by various other identity documents issued by the government of India, such as passport, voting card, ration card, driving license, job card issued by NREGA duly signed by an officer of the State government, employment certificate by a public authority, birth certificate, school leaving certificate, PAN card, overseas Indian citizen card/PIO/OCI of Indian origin card.
There is no justification to impose Aadhaar under as the exclusive means of identification under Section 7, without which a person would be unable to secure her entitlements. Such mandate would not only infringe upon the privacy of a person and violate a person’s fundamental rights, but would also unreasonably deprive a person of her entitlements on a ground that has little connection with her right to receive such entitlements.
240) Judgment in the case of Jordan & Ors v. State82 was also cited wherein Sachs & O’Regan JJ. concurringly held that continuum of privacy rights start with the inviolable inner self, move to the home, and end with the public realm; and that commitment to dignity invests great value in the inviolability and worth of the body. Decisional privacy allows individuals to make decisions about their own body, and is an aspect of right to self determination. It is underscored by personal autonomy, which prevents the State from using citizens as puppets and controlling their body and decisions. Informational privacy deals with a person’s mind and comprises of (i) anonymity, (ii) secrecy, and (iii) freedom.
It is premised on the assumption that all information about a person is in a fundamental way her own, for her to communicate or retain for herself as she sees fit.
241) It was submitted that privacy rights against both the State and non-State actors. There is a qualitative difference between right to privacy against the State and against Non-state actors. Subba Rao. J’s dissent in Kharak Singh, was relied upon wherein it was stated that the existence of concentrated and centralized State power, rather than its actual or potential use that creates the chilling effect and leads to psychological restraint on the ability of citizens to think freely. Therefore, individuals have a higher expectation of privacy from the State. In the vein, it was further submitted that the State was imposing disproportionate and unreasonable State compulsion. States do not have the power to compel their citizens to do particular acts, except in a narrow range of defined circumstances.
As sentinels on the qui vive, Courts are duty bound to protect citizens against State compulsion, whether in the context of forcibly undergoing narco-analysis/lie detectors tests or forcibly undergoing sterilization. Compulsion can be used in limited circumstances such as punishment for law-breaking, compulsion in the aid of law enforcement, and compulsion to prevent potential law-breaking. These include fines, imprisonment, fingerprint collection for criminals and prisoners. Even in medical jurisprudence, the case of Common Cause v. Union of India83 elaborates on the concepts of dignity, bodily integrity and decisional autonomy. For DNA tests and blood tests to be conducted a high standard of evidence is required. Similarly ‘refusal of treatment’ is a constitutionally protected liberty interest in the United States of America as stated in the case of Cruzan v. Director, Missouri Dept. of Health84.
242) The petitioners further submitted that although the Aadhaar Act is ostensibly framed as a voluntary entitlement to establish one’s identity under section 3 read with Section 4(3) of the Aadhaar Act, the actions of the Executive and private entities under sections 7 and 57 have made possession of Aadhaar de facto mandatory. Residents have thus been forced to obtain an Aadhaar number, for continued access to statutory entitlements and services. 252 government schemes have been notified by various Ministries/Departments of the Central Government under section 7 (as on 30.11.2017) requiring Aadhaar as a condition precedent for availing services, subsidies and benefits including for persons with disabilities, for SC/STs, and for rehabilitation of Manual Scavengers. It has also been made mandatory for mobile services, banking and tax payments, registration of students of CBSE, amongst other things. It thus pervades every aspect of an individual’s life. Concomitantly, there is no opt out option in the Aadhaar Act, which makes consent irrevocable and deprives individuals the ability to make decisions about their life.
243) As per the petitioners, this kind of mandatory nature of Section 7 violates Article 14. They submit that mandatory authentication has caused, and continues to cause, exclusion of the most marginalized sections of society. Proof of possession of an enrolment number or undergoing Aadhaar authentication is a mandatory pre-requisite for receiving subsidised food grain under the National Food Security Act. It creates “undue burden” on citizen which is unconstitutional. Successful monthly authentication is contingent on harmonious working of all attendant Aadhaar processes and technologies-i.e. correct Aadhaar-seeding, successful fingerprint recognition, mobile and wireless connectivity, electricity, functional POS machines and server capacity-each time. It is also dependant on age, disability (e.g.leprosy), class of work (e.g. manual labour), and the inherently probabilistic nature of biometric. Economic Survey of India 2016 reports that authentication failures have been as high as 49% in Jharkhand and 37% in Rajasthan, recognising that “failure to identify genuine beneficiaries results in exclusion error”.
244) The exclusion is not simply a question of poor implementation that can be administratively resolved, but stems from the very design of the Act, i.e. the use of biometric authentication as the primary method of identification. Determination of legal entitlements is contingent on a positive authentication response from the UIDAI. Biometric technology does not guarantee 100% accuracy and is fallible, with inevitable false positives and false negatives that are design flaws of such a probabilistic system, especially because biometrics also change over time.
245) Classification caused by the Act lacks rational nexus. The entitlement of an individual depends upon status, and not proof of identity. At the point of use, The Biometric Authentication divides residents into two classes: those who have and do not have Aadhaar; and those who authenticate successfully, and those who do not. Given that the probability of biometric mismatch is greatest for the aged, disabled, and individuals engaging in manual labour – amongst the most vulnerable sections of society-the decision to use periodic biometric authentications has a direct and disparate effect of violating fundamental rights of this class. This division bears no rational nexus with the question of status for receiving benefits. It leads to underinclusion, and is thus arbitrary, causing an Article 14 violation.
246) It is also argued that mandatory nature of Section 7 violates Article 21 as well. The Aadhaar Act alters the entire design & institutional structure through which residents were receiving entitlements. Mandatory imposition of Aadhaar violates their rights to choose how to identify themselves to the government in a reasonable and non-intrusive fashion. On making Aadhaar mandatory, instead of the citizen’s right to food and a correlative duty on the State to take action to ensure the proper fulfilment of such rights, the State is exercising its power to convert the constitutional rights of its citizens into liabilities.
247) As per the petitioners, having established the infringement of Article 21, the invasion is not justified under the principle of proportionality. The State’s primary justification of eliminating welfare leakages and ensuring “better targeting” does not stand up to judicial scrutiny. First, it has failed to discharge its burden of showing that the purported leakages were exclusively caused due to identity fraud, and that those leakages would not exist if Aadhaar is implemented. The state has not given any empirical data. Leakages exist due to eligibility frauds, quantity frauds and identity frauds. Studies filed in Petitioner’s affidavits show that eligibility and quantity frauds are the substantial cause for leakages. Assuming that the Aadhaar Act prevents leakages, the biometric identification system can, at best, only cure leakages related to identity fraud. The government’s claims of savings inter alia of Rs. 14,000 crores in the PDS system, due to the deletion of 2.33 crore ration cards is incorrect, inflated, and based on wrong assumptions for the following reasons: (a) it admittedly does not have estimates of leakages in PDS, nor has any study been done to see if POS machines are effective in removing PDS irregularities;
(b) it conflates issue of “bogus /ineligible ration cards” (eligibility fraud) with identity fraud;
(c) the figure of 2.33 crore includes West Bengal, where ration cards are issued to each person, as opposed to each household;
(d) a large number of these 2.33 crore cards were deleted even before Aadhaar-integration and seeding came into effect;
(e) the savings figure includes even those eligible beneficiaries who have been removed from the list due to failure to link Aadhaar properly; and
(f) it does not value the cost of loss of privacy. Most importantly, the basis for reaching such savings figure has not been disclosed. Similarly, incorrect averments have been made in the context of LPG savings, using Aadhaar-enabled Direct Benefit Transfer (‘DBT’) scheme known as PAHAL. Secondly, it has failed to show how the introduction of Aadhaar will stop the losses causes on any of the grounds above. Aadhaar is susceptible to its own unique forms of mischief by the vendor.
Thirdly, the State has failed to demonstrate that other, less invasive ways would be significantly worse at addressing the problem, especially given recent studies that found a significant reduction in PDS leakages, due to innovations devised to work within the PDS system; alternatives such as food coupons, digitisation of records, doorstep delivery, SMS alerts, social audits, and toll-free helplines have not been looked at.
Fourthly, the absence of proportionality is further established by the fact of systematic exclusion.
248) The respondents refuted, in strongest possible manner, all the aforesaid submissions in the following manner:
(i) No reasonable expectation of privacy
At the outset it was argued that Right to Privacy exists when there is a reasonable expectation of privacy. K.S. Puttaswamy judgment, US case law, UK case laws and the European cases on Article 8 of ECHR were referred to to determine the contours of reasonable expectation of privacy. Submission was that the Act operates in the public and relational sphere and not in the core, private or personal sphere of residents. It involves minimal identity information for effective authentication. The purpose is limited to authentication for identification. Section 29 of the Aadhaar Act, 2016 provides protection against disclosure of identity information without the prior consent of the ANH concerned. Sharing is intended only for authentication purposes. It was also submitted that there is no reasonable expectation of privacy with respect to identity information collected under the Aadhaar Act for the purposes of authentication and therefore Article 21 is not attracted.
249) The respondents point out that four types of information collected for providing Aadhaar
(i). Mandatory demographic information comprising name, date of birth, address and gender [Section 2(k) read with Regulation 4(1) of the Aadhaar (Enrolment and Update) Regulations, 2016];
(ii) Optional demographic information [Section 2(k) read with Regulation 4(2) of the Aadhaar (Enrolment and Update) Regulations, 2016].
(iii) Non-core biometric information comprising photograph.
(iv) Core biometric information comprising finger print and iris scan. 250) Demographic information, both mandatory and optional, and photographs does not raise a reasonable expectation of privacy under Article 21 unless under special circumstances such as juveniles in conflict of law or a rape victim’s identity.
Today, all global ID cards contain photographs for identification alongwith address, date of birth, gender etc. The demographic information is readily provided by individuals globally for disclosing identity while relating with others and while seeking benefits whether provided by government or by private entities, be it registration for citizenship, elections, passports, marriage or enrolment in educational institutions. Email ids and phone numbers are also available in public domain, For example in telephone directories. Aadhaar Act only uses demographic information which are not sensitive and where no reasonable expectation of privacy exists – name, date of birth, address, gender, mobile number and e mail address. Section 2(k) specifically provides that Regulations cannot include race, religion, caste, tribe, ethnicity, language, records of entitlement, income or medical history. Thus, sensitive information specifically stand excluded.
251) Face Photographs for the purpose of identification are not covered by a reasonable expectation of privacy. Barring unpublished intimate photographs and photographs pertaining to confidential situations there will be no zone of privacy with respect to normal facial photographs meant for identification. Face-photographs are given by people for driving license, passport, voter id, school admissions, examination admit cards, employment cards, enrolment in professions and even for entry in courts. In our daily lives we recognize each other by face which stands exposed to all, all the time. The face photograph by itself reveals no information.
252) There is no reasonable expectation of privacy with respect to fingerprint and iris scan as they are not dealing with the intimate or private sphere of the individual but are used solely for authentication. Iris scan is nothing but a photograph of the eye, taken in the same manner as a face photograph. Fingerprints and iris scans are not capable of revealing any personal information about the individual except for serving the purpose of identification.
Fingerprints are largely used in biometric attendance, laptops and mobiles. Even when a privacy right exists on a fingerprint, it will be weak. Finger print and iris scan have been considered to be the most accurate and non-invasive mode of identifying an individual. They are taken for passports, visa and registration by the State and also used in mobile phones, laptops, lockers etc for private use. Biometrics are being used for unique identification in e passports by 120 countries.
(ii) Least intrusive and strict scrutiny tests do not apply in the proportionality test. Learned Attorney General argued that the “least intrusive test” is not applicable while asserting the test of proportionality.
He relied on various U.S. Supreme Court judgments which explicitly rejected the test and the case of Modern Dental College & Research Centre which does not use the least intrusive measure test while undertaking the proportionality test. Mr.Dwivedi contends that the least intrusive means of achieving the state object, while carrying out the proportionality test, has been rejected by Indian courts in a catena of decisions as it involves a value judgment or second guessing of the Legislation. Such a test violates the separation of powers between the legislature and the judiciary.
Even assuming that the ‘least intrusive method’ test applies, the exercise of determining the least intrusive method of identification is a technical exercise and cannot be undertaken in the court of law. Moreover, the Petitioners, who have furnished smartcards as an alternative, have not established that smartcards are less intrusive than the Aadhaar card authentication process. The argument of applying the ‘Strict Scrutiny Test’ to test the Constitutionality of the Aadhaar Act by the Petitioners was flawed. Strict scrutiny test is a test conceptualised in the United States, only applied to ‘super suspect legislations’.
This compulsion arises because the scope of reasonable restrictions not having been specified specifically in the U.S. Constitution. That leaves the scrutiny of the Legislations by the courts based on the due process clause in the U.S. Constitution. Such a test does not have applicability in India. In Ashoka Kumar Thakur (2008) 6 SCC 1, the court referred to the test of strict scrutiny, narrow tailoring and compelling interest and observed that these principles cannot be applied directly to India as affirmative action is Constitutionally supported.
(iii) Act satisfies Proportionality Test Ld. Attorney General submitted that the legitimate state interest that the Aadhaar Act fulfils are prevention of leakages and dissipation of subsidies and social welfare benefits that are covered under Section 7 of the Aadhaar Act. He also submits that the larger public/state interest is to be decided by the State and cannot be second guessed by the Judiciary. The state had rejected the idea of ‘smart cards’ and other alternative models after due deliberations. The learned Attorney General cited various reports highlighting leakages, wastage, high costs and inefficiencies in the Public Distribution System, MGNREGA scheme and fuel subsidy.
He cited the Thirteenth Finance Commission Report 2010-2015 which stated that creation of a biometric-based unique identity for all residents in the country has potential to address need of the government to ensure that only eligible persons are provided subsidies and that all eligible persons are covered. He also cited the Economic Surveys of 2014-15 and 2015-16 both of which dilated upon the benefits of Aadhaar. The 2015-16 Survey says that the use of Aadhaar has significantly reduced leakages in LPG and MGNREGA with limited exclusion of the poor by linking households’ LPG customer numbers with Aadhaar numbers to eliminate ‘ghosts’ and duplicate households from beneficiary rolls.
The United Nations, in its report titled ‘Leaving No One Behind: the imperative of inclusive development’, praised India’s decision of launching Aadhaar as it will be a step forward in ensuring inclusion of all people especially the poorest and the most marginalized. This court in the case of PUCL v. Union of India85 has approved the recommendations of the High-powered committee headed by Justice D.P Wadhwa, which recommended linking of Aadhaar with PDS and encouraged State Governments to adopt the same. The court also lauded the efforts of State government for using biometric identification.
He also referred to the case of Binoy Viswam v. Union of India86 where the economic rationale for and benefits of Aadhaar was discussed and validated. Mr. Dwivedi has argued that 3% of GDP amounting to trillions of rupees is allocated by Governments towards subsidies, scholarships, pensions, education, food and other welfare programmes. But approximately half of if does not reach the intended beneficiaries. Aadhaar is necessary for fixing this problem as there is no other identification document which is widely and commonly possessed by the residents of the country and most of the identity documents do not enjoy the quality of portability. Moreover, Aadhaar lends assurance and accuracy on account of existence of fake, bogus and ghost cards, vide the process of de-duplication and authentication. De-duplication is ensured by the three sub systems are :-
(i) demographic deduplication
(ii) multi-ABIS multi-modal biometric de-duplication
(iii) manual adjudication. Biometric system provides high accuracy of over 99.86 %. The mixed biometric have been adopted only to enhance the accuracy and to reduce the errors which may arise on account of some residents either not having biometrics or not having some particular biometric.
(iv) Act empowers various facets of right to life under Article 21 The Ld. Attorney General submitted that Section 7 of the Act is traceable to Article 21 of the Constitution. Right to life is not a mere animal existence but the right to live with human dignity which includes the right to food, the right to shelter, right to employment, right to medical care, etc. Fulfilling these rights will justify the minimal invasion of the right to privacy of the citizens. The counsel for the respondent also referred to the case of G. Sundarrajan v. Union of India87 in which the petitioner therein challenged the violation of their Right to the Life due to the risk posed by the Kudanakulam Nuclear Plant. The court struck a balance between production of nuclear energy, which was of extreme importance for the economic growth, alleviation of poverty, generation of employment , and the violation of right to life and dignity under Article 21 posed by the threat of a nuclear disaster.
The court observed that adequate safety measure – both in design and operation – had been taken hence the violation of right to life was justified.
253) The argument of ‘illusory consent’ was refuted with the submission that Section 7 of the Act which mandatorily requires Aadhaar for receipt of benefit, service or subsidy linked to the Consolidated Fund of India, does not violate any Fundamental Rights. It involves a balancing of two Fundamental Rights: the Right to Privacy and the positive obligation of the State to ensure right to food, shelter and employment under Article 21 of the Constitution. Aadhaar enables furtherance of Article 21 by eliminating leakages and ensuring that no deserving individual is denied her/his entitlement.
The object of the Act i.e. the efficient, transparent and targeted delivery of subsidies, benefits and services to genuine beneficiaries is in, furtherance of various facets of Article 21 of the poor people of India and in furtherance of the Directive Principles of State Policy inter alia Articles 38,39, 41, 43, 47 and 48. 254) It was further argued that Section 7 is not a restriction at all and it does not require any surrender of Fundamental Rights. It is merely a regulatory procedure to receipt of subsidy, benefit or service. Section 7 purports to enliven the Fundamental Right under Article 21 , and Article 14. To achieve the goal of enlivening Fundamental Rights of the poor and the deprived and to prevent siphoning off the benefits, service or subsidy, it becomes necessary to require compliance with the condition of undergoing authentication.
255) Section 7 of the Aadhaar Act protects right to human dignity recognized by Article 21 of the Constitution. Aadhaar is used as means of authentication for availing services, benefits and subsidies. Welfare schemes funded from the consolidated fund of India such as PDS, scholarship, mid day meals, LPG subsidies, free education ensure that the Right to Life and Dignity of citizens are being enforced, which includes Justice (Social, Political and Economic). It also eliminates inequality with a view to ameliorate the poor, Dalits and other downtrodden classes and sections of the society.
256) In response to the argument that Fundamental Right to Privacy cannot be waived, the Mr.Dwivedi submits that Section 7 of the Aadhaar Act does not involve any issue of waiver. When an individual undergoes any authentication to establish his identity to receive benefits, services or subsidy, he does so to enliven his Fundamental Right to life and personal liberty under Article 21. When an individual makes a choice to enter into a relational sphere then his choice as to mode of identification would automatically get restricted on account of the autonomy of the individuals or institution with whom he wishes to relate. This is more so where the individual seeks employment, service , subsidy or benefits. Moreover, Aadhaar is of a Universal nature, unlike any other identification card which are not portable. They generally have a localized value and limited purpose.
257) In response to the arguments of the petitioners that Aadhaar reduces individuals to numbers, it was submitted that the Aadhaar number is absolutely necessary for authentication and it is solely used for that purpose. It was argued that the petitioner have conflated the concepts of identity and identification. Authentication is merely an identification process and does not alter the identity of an individual. Further Aadhaar number is a randomly generated number and bears no relation to the attributes of individuals. It is similar to an examiner allotting codes to examinees for administrative convenience.
258) It was also argued that the State has an obligation to enlivening right to food, right to shelter etc envisaged under Article 21 and for this purpose they may encroach upon the right of privacy of the beneficiaries. The state requires to strike a fair balance between the right of privacy and right to life of beneficiaries. An example furnished by the counsel for this is the Prohibition of Employment as Manual Scavengers and their Rehabilitation Act, 2013, which restricts a scavenger’s right to practice any profession, occupation, trade or business under Article 19(g) is order to enliven Article 21 and 17.
The counsel also gave the example of the practice of dwarftossing, which was banned in France. The law was challenged on ground that it interferes with the economic right of one practicing it. The challenge was negatived on the ground that permitting such a practice even though voluntary will be degrading of human dignity by Human Right Committee. Certain choices are restricted /prohibited by the Constitution itself (Articles 17,18, 23 and 24). Article 23 abolishes forced labour so it prohibits even those choosing to indulge in forced labour from doing so. The aforesaid actually result in enhancement of the Fundamental Right. The person is emancipated from a social condition which is below human dignity. Similarly Section 7 of the Act involves an identification for the purpose of enhancing human dignity.
259) In response to the argument of Aadhaar causing exclusion, the learned Attorney General responded by saying that if authentication fails, despite more than one attempt, then the possession of Aadhaar number can be proved otherwise i.e. by producing the Aadhaar card. And those who do not have Aadhaar number can make an application for enrolment and produce the enrolment id number).
260) Before we proceed to analyse the respective submissions, it has also to be kept in mind that all matters pertaining to an individual do not qualify as being an inherent part of right to privacy. Only those matters over which there would be a reasonable expectation of privacy are protected by Article 21. This can be discerned from the reading of Paras 297 to 307 of the judgment, relevant portions whereof have already been quoted above.
261) We may also clarify that the arguments of privacy are examined in the context of Sections 7 and 8 and the provisions related thereto under the Aadhaar Act. Validity of the other provisions of the Aadhaar Act, which is questioned in these proceedings, is dealt with separately. As per Section 7 of the Aadhaar Act in case an individual wants to avail any subsidy benefit or services, she is required to produce the Aadhaar number and, therefore, it virtually becomes compulsory for such a person. To that extent the petitioners may be right in submitting that even if enrolment in Aadhaar is voluntary, it assumes the character of compulsory enrolment for those who want to avail the benefits under Section
7. Likewise, authentication, as mentioned in Section 8, also becomes imperative. The relevant question, therefore, is as to whether invasion into this privacy meets the triple requirements or right to privacy.
(i) Requirement of law :
The Parliament has now passed Aadhaar Act, 2016. Therefore, law on the subject in the form of a statute very much governs the field and, thus, first requirement stands satisfied. We may point out at this stage that insofar as period from 2009 (when the Aadhaar scheme was launched with the creation of Authority vide notification No. A-43011/02/2009- Admin. I dated January 28, 2009 till the date Aadhaar Act came into force i.e. March 26, 2016, it is the argument of the petitioners that insofar as this period is concerned, it is not backed by any law and, therefore, notification dated January 28, 2009 should be struck down on this ground itself and all acts done including enrolment under the Aadhaar scheme from 2009 to 2016 should be invalidated. This aspect we propose to deal at a later stage. At this juncture, we are looking into the vires of Aadhaar Act.
In that context, the first requirement stands fulfilled.
(ii) Whether Aadhaar Act serves legitimate State aim?
‘Introduction’ to the said Act gives the reasons for passing that Act and the ‘Statement of Objects and Reasons’ mentions the objectives sought to be achieved with the enactment of the Aadhaar Act. ‘Introduction’ reads as under: “The Unique Identification Authority of India was established by a resolution of the Government of India in 2009. It was meant primarily to lay down policies and to implement the Unique Identification Scheme, by which residents of India were to be provided unique identity number. This number would serve as proof of identity and could be used for identification of beneficiaries for transfer of benefits, subsidies, services and other purposes.
Later on, it was felt that the process of enrolment, authentication, security, confidentiality and use of Aadhaar related information be made statutory so as to facilitate the use of Aadhaar number for delivery of various benefits, subsidies and services, the expenditures of which were incurred from or receipts therefrom formed part of the Consolidated Fund of India. The Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Bill, 2016 inter alia, provides for establishment of Unique Identification Authority of India, issuance of Aadhaar number to individuals, maintenance and updating of information in the Central Identities Data Repository, issues pertaining to security, privacy and confidentiality of information as well as offences and penalties for contravention of relevant statutory provisions.”
In the Statement of Objects and Reasons, it is inter alia mentioned that though number of social benefits schemes have been floated by the Government, the failure to establish identity of an individual has proved to be a major hindrance for successful implementation of those programmes as it was becoming difficult to ensure that subsidies, benefits and services reach the unintended beneficiaries in the absence of a credible system to authenticate identity of beneficiaries. The Statement of Objects and Reasons also discloses that over a period of time, the use of Aadhaar number has been increased manifold and, therefore, it is also necessary to take measures relating to ensuring security of the information provided by the individuals while enrolling for Aadhaar card. Having these parameters in mind, Para 5 of the Statement of Objects and Reasons enumerates the objectives which the Aadhaar Act seeks to achieve.
It reads as under:
“5. The Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Bill, 2016 inter alia, seeks to provide for-
(a) issue of Aadhaar numbers to individuals on providing his demographic and biometric information to the Unique Identification Authority of India;
(b) requiring Aadhaar numbers for identifying an individual for delivery of benefits, subsidies, and services the expenditure is incurred from or the receipt therefrom forms part of the Consolidated Fund of India;
(c) authentication of the Aadhaar number of an Aadhaar number holder in relation to his demographic and biometric information;
(d) establishment of the Unique Identification Authority of India consisting of a Chairperson, two Members and a Member-Secretary to perform functions in pursuance of the objectives above;
(e) maintenance and updating the information of individuals in the Central Identities Data Repository in such manner as may be specified by regulations;
(f) measures pertaining to security, privacy and confidentiality of information in possession or control of the Authority including information stored in the Central Identities Data Repository; and
(g) offences and penalties for contravention of relevant statutory provisions.”
262) After taking into consideration the Statement of Objects and Reasons, a two Judge Bench of this Court in Binoy Viswam v. Union of India & Ors.88, recapitulated the objectives of Aadhaar in the following manner:
“125. By making use of the technology, a method is sought to be devised, in the form of Aadhaar, whereby identity of a person is ascertained in a flawless manner without giving any leeway to any individual to resort to dubious practices of showing multiple identities or fictitious identities. That is why it is given the nomenclature “unique identity”. It is aimed at securing advantages on different levels some of which are described, in brief, below:
125.1. In the first instance, as a welfare and democratic State, it becomes the duty of any responsible Government to come out with welfare schemes for the upliftment of poverty-stricken and marginalised sections of the society. This is even the ethos of Indian Constitution which casts a duty on the State, in the form of “directive principles of State policy”, to take adequate and effective steps for betterment of such underprivileged classes. State is bound to take adequate measures to provide education, health care, employment and even cultural opportunities and social standing to these deprived and underprivileged classes. It is not that Government has not taken steps in this direction from time to time. At the same time, however, harsh reality is that benefits of these schemes have not reached those persons for whom that are actually meant.
125.1.1. India has achieved significant economic growth since Independence. In particular, rapid economic growth has been achieved in the last 25 years, after the country adopted the policy of liberalisation and entered the era of, what is known as, globalisation. Economic growth in the last decade has been phenomenal and for many years, the Indian economy grew at highest rate in the world. At the same time, it is also a fact that in spite of significant political and economic success which has proved to be sound and sustainable, the benefits thereof have not percolated down to the poor and the poorest. In fact, such benefits are reaped primarily by rich and upper middle classes, resulting into widening the gap between the rich and the poor.
125.1.2. Jean Dreze and Amartya Sen pithily narrate the position as under [An Uncertain Glory : India and its Contradictions] : “Since India’s recent record of fast economic growth is often celebrated, with good reason, it is extremely important to point to the fact that the societal reach of economic progress in India has been remarkably limited. It is not only that the income distribution has been getting more unequal in recent years (a characteristic that India shares with China), but also that the rapid rise in real wages in China from which the working classes have benefited greatly is not matched at all by India’s relatively stagnant real wages. No less importantly, the public revenue generated by rapid economic growth has not been used to expand the social and physical infrastructure in a determined and well-planned way (in this India is left far behind by China).
There is also a continued lack of essential social services (from schooling and health care to the provision of safe water and drainage) for a huge part of the population. As we will presently discuss, while India has been overtaking other countries in the progress of its real income, it has been overtaken in terms of social indicators by many of these countries, even within the region of South Asia itself (we go into this question more fully in Chapter 3, ‘India in Comparative Perspective’). To point to just one contrast, even though India has significantly caught up with China in terms of GDP growth, its progress has been very much slower than China’s in indicators such as longevity, literacy, child undernourishment and maternal mortality.
In South Asia itself, the much poorer economy of Bangladesh has caught up with and overtaken India in terms of many social indicators (including life expectancy, immunisation of children, infant mortality, child undernourishment and girls’ schooling). Even Nepal has been catching up, to the extent that it now has many social indicators similar to India’s, in spite of its per capita GDP being just about one third. Whereas twenty years ago India generally had the second best social indicators among the six South Asian countries (India, Pakistan, Bangladesh, Sri Lanka, Nepal and Bhutan), it now looks second worst (ahead only of problem-ridden Pakistan). India has been climbing up the ladder of per capita income while slipping down the slope of social indicators.”
125.1.3. It is in this context that not only sustainable development is needed which takes care of integrating growth and development, thereby ensuring that the benefit of economic growth is reaped by every citizen of this country, it also becomes the duty of the Government in a welfare State to come out with various welfare schemes which not only take care of immediate needs of the deprived class but also ensure that adequate opportunities are provided to such persons to enable them to make their lives better, economically as well as socially. As mentioned above, various welfare schemes are, in fact, devised and floated from time to time by the Government, keeping aside substantial amount of money earmarked for spending on socially and economically backward classes.
However, for various reasons including corruption, actual benefit does not reach those who are supposed to receive such benefits. One of the main reasons is failure to identify these persons for lack of means by which identity could be established of such genuine needy class. Resultantly, lots of ghosts and duplicate beneficiaries are able to take undue and impermissible benefits. A former Prime Minister of this country [ Late Shri Rajiv Gandhi] has gone on record to say that out of one rupee spent by the Government for welfare of the downtrodden, only 15 paisa thereof actually reaches those persons for whom it is meant. It cannot be doubted that with UID/Aadhaar much of the malaise in this field can be taken care of.
263) It may be highlighted at this stage that the petitioners are making their claim on the basis of dignity as a facet of right to privacy. On the other hand, Section 7 of the Aadhaar Act is aimed at offering subsidies, benefits or services to the marginalised section of the society for whom such welfare schemes have been formulated from time to time. That also becomes an aspect of social justice, which is the obligation of the State stipulated in Para IV of the Constitution. The rationale behind Section 7 lies in ensuring targeted delivery of services, benefits and subsidies which are funded from the Consolidated Fund of India. In discharge of its solemn Constitutional obligation to enliven the Fundamental Rights of life and personal liberty (Article 21) to ensure Justice, Social, Political and Economic and to eliminate inequality (Article 14) with a view to ameliorate the lot of the poor and the Dalits, the Central Government has launched several welfare schemes.
Some such schemes are PDS, scholarships, mid day meals, LPG subsidies, etc. These schemes involve 3% percentage of the GDP and involve a huge amount of public money. Right to receive these benefits, from the point of view of those who deserve the same, has now attained the status of fundamental right based on the same concept of human dignity, which the petitioners seek to bank upon. The Constitution does not exist for a few or minority of the people of India, but “We the people”. The goals set out in the Preamble of the Constitution do not contemplate statism and do not seek to preserve justice, liberty, equality an fraternity for those who have the means and opportunity to ensure the exercise of inalienable rights for themselves.
These goals are predominantly or at least equally geared to “secure to all its citizens”, especially, to the downtrodden, poor and exploited, justice, liberty, equality and “to promote” fraternity assuring dignity. Interestingly, the State has come forward in recognising the rights of deprived section of the society to receive such benefits on the premise that it is their fundamental right to claim such benefits. It is acknowledged by the respondents that there is a paradigm shift in addressing the problem of security and eradicating extreme poverty and hunger. The shift is from the welfare approach to a right based approach. As a consequence, right of everyone to adequate food no more remains based on Directive Principles of State Policy (Art 47), though the said principles remain a source of inspiration. This entitlement has turned into a Constitutional fundamental right. This Constitutional obligation is reinforced by obligations under International Convention.
The Universal Declaration of Human Rights (Preamble, Article 22 & 23) and International Covenant on Economic, Social and Cultural Rights to which India is a signatory, also casts responsibilities on all State parties to recognize the right of everyone to adequate food. Eradicating extreme poverty and hunger is one of the goals under the Millennium Development Goals of the United Nations. The Parliament enacted the National Security Food Act, 2013 to address the issue of food security at the household level. The scheme of the Act designs a targeted public distribution system for providing food grains to those below BPL. The object is to ensure to the people adequate food at affordable prices so that people may live a life with dignity.
The reforms contemplated under Section 12 of the Act include, application of information and communication technology tools with end to end computerization to ensure transparency and to prevent diversion, and leveraging Aadhaar for unique biometric identification of entitled beneficiaries. The Act imposes obligations on the Central Government, State Government and local authorities vide Chapter VIII, IX and X. Section 32 contemplates other welfare schemes. It provides for nutritional standards in Schedule II and the undertaking of further steps to progressively realize the objectives specified in Schedule III. 264) At this juncture, we would also like to mention that historic judgment of this Court in His Holiness Kesavananda Bharati Sripadagalvaru v. State of Kerala & Anr.89 emphasised on the attainment of socio-economic rights and its interplay with fundamental rights. Following passages from the opinion rendered by Khanna, J. need a specific mention:
“1477. I may also refer to another passage on p. 99 of Grammar of Politics by Harold Laski: “The state, therefore, which seeks to survive must continually transform itself to the demands of men who have an equal claim upon that common welfare which is its ideal purpose to promote. We are concerned here, not with the defence of anarchy, but with the conditions of its avoidance. Men must learn to subordinate their self-interest to the common welfare. The privileges of some must give way before the rights of all. Indeed, it may be urged that the interest of the few is in fact the attainment of those rights, since in no other environment is stability to be assured.”
1478. A modern State has to usher in and deal with large schemes having social and economic content. It has to undertake the challenging task of what has been called social engineering, the essential aim of which is the eradication of the poverty, uplift of the downtrodden, the raising of the standards of the vast mass of people and the narrowing of the gulf between the rich and the poor. As occasions arise quite often when the individual rights clash with the larger interests of the society, the State acquires the power to subordinate the individual rights to the larger interests of society as a step towards social justice.
As observed by Roscoe Pound on p. 434 of Volume I of Jurisprudence under the heading “Limitations on the Use of Property”: “Today the law is imposing social limitations – limitations regarded as involved in social life. It is endeavouring to delimit the individual interest better with respect to social interests and to confine the legal right or liberty or privilege to the bounds of the interest so delimited.” To quote the words of Friedmann in Legal Theory: “But modern democracy looks upon the right to property as one conditioned by social responsibility by the needs of society, by the ‘balancing of interests’ which looms so large in modern jurisprudence, and not as pre-ordained and untouchable private right.” (Fifth Edition, p. 406).”
265) It would also be worthwhile to mark, in continuity with the aforesaid thought, what Dwivedi, J. emphasised. “…The Nation stands to-day at the cross-roads of history and exchanging the time-honoured place of the phrase, may I say that the Directive Principles of State Policy should not be permitted to become “a mere rope of sand”. If the State fails to create conditions in which the fundamental freedoms could be enjoyed by all, the freedom of the few will be at the mercy of the many and then all freedoms will vanish. In order, therefore, to preserve their freedom, the privileged few must part with a portion of it.”
266) By no stretch of imagination, therefore, it can be said that there is no defined State aim in legislating Aadhaar Act. We may place on record that even the petitioners did not seriously question the purpose bona fides of the legislature in enacting this law. In a welfare State, where measures are taken to ameliorate the sufferings of the downtrodden, the aim of the Act is to ensure that these benefits actually reach the populace for whom they are meant. This is naturally a legitimate State aim.
(iii) Whether Aadhaar Act meets the test of proportionality?
267) The concept and contours of doctrine of proportionality have already been discussed in detail. We have also indicated the approach that we need to adopt while examining the issue of proportionality. This discussion bring out that following four subcomponents of proportionality need to be satisfied:
(a) A measure restricting a right must have a legitimate goal (legitimate goal stage).
(b) It must be a suitable means of furthering this goal (suitability or rationale connection stage).
(c) There must not be any less restrictive but equally effective alternative (necessity stage).
(d) The measure must not have a disproportionate impact on the right holder (balancing stage).
268) We now proceed to examine as to whether these components meet the required parameters in the instant case.
(a) Legitimate Goal Stage: At this stage, the exercise which needs to be undertaken is to see that the State has legitimate goal in restricting the right. It is also to be seen that such a goal is of sufficient importance justifying overriding a constitutional right of freedom. Further, it impairs freedom as little as possible.
269) In our preceding discussion, we have already pointed out above that Aadhaar Act serves the legitimate state aim. That, in fact, provides answer to this component as well. Some additions to the said discussion is as follows: It is a matter of common knowledge that various welfare schemes for marginalised section of the society have been floated by the successive governments from time to time in last few decades. These include giving ration at reasonable cost through ration shops (keeping in view Right to Food), according certain benefits to those who are below poverty line with the issuance of BPL Cards, LPG connections and LPG cylinders at minimal costs, old age and other kinds of pensions to deserving persons, scholarships, employment to unemployed under Mahatma Gandhi National Rural Employment Guarantee Act, 2005 (MGNREGA) Scheme.
There is an emergence of socioeconomic rights, not only in India but in many other countries world-wide. There is, thus, recognisation of civil and political rights on the one hand and emergence of socio-economic rights on the other hand. The boundaries between civil and political rights review as well as socio-economic rights review are rapidly crumbling. This rights jurisprudence created in India is a telling example.
270) This Court has developed a reputation as both a protector of Human Rights and an engine of economic and social reforms. In People’s Union for Civil Liberties (PUCL) v. Union of India90, the Court’s treatment of Right to Food as a fundamental right has been seen as victory for India’s impoverished population. The Court had passed orders enforcing the Government to take steps to ensure the effective implementation of the Food Distribution Schemes created by the Famine Code. Series of interim orders were passed aimed at bringing immediate relief to the drought affected individuals.
The benefits of the schemes were converted into legal entitlements by orders dated November 28, 2001 passed in the said case. Amongst other things, the Court ordered government to complete the identification of people who fell into the groups targeted for food distribution, issue cards to allow these people to collect the grain and distribute the grain to the relevant centres. The order also provided for governmental inspections to ensure fair quality grain. In this and subsequent orders, the court set the requirements on reporting, accountability, monitoring, transparency and dissemination of court orders aimed at ensuring that its orders are followed.
271) The purpose behind these orders was to ensure that the deserving beneficiaries of the scheme are correctly identified and are able to receive the benefits under the said scheme, which is their entitlement. The orders also aimed at ensuring ‘good governance’ by bringing accountability and transparency in the distribution system with the pious aim in mind, namely, benefits actually reached those who are rural, poor and starving.
272) Again, in People’s Union for Civil Liberties (PUCL) case, orders dated January 20, 2010 were passed by the Division Bench of this Court directing the Government of Delhi to respond to the extreme weather conditions ‘by setting up more shelters and protecting homeless people from the cold’. The assurance was extracted from the then Additional Solicitor General on behalf of the Government that affected people would be provided with shelter as a matter of priority and that arrangement should be made for this within a day.
273) In the context of Right to Education, this Court in State of Bihar & Ors. v. Project Uchcha Vidya, Sikshak Sangh & Ors.91 passed orders on January 3, 2006 thereby directing that a committee be appointed to investigate departures from the State of Bihar’s policy concerning the establishment of ‘Project Schools’ aimed at improving its poor education record. The Court appointed a committee to investigate the matter. The Court’s order included details as to the composition and functions of the committee, guidelines as to what would constitute irregularities in the implementation of the policy and an expectation that the State of Bihar would take remedial action if the committee found any irregularities. The Court’s approach to affirmative action in education is also instructive.
274) In Ashoka Thakur v. Union of India92, the Court upheld the Ninety- Third Amendment to the Constitution, which allows for certain educational institutions to put in place special admissions rules in order to advance India’s ‘socially or educationally backward classes of citizens or for the Scheduled Castes or the Scheduled Tribes’.93 The Court held that people who are wealthier and better educated (the ‘creamy layer’) should be excluded from the 27 per cent quota for ‘Other Backward Classes’ (OBC). This step was needed to ensure that benefits reached those people living in desperate poverty. In addition, the inclusion of particular groups in the OBC category had to be reviewed every five years.
275) In Paschim Banga Ket Mazdoor Samity v. State of West Bengal94, the Court found that Article 21 encompasses a right to adequate medical facilities or health care. It also interpreted other fundamental rights in light of directive principles.
Likewise, in Mohini Jain v. State of Kerala & Ors.95, the Court held that the right to equality before the law in Article 14 includes a right to education. In the subsequent case, Unnikrishnan v. State of Andhra Pradesh96, the Court clarified its findings in Mohini Jain, stating that Article 14 gave rise to a right to primary education. Following the cases on education, in 1997 the Indian government proposed a constitutional Amendment recognising education for children under 14 as a fundamental right. This Amendment was passed in 2002 as Article 21A. One of the Court’s earliest cases dealing with the role of the directive principles in constitutional interpretation is arguably also its most celebrated judgment. Some commentators see the decision in Olga Tellis & Ors. v. Bombay Municipal Corporation & Ors.97 as a recognition of enforceable right to shelter.
276) The purpose of citing aforesaid judgments is to highlight that this Court expanded the scope of Articles 14 and 21 of the Constitution by recognising various socio-economic rights of the poor and marginalised section of the society and, in the process, transforming the constitutional jurisprudence by putting a positive obligation on the State to fulfill its duty as per the Charter of Directive Principles of the State Policy, contained in Part IV of the Constitution.
It is to be kept in mind that while acknowledging that economic considerations would play a role in determining the full content of the right to life, the Court also held that right included the protection of human dignity and all that is attached to it, ‘namely, the bare necessities of life such as adequate nutrition, clothing and shelter and facilities for reading, writing and expressing oneself in diverse forms’ (See Francis Coralie Mullin v. The Administrator, Union Territory of Delhi & Ors.98). It is, thus, of some significance to remark that it is this Court which has been repeatedly insisting that benefits to reach the most deserving and should not get frittered mid-way. We are of the opinion that purpose of Aadhaar Act, as captured in the Statement of Objects and Reasons and sought to be implemented by Section 7 of the Aadhaar Act, is to achieve the stated objectives. This Court is convinced by its conscience that the Act is aimed at a proper purpose, which is of sufficient importance.
(b) Suitability or rationale connection stage:
277) We are also of the opinion that the measures which are enumerated and been taken as per the provisions of Section 7 read with Section 5 of the Aadhaar Act are rationally connected with the fulfillment of the objectives contained in the Aadhaar Act. It may be mentioned that the scheme for enrolling under the Aadhaar Act and obtaining the Aadhaar number is optional and voluntary. It is given the nomenclature of unique identity. A person with Aadhaar number gets an identity. No doubt, there are many other modes by which a person can be identified. However, certain categories of persons, particularly those living in abject poverty and those who are illiterate will not be in a position to get other modes of identity like Pan Card, Passport etc. That apart giving unique identity of each resident of the country is a special feature of this scheme, more so, when it comes with the feature stated above, namely, no person can have more than one Aadhaar number; Aadhaar number given to a particular person cannot be reassigned again to any individual even if that is cancelled and there is hardly any possibility to have fake identity.
278) As pointed out above, enrolling for Aadhaar is not the serious concern of the petitioners. It is only the process of authentication and other related issues which bothers the petitioners which shall be considered at the appropriate stage. At this point of time, we are discussing the issue as to whether the limitation on the rights of the individuals is rationally connected to the fulfillment of the purpose contained in the Aadhaar Act. Here, Section 5 talks of special measures for issuance of Aadhaar number to certain categories of persons. It gives identity to those persons who otherwise may not have any such identity. In that manner, it recognises them as residents of this nation and in that form gives them their ‘dignity’.
279) Section 7, which provides for necessity of authentication for receipt of certain subsidies, benefits and services has a definite purpose and this authentication is to achieve the objectives for which Aadhaar Act is enacted, namely, to ensure that such subsidies, benefits and services reach only the intended beneficiaries. We have seen rampant corruption at various levels in implementation of benevolent and welfare schemes meant for different classes of persons. It has resulted in depriving the actual beneficiaries to receive those subsidies, benefits and services which get frittered away though on papers, it is shown that they are received by the persons for whom they are meant.
There have been cases of duplicate and bogus ration cards, BPL cards, LPG connections etc. Some persons with multiple identities getting those benefits manifold. Aadhaar scheme has been successful, to a great extent, in curbing the aforesaid malpractices. By providing that the benefits for various welfare schemes shall be given to those who possess Aadhaar number and after undergoing the authentication as provided in Section 8 of the Aadhaar Act, the purpose is to ensure that only rightful persons receive these benefits. Non-action is not costly. It’s the affirmative action which costs the Government. And that money comes from exchequer. So, it becomes the duty of the Government to ensure that it goes to deserving persons. Therefore, second component also stands fulfilled.
(c) Necessity Stage:
280) Insofar as third component is concerned, most of it stands answered while in the discussion that has ensued in respect of component No. 1 and 2. The manner in which malpractices have been committed in the past leaves us to hold that apart from the system of unique identity in Aadhaar and authentication of the real beneficiaries, there is no alternative measure with lesser degree of limitation which can achieve the same purpose. In fact, on repeated query by this Court, even the petitioners could not suggest any such method.
(d) Balancing Stage:
281) With this, we now advert to the most important component of proportionality i.e. balancing between importance of achieving the proper purpose and the social importance of preventing the limitation on the constitutional right.
282) Argument of the petitioners is that Aadhaar project creates the architect of surveillance state and society, which is antithetical to the principles of democracy. It is premised on the basis that the Aadhaar project enables the State to profile citizens, track their movements, assess their habits and silently influence their behaviour throughout their lives. It may stifle dissent and influence political decision making. It is also argued that aggregation, storage and use of such stored information is violative of fundamental right to privacy, dignity and individual autonomy. Informational privacy is expected as part of right to privacy.
The Act allows data aggregation as well. Such an Act is unconstitutional as there is violation of a fundamental rights but there is absence of procedural safeguards to protect data in the Act. It is also argued that extent of information collected with the use of Aadhaar, specially by the methodology of authentication, is not proportionate to the ‘compelling interest of the State’ and there are various other methods available for identification. It is, thus, disproportionate and unreasonable state compulsion.
283) The respondents, on the other hand, have argued that there cannot be any reasonable expectation of privacy inasmuch as the Aadhaar Act operates in the public and relationally sphere and not in the core, private or personal sphere of the residents. Moreover, it involves minimal identity information for effective authentication which stands the test of reasonableness. The Act is, thus, least intrusive and strict scrutiny test does not apply in the proportionality test. It is also the case of the respondents that the Aadhaar Act does not allow aggregation at all and, therefore, all the apprehension are ill-founded and have no basis. It is also submitted that the Aadhaar Act is, in fact, the facilitator in empowering various facets of right to life under Article 21 and thereby ensures that unprivileged class is also able to live with human dignity.
284) Before undertaking this exercise of balancing, we would like to point out that we are not convinced with the argument of the respondents that there cannot be any reasonable expectation of privacy. No doubt, the information which is gathered by the UIDAI (whether biometric or demographic) is parted with by the individuals to other agencies/body corporates etc. in many other kinds of transactions as well, as pointed out by the respondents. However, the matter is to be looked into from the angle that this information is collected and stored by the State or instrumentality of the State. Therefore, it becomes important to find out as to whether it meets the test of proportionality, and satisfies the condition that the measure must not have disproportionate impact on the right-holder (balancing stage). However, at the same time, the fact that such information about individuals is in public domain may become a relevant factor in undertaking the exercise of balancing.
285) We have already traced the objectives with which the Aadhaar Act has been enacted. No doubt, there is a right to privacy, which is now entrenched in fundamental rights. On the other hand, we are also concerned with the rights of those persons whose dignity is sought to be ensured by giving them the facilities which are necessary to live as dignified life.
Therefore, balancing has to be done at two levels:
(i) Whether, ‘legitimate state interest’ ensures ‘reasonable tailoring’? There is a minimal intrusion into the privacy and the law is narrowly framed to achieve the objective. Here the Act is to be tested on the ground that whether it is found on a balancing test that the social or public interest and the reasonableness of the restrictions outweigh the particular aspect of privacy, as claimed by the petitioners. This is the test we have applied in the instant case.
(ii) There needs to be balancing of two competing fundamental rights, right to privacy on the one hand and right to food, shelter and employment on the other hand. Axiomatically both the rights are founded on human dignity. At the same time, in the given context, two facets are in conflict with each other. The question here would be, when a person seeks to get the benefits of welfare schemes to which she is entitled to as a part of right to live life with dignity, whether her sacrifice to the right to privacy, is so invasive that it creates imbalance?
286) In a way, both the aforesaid questions have some overlapping inasmuch as even while finding answer to the second question, it will have to be determined as to whether there is a least intrusion into the privacy of a person while ensuring that the individual gets the benefits under the welfare schemes.
287) The respondents seemed to be right when they argue that all matters pertaining to an individual do not qualify as being an inherent part of right to privacy. Only those which concern matters over which there can be a reasonable expectation of privacy would be protected by Article 21. In this behalf, we may recapitulate the discussion on some significant aspects in Puttaswamy: Privacy postulates the reservation of a private space, described as the right to be let alone.
The integrity of the body and the sanctity of the mind can exist on the foundation of the individual’s ‘right to preserve a private space in which the human personality can develop’ and this involves the ability to make choices. In this sense privacy is a postulate of human dignity itself. The inviolable nature of the human personality is manifested in the ability to make decisions on matters intimate to human life. The autonomy of the individual is associated ‘over matters which can be kept private. These are concerns over which there is a legitimate expectation of privacy’. Thoughts and behavioral patterns which are intimate to an individual are entitled to a zone of privacy where one is free of social expectations. In that zone of privacy an individual is not judged by others.
The judgment refers to the expert group report and identifies nine privacy principles pertaining to notice, choice and consent, collection limitation, purpose limitation, access and correction, non disclosure of information, security of data, openness or proportionality as to the scale, scope and sensitivity to the data collected, and accountability. At the same time, privacy is a subset of liberty. All liberties may not be exercised in privacy. It lies across the spectrum of protected freedoms. Further, the notion of reasonable expectation of privacy has both subjective and objective elements. At a subjective level it means ‘an individual desires to be left alone’. On an objective plain privacy is defined by those Constitutional values which shape the content of the protected zone where the individual ‘ought to be left alone’.
Further, the notion of reasonable expectation of privacy ensures that while on the one hand, the individual has a protected zone of privacy, yet on the other ‘the exercise of individual choices is subject the right of others to lead orderly lives’. The extent of the zone of privacy would, therefore, depend upon both the subjective expectation and the objective principle which defines a reasonable expectation. It is pertinent to point out that while dealing with informational privacy, the judgment notes that privacy concerns are seriously an issue in the age of information. It also notes the data mining processes together with knowledge discovery, and the age of big data.
The court finds that data regulation and individual privacy raises complex issues requiring delicate balances to be drawn between the legitimate concerns of the State and individual interest in the protection of privacy, and in this sphere, data protection assumes significance. Data such as medical information would be a category to which a reasonable expectation of privacy attaches. There may be other data which falls outside the reasonable expectation paradigm. Data protection regimes seek to protect the autonomy of the individual. This is a complex exercise involving careful balancing. In this balancing process, following parameters are to be kept in mind:
(i) The judgment also holds that the legitimate expectation of privacy may vary from the intimate zone to the private zone and from the private to the public arenas. However, ‘the privacy is not lost or surrendered merely because the individual is in a public space’.
(ii) One of the chief concerns is that ‘while the web is a source of lawful activity – both personal and commercial, concerns of National security intervene since the seamless structure of the web can be exploited by terrorist to wreak havoc and destruction on civilized societies.’ Noting an article of Richard A. Posner, which says ‘privacy is the terrorist’s best friend..’ It is observed that this formulation indicates that State has legitimate interest when it monitors the web to secure the Nation.
(iii) Apart from National security, State may have justifiable reasons for the collection and storage of data as where it embarks upon programs to provide benefits to impoverished and marginalized sections of society and for ensuring that scarce public resources are not dissipated and diverted to non-eligible recipients. Digital platforms are a vital tool of ensuring good governance in a social welfare State and technology is a powerful enabler.
288) In the first instance, therefore, it is to be seen as to whether the petitioners claim on the information supplied while authentication to be protected is based on reasonable expectation.
289) ‘Reasonable Expectation’ involves two aspects. First, the individual or individuals claiming a right to privacy must establish that their claim involves a concern about some harm likely to be inflicted upon them on account of the alleged act. This concern ‘should be real and not imaginary or speculative’. Secondly, ‘the concern should not be flimsy or trivial’. It should be a reasonable concern. It has to be borne in mind that the concept of ‘reasonable expectation’ has its genesis in the US case laws. UK judgments adopted the test of reasonable expectation from the US jurisprudence. The ECHR and ECJ judgments reveal a little divergence with regard to right of privacy. The ECHR in general adopts the approach that ‘a person’s reasonable expectation as to privacy may be significant, although, not necessarily conclusive factor’. This perhaps explains the apparent conflict as regards finger prints.
290) In the leading case Katz v. US99 Reasonable Expectation was stated to embrace two distinct questions. The first was whether the individual, by his conduct has exhibited an actual (subjective expectation of privacy), and the second, whether the subjective expectation is one that the society is prepared to recognize as reasonable. This was also followed in Smith v. Marlyand100.
291) In the judgment of Court of Appeal in R. Wood v. Commissioner101, the appellant complained against taking and retention of his photograph in Central London in the context of a meeting by the police force to enable identification at a later time in the event of eruption of disorder and commission of offence. The concept of reasonable expectation was examined after surveying a series of judgments which sought to consider violation of Article 8 of the ECHR. The following pertinent aspects emerge:
(i) Whether information related to private or public matter?
(ii) Whether the material obtained was envisaged for a limited use or was likely to be made available to general public?
(iii) Private life was a broad term covering physical and psychological integrity of a person.
(iv) Storing of data relating to private life of an individual interferes with Article 8. However, in determining whether information retained involves any private life aspect would have to be determined with due regard to the specific context.
(v) Article 8, however protean, should not be so construed widely that its claims become unreal and unreasonable. Firstly, the threat to individuals personal autonomy must attain a certain level of seriousness. Secondly, the claimant must enjoy on the facts a reasonable expectation of privacy. Thirdly, the breadth of Article 8(1) may in many instances be greatly curtailed by scope of justifications available to the State.
(vi) Reasonable expectation of privacy is a broad concept which takes into account all the circumstances of the case. They include attributes of the claimants, the nature of the activity in which the claimant was engaged, the place at which it was happening, the nature and purpose of the intrusion, the absence (or presence) of consent, the effect on the claimant and the purpose for which information is taken.
292) Therefore, when a claim of privacy seeks inclusion in Article 21 of the Constitution of India, the Court needs to apply the reasonable expectation of privacy test.
It should, inter alia, see:
(i) What is the context in which a privacy claim is set up?
(ii) Does the claim relate to private or family life, or a confidential relationship?
(iii) Is the claim a serious one or is it trivial?
(iv) Is the disclosure likely to result in any serious or significant injury and the nature and extent of disclosure?
(v) Is disclosure relates to personal and sensitive information of an identified person?
(vi) Does disclosure relate to information already disclosed publicly?
If so, its implication?
293) Under the Aadhaar Act Architecture, four types of information is to be given at the time of enrolment:
(i) Mandatory demographic information comprising name, date of birth, address and gender (Section 2(k) read with Regulation 4(1) of the Aadhaar (Enrolment and Update) Regulations, 2016).
(ii) Optional demographic information (Section 2(k) read with Regulation 4(2) of the Aadhaar (Enrolment and Update) Regulations, 2016).
(iii) Non core biometric information comprising photograph.
(iv) Core biometric information comprising finger print and iris scan.
294) Insofar as demographic information is concerned, it is required by the provisions of many other enactments as well like Companies Act, Special Marriage Act, Central Motor Vehicle Rules, Registration of Electoral Rules, The Citizenship Rules, The Passport Act and even Supreme Court Rules.
295) As regards core biometric information which comprises finger prints, iris scan, for the purpose of enrolling in Aadhaar scheme, we have already held earlier that it is minimal information required for enrolment. This information becomes essential for authentication use in a public sphere and in relational context.
296) It may also be mentioned that with the advent of science and technology, finger print and iris scan have been considered to be the most accurate and non invasive mode of identifying an individual. It is for this reason that these are taken also for driving licenses, passports, visa as well as at the time of registration of documents by the State. These are also used in mobile phones, laptops, lockers etc. for private use. International Civil Aviation Organisation (ICAO) has recommended use of biometric passports.
Many civilized countries with robust democratic regime have also introduced biometric based identity cards. Therefore, collection of information in the four different categories mentioned above may not be unreasonable. However, as stated earlier as well, the issue is not of taking the aforesaid information for the purpose of enrolling in Aadhaar and for authentication. It is the storage and retention of this data, whenever authentication takes place, about which the concerns are raised by the petitioners. The fears expressed by the petitioners are that with the storage and retention of such data, profile of the persons can be created which is susceptible to misuse.
297) This aspect has already been dealt with earlier and apprehension of the petitioners are taken care of. To recapitulate, at the time of enrolment, the data collected is minimal and there is no data collection in respect of religion, caste, tribe, language of records of entitlement income or medical history of the applicant at the time of Aadhaar enrolment. Full care is taken that even the minimal data collected at the time of enrolment does not remain with the enrolment agency and immediately gets transmitted to CIDR. Even at the time of authentication, the only exercise which is undertaken by the Authority is to see that the finger prints and/or iris scan of the concerned person sent for authentication match with the one which is in the system of Authority.
298) Let us advert to the second facet of balancing, namely, balancing of two fundamental rights. As already pointed out above, the Aadhaar Act truly seeks to secure to the poor and deprived persons an opportunity to live their life and exercise their liberty. By ensuring targeted delivery through digital identification, it not only provides them a nationally recognized identity but also attempts to ensure the delivery of benefits, service and subsidies with the aid of public exchequer/Consolidated Fund of India. National Security Food Act, 2013 passed by the Parliament seeks to address the issue of food, security at the household level. The scheme of that Act is aimed at providing food grains to those belonging to BPL categories. Like the MGNREGA Act, 2005 takes care of employment.
The MGNREGA Act has been enacted for the enhancement, livelihood, security of the households in rural areas of the country. It guarantees at least 100 days of wage employment in every financial year to at least one able member of every household in the rural area on assets creating public work programme. Sections 3 and 4 of the MGNREGA Act contain this guarantee. The minimum facilities to be provided are set out by Section 5 read with Schedule II. Section 22 provides for funding pattern and Section 23 provides for transparency and accountability. This Act is another instance of a rights based approach and it enlivens the Fundamental Right to life and personal liberty of Below Poverty Line people in rural areas.
299) We may mention here that Mr. Dwivedi had pointed out not only India but several other countries including western nations which have read socio-economic rights into human dignity and right to life. Hungary and South Africa have gone to the extent of making express provisions in their Constitutions. The Federal Constitution Court of Germany in a decision dated February 09, 2010 while deciding the question whether the amount of standard benefit aid is compatible with the Basic Law held that:
“The Fundamental Right to the guarantee of a subsistence minimum is in line with human dignity emerges from Article 1.1 of the Basic Law in conjunction with Article 20.1 of the Basic Law… Article 1.1 of the Basic Law established this claim. The principle of the social welfare State contained in Article 20.1 of the Basic Law, in turn grants to the Legislature the mandate to ensure a subsistence minimum for all that is in line with human dignity”.
It is further held that:
“if a person does not have the material means to guarantee an existence that is in line with human dignity because he or she is unable to obtain it either out of his or her gainful employment, or from own property or by benefits from third parties, the State is obliged within its mandate to protect human dignity and to ensure, in the implementation of its social welfare state mandate, that the material prerequisites for this are at the disposal of the person in need of assistance.”
Similarly, in a latter judgment dated July 18, 2012 while deciding whether the amount of the cash benefit provided for in the Asylum Seekers Benefits Act was constitutional it reiterated that: “the direct constitutional benefit claim to the guarantee of a dignified minimum existence does only cover those means that are absolutely necessary to maintain a dignified life. It guarantees the entire minimum existence as a comprehensive fundamental rights guarantee, that encompasses both humans’ physical existence, that is food, clothing, household items, housing, heating, hygiene, and health, and guarantees the possibility maintain interpersonal relationships and a minimal degree of participation in social, cultural and political life, since a human as a person necessarily exists in a social context..”
300) The Constitutional Court of South Africa in Government of the Republic of South Africa & Ors. v. Grootboom102 held that: “…these rights need to be considered in the context of the socio-economic rights enshrined in the Constitution. They entrench the right to access to land, to adequate housing and to health care, food, water and social security..”
301) In 1995, Hungary’s Constitutional Court ruled that the right to social security as contained in Article 70/E of the Constitution obligated the State to secure a minimum livelihood through all of the welfare benefits necessary for the realization of the right to human dignity.
302) Even in Italy, the Courts have emphasized on the right to social security.
303) In Budina v. Russia103, the European Court of Human Rights has recognized, in principle, that inadequate benefits could fall under Article 3 of the European Convention on Human Rights (ECHR) on the right to be free from inhuman and degrading treatment.
304) In 1996, the Swiss Federal Court ruled that three Czechs illegally residing in Switzerland are entitled to social benefit in order to have a minimal level of subsistence for a life in dignity to prevent a situation where people “are reduced to beggars, a condition unworthy of being called human. It held: “…The federal constitution does not (though the 1995 draft new constitution is now different) explicitly provide for a fundamental right to a subsistence guarantee. One can however also derive unwritten constitutional right from it.
A guarantee of freedoms not mentioned in the constitution by unwritten constitutional law was assumed by the exercise of other freedoms (mentioned in the constitution), or otherwise evidently indispensable components of the democratic constitutional order of the Federation…” “…The guaranteeing of elementary human needs like food, clothing and shelter is the condition for human existence and development as such. It is at the same time an indispensable component of a constitutional, democratic polity.”
305) Nelson Mandela in his speech at Trafalgar Square in London in 2005 said: “…Massive poverty and obscene inequality are such terrible scourges of our times – times in which the world boasts breathtaking advances in science, technology, industry and wealth accumulation – that they have to rank alongside slavery and apartheid as social evils…And overcoming poverty is not a gesture of charity. It is an act of justice. It is the protection of a fundamental human right, the right to dignity and a decent life. While poverty persists, there is no true freedom.”
306) Following passages by James Griffin in his book on “Human Rights” are worth noting :
“10.1 THE HISTORICAL GROWTH of RIGHTS:
Contrary to widespread belief, welfare rights are not a twentieth-century innovation, but are among the first human rights ever to be claimed. When in the twelfth and thirteenth centuries our modern conception of a right first appeared, one of the earliest examples offered was the right of those in dire need to receive aid from those in surplus. This right was used to articulate the attractive view of property prevalent in the medieval Church. God has given all things to us in common, but as goods will not be cared for and usefully developed unless assigned to particular individuals, we creatures have instituted systems of property. In these systems, however, an owner is no more than a custodian.
We all thus have a right, if we should fall into great need, to receive necessary goods or, failing that, to take them from those in surplus. One finds, every occasionally, what seem to be human rights to welfare asserted in the Enlightenment, for example, by John Locke, Tom Paine, and William Cobbett. Following the Enlightenment, right to welfare have often appeared in national constitutions; for example, the French constitutions of the 1790s, the Prussian Civil Code (1794), the Constitutions of Sweden (1809), Norway (1814), The Netherlands (1814), Denmark (1849), and, skipping to the twentieth century, the Soviet Union (1936)-though it is not always clear that the drafters of these various documents thought of these fundamental civil rights as also human rights.
By the end of the nineteenth century, political theorists were beginning to make a case that welfare rights are basic in much the sense that Civil and political rights are. But it was Franklin Roosevelt who did most to bring welfare rights into public life. The Atlantic Charter (1941), signed by Roosevelt and Churchill but in this respect primarily Roosevelt’s initiative, declared that in addition to the classical civil and political freedoms here were also freedoms from want and fear. In his State of the Union message of 1944, Roosevelt averred :
We have come to a clear realization of the fact that true individual freedom cannot exist without economic security and independence. ‘Necessitous men are not free men’… In our day these economic truths have become accepted as self evident. We have accepted, so to speak, a second Bill of Rights… Among these are : The right to a useful and remunerative job…. The right to earn enough to provide adequate food and clothing and recreation… The United Nations committee charged with drafting the Universal Declaration of Human Rights (1948), chaired by Eleanor Roosevelt, included most of the now standard welfare rights; rights to social security, to work, to rest and leisure, to medical care, to education, and ‘to enjoy the arts and to share in scientific advancements and its benefits’.
The Universal Declaration is a good example of how extensive-some would say lavish-proposed welfare rights have become. …If human rights are protections of a form of life that is autonomous and free, they should protect life as well as that form of it. But if they protect life, must they not also ensure the wherewithal to keep body and soul together that is, some minimum material provision? And as mere subsistence-that is, keeping body and soul together-is too meager to ensure normative agency, must not human rights guarantee also whatever leisure and education and access to the thought of others that are also necessary to being a normative agent?
That is the heart of the case. It appeals to our picture of human agency and argues that both life and certain supporting goods are integral to it. Life and certain supporting goods are necessary conditions of being autonomous and free. Many philosophers employ this necessary – condition argument to establish a human right to welfare-or, at least, to establish the right’s being as basic as any other rights. I too want to invoke the necessary-conditions arguments; I should only want to strengthen it. It is now common to say that liberty rights and welfare rights are ‘indivisible’. But that, also, is too weak.
It asserts that one cannot enjoy the benefits of liberty rights without enjoying the benefits of welfare rights, and vice versa. But something stronger still may be said. There are forms of welfare that are empirically necessary conditions of a person’s being autonomous and free, but there are also forms that are logically necessary-part of what we mean in saying that a person has these rights. The value in which human rights are grounded is the value attaching to normative agency. The norm arising from this value, of course, prohibits persons from attacking another’s autonomy and liberty. But it prohibits more. The value concerned is being a normative agent, a self-creator, made in god’s image…. The value resides not simply in one’s having the undeveloped, unused capacities for autonomy and liberty but also in exercising them-not just in being able to be autonomous but also in actually being so.
The norm associated with this more complex value would address other ways of failing to be an agent. It would require protecting another person from losing agency, at least if one can do this without great cost to oneself; it would require helping to restore another’s agency if it has already been lost, say through giving mobility to the crippled or guidance to the blind, again with the same proviso. All of this is involved simply in having a right to autonomy or to liberty. Welfare claims are already part of the content of these rights. What, then, should we think of the common division of basic rights into ‘classical’ liberty rights and welfare rights? Into which of these two classes does the right to autonomy or to liberty go? Into which of the two classes do the difficult, apparently borderline cases go, such as rights to life, to property, to the pursuit of happiness, to security of person, and to privacy? The sensible response would be to drop the distinction. What is more, a right to welfare is a human right.
36. Amartya Sen in his book “Development as Freedom” says: Development requires the removal of major sources of unfreedom: poverty as well as tyranny, poor economic opportunities as well as systematic social deprivation, neglect of public facilities as well as intolerance or overactivity of repressive states. Despite unprecedented increases in overall opulence, the contemporary world denies elementary freedoms to vast numbers-perhaps even the majority-of people.
Sometimes the lack of substantive freedoms relates directly to economic poverty, which robs people of the freedom to satisfy hunger, or to achieve sufficient nutrition, or to obtain remedies for treatable illnesses, or the opportunity to be adequately clothed or sheltered, or to enjoy clean water or sanitary facilities. In other cases, the unfreedom links closely to the lack of public facilities and social care, such as the absence of epidemiological programs, or of organized arrangements for health care or educational facilities, or of effective institutions for the maintenance of local peace and order. In still other cases, the violation of freedom results directly from a denial of political and civil liberties by authoritarian regimes and from imposed restrictions on the freedom to participate in the social, political and economic life of the community.”
307) In the aforesaid backdrop, this Court is called upon to find out whether Aadhaar Act strikes a fair balance between the two rights. In this context, we have to examine the importance of achieving the proper purpose and the social importance of preventing the limitation on the constitutional rights. Insofar as importance of achieving the proper purpose is concerned, that has already been highlighted above. To reiterate some of the important features, it is to be borne in mind that the State is using Aadhaar as an enabler for providing deserving section of the society their right to food, right to livelihood, right to receive pension and other social assistance benefits like scholarships etc. thereby bringing their right to life to fruition. This necessity of Aadhaar has arisen in order to ensure that such benefits are given to only genuine beneficiaries.
The Act aims at efficient, transparent and targeted delivery of subsidies, benefits and services. In the process, it wants to achieve the objective of checking the corrupt practices at various levels of distribution system which deprive genuine persons from receiving these benefits. There have been reports relating to leakages in PDS as well as in fuel subsidies and also in working of MGNREGA scheme. Mr. Venugopal, learned Attorney General has given the following details about these reports:
(I) Reports relating to leakages in PDS
Several studies initiated by the Government as well as the World Bank and Planning Commission revealed that food grains did not reach the intended beneficiaries and that there was large scale leakages due to the failure to establish identity:
(a) The Comptroller and Auditor General of India in its Audit Report No. 3 of 2000 in its overview for the Audit Report observed that the Public Distribution Scheme suffered from serious targeting problems. 1.93 Crore bogus ration cards were found to be in circulation in 13 States and a significant portion of the subsidized foodgrains and other essential commodities did not reach the beneficiaries due to their diversion in the open market.
(b) A Report titled “Budget Briefs: Targeted Public Distribution System (TPDS), GOI 2011-2012” prepared by Avani Kapur and Anirvan Chowdhury and published by the Accountability Initiative observed that there were large number of fake ration cards which were causing inefficiencies in targeting. Between July 2006 and July 2010, in Bihar, Madhya Pradesh, Uttar Pradesh and Orissa, total of 37 lakh ineligible/fake ration cards for households have been eliminated. Additionally, in Maharashtra and Madhya Pradesh, 29 lakh and 25 lakh ineligible ration cards were discovered and cancelled.
(c) World Bank published a Discussion Paper No. 380 titled “India’s Public Distribution System: A National and International Perspective” dated November, 1997 coauthored by R. Radhakrishna and K. Subbarao, in which it was found that in the year in 1986-87 for every one rupee (Re. 1) transferred under the PDS, the expenditure incurred by the central government was Rs. 4.27.
(d) The Planning Commission of India in its Performance Evaluation Report titled “Performance Evaluation Report of Targeted Public Distribution System (TPDS)” dated March, 2005 found as follows:
(i) State-wise figure of excess Ration Cards in various states and the existence of over 1.52 Crore excess Ration Cards issued.
(ii) Existence of fictitious households and identification errors leading to exclusion of genuine beneficiaries.
(iii) Leakage through ghost BPL Ration Cards found to be prevalent in almost all the states under study. (iv) The Leakage of food grains through ghost cards has been tabulated and the percentage of such leakage on an All India basis has been estimated at 16.67%.
(v) It is concluded that a large part of the subsidized food-grains were not reaching the target group.
(II) Report relating to Fuel subsidies
13. With respect of Kerosene subsidies:
(a) A Report titled “Budgetary Subsidies in India – Subsidizing Social and Economic Services” prepared by the National Institute of Public Finance and Policy dated March, found that the key to lowering volume of subsidies was better targeting without which, there was significant leakage to unintended beneficiaries, with only 70% of the kerosene reaching the poorer section of society.
(b) The Economic Survey 2014-15 at Chapter 3 titled “Wiping Every Tear from every Eye: The JAM Number Trinity Solution” dated February, 2015 noted that only 59 percent of subsidized kerosene allocated via the PDS is actually consumed by households, with the remainder lost to leakage and only 46 percent of total consumption is by poor households.
14. With respect to the MGNREGA Scheme the following reports have found large scale leakages in the scheme:
(a) Report prepared by the V.V. Giri National Labour Institute and sponsored by the Department of Rural Development, Ministry of Rural Development, Government of India as “The study of Schedule of Rates for National Rural Employment Guarantee Scheme” observes that there was great fraud in making fake job cards and it was found that in many cases, it was found that workers performed one day’s job, but their attendance was put for 33 days. The workers got money for one day while wages for 32 days were misappropriated by the people associated with the functioning of NREGS.
(b) The National Institute of Public Finance and Policy’s report titled as “A Cost-benefit analysis of Aadhaar” dated 09.11.2012 estimated that a leakage of approximately 12 percent is being caused to the government on account of ghost workers and manipulated muster rolls and assumed that 5 percent of the leakages can be plugged through wage disbursement using Aadhaar-enabled bank accounts and 7 percent through automation of muster rolls.
(III) It was also pointed out that the Thirteenth Finance Commission Report for 2010-2015 dated December, 2009 at page 218 in “Chapter 12 – Grants in Aid” states that the creation of a biometric-based unique identity for all residents in the country has the potential to address need of the government to ensure that only eligible persons are provided subsidies and benefits and that all eligible persons are covered. The relevant findings of the above Report are as follows:
(i) Government of India’s expenditure on subsidies is expected to be about Rs.1,11,000 Crore in 2009-10, or nearly 18 per cent of the non-plan revenue expenditure.
(ii) The data base of eligible persons presently maintained has both Type I (exclusion) and Type II (inclusion) errors. The first error arises from the difficulty faced by the poor in establishing their identity in order to be eligible for government subsidies and social safety net programmes. The second error arises because of the inability to cross-verify lists of eligible persons across district-level and state-level data bases to eliminate duplicate and ghost entries. We need to ensure that only eligible persons are provided subsidies and benefits and that all eligible persons are covered.
(iii) Creation of a biometric-based unique identity for all residents in the country has the potential to address both these dimensions simultaneously. It will provide the basis for focusing subsidies to target groups. Possession of such an identity will also enable the poor and underprivileged to leverage other resources like bank accounts, cell phones, which can empower them and catalyse their income growth. These benefits cannot be accessed by them presently due to their inability to provide acceptable identification. The initiative to provide unique IDs has the potential to significantly improve the governance and delivery framework of public services while substantially reducing transaction costs, leakages and frauds.
308) As against the above larger public interest, the invasion into the privacy rights of these beneficiaries is minimal. By no means it can be said that it has disproportionate effect on the right holder.
309) Intensity of review depends upon the particular context of question in a given case. There is yet another significant angle in these matters, which has to be emphasised at this stage viz. dignity in the form of autonomy (informational privacy) and dignity in the form of assuring better living standards, of the same individual. In the instant case, a holistic view of the matter, having regard to the detailed discussion hereinabove, would amply demonstrate that enrolment in Aadhaar of the unprivileged and marginalised section of the society, in order to avail the fruits of welfare schemes of the Government, actually amounts to empowering these persons. On the one hand, it gives such individuals their unique identity and, on the other hand, it also enables such individuals to avail the fruits of welfare schemes of the Government which are floated as socio-economic welfare measures to uplift such classes. In that sense, the scheme ensures dignity to such individuals. This facet of dignity cannot be lost sight of and needs to be acknowledged. We are, by no means, accepting that when dignity in the form of economic welfare is given, the State is entitled to rob that person of his liberty. That can never be allowed. We are concerned with the balancing of the two facets of dignity. Here we find that the inroads into the privacy rights where these individuals are made to part with their biometric information, is minimal. It is coupled with the fact that there is no data collection on the movements of such individuals, when they avail benefits under Section 7 of the Act thereby ruling out the possibility of creating their profiles. In fact, this technology becomes a vital tool of ensuring good governance in a social welfare state. We, therefore, are of the opinion that the Aadhaar Act meets the test of balancing as well.
310) We may profitably refer to the judgment of this Court in People’s Union for Civil Liberties (PUCL) & Anr. v. Union of India & Anr.104 which dealt with the issue of right to privacy vis-a-vis in public interest and leaned in favour of public interest which can be seen from the following discussion:
“121. It has been contended with much force that the right to information made available to the voters/citizens by judicial interpretation has to be balanced with the right of privacy of the spouse of the contesting candidate and any insistence on the disclosure of assets and liabilities of the spouse invades his/her right to privacy which is implied in Article 21. After giving anxious consideration to this argument, I am unable to uphold the same. In this context, I would like to recall the apt words of Mathew, J., in Gobind v. State of M.P. [1969 UJ (SC) 616] While analysing the right to privacy as an ingredient of Article 21, it was observed: (SCC p. 155, para 22)
“22. There can be no doubt that privacy-dignity claims deserve to be examined with care and to be denied only when an important countervailing interest is shown to be superior.”
(emphasis supplied)
It was then said succinctly: (SCC pp. 155-56, para 22) “If the court does find that a claimed right is entitled to protection as a fundamental privacy right, a law infringing it must satisfy the compelling State-interest test. Then the question would be whether a State interest is of such paramount importance as would justify an infringement of the right.”
It was further explained: (SCC p. 156, para 23) “[P]rivacy primarily concerns the individual. It therefore relates to and overlaps with the concept of liberty. The most serious advocate of privacy must confess that there are serious problems of defining the essence and scope of the right. Privacy interest in autonomy must also be placed in the context of other rights and values.” By calling upon the contesting candidate to disclose the assets and liabilities of his/her spouse, the fundamental right to information of a voter/citizen is thereby promoted. When there is a competition between the right to privacy of an individual and the right to information of the citizens, the former right has to be subordinated to the latter right as it serves the larger public interest. The right to know about the candidate who intends to become a public figure and a representative of the people would not be effective and real if only truncated information of the assets and liabilities is given.
It cannot be denied that the family relationship and social order in our country is such that the husband and wife look to the properties held by them as belonging to the family for all practical purposes, though in the eye of law the properties may distinctly belong to each of them. By and large, there exists a sort of unity of interest in the properties held by spouses. The property being kept in the name of the spouse benami is not unknown in our country. In this situation, it could be said that a countervailing or paramount interest is involved in requiring a candidate who chooses to subject himself/herself to public gaze and scrutiny to furnish the details of assets and liabilities of the spouse as well. That is one way of looking at the problem. More important, it is to be noted that Parliament itself accepted in principle that not only the assets of the elected candidates but also his or her spouse and dependent children should be disclosed to the constitutional authority and the right of privacy should not come in the way of such disclosure;…”
311) In Vernonia School District 47J v. Acton et ux., Guardians Ad Litem for Acton105, the Supreme Court of United States, while repelling the Fourth Amendment challenge wherein the petitioner had adopted a Drug Policy which authorised random urinalysis drug testing of students participating in athletics programs, remarked as under: “Taking into account all the factors we have considered above- the decreased expectation of privacy, the relative unobtrusiveness of the search, and the severity of the need met by the search-we conclude Vernonia’s Policy is reasonable and hence constitutional.”
312) This very exercise of balancing of two fundamental rights was also carried out in Subramanian Swamy v. Union of India, Ministry of Law & Ors.106 where the Court dealt with the matter in the following manner:
“122. In State of Madras v. V.G. Row [State of Madras v. V.G. Row, AIR 1952 SC 196 : 1952 Cri LJ 966], the Court has ruled that the test of reasonableness, wherever prescribed, should be applied to each individual statute impugned and no abstract standard, or general pattern of reasonableness can be laid down as applicable to all cases. The nature of the right alleged to have been infringed, the underlying purpose of the restrictions imposed, the extent and urgency of the evil sought to be remedied thereby, the disproportion of the imposition, the prevailing conditions at the time, should all enter into the judicial verdict.
xx xx xx
130. The principles as regards reasonable restriction as has been stated by this Court from time to time are that the restriction should not be excessive and in public interest. The legislation should not invade the rights and should not smack of arbitrariness. The test of reasonableness cannot be determined by laying down any abstract standard or general pattern. It would depend upon the nature of the right which has been infringed or sought to be infringed. The ultimate “impact”, that is, effect on the right has to be determined.
The “impact doctrine” or the principle of “inevitable effect” or “inevitable consequence” stands in contradistinction to abuse or misuse of a legislation or a statutory provision depending upon the circumstances of the case. The prevailing conditions of the time and the principles of proportionality of restraint are to be kept in mind by the court while adjudging the constitutionality of a provision regard being had to the nature of the right. The nature of social control which includes public interest has a role. The conception of social interest has to be borne in mind while considering reasonableness of the restriction imposed on a right. The social interest principle would include the felt needs of the society.
xx xx xx
Balancing of fundamental rights
136. To appreciate what we have posed hereinabove, it is necessary to dwell upon balancing the fundamental rights. It has been argued by the learned counsel for the petitioners that the right conferred under Article 19(1)(a) has to be kept at a different pedestal than the individual reputation which has been recognised as an aspect of Article 21 of the Constitution. In fact the submission is that right to freedom of speech and expression which includes freedom of press should be given higher status and the individual’s right to have his/her reputation should yield to the said right. In this regard a passage from Sakal Papers (P) Ltd. [Sakal Papers (P) Ltd. v. Union of India, (1962) 3 SCR 842 : AIR 1962 SC 305] has been commended to us.
It says: (AIR pp. 313-14, para 36) “36. … Freedom of speech can be restricted only in the interests of the security of the State, friendly relations with foreign State, public order, decency or morality or in relation to contempt of court, defamation or incitement to an offence. It cannot, like the freedom to carry on business, be curtailed in the interest of the general public. If a law directly affecting it is challenged, it is no answer that the restrictions enacted by it are justifiable under clauses (3) to (6). For, the scheme of Article 19 is to enumerate different freedoms separately and then to specify the extent of restrictions to which they may be subjected and the objects for securing which this could be done. A citizen is entitled to enjoy each and every one of the freedoms together and clause (1) does not prefer one freedom to another. That is the plain meaning of this clause. It follows from this that the State cannot make a law which directly restricts one freedom even for securing the better enjoyment of another freedom.”
(emphasis supplied)
137. Having bestowed our anxious consideration on the said passage, we are disposed to think that the above passage is of no assistance to the petitioners, for the issue herein is sustenance and balancing of the separate rights, one under Article 19(1)(a) and the other, under Article 21. Hence, the concept of equipoise and counterweighing fundamental rights of one with other person. It is not a case of mere better enjoyment of another freedom. In Acharya Maharajshri Narendra Prasadji Anandprasadji Maharaj v. State of Gujarat [Acharya Maharajshri Narendra Prasadji Anandprasadji Maharaj v. State of Gujarat, (1975) 1 SCC 11], it has been observed that a particular fundamental right cannot exist in isolation in a watertight compartment. One fundamental right of a person may have to coexist in harmony with the exercise of another fundamental right by others and also with reasonable and valid exercise of power by the State in the light of the directive principles in the interests of social welfare as a whole. The Court’s duty is to strike a balance between competing claims of different interests…
xx xx xx
194. Needless to emphasise that when a law limits a constitutional right which many laws do, such limitation is constitutional if it is proportional. The law imposing restriction is proportional if it is meant to achieve a proper purpose, and if the measures taken to achieve such a purpose are rationally connected to the purpose, and such measures are necessary. Such limitations should not be arbitrary or of an excessive nature beyond what is required in the interest of the public.
Reasonableness is judged with reference to the objective which the legislation seeks to achieve, and must not be in excess of that objective (see P.P. Enterprises v. Union of India [P.P. Enterprises v. Union of India, (1982) 2 SCC 33 : 1982 SCC (Cri) 341]). Further, the reasonableness is examined in an objective manner from the standpoint of the interest of the general public and not from the point of view of the person upon whom the restrictions are imposed or abstract considerations (see Mohd. Hanif Quareshi v. State of Bihar [Mohd. Hanif Quareshi v. State of Bihar, AIR 1958 SC 731]).”
313) Thus, even when two aspects of the fundamental rights of the same individual, which appear to be in conflict with each other, is done, we find that the Aadhaar Act has struck a fair balance between the right of privacy of the individual with right to life of the same individual as a beneficiary. In the face of the all pervading prescript for accomplished socio-economic rights, that need to be given to the deprived and marginalised section of the society, as the constitutional imperative embodied in these provisions of the Act, it is entitled to receive judicial imprimatur.
Re : Argument on Exclusion:
314) Some incidental aspects, however, remain to be discussed. It was argued by the petitioners that the entire authentication process is probabilistic in nature inasmuch as case of a genuine person for authentication can result in rejection as biometric technology does not guarantee 100% accuracy. It may happen for various reasons, namely, advance age, damage to fingerprints due to accident, etc. Even in case of children the fingerprints may change when they grow up. The emphasis was that there was a possibility of failure in authentication for various reasons and when it happens it would result in the exclusion rather than inclusion.
In such eventuality an individual would not only be denied the benefits of welfare schemes, it may threaten his very identity and existence as well and it would be violative of Articles 14 and 21 of the Constitution. The Authority has claimed that biometric accuracy is 99.76%. It was, however, submitted that where more than 110 crores of persons have enrolled themselves, even 0.232% failure would be a phenomenal figure, which comes to 27.60 lakh people. Therefore, the rate of exclusion is alarming and this would result in depriving needy persons to enjoy their fundamental rights, which is the so-called laudable objective trumpeted by the respondents.
TO DICTATE FURTHER
Re.: Studies on exclusion
Re.: Finger prints of disabled, old persons etc.
See other mode of identity
315) The aforesaid apprehensions are sought to be assuaged by the respondents by submitting that Section 7 of the Act nowhere says that if authentication fails, the concerned person would be deprived of subsidies, benefits or services. It is only an enabling provision. It also provides that in case of such a failure, such an individual would be permitted to establish her identity by any other means so that genuine persons are not deprived of their benefits which are mentioned in Section 7 as the entire Act is to facilitate delivery of those benefits to such persons. Learned Attorney General also referred to the Circular dated October 24, 2017 in this behalf which is issued by the Authority. That, according to us, takes care of the problem.
316) We understand and appreciate that execution of the Aadhaar scheme, which has otherwise a laudable objective, is a ‘work in progress’. There have been substantial improvements in the system over a period of time from the date of its launch. It was stated by the learned Attorney General as well as Mr. Rakesh Dwivedi, at the Bar, that whenever difficulties in implementation are brought to the notice of the respondents, remedial measures are taken with promptness. Cases of denial of services are specifically looked into which is very much needed in a welfare State and there can be a genuine hope that with the fine tuning of technology, i.e. the mode of advancement at rapid pace, such problems and concerns shall also be completely taken care of.
317) In fairness to the petitioners, it is worth mentioning that they have referred to the research carried out by some individuals and even NGOs which have been relied upon to demonstrate that there are number of instances leading to the exclusion i.e. the benefits are allegedly denied on the ground of failure of authentication. The respondents have refuted such studies. These become disputed question of facts. It will be difficult to invalidate provisions of Parliamentary legislations on the basis of such material, more particularly, when their credence has not been tested.
318) That apart, there is another significant and more important aspect which needs to be highlighted. The objective of the Act is to plug the leakages and ensure that fruits of welfare schemes reach the targeted population, for whom such schemes are actually meant. This is the larger purpose, and very important public purpose, which the Act is supposed to subserve. We have already held that it fulfills legitimate aim and there is a rational connection between the provisions of the Act and the goals which it seeks to attain. The Act passes the muster of necessity stage as well when we do not find any less restrictive measure which could be equally effective in achieving the aim. In a situation like this where the Act is aimed at achieving the aforesaid public purpose, striving to benefit millions of deserving people, can it be invalidated only on the ground that there is a possibility of exclusion of some of the seekers of these welfare schemes? Answer has to be in the negative.
We may hasten to add that by no means, we are accepting that if such an exclusion takes place, it is justified. We are only highlighting the fact that the Government seems to be sincere in its efforts to ensure that no such exclusion takes place and in those cases where an individual who is rightfully entitled to benefits under the scheme is not denied such a benefit merely because of failure of authentication. In this scenario, the entire Aadhaar project cannot be shelved. If that is done, it would cause much more harm to the society.
319) We are also conscious of the situation where the formation of fingerprints may undergo change for various reasons. It may happen in the case of a child after she grows up; it may happen in the case of an individual who gets old; it may also happen because of damage to the fingers as a result of accident or some disease etc. or because of suffering of some kind of disability for whatever reason. Even iris test can fail due to certain reasons including blindness of a person. We again emphasise that no person rightfully entitled to the benefits shall be denied the same on such grounds. It would be appropriate if a suitable provision be made in the concerned regulations for establishing an identity by alternate means, in such situations.
Furthermore, if there is a 0.232% failure in authentication, it also cannot be said that all these failures were only in those cases where authentication was for the purpose of utilising for the benefit of the welfare schemes, i.e. with reference to Section 7 of the Act. It could have happened in other cases as well. Be as it may, there is yet another angle which has to be kept in mind and cannot be ignored. We have already highlighted above as to how the Aadhaar project is aimed at serving a much larger public interest. The Authority has claimed that biometric accuracy is 99.76% and the petitioners have also proceeded on that basis. In this scenario, if the Aadhaar project is shelved, 99.76% beneficiaries are going to suffer.
Would it not lead to their exclusion? It will amount to throwing the baby out of hot water along with the water. In the name of 0.232% failure (which can in any case be remedied) should be revert to the pre-Aadhaar stage with a system of leakages, pilferages and corruption in the implementation of welfare schemes meant for marginalised section of the society, the full fruits thereof were not reaching to such people? The Aadhaar programme was conceived and conceptualised by Mr. Nandan Nilekani under the leadership of then Prime Minister, a great economist himself. It went through rigorous process of testing about its effectiveness before it is launched. This has been stated in the beginning.
The entire aim behind launching this programme is the ‘inclusion’ of the deserving persons who need to get such benefits. When it is serving much larger purpose by reaching hundreds of millions of deserving persons, it cannot be crucified on the unproven plea of exclusion of some. We again repeat that the Court is not trivialising the problem of exclusion if it is there. However, what we are emphasising is that remedy is to plug the loopholes rather than axe a project, aimed for the welfare of large section of the society. Obviously, in order to address the failures of authentication, the remedy is to adopt alternate methods for identifying such persons, after finding the causes of failure in their cases. We have chosen this path which leads to better equilibrium and have given necessary directions also in this behalf.
320) Another facet which needs examination at this stage is the meaning that is to be assigned to the expression ‘benefits’ occurring in Section 7 of the Aadhaar Act, along with ‘subsidies’ and ‘services’. It was argued that the expression ‘benefits’ is very lose and wide and the respondents may attempt to bring within its sweep any and every kind of governmental activity in the name of welfare of communities, which would result in making the requirement of Aadhaar virtually mandatory. It was pointed out that by issuing various circulars the Government has already brought within the sweep of Section 7, almost 139 such subsidies, services and benefits.
321) No doubt, the Government cannot take umbrage under the aforesaid provision to enlarge the scope of subsidies, services and benefits. ‘Benefits’ should be such which are in the nature of welfare schemes for which resources are to be drawn from the Consolidated Fund of India. Therefore actions by CBSE, NEET, JEE and UGC requirements for scholarship shall not be covered under Section 7, unless it is demonstrated that the expenditure is incurred from Consolidated Fund of India. Further, the expression ‘benefit’ has to be read ejusdem generis with the preceding word ‘subsidies’.
322) We also make it clear that a benefit which is earned by an individual (e.g. pension by a government employee) cannot be covered under Section 7 of the Act, as it is the right of the individual to receive such benefit. At the same time, we have gone through the list of notifications which are issued under Section 7 of the Aadhaar Act. We find that most of these notifications pertain to various welfare schemes under which benefits, subsidies or services are provided to the intending recipients. Moreover, in order to avail the benefits, only one time verification is required except for few services where annual verification is needed. It is only in respect of fertilizer subsidy where authentication is required every time the fertilizer is disbursed. However, it is clarified that fertilizer is also given on the basis of other documents such as Kisan Credit Card, etc. At the same time, we hope that the respondents shall not unduly expand the scope of ‘subsidies, services and benefits’ thereby widening the net of Aadhaar, where it is not permitted otherwise. Insofar as notifications relating to children are concerned, we have already dealt with the same separately. We, thus, conclude this aspect as under:
(a) ‘benefits’ and ‘services’ as mentioned in Section 7 should be those which have the colour of some kind of subsidies etc., namely, welfare schemes of the Government whereby Government is doling out such benefits which are targeted at a particular deprived class.
(b) The expenditure thereof has to be drawn from the Consolidated Fund of India.
(c) On that basis, CBSE, NEET, JEE, UGC etc. cannot make the requirement of Aadhaar mandatory as they are outside the purview of Section 7 and are not backed by any law.
Children:
323) Though, we have upheld, in general, the validity of Section 7 of the Aadhaar Act, one specific aspect thereof is yet to be considered. Section 7 mandates requirement of Aadhaar for the purposes of receiving certain subsidies, benefits and services. Thus, any individual who wants to seek any of these subsidies, benefits and services is compulsorily required to have an Aadhaar number. This will include children as well. Some of the petitioners as well as some other applicants who have intervened in these petitions have expressed their concern about the mandatory requirement of Aadhaar for children and subsequent linking for realising their basic rights including education. They have referred to various circulars and notifications issued through various functionaries, schools, The Ministry of Human Resource Development (MHRD) which have mandated production of Aadhaar card details for the children seeking admission to schools and to link the Aadhaar of the students already enrolled. We have held that Aadhaar is a voluntary scheme and, therefore, the Aadhaar number is to be alloted to an individual on his ‘consent’. No doubt, for the purposes of utilising any of the benefits under Section 7 of the Aadhaar Act, it becomes necessary to have Aadhaar number. However, the question is as to whether it can be extended to children? It is more so when they are not under legal capacity to provide any ‘consent’ under the law.
324) Article 21A of the Constitution guarantees right to education and makes it fundamental right of the children between 6 years and 14 years of age. Such a right cannot be taken away by imposing requirement of holding Aadhaar card, upon the children.
325) In view thereof, admission of a child in his school cannot be covered under Section 7 of the Aadhaar Act as it is neither subsidy nor service. No doubt, the expression ‘benefit’ occurring in Section 7 is very wide. At the same time, it has to be given restrictive meaning and the admission of children in the schools, when they have fundamental right to education, would not be covered by Section 7, in our considered view. The respondents made an attempt to justify the linkage of Aadhaar with child information and records by arguing that there have been several instances of either impersonations at examinations or bogus admissions which have the potential to pilfer away various scholarship schemes which the Government provides for weaker sections from time to time.
If this is the objective, then also requirement of Aadhaar cannot insisted at the time of admission but only at the stage of application for Government scholarships. Insofar as impersonation at examination is concerned, that can be easily checked and contained by other means with effective checks and balances. When there are alternative means, insistence on Aadhaar would not satisfy the test or proportionality. This would violate the privacy right of the children importance whereto is given by the Constitution Bench in K.S. Puttaswamy in the following words: “633. Children around the world create perpetual digital footprints on social network websites on a 24/7 basis as they learn their ‘ABCs’: Apple, Bluetooth, and Chat followed by Download, E-Mail, Facebook, Google, Hotmail, and Instagram. They should not be subjected to the consequences of their childish mistakes and naivety, their entire life. Privacy of children will require special protection not just in the context of the virtual world, but also the real world.”
326) It is also important to note herein that the Juvenile Justice Act, 2015 while addressing children in need of care and protection and children in conflict with law enunciates that the records of the children are confidential and will not be parted with unless requested by the Children’s Court. In contrast, the submission of the Union justifying linking of Aadhaar with student records on malpractice in examinations and potential bogus admissions with no safeguards whatsoever.
327) It has to be kept in mind that when the children are incapable of giving consent, foisting compulsion of having Aadhaar card upon them would be totally disproportionate and would fail to meet the proportionality test. As the law exists today, a child can hold property, operate a bank account, be eligible to be a nominee in an insurance policy or a bank account or have any financial transaction only through a legal guardian who has to be a major of sound mind. In cases where a child is in conflict with the law, the child is given a special criminal trial under the Juvenile Justice (Care and Protection of Children) Act, 2015 and there is a mandatory requirement for the records to be kept confidential and destroyed so that the criminal record of the child is not maintained. This is the position in law contained in Section 11 of the Indian Contract Act, 1872, Section 45ZA of the Banking Regulation Act, 1949, Section 39 of the Insurance Act, 1938, Section 90 of the Indian Penal Code (which provides that consent of the child who is under 12 years of age shall not be regarded as consent) etc.
Thus, when a child is not competent to contract; not in a position to consent; barred from transferring property; prohibited from taking employment; and not allowed to open/operate bank accounts and, as a consequence, not in a position to negotiate her rights, thirsting upon compulsory requirement of holding Aadhaar would be an inviable inroad into their fundamental rights under Article 21. The restriction imposed on such a right in the form of an Aadhaar cannot be treated as constitutionally justified. We may also mention here that State is supposed to keep in mind the best interest of the children which is regarded as primary consideration in our Constitution (See R.D. Upadhyay v. State of Andhra Pradesh & Ors.107). The convention on the Rights of Child108 reiterates that the best interests of the child will be the basic concern of the parents or legal guardians of the child.
The Constitution affirms acting in the best interest of the children and confers the responsibility on the State to not only safeguard the best interests of children but also act in furtherance of it. Therefore, we are of the opinion that the State is constitutionally bound to facilitate and enable the parents and guardians of the children to assert their rights and act in their best interest and this has to be done without having any mandatory directives to it. The onus of overseeing and lawfully safeguarding the rights and immunities, to which children are entitled to, rests on the State and the authorities under it. Giving proper education to children and ensuring that they become valuable citizens of this nation subserves public interest.
This is the mandate of Convention on the Rights of Child (CRC) as well. We may reproduce Article 27 of the CRC: “States Parties recognize the right of every child to a standard of living adequate for the child’s physical, mental, spiritual, moral and social development.
2. The parent(s) or others responsible for the child have the primary responsibility to secure, within their abilities and financial capacities, the conditions of living necessary for the child’s development.
3. States Parties, in accordance with national conditions and within their means, shall take appropriate measures to assist parents and others responsible for the child to implement this right and shall in case of need provide material assistance and support programmes, particularly with regard to nutrition, clothing and housing.”
328) Article 8 of the CRC provides that:
“(2) For the purpose of guaranteeing and promoting the rights set forth in the present Convention, States Parties shall render appropriate assistance to parents and legal guardians in the performance of their child-rearing responsibilities and shall ensure the development of institutions, facilities and services for the care of children.
(3) States Parties shall take all appropriate measures to ensure that children of working parents have the right to benefit from child-care services and facilities for which they are eligible.”
329) Further, Article 16 of the Convention on the Rights of Child, 1989 bars children from being subject to arbitrary or unlawful interference in their privacy, family, home, or correspondence. One of the principles espousing the Juvenile Justice Act, 2015 is the principle of confidentiality. Section 24 of the Act, dealing with children in conflict with law, further emphasizes:
“(2) The Board shall make an order directing the Police, or by the Children’s court to its own registry that the relevant records of such conviction shall be destroyed after the expiry of the period of appeal or, as the case may be, a reasonable period as may be prescribed.”
330) Section 3 of the Juvenile Justice Act, 2015 expounds the principles underlying the process in dealing with children under the Statute. The principle of right to privacy and confidentiality emphasizes, “Every child shall have a right to protection of his privacy and confidentiality, by all means and throughout the judicial process.”
331) We would like to reproduce the following observations of English quote in Murray v. Big Pictures (UK) Ltd.109 where greatest significance is attached to the privacy right when it comes to children. That was a case where photographer had taken a series of photographs of a writer’s infant son, which were later published in a newspaper. The issue was whether there was misuse of private information by taking photographs. It was held that: “The question of whether there is a reasonable expectation of privacy is a broad one, which takes account of all the circumstances of the case.
They include the attributes of the claimant, the nature of the activity in which the claimant was engaged, the place at which it was happening, the nature and purpose of the intrusion, the absence of consent and whether it was known or could be inferred, the effect on the claimant and the circumstances in which and the purposes for which the information came into the hands of the publisher…It is at least arguable that David had a reasonable expectation of privacy. The fact that he is a child is in our view of greater significance than the judge thought.” We may also record at this stage that various circulars, orders and notifications are issued by different Ministries and Departments under Section 7 of the Aadhaar Act which pertain to children. Some of these are:
(1) National Child Labour Project (NCLP).
(2) Scholarship schemes which are given to school students, like National Means-cum-Merit Scholarship Scheme; National Scheme of Incentive to Girls for Secondary Education; Benefit to 6 to 14 years children under Sarva Shiksha Abhiyan; Inclusive Education of the Disabled at Secondary State; and Mid-day Meal for Children.
(3) Assistance/Scholarship given by the Department of Empowerment to the Persons with Disabilities, which include Scholarship Schemes for education of students with disabilities.
(4) Following Schemes floated by the Ministry of Women and Child Development, some of which relate to children:
(a) Supplementary Nutrition Programme under ICDS Scheme.
(b) Payment of honorarium to AWWs & AWHs under ICDS Scheme.
(c) Supplementary Nutrition for children offered at Creche Centres.
(d) Honorarium paid towards the Creche Workers and Creche Helpers.
(e) Maternity Benefit Programme (MBP).
(f) Scheme for Adolescent Girls.
(g) National Mission for Empowerment of Women.
(h) ICDS Training Programme.
(i) Ujjawala Scheme.
(j) Swadhar Scheme.
(k) Integrated Child Protection Scheme.
(l) STEP programme.
(m) Rashtriya Mahila Kosh.
(n) Pradhan Mantri Matru Vanana Yojana.
(5) Painting and Essay competitions for school children under IEC component of Human Resource Development and Capacity Building.
332) After considering the matter in depth and having regard to the discussion aforesaid, we hold as under:
(a) For the enrolment of children under the Aadhaar Act, it would be essential to have the consent of their parents/guardian.
(b) On attaining the age of majority, such children who are enrolled under Aadhaar with the consent of their parents, shall be given the right to exit from Aadhaar, if they so choose.
(c) Insofar as the school admissions of children are concerned, requirement of Aadhaar would not be compulsory as it is neither a service nor subsidy. Further, having regard to the fact that a child between the age of 6 to 14 years has the fundamental right to education under Article 21A of the Constitution, school admission cannot be treated as ‘benefit’ as well.
(d) Benefits to children between 6 to 14 years under Sarva Shiksha Abhiyan, likewise, shall not require mandatory Aadhaar enrolment.
(e) For availing the benefits of other welfare schemes which are covered by Section 7 of the Aadhaar Act, though enrolment number can be insisted, it would be subject to the consent of the parents, as mentioned in (a) above.
(f) We also clarify that no child shall be denied benefit of any of these schemes if, for some reasons, she is not able to produce the Aadhaar number and the benefit shall be given by verifying the identity on the basis of any other documents. We may record that a statement to this effect was also made by Mr. K.K. Venugopal, learned Attorney General for India, at the Bar.
Challenge to the other provisions of the Aadhaar Act:
333) The petitioners have challenged the constitutionality of certain other provisions of Aadhaar Act as well. They have submitted their reasons on the basis of which they are seeking the declaration to the effect these provisions are unconstitutional. We reproduce the provisions of Aadhaar Act as well as reasons given by the petitioners in tabulated form, as under
|
S.No. |
Provisions of the Aadhaar Act |
Reason for being unconstitutional |
|
1. |
Section 2(c) and 2(d) – authentication and authentication record, read with Section 32 |
‘Authentication Record’ includes the time of authentication and the identity of the requesting entity. The UIDAI and the Authentication Service Agency (ASA) is permitted to store this authentication record for 2+5 years (as per Regulations 20 and 26/27 of the Authentication Regulations). By definition it provides for real-time surveillance and profiling. The record stores both the time and the identity of the requesting entity. |
|
2. |
Section 2(h) read with Section 10 of CIDR |
The notion of CIDR is by itself an unconstitutional database. The statute cannot operate without a CIDR. The notion of a CIDR where every individual’s biometric as well as demographic information is centrally stored is an authoritarian or police state construct and has no place in a democracy that guarantees individual freedom. A CIDR from where data can be backed, and which is operated not by the respondents but by foreign entities, is conceptually and constitutionally an impermissible compromise on national sovereignty and security. Notably, Section 10 empowers UIDAI to appoint one or more entity to establish and maintain the CIDR. |
|
3.
|
Section 2(l) read with Regulation 23 of the Aadhaar (Enrolment and Updates) Regulation – ‘enrolling agency’ |
The notion of an enrolling agency as defined in Section 2(l) is also unconstitutional inasmuch as the agency, as defined, need not be a Government entity but could be a private entity. The collection of sensitive personal biometric and demographic data and information for the purposes of storage must be conducted by a Government agency alone since this is a bare minimum procedural safeguard against the misuse and commercial exploitation of private personal information. The State, acting as a trustee and fiduciary, cannot delegate or require private enrolling agencies to discharge this non-delegable function. Moreover, an enrolling agency that is operated privately cannot be entrusted with the crucial tasks of explaining the voluntary nature of Aadhaar enrolments and securing informed consent. |
|
4. |
Section 2(v) – ‘resident’ |
The expression ‘Resident’ defined in Section 2(v) is arbitrary and unconstitutional inasmuch as the Act creates no credible machinery for evaluating a claim that a person has been residing in India for a period of 182 days or more, in the 12 months immediately preceding the date of application for enrolment. The forms being used by the respondents as also proof of identification and proof of address requirement being used by the respondents until enactment of the statute nowhere require any proof relating to residence for 182 days. The impugned Act purports to validate all these enrolments. The forms being used by the respondents do not even contain a declaration regarding the enrolee being resident for 182 days. Further, there is no requirement in the definition of ‘Resident’ that the person has to be legally resident and the expression would wrongly take in illegal immigrants as well. |
|
5. |
Section 3 – Aadhaar Number |
It is an ‘entitlement’. It cannot be understood to be mandatory. The information provided under Section 3(2) is of no relevance if obtaining Aadhaar is made mandatory. By design, Aadhaar was never meant to be mandatory. |
|
6. |
Section 5 – Special treatment to children |
Section 5 of the Aadhaar Act, inasmuch as it extends to children and persons with disabilities, implies that the State is securing biometric and demographic data even before the age of consent insofar as children are concerned. The Act in its coercive reach and application to children who have not attained the age of consent is per se unconstitutional and violate of the fundamental rights of the children. |
|
7. |
Section 6 – Update of information |
Section 6 of the Act is unconstitutional inasmuch as it enables the respondents to continually compel residents to periodically furnish demographic and biometric information. This provision is coercive in operation and effect and not only undermines the so-called ‘voluntary’ nature of the programme (as falsely claimed by the respondents) but also undermines the false claim with respect to the ‘reliability of biometrics’. |
|
8. |
Section 8 |
Section 8 is unconstitutional inasmuch as it enables tracking, tagging and profiling of individuals through the authentication process. It is a charter for surveillance in real time and with a degree of specificity that enables persons’ physical movements to be traced in real time. The authentication mandate in terms of Section 8 is not being worked by the respondents through any proprietary technology and is outsourced to foreign entities or entities under the ownership and control of foreign companies and corporations. The entire framework and working of the authentication procedure in terms of Section 8 is an impermissible, permanent and irreversible compromise of national sovereignty and national security. |
|
9. |
Section 9 |
Section 9 of the Aadhaar Act is also unconstitutional inasmuch as the Aadhaar number is de facto serving as proof of citizenship and domicile. This is seen from various media reports where even in the absence of any rigorous verification process, Aadhaar numbers are being issued. The petitioners submit that equally subversive of national security and national integrity is the practice of passports being issued based upon an Aadhaar card. In other words, persons who may not be entitled to passports are having Aadhaar numbers issued and thereafter securing passports in violation of the citizenship provisions. |
|
10. |
Chapter IV – Sections 11 to 23 |
The petitioners submit that the whole of Chapter IV of the Act comprising Sections 11 to 23 is ultra vires and unconstitutional. The Constitution does not permit the establishment of an authority that in turn through an invasive programme can chain every Indian citizen/resident to a central data bank and maintain lifelong records and logs of that individual. The Constitution of India when read as a whole is designed for a nation of free individuals who enjoy a full range of rights and who are entitled under the Constitution to lead their lives without any monitoring or scrutiny or continuous oversight by the State or any of its organs. The high value of personal freedom runs throughout the fabric of the Indian Constitution and any authority created for the purpose of ‘cradle to grave’ scrutiny is directly violative of the personal freedom charter built into the Indian Constitution. The Constitution of India does not contemplate a ‘nanny state’ where the State oversees every individual’s conduct and maintains a record of individual interactions. The UIDAI by design and function is created for an absolutely unconstitutional objective of invading privacy, electronically overseeing individuals and tethering them to a central data repository that will maintain lifelong records. The notion of individual freedom must entail the right to be alone; the right of an individual to be free from any monitoring so long as that individual does not breach or transgress any criminal law. Here, the establishment of the second respondent is for an unconstitutional purpose of overseeing and monitoring individual conduct even where the person does not remotely fall foul of any law. The second respondent is a State organ designed to invade individual freedom and whose purpose is to constrict individual freedom. |
|
11. |
Sections 23 and 54 – excessive delegation |
Section 23, read with Section 54 of the Aadhaar Act, is unconstitutional on the ground of excessive delegation. A perusal of the sub-clauses in Section 23(2) and Section 54(2) indicate that on every crucial aspect pertaining to biometric data, demographic information, the operation and working of the CIDR, generating and assigning Aadhaar numbers, authentication of Aadhaar numbers, omitting and deactivating Aadhaar numbers, commercial exploitation of information collected by the Government, etc. are all left entirely to the UIDAI without any sufficient defined legislative policy indicating the limits within which the UIDAI may legitimately operate. Having regard to the invasive nature of the Aadhaar programme, its deep and pervasive impact on civil liberties and the fiduciary/trusteeship principle based on which data and information is being collected, it was incumbent upon the legislature to set out detailed and adequate limits to restrict the discretion conferred on the UIDAI. The impugned provisions virtually give an unlimited charter to the UIDAI to ride rough shod over fundamental rights by framing regulations as it pleases. |
|
12. |
Section 23(2)(g) read with Chapter VI & VII – Regulations 27 to 32 of the Aadhaar (Enrolment and Update) Regulations, 2016 |
This empowers the UIDAI alone to omit and deactivate an Aadhaar number with almost no redressal to the individual Aadhaar number holder. Regulation 27(2) provides that upon cancellation of an Aadhaar number, all services provided by the authority shall be permanently disabled. Regulation 28(2) provides that upon deactivation of an Aadhaar number, all numbers shall be temporarily suspended till such time that the Aadhaar number holder updates or rectifies the alleged error. Notably, as per Regulation 30, there shall be a post facto communication of omission or deactivation of the Aadhaar number shall be informed to the Aadhaar number holder. The only redressal mechanism provided under the Aadhaar Act is under Regulation 32 wherein a grievance redressal call centre shall be provided by the UIDAI. This provision provides unbridled power to the UIDAI to switch of the life of an individual. There is absolutely no redressal mechanism for the individual. He is not even provided with an opportunity of hearing prior to deactivation, which violates principles of natural justice. |
|
13. |
Section 29 |
This Section is liable to be struck down inasmuch as it pertains sharing of identity information. The provisions suffer from the vice of permitting the spread and dissemination of sensitive personal information through a network of entities and individuals for commercial gain or otherwise and allows for the sharing of information beyond the ostensible object of targeted deliveries. Both the biometric as well as the demographic information are entitled to the highest degree of protection and the impugned provision, inasmuch as it draws a distinction between core biometric information and other information, creates an artificial distinction into two classes of information which in law are both entitled to equal protection against sharing or dissemination. Sub-section (4) permits UIDAI by regulation to permit ‘core biometric information’ to be displayed publicly. |
|
14. |
Section 33 |
Section 33 is unconstitutional inasmuch as it provides for the use of the Aadhaar database for police investigation pursuant to an order of a competent court. Section 3 violates the protection against selfincrimination as enshrined under Article 20(3) of the Constitution of India. Furthermore, Section 33 does not afford an opportunity of hearing to the concerned individual whose information is sought to be released by the UIDAI pursuant to the Court’s order. This is contrary to the principles of natural justice. Section 33(2) provides for disclosure of information in the interest of national security pursuant to a direction of a competent officer. The said provision is also hit by the principles of protection against self-incrimination, as enshrined under Article 20(3) of the Constitution. Further, the impugned Act does not define ‘interest of national security’ or otherwise limit the circumstances where the said provision can be invoked. This makes the impugned provision unconstitutional as it suffers from the vice of vagueness and arbitrariness. |
|
15. |
Section 47 |
Section 47 of the impugned Act is unconstitutional inasmuch as it does not allow an individual citizen who finds that there is a violation of the impugned Act to initiate the criminal process. There could be several circumstances where UIDAI itself or some third party is guilty of having committed offences under the Act. By restricting the initiation of the criminal process, the Aadhaar Act renders the penal machinery ineffective and sterile. The said section creates a bar on a court to take cognizance of any offence under the impugned Act, save on a complaint made by the UIDAI or an officer authorized by it. In effect there is a bar of cognizance of a complaint made by an individual for breach of his biometric or demographic information which has been collected by the respondent. Such bar is unconstitutional as it forecloses legal remedy to affected individuals. |
|
16. |
Section 48 – Power of Central Government to supersede UIDAI |
This Section is vague and arbitrary inasmuch as it permits the Central Government to take over the UIDAI. The Act does not define a ‘pubic emergency’. This Section empowers the Central Government in an ’emergency’ situation to be in a position to completely control the life of every citizen who is enrolled with the UIDAI. |
|
17. |
Section 57 |
Section 57 is patently unconstitutional inasmuch as it allows an unrestricted extension of the Aadhaar platform to users who may be Government agencies or private sector operators. This provision clearly shows that the impugned Act has a much wider scope than what may legitimately be considered as a Money Bill. Moreover, this provision enables the seeding of the Aadhaar number across service providers and other gateways and thereby enables the establishment of a surveillance state. The impugned provision enables the spread of applications and Aadhaar dependent delivery systems that are provided not from Consolidated Fund of India resources but through any other means. It is submitted that Section 57 also enables commercial exploitation of an individual’s biometrics and demographic information by the respondents as well as private entities. It ensures that creation of a surveillance society, where every entity assists the State to snoop upon an Aadhaar holder. |
|
18. |
Section 59 |
Section 59 of the impugned Act is unconstitutional inasmuch as it seeks to validate all action undertaken by the Central Government pursuant to the Notification dated January 28, 2009. It is submitted that there was no consent, let alone informed consent obtained from individuals at the time of enrolment under the said notification. Such enrolment which has been conducted without obtaining adequate consent is unconstitutional as it amounts to wrongful deprivation of the most intimate personal information of an individual. Indeed, taking of an individual’s biometric information without informed consent is a physical invasion of his or her bodily integrity. The collection of demographic information through private entities and without proper counselling or written informed consent is illegal and incapable of being retrospectively ratified. All these records which have been illegally obtained and created without necessary consent out to be destroyed and cannot be said to be validated by the impugned provision. The Parliament cannot create a legal fiction of ‘consent’ where there was none. The executive under the Constitution of India cannot take away someone’s fundamental right to privacy and then support its action on the proposition of law that ‘retrospectively’ deems consent must have been given. The said provision seeks to validate any action taken by the Central Government alone. The action of private enrolers is not even sought to be protected. Therefore, all collections made by private entities under the said notification should also stand invalidated and all data collected by private entities should be destroyed forthwith. |
334) We have already dealt with the issue of validity of some of the provisions. We would now advert to the remaining provisions, validity whereof is questioned. Keeping in view the preceding discussion, challenge to most of these provisions would fail. Insofar as Section 2(l) read with Regulation 23 of the Aadhaar (Enrolment and Update) Regulations is concerned which deals with ‘enrolling agency’, main challenge is on the ground that the work of an enrolment could not have been given to a private entity as private entity cannot be entrusted with the crucial task of explaining the nature of Aadhaar enrolment and securing informed consent. Further, the task of collection of sensitive personal biometric and demographic data and information for the purpose of storage cannot be given to private hands. However, having regard to the nature of process that has been explained by the Authority, which ensures that immediately on enrolment, the concerned data collected by the private entity is beyond its control; it gets encrypted; and stands transmitted to CIDR, we do not find any basis of the apprehension expressed by the petitioners.
335) Insofar as Section 2(v) is concerned which defines resident, there is nothing wrong with the definition. The grievance of the petitioners is that the Aadhaar Act creates no credible machinery for availing a claim that a person has been residing in India for 182 days or more. Apprehension is expressed that this expression may also facilitate the entry of illegal immigrants. These aspects can be taken care of by the respondents by providing appropriate mechanism. We direct the respondents to do the needful in this behalf. However, that would not render the definition unconstitutional.
336) Section 3, by the very language thereof, mentions that it is an enabling provision which ‘entitles’ every resident to obtain Aadhaar number. Therefore, it is voluntary in nature. This is so held by Division Bench of this Court in Binoy Viswam in the following words:
“93. Before proceeding to discuss this argument, one aspect of the matter needs clarification. There was a debate as to whether the Aadhaar Act is voluntary or even that Act makes enrolment under Aadhaar mandatory.
94. First thing that is to be kept in mind is that the Aadhaar Act is enacted to enable the Government to identify individuals for delivery of benefits, subsidies and services under various welfare schemes. This is so mentioned in Section 7 of the Aadhaar Act which states that proof of Aadhaar number is necessary for receipt of such subsidies, benefits and services. At the same time, it cannot be disputed that once a person enrols himself and obtains Aadhaar number as mentioned in Section 3 of the Aadhaar Act, such Aadhaar number can be used for many other purposes. In fact, this Aadhaar number becomes the Unique Identity (UID) of that person. Having said that, it is clear that there is no provision in the Aadhaar Act which makes enrolment compulsory. May be for the purpose of obtaining benefits, proof of Aadhaar card is necessary as per Section 7 of the Act. The proviso to Section 7 stipulates that if an Aadhaar number is not assigned to enable an individual, he shall be offered alternate and viable means of identification for delivery of the subsidy, benefit or service. According to the petitioners, this proviso, which acknowledges alternate and viable means of identification, and therefore makes Aadhaar optional and voluntary and the enrolment is not necessary even for the purpose of receiving subsidies, benefits and services under various schemes of the Government. The respondents, however, interpret the proviso differently and their plea is that the words “if an Aadhaar number is not assigned to an individual” deal with only that situation where application for Aadhaar has been made but for certain reasons Aadhaar number has not been assigned as it may take some time to give Aadhaar card. Therefore, this proviso is only by way of an interim measure till Aadhaar number is assigned, which is otherwise compulsory for obtaining certain benefits as stated in Section 7 of the Aadhaar Act. Fact remains that as per the Government and UIDAI itself, the requirement of obtaining Aadhaar number is voluntary. It has been so claimed by UIDAI on its website and clarification to this effect has also been issued by UIDAI. 95. Thus, enrolment under Aadhaar is voluntary. However, it is a moot question as to whether for obtaining benefits as prescribed under Section 7 of the Aadhaar Act, it is mandatory to give Aadhaar number or not is a debatable issue which we are not addressing as this very issue is squarely raised which is the subject-matter of other writ petition filed and pending in this Court.” Therefore, the apprehension of the petitioners that Section 3 is mandatory stands assuaged.
337) Section 5 is a special measure for issuance of Aadhaar number to certain category of persons which attempts to take care of certain disabilities with which certain individuals may be suffering. Therefore, this provision is for the benefit of the categories of persons mentioned in Section 5. No doubt, it mentions children and persons with disabilities as well, that is an aspect is already dealt with separately.
338) Section 6 deals only with the updation of demographic and biometric information. This may become necessary under certain circumstances. That by itself does not take away the voluntary nature of the programme.
339) Insofar Section 9 is concerned, validity thereof is challenged primarily on the ground that it serves as a proof of citizenship and domicile as well and some apprehensions are expressed on that basis. Such apprehensions have already been taken care of while discussing the issue no. 1 pertaining to surveillance.
340) We have already discussed in detail the purpose of constituting the Authority. In fact, the Act cannot operate without such an Authority and, therefore, it’s constitution is imperative. Challenge to validity of Sections 11 to 23 is predicated on the arguments of surveillance etc. fails, having regard to our detailed discussion on the said aspect.
341) Section 23 read with Section 54 give power to the Authority to make certain Regulations. We do not find that this provision gives excessive delegation to the Authority. These aspects have already been discussed while determining the issue pertaining to surveillance.
342) Apprehension expressed qua Section 29 are equally unfounded. This Section rather imposes restrictions on sharing information. No doubt, sub-section (2) states that the identity information (and specifically excludes core biometric information) can be shared only in accordance with the provisions of the Act and in such a manner as may be specified by Regulations. That would not make the provision unconstitutional when it is with the consent of the individual.
In case, any regulation is made which permits sharing of information that may contain undesirable circumstance/reason for sharing information, such a regulation can always be struck down. Insofar as sub-section (4) is concerned, it is generally in favour of the residents/individuals inasmuch as it states that information collected or created under this Act shall not be published, displayed or posted publicly. The is grievance, however, is that this provision enables the Authority to publish or display etc. such an information ‘for the purposes as may be specified by regulations’.
The apprehension is that under this provision, the Government can always make regulations permitting publication of such information under certain circumstances. At present, regulations which are in force are the Aadhaar (Sharing of Information) Regulations, 2016.
Chapter II thereof is titled ‘restriction on sharing of identity information’. Regulation 3(1) which falls under this chapter puts a categorical ban on sharing of core biometric information collected by the Authority under the Act, by mandating that it shall not be sharing with anyone for any reason whatsoever. Sub-regulation (2) of Regulation 3 permits sharing of demographic information and photograph of an individual collected by the Authority under the Act, only with the consent of the Aadhaar number holder, that too for authentication process in accordance with Authentication Regulations.
As already held by us, insofar as utilisation of subsidies, benefits and services are concerned, the authentication would be needed by the provider of such services which would be the requesting entity and this provision has already been upheld. Sub-regulation (3) permits sharing of authentication records of Aadhaar number holder with him in accordance with Regulation 28 of the Authentication Regulations. This provision facilitates obtaining the information from the Authority by the Aadhaar number holder herself. We are, thus, of the opinion that Section 29 and the sharing regulations are the provisions enacted to protect the interest of Aadhaar card holders as they put restrictions on the sharing of information, which may be described as provisions pertaining to data protection and surveying legitimate state aim/interest as well. No doubt, Section 29 gives power to the delegatee to make regulations. However, as already clarified above, as and when a regulation is made, which impinges upon the privacy right of the Aadhaar card holders, that can always be challenged. As of now, sharing regulations do not contain any such provision.
343) Section 33 provides for disclosure of information in certain cases. The challenge to this provision is predicated on the ground that it provides for the use of Aadhaar database for police verification, which is against the ethos of Article 20(3) of the Constitution of India, which is a rule against self-incrimination. In order to appreciate this argument, we would like to reproduce Section 33 in its entirety:
“33. (1) Nothing contained in sub-section (2) or sub-section (5) of section 28 or sub-section (2) of section 29 shall apply in respect of any disclosure of information, including identity information or authentication records, made pursuant to an order of a court not inferior to that of a District Judge: Provided that no order by the court under this subsection shall be made without giving an opportunity of hearing to the Authority.
(2) Nothing contained in sub-section (2) or sub-section (5) of section 28 and clause (b) of sub-section (1), sub-section (2) or sub-section (3) of section 29 shall apply in respect of any disclosure of information, including identity information or authentication records, made in the interest of national security in pursuance of a direction of an officer not below the rank of Joint Secretary to the Government of India specially authorised in this behalf by an order of the Central Government: Provided that every direction issued under this subsection, shall be reviewed by an Oversight Committee consisting of the Cabinet Secretary and the Secretaries to the Government of India in the Department of Legal Affairs and the Department of Electronics and Information Technology, before it takes effect:
Provided further that any direction issued under this sub-section shall be valid for a period of three months from the date of its issue, which may be extended for a further period of three months after the review by the Oversight Committee.”
344) A close look at sub-section (1) of Section 33 would demonstrate that the sub-section (1) is an exception to Section 28(2), Section 28(5) and Section 29(2) of the Act. Those provisions put a bar on the disclosure of an information thereby protecting the information available with the UIDAI in respect of any person. However, as per sub-section (1), such information can be disclosed if there is an order of a court which order is not inferior to that of a District Judge. This provision, therefore, only states that in suitable cases, if court passes an order directing an Authority to disclose such an information, then the Authority would be obliged to do so.
Thus, an embargo contained in Sections 28 and 29 is partially lifted only in the eventuality on passing an order by the court not inferior to that of District Judge. This itself is a reasonable safeguard. Obviously, in any proceedings where the Court feels such an information is necessary for the determination of controversy that is before the Court, before passing such an order, it would hear the concerned parties which will include the person in respect of whom the disclosure of information is sought. We, therefore, clarify that provisions of sub-section (1) of Section 33 by reading into the provisions that an individual whose information is sought to be released shall be afforded an opportunity of hearing.
There is a reasonable presumption that the said court shall take into consideration relevant law including Article 20(3) of the Constitution as well as privacy rights or other rights of that person before passing such an order. Moreover, a person in respect of whom order is passed shall also be heard and will have right to challenge the order in a higher forum. Not only this, proviso to Section 33(1) puts an additional safeguard by providing that even UIDAI shall be heard before an order is passed to this effect by the Court. In that sense, the Authority is to act as trustee and it may object to passing of the order by the court. Such a happening is actually taken place.
We have already noticed that against the order of the High Court of Bombay in some criminal proceedings, order was passed directing the Authority to give biometric information of a person, the Authority had filed Special Leave Petition (Criminal) No. 2524 of 2014 challenging the said order on the ground that giving of such biometric information was contrary to the provisions of the Aadhaar Act as the information was confidential. This Court stays the operation of the said order which depicts that there are sufficient safeguards provided in sub-section (1) of Section 33 itself.
345) Adverting to sub-section (2) of Section 33, it can be seen that this provision enables disclosure of information including identity information records in the interest of national security. This provision further states that the Authority is obliged to disclose such information in pursuance of a direction of an officer not below the rank of Joint Secretary to the Government of India specially authorised in this behalf by an order of the Central Government. Proviso thereto sub-section (2) puts an additional safeguard by prescribing that every direction issued under this sub-section shall be reviewed by an Oversight Committee consisting of the Cabinet Secretary and the Secretaries to the Government of India in the Department of Legal Affairs and the Department of Electronics and Information Technology before it takes effect. Further, such a direction is valid only for a period of three months from the date of its issue which can be extended by another three months.
346) Main contention of the petitioners in challenging the provisions of sub-section (2) of Section 33 are that no definition of national security is provided and, therefore, it is a loose ended provision susceptible to misuse. It is also argued that there is no independent oversight disclosure of such data on the ground of security and also that the provision is unreasonable and disproportionate and, therefore, unconstitutional.
347) We may point out that this Court has held in Ex-Armymen’s Protection Services Private Limited v. Union of India & Ors.110 that what is in the interest of national security is not a question of law but it is a matter of policy. We would like to reproduce following discussion therefrom: “16. What is in the interest of national security is not a question of law. It is a matter of policy. It is not for the court to decide whether something is in the interest of the State or not. It should be left to the executive. To quote Lord Hoffman in Secy. of State for Home Deptt. v. Rehman [(2003) 1 AC 153 : (2001) 3 WLR 877 : (2002) 1 All ER 122 (HL)] : (AC p. 192C) “… [in the matter] of national security is not a question of law. It is a matter of judgment and policy. Under the Constitution of the United Kingdom and most other countries, decisions as to whether something is or is not in the interests of national security are not a matter for judicial decision. They are entrusted to the executive.”
17. Thus, in a situation of national security, a party cannot insist for the strict observance of the principles of natural justice. In such cases, it is the duty of the court to read into and provide for statutory exclusion, if not expressly provided in the rules governing the field. Depending on the facts of the particular case, it will however be open to the court to satisfy itself whether there were justifiable facts, and in that regard, the court is entitled to call for the files and see whether it is a case where the interest of national security is involved. Once the State is of the stand that the issue involves national security, the court shall not disclose the reasons to the affected party.”
348) Even in K.S. Puttaswamy, this Court has recognised data retention by the Government which may be necessitated in the public interest and in the interest of national security. We may also usefully refer to the judgment of People’s Union for Civil Liberties (PUCL) v. Union of India & Anr.111. In that case, action of telephone tapping was challenged as serious invasion of individual’s privacy. The Court found that Section 5(2) of the Telegraph Act, 1885 permits the interception of messages in circumstances mentioned therein i.e. ‘occurrence of any public emergency’ or ‘in the interest of public safety’. The Court explained these expressions in the following manner:
“28. Section 5(2) of the Act permits the interception of messages in accordance with the provisions of the said section. “Occurrence of any public emergency” or “in the interest of public safety” are the sine qua non for the application of the provisions of Section 5(2) of the Act. Unless a public emergency has occurred or the interest of public safety demands, the authorities have no jurisdiction to exercise the powers under the said section. Public emergency would mean the prevailing of a sudden condition or state of affairs affecting the people at large calling for immediate action. The expression “public safety” means the state or condition of freedom from danger or risk for the people at large.
When either of these two conditions are not in existence, the Central Government or a State Government or the authorised officer cannot resort to telephone-tapping even though there is satisfaction that it is necessary or expedient so to do in the interests of sovereignty and integrity of India etc. In other words, even if the Central Government is satisfied that it is necessary or expedient so to do in the interest of the sovereignty and integrity of India or the security of the State or friendly relations with sovereign States or public order or for preventing incitement to the commission of an offence, it cannot intercept the messages or resort to telephonetapping unless a public emergency has occurred or the interest of public safety or the existence of the interest of public safety requires. Neither the occurrence of public emergency nor the interest of public safety are secretive conditions or situations. Either of the situations would be apparent to a reasonable person.”
349) Having regard to the aforesaid legal position, disclosure of information in the interest of national security cannot be faulted with. However, we are of the opinion that giving of such important power in the hands of Joint Secretary may not be appropriate. There has to be a higher ranking officer along with, preferably, a Judicial Officer. The provisions contained in Section 33(2) of the Act to the extent it gives power to Joint Secretary is, therefore, struck down giving liberty to the respondents to suitably enact a provision on the aforesaid lines, which would adequately protect the interest of individuals.
350) We now advert to the challenge laid to Section 47 of the Aadhaar Act, which is captioned as ‘cognizance of offences’, it reads as under: “47. (1) No court shall take cognizance of any offence punishable under this Act, save on a complaint made by the Authority or any officer or person authorised by it. (2) No court inferior to that of a Chief Metropolitan Magistrate or a Chief Judicial Magistrate shall try any offence punishable under this Act.”
351) Certain acts in Chapter VII are treated as offences and penalties are also provided, from Section 34 to Section 43.
352) Section 44 clarifies that this Act would apply for offence or contravention committed even outside India. Insofar as investigation of these offences is concerned, Section 45 provides that a police officer not below the rank of Inspector of Police shall investigate any offence under this Act. Section 46, thereafter, clarifies that penalties imposed under this Act shall not prevent the imposition of any other penalty or punishment under any other law for the time being in force. This scheme of Chapter VII makes very strict provisions in respect of enforcement of the Act which includes data protection as well.
Last provision in Chapter VII is Section 47 which provides that the cognizance would be taken only on a complaint made by the Authority or any officer or person authorised by it. Petitioners feel aggrieved by this provision as it does not permit an individual citizen whose rights are violated, to initiate the criminal process. Apprehensions are expressed by submitting that there may be a possibility where the Authority itself or some Governmental Authority may be guilty of committing the offences under the Act and, in such a situation, the Authority or any officer or person authorised by it may choose not to file any complaint.
353) According to the respondents, the rationale behind Section 47 is to maintain purity and integrity of CIDR and the entire enrolment storage in the CIDR and authentication exercise can be handled only by the Authority. For this reason, it is the Authority which is empowered to lodge the complaint. It is also pointed out that similar provisions akin to Section 47 of the Aadhaar Act are contained in many other statutes.
Reference is made to Section 22 of the Mines and Minerals (Development and Regulation) Act, 1957, Section 34 of the Bureau of Indian Standards Act, 1986, Section 34 of the Telecom Regulatory Authority of India Act, 1997, Section 47 of the Banking Regulation Act, 1949, Section 26(1) of the Securities and Exchange Board of India Act, 1992, Section 19 of the Environment (Protection) Act, 1986, Section 43 of the Air (Prevention and Control of Pollution) Act, 1981 and Section 57(1) of the Petroleum and Natural Gas Regulatory Board Act, 2006. The respondents have also submitted that validity of such provisions have been tested and affirmed by this Court. Reference is made to the judgment in Raj Kumar Gupta v. Lt. Governor, Delhi & Ors.112.
The respondents have also taken support of the decision of this Court in State (NCT of Delhi) v. Sanjay113 wherein Section 22 of the Mines and Minerals (Development and Regulation) Act, 1957 was tested. Insofar as grievance and apprehension of the petitioners is concerned, it can be taken care on interpreting the provisions by holding that the Authority can lodge a complaint of its own motion or at the request of the individual whose rights are affected thereby. Notwithstanding the above, we are of the opinion that it would be in the fitness of things if Section 47 is amended by allowing individual/victim whose right is violated, to file a complaint and initiate the proceedings.
We hope that this aspect shall be addressed at the appropriate level and if considered fit, Section 47 would be suitably amended.
354) Section 48 cannot be treated as vague or arbitrary. ‘Public Emergency’ is the expression which has been used in several other enactments and held to be constitutional. It can always be subject to scrutiny of the Courts.
355) With this, now we come to a provision which was highly debated. At the time of arguments, the petitioners had taken strong exception to some of its aspects. We may first take note of the exact language of this provision:
“57. Nothing contained in this Act shall prevent the use of Aadhaar number for establishing the identity of an individual for any purpose, whether by the State or any body corporate or person, pursuant to any law, for the time being in force, or any contract to this effect: Provided that the use of Aadhaar number under this section shall be subject to the procedure and obligations under section 8 and Chapter VI.”
356) In first blush, the provision appears to be innocuous. It enables Aadhaar holder to establish her identity for any purpose as well. In that sense, it may amount to empowering the Aadhaar number holder, when she is carrying unique identity. It is her identity card which she is able to use not only for the purposes mentioned in the Aadhaar Act but also for any other purpose.
357) The petitioners, however, have pricked the provision with the submission that it may be susceptible to making deep in-roads in the privacy of individuals and is utterly disproportionate. The taint in the provision, as projected by the petitioners, is that it brings in private parties as well, apart from the State within the fold of Aadhaar network giving untrammeled opportunity to them to invade the privacy of such user. The offending portion of the provision, according to them, is that:
(a) It allows ‘any body corporate or person’ (thereby encompassing private bodies/persons as well) to make use of authentication process, once an individual offers Aadhaar for establishing her identity.
(b) The expression ‘for any purpose’ is wide enough, which may be susceptible to misuse.
(c) This is permitted not only pursuant to any law for time being in force but also pursuant to ‘any contract to this effect’ which would mean that individuals may be forced to give their consent in the form of contract for a purpose that may be justified or not thereby permitting the private parties to collect biometric information about the said individual.
358) It is argued that there are no procedural safeguards governing the actions of the private entities. Equally no remedy is provided in case such body corporate or person fails or denies services. In this hue, it is also argued that it is an excessive piece of legislation inasmuch as taking the umbrage of ‘any law’, the regulations etc. can be framed by including within its fold much more than what is provided by Section 7 of the Aadhaar Act. It, therefore, according to the petitioners, does not meet the test of proportionality. Mr. Divan submits that Section 57 is also patently unconstitutional inasmuch as it allows an unrestricted extension of the Aadhaar platform to users who may be government agencies or private sector operators. Moreover, this provision enables the seeding of the Aadhaar number across service providers and other gateways and thereby enables the establishment of a surveillance state. The impugned provision enables the spread of applications and Aadhaar dependent delivery systems that are provided not from Consolidated Fund of India resources but through any other means. He also submits that section 57 also enables commercial exploitation of an individual’s biometrics and demographic information by the Respondents as well as private entities.
359) As mentioned above, the respondents contend that it is only an enabling provision which gives further facilities to Aadhaar card holder, as per her choice and is, thus, enacted for the benefit of such individuals.
360) We have already discussed in detail the principles on which doctrine of proportionality is built upon and the test which need to be satisfied. To put in nutshell, the proportionality principles seek to safeguard citizens from excessive Government measures. The inquiry, in such cases, is that a particular measure must not be disproportionate in two distinctive utilitarian senses:
(i) The cost or burdens of the measure must not clearly exceed the likely benefits, which can be described as ‘ends’ or ‘ends-benefits’ proportionality.
(ii) The measure must not be clearly more costly or more burdensome than equally alternative measures, which is also described by some jurists as a concept of necessity and narrow tailoring and can be referred to as ‘means’ or ‘alternative-means’ proportionality.
361) We have also discussed in detail the principle of proportionality that is developed in certain foreign legal regimes, particularly Germany and Canada. The Supreme Court of Canada in R. v. Oakes114 developed a two-tier constitutional control test. Once the claimant has proved a violation of a right guaranteed in the charter, the government must satisfy two criteria to establish that the limit on individual rights “can be demonstrably justified in a free and democratic society.”
362) First, measures limiting a constitutionally protected right must serve an important objective that “relate[s] to concerns which are pressing and substantial in a free and democratic society.” Legislation limiting the rights of English-speaking parents in Quebec to educate their children in English-speaking schools115 has been found lacking an important public objective. Likewise, the Supreme Court of Canada was unable to find any legitimate public objective that justified denying protection to gays and lesbians under Alberta’s human rights law in Vriend v. Alberta116. In R. v. Zundel117, it also prohibited an intrusive use of a law that was unrelated to the objectives originally contemplated by the Parliament when that law was enacted.
363) Secondly, once an important public objective or end has been established, the selected means to attain it must be “reasonable and demonstrably justified.” The Court said in R. v. Big M Drug Mart Ltd.118 that this determination involves “a form of proportionality test”. Although, it varies depending on the facts of the case, the test involves the balancing of public and individual interests based on three principles, which are as follows:
(i) the means must be rationally related to the objective. The court has infrequently struck down legislation for lack of any rational relation to the objective pursued. It employs a rather deferential and contextual approach to determine the rational relation of a provision to the desired end.
(ii) The means should “impair ‘as little as possible’ the right or freedom in question.” This is believe to be the decisive element of proportionality review. It requires that the legislature adopt the least intrusive measure capable of attaining the desired objective.
(iii) The public objective and actual effects of the means adopted for its attainment must be proportionate to an important public end or objective. The court noted that even if the means satisfies the first two criteria, it may be declared unconstitutional in view of its disproportionate harmful effects on an individual. 364) Insofar as development of law in Germany is concerned, as already discussed in detail, proportionality is defined “as an expression of general right of the citizen towards the State that his freedom should be limited by the public authorities only to the extent indispensable for the protection of the public interest.”
119 The principle of proportionality in German law incorporates three important subprinciples: suitability, necessity, and proportionality in the narrower sense. According to the High Court of Germany, any government interference with basic rights must be suitable and necessary for reaching the ends sought. Its disadvantages to individuals “are generally only permissible if the protection of others or of the public interest requires them, after having due regard to the principle of proportionality.”
365) The European Union has, by and large, adopted the German system. We have also taken note of the development of doctrine of proportionality in India through various judgments120.
366) We may mention here that insofar as U.S. Supreme Court is concerned, it has refused to apply the least intrusive test121 Though there was a debate at the bar as to whether this Court should adopt European approach of applying least intrusive test or go by American approach which repeatedly refused to apply this test. Without going into this debate, even when we apply the accepted norms laid down by this Court in Modern Dental College and Research Centre and K.S. Puttaswamy cases, we are of the view that a part of Section 57 does not pass the muster of proportionality doctrine.
367) The respondents may be right in their explanation that it is only an enabling provision which entitles Aadhaar number holder to take the help of Aadhaar for the purpose of establishing his/her identity. If such a person voluntary wants to offer Aadhaar card as a proof of his/her identity, there may not be a problem.
368) Section 59, which is the last provision in the Act is aimed at validating actions taken by the Central Government pursuant to notification dated January 28, 2009 till the passing of the Act.
It reads as under:
“59. Anything done or any action taken by the Central Government under the Resolution of the Government of India, Planning Commission bearing notification number A- 43011/02/2009-Admin. I, dated the 28th January, 2009, or by the Department of Electronics and Information Technology under the Cabinet Secretariat Notification bearing notification number S.O. 2492(E), dated the 12th September, 2015, as the case may be, shall be deemed to have been validly done or taken under this Act.”
369) The challenge to this provision is on the premise that in the regime which prevailed prior to the passing of the Act and the enrolments into Aadhaar scheme were done, that happened without the consent of the persons who sought enrolment and, therefore, those enrolments cannot be validated by making such a provision. It was argued that even the Act makes provisions for informed consent which is to be obtained from individuals at the time of enrolment and absence of such consent makes the very enrolment as impermissible thereby violating the right to privacy and such acts cannot be validated.
370) The contention of the respondents, on the other hand, is that by the very nature of the provision, it is intended to be prospective in nature with a clear purport in mind, namely, to validate the notification dated August 21, 2009 vide which the Authority was created and the Aadhaar scheme was launched by administrative fiat. The purpose is to give it a statutory backing.
371) We find that Section 59 uses the expression ‘anything done or any action under the resolution’. According to us, this terminology used in the provision by the legislature is clearly to cover all actions of the Authority including enrolment of individuals into Aadhaar scheme. The words ‘shall be deemed to have been validly done or taken under this Act’ at the end of the Section put the things beyond any pale of doubt. The legislative intent is clear, namely, to make the provision retrospective so as to cover the actions of the Authority from the date of its establishment. Reading the provision in the manner the petitioners suggest would have the effect of annulling Section 59 itself. Such an interpretation cannot be countenanced.
We are of the opinion that case is squarely covered by the Constitution Bench judgment of this Court in West Ramnad Electric Distribution Co., Ltd. v. State of Madras & Anr.122as well as Bishambhar Nath Kohli & Ors. v. State of Uttar Pradesh & Ors.123.
372) We would also like to point out that the submission of the petitioners that a particular action or a provision or statute which is hit by Article 14 cannot be allowed to be validated is repelled by this Court in State of Mysore & Anr. v. D. Achiah Chetty, Etc.124. The legislature is, thus, empowered to incorporate deeming provisions in a statute. This proposition has also been repeatedly affirmed by this Court. We may refer in this behalf the decision in State of Karnataka v. State of Tamil Nadu & Ors.125 will be of relevance wherein the Court held as under:
“72. The second limb of submission of Mr Rohatgi as regards the maintainability pertains to the language employed under Section 6(2) of the 1956 Act, which reads as follows:
“6. (2) The decision of the Tribunal, after its publication in the Official Gazette by the Central Government under sub-section (1), shall have the same force as an order or decree of the Supreme Court.” 73. Relying on Section 6(2), which was introduced by way of the Amendment Act, 2002 (Act 14 of 2002) that came into force from 6-8-2002, it is submitted by Mr Rohatgi that the jurisdiction of this Court is ousted as it cannot sit over in appeal on its own decree.
The said submission is seriously resisted by Mr Nariman and Mr Naphade, learned Senior Counsel contending that the said provision, if it is to be interpreted to exclude the jurisdiction of the Supreme Court of India, it has to be supported by a constitutional amendment adding at the end of Article 136(2) the words “or to any determination of any tribunal constituted under the law made by Parliament under Article 262(2)” and, in such a situation, in all possibility such an amendment to the Constitution may be ultra vires affecting the power of judicial review which is a part of basic feature of the Constitution.
The learned Senior Counsel for the respondent has drawn a distinction between the conferment and the exclusion of the power of the Supreme Court of India by the original Constitution and any exclusion by the constitutional amendment. Be that as it may, the said aspect need not be adverted to, as we are only required to interpret Section 6(2) as it exists today on the statute book. The said provision has been inserted to provide teeth to the decision of the Tribunal after its publication in the Official Gazette by the Central Government and this has been done keeping in view the Sarkaria Commission’s Report on Centre-State Relations (1980). The relevant extract of the Sarkaria Commission’s Report reads as follows:
“17.4.19. The Act was amended in 1980 and Section 6-A was inserted. This section provides for framing a scheme for giving effect to a Tribunal’s award. The scheme, inter alia provides for the establishment of the authority, its term of office and other conditions of service, etc. But the mere creation of such an agency will not be able to ensure implementation of a Tribunal’s award. Any agency set up under Section 6- A cannot really function without the cooperation of the States concerned. Further, to make a Tribunal’s award binding and effectively enforceable, it should have the same force and sanction behind it as an order or decree of the Supreme Court. We recommend that the Act should be suitably amended for this purpose. ***
17.6.05. The Inter-State Water Disputes Act, 1956 should be amended so that a Tribunal’s award has the same force and sanction behind it as an order or decree of the Supreme Court to make a Tribunal’s award really binding.”
74. The Report of the Commission as the language would suggest, was to make the final decision of the Tribunal binding on both the States and once it is treated as a decree of this Court, then it has the binding effect. It was suggested to make the award effectively enforceable. The language employed in Section 6(2) suggests that the decision of the Tribunal shall have the same force as the order or decree of this Court. There is a distinction between having the same force as an order or decree of this Court and passing of a decree by this Court after due adjudication.
Parliament has intentionally used the words from which it can be construed that a legal fiction is meant to serve the purpose for which the fiction has been created and not intended to travel beyond it. The purpose is to have the binding effect of the Tribunal’s award and the effectiveness of enforceability. Thus, it has to be narrowly construed regard being had to the purpose it is meant to serve.
75. In this context, we may usefully refer to the Principles of Statutory Interpretation, 14th Edn. by G.P. Singh. The learned author has expressed thus: “In interpreting a provision creating a legal fiction, the court is to ascertain for what purpose the fiction is created [State of Travancore-Cochin v. Shanmugha Vilas Cashewnut Factory, AIR 1953 SC 333; State of Bombay v. Pandurang Vinayak, AIR 1953 SC 244 : 1953 Cri LJ 1094] , and after ascertaining this, the Court is to assume all those facts and consequences which are incidental or inevitable corollaries to the giving effect to the fiction. [East End Dwellings Co. Ltd.v. Finsbury Borough Council, 1952 AC 109 : (1951) 2 All ER 587 (HL); CIT v. S. Teja Singh, AIR 1959 SC 352] But in so construing the fiction it is not to be extended beyond the purpose for which it is created [Bengal Immunity Co. Ltd. v. State of Bihar, AIR 1955 SC 661; CIT v. Amarchand N. Shroff, AIR 1963 SC 1448], or beyond the language of the section by which it is created. [CIT v. Shakuntala, AIR 1966 SC 719; Mancheri Puthusseri Ahmed v. Kuthiravattam Estate Receiver, (1996) 6 SCC 185 : AIR 1997 SC 208]
It cannot also be extended by importing another fiction. [CIT v. Moon Mills Ltd., AIR 1966 SC 870] The principles stated above are ‘wellsettled’. [State of W.B. v. Sadan K. Bormal, (2004) 6 SCC 59 : 2004 SCC (Cri) 1739 : AIR 2004 SC 3666] A legal fiction may also be interpreted narrowly to make the statute workable. [Nandkishore Ganesh Joshi v. Commr., Municipal Corpn. of Kalyan and Dombivali, (2004) 11 SCC 417 : AIR 2005 SC 34] ” 76. In Aneeta Hada v. Godfather Travels and Tours [Aneeta Hada v. Godfather Travels and Tours, (2012) 5 SCC 661 : (2012) 3 SCC (Civ) 350 : (2012) 3 SCC (Cri) 241] , a three-Judge Bench has ruled thus: (SCC p. 681, paras 37-38)
“37. In State of T.N. v. Arooran Sugars Ltd. [State of T.N. v. Arooran Sugars Ltd., (1997) 1 SCC 326] the Constitution Bench, while dealing with the deeming provision in a statute, ruled that the role of a provision in a statute creating legal fiction is well settled. Reference was made to Chief Inspector of Mines v. Karam Chand Thapar [Chief Inspector of Mines v. Karam Chand Thapar, AIR 1961 SC 838 : (1961) 2 Cri LJ 1], J.K. Cotton Spg. and Wvg. Mills Ltd. v. Union of India[J.K. Cotton Spg. and Wvg. Mills Ltd. v. Union of India, 1987 Supp SCC 350 : 1988 SCC (Tax) 26], M. Venugopal v. LIC [M. Venugopal v. LIC, (1994) 2 SCC 323 : 1994 SCC (L & S) 664] and Harish Tandon v. ADM, Allahabad [Harish Tandon v. ADM, Allahabad, (1995) 1 SCC 537] and eventually, it was held that when a statute creates a legal fiction saying that something shall be deemed to have been done which in fact and truth has not been done, the Court has to examine and ascertain as to for what purpose and between which persons such a statutory fiction is to be resorted to and thereafter, the courts have to give full effect to such a statutory fiction and it has to be carried to its logical conclusion.
38. From the aforesaid pronouncements, the principle that can be culled out is that it is the bounden duty of the court to ascertain for what purpose the legal fiction has been created. It is also the duty of the court to imagine the fiction with all real consequences and instances unless prohibited from doing so. That apart, the use of the term “deemed” has to be read in its context and further, the fullest logical purpose and import are to be understood. It is because in modern legislation, the term “deemed” has been used for manifold purposes. The object of the legislature has to be kept in mind.”
77. In Hari Ram [State of U.P. v. Hari Ram, (2013) 4 SCC 280 : (2013) 2 SCC (Civ) 583] , the Court has held that (SCC p. 293, para 18) in interpreting the provision creating a legal fiction, the court is to ascertain for what purpose the fiction is created and after ascertaining the same, the court is to assume all those facts and consequences which are incidental or inevitable corollaries for giving effect to the fiction.”
373) There is yet another angle from which the matter can be looked into. In any case, when the Aadhaar scheme/project under the Act has been saved from the challenge to its constitutionality, we see no reason to invalidate the enrolments which were made prior to the passing of this Act as it would lead to unnecessary burden and exercise of enrolling these persons all over again. Instead the problem can be solved by eliciting ‘consent’ of all those persons who were enrolled prior to the passing of the Act. Since, we have held that enrolment is voluntary in nature, those who specifically refuse to give the consent, they would be allowed to exit from Aadhaar scheme. After all, by getting Aadhaar card, an individual so enrolled is getting a form of identity card.
It would still be open to such an individual to make use of the said Aadhaar number or not. Those persons who need to avail any subsidy, benefit or service would need Aadhaar in any case. It would not be proper to cancel their Aadhaar cards. If direction is given to invalidate all those enrolments which were made prior to 2016 then such persons will have to undergo the rigours of getting themselves enrolled all over again. On the other hand, those who do not get any benefit of the nature prescribed under Section 7 of the Act, it would always be open for them not to make use of Aadhaar card or to make use of this card in a limited sense, namely, showing it as a proof of their identity, without undergoing any authentication process. Therefore, to a large extent, it does not harm this later category as well. We, thus, uphold the validity of Section 59. As a corollary, Aadhaar for the period from 2009 to 2016 also stands validated.
LIMITED GOVERNMENT, GOOD GOVERNANCE, CONSTITUTIONAL TRUST AND CONSTITUTIONALISM
374) Mr. Shyam Divan and Mr. Gopal Subramanium, learned senior counsel, submit that a fundamental feature of the Constitution is the sovereignty of the people with limited government authority. The Constitution limits governmental authority in various ways, amongst them Fundamental Rights, the distribution of powers amongst organs of the state and the ultimate check by way of judicial review. Article 245 of the Constitution of India is an express embodiment of the principle of limited government to the legislature inasmuch as it subjects laws to the Constitution:
“(1) Subject to the provisions of this Constitution, Parliament may make laws for the whole or any part of the territory of India, and the Legislature of a State may make laws for the whole or any part of the State.”
375) The concept of limited government is the underlying difference between a ‘Constitution’ and ‘Constitutionalism’. Mr. Shyam Divan refers to the introductory chapter of his book Indian Constitutional Law, Prof. M.P. Jain writes: “Modern political thought draws a distinction between ‘Constitutionalism’ and ‘Constitution’. A country may have the ‘Constitution’ but not necessary ‘Constitutionalism’.
For example, a country with a dictatorship, where the dictator’s word is law, can be said to have a ‘Constitution’ but not ‘Constitutionalism’. The underlying difference between the two concepts is that a Constitution ought not merely to confer powers on the various organs of the government, but also seek to restrain those powers. Constitutionalism recognises the need for government but insists upon limitations being placed upon governmental powers. Constitutionalism envisages checks and balances and putting the powers of the legislature and the executive under some restraints and not making them uncontrolled and arbitrary. Unlimited powers jeopardise freedom of the people … If the Constitution confers unrestrained power on either the legislature or the executive, it might lead to an authoritarian, oppressive government… to preserve the basic freedoms of the individual, and to maintain his dignity and personality, the Constitution should be permeated with ‘Constitutionalism’: it should have some in-built restrictions on the powers conferred by it on governmental organs. ‘Constitutionalism’ connotes in essence limited government or a limitation on government. Constitutionalism is the antithesis of arbitrary powers… … As PROFESSOR VILE has remarked:
“Western institutional theorists have concerned themselves with the problems of ensuring that the exercise of governmental power…should be controlled in order that it should not itself be destructive of the values it was intended to promote.”
376) Mr. Divan then cited various paragraphs from the cases of State of M.P. v. Thakur Bharat Singh126, (1967) 2 SCR 454, Gobind v. State of M.P.127, S.P. Sampath Kumar v. Union of India128, Sub- Committee on Judicial Accountability v. Union of India129, I.R. Coelho v. State of T.N.130, Nandini Sundar v. State of Chhattisgarh131, which have reiterated and upheld the principle of limited governments and constitutionalism as a fundamental principle of our constitutional scheme.
377) He submitted that limited government is also enshrined within our Preamble, which is the essence of the Constitution of India, and entitles every individual citizen and the citizenry collectively to live, work, and enjoy their varied lives without being under the continuous gaze of the State. He cites Chelameswar, J. in K.S. Puttaswamy wherein he observed:
“The Constitution of any country reflects the aspirations and goals of the people of that country (…) The Constitution cannot be seen as a document written in ink to replace one legal regime by another. It is a testament created for securing the goals professed in the Preamble. Part-III of the Constitution is incorporated to ensure achievement of the objects contained in the Preamble. ‘We the People’ of this country are the intended beneficiaries of the Constitution. Man is not a creature of the State. Life and liberty are not granted by the Constitution. Constitution only stipulates the limitations on the power of the State to interfere with our life and liberty.
Law is essential to enjoy the fruits of liberty; it is not the source of liberty and emphatically not the exclusive source.”
378) The Directive Principles of State Policy also envisage a limited government. Violation of fundamental rights cannot be justified by the State on grounds of administrative convenience in meeting its obligations under the Directive Principles of State Policy. Protection of fundamental rights is essential for public welfare contemplated under the Directive Principles of State Policy. This has been upheld in various cases such as Minerva Mills Ltd. v. Union of India132, where Y.V. Chandrachud, C.J observed:
“57. (…) just as the rights conferred by Part III would be without a radar and a compass if they were not geared to an ideal, in the same manner the attainment of the ideals set out in Part IV would become a pretence for tyranny if the price to be paid for achieving that ideal is human freedoms.”
379) Similarly, in Kesavananda Bharati v. State of Kerala133, S.M. Sikri, C.J., inter alia, held: “209. …In my view that meaning would be appropriate which would enable the country to achieve a social and economic revolution without destroying the democratic structure of the Constitution and the basic inalienable rights guaranteed in Part III and without going outside the contours delineated in the Preamble.
xx xx xx
299. I am unable to hold that these provisions show that some rights are not natural or inalienable rights. As a matter of fact, India was a party to the Universal Declaration of Rights which I have already referred to and that Declaration describes some fundamental rights as inalienable. Various decisions of this Court describe fundamental rights as ‘natural rights’ or ‘human rights’ …”
380) Mr. Divan quotes Seervai in his book Constitutional Law of India134: A Critical Commentary where he writes:
“17.14… In India “Public Welfare” and “Welfare State” became in the language of the Chaldean Oracle, “Godgiven names of unexplained power”, which absolved judges from a critical examination of the nature of fundamental rights, and why they were made legally enforceable and the nature of directive principles and why they were made legally unenforceable
xx xx xx
17.20…it is simply not true that persons entrusted with the duty of implementing the directives will strive in good faith to implement them according to the expectations of the community.
xx xx xx
The question then arises: What is the agency for bringing about social and economic changes which would enable a welfare state to be created? The answer is, legislative and executive power controlled by constitutional limitations including fundamental rights …
xx xx xx
17.30 … the conferment of legally enforceable fundamental rights by our Constitution on persons, citizens and groups of persons was the most effective way of securing public welfare…Anything which enables those objectives to be realised as fully as is practicable must, broadly speaking, subserve public welfare…However, the Preamble, and to a large extent, Fundamental Rights, enable us to say that our Constitution has rejected a totalitarian form of government in favour of a liberal democracy. The emphasis of the Preamble is on securing the dignity of the individual …
xx xx xx
17.34 But can fundamental rights acting as limitations on legislative and executive power secure public welfare as the framers of our Constitution intended? The answer is “Yes”. For, when during the Emergency of 1975-77, almost all the fetters on legislative power became unenforceable, the public welfare suffered gravely and our free democratic constitution was twisted out of shape and came near to a dictatorship or a Police State …”
381) The principles of constitutional trust, constitutional morality and good governance are also deeply intertwined with the principle of minimum government. In Manoj Narula v. Union of India135, the Court, inter alia, held:
“1. … Democracy, which has been best defined as the government of the people, by the people and for the people, expects prevalence of genuine orderliness, positive propriety, dedicated discipline and sanguine sanctity by constant affirmance of constitutional morality which is the pillar stone of good governance.
xx xx xx
75. The principle of constitutional morality basically means to bow down to the norms of the Constitution and not to act in a manner which would become violative of the rule of law or reflectible of action in an arbitrary manner. It actually works at the fulcrum and guides as a laser beam in institution building. The traditions and conventions have to grow to sustain the value of such a morality. The democratic values survive and become successful where the people at large and the persons in charge of the institution are strictly guided by the constitutional parameters without paving the path of deviancy and reflecting in action the primary concern to maintain institutional integrity and the requisite constitutional restraints. Commitment to the Constitution is a facet of constitutional morality.”
xx xx xx
82. In a democracy, the citizens legitimately expect that the Government of the day would treat the public interest as the primary one and any other interest secondary. The maxim salus populi suprema lex, has not only to be kept in view but also has to be revered. The faith of the people is embedded in the root of the idea of good governance which means reverence for citizenry rights, respect for fundamental rights and statutory rights in any governmental action, deference for unwritten constitutional values, veneration for institutional integrity, and inculcation of accountability to the collective at large. It also conveys that the decisions are taken by the decision-making authority with solemn sincerity and policies are framed keeping in view the welfare of the people, and including all in a homogeneous compartment.
The concept of good governance is not a Utopian conception or an abstraction. It has been the demand of the polity wherever democracy is nourished. The growth of democracy is dependent upon good governance in reality and the aspiration of the people basically is that the administration is carried out by people with responsibility with service orientation.
83. … The issue of constitutional trust arises in the context of the debate in the Constituent Assembly that had taken place pertaining to the recommendation for appointment of a Minister to the Council of Ministers. Responding to the proposal for the amendment suggested by Prof. K.T. Shah with regard to the introduction of a disqualification of a convicted person becoming a Minister, Dr B.R. Ambedkar had replied: (CAD Vol. VII, p. 1160) “His last proposition is that no person who is convicted may be appointed a Minister of the State.
Well, so far as his intention is concerned, it is no doubt very laudable and I do not think any Member of this House would like to differ from him on that proposition. But the whole question is this: whether we should introduce all these qualifications and disqualifications in the Constitution itself. Is it not desirable, is it not sufficient that we should trust the Prime Minister, the legislature and the public at large watching the actions of the Ministers and the actions of the legislature to see that no such infamous thing is done by either of them?I think this is a case which may eminently be left to the good sense of the Prime Minister and to the good sense of the legislature with the general public holding a watching brief upon them. I therefore say that these amendments are unnecessary.”
382) It is submitted by Mr. Divan that the Aadhaar project is destructive of limited government, constitutionalism and constitutional trust. The Constitution is not about the power of the State, but about the limits on the power of the State. Post Aadhaar, the State will completely dominate the citizen and alter the relationship between citizen and State. The features of a Totalitarian State is seen from:
(a) A person cannot conduct routine activities such as operating a bank account, holding an investment in mutual funds, receiving government pension, receiving scholarship, receiving food rations, operating a mobile phone without the State knowing about these activities.(Sections 7, 32 and 57 of the Aadhaar Act).
(b) The State can build a profile of the individual based on the trail of authentication from which the nature of the citizen’s activity can be determined. (Sections 2(d) and 32 of the Aadhaar Act and Regulation 20, 26 and 27 of the Aadhaar (Authentication) Regulation, 2016.
(c) By disabling Aadhaar the State can cause the civil death of the person.(Sections 23(2)(g) of the Aadhaar Act and Regulation 27 and 28 of the Aadhaar (Enrolment and Updates) Act, 2016).
(d) By making Aadhaar compulsory for other activities such as air travel, rail travel, directorship in companies, services and benefits extended by State governments and municipal corporations etc. there will be virtually no zone of activity left where the citizen is not under the gaze of the State. This will have a chilling effect on the citizen.
(e) In such a society, there is little or no personal autonomy. The State is pervasive, and dignity of the individual stands extinguished.
(f) This is an inversion of the accountability in the Right to Information age: instead of the State being transparent to the citizen, it is the citizen who is rendered transparent to the State.
383) Mr. Sibal also added that accountability of governments and the state is a phenomenon which is accepted across the world. In furtherance of the Right to information Act, 2005 was passed intended to ensure transparency and state accountability. Through Aadhaar, on the other hand, the state seeks transparency and accountability of an individual’s multifarious activities in the course of his everyday life. This fundamentally alters the relationship between the citizen and the State and skews the balance of power in favour of the State, which is anathema to the Constitution.
384) There is no dispute about the exposition of the principles of limited government and good governance, etc., as highlighted by the learned counsel for the petitioners and noted above. We may add that we are the Republic and it becomes the duty of the Court to keep it. That can be achieved by asking the stakeholders to follow the Constitution, which we have. There are six key constitutional notions, a brilliant exposition whereof has been provided in the case of Manoj Narula v. Union of India136. The idea of constitutional renaissance was first sounded in the said judgment. It is further elaborated in the case of Government of NCT of Delhi v. Union of India137 in the opinion penned down by one of us138.
It stands severally described now as “a constant awakening as regards the text, context, perspective, purpose, and the rule of law”, an awakening that makes space for a “resurgent constitutionalism” and “allows no room for absolutism” nor any “space for anarchy”. It is held, therein the term “rational anarchism” has “no entry in the field of constitutional governance or the rule of law” and by the same token constitutional text and context resolutely repudiate the lineages of absolutism or the itineraries of dictatorship.
One may then say that “constitutionalism” is the space between “absolutism” and “anarchy” and its constant repair and renewal is the prime function of adjudication.
385) In an illuminating Article titled ‘A Constitutional Renaissance’ on the aforesaid verdict authored by Prof. Upendra Baxi139, the learned Professor has made following pertinent comments: “Awakening is a constant process; renaissance has a beginning but knows no end because everyday fidelity to the vision, spirit and letter of the Constitution is the supreme obligation of all constitutional beings.
One ought to witness in daily decisions an “acceptance of constitutional obligations” not just within the text of the Constitution but also its “silences”. To thus reawaken is to be “obeisant to the constitutional conscience with a sense of constitutional vision”. Second, courts should adopt that approach to interpretation which “glorifies the democratic spirit of the Constitution”. “Reverence” for the Constitution (or constitutionalism) is the essential first step towards constitutional renaissance. Third, people are the true sovereigns, never to be reduced to the servile status of being a subject; rather as beings with rights, they are the source of trust in governance and founts of legitimacy. The relatively autonomous legislative, executive, administrative and adjudicatory powers are legitimate only when placed at the service of constitutional ends. All forms of public power are held in trust. And political power is not an end but a means to constitutional governance.”
386) Since the arguments on limited government advanced by Mr. Shyam Divan were the same as advanced by him during the hearing of Binoy Viswam, our purpose would be served by reproducing the following discussion from the said judgment: “85. There cannot be any dispute about the manner in which Mr Shyam Divan explained the concept of “limited Government” in his submissions. Undoubtedly, the Constitution of India, as an instrument of governance of the State, delineates the functions and powers of each wing of the State, namely, the Legislature, the Judiciary and the Executive. It also enshrines the principle of separation of powers which mandates that each wing of the State has to function within its own domain and no wing of the State is entitled to trample over the function assigned to the other wing of the State.
This fundamental document of governance also contains principle of federalism wherein the Union is assigned certain powers and likewise powers of the State are also prescribed. In this context, the Union Legislature i.e. Parliament, as well as the State Legislatures are given specific areas in respect of which they have power to legislate. That is so stipulated in Schedule VII to the Constitution wherein List I enumerates the subjects over which Parliament has the dominion, List II spells out those areas where the State Legislatures have the power to make laws while List III is the Concurrent List which is accessible both to the Union as well as the State Governments.
The scheme pertaining to making laws by Parliament as well as by the legislatures of the State is primarily contained in Articles 245 to 254 of the Constitution. Therefore, it cannot be disputed that each wing of the State has to act within the sphere delineated for it under the Constitution. It is correct that crossing these limits would render the action of the State ultra vires the Constitution. When it comes to power of taxation, undoubtedly, power to tax is treated as sovereign power of any State. However, there are constitutional limitations briefly described above. 86. In a nine Judge Bench decision of this Court in Jindal Stainless Ltd. & Anr. v. State of Haryana & Ors. discussion on these constitutional limitations are as follows:
“20. Exercise of sovereign power is, however, subject to Constitutional limitations especially in a federal system like ours where the States also to the extent permissible exercise the power to make laws including laws that levy taxes, duties and fees. That the power to levy taxes is subject to constitutional limitations is no longer res-integra. A Constitution Bench of this Court has in Synthetics and Chemicals Ltd. v. State of U.P. (1990) 1 SCC 109 recognised that in India the Centre and the States both enjoy the exercise of sovereign power, to the extent the Constitution confers upon them that power. This Court declared:
“56 … We would not like, however, to embark upon any theory of police power because the Indian Constitution does not recognise police power as such. But we must recognise the exercise of Sovereign power which gives the State sufficient authority to enact any law subject to the limitations of the Constitution to discharge its functions. Hence, the Indian Constitution as a sovereign State has power to legislate on all branches except to the limitation as to the division of powers between the Centre and the States and also subject to the fundamental rights guaranteed under the Constitution.
The Indian States, between the Centre and the States, has sovereign power. The sovereign power is plenary and inherent in every sovereign State to do all things which promote the health, peace, morals, education and good order of the people. Sovereignty is difficult to define. This power of sovereignty is, however, subject to constitutional limitations.”This power, according to some constitutional authorities, is to the public what necessity is to the individual. Right to tax or levy impost must be in accordance with the provisions of the Constitution.”
21. What then are the Constitutional limitations on the power of the State legislatures to levy taxes or for that matter enact legislations in the field reserved for them under the relevant entries of List II and III of the Seventh Schedule. The first and the foremost of these limitations appears in Article 13 of the Constitution of India which declares that all laws in force in the territory of India immediately before the commencement of the Constitution are void to the extent they are inconsistent with the provisions of Part III dealing with the fundamental rights guaranteed to the citizens. It forbids the States from making any law which takes away or abridges, any provision of Part III. Any law made in contravention of the said rights shall to the extent of contravention be void. There is no gain saying that the power to enact laws has been conferred upon the Parliament subject to the above Constitutional limitation. So also in terms of Article 248, the residuary power to impose a tax not otherwise mentioned in the Concurrent List or the State List has been vested in the Parliament to the exclusion of the State legislatures, and the States’ power to levy taxes limited to what is specifically reserved in their favour and no more.
22. Article 249 similarly empowers the Parliament to legislate with respect to a matter in the State List for national interest provided the Council of States has declared by a resolution supported by not less than two-thirds of the members present and voting that it is necessary or expedient in national interest to do so. The power is available till such time any resolution remains in force in terms of Article 249(2) and the proviso thereunder.
23. Article 250 is yet another provision which empowers the Parliament to legislate with respect to any matter in the State List when there is a proclamation of emergency. In the event of an inconsistency between laws made by Parliament under Articles 249 and 250, and laws made by legislature of the States, the law made by Parliament shall, to the extent of the inconsistency, prevail over the law made by the State in terms of Article 251.
24. The power of Parliament to legislate for two or more States by consent, in regard to matters not otherwise within the power of the Parliament is regulated by Article 252, while Article 253 starting with a non-obstante clause empowers Parliament to make any law for the whole country or any part of the territory of India for implementing any treaty, agreement or convention with any other country or countries or any decision made at any international conference, association or other body.”
87. Mr. Divan, however, made an earnest endeavour to further broaden this concept of ‘limited Government’ by giving an altogether different slant. He submitted that there are certain things that the States simply cannot do because the action fundamentally alters the relationship between the citizens and the State. In this hue, he submitted that it was impermissible for the State to undertake the exercise of collection of bio-metric data, including fingerprints and storing at a central depository as it puts the State in an extremely dominant position in relation to the individual citizens. He also submitted that it will put the State in a position to target an individual and engage in surveillance thereby depriving or withholding the enjoyment of his rights and entitlements, which is totally impermissible in a country where governance of the State of founded on the concept of ‘limited Government’. Again, this concept of limited government is woven around Article 21 of the Constitution.
88. Undoubtedly, we are in the era of liberalised democracy. In a democratic society governed by the Constitution, there is a strong trend towards the constitutionalisation of democratic politics, where the actions of democratically elected Government are judged in the light of the Constitution. In this context, judiciary assumes the role of protector of the Constitution and democracy, being the ultimate arbiter in all matters involving the interpretation of the Constitution.”
387) We may observe that the matter is examined keeping in view the fundamental principles of constitutionalism in mind, and more particularly the principle that the concept of ‘limited government’ is applicable having regard to the fact that the three limbs of the State are to act within the framework of a written Constitution which assigns specific powers to each of the wing of the State and this presupposes that the sovereign power of the Parliament is circumscribed by the provisions of the Constitution and the legislature is supposed to Act within the boundaries delineated by the Constitution. The constitutionalism, which is the bedrock of rule of law, is to be necessarily adhered to by the Parliament. Further, the power of judicial review which is accorded to the courts can be exercised to strike down any legislation or executive action if it is unconstitutional.
388) When we examine this issue in the context of discussion on various issues already dealt with, it is difficult to agree with the sweeping proposition advanced by the petitioners that the Aadhaar project is destructive of limited government and constitutional trust. These submissions are premised on the architecture of the Aadhaar being constitutionally intrusive which threatens the autonomy of individuals and has a tendency of creating a surveillance state. In support, the petitioners have referred to certain provisions of the Aadhaar Act. Some provisions which we found offending are struck down, some others have been read down and some are tweaked with. We feel that the statutory regime that would now govern the citizenry, wards off such a danger, if any.
MONEY BILL
Is the Aadhaar Act a validly enacted law having been passed as a Money Bill?
389) Mr. Chidambaram and Mr. Datar had laid attack on the Act on the ground that the Bill it could not have been introduced and passed by the Parliament as Money Bill. It was argued that the Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Bill, 2016 (for short the ‘Bill’) was wrongly certified as Money Bill under Article 110 of the Constitution of India by the Hon’ble Speaker of the Lok Sabha, thereby, virtually excluding the Rajya Sabha from the legislative process and depriving the Hon’ble President of his power of return. This, according to them, is illegal and grossly violates the constitutional provisions.
390) It was submitted that Bills are of three kinds:
(i) Ordinary Bills (Article 107);
(ii) Financial Bills viz. subset of Ordinary Bills (Article 117);
(iii) Money Bill viz. subset of Financial Bills (Article 110).
391) Article 110 reads as under:
“Article 110 – Definition of “Money Bills”.-
(1) For the purposes of this Chapter, a Bill shall be deemed to be a Money Bill if it contains only provisions dealing with all or any of the following matters, namely:–
(a) the imposition, abolition, remission, alteration or regulation of any tax;
(b) the regulation of the borrowing of money or the giving of any guarantee by the Government of India, or the amendment of the law with respect to any financial obligations undertaken or to be undertaken by the Government of India;
(c) the custody of the Consolidated Fund or the Contingency Fund of India, the payment of moneys into or the withdrawal of moneys from any such Fund;
(d) the appropriation of moneys out of the Consolidated Fund of India;
(e) the declaring of any expenditure to be expenditure charged on the Consolidated Fund of India or the increasing of the amount of any such expenditure;
(f) the receipt of money on account of the Consolidated Fund of India or the public account of India or the custody or issue of such money or the audit of the accounts of the Union or of a State; or
(g) any matter incidental to any of the matters specified in sub-clauses (a) to (f).
(2) A Bill shall not be deemed to be a Money Bill by reason only that it provides for the imposition of fines or other pecuniary penalties, or for the demand or payment of fees for licenses or fees for services rendered, or by reason that it provides for the imposition, abolition, remission, alteration or regulation of any tax by any local authority or body for local purposes.
(3) If any question arises whether a Bill is a Money Bill or not, the decision of the Speaker of the House of the People thereon shall be final.
(4) There shall be endorsed on every Money Bill when it is transmit led to the Council of States under article 109, and when it is presented to the President for assent under article 111, the certificate of the Speaker of the House of the People signed by him that it is a Money Bill.”
392) It was submitted that a Money Bill may provide for matters enumerated in Clause (a) to (f) of Article 110. Clause (g) has been added because it may be necessary to include provisions that are only “incidental” to any of matters specified in (a) to (f).
The learned counsel pointed out the distinguishing features of a Money Bill are as below:
(i) It shall be introduced only on the recommendation of President (Article 117(1)).
(ii) It shall be introduced only in the House of the People (Article 117(1), 109(1)).
(iii) A Money Bill is transmitted by the Lok Sabha to the Rajya Sabha. Rajya Sabha thereafter may only make recommendations and return the Bill and not make amendments.
The recommendations may or may not be accepted by the Lok Sabha. If the Money Bill is not returned within 14 days, it is deemed to have been passed by both the Houses. (Article 109(2) to Article 109(5)).
(iv) Upon submission of a Money Bill to the President for his assent, the President cannot return the Money Bill with the message requesting that the Houses will reconsider the Bill (proviso to Article 111). Hence, it is manifest that a Money Bill that a Money Bill is a special kind of Bill that has the effect of denuding the power of the Rajya Sabha of its power to amend the Bill and depriving the President of his power to return the bill for reconsideration. On that premise, it was argued that the provisions of a Money Bill must be construed very strictly and narrowly and only if a Bill falls strictly under definition of a Money Bill (Article 110), it can be passed as a Money Bill. If the provisions of the Bill fall outside the strict definition of Money Bill, the said Bill cannot be passed as a Money Bill.
393) Great emphasis was laid on the word ‘only’ appearing in Article 110 which signified that to qualify as a Money Bill, it has to strictly fall within one or more of the clauses of Article 110. For the interpretation of the word ‘only’, reference was made to the judgment in the case of Hari Ram & Ors. v. Babu Gokul Prasad140:
“3. Section 166 of M.P. Land Revenue Code, 1954 reads as under:
“166. Any person who holds land for agricultural purposes from a tenure holder and who is not an occupancy tenant under Section 169 or a protected lessee under the Berar Regulation of Agricultural Leases Act, 1951, shall be ordinary tenant of such land.
Explanation.- For the purposes of this section –
(i) any person who pays lease money in respect of any land in the form of crop share shall be deemed to hold such land;
(ii) any person who cultivates land in partnership with the tenure holder shall not be deemed to hold such land;
(iii) any person to whom only the right to cut grass or to graze cattle or to grow singhara (Trapa bispinosa) or to propagate or collect lac is granted in any land shall not be deemed to hold such land for agricultural purposes.” A bare perusal of the section indicates that any tenant other than occupancy tenant if he held the land for agricultural purposes from a tenure holder, then he became ordinary tenant by operation of law. Doubt if any stood removed by the explanation which clarifies the class of persons who could be deemed to be covered under a tenant other than occupancy tenant. Since it has been found that the land was let out to appellant not only for the right to cut grass, he could not be held to be a person who was not holding the land for agricultural purposes.
The word ‘only’ in Explanation (iii) is significant. It postulates that entire land should have been used for the purposes enumerated. If part of the land was used for cultivation, then the land could not be deemed to have been granted for cutting grass only. It has been found that out of 5 and odd acres of land, the land under cultivation was 2 acres. Therefore, the negative clause in Explanation (iii) did not apply and the appellant became ordinary tenant under Section 166. In 1959, M.P. Land Revenue Code was enacted and Section 185 provided for the persons who could be deemed to be occupancy tenants. Its relevant part is extracted below: “185. Occupancy tenants.-
(1) Every person who at the coming into force of this Code holds-
(i) in the Mahakoshal Region-
(a) *** (b) *** (c) any land as an ordinary tenant as defined in the Madhya Pradesh Land Revenue Code, 1954 (2 of 1955);”
394) The learned counsel also referred to M/s. Saru Smelting (P) Ltd. v. Commissioner of Sales Tax, Lucknow141:
“3. The contention of the respondent is that Phosphorous Bronze is an alloy containing not only the metals mentioned in the aforesaid entry but Phosphorous also and as such it is not covered under the aforesaid entry. The words “other alloy containing any of these metals only” mean that the alloy made of these metals i.e. copper, tin, nickel or zinc only and that alone is covered under the said entry. It was submitted that if any other metal or substance is included in such an alloy, the same would not be covered under the aforesaid entry.
xx xx xx
5. We were referred to various dictionary meanings of the words ‘Phosphorous Bronze’ which have been noticed by the learned Judge dealing with the case in the High Court. We are really concerned with the interpretation of the entry.
The emphasis in the entry is – either it should be pure copper, tin, nickel or zinc and if it is an alloy containing two or more metals, it must be an alloy containing these metals only. The expression “only” is very material for understanding the meaning of the entry. Since the alloy in dispute contains Phosphorous, may be in a very small quantity, it cannot fall within Entry 2(a) of the aforesaid Notification. The appeal consequently fails and is dismissed with costs.”
395) In order to demonstrate as to what would be the nature and scope of the Money Bill, reference was made to the following literature:
“RELEVANT EXCERPTS FROM ERSKINE MAY’S “PARLIAMENTARY PRACTICE”
Definition of Money Bill
– Section 1(2) of the Act defines a ‘Money Bill’ as a public bill which in the opinion of the Speaker of the House of Commons contains only provisions dealing with all or any of the following subjects, namely, the imposition, repeal, remission, alteration, or regulation of taxation; the imposition for the payment of debt or other financial purposes of charges on the Consolidated Fund or the national Loans Fund, or on money provided by Parliament or the variation or repeal of any such charges; Supply; the appropriation, receipt, custody, issue or audit of accounts of public money; the raising or guarantee of any loan or the repayment thereof; or subordinate matters incidental to those subjects or any of them. For the purposes of this definition the expressions ‘taxation’, ‘public money’, and ‘loan’ respectively do not include any taxation, money, or loan raised by local authorities or bodies for local purposes, matters which, on the other hand, are included within the scope of Commons financial privilege.
PROCEDURE IN PASSING MONEY BILL A
‘Money Bill’ which has been passed by the House of Commons and sent up to the House of Lords at least one month before the end of the session, but is not passed by the House of Lords without amendment within one month after it is so sent up, is, unless the House of Commons direct to the contrary, to be presented for the Royal Assent and becomes an Act of Parliament on the Royal Assent being signified to it. A ‘Money Bil’, when it is sent up to the House of Lords and when it is presented to Her Majesty, must be endorsed with the Speaker’s certificate that it is such a bill. Before giving this certificate the Speaker is directed to consult, if practicable, those two members of the Panel of Chairs who are appointed for the purpose at the beginning of each session by the Committee of Selection.
When the Speaker has certified a bill to be a ‘Money Bill’ this is recorded in the Journal; and Section 3 of the Parliament Act 1911 stipulates that such certificate is conclusive for all purposes and may not be questioned in a court of law. No serious practical difficulty normally arises in deciding whether a particular bill is or is not a ‘Money Bill’; and criticism has seldom been voiced of the Speaker’s action in giving or withholding a certificate. A bill which contains any of the enumerated matters and nothing besides is indisputably a ‘Money bill’. If it contains any other matters, then, unless these are ‘subordinate matters incidental to’ any of the enumerated matters so contained in the bill, the bill is not a ‘Money bill’. Furthermore, even if the main object of a bill is to create a new charge on the Consolidated Fund or on money provided by Parliament, the bill will not be certified if it is apparent that the primary purpose of the new charge is not purely financial.”
THE PARLIAMENTARY ACT, 1911
Chapter 13 of the Parliament Act, 1911 wherein Money Bill is defined as under:
“(1) … (2) A Money Bill means a Public Bill which in the opinion of the Speaker of the House of Commons contains only provisions dealing with all or any of the following subjects, namely, the imposition, repeal, remission, alteration, or regulation of taxation; the imposition for the payment of debt or other financial purposes of charges on the Consolidated Fund, or on money provided by Parliament, or the variation or repeal of any such charges; supply; the appropriation, receipt, custody, issue or audit of accounts of public money; the raising or guarantee of any loan or the repayment thereof; or subordinate matters incidental to those subjects or any of them. In this subsection the expressions “taxation”, “public money”, and “loan” respectively do not include any taxation, money, or loan raised by local authorities or bodies for local purposes.
(3) There shall be endorsed on every Money Bill when it is sent up to the House of Lords and when it is presented to His Majesty for assent the certificate of the Speaker of the House of Commons signed by him that it is a Money Bill. Before giving his certificate, the Speaker shall consult, if practicable, two members to be appointed from the Chairmen’s Panel at the beginning of each Session by the Committee of Selection.”
RELEVANT EXCERPTS FROM THE CONSTITUTION of IRELAND
(1) A Money Bill means a Bill which contains only provisions dealing with all or any of the following matters, namely, the imposition, repeal, remission, alteration or regulation of taxation; the imposition for the payment of debt or other financial purposes of charges on public moneys or the variation or repeal of any such charges; supply, the appropriation, receipt, custody, issue or audit of accounts of public money; the raising or guarantee of any loan or the repayment thereof; matters subordinate and incidental to these matters or any of them.
(2) In this definition the expressions “taxation”, “public money” and “loan” respectively do not include any taxation, money or loan raised by local authorities or bodies for local purposes.
RELEVANT EXCERPTS FROM KAUL & SHAKDER’S “PRACTICE AND PROCEDURE of PARLIAMENT”, LOK SABHA SECRETARIAT AT INDIA
Speaker Mavalankar observed as follows: “Prima facie, it appears to me that the words of article 110 (imposition, abolition, remission, alteration, regulation of any tax) are sufficiently wide to make the Consolidated Bill a Money Bill. A question may arise as to what is the exact significance or scope of the word ‘only’ and whether and how far that word goes to modify or control the wide and general words ‘imposition, abolition, remission, etc.’. I think, prima facie, that the word ‘only’ is not restrictive of the scope of the general terms.
If a Bill substantially deals with the imposition, abolition, etc., of a tax, then the mere fact of the inclusion in the Bill of other provisions which may be necessary for the administration of that tax or, I may say, necessary for the achievement of the objective of the particular Bill, cannot take away the Bill from the category of Money Bills. One has to look to the objective of the bill. Therefore, if the substantial provisions of the Bill aim at imposition, abolition, etc., of any tax then the other provisions would be incidental and their inclusion cannot be said to take it away from the category of a Money Bill. Unless one construes the word ‘only’ in this way it might lead to make article 110 a nullity. No tax can be imposed without making provisions for its assessment, collection, administration, reference to courts or tribunals, etc, one can visualise only one section in a Bill imposing the main tax and there may be fifty other sections which may deal with the scope, method, manner, etc., of that imposition.
Further, we have also to consider the provisions of sub-clause (2) of article 110; and these provisions may be helpful to clarify the scope of the word ‘only’, not directly but indirectly.” 396) It was further submitted that though clause (3) of Article 110 stipulates that decision of the Speaker on whether a Bill is a Money Bill or not is final, that did not mean that it was not subject to the judicial scrutiny and, therefore, in a given case, the Court was empowered to decide as to whether decision of the Speaker was constitutionally correct. In respect of Bill in question, it was argued that though Section 7 states that subsidies, benefits and services shall be provided from Consolidated Fund of India which was an attempt to give it a colour of Money Bill, some of the other provisions, namely, clauses 23(2)(h), 54(2)(m) and 57 of the Bill (which corresponds to Sections 23(2)(h), 54(2)(m) and 57 of the Aadhaar Act) do not fall under any of the clauses of Article 110 of the Constitution.
Therefore, some provisions which were other than those covered by Money Bill and, therefore, introduction of the Bill as Money Bill was clearly inappropriate. It was also argued that, in this scenario, entire Act was bound to fail as there is no provision for severing clauses in Indian Constitution, unlike Section 55 of the Australian Constitution. Insofar as justiciability of the Speaker’s decision is concerned, following judgments were referred to:
(i) Sub-Committee on Judicial Accountability v. Union of India & Ors.142
(ii) S.R. Bommai & Ors. v. Union of India & Ors.143
(iii) Raja Ram Pal v. Hon’ble Speaker, Lok Sabha & Ors.144
(iv) Ramdas Athawale v. Union of India & Ors.145
(v) Kihoto Hollohan v. Zachillhu & Ors.146 397)
It was emphasised that the creation and composition of the Rajya Sabha (Upper House) is an indicator of, and is essential to, constitutional federalism. It is a part of basic structure of the Constitution as held in Kuldip Nayar & Ors. v. Union of India & Ors.147. Therefore, Rajya Sabha could not have been by-passed while passing the legislation in question and doing away with this process and also right of the President to return the Bill has rendered the statute unconstitutional.
398) The learned Attorney General as well as Mr. Dwivedi and some other counsel appearing for respondents refuted the aforesaid submissions in a strongest manner possible. It was argued that the Bill was rightly characterised as a Money Bill and introduced under Article 110 of the Constitution. According to them, the heart of the Aadhaar Act is Section 7. It is not the creation of Aadhaar number per se which is the core of the Act, rather, that is only a means to identify the correct beneficiary and ensure “targeted delivery of subsidies, benefits and services”, the expenditure for which is incurred from the Consolidated Fund of India.
A conjoint reading of the preamble to the Act along with Section 7 clearly discloses the legislative intent and the object of the Act, which is to ensure that subsidy, benefit or service for which expenditure is incurred from or the receipt therefrom forms part of, the Consolidated Fund of India should be targeted to reach the intended beneficiary.
It was argued, without prejudice to the above, that the decision of the Speaker incorporated into a certificate sent to the President is final and cannot be the subject matter of judicial review. To support the aforesaid proposition, reference was made to the judgment in the case of Mohd. Saeed Siddiqui v. State of Uttar Pradesh & Anr.148 wherein the Court held as under:
“7. Leave granted in the special leave petition. This appeal is directed against the order dated 27-8-2012 passed by the Division Bench of the High Court of Judicature of Allahabad in Mukul Upadhyay v. N.K. Mehrotra [Civil Misc. Writ Petition No. 24905 of 2012 (Writ-C 24905 of 2012), order dated 27-8-2012 (All)] whereby the High Court, while allowing the amendment application to the writ petition and holding the writ petition to be maintainable, directed to list the petition on 27-9-2012 for hearing on merits. By way of the said amendment application, the writ petitioner sought to add two grounds in the writ petition viz. the Amendment Act is violative of the provisions of the Constitution of India and the same was wrongly introduced as a Money Bill in clear disregard to the provisions of Article 199 of the Constitution of India. Accordingly, it was prayed to issue a writ, order or direction in the nature of mandamus declaring the Amendment Act as ultra vires the provisions of the Constitution of India.
xx xx xx
12. It was further submitted by Mr Venugopal that the Amendment Act was not even passed by the State Legislature in accordance with the provisions of the Constitution of India and is, thus, a mere scrap of paper in the eye of the law. The Bill in question was presented as a Money Bill when, on the face of it, it could never be called as a Money Bill as defined in Articles 199(1) and 199(2) of the Constitution of India. Since the procedure for an ordinary Bill was not followed and the assent of the Governor was obtained to an inchoate and incomplete Bill which had not even gone through the mandatory requirements under the Constitution of India, the entire action was unconstitutional and violative of Article 200 of the Constitution of India.
xx xx xx
31. The main apprehension of the petitioner is that the Bill that led to the enactment of the Amendment Act was passed as a Money Bill in violation of Articles 197 and 198 of the Constitution of India which should have been passed by both the Houses viz. U.P. Legislative Assembly and U.P. Legislative Council and was wrongly passed only by the U.P. Legislative Assembly. During the course of hearing, Mr Desai, learned Senior Counsel appearing for the State of U.P., placed the original records pertaining to the proceedings of the Legislative Assembly, decision of the Speaker as well as the Governor, which we are going to discuss in the latter part of our judgment.
xx xx xx
34. The above provisions make it clear that the finality of the decision of the Speaker and the proceedings of the State Legislature being important privilege of the State Legislature viz. freedom of speech, debate and proceedings are not to be inquired by the courts. The “proceeding of the legislature” includes everything said or done in either House in the transaction of the parliamentary business, which in the present case is enactment of the Amendment Act. Further, Article 212 precludes the courts from interfering with the presentation of a Bill for assent to the Governor on the ground of non-compliance with the procedure for passing Bills, or from otherwise questioning the Bills passed by the House. To put it clear, proceedings inside the legislature cannot be called into question on the ground that they have not been carried on in accordance with the Rules of Business. This is also evident from Article 194 which speaks about the powers, privileges of the Houses of the Legislature and of the members and committees thereof.
35. We have already quoted Article 199. In terms of Article 199(3), the decision of the Speaker of the Legislative Assembly that the Bill in question was a Money Bill is final and the said decision cannot be disputed nor can the procedure of the State Legislature be questioned by virtue of Article 212. We are conscious of the fact that in the decision of this Court in Raja Ram Pal v. Lok Sabha [(2007) 3 SCC 184] , it has been held that the proceedings which may be tainted on account of substantive or gross irregularity or unconstitutionality are not protected from judicial scrutiny. 36. Even if it is established that there was some infirmity in the procedure in the enactment of the Amendment Act, in terms of Article 255 of the Constitution the matters of procedure do not render invalid an Act to which assent has been given by the President or the Governor, as the case may be.
xx xx xx
43. As discussed above, the decision of the Speaker of the Legislative Assembly that the Bill in question was a Money Bill is final and the said decision cannot be disputed nor can the procedure of the State Legislature be questioned by virtue of Article 212. Further, as noted earlier, Article 252 also shows that under the Constitution the matters of procedure do not render invalid an Act to which assent has been given by the President or the Governor, as the case may be. Inasmuch as the Bill in question was a Money Bill, the contrary contention by the petitioner against the passing of the said Bill by the Legislative Assembly alone is unacceptable.”
399) It was submitted that the challenge on identical grounds was, thus, repelled in the aforesaid case wherein validity of legislative enactment of a State in question, on the same ground, namely, it could not called Money Bill as defined in Article 199 of the Constitution, which was pari materia with Article 110 of the Constitution qua the Parliament. Judgment in the case of Yogendra Kumar Jaiswal & Ors. v. State of Bihar & Ors.149 was also referred to wherein the Court was concerned with Orissa Special Courts Act, 2006 which was also passed as Money Bill and was challenged as violative of Article 199 of the Constitution. It was argued that the Court held in this case that decision of the Speaker that the Bill in question is a Money Bill is final and such a decision cannot be disputed nor can the procedure of the state legislature can be questioned by virtue of Article 212 of the Constitution. The learned Attorney General specifically read out the following portion from the said judgment:
“42. In this regard, we may profitably refer to the authority in Mohd. Saeed Siddiqui v. State of U.P. [Mohd. Saeed Siddiqui v. State of U.P., (2014) 11 SCC 415], wherein a three-Judge Bench while dealing with such a challenge, held that Article 212 precludes the courts from interfering with the presentation of a Bill for assent to the Governor on the ground of non-compliance with the procedure for passing Bills, or from otherwise questioning the Bills passed by the House, for proceedings inside the legislature cannot be called into question on the ground that they have not been carried on in accordance with the Rules of Business.
Thereafter, the Court referring to Article 199(3) ruled that the decision of the Speaker of the Legislative Assembly that the Bill in question was a Money Bill is final and the said decision cannot be disputed nor can the procedure of the State Legislature be questioned by virtue of Article 212. The Court took note of the decision in Raja Ram Pal [Raja Ram Pal v. Lok Sabha, (2007) 3 SCC 184] wherein it has been held that the proceedings which may be tainted on account of substantive or gross irregularity or unconstitutionality are not protected from judicial scrutiny. Eventually, the Court repelled the challenge.
43. In our considered opinion, the authorities cited by the learned counsel for the appellants do not render much assistance, for the introduction of a Bill, as has been held in Mohd. Saeed Siddiqui [Mohd. Saeed Siddiqui v. State of U.P., (2014) 11 SCC 415] , comes within the concept of “irregularity” and it does come within the realm of substantiality. What has been held in Special Reference No. 1 of 1964 [Powers, Privileges and Immunities of State Legislatures, In re, Special Reference No. 1 of 1964, AIR 1965 SC 745] has to be appositely understood. The factual matrix therein was totally different than the case at hand as we find that the present controversy is wholly covered by the pronouncement in Mohd. Saeed Siddiqui [Mohd. Saeed Siddiqui v. State of U.P., (2014) 11 SCC 415] and hence, we unhesitatingly hold that there is no merit in the submission so assiduously urged by the learned counsel for the appellants.”
400) Reliance was also placed on three judgments of Constitution Bench of this Court150.
The learned Attorney General also submitted that even if it is presumed that there is illegality of procedure in the conduct of business in the Parliament, such parliamentary proceedings were immune from challenge. Attention of the Court was also drawn to Article 122, which prohibits any proceedings of Parliament being called in question on the ground of “any alleged irregularity of procedure”.
It was submitted that the decision and certification of the Speaker being a matter of procedure is included in the Chapter under the heads “Legislative Procedure” being Articles 107 to 111, “Procedure in Financial Matters” being Articles 112 to 117 and “Procedure Generally” being Article 118 to 122 placing beyond doubt that separation of powers is embedded in these provisions clearly excluding judicial review in matters of procedure. Submission was that if this is clearly a Money Bill, being placed beyond challenge in a Court of Law, then to term it as a Financial Bill as contended by the petitioners would be wholly unjustified. Dilating the aforesaid proposition, it was pointed out that in the Draft Constitution prepared by the drafting committee, Article 101 provided for immunity of Parliamentary proceedings from judicial intervention on ‘alleged irregularity of procedure’.
This article finally got renumbered as Article 122 in the Constitution of India. During the Constituent Assembly debates, Shri H.V. Kamath suggested an amendment to draft Article 101 to clarify that the validity of any Parliamentary proceedings shall not be called in question in any court. Accordingly, he suggested that the words ‘called in question’ be replaced with ‘called in question in any court’. Refuting this suggested amendment, Dr. B.R. Ambedkar categorically stated:
“Sir, with regard to the amendment of Mr. Kamath, I do not think it is necessary, because where can the proceedings of Parliament be questioned in a legal manner except in a court? Therefore the only place where the proceedings of Parliament can be questioned in a le-gal manner and legal sanction obtained is the Court. Therefore it is unnecessary to mention the words which Mr. Kamath wants in his amendment. For the reason I have explained, the only forum there the proceedings can be questioned in a legal manner and legal relief obtained either against the President or the Speaker or any officer or Member, being the Court, it is unnecessary to specify the forum. Mr. Kamath will see that the marginal note makes it clear.”
401) Support of the judgment rendered by Patna High Court in Patna Zilla Truck Owners Association & Ors. v. State of Bihar & Ors.151 was also taken, which has been approved by the Constitution Bench judgment of this Court in State of Punjab v. Sat Pal Dang & Ors.152. It was also argued that the legal position was similar in other Parliamentary democracies like Australia and Canada.
402) In any case, argued the learned Attorney General and Mr. Dwivedi, the Bill was rightly introduced as Money Bill as it merited such a description in law as well. To buttress this submission, doctrine of pith and substance was invoked as a guiding test. It was argued that Section 7 which was the heart and soul of the Aadhaar Act fulfilled this requirement as the subsidies, benefits and services, the expenditure of which is incurred from the Consolidated Fund of India. Therefore, conditions laid down in Article 110 were fully satisfied. Following judgments153 explaining the doctrine of pith and substance were pressed into substance.
It was submitted that undoubtedly in pith and substance, the object of the Aadhaar Act is to identify the correct beneficiaries and ensure the “targeted delivery of subsidies, benefits and services”, the expenditure for which is incurred from the Consolidated Fund of India. The creation of the Aadhaar number and authentication facility are in furtherance of the object of the Aadhaar Act, which is permissible under Article 110(g).
It was also argued that Section 57, which has been attacked as being untraceable to any of the sub-clauses of (a) to (f) of Article 110 cannot be looked at in isolation. This Bill in its pith and substance should pass the test of being a Money Bill and not isolated provisions. On the contrary, Section 57 of the Act is also incidental to the object of the Act and creates a limitation upon use of Aadhaar by private parties wherein even though nothing prevents them from using Aadhaar for other purposes, the same has been subjected to the procedure and obligations of Section 8, which requires, inter alia, informed consent of the Aadhaar number holder, purpose limitation, i.e. the identity information will be used only for submission to CIDR for authentication and the private entity must provide alternatives to submission of such identity information, which, in other words, means that private parties cannot insist upon Aadhaar and make Aadhaar mandatory, unless required by law. Therefore, Section 57 is a limitation imposed under the Aadhaar Act on the use of Aadhaar number by private parties which is purely incidental to the object of the Act and would squarely fall within Article 110(g) of the Constitution.
403) At the outset, we would like to recognise the importance of Rajya Sabha (Upper House) in a bicameral system of the Parliament. The significance and relevance of the Upper House has been succinctly exemplified by this Court in Kuldip Nayar’s case in the following words:
“74. The growth of “bicameralism” in parliamentary forms of Government has been functionally associated with the need for effective federal structures. This nexus between the role of “Second Chambers” or Upper Houses of Parliament and better coordination between the Central Government and those of the constituent units, was perhaps first laid down in definite terms with the Constitution of the United States of America, which was ratified by the thirteen original States of the Union in the year 1787. The Upper House of the Congress of USA, known as the Senate, was theoretically modelled on the House of Lords in the British Parliament, but was totally different from the latter with respect to its composition and powers.
75. Since then, many nations have adopted a bicameral form of Central Legislature, even though some of them are not federations. On account of colonial rule, these British institutions of parliamentary governance were also embodied in the British North America Act, 1867 by which the Dominion of Canada came into existence and the Constitution of India, 1950. In Canada, Parliament consists of the House of Commons and the Senate (the Upper House). Likewise, the Parliament of the Union of India consists of the Lok Sabha (House of the People) and the Rajya Sabha (Council of States, which is the Upper House). In terms of their functions as agencies of representative democracies, the Lower Houses in the legislatures of India, USA and Canada, namely, the Lok Sabha, the House of Representatives and the House of Commons broadly follow the same system of composition.
As of now, Members of the Lower Houses are elected from pre-designated constituencies through universal adult suffrage. The demarcation of these constituencies is in accordance with distribution of population, so as to accord equity in the value of each vote throughout the territory of the country. However, with the existence of constituent States of varying areas and populations, the representation accorded to these States in the Lower House becomes highly unequal. Hence, the composition of the Upper House has become an indicator of federalism, so as to more adequately reflect the interests of the constituent States and ensure a mechanism of checks and balances against the exercise of power by Central authorities that might affect the interests of the constituent States.
xx xx xx
79. The genesis of the Indian Rajya Sabha on the other hand benefited from the constitutional history of several nations which allowed the Constituent Assembly to examine the federal functions of an Upper House. However, “bicameralism” had been introduced to the provincial legislatures under the British rule in 1921. The Government of India Act, 1935 also created an Upper House in the federal legislature, whose members were to be elected by the members of provincial legislatures and in case of Princely States to be nominated by the rulers of such territories. However, on account of the realities faced by the young Indian Union, a Council of States (the Rajya Sabha) in the Union Parliament was seen as an essential requirement for a federal order. Besides the former British provinces, there were vast areas of Princely States that had to be administered under the Union.
Furthermore, the diversity in economic and cultural factors between regions also posed a challenge for the newly-independent country. Hence, the Upper House was instituted by the Constitutionframers which would substantially consist of members elected by the State Legislatures and have a fixed number of nominated members representing non-political fields. However, the distribution of representation between the States in the Rajya Sabha is neither equal nor entirely based on population distribution. A basic formula is used to assign relatively more weightage to smaller States but larger States are accorded weightage regressively for additional population. Hence the Rajya Sabha incorporates unequal representation for States but with proportionally more representation given to smaller States.
The theory behind such allocation of seats is to safeguard the interests of the smaller States but at the same time giving adequate representation to the larger States so that the will of the representatives of a minority of the electorate does not prevail over that of a majority.
80. In India, Article 80 of the Constitution of India prescribes the composition of the Rajya Sabha. The maximum strength of the House is 250 members, out of which up to 238 members are the elected representatives of the States and the Union Territories [Article 80(1)(b)], and 12 members are nominated by the President as representatives of non-political fields like literature, science, art and social services [Articles 80(1)(a) and 80(3)]. The members from the States are elected by the elected members of the respective State Legislative Assemblies as per the system of proportional representation by means of the single transferable vote [Article 80(4)]. The manner of election for representatives from the Union Territories has been left to prescription by Parliament [Article 80(5)].
The allocation of seats for the various States and Union Territories of the Indian Union is enumerated in the Fourth Schedule to the Constitution, which is read with Articles 4(1) and 80(2). This allocation has obviously varied with the admission and reorganisation of States.”
404) The Rajya Sabha, therefore, becomes an important institution signifying constitutional fedaralism. It is precisely for this reason that to enact any statute, the Bill has to be passed by both the Houses, namely, Lok Sabha as well as Rajya Sabha. It is the constitutional mandate. The only exception to the aforesaid Parliamentary norm is Article 110 of the Constitution of India. Having regard to this overall scheme of bicameralism enshrined in our Constitution, strict interpretation has to be accorded to Article 110. Keeping in view these principles, we have considered the arguments advanced by both the sides.
405) We would also like to observe at this stage that insofar as submission of the respondents about the justiciability of the decision of the Speaker of the Lok Sabha is concerned, we are unable to subscribe to such a contention. Judicial review would be admissible under certain circumstances having regard to the law laid down by this Court in various judgments which have been cited by Mr. P. Chidambaran, learned senior counsel appearing for the petitioners, and taken note of in paragraph 396. 406) From the submissions of the learned counsel for the parties as taken note of above, it is clear that the petitioners accept that Section 7 of the Aadhaar Act has the elements of ‘Money Bill’.
The attack is on the premise that some other provisions, namely, clauses 23(2)(h), 54(2)(m) and 57 of the Bill (which corresponds to Sections 23(2)(h), 54(2)(m) and 57 of the Aadhaar Act) do not fall under any of the clauses of Article 110 of the Constitution and, therefore, Bill was not limited to only those subjects mentioned in Article 110. Insofar as Section 7 is concerned, it makes receipt of subsidy, benefit or service subject to establishing identity by the process of authentication under Aadhaar or furnish proof of Aadhaar etc.
It is also very clearly declared in this provision that the expenditure incurred in respect of such a subsidy, benefit or service would be from the Consolidated Fund of India. It is also accepted by the petitioners that Section 7 is the main provision of the Act. In fact, Introduction to the Act as well as the Statement of Objects and Reasons very categorically record that the main purpose of Aadhaar Act is to ensure that such subsidies, benefits and services reach those categories of persons, for whom they are actually meant. Sections 2(f), (w) and (x) of the Aadhaar Act define benefit, service and subsidy respectively. These provisions read as under:
“2(f) “benefit” means any advantage, gift, reward, relief, or payment, in cash or kind, provided to an individual or a group of individuals and includes such other benefits as may be notified by the Central Government; 2(w) “service” means any provision, facility, utility or any other assistance provided in any form to an individual or a group of individuals and includes such other services as may be notified by the Central Government; 2(x) “subsidy” means any form of aid, support, grant, subvention, or appropriation, in cash or kind, to an individual or a group of individuals and includes such other subsidies as may be notified by the Central Government.”
407) As all these three kinds of welfare measures are sought to be extended to the marginalised section of society, a collective reading thereof would show that the purpose is to expand the coverage of all kinds of aid, support, grant, advantage, relief provisions, facility, utility or assistance which may be extended with the support of the Consolidated Fund of India with the objective of targeted delivery. It is also clear that various schemes which can be contemplated by the aforesaid provisions, relate to vulnerable and weaker section of the society. Whether the social justice scheme would involve a subsidy or a benefit or a service is merely a matter of the nature and extent of assistance and would depend upon the economic capacity of the State. Even where the state subsidizes in part, whether in cash or kind, the objective of emancipation of the poor remains the goal.
408) The respondents are right in their submission that the expression subsidy, benefit or service ought to be understood in the context of targeted delivery to poorer and weaker sections of society. Its connotation ought not to be determined in the abstract. For as an abstraction one can visualize a subsidy being extended by Parliament to the King; by Government to the Corporations or Banks; etc. The nature of subsidy or benefit would not be the same when extended to the poor and downtrodden for producing those conditions without which they cannot live a life with dignity. That is the main function behind the Aadhaar Act and for this purpose, enrolment for Aadhaar number is prescribed in Chapter II which covers Sections 3 to 6. Residents are, thus, held entitled to obtain Aadhaar number. We may record here that such an enrolment is of voluntary nature.
However, it becomes compulsory for those who seeks to receive any subsidy, benefit or service under the welfare scheme of the Government expenditure whereof is to be met from the Consolidated Fund of India. It follows that authentication under Section 7 would be required as a condition for receipt of a subsidy, benefit or service only when such a subsidy, benefit or service is taken care of by Consolidated Fund of India.
Therefore, Section 7 is the core provision of the Aadhaar Act and this provision satisfies the conditions of Article 110 of the Constitution. Upto this stage, there is no quarrel between the parties. 409) In this context, let us examine provisions of Sections 23(2)(h), 54(2)(m) and 57 of the Aadhaar Act. Insofar as Section 23 is concerned, it deals with powers and functions of the Authority. Sub-section (1) thereof says that the Authority shall develop the policy, procedure and systems for issuing Aadhaar numbers to individuals and perform authentication thereof under this Act. As mentioned above, under Section 3 of the Aadhaar Act, Aadhaar number is to be issued and authentication is performed under Section 8 of the Aadhaar Act.
Sub-section (2) stipulates certain specified powers and functions which the Authority may perform and sub-section (h) thereof reads as under: “23(2)(h) specifying the manner of use of Aadhaar numbers for the purposes of providing or availing of various subsidies, benefits, services and other purposes for which Aadhaar numbers may be used.”
410) This provision, thus, enables the Authority to specify the manner of use of Aadhaar with specific purpose in mind, namely, for providing or availing of various subsidies, benefits and services. These are relatable to Section 7. However, it uses the expression ‘other purposes’ as well. The expression ‘other purposes’ can be read ejusdem generis which would have its relation to subsidies, benefits and services as mentioned in Section 7 and it can be confined only to that purpose i.e. scheme of targeted delivery for giving any grant, relief etc. when it is chargeable to Consolidated Fund of India. Therefore, this provision, according to us, can be read as incidental to the main provision and would be covered by Article 110(g) of the Constitution. Section 54 confers power upon the Authority to make regulations consistent with the Act and rules made thereunder, for carrying out the provisions of the Act.
Clause (m) of sub-section (2) of Section 54 relates to Section 23(2)(h) as can be seen from its language.
“54(2)(m) the manner of use of Aadhaar numbers for the purposes of providing or availing of various subsidies, benefits, services and other purposes for which Aadhaar numbers may be used under clause (h) of sub-section (2) of section 23.”
411) The interpretation which we have given to Section 23(2)(h) would apply here as well and, therefore, we do not find any problem with this provision also. Coming to Section 57 of the Aadhaar Act, it mentions that Aadhaar Act would not prevent use of Aadhaar number for other purposes under the law. It is only an enabling provision as it permits the use of Aadhaar number for other purposes as well. This provision is to be viewed in the backdrop that Section 7 is the core provision.
We have already held that it has substantial nexus with the appropriation of funds from the Consolidated Fund of India and is directly connected with Article 110 of the Constitution. To facilitate this, UIDAI is established as Authority under the Act which performs various functions including that of a regulator needing funds for staff salary and it’s own expenses. Respondents have rights remarked that the Authority is the performer in chief, the predominant dramatis personae. It appoints Registrars, enrollers, REs and ASAs; it lays down device and software specifications, and develops softwares too; it enrols; it de-duplicates; it establishes CIDR and manages it; it authenticates; it inspects; it prosecutes; it imposes disincentives; etc. And all this it does based on funds obtained by appropriations from Consolidated Fund of India (Section 24).
412) When we examine the provision of Section 57 in the aforesaid backdrop, as stated above, it only enables holder of Aadhaar number to use the said number for other purposes as well. That would not take away or dilute the sheen of clause 7 (now Section 7) for which purposes the Bill was introduced as Money Bill. In any case, a part of Section 57 has already declared unconstitutional whereby even a body corporate in private sector or person may seek authentication from the Authority for establishing the identity of an individual.
For all the aforesaid reasons, we are of the opinion that Bill was rightly introduced as Money Bill. Accordingly, it is not necessary for us to deal with other contentions of the petitioners, namely, whether certification by the Speaker about the Bill being Money Bill is subject to judicial review or not, whether a provision which does not relate to Money Bill is severable or not. We reiterate that main provision is a part of Money Bill and other are only incidental and, therefore, covered by clause (g) of Article 110 of the Constitution.
Section 139AA of the Income Tax Act, 1961:
413) The Division Bench of this Court in Binoy Viswam has already upheld the validity of Section 139AA of the Income Tax Act, 1961 by repelling the contention predicated on Articles 14 and 19 of the Constitution of India. No doubt, in the said judgment, the Court held that insofar as scope of judicial review of legislative act is concerned, it is available on two grounds, namely:
(i) The Act is not within the competence of the legislature which passed the law, and/or
(ii) It is in contravention of any fundamental rights stipulated in Part III of the Constitution or any other rights/provisions of the Constitution.
414) We have already acknowledged the existence of third ground as pointed out in Shayara Bano case, namely, ‘manifest arbitrariness’. An Act which is manifestly arbitrary would be unreasonable and contrary to rule of law and, therefore, violative of Article 14 of the Constitution. Even when we consider the provisions of Section 139AA of the Income Tax Act, 1961 from this point of view, it cannot be said that the provision suffers from the vice of manifest arbitrariness. On the contrary, in Binoy Viswam itself, the benevolent purpose for inserting such a provision as a bona fide move has been highlighted. Therefore, the provision needs this test as well. In this behalf, the Court observed:
“101. The varying needs of different classes or sections of people require differential and separate treatment. The legislature is required to deal with diverse problems arising out of an infinite variety of human relations. It must, therefore, necessarily have the power of making laws to attain particular objects and, for that purpose, of distinguishing, selecting and classifying persons and things upon which its laws are to operate. The principle of equality of law, thus, means not that the same law should apply to everyone but that a law should deal alike with all in one class; that there should be an equality of treatment under equal circumstances. It means that equals should not be treated unlike and unlikes should not be treated alike. Likes should be treated alike.”
415) Since the issue as to whether right to privacy is a facet of fundamental rights or not was pending before the Constitution Bench, the challenge to Section 139AA was not examined in the context of privacy rights, specifically Article 21 of the Constitution though this aspect was argued. The Division Bench observed in this behalf, as under:
“136. Subject to the aforesaid, these writ petitions are disposed of in the following manner: 136.1. We hold that Parliament was fully competent to enact Section 139-AA of the Act and its authority to make this law was not diluted by the orders of this Court.
136.2. We do not find any conflict between the provisions of the Aadhaar Act and Section 139-AA of the Income Tax Act inasmuch as when interpreted harmoniously, they operate in distinct fields.
136.3. Section 139-AA of the Act is not discriminatory nor it offends equality clause enshrined in Article 14 of the Constitution. 136.4. Section 139-AA is also not violative of Article 19(1) (g) of the Constitution insofar as it mandates giving of Aadhaar enrolment number for applying for PAN cards, in the income tax returns or notified Aadhaar enrolment number to the designated authorities. Further, the proviso to sub-section (2) thereof has to be read down to mean that it would operate only prospectively.
136.5. The validity of the provision upheld in the aforesaid manner is subject to passing the muster of Article 21 of the Constitution, which is the issue before the Constitution Bench in Writ Petition (Civil) No. 494 of 2012 and other connected matters. Till then, there shall remain a partial stay on the operation of the proviso to sub-section (2) of Section 139-AA of the Act, as described above. No costs.”
416) The nine Judge Bench has already, since then, answered the reference by holding that right to privacy is a fundamental right. Having regard to that, validity of Section 139AA of the Act needs to be tested on this ground.
417) As already explained above, the Constitution Bench has held that in K.S. Puttaswamy though privacy is a fundamental right inter alia traceable to the right to liberty enshrined in Article 21 of the Constitution, it is not an absolute right but subject to limitations. The Court also laid down the triple test which need to be satisfied for judging the permissible limits for invasion of privacy while testing the validity of any legislation.
These are:
(a) The existence of a law.
(b) A “legitimate State interest”; and
(c) Such law should pass the “test of proportionality”.
418) In the present case, there is no dispute that first requirement stands satisfied as Section 139AA is a statutory provision and, therefore, there is a backing of law. Mr. Tushar Mehta, learned ASG had argued that not only other two requirements are also satisfied, rather these have been specifically dealt with by the Division Bench in Binoy Viswam inasmuch as these aspects were eluded to, consider, examined and the Court recorded its findings on these aspects. We find force in this submission of Mr. Mehta. Insofar as requirement of ‘legitimate State interest’ is concerned, he pointed out that though Nariman, J. provided for a lenient test, namely, ‘larger public interest’ as against ‘legitimate State interest’, the provision satisfies both the tests. We agree with his submission, as Section 139AA of the Income Tax Act, 1961 seeks to safeguard the following interest:
“To prevent income tax evasion by requiring, through an amendment to the Income Tax Act, that the Aadhaar number be linked with the PAN.”
419) The mandatory requirement of quoting/producing PAN number is given in Rule 114 and the Form 49A. While mandating that “every person”, (the term “person” as defined under Section 2(31) of the Act), shall apply for and get a PAN, the legislature also provided for the requirement so as to how such number will be given to every “person” in Rule 114 of the Income Tax Rules, the relevant part of which is Rule 114(1). While complying with the mandatory requirement (which have been in existence since 1989) and that for all “persons”, many facts were required to be disclosed and such disclosure was/is in public interest including demographic details and biometrics i.e. left thumb impression/signature.
420) The Parliament, considering the “legitimate State interest” as well as the “larger public interest” has now introduced Section 139AA which is only an extension of Section 139A which requires linking of PAN number with Aadhaar number which is issued under the Act for the purpose of eliminating duplicate PANs from the system with the help of a robust technology solution. Therefore, those who have PAN number and have already provided the information required to get PAN number cannot claim to have any legitimate expectation of withholding any data required for Aadhaar under the ground of “privacy”.
421) The respondents have demonstrated with empirical data, in the common additional affidavit of respondent Nos. 1 and 3 the existence of the “legitimate State interest” and “larger public interest”. Being a unique identifier, the problem of bogus or duplicate PANs can be dealt with in a more systematic and fullproof manner (though, in the context of Articles 14 and 19 of the Constitution, but at the same time, relevant from the perspective of legitimate State interest also). Discussion on this aspect, in Binoy Viswam, proceeds as under:
“60.2. PAN is the key or identifier of all computerised records relating to the taxpayer. The requirement for obtaining of PAN is mandated through Section 139-A of the Act. The procedure for application for PAN is prescribed in Rule 114 of the Rules. The forms prescribed for PAN application are Forms 49-A and 49-AA for Indian and foreign citizens/entities. Quoting of PAN has been mandated for certain transactions above specified threshold value in Rule 114-B of the Rules.
60.3. For achieving the objective of one PAN to one assessee, it is required to maintain uniqueness of PAN. The uniqueness of PAN is achieved by conducting a deduplication check on all already existing allotted PAN against the data furnished by new applicant. Under the existing system of PAN only demographic data is captured. De-duplication process is carried out using a phonetic algorithm whereby a Phonetic PAN (PPAN) is created in respect of each applicant using the data of applicant’s name, father’s name, date of birth, gender and status. By comparison of newly generated PPAN with existing set of PPANs of all assessees duplicate check is carried out and it is ensured that same person does not acquire multiple PANs or one PAN is not allotted to multiple persons.
Due to prevalence of common names and large number of PAN holders, the demographic way of de-duplication is not foolproof. Many instances are found where multiple PANs have been allotted to one person or one PAN has been allotted to multiple persons despite the application of abovementioned de-duplication process. While allotment of multiple PANs to one person has the risk of diversion of income of person into several PANs resulting in evasion of tax, the allotment of same PAN to multiple persons results in wrong aggregation and assessment of incomes of several persons as one taxable entity represented by single PAN.
60.4. Presently verification of original documents in only 0.2% cases (200 out of 1,00,000 PAN applications) is done on a random basis which is quite less. In the case of Aadhaar, 100% verification is possible due to availability of online Aadhaar authentication service provided by the UIDAI. Aadhaar seeding in PAN database will make PAN allotment process more robust.
60.5. Seeding of Aadhaar number into PAN database will allow a robust way of de-duplication as Aadhaar number is de-duplicated using biometric attributes of fingerprints and iris images. The instance of a duplicate Aadhaar is almost non-existent. Further seeding of Aadhaar will allow the Income Tax Department to weed out any undetected duplicate PANs. It will also facilitate resolution of cases of one PAN allotted to multiple persons.
xx xx xx
104. Insofar as the impugned provision is concerned, Mr Datar had conceded that first test that of reasonable classification had been satisfied as he conceded that individual assessees form a separate class and the impugned provision which targeted only individual assessees would not be discriminatory on this ground. His whole emphasis was that Section 139-AA of the Act did not satisfy the second limb of the twin tests of classification as, according to him, this provision had no rational nexus with the object sought to be achieved. In this behalf, his submission was that if the purpose of the provision was to curb circulation of black money, such an object was not achievable by seeding PAN with Aadhaar inasmuch as Aadhaar is only for individuals. His submission was that it is only the individuals who are responsible for generating black money or money laundering. This was the basis for Mr Datar’s submission. We find it somewhat difficult to accept such a submission.
105. Unearthing black money or checking money laundering is to be achieved to whatever extent possible. Various measures can be taken in this behalf. If one of the measures is introduction of Aadhaar into the tax regime, it cannot be denounced only because of the reason that the purpose would not be achieved fully. Such kind of menace, which is deep-rooted, needs to be tackled by taking multiple actions and those actions may be initiated at the same time. It is the combined effect of these actions which may yield results and each individual action considered in isolation may not be sufficient. Therefore, rationality of a particular measure cannot be challenged on the ground that it has no nexus with the objective to be achieved. of course, there is a definite objective.
For this purpose alone, individual measure cannot be ridiculed. We have already taken note of the recommendations of SIT on black money headed by Justice M.B. Shah. We have also reproduced the measures suggested by the Committee headed by Chairman, CBDT on “Measures to Tackle Black Money in India and Abroad”. They have, in no uncertain terms, suggested that one singular proof of identity of a person for entering into finance/business transactions, etc. may go a long way in curbing this foul practice. That apart, even if solitary purpose of de-duplication of PAN cards is taken into consideration, that may be sufficient to meet the second test of Article 14.
It has come on record that 11.35 lakh cases of duplicate PAN or fraudulent PAN cards have already been detected and out of this 10.52 lakh cases pertain to individual assessees. Seeding of Aadhaar with PAN has certain benefits which have already been enumerated. Furthermore, even when we address the issue of shell companies, fact remains that companies are after all floated by individuals and these individuals have to produce documents to show their identity. It was sought to be argued that persons found with duplicate/bogus PAN cards are hardly 0.4% and, therefore, there was no need to have such a provision. We cannot go by percentage figures. The absolute number of such cases is 10.52 lakhs, which figure, by no means, can be termed as miniscule, to harm the economy and create adverse effect on the nation. The respondents have argued that Aadhaar will ensure that there is no duplication of identity as biometrics will not allow that and, therefore, it may check the growth of shell companies as well.
xx xx xx
127. It would be apposite to quote the following discussion by the Comptroller and Auditor General in his report for the year 2011: “Widening of Tax Base The assessee base grew over the last five years from 297.9 lakh taxpayers in 2005-06 to 340.9 lakh taxpayers in 2009-10 at the rate of 14.4 per cent. The Department has different mechanisms available to enhance the assessee base which include inspection and survey, information sharing with other tax departments and third-party information available in annual information returns. Automation also facilitates greater crosslinking. Most of these mechanisms are available at the level of assessing officers. The Department needs to holistically harness these mechanisms at macro level to analyse the gaps in the assessee base.
Permanent Account Numbers (PANs) issued up to March 2009 and March 2010 were 807.9 lakhs and 958 lakhs respectively. The returns filled in 2008-09 and 2009-10 were 326.5 lakhs and 340.9 lakhs respectively. The gap between PANs and the number of returns filed was 617.1 lakhs in 2009-10. The Board needs to identify the reasons for the gap and use this information for appropriately enhancing the assessee base. The gap may be due to issuance of duplicate PAN cards and death of some PAN card holders.
The Department needs to put in place appropriate controls to weed out the duplicate PANs and also update the position in respect of deceased assessee. It is significant to note that the number of PAN card holders has increased by 117.7 per cent between 2005-06 to 2009-10 whereas the number of returns filed in the same period has increased by 14.4 per cent only. The total direct tax collection has increased by 128.8 per cent during the period 2005-06 to 2009-10. The increase in the tax collection was around nine times as compared to increase in the assessee base. It should be the constant endeavour of the Department to ensure that the entire assessee base, once correctly identified is duly meeting the entire tax liability.
However, no assurance could be obtained that the tax liability on the assessee is being assessed and collected properly. This comment is corroborated in Para 2.4.1 of Chapter 2 of this report where we have mentioned about our detection of undercharge of tax amounting to Rs 12,842.7 crores in 19,230 cases audited during 2008-09. However, given the fact that ours is a test audit, the Department needs to take firm steps towards strengthening the controls available on the existing statutes towards deriving an assurance on the tax collections.”
(emphasis supplied)
128. Likewise, the Finance Minister in his Budget speech in February 2013 described the extent of tax evasion and offering lesser income tax than what is actually due thereby labelling India as tax non-compliant, with the following figures: “India’s tax to GDP ratio is very low, and the proportion of direct tax to indirect tax is not optional from the viewpoint of social justice. I place before you certain data to indicate that our direct tax collection is not commensurate with the income and consumption pattern of Indian economy. As against estimated 4.2 crore persons engaged in organised sector employment, the number of individuals filing return for salary income are only 1.74 crores.
As against 5.6 crore informal sector individual enterprises and firms doing small business in India, the number of returns filed by this category are only 1.81 crores. Out of the 13.94 lakh companies registered in India up to 31-3- 2014, 5.97 lakh companies have filed their returns for Assessment Year 2016-17. of the 5.97 lakh companies which have filed their returns for Assessment Year 2016-17 so far, as many as 2.76 lakh companies have shown losses or zero income. 2.85 lakh companies have shown profit before tax of less than Rs 1 crore. 28,667 companies have shown profit between Rs 1 crore to Rs 10 crores, and only 7781 companies have profit before tax of more than Rs 10 crores.
Among 3.7 crore individuals who filed the tax returns in 2015-16, 99 lakhs show income below the exemption limit of Rs 2.5 lakh p.a. 1.95 crores show income between Rs 2.5 to Rs 5 lakhs, 52 lakhs show income between Rs 5 to Rs 10 lakhs and only 24 lakh people show income above Rs 10 lakhs. of the 76 lakh individual assessees who declare income above Rs 5 lakhs, 56 lakhs are in the salaried class. The number of people showing income more than 50 lakhs in the entire country is only 1.72 lakhs. We can contrast this with the fact that in the last five years, more than 1.25 crore cars have been sold, and number of Indian citizens who flew abroad, either for business or tourism, is 2 crores in the year 2015. From all these figures we can conclude that we are largely a tax non-compliant society. The predominance of the cash in the economy makes it possible for the people to evade their taxes.
When too many people evade the taxes, the burden of their share falls on those who are honest and compliant.”
129. The respondents have also claimed that linking of Aadhaar with PAN is consistent with India’s international obligations and goals. In this behalf, it is pointed out that India has signed the Inter-Governmental Agreement (IGA) with USA on 9-7-2015, for Improving International Tax Compliance and implementing the Foreign Account Tax Compliance Act (FATCA). India has also signed a multilateral agreement on 3-6-2015, to automatically exchange information based on Article 6 of the Convention on Mutual Administrative Assistance in Tax Matters under the Common Reporting Scheme (CRS), formally referred to as the Standard for Automatic Exchange of Financial Account Information (AEoI).
As part of India’s commitment under FATCA and CRS, financial sector entities capture the details about the customers using the PAN. In case the PAN or submitted details are found to be incorrect or fictitious, it will create major embarrassment for the country. Under Non-filers Monitoring System (NMS), the Income Tax Department identifies non-filers with potential tax liabilities. Data analysis is carried out to identify non-filers about whom specific information was available in AIR, CIB data and TDS/TCS returns.
Email/SMS and letters are sent to the identified non-filers communicating the information summary and seeking to know the submission details of income tax return. In a large number of cases (more than 10 lakh PANs every year) it is seen that the PAN holder neither submits the response and in many cases the letters are return unserved. Field verification by field formations have found that in a large number of cases, the PAN holder is untraceable. In many cases, the PAN holder mentions that the transaction does not relate to them. There is a need to strengthen PAN by linking it with Aadhaar/biometric information to prevent use of wrong PAN for high value transactions.”
422) Adverting to the aspect of proportionality, here again there was a specific discussion in Binoy Viswam as this argument was raised, though in the context of Article 19 of the Constitution. The Court after explaining the doctrine of proportionality specifically held that proportionality test stood applied with. Following discussion in the said judgment would amply demonstrate this proposition:
“65. While monitoring the PILs relating to night shelters for the homeless and the right to food through the public distribution system, this Court has lauded and complimented the efforts of the State Governments for inter alia carrying out biometric identification of the head of family of each household to eliminate fictitious, bogus and ineligible BPL/AAY household cards.
xx xx xx
125.2. Menace of corruption and black money has reached alarming proportion in this country. It is eating into the economic progress which the country is otherwise achieving. It is not necessary to go into the various reasons for this menace. However, it would be pertinent to comment that even as per the observations of the Special Investigation Team (SIT) on black money headed by Justice M.B. Shah, one of the reasons is that persons have the option to quote their PAN or UID or passport number or driving licence or any other proof of identity while entering into financial/business transactions. Because of this multiple methods of giving proofs of identity, there is no mechanism/system at present to collect the data available with each of the independent proofs of ID.
For this reason, even SIT suggested that these databases be interconnected. To the same effect is the recommendation of the Committee headed by Chairman, CBDT on measures to tackle black money in India and abroad which also discusses the problem of money laundering being done to evade taxes under the garb of shell companies by the persons who hold multiple bogus PAN numbers under different names or variations of their names. That can be possible if one uniform proof of identity, namely, UID is adopted. It may go a long way to check and minimise the said malaise.
125.3. Thirdly, Aadhaar or UID, which has come to be known as the most advanced and sophisticated infrastructure, may facilitate law-enforcement agencies to take care of problem of terrorism to some extent and may also be helpful in checking the crime and also help investigating agencies in cracking the crimes. No doubt, going by the aforesaid, and may be some other similarly valid considerations, it is the intention of the Government to give fillip to Aadhaar movement and encourage the people of this country to enrol themselves under the Aadhaar Scheme.
126. Whether such a scheme should remain voluntary or it can be made mandatory imposing compulsiveness on the people to be covered by Aadhaar is a different question which shall be addressed at the appropriate stage. At this juncture, it is only emphasised that mala fides cannot be attributed to this scheme. In any case, we are concerned with the vires of Section 139-AA of the Income Tax Act, 1961 which is a statutory provision. This Court is, thus, dealing with the aspect of judicial review of legislation. Insofar as this provision is concerned, the explanation of the respondents in the counter-affidavit, which has already been reproduced above, is that the primary purpose of introducing this provision was to take care of the problem of multiple PAN cards obtained in fictitious names. Such multiple cards in fictitious names are obtained with the motive of indulging into money laundering, tax evasion, creation and channelising of black money.
It is mentioned that in de-duplication exercises, 11.35 lakh cases of duplicate PANs/fraudulent PANs have been detected. Out of these, around 10.52 lakhs pertain to the individual assessees. Parliament in its wisdom thought that one PAN to one person can be ensured by adopting Aadhaar for allotment of PAN to individuals. As of today, that is the only method available i.e. by seeding of existing PAN with Aadhaar. It is perceived as the best method, and the only robust method of de-duplication of PAN database. It is claimed by the respondents that the instance of duplicate Aadhaar is almost non-existent. It is also claimed that seeding of PAN with Aadhaar may contribute to widening of the tax case as well, by checking the tax evasions and bringing into tax hold those persons who are liable to pay tax but deliberately avoid doing so.”
423) It has been stated by the respondents, on affidavit, that analysis of Form 61/60 data using PAN Aadhaar linkage shows that a large number of PAN holders do not quote their PAN in the prescribed transactions to prevent linking of the transactions to the PAN. The analysis was performed by matching the Aadhaar number and person name reported in Form 61 (which was possible only due to linking of financial transactions/accounts with Aadhaar) with the Aadhaar and name of the entity available in the ITD PAN database (possible due to linking of PAN with Aadhaar).
This analysis identified 1.65 crore non-PAN transactions reported through Form 61 (relating to FY 2016-17 and FY 2017-18) where PAN of the transacting party was present in the PAN database and was not mentioned filing a wrong form deliberately. These transactions totalled to around Rs. 33,000 crore (based on transaction amount reported). This is the amount of undisclosed high value transaction which would have gone undetected had it not been for Aadhaar linkage. Similar matching has also helped populating PAN in 1.12 lakh non-PAN transactions reported under Statement of Financial Transactions (SFT). Majority of the non- PAN transactions reported are around Deposit in Cash, Investment in time deposit, Sale of immovable property, Purchase of immovable property and Opening an account (other than savings and time deposit). Thus, linking of PAN with Aadhaar will significantly enhance legitimate collection of country’s revenue.
424) Taking into account the aforesaid consideration as well as other factors mentioned above, we feel that there is a justifiable reason with the State for collection and storage of data in the form of Aadhaar and linking it with PAN insofar as Section 139AA of the Income Tax Act is concerned. We would like to reproduce para 311 of K.S. Puttaswamy judgment, which reads as under:
“311. Apart from national security, the State may have justifiable reasons for the collection and storage of data. In a social welfare State, the Government embarks upon programmes which provide benefits to impoverished and marginalised sections of society. There is a vital State interest in ensuring that scarce public resources are not dissipated by the diversion of resources to persons who do not qualify as recipients. Allocation of resources for human development is coupled with a legitimate concern that the utilisation of resources should not be siphoned away for extraneous purposes.
Data mining with the object of ensuring that resources are properly deployed to legitimate beneficiaries is a valid ground for the State to insist on the collection of authentic data. But, the data which the State has collected has to be utilised for legitimate purposes of the State and ought not to be utilised unauthorisedly for extraneous purposes. This will ensure that the legitimate concerns of the State are duly safeguarded while, at the same time, protecting privacy concerns. Prevention and investigation of crime and protection of the revenue are among the legitimate aims of the State. Digital platforms are a vital tool of ensuring good governance in a social welfare State. Information technology-legitimately deployed is a powerful enabler in the spread of innovation and knowledge.”
425) Following passages from Subramanian Swamy v. Union of India, Ministry of Law & Ors.154 may also be relevant in this behalf and the same are reproduced below:
“122. In State of Madras v. V.G. Row, the Court has ruled that the test of reasonableness, wherever prescribed, should be applied to each individual statute impugned and no abstract standard, or general pattern of reasonableness can be laid down as applicable to all cases. The nature of the right alleged to have been infringed, the underlying purpose of the restrictions imposed, the extent and urgency of the evil sought to be remedied thereby, the disproportion of the imposition, the prevailing conditions at the time, should all enter into the judicial verdict.
xx xx xx
130. The principles as regards reasonable restriction as has been stated by this Court from time to time are that the 154(2016) 7 SCC restriction should not be excessive and in public interest. The legislation should not invade the rights and should not smack of arbitrariness. The test of reasonableness cannot be determined by laying down any abstract standard or general pattern. It would depend upon the nature of the right which has been infringed or sought to be infringed. The ultimate “impact”, that is, effect on the right has to be determined. The “impact doctrine” or the principle of “inevitable effect” or “inevitable consequence” stands in contradistinction to abuse or misuse of a legislation or a statutory provision depending upon the circumstances of the case. The prevailing conditions of the time and the principles of proportionality of restraint are to be kept in mind by the court while adjudging the constitutionality of a provision regard being had to the nature of the right. The nature of social control which includes public interest has a role. The conception of social interest has to be borne in mind while considering reasonableness of the restriction imposed on a right. The social interest principle would include the felt needs of the society.
xx xx xx
194. Needless to emphasise that when a law limits a constitutional right which many laws do, such limitation is constitutional if it is proportional. The law imposing restriction is proportional if it is meant to achieve a proper purpose, and if the measures taken to achieve such a purpose are rationally connected to the purpose, and such measures are necessary. Such limitations should not be arbitrary or of an excessive nature beyond what is required in the interest of the public. Reasonableness is judged with reference to the objective which the legislation seeks to achieve, and must not be in excess of that objective (see P.P. Enterprisesv. Union of India). Further, the reasonableness is examined in an objective manner from the standpoint of the interest of the general public and not from the point of view of the person upon whom the restrictions are imposed or abstract considerations (see Mohd. Hanif Quareshi v. State of Bihar) On independent examination of the matter, the aforesaid exercise undertaken in the Binoy Viswam is hereby affirmed as we are in agreement therewith. We, thus, hold that the provisions of Section 139AA of the Income Tax Act, 1961 meet the triple test of right to privacy, contained in K.S. Puttaswamy.
Prevention of Money Laundering Rules:
426) The petitioners have challenged amendment to Rule 9 of the Prevention of Money Laundering (Maintenance of Records) Rules, 2005, (Rules, 2005) which was amended by Prevention of Money Laundering (Maintenance of Records) Seventh Amendment Rules, 2017. Rule 9 of the aforesaid Rules is amended by Second Amendment Rules, 2017 whereby following additions are made. The amendment reads as under:
“(b) in rule 9, for sub-rule (4) to sub-rule (9), the following sub-rules shall be substituted, namely:-
(4) Where the client is an individual, who is eligible to be enrolled for an Aadhaar number, he shall for the purpose of sub-rule (1) submit to the reporting entity,-
(a) the Aadhaar number issued by the Unique Identification Authority of India; and (b) the Permanent Account Number or Form No. 60 as defined in Income Tax Rules, 1962, and such other documents including in respect of the nature of business and financial status of the client as may be required by the reporting entity: Provided that where an Aadhaar number has not been assigned to a client, the client shall furnish proof of application of enrolment for Aadhaar and in case the Permanent Account Number is not submitted, one certified copy of an ‘officially valid document’ shall be submitted. Provided further that photograph need not be submitted by a client falling under clause (b) of sub-rule (1).
(4A) Where the client is an individual, who is not eligible to be enrolled for an Aadhaar number, he shall for the purpose of sub-rule (1), submit to the reporting entity, the Permanent Account Number or Form No. 60 as defined in the Income Tax Rules, 1962: Provided that if the client does not submit the Permanent Account Number, he shall submit one certified copy of an ‘officially valid document’ containing details of his identity and address, one recent photograph and such other documents including in respect of the nature or business and financial status of the client as may be required by the reporting entity.
(5) Notwithstanding anything contained in sub-rules (4) and (4A), an individual who desires to open a small account in a banking company may be allowed to open such an account on production of a self-attested photograph and affixation of signature or thumb print, as the case may be, on the form for opening the account:
Provided that-
(i) the designated officer of the banking company, while opening the small account, certifies under his signature that the person opening the account has affixed his signature or thumb print, as the case may be, in his presence;
(ii) the small account shall be opened only at Core Banking Solution linked banking company branches or in a branch where it is possible to manually monitor and ensure that foreign remittances are not credited to a small account and that the stipulated limits on monthly and annual aggregate of transactions and balance in such accounts are not breached, before a transaction is allowed to take place;
(iii) the small account shall remain operational initially for a period of twelve months, and thereafter for a further period of twelve months if the holder of such an account provides evidence before the banking company of having applied for any of the officially valid documents within twelve months of the opening of the said account, with the entire relaxation provisions to be reviewed in respect of the said account after twenty-four months;
(iv) the small account shall be monitored and when there is suspicion of money laundering or financing of terrorism or other high risk scenarios, the identity of client shall be established through the production of officially valid documents, as referred to in sub-rule (4) and the Aadhaar number of the client or where an Aadhaar number has not been assigned to the client, through the production of proof of application towards enrolment for Aadhaar along with an officially valid document; Provided further that if the client is not eligible to be enrolled for an Aadhaar number, the identity of client shall be established through the production of an officially valid document;
(v) the foreign remittance shall not be allowed to be credited into the small account unless the identity of the client is fully established through the production of officially valid documents, as referred to in sub-rule (4) and the Aadhaar number of the client or where an Aadhaar number has not been assigned to the client, through the production of proof of application towards enrolment for Aadhaar along with an officially valid document: Provided that if the client is not eligible to be enrolled for the Aadhaar number, the identity of client shall be established through the production of an officially valid document.
(6) Where the client is a company, it shall for the purposes of sub-rule (1), submit to the reporting entity the certified copies of the following documents:-
(i) Certificate of incorporation;
(ii) Memorandum and Articles of Association;
(iii) A resolution from the Board of Directors and power of attorney granted to its managers, officers or employees to transact on its behalf;
(iv)
(a) Aadhaar numbers; and
(b) Permanent Account Numbers or Form 60 as defined in the Income Tax Rules, 1962, issued to managers, officers or employees holding an attorney to transact on the company’s behalf or where an Aadhaar number has not been assigned, proof of application towards enrolment for Aadhaar and in case Permanent Account Number is not submitted an officially valid document shall be submitted: Provided that for the purpose of this clause if the managers, officers or employees holding an attorney to transact on the company’s behalf are not eligible to be enrolled for Aadhaar number and do not submit the Permanent Account Number, certified copy of an officially valid document shall be submitted. (7) Where the client is a partnership firm, it shall, for the purposes of sub-rule (1), submit to the reporting entity the certified copies of the following documents:-
(i) registration certificate;
(ii) partnership deed; and
(iii)
(a) Aadhaar number; and
(b) Permanent Account Number or Form 60 as defined in the Income Tax Rules, 1962, issued to the person holding an attorney to transact on its behalf or where an Aadhaar number has not been assigned, proof of application towards enrolment for Aadhaar and in case Permanent Account Number is not submitted an officially valid document shall be submitted: Provided that for the purpose of this clause, if the person holding an attorney to transact on the company’s behalf is not eligible to be enrolled for Aadhaar number and does not submit the Permanent Account Number, certified copy of an officially valid document shall be submitted.
(8) Where the client is a trust, it shall, for the purposes of sub-rule (1) submit to the reporting entity the certified copies of the following documents:-
(i) registration certificate;
(ii) trust deed; and
(iii)
(a) Aadhaar number; and
(b) Permanent Account Number or Form 60 as defined in the Income Tax Rules, 1962, issued to the person holding an attorney to transact on its behalf or where Aadhaar number has not been assigned, proof of application towards enrolment for Aadhaar and in case Permanent Account Number is not submitted an officially valid document shall be submitted: Provided that for the purpose of this clause if the person holding an attorney to transact on the company’s behalf is not eligible to be enrolled for Aadhaar number and does not submit the Permanent Account Number, certified copy of an officially valid document shall be submitted.
(9) Where the client is an unincorporated association or a body of individuals, it shall submit to the reporting entity the certified copies of the following documents:-
(i) resolution of the managing body of such association or body of individuals;
(ii) power of attorney granted to him to transact on its behalf;
(iii)
(a) the Aadhaar number; and
(b) Permanent Account Number or Form 60 as defined in the Income Tax Rules, 1962, issued to the person holding an attorney to transact on its behalf or where Aadhaar number has not been assigned, proof of application towards enrolment for Aadhaar and in case the Permanent Account Number is not submitted an officially valid document shall be submitted; and
(iv) such information as may be required by the reporting entity to collectively establish the legal existence of such an association or body of individuals: Provided that for the purpose of this clause if the person holding an attorney to transact on the company’s behalf is not eligible to be enrolled for Aadhaar number and does not submit the Permanent Account Number, certified copy of an officially valid document shall be submitted.”
(c) after sub-rule (14), the following sub-rules shall be inserted, namely,-
(15) Any reporting entity, at the time of receipt of the Aadhaar number under provisions of this rule, shall carry out authentication using either e-KYC authentication facility or Yes/No authentication facility provided by Unique Identification Authority of India.
(16) In case the client referred to in sub-rules (4) to (9) of rule 9 is not a resident or is a resident in the States of Jammu and Kashmir, Assam or Meghalaya and does not submit the Permanent Account Number, the client shall submit to the reporting entity one certified copy of officially valid document containing details of his identity and address, one recent photograph and such other document including in respect of the nature of business and financial status of the client as may be required by the reporting entity.
(17)
(a) In case the client, eligible to be enrolled for Aadhaar and obtain a Permanent Account Number, referred to in sub-rules (4) to (9) of rule 9 does not submit the Aadhaar number or the Permanent Account Number at the time of commencement of an account based relationship with a reporting entity, the client shall submit the same within a period of six months from the date of the commencement of the account based relationship: Provided that the clients, eligible to be enrolled for Aadhaar and obtain the Permanent Account Number, already having an account based relationship with reporting entities prior to date of this notification, the client shall submit the Aadhaar number and Permanent Account Number by 31st December, 2017.
(b) As per regulation 12 of the Aadhaar (Enrolment and Update) Regulations, 2016, the local authorities in the State Governments or Union-territory Administrations have become or are in the process of becoming UIDAI Registrars for Aadhaar enrolment and are organising special Aadhaar enrolment camps at convenient locations for providing enrolment facilities in consultation with UIDAI and any individual desirous of commencing an account based relationship as provided in this rule, who does not possess the Aadhaar number or has not yet enrolled for Aadhaar, may also visit such special Aadhaar enrolment camps for Aadhaar enrolment or any of the Aadhaar enrolment centres in the vicinity with existing registrars of UIDAI.
(c) In case the client fails to submit the Aadhaar number and Permanent Account Number within the aforesaid six months period, the said account shall cease to be operational till the time the Aadhaar number and Permanent Account Number is submitted by the client: Provided that in case client already having an account based relationship with reporting entities prior to date of this notification fails to submit the Aadhaar number and Permanent Account Number by 31st December, 2017, the said account shall cease to be operational till the time the Aadhaar number and Permanent Account Number is submitted by the client.
(18) In case the identity information relating to the Aadhaar number or Permanent Account Number submitted by the client referred to in sub-rules (4) to (9) of rule 9 does not have current address of the client, the client shall submit an officially valid documents to the reporting entity.” As can be seen from the above, linking of Aadhaar with the bank account is now mandatory. It applies not only to those bank accounts which would be opened after the bringing into force the amendment but even the existing accounts as well.
427) Linking of a banking account to Aadhaar is challenged as violative of Articles 14, 19(1)(g) and 21 of the Constitution and also of Prevention of Money Laundering Act, 2002. Elaborate submissions were made by Mr. Arvind Datar on the aforesaid aspects. It was argued that those persons who do not choose to enrol for Aadhaar number would not be in a position to open the bank account or even operate the existing bank account and there is no valid explanation as to why all bank accounts had to be authenticated. It was also argued that provisions of the Rule referred to companies, firms, trust etc. as well, though the Aadhaar Act is meant for establishing identity of individuals only.
It was further submitted that in case a person fails to link Aadhaar with the bank account, such person would be rendered ineligible to operate the bank account, which would amount to forfeiting her money lying in the account which belongs to her. This amounts to depriving the person from her property and is, therefore, violative of Article 300A of the Constitution as such a deprivation can take place only by primary legislation and not by subordinate legislation in the form of Rules. Much emphasis was also laid on the argument that the amended Rule does not pass the proportionality test.
428) Mr. Tushar Mehta, learned Additional Solicitor General, refuted the aforesaid submissions. He pointed out the objective with which the Prevention of Money Laundering Act was enacted, namely, to curb money laundering and black money, which is becoming a menace. Therefore, the amendment to Rules serves a legitimate State aim. He argued that the Rules are not arbitrary and satisfies the proportionality test also, having regard to the laudable objective which it seeks to serve.
429) After giving our thoughtful consideration to the various aspects, we feel that it is not even necessary to deal with each and every contention raised by the petitioners. Our considered opinion is that it does not meet the test of proportionality and is also violative of right to privacy of a person which extends to banking details.
430) This Court has held in Ram Jethmalani & Ors. v. Union of India & Ors.155 that revelation of bank details without prima facie ground of wrong doing would be violative of right to privacy. The said decision has been approved in K.S. Puttaswamy. Under the garb of prevention of money laundering or black money, there cannot be such a sweeping provision which targets every resident of the country as a suspicious person. Presumption of criminality is treated as disproportionate and arbitrary.
431) Nobody would keep black money in the bank account. We accept the possibility of opening an account in an assumed name and keeping black money therein which can be laundered as well. However, the persons doing such an Act, if at all, would be very few. More importantly, those having bank accounts with modest balance and routine transactions can be safely ruled out. Therefore, the provision in the present form does not meet the test of proportionality. Therefore, for checking this possible malice, there cannot be a mandatory provision for linking of every bank account.
432) In Lal Babu Hussein v. Electoral Registration Officer and Others156, this Court had struck down the order of the Electoral Officer asking the residents of a particular en masse to prove their identity as unconstitutional. The Court held that the Electoral officer asking residents of a particular area en masse to prove their identity was unconstitutional. In the case, the EO went on the assumption that all inhabitants of a particular area were foreigners, notwithstanding their name appearing in earlier electoral rolls. The court held the following:
(a) Right to vote cannot be disallowed by insisting only on 4 proofs of identity-voters can rely on any other proof of identity and obtain right to vote.
(b) Notices were quashed because they failed to distinguish between existing voters who had voted several times and new voters.
(c) Large-scale presumption of illegality impermissible.
433) This linking is made compulsory not only for opening a new bank account but even for existing bank accounts with a stipulation that if the same is not done then the account would be deactivated, with the result that the holder of the account would not be entitled to operate the bank account till the time seeding of the bank account with Aadhaar is done. This amounts to depriving a person of his property. We find that this move of mandatory linking of Aadhaar with bank account does not satisfy the test of proportionality. To recapitulate, the test of proportionality requires that a limitation of the fundamental rights must satisfy the following to be proportionate:
(i) it is designated for a proper purpose;
(ii) measures are undertaken to effectuate the limitation are rationally connected to the fulfilment of the purpose;
(iii) there are no alternative less invasive measures; and
(iv) there is a proper relation between the importance of achieving the aim and the importance of limiting the right.
434) The Rules are disproportionate for the following reasons:
(a) a mere ritualistic incantation of “money laundering”, “black money” does not satisfy the first test;
(b) no explanations have been given as to how mandatory linking of every bank account will eradicate/reduce the problems of “money laundering” and “black money”;
(c) there are alternative methods of KYC which the banks are already undertaking, the state has not discharged its burden as to why linking of Aadhaar is imperative. We may point out that RBI’s own Master Direction (KYC Direction, 2016) No. DBR.AML.BC. No. 81/14.01.001/2015-16 allows using alternatives to Aadhaar to open bank accounts.
435) There may be legitimate State aim for such a move as it aims at prevention of money laundering and black money. However, there has not been a serious thinking while making such a provision applicable for every bank account. Maintaining back account in today’s world has almost become a necessity. The Government itself has propagated the advantages thereof and is encouraging people to open the bank account making it possible to have one even with Zero Balance under the Pradhan Mantri Jan Dhan Yojana. The Government has taken various measures to give a boost to digital economy. Under these schemes, millions of persons, who are otherwise poor, are opening their bank accounts.
They are also becoming habitual to the good practice of entering into transactions through their banks and even by using digital modes for operation of the bank accounts. Making the requirement of Aadhaar compulsory for all such and other persons in the name of checking money laundering or black money is grossly disproportionate. There should have been a proper study about the methods adopted by persons who indulge in money laundering, kinds of bank accounts which such persons maintain and target those bank accounts for the purpose of Aadhaar. It has not been done.
436) We, thus, hold the amendment to Rule 9, by the Seventh Amendment Rules, 2017, in the present form, to be unconstitutional.
Linking of Mobile Number with Aadhaar
437) By a Circular dated March 23, 2017, the Department of Telecommunications has directed that all licensees shall reverify the existing mobile subscribers (pre-paid and post-paid) through Aadhaar based e-KYC process. In fine, it amounts to mandatory linking of mobile connections with Aadhaar, which requirement is not only in respect of those individuals who would be becoming mobile subscribers, but applies to existing subscribers as well.
438) It was the submission of the petitioners that such a linking of the SIM card with Aadhaar number violates their right to privacy. It is argued that since it is a fundamental right, the restrictions/curb thereupon in the form of said linking does not satisfy the tests laid down in K.S. Puttaswamy inasmuch as it is neither backed by any law nor it serves any legitimate state aim nor does it meet the requirement of proportionality test.
439) At the outset, it may be mentioned that the respondents have not been able to show any statutory provision which permits the respondents to issue such a circular. It is administrative in nature. The respondents have, however, tried to justify the same on the ground that there have been numerous instances where non-verification of SIM cards have posed serious security threats. Having regard to the same, this Court had given direction in Lokniti Foundation v. Union of India & Anr.157 for the linking of SIM card with Aadhaar and it is pursuant to those directions that the Telecom Regulatory Authority of India (TRAI) recommended this step.
Therefore, as per the respondents, Circular dated March 23, 2017 is the outcome of the aforesaid directions and recommendations which should be treated as backing of law. According to them, direction of this Court is a law under Article 141 of the Constitution. In addition, it is also argued that since Section 4 of the Indian Telegraph Act, 1885 empowers the Central Government to issue licenses for establishing, maintaining and working telegraphs, it is within the power of the Central Government to grant such licenses with condition and, therefore, Circular dated March 23, 2017 may be read as condition for grant of licenses.
On this premise, attempt is to show that the Circular is issued in exercise of the powers contained in Section 4 of the Indian Telegraph Act, 1885 which is the force of law.
440) In order to appreciate the respondents’ contentions, we reproduce the relevant portion of Circular dated March 23, 2017, which reads as under: “Hon’ble Supreme Court, in its order dated 06.02.2017 passed in Writ Petition (C) No. 607/2016 filed by Lokniti Foundation v/s Union of India, while taking into cognizance of “Aadhaar based e-KYC process for issuing new telephone connection” issued by the Department, has interalia observed that “an effective process has been evolved to ensure identity verification, as well as, the addresses of all mobile phone subscribers for new subscribers. In the near future, and more particularly, within one year from today, a similar verification will be completed, in case of existing subscribers.” This amounts to a direction which is to be completed within a time frame of one year.
2. A meeting was held on 13.02.2017 in the Department with the telecom industry wherein UIDAI, TRAI and PMO representatives also participated to discuss the way forward to implement the directions of Hon’ble Supreme Court. Detailed discussions and deliberations were held in the meeting. The suggestions received from the industry have been examined in the Department.
3. Accordingly, after taking into consideration the discussions held in the meeting and suggestions received from telecom industry, the undersigned is directed to convey the approval of competent authority that all Licensees shall re-verify all existing mobile subscribers (prepaid and postpaid) through Aadhaar based e-KYC process as mentioned in this office letter No. 800-29/2010- VAS dated 16.08.2016. The instructions mentioned in subsequent paragraphs shall be strictly followed while carrying out the re-verification exercise.”
441) In the first instance, it may be noticed that reference is made to the judgment of this Court in Lokniti Foundation which has prompted the Ministry of Communications to issue this circular. Paragraph 1 of the Circular itself states that the observations of the Court in Lokniti Foundation amount to a direction. Thus, the Circular is not issued in exercise of powers under Section 4 of the Indian Telegraph Act, 1885 (though that itself would be debatable as to whether Section 4 gives such a power at all). Insofar as observations of this Court in that case are concerned, it is clear that in the said brief order, this Court did not go into the issue as to whether linking of SIM card with Aadhaar would be violate of privacy rights of the citizens.
In that petition filed as a Public Interest Litigation, a prayer was made to the effect that identity of each subscriber and also the numbers should be verified so that unidentified and unverified subscribers are not allowed to misuse mobile numbers. In response, the Union of India had filed the counter affidavit bringing to the notice of the Court that the Department had launched Aadhaar based e-KYC for issuing mobile connections. Based on this statement, orders were passed by this Court. Lis, which is the subject matter of instant petitions, was not raised in the said case.
Obviously, the Court did not deliberate on the aspects of necessity of such a provision in the light of right to privacy. It was a case where both the sides were at ad idem. In the absence of any such issue or discussion thereupon, such a case cannot be treated as precedent and as a corollary it cannot be termed as ‘law’ within the meaning of Article 13 or Article 141 of the Constitution. Moreover, we are unable to read the order in Lokniti Foundation as a direction of the Court. It simply disposed of the petition after recording the submission of the Union of India to the effect that the grievance of the petitioner therein stood redressed by evolving the procedure of linking.
On that the Court simply observed that undertaking given to this Court will be seriously taken and given effect to. No doubt, the Central Government, as a licensor, can impose conditions while granting licenses under Section 4 of the Indian Telegraph Act, 1885. However, such directions/conditions have to be legally valid. When it affects the rights of the third parties (like the petitioners herein who are not party to the licenses granted by the Government to the Telecom Service Providers) they have a right to challenge such directions. Here, the case made out by the petitioners is that it infringes their right to privacy.
442) We are of the opinion that not only such a circular lacks backing of a law, it fails to meet the requirement of proportionality as well. It does not meet ‘necessity stage’ and ‘balancing stage’ tests to check the primary menace which is in the mind of the respondent authorities. There can be other appropriate laws and less intrusive alternatives. For the misuse of such SIM cards by a handful of persons, the entire population cannot be subjected to intrusion into their private lives. It also impinges upon the voluntary nature of the Aadhaar scheme. We find it to be disproportionate and unreasonable state compulsion. It is to be borne in mind that every individual/resident subscribing to a SIM card does not enjoy the subsidy benefit or services mentioned in Section 7 of the Act. We, therefore, have no hesitation in declaring the Circular dated March 23, 2017 as unconstitutional.
Violation of the orders passed by this Court:
Whether certain actions of the respondents are in contravention of the interim orders passed by the Court, if so, the effect thereof?
443) It was vehemently argued that this Court had passed number of interim orders (which have already been taken note of in the beginning of this judgment) categorically stating that the Aadhaar enrolment is voluntary; that no person would be forced to enrol under the scheme; that a person would be told about the voluntary nature of the scheme; and that enrolment shall not be given to any illegal migrant. As per the petitioners, notwithstanding these orders, the Central Government as well as the State Governments have issued various notifications requiring Aadhaar authentication for benefits, subsidies and schemes mandatory. In this manner, according to the petitioners, the respondents have violated the orders of this Court and it is the majesty of the Court which is at stake.
444) It is not in dispute that the aforesaid orders were passed when the Aadhaar Act had not come into force. After the enactment, Section 7 had altered the position statutorily. The notifications and circulars etc. are issued under this provision. Therefore, technically speaking, it cannot be held that these circulars are issued in contravention of the orders passed by this Court.
445) We feel that it would have been better had a clarification been obtained from the Court after the passing of the Aadhaar Act before issuing such circulars and orders under Section 7. When the matter is sub judice in the Court and certain orders operating, the respondents should have shown some fairness by taking that route, which expectation would be high where the respondent is the State. However, it would be difficult to hold the respondents in contempt of the orders passed by this Court. We may note that similar argument was advanced in Binoy Viswam, namely, insertion of Section 139AA in the Income Tax Act was in breach of interim orders passed by this Court. This argument was repelled in the following manner:
“99. Main emphasis, however, is on the plea that Parliament or any State Legislature cannot pass a law that overrules a judgment thereby nullifying the said decision, that too without removing the basis of the decision. This argument appears to be attractive inasmuch as few orders are passed by this Court in pending writ petitions which are to the effect that the enrolment of Aadhaar would be voluntary. However, it needs to be kept in mind that the orders have been passed in the petitions where Aadhaar Scheme floated as an executive/administrative measure has been challenged. In those cases, the said orders are not passed in a case where the Court was dealing with a statute passed by Parliament.
Further, these are interim orders as the Court was of the opinion that till the matter is decided finally in the context of right to privacy issue, the implementation of the said Aadhaar Scheme would remain voluntary. In fact, the main issue as to whether Aadhaar card scheme whereby biometric data of an individual is collected violates right to privacy and, therefore, is offensive of Article 21 of the Constitution or not is yet to be decided. In the process, the Constitution Bench is also called upon to decide as to whether right to privacy is a part of Article 21 of the Constitution at all.
Therefore, no final decision has been taken. In a situation like this, it cannot be said that Parliament is precluded from or it is rendered incompetent to pass such a law. That apart, the argument of the petitioners is that the basis on which the aforesaid orders are passed has to be removed, which is not done. According to the petitioners, it could be done only by making the Aadhaar Act compulsory. It is difficult to accept this contention for two reasons: first, when the orders passed by this Court which are relied upon by the petitioners were passed when the Aadhaar Act was not even enacted. Secondly, as already discussed in detail above, the Aadhaar Act and the law contained in Section 139-AA of the Income Tax Act deal with two different situations and operate in different fields. This argument of legislative incompetence also, therefore, fails.”
Summary and Conclusions:
446)
(a) The architecture and structure of the Aadhaar Act reveals that the UIDAI is established as a statutory body which is given the task of developing the policy, procedure and system for issuing Aadhaar numbers to individuals and also to perform authentication thereof as per the provisions of the Act. For the purpose of enrolment and assigning Aadhaar numbers, enrolling agencies are recruited by the Authority. All the residents in India are eligible to obtain an Aadhaar number. To enable a resident to get Aadhaar number, he is required to submit demographic as well as biometric information i.e., apart from giving information relating to name, date of birth and address, biometric information in the form of photograph, fingerprint, iris scan is also to be provided. Aadhaar number given to a particular person is treated as unique number as it cannot be reassigned to any other individual.
(b) Insofar as subsidies, benefits or services to be given by the Central Government or the State Government, as the case may be, is concerned, these Governments can mandate that receipt of these subsidies, benefits and services would be given only on furnishing proof of possession of Aadhaar number (or proof of making an application for enrolment, where Aadhaar number is not assigned). An added requirement is that such individual would undergo authentication at the time of receiving such benefits etc. A particular institution/body from which the aforesaid subsidy, benefit or service is to be claimed by such an individual, the intended recipient would submit his Aadhaar number and is also required to give her biometric information to that agency. On receiving this information and for the purpose of its authentication, the said agency, known as Requesting Entity (RE), would send the request to the Authority which shall perform the job of authentication of Aadhaar number. On confirming the identity of a person, the individual is entitled to receive subsidy, benefit or service. Aadhaar number is permitted to be used by the holder for other purposes as well.
(c) In this whole process, any resident seeking to obtain an Aadhaar number is, in the first instance, required to submit her demographic information and biometric information at the time of enrolment. She, thus, parts with her photograph, fingerprint and iris scan at that stage by giving the same to the enrolling agency, which may be a private body/person. Likewise, every time when such Aadhaar holder intends to receive a subsidy, benefit or service and goes to specified/designated agency or person for that purpose, she would be giving her biometric information to that RE, which, in turn, shall get the same authenticated from the Authority before providing a subsidy, benefit or service.
(d) Attack of the petitioners to the Aadhaar programme and its formation/structure under the Aadhaar Act is founded on the arguments that it is a grave risk to the rights and liberties of the citizens of this country which are secured by the Constitution of India. It militates against the constitutional abiding values and its foundational morality and has the potential to enable an intrusive state to become a surveillance state on the basis of information that is collected in respect of each individual by creation of a joint electronic mesh. In this manner, the Act strikes at the very privacy of each individual thereby offending the right to privacy which is elevated and given the status of fundamental right by tracing it to Articles 14, 19 and 21 of the Constitution of India by a nine Judge Bench judgment of this Court in K.S. Puttaswamy.
(e) The respondents, on the other hand, have attempted to shake the very foundation of the aforesaid structure of the petitioners’ case. They argue that in the first instance, minimal biometric information of the applicant, who intends to have Aadhaar number, is obtained which is also stored in CIDR for the purpose of authentication. Secondly, no other information is stored. It is emphasised that there is no data collection in respect of religion, caste, tribe, language records of entitlement, income or medical history of the applicant at the time of Aadhaar enrolment.
Thirdly, the Authority also claimed that the entire Aadhaar enrolment eco-system is foolproof inasmuch as within few seconds of the biometrics having been collected by the enrolling agency, the said information gets transmitted the Authorities/CIDR, that too in an encrypted form, and goes out of the reach of the enrolling agency. Same is the situation at the time of authentication as biometric information does not remain with the requesting agency. Fourthly, while undertaking the authentication process, the Authority simply matches the biometrics and no other information is received or stored in respect of purpose, location or nature or transaction etc. Therefore, the question of profiling does not arise at all.
(f) In the aforesaid scenario, it is necessary, in the first instance, to find out the extent of core information, biometric as well as demographic, that is collected and stored by the Authority at the time of enrolment as well as at the time of authentication. This exercise becomes necessary in order to consider the argument of the petitioners about the profiling of the Aadhaar holders. On going through this aspect, on the basis of the powerpoint presentation given by Dr. Ajay Bhushan Pandey, CEO of UIDAI, and the arguments of both the sides, including the questions which were put by the petitioners to Dr. Pandey and the answers thereupon, the Court has come to the conclusion that minimal possible data, demographic and biometric, is obtained from the Aadhaar holders.
(g) The Court also noticed that the whole architecture of Aadhaar is devised to give unique identity to the citizens of this country. No doubt, a person can have various documents on the basis of which that individual can establish her identify. It may be in the form of a passport, PAN card, ration card and so on. For the purpose of enrolment itself number of documents are prescribed which an individual can produce on the basis of which Aadhaar card can be issued. Thus, such documents, in a way, are also proof of identity. However, there is a fundamental difference between the Aadhaar card as a mean of identity and other documents through which identity can be established. Enrolment for Aadhaar card also requires giving of demographic information as well as biometric information which is in the form of iris and fingerprints.
This process eliminates any chance of duplication. It is emphasised that an individual can manipulate the system by having more than one or even number of PAN cards, passports, ration cards etc. When it comes to obtaining Aadhaar card, there is no possibility of obtaining duplicate card. Once the biometric information is stored and on that basis Aadhaar card is issued, it remains in the system with the Authority. Wherever there would be a second attempt for enrolling for Aadhaar and for this purpose same person gives his biometric information, it would be immediately get matched with the same biometric information already in the system and the second request would stand rejected. It is for this reason the Aadhaar card is known as Unique Identification (UID). Such an identity is unparalleled.
(h) There is, then, another purpose for having such a system of issuing unique identification cards in the form of Aadhaar card. A glimpse thereof is captured under the heading ‘Introduction’ above, while mentioning how and under what circumstances the whole project was conceptualised. To put it tersely, in addition to enabling any resident to obtain such unique identification proof, it is also to empower marginalised section of the society, particularly those who are illiterate and living in abject poverty or without any shelter etc. It gives identity to such persons also. Moreover, with the aid of Aadhaar card, they can claim various privileges and benefits etc. which are actually meant for these people.
(i) Identity of a person has a significance for every individual in his/her life. In a civilised society every individual, on taking birth, is given a name. Her place of birth and parentage also becomes important as she is known in the society and these demographic particulars also become important attribute of her personality. Throughout their lives, individuals are supposed to provide such information: be it admission in a school or college or at the time of taking job or engaging in any profession or business activity, etc. When all this information is available in one place, in the form of Aadhaar card, it not only becomes unique, it would also qualify as a document of empowerment. Added with this feature, when an individual knows that no other person can clone her, it assumes greater significance.
(j) Thus, the scheme by itself can be treated as laudable when it comes to enabling an individual to seek Aadhaar number, more so, when it is voluntary in nature. Howsoever benevolent the scheme may be, it has to pass the muster of constitutionality. According to the petitioners, the very architecture of Aadhaar is unconstitutional on various grounds.
(k) The Court has taken note of the heads of challenge of the Act, Scheme and certain Rules etc. and clarified that the matter is examined with objective examination of the issues on the touchstone of the constitutional provisions, keeping in mind the ethos of constitutional democracy, rule of law, human rights and other basic features of the Constitution. Discussing the scope of judicial review, the Court has accepted that apart from two grounds noticed in Binoy Viswam, on which legislative Act can be invalidated
[(a) the Legislature does not have competence to make the law; and
b) law made is in violation of fundamental rights or any other constitutional provision], another ground, namely, manifest arbitrariness, can also be the basis on which an Act can be invalidated. The issues are examined having regard to the aforesaid scope of judicial review.
(l) From the arguments raised by the petitioners and the grounds of challenge, it becomes clear that the main plank of challenge is that the Aadhaar project and the Aadhaar Act infringes right to privacy. Inbuilt in this right to privacy is the right to live with dignity, which is a postulate of right to privacy. In the process, discussion leads to the issue of proportionality, viz. whether measures taken under the Aadhaar Act satisfy the doctrine of proportionality.
(m) In view of the above, the Court discussed the contours of right to privacy, as laid down in K.S. Puttaswamy, principle of human dignity and doctrine of proportionality. After taking note of the discussion contained in different opinions of six Hon’ble Judges, it stands established, without any pale of doubt, that privacy has now been treated as part of fundamental right. The Court has held that, in no uncertain terms, that privacy has always been a natural right which given an individual freedom to exercise control over his or her personality. The judgment further affirms three aspects of the fundamental right to privacy, namely: (i) intrusion with an individual’s physical body, (ii) informational privacy and (iii) privacy of choice.
(n) As succinctly put by Nariman, J., first aspect involves the person himself/herself and guards a person’s rights relatable to his physical body thereby controlling the uncalled invasion by the State. Insofar as second aspect, namely, informational privacy is concerned, it does not deal with a person’s body but deals with a person’s mind. In this manner, it protects a person by giving her control over the dissemination of material that is personal to her and disallowing unauthorised use of such information by the State. Third aspect of privacy relates to individual’s autonomy by protecting her fundamental personal choices.
These aspects have functional connection and relationship with dignity. In this sense, privacy is a postulate of human dignity itself. Human dignity has a constitutional value and its significance is acknowledged by the Preamble. Further, by catena of judgments, human dignity is treated as fundamental right as a facet not only of Article 21, but that of right to equality (Article 14) and also part of bouquet of freedoms stipulated in Article 19. Therefore, privacy as a right is intrinsic of freedom, liberty and dignity. Viewed in this manner, one can trace positive and negative contents of privacy. The negative content restricts the State from committing an intrusion upon the life and personal liberty of a citizen. Its positive content imposes an obligation on the State to take all necessary measures to protect the privacy of the individual.
(o) In developing the aforesaid concepts, the Court has been receptive to the principles in international law and international instruments. It is a recognition of the fact that certain human rights cannot be confined within the bounds of geographical location of a nation but have universal application. In the process, the Court accepts the concept of universalisation of human rights, including the right to privacy as a human right and the good practices in developing and understanding such rights in other countries have been welcomed. In this hue, it can also be remarked that comparative law has played a very significant role in shaping the aforesaid judgment on privacy in Indian context, notwithstanding the fact that such comparative law has only persuasive value. The whole process of reasoning contained in different opinions of the Hon’ble Judges would, thus, reflect that the argument that it is difficult to precisely define the common denominator of privacy, was rejected. While doing so, the Court referred to various approaches to formulating privacy
(p) We have also remarked above, the taxonomy of privacy, namely, on the basis of ‘harms’, ‘interest’ and ‘aggregation of rights’. We have also discussed the scope of right to privacy with reference to the cases at hand and the circumstances in which such a right can be limited. In the process, we have also taken note of the passage from the judgment rendered by Nariman, J. in K.S. Puttaswamy stating the manner in which law has to be tested when it is challenged on the ground that it violates the fundamental right to privacy.
(q) One important comment which needs to be made at this stage relates to the standard of judicial review while examining the validity of a particular law that allegedly infringes right to privacy. The question is as to whether the Court is to apply ‘strict scrutiny’ standard or the ‘just, fair and reasonableness’ standard. In the privacy judgment, different observations are made by the different Hon’ble Judges and the aforesaid aspect is not determined authoritatively, may be for the reason that the Bench was deciding the reference on the issue as to whether right to privacy is a fundamental right or not and, in the process, it was called upon to decide the specific questions referred to it. This Court preferred to adopt a ‘just, fair and reasonableness’ standard which is in tune with the view expressed by majority of Judges in their opinion.
Even otherwise, this is in consonance with the judicial approach adopted by this Court while construing ‘reasonable restrictions’ that the State can impose in public interest, as provided in Article 19 of the Constitution. Insofar as principles of human dignity are concerned, the Court, after taking note of various judgments where this principle is adopted and elaborated, summed up the essential ingredients of dignity jurisprudence by noticing that the basic principle of dignity and freedom of the individual is an attribute of natural law which becomes the right of all individuals in a constitutional democracy. Dignity has a central normative role as well as constitutional value. This normative role is performed in three ways:
First, it becomes basis for constitutional rights;
Second, it serves as an interpretative principle for determining the scope of constitutional rights; and, Third, it determines the proportionality of a statute limiting a constitutional right. Thus, if an enactment puts limitation on a constitutional right and such limitation is disproportionate, such a statute can be held to be unconstitutional by applying the doctrine of proportionality.
(r) As per Dworkin, there are two principles about the concept of human dignity, First principle regards an ‘intrinsic value’ of every person, namely, every person has a special objective value which value is not only important to that person alone but success or failure of the lives of every person is important to all of us. It can also be described as self respect which represents the free will of the person, her capacity to think for herself and to control her own life. The second principle is that of ‘personal responsibility’, which means every person has the responsibility for success in her own life and, therefore, she must use her discretion regarding the way of life that will be successful from her point of view.
(s) Sum total of this exposition can be defined by explaining that as per the aforesaid view dignity is to be treated as ’empowerment’ which makes a triple demand in the name of ‘respect’ for human dignity, namely:
(i) respect for one’s capacity as an agent to make one’s own free choices;
(ii) respect for the choices so made; and
(iii) respect for one’s need to have a context and conditions in which one can operate as a source of free and informed choice.
(t) In the entire formulation of dignity right, ‘respect’ for an individual is the fulcrum, which is based on the principle of freedom and capacity to make choices and a good or just social order is one which respects dignity via assuring ‘contexts’ and ‘conditions’ as the ‘source of free and informed choice’. The aforesaid discourse on the concept of human dignity is from an individual point of view. That is the emphasis of the petitioners as well. That would be one side of the coin. A very important feature which the present case has brought into focus is another dimension of human dignity, namely, in the form of ‘common good’ or ‘public good’. Thus, our endeavour here is to give richer and more nuanced understanding to the concept of human dignity.
(u) We, therefore, have to keep in mind humanistic concept of Human Dignity which is to be accorded to a particular segment of the society and, in fact, a large segment. Their human dignity is based on the socio-economic rights that are read in to the Fundamental Rights as already discussed above. When we read socio-economic rights into human dignity, the community approach also assumes importance along with individualistic approach to human dignity. It has now been well recognised that at its core, human dignity contains three elements, namely, Intrinsic Value, Autonomy and Community Value. These are known as core values of human dignity. These three elements can assist in structuring legal reasoning and justifying judicial choices in ‘hard cases’.
(v) When it comes to dignity as a community value, it emphasises the role of the community in establishing collective goals and restrictions on individual freedoms and rights on behalf of a certain idea of good life. The relevant question here is in what circumstances and to what degree should these actions be regarded as legitimate in a constitutional democracy? The liberal predicament that the state must be neutral with regard to different conceptions of the good in a plural society is not incompatible, of course, with limitation resulting from the necessary coexistence of different views and potentially conflicting rights.
Such interferences, however, must be justified on grounds of a legitimate idea of justice, an “overlapping consensus”158 that can be shared by most individuals and groups. Whenever such tension arises, the task of balancing is to be achieved by the Courts. We would like to highlight one more significant feature which the issues involved in the present case bring about. It is the balancing of two facets of dignity of the same individual. Whereas, on the one hand, right of personal autonomy is a part of dignity (and right to privacy), another part of dignity of the same individual is to lead a dignified life as well (which is again a facet of Article 21 of the Constitution).
Therefore, in a scenario where the State is coming out with welfare schemes, which strive at giving dignified life in harmony with human dignity and in the process some aspect of autonomy is sacrificed, the balancing of the two becomes an important task which is to be achieved by the Courts. For, there cannot be undue intrusion into the autonomy on the pretext of conferment of economic benefits.
(w) In this way, the concept of human dignity has been widened to deal with the issues at hand. As far as doctrine of proportionality is concerned, after discussing the approaches that are adopted by the German Supreme Court and the Canadian Supreme Court, which are somewhat different from each other, this Court has applied the tests as laid down in Modern Dental College & Research Centre, which are approved in K.S. Puttaswamy as well. However, at the same time, a modification is done by focusing on the parameters set down of Bilchitz which are aimed at achieving a more ideal approach.
447) After stating the aforesaid manner in which different issues that arose are specified and discussed, these questions and conclusions thereupon are summarised below:
(1) Whether the Aadhaar Project creates or has tendency to create surveillance state and is, thus, unconstitutional on this ground? Incidental Issues:
(a) What is the magnitude of protection that need to be accorded to collection, storage and usage of biometric data?
(b) Whether the Aadhaar Act and Rules provide such protection, including in respect of data minimisation, purpose limitation, time period for data retention and data protection and security?
Answer:
(a) The architecture of Aadhaar as well as the provisions of the Aadhaar Act do not tend to create a surveillance state. This is ensured by the manner in which the Aadhaar project operates.
(b) We have recorded in detail the powerpoint presentation that was given by Dr. Ajay Bhushan Pandey, CEO of the Authority, which brings out the following salient features:
(i) During the enrolment process, minimal biometric data in the form of iris and fingerprints is collected. The Authority does not collect purpose, location or details of transaction. Thus, it is purpose blind. The information collected, as aforesaid, remains in silos. Merging of silos is prohibited. The requesting agency is provided answer only in ‘Yes’ or ‘No’ about the authentication of the person concerned. The authentication process is not exposed to the Internet world. Security measures, as per the provisions of Section 29(3) read with Section 38(g) as well as Regulation 17(1)(d) of the Authentication Regulations, are strictly followed and adhered to.
(ii) There are sufficient authentication security measures taken as well, as demonstrated in Slides 14, 28 and 29 of the presentation.
(iii) The Authority has sufficient defence mechanism, as explained in Slide 30. It has even taken appropriate protection measures as demonstrated in Slide 31.
(iv) There is an oversight by Technology and Architecture Review Board (TARB) and Security Review Committee.
(v) During authentication no information about the nature of transaction etc. is obtained.
(vi) The Authority has mandated use of Registered Devices (RD) for all authentication requests. With these, biometric data is signed within the device/RD service using the provider key to ensure it is indeed captured live. The device provider RD service encrypts the PID block before returning to the host application. This RD service encapsulates the biometric capture, signing and encryption of biometrics all within it. Therefore, introduction of RD in Aadhaar authentication system rules out any possibility of use of stored biometric and replay of biometrics captured from other source. Requesting entities are not legally allowed to store biometrics captured for Aadhaar authentication under Regulation 17(1)(a) of the Authentication Regulations.
(vii) The Authority gets the AUA code, ASA code, unique device code, registered device code used for authentication. It does not get any information related to the IP address or the GPS location from where authentication is performed as these parameters are not part of authentication (v2.0) and e-KYC (v2.1) API. The Authority would only know from which device the authentication has happened, through which AUA/ASA etc. It does not receive any information about at what location the authentication device is deployed, its IP address and its operator and the purpose of authentication. Further, the authority or any entity under its control is statutorily barred from collecting, keeping or maintaining any information about the purpose of authentication under Section 32(3) of the Aadhaar Act.
(c) After going through the Aadhaar structure, as demonstrated by the respondents in the powerpoint presentation from the provisions of the Aadhaar Act and the machinery which the Authority has created for data protection, we are of the view that it is very difficult to create profile of a person simply on the basis of biometric and demographic information stored in CIDR.
Insofar as authentication is concerned, the respondents rightly pointed out that there are sufficient safeguard mechanisms. To recapitulate, it was specifically submitted that there was security technologies in place (slide 28 of Dr. Pandey’s presentation), 24/7 security monitoring, data leak prevention, vulnerability management programme and independent audits (slide 29) as well as the Authority’s defence mechanism (slide 30). It was further pointed out that the Authority has taken appropriate pro-active protection measures, which included disaster recovery plan, data backup and availability and media response plan (slide 31). The respondents also pointed out that all security principles are followed inasmuch as:
(a) there is PKI-2048 encryption from the time of capture, meaning thereby, as soon as data is given at the time of enrolment, there is an end to end encryption thereof and it is transmitted to the Authority in encrypted form. The said encryption is almost foolproof and it is virtually impossible to decipher the same;
(b) adoption of best-in-class security standards and practices; and
(c) strong audit and traceability as well as fraud detection. Above all, there is an oversight of Technology and Architecture Review Board (TARB) and Security Review Committee. This Board and Committee consists of very high profiled officers. Therefore, the Act has endeavoured to provide safeguards.
(d) Insofar as use and protection of data is concerned, having regard to the principles enshrined in various cases, Indian and foreign, the matter is examined from the stand point of data minimisation, purpose limitation, time period for data retention, data protection and security (qua CIDR, requisite entities, enrolment agencies and Registrars, authentication service agency, hacking, biometric solution providers, substantive procedural or judicial safeguards). After discussing the aforesaid aspect with reference to certain provisions of the Aadhaar Act, we are of the view that apprehensions of the petitioners stand assuaged with the striking down or reading down or clarification of some of the provisions, namely:
(i) Authentication records are not to be kept beyond a period of six months, as stipulated in Regulation 27(1) of the Authentication Regulations. This provision which permits records to be archived for a period of five years is held to be bad in law.
(ii) Metabase relating to transaction, as provided in Regulation 26 of the aforesaid Regulations in the present form, is held to be impermissible, which needs suitable amendment.
(iii) Section 33(1) of the Aadhaar Act is read down by clarifying that an individual, whose information is sought to be released, shall be afforded an opportunity of hearing.
(iv) Insofar as Section 33(2) of the Act in the present form is concerned, the same is struck down.
(v) That portion of Section 57 of the Aadhaar Act which enables body corporate and individual to seek authentication is held to be unconstitutional.
(vi) We have also impressed upon the respondents, to bring out a robust data protection regime in the form of an enactment on the basis of Justice B.N. Srikrishna (Retd.) Committee Report with necessary modifications thereto as may be deemed appropriate.
(2) Whether the Aadhaar Act violates right to privacy and is unconstitutional on this ground?
Answer:
(a) After detailed discussion, it is held that all matters pertaining to an individual do not qualify as being an inherent part of right to privacy. Only those matters over which there would be a reasonable expectation of privacy are protected by Article 21. This can be discerned from the reading of Paras 297 to 307 of the judgment.
(b) The Court is also of the opinion that the triple test laid down in order to adjudge the reasonableness of the invasion to privacy has been made. The Aadhaar scheme is backed by the statute, i.e. the Aadhaar Act. It also serves legitimate State aim, which can be discerned from the Introduction to the Act as well as the Statement of Objects and Reasons which reflect that the aim in passing the Act was to ensure that social benefit schemes reach the deserving community.
The Court noted that the failure to establish identity of an individual has proved to be a major hindrance for successful implementation of those programmes as it was becoming difficult to ensure that subsidies, benefits and services reach the unintended beneficiaries in the absence of a credible system to authenticate identity of beneficiaries. The Statement of Objects and Reasons also discloses that over a period of time, the use of Aadhaar number has been increased manifold and, therefore, it is also necessary to take measures relating to ensuring security of the information provided by the individuals while enrolling for Aadhaar card.
(c) It may be highlighted that the petitioners are making their claim on the basis of dignity as a facet of right to privacy. On the other hand, Section 7 of the Aadhaar Act is aimed at offering subsidies, benefits or services to the marginalised section of the society for whom such welfare schemes have been formulated from time to time. That also becomes an aspect of social justice, which is the obligation of the State stipulated in Para IV of the Constitution. The rationale behind Section 7 lies in ensuring targeted delivery of services, benefits and subsidies which are funded from the Consolidated Fund of India.
In discharge of its solemn Constitutional obligation to enliven the Fundamental Rights of life and personal liberty (Article 21) to ensure Justice, Social, Political and Economic and to eliminate inequality (Article 14) with a view to ameliorate the lot of the poor and the Dalits, the Central Government has launched several welfare schemes.
Some such schemes are PDS, scholarships, mid day meals, LPG subsidies, etc. These schemes involve 3% percentage of the GDP and involve a huge amount of public money. Right to receive these benefits, from the point of view of those who deserve the same, has now attained the status of fundamental right based on the same concept of human dignity, which the petitioners seek to bank upon. The Constitution does not exist for a few or minority of the people of India, but “We the people”. The goals set out in the Preamble of the Constitution do not contemplate statism and do not seek to preserve justice, liberty, equality an fraternity for those who have the means and opportunity to ensure the exercise of inalienable rights for themselves.
These goals are predominantly or at least equally geared to “secure to all its citizens”, especially, to the downtrodden, poor and exploited, justice, liberty, equality and “to promote” fraternity assuring dignity. Interestingly, the State has come forward in recognising the rights of deprived section of the society to receive such benefits on the premise that it is their fundamental right to claim such benefits. It is acknowledged by the respondents that there is a paradigm shift in addressing the problem of security and eradicating extreme poverty and hunger. The shift is from the welfare approach to a right based approach. As a consequence, right of everyone to adequate food no more remains based on Directive Principles of State Policy (Art 47), though the said principles remain a source of inspiration. This entitlement has turned into a Constitutional fundamental right. This Constitutional obligation is reinforced by obligations under International Convention.
(d) Even the petitioners did not seriously question the purpose and bona fides of the Legislature enacting the law.
(e) The Court also finds that the Aadhaar Act meets the test of proportionality as the following components of proportionality stand satisfied:
(i) A measure restricting a right must have a legitimate goal (legitimate goal stage).
(ii) It must be a suitable means of furthering this goal (suitability or rationale connection stage).
(iii) There must not be any less restrictive but equally effective alternative (necessity stage).
(iv) The measure must not have a disproportionate impact on the right holder (balancing stage).
(f) In the process, the Court has taken note of various judgments pronounced by this Court pertaining to right to food, issuance of BPL Cards, LPG connections and LPG cylinders at minimal cost, old age and other kind of pensions to deserving persons, scholarships and implementation of MGNREGA scheme.
(g) The purpose behind these orders was to ensure that the deserving beneficiaries of the scheme are correctly identified and are able to receive the benefits under the said scheme, which is their entitlement. The orders also aimed at ensuring ‘good governance’ by bringing accountability and transparency in the distribution system with the pious aim in mind, namely, benefits actually reached those who are rural, poor and starving.
(h) All this satisfies the necessity stage test, particularly in the absence of any less restrictive but equally effective alternative.
(i) Insofar as balancing is concerned, the matter is examined at two levels:
(i) Whether, ‘legitimate state interest’ ensures ‘reasonable tailoring’? There is a minimal intrusion into the privacy and the law is narrowly framed to achieve the objective. Here the Act is to be tested on the ground that whether it is found on a balancing test that the social or public interest and the reasonableness of the restrictions outweigh the particular aspect of privacy, as claimed by the petitioners. This is the test we have applied in the instant case.
(ii) There needs to be balancing of two competing fundamental rights, right to privacy on the one hand and right to food, shelter and employment on the other hand. Axiomatically both the rights are founded on human dignity. At the same time, in the given context, two facets are in conflict with each other. The question here would be, when a person seeks to get the benefits of welfare schemes to which she is entitled to as a part of right to live life with dignity, whether her sacrifice to the right to privacy, is so invasive that it creates imbalance?
(j) In the process, sanctity of privacy in its functional relationship with dignity is kept in mind where it says that legitimate expectation of privacy may vary from intimate zone to the private zone and from the private to public arena. Reasonable expectation of privacy is also taken into consideration. The Court finds that as the information collected at the time of enrolment as well as authentication is minimal, balancing at the first level is met. Insofar as second level, namely, balancing of two competing fundamental rights is concerned, namely, dignity in the form of autonomy (informational privacy) and dignity in the form of assuring better living standards of the same individual, the Court has arrived at the conclusion that balancing at the second level is also met.
The detailed discussion in this behalf amply demonstrates that enrolment in Aadhaar of the unprivileged and marginalised section of the society, in order to avail the fruits of welfare schemes of the Government, actually amounts to empowering these persons. On the one hand, it gives such individuals their unique identity and, on the other hand, it also enables such individuals to avail the fruits of welfare schemes of the Government which are floated as socio-economic welfare measures to uplift such classes. In that sense, the scheme ensures dignity to such individuals.
This facet of dignity cannot be lost sight of and needs to be acknowledged. We are, by no means, accepting that when dignity in the form of economic welfare is given, the State is entitled to rob that person of his liberty. That can never be allowed. We are concerned with the balancing of the two facets of dignity. Here we find that the inroads into the privacy rights where these individuals are made to part with their biometric information, is minimal. It is coupled with the fact that there is no data collection on the movements of such individuals, when they avail benefits under Section 7 of the Act thereby ruling out the possibility of creating their profiles. In fact, this technology becomes a vital tool of ensuring good governance in a social welfare state. We, therefore, are of the opinion that the Aadhaar Act meets the test of balancing as well.
(k) Insofar as the argument based on probabilistic system of Aadhaar, leading to ‘exclusion’ is concerned, the Authority has claimed that biometric accuracy is 99.76% and the petitioners have also proceeded on that basis. In this scenario, if the Aadhaar project is shelved, 99.76% beneficiaries are going to suffer. Would it not lead to their exclusion? It will amount to throwing the baby out of hot water along with the water. In the name of 0.232% failure (which can in any case be remedied) should be revert to the pre-Aadhaar stage with a system of leakages, pilferages and corruption in the implementation of welfare schemes meant for marginalised section of the society, the full fruits thereof were not reaching to such people?
(l) The entire aim behind launching this programme is the ‘inclusion’ of the deserving persons who need to get such benefits. When it is serving much larger purpose by reaching hundreds of millions of deserving persons, it cannot be crucified on the unproven plea of exclusion of some. It is clarified that the Court is not trivialising the problem of exclusion if it is there. However, what we are emphasising is that remedy is to plug the loopholes rather than axe a project, aimed for the welfare of large section of the society. Obviously, in order to address the failures of authentication, the remedy is to adopt alternate methods for identifying such persons, after finding the causes of failure in their cases. We have chosen this path which leads to better equilibrium and have given necessary directions also in this behalf, viz:
(i) We have taken on record the statement of the learned Attorney General that no deserving person would be denied the benefit of a scheme on the failure of authentication.
(ii) We are also conscious of the situation where the formation of fingerprints may undergo change for various reasons. It may happen in the case of a child after she grows up; it may happen in the case of an individual who gets old; it may also happen because of damage to the fingers as a result of accident or some disease etc. or because of suffering of some kind of disability for whatever reason. Even iris test can fail due to certain reasons including blindness of a person. We again emphasise that no person rightfully entitled to the benefits shall be denied the same on such grounds. It would be appropriate if a suitable provision be made in the concerned regulations for establishing an identity by alternate means, in such situations.
(m) As far as subsidies, services and benefits are concerned, their scope is not to be unduly expanded thereby widening the net of Aadhaar, where it is not permitted otherwise. In this respect, it is held as under:
(i) ‘Benefits’ and ‘services’ as mentioned in Section 7 should be those which have the colour of some kind of subsidies etc., namely, welfare schemes of the Government whereby Government is doling out such benefits which are targeted at a particular deprived class.
(ii) It would cover only those ‘benefits’ etc. the expenditure thereof has to be drawn from the Consolidated Fund of India.
(iii) On that basis, CBSE, NEET, JEE, UGC etc. cannot make the requirement of Aadhaar mandatory as they are outside the purview of Section 7 and are not backed by any law.
(3) Whether children can be brought within the sweep of Sections 7 and 8 of the Aadhaar Act?
Answer:
(a) For the enrolment of children under the Aadhaar Act, it would be essential to have the consent of their parents/guardian.
(b) On attaining the age of majority, such children who are enrolled under Aadhaar with the consent of their parents, shall be given the option to exit from the Aadhaar project if they so choose in case they do not intend to avail the benefits of the scheme.
(c) Insofar as the school admission of children is concerned, requirement of Aadhaar would not be compulsory as it is neither a service nor subsidy. Further, having regard to the fact that a child between the age of 6 to 14 years has the fundamental right to education under Article 21A of the Constitution, school admission cannot be treated as ‘benefit’ as well.
(d) Benefits to children between 6 to 14 years under Sarv Shiksha Abhiyan, likewise, shall not require mandatory Aadhaar enrolment.
(e) For availing the benefits of other welfare schemes which are covered by Section 7 of the Aadhaar Act, though enrolment number can be insisted, it would be subject to the consent of the parents, as mentioned in (a) above.
(f) We also clarify that no child shall be denied benefit of any of these schemes if, for some reasons, she is not able to produce the Aadhaar number and the benefit shall be given by verifying the identity on the basis of any other documents. This we say having regard to the statement which was made by Mr. K.K. Venugopal, learned Attorney General for India, at the Bar.
(4) Whether the following provisions of the Aadhaar Act and Regulations suffer from the vice of unconstitutionality: (i) Sections 2(c) and 2(d) read with Section 32 (ii) Section 2(h) read with Section 10 of CIDR (iii) Section 2(l) read with Regulation 23 (iv) Section 2(v) (v) Section 3 (vi) Section 5 (vii) Section 6 (viii) Section 8 (ix) Section 9 (x) Sections 11 to 23 (xi) Sections 23 and 54 (xii) Section 23(2)(g) read with Chapter VI & VII – Regulations 27 to 32 (xiii) Section 29 (xiv) Section 33 (xv) Section 47 (xvi) Section 48 (xvii) Section 57 (xviii) Section 59
Answer:
(a) Section 2(d) which pertains to authentication records, such records would not include metadata as mentioned in Regulation 26(c) of the Aadhaar (Authentication) Regulations, 2016. Therefore, this provision in the present form is struck down. Liberty, however, is given to reframe the regulation, keeping in view the parameters stated by the Court.
(b) Insofar as Section 2(b) is concerned, which defines ‘resident’, the apprehension expressed by the petitioners was that it should not lead to giving Aadhaar card to illegal immigrants. We direct the respondent to take suitable measures to ensure that illegal immigrants are not able to take such benefits.
(c) Retention of data beyond the period of six months is impermissible. Therefore, Regulation 27 of Aadhaar (Authentication) Regulations, 2016 which provides archiving a data for a period of five years is struck down.
(d) Section 29 in fact imposes a restriction on sharing information and is, therefore, valid as it protects the interests of Aadhaar number holders. However, apprehension of the petitioners is that this provision entitles Government to share the information ‘for the purposes of as may be specified by regulations’. The Aadhaar (Sharing of Information) Regulations, 2016, as of now, do not contain any such provision. If a provision is made in the regulations which impinges upon the privacy rights of the Aadhaar card holders that can always be challenged.
(e) Section 33(1) of the Act prohibits disclosure of information, including identity information or authentication records, except when it is by an order of a court not inferior to that of a District Judge. We have held that this provision is to be read down with the clarification that an individual, whose information is sought to be released, shall be afforded an opportunity of hearing. If such an order is passed, in that eventuality, he shall also have right to challenge such an order passed by approaching the higher court. During the hearing before the concerned court, the said individual can always object to the disclosure of information on accepted grounds in law, including Article 20(3) of the Constitution or the privacy rights etc.
(f) Insofar as Section 33(2) is concerned, it is held that disclosure of information in the interest of national security cannot be faulted with. However, for determination of such an eventuality, an officer higher than the rank of a Joint Secretary should be given such a power. Further, in order to avoid any possible misuse, a Judicial Officer (preferably a sitting High Court Judge) should also be associated with. We may point out that such provisions of application of judicial mind for arriving at the conclusion that disclosure of information is in the interest of national security, are prevalent in some jurisdictions. In view thereof, Section 33(2) of the Act in the present form is struck down with liberty to enact a suitable provision on the lines suggested above.
(g) Insofar as Section 47 of the Act which provides for the cognizance of offence only on a complaint made by the Authority or any officer or person authorised by it is concerned, it needs a suitable amendment to include the provision for filing of such a complaint by an individual/victim as well whose right is violated.
(h) Insofar as Section 57 in the present form is concerned, it is susceptible to misuse inasmuch as:
(a) It can be used for establishing the identity of an individual ‘for any purpose’. We read down this provision to mean that such a purpose has to be backed by law. Further, whenever any such “law” is made, it would be subject to judicial scrutiny.
(b) Such purpose is not limited pursuant to any law alone but can be done pursuant to ‘any contract to this effect’ as well. This is clearly impermissible as a contractual provision is not backed by a law and, therefore, first requirement of proportionality test is not met.
(c) Apart from authorising the State, even ‘any body corporate or person’ is authorised to avail authentication services which can be on the basis of purported agreement between an individual and such body corporate or person. Even if we presume that legislature did not intend so, the impact of the aforesaid features would be to enable commercial exploitation of an individual biometric and demographic information by the private entities.
Thus, this part of the provision which enables body corporate and individuals also to seek authentication, that too on the basis of a contract between the individual and such body corporate or person, would impinge upon the right to privacy of such individuals. This part of the section, thus, is declared unconstitutional.
(i) Other provisions of Aadhaar Act are held to be valid, including Section 59 of the Act which, according to us, saves the pre-enactment period of Aadhaar project, i.e. from 2009-2016.
(5) Whether the Aadhaar Act defies the concept of Limited Government, Good Governance and Constitutional Trust? Answer: Aadhaar Act meets the concept of Limited Government, Good Governance and Constitutional Trust.
(6) Whether the Aadhaar Act could be passed as ‘Money Bill’ within the meaning of Article 110 of the Constitution? Answer:
(a) We do recognise the importance of Rajya Sabha (Upper House) in a bicameral system of the Parliament. The significance and relevance of the Upper House has been succinctly exemplified by this Court in Kuldip Nayar’s case. The Rajya Sabha, therefore, becomes an important institution signifying constitutional fedaralism. It is precisely for this reason that to enact any statute, the Bill has to be passed by both the Houses, namely, Lok Sabha as well as Rajya Sabha. It is the constitutional mandate. The only exception to the aforesaid Parliamentary norm is Article 110 of the Constitution of India. Having regard to this overall scheme of bicameralism enshrined in our Constitution, strict interpretation has to be accorded to Article 110. Keeping in view these principles, we have considered the arguments advanced by both the sides.
(b) The petitioners accept that Section 7 of the Aadhaar Act has the elements of ‘Money Bill’. The attack is on the premise that some other provisions, namely, clauses 23(2)(h), 54(2)(m) and 57 of the Bill (which corresponds to Sections 23(2)(h), 54(2)(m) and 57 of the Aadhaar Act) do not fall under any of the clauses of Article 110 of the Constitution and, therefore, Bill was not limited to only those subjects mentioned in Article 110. Insofar as Section 7 is concerned, it makes receipt of subsidy, benefit or service subject to establishing identity by the process of authentication under Aadhaar or furnish proof of Aadhaar etc. It is also very clearly declared in this provision that the expenditure incurred in respect of such a subsidy, benefit or service would be from the Consolidated Fund of India. It is also accepted by the petitioners that Section 7 is the main provision of the Act. In fact, introduction to the Act as well as Statement of Objects and Reasons very categorically record that the main purpose of Aadhaar Act is to ensure that such subsidies, benefits and services reach those categories of persons, for whom they are actually meant.
(c) As all these three kinds of welfare measures are sought to be extended to the marginalised section of society, a collective reading thereof would show that the purpose is to expand the coverage of all kinds of aid, support, grant, advantage, relief provisions, facility, utility or assistance which may be extended with the support of the Consolidated Fund of India with the objective of targeted delivery. It is also clear that various schemes which can be contemplated by the aforesaid provisions, relate to vulnerable and weaker section of the society. Whether the social justice scheme would involve a subsidy or a benefit or a service is merely a matter of the nature and extent of assistance and would depend upon the economic capacity of the State. Even where the state subsidizes in part, whether in cash or kind, the objective of emancipation of the poor remains the goal.
(d) The respondents are right in their submission that the expression subsidy, benefit or service ought to be understood in the context of targeted delivery to poorer and weaker sections of society. Its connotation ought not to be determined in the abstract. For as an abstraction one can visualize a subsidy being extended by Parliament to the King; by Government to the Corporations or Banks; etc. The nature of subsidy or benefit would not be the same when extended to the poor and downtrodden for producing those conditions without which they cannot live a life with dignity. That is the main function behind the Aadhaar Act and for this purpose, enrolment for Aadhaar number is prescribed in Chapter II which covers Sections 3 to 6. Residents are, thus, held entitled to obtain Aadhaar number. We may record here that such an enrolment is of voluntary nature.
However, it becomes compulsory for those who seeks to receive any subsidy, benefit or service under the welfare scheme of the Government expenditure whereof is to be met from the Consolidated Fund of India. It follows that authentication under Section 7 would be required as a condition for receipt of a subsidy, benefit or service only when such a subsidy, benefit or service is taken care of by Consolidated Fund of India. Therefore, Section 7 is the core provision of the Aadhaar Act and this provision satisfies the conditions of Article 110 of the Constitution. Upto this stage, there is no quarrel between the parties. (e) On examining of the other provisions pointed out by the petitioners in an attempt to take it out of the purview of Money Bill, we are of the view that those provisions are incidental in nature which have been made in the proper working of the Act. In any case, a part of Section 57 has already been declared unconstitutional. We, thus, hold that the Aadhaar Act is validly passed as a ‘Money Bill’.
(7) Whether Section 139AA of the Income Tax Act, 1961 is violative of right to privacy and is, therefore, unconstitutional? Answer: Validity of this provision was upheld in the case of Binoy Viswam by repelling the contentions based on Articles 14 and 19 of the Constitution. The question of privacy which, at that time, was traced to Article 21, was left open. The matter is reexamined on the touchstone of principles laid down in K.S. Puttaswamy. The matter has also been examined keeping in view that manifest arbitrariness is also a ground of challenge to the legislative enactment. Even after judging the matter in the context of permissible limits for invasion of privacy, namely:
(i) the existence of a law;
(ii) a ‘legitimate State interest’; and
(iii) such law should pass the ‘test of proportionality’, we come to the conclusion that all these tests are satisfied. In fact, there is specific discussion on these aspects in Binoy Viswam’s case as well.
(8) Whether Rule 9 of the Prevention of Money Laundering (Maintenance of Records) Rules, 2005 and the notifications issued thereunder which mandates linking of Aadhaar with bank accounts is unconstitutional?
Answer:
(a) We hold that the provision in the present form does not meet the test of proportionality and, therefore, violates the right to privacy of a person which extends to banking details.
(b) This linking is made compulsory not only for opening a new bank account but even for existing bank accounts with a stipulation that if the same is not done then the account would be deactivated, with the result that the holder of the account would not be entitled to operate the bank account till the time seeding of the bank account with Aadhaar is done. This amounts to depriving a person of his property. We find that this move of mandatory linking of Aadhaar with bank account does not satisfy the test of proportionality. To recapitulate, the test of proportionality requires that a limitation of the fundamental rights must satisfy the following to be proportionate:
(i) it is designated for a proper purpose;
(ii) measures are undertaken to effectuate the limitation are rationally connected to the fulfilment of the purpose;
(iii) there are no alternative less invasive measures; and
(iv) there is a proper relation between the importance of achieving the aim and the importance of limiting the right.
(c) The Rules are held to be disproportionate for the reasons stated in the main body of this Judgment.
(9) Whether Circular dated March 23, 2017 issued by the Department of Telecommunications mandating linking of mobile number with Aadhaar is illegal and unconstitutional?
Answer: Circular dated March 23, 2017 mandating linking of mobile number with Aadhaar is held to be illegal and unconstitutional as it is not backed by any law and is hereby quashed.
(10) Whether certain actions of the respondents are in contravention of the interim orders passed by the Court, if so, the effect thereof?
Answer: This question is answered in the negative. 448) In view of the aforesaid discussion and observations, the writ petitions, transferred cases, special leave petition, contempt petitions and all the pending applications stand disposed of.
………………………………………CJI. (DIPAK MISRA)
………………………………………J. (A.K. SIKRI)
………………………………………J. (A.M. KHANWILKAR)
NEW DELHI;
SEPTEMBER 26, 2018.
1 1954 SCR 1077
2 (2011) 14 SCC 331
3 (2010) 5 SC 318
4 (2010) 13 SCC 45
5 (2013) 2 SCC 705
6 (2017) 10 SCC 1
7 S/Shri Kapil Sibal, Gopal Subramaniam, P. Chidambaram, Shyam Divan, K.V. Viswanathan, Neeraj Kishan Kaul, C.U. Singh, Anand Grover, Sanjay R. Hegde, Arvind P. Datar, V. Giri, Rakesh Dwivedi, Jayant Bhushan, Sajan Poovayya, P.V. Surendra Nath, Senior Advocates, K.K. Venugopal, Attorney General for India, Tushar Mehta, Additional Solicitor General of India, Gopal Sankaranarayanan and Zoheb Hossain, Advocates.
8 Thiruvengadam, The Use of Foreign Law in Constitutional Cases in India and Singapore (2010)
9 Basheshar Nath v. Commissioner of Income Tax, Delhi and Rajasthan & Anr., 1959 Supp (1) SCR 528
10 Romesh Thappar v. State of Madras, 1950 SCR 594
11 Ex Parte Jackson, 96 US 727 (1878).
12 Lovell v. City of Griffin, 303 US 444 (1938).
13 Near v. Minnesota, 282 US 607 (1931) 717-18.
14 Bidie v. General Accident, Fire and Life Assurance Corporation (1948) 2 All ER 995, 998.
15 Towne v. Eisner, 245 US 418.
16 James v. Commonwealth of Australia, (1936) AC 578.
17 (1977) 4 SCC 471
18 (1977) 2 SCC 548
19 (1996) 1 SCC 742
20 (2017) 7 SCC 59
21 State of M.P. v. Rakesh Kohli, (2012) 6 SCC 312; Ashoka Kumar Thakur v. Union of India, (2008) 6 SCC 1
22 (1996) 3 SCC 709
23 (2016) 2 SCC 445
24 (2017) 9 SCC 1
25 (1996) 2 SCC 226
26 (1978) 1 SCC 248
27 There are few other incidental and ancillary issues raised by the petitioners as well, which we propose to discuss and deal with after answering these fundamental submissions.
28 (1975) 2 SCC 148
29 AIR 1963 SC 1295
30 See the analysis of this judgment by the Centre for Internet and Society, https://cisindia. org/internet-governance/blog/the-fundamental-right-to-privacy-an-analysis
31 Daniel Solove, Understanding Privacy, Cambridge, Massachusetts: Harvard University Press, 2008.
32 (2018) 5 SCC 1
33 See paras 72-79 of the judgment
34 (2014) 5 SCC 438
35 (2015) 6 SCC 702
36 (2016) 7 SCC 761
37 (2018) 5 SCC 1
38 (2011) 4 SCC 454
39 Rendered by Dipak Misra, CJI
40 Rendered by A.K. Sikri, J.
41 Ronald Dworkin, Taking Rights Seriously (A & C Black, 2013) 239.
42 Ronald Dworkin, Is Democracy Possible Here? Principles for a New Political Debate (Princeton University Press, 2006)
43 Harvard University Press, 2011.
44 Kenneth W. Simons, “Dworkin’s Two Principle of Dignity: An Unsatisfactory Non- Consequentialist Account of Interpersonal Moral Duties”, 90 Boston Law Rev. 715 (2010)]
45 Footnote 33 above.
46 Footnote 32 above.
47 published in the European Journal of International Law on September 01, 2008
48 See George Kateb, Human Dignity 5 (2011) (“[W]e can distinguish between the dignity of every human individual and the dignity of the human species as a whole.”).
49 See John Donne, XVII. Mediation, in Devotions upon Emergent Occasions 107, 108-09 (Uyniv. of Mich. Press 1959) (1624)
50 “Overlapping consensus” is a term coined by John Rawls that identifies basic ideas of justice that can be shared by supporters of different religious, political, and moral comprehensive doctrines.
51 (2016) 7 SCC 353
52 Robert Alexy, A Theory of Constitutional Rights, (Oxford, Oxford University Press, 2002)
53 M Kumm, ‘The Idea of Socratic Contestation and the Right to Justification:
The Point and Purpose of Rights-Based Proportionality Review’ (2010) 4 Law & Ethics of Human Rights 141; M Kumm, ‘Institutionalising Socratic Contestation: The Rationalist Human Rights Paradigm, Legitimate Authority and the point of Judicial Review’ (2007) 1 European Journal of Legal Studies.
54 K Moller, The Global Model of Constitutional Rights (Oxford, Oxford University Press, 2012).
55 On this issue there is a detailed discussion in M Kumm, ‘Political Liberalism and the Structure of Rights: On the Place and Limits of the Proportionality Requirement’ in Pavlakos (ed), Law, Rights and Discourse:
The Legal Philosophy of Robert Alexy (Oxford, Hart Publishing, 2007) 131; Moller, the Global Model of Constitutional Rights (Oxford, Oxford University Press, 2012) ch 7.
56 As a proposal of how to deal with uncertainty, see Alexy’s ‘Second Law of Balancing’, which he proposes in the Postscript to A Theory of Constitutional Rights (Oxford, Oxford University Press, 2002).
57 (1986) 1 SCR 103
58 ‘Necessity and Proportionality: Towards A Balanced Approach?’, Hart Publishing, Oxford and Portland, Oregon, 2016.
59 On the various problems which the Canadian Supreme Court created for itself because of its early unfortunate statements on proportionality see S Choudhry, ‘So What Is the Real Legacy of Oakes? Two Decades of Proportionality Analysis under the Canadian Charter’s Section 1’ (2006) 34 Supreme Court Law Review 501.
60 (2010) 7 SCC 263
61 (1964) 1 SCR 332
62 (2005) 1 SCC 496
63 132 S.Ct. 945 (2012)
64 (2015) Application No. 47143/2006
65 [2014] All ER (D)
66 (Apr) 66 (2008) ECHR 1581
67 We may also take on record responsible statements of the learned Attorney General and Mr. Dwivedi who appeared for UIDAI that no State would be interested in any mass surveillance of 1.2 Billion people of the country or even the overwhelming majority of officers and employees or professionals.
The very idea of mass surveillance by State which pursues what an ANH does all the time and based on Aadhaar is an absurdity and an impossibility. According to them, the petitioners submission is based on too many imaginary possibilities, viz.:
(i) Aadhaar makes it possible for the State to obtain identity information of all ANH. It is possible that UIDAI would share identity information/authentication records in CIDR notwithstanding statutory prohibition and punitive injunctions in the Act. It is possible that the State would unleash its investigators to surveil a sizeable section of the ANH, if not all based on the authentication records. It is submitted that given the architecture of the Aadhaar Act, there are no such possibilities and in any event, submission based on imaginary possibility do not provide any basis for questioning the validity of Aadhaar Act.
(ii) None of the writ petitions set forth specific facts and even allegations that any Aadhaar number holder is being subjected to
surveillance by UIDAI or the Union/States. The emphasis during the argument was only on the possibility of surveillance based on electronic track trails and authentication records. It was asserted that there are tools in the market for track back. The entire case was speculative and conjectural. In Clapper, Director of National Intelligence v. Amnesty International USA, the majority judgment did not approve the submissions in the context of Foreign Intelligence Surveillance Act and one of the reason was that the allegations were conjectural and speculative.
There were no facts pleaded on the basis of which the asserted threat could be fairly traced to. However, we have not deliberated on this argument.
68 A challenge to the Aadhaar project for violation of IT Act and Rules has been filed in the Delhi High Court in the matter of Shamnad Basheer v UIDAI and Ors. Therefore, we are not dealing with this aspect, nor does it arise for consideration in these proceedings.
69 Regulation (EU) 2016/679 of the European Parliament and of the Council of 27 April 2016 on the protection of natural persons with regard to the processing of personal data and on the free movement of such data, and repealing Directive 95/46/EC (General Data Protection Regulation)
70 Regulation (EU) 2016/679 of the European Parliament and of the Council of 27 April 2016 on the protection of natural persons with regard to the processing of personal data and on the free movement of such data, and repealing Directive 95/46/EC (General Data Protection Regulation)
71 S and Marper v. United Kingdom [2008] ECHR 1581
72 Digital Rights Ireland Ltd v Minister for Communication, Marine and Natural Resources [2014] All ER (D) 66 (Apr)
73 Tele2 Sverige AB v. Post-och telestyrelsen and Secretary of State for the Home Department v. Tom Watson, Peter Brice, Geoffrey Lewis, Joined Cases C-203/15 and C-698/15, 2016
74 2.03. 2010, 1 BvR 256 / 08 , 1 BvR 263 / 08 , 1 BvR 586 / 08
75 [2016] 2 W.L.R. 873
76 Eur. Ct. H.R. 2016
77 See paragraphs 320 to 322
78 (2013) 6 SCC 620
79 “Report of the Group of Experts on Privacy” (16 October, 2012), Government of India, available at http://planningcommission.nic.in/reports/genrep/rep_privacy.pdf
80 (1975) 2 SCC 148
81 (2010) 6 SCC 614
82 (2002) ZACC 22
83 Writ Petition (Civil) No. 215 of 2005
84 497 US 361 (1990)
85 (2011) 14 SCC 331
86 (2017) 7 SCC 59
87 (2013) 6 SCC 670
88 (2017) 7 SCC 59
89 (1973) 4 SCC 225
90 (2001) 5 Scale 303
91 Civil Appeal No. 6626-6675 of 2001
92 Writ Petition (Civil) No. 265 of 2006, judgment delivered on April 10, 2008. 93 The challenge made in the case related to ‘Other Backward Classes’ rather than the Scheduled Castes or Tribes.
94 (1996) 4 SCC 37
95 (1992) 3 SCC 666
96 (1993) 1 SCC 645
97 1985 SCR Supl. (2) 51
98 (1981) 2 SCR 516
99 389 U.S. 347
100 442 US 735
101 (2010) 1 WLR 123
102 (2000) ZACC 19
103 App. No. 45603/05 decided on 18.06.2009
104(2003) 4 SCC 399
105 515 US 646 (1995)
106 (2016) 7 SCC 221
107 (2007) 15 SCC 49
108 India acceded to the UN Convention on the Rights of the Child in December 1992 to reiterate its commitment to the cause of the children.
109 (2008) 3 WLR 1360
110 (2014) 5 SCC 409
111 (1997) 1 SCC 301
112 (1997) 1 SCC 556
113 (2014) 9 SCC 772
114(1986) 1 SCR 103
115 Quebec Ass’n of Protestant Sch. Bds. v. Quebec (A.G.), (1984) 2 SCR 66
116(1998) 1 SCR 493
117(1992) 2 SCR 731
118 (1985) 1 SCR 295
119 See Nicholas Emiliou, The Principle of Proportionality in European Law: A comparative Study 5 (Kluwer Law Int’l. 1996).
120 Om Kumar & Ors. v. Union of India, (2001) 2 SCC 386 where R. v. Oakes was referred to and relied upon; Teri Oat Estates (P) Ltd. v. U.T., Chandigarh & Ors., (2004) 2 SCC 130 where the Court stressed upon maintaining a proper balance between adverse effect which the legislation or the administrative order may have on the rights, liberties or interests of persons keeping in mind the purpose which they were intended to serve; Modern Dental College and Research Centre and K.S. Puttaswamy amongst others.
121 Vernonia School District v. Wayne Acton, 515 US 646, 132 L.Ed. 2D 564, Board of Education of Independent School District v. Lindsay Earls, 536 US 822=153 L.Ed.2d. 735.
122 (1963) 2 SCR 747
123 (1966) 2 SCR 158
124 (1969) 1 SCC 248
125 (2017) 3 SCC 362
126 (1967) 2 SCR 454
127 (1975) 2 SCC 148
128 (1987) 1 SCC 124
129 (1991) 4 SCC 699
130 (2007) 2 SCC 1
131 (2011) 7 SCC 547
132 (1980) 3 SCC 625
133 (1973) 4 SCC 225
134 H.M. Seervai, Constitutional Law of India: A Critical Commentary (N.M. Tripathi Private Limited, Bombay, 4th Ed., Vol. 2, 1993) at pages 1928-1937.
135 (2014) 9 SCC 1
136 (2014) 9 SCC 1
137 (2018) SCC Online SC 661
138 Dipak Misra, CJI
139 Published in The Indian Express on July 16, 2018.
140 (1991) Supp. 2 SCC 608
141 (1993) Supp. 3 SCC 97
142 (1991) 4 SCC 699
143 (1994) 3 SCC 1
144 (2007) 3 SCC 184
145 (2010) 4 SCC 1
146 (1992) Supp. 2 SCC 651
147 (2006) 7 SCC 1
148 (2014) 11 SCC 415
149 (2016) 3 SCC 183
150 Mangalore Ganesh Beedi Works v. State of Mysore & Anr., 1963 Supp (1) SCR 275; Ramdas Athawale v. Union of India & Ors., (2010) 4 SCC 1, and; M.S.M. Sharma v. Dr. Shree Krishna Sinha & Ors., AIR 1960 SC 1186
151 AIR 1963 Pat 16
152 (1969) 1 SCR 478
153 A.S. Krishna v. State of Madras, (1957) SCR 399; Union of India & Ors. v. Shah Goverdhan L. Kabra Teachers’ College, (2002) 8 SCC 228, and; P.N. Krishna Lal & Ors. v. Government of Kerala & Anr., 1995 Supp (2) SCC 187
154 (2016) 7 SCC 221
155 (2011) 8 SCC 1
156 (1995) 3 SCC 100
157 (2017) 7 SCC 155
158 “Overlapping consensus” is a term coined by John Rawls that identifies basic ideas of justice that can be shared by supporters of different religious, political, and moral comprehensive doctrines.
![]()
Justice K S Puttaswamy (Retd) & ANR Vs. Union of India & Ors.
[Writ Petition (Civil) No 494 of 2012] See below
INDEX
|
A |
|
Introduction: technology, governance and freedom |
|
B |
|
The Puttaswamy1 principles |
|
|
B.I |
Origins: privacy as a natural right |
|
|
B.2 |
Privacy as a constitutionally protected right : liberty and dignity |
|
|
B.3 |
Contours of privacy |
|
|
B.4 |
Informational privacy |
|
|
B.5 |
Restricting the right to privacy |
|
|
B.6 |
Legitimate state interests |
|
C |
|
Submissions |
|
|
C.I |
Petitioners’ submissions |
|
|
C.2 |
Respondents’ submissions |
|
D |
|
Architecture of Aadhaar: analysis of the legal framework |
|
E |
|
Passage of Aadhaar Act as a Money Bill |
|
|
E.I |
Judicial Review of the Speaker’s Decision |
|
|
E.2 |
Aadhaar Act as a Money Bill |
|
F |
|
Biometrics, Privacy and Aadhaar |
|
|
F.I |
Increased use of biometric technology |
|
|
F.2 |
Consent in the collection of biometric data |
|
|
F.3 |
Position before the Aadhaar legislation |
|
|
F.4 |
Privacy Concerns in the Aadhaar Act |
|
|
1. |
Consent during enrolment and authentication & the right to access information under the Aadhaar Act |
|
|
2. |
Extent of information disclosed during authentication & sharing of core biometric information |
|
|
3. |
Expansive scope of biometric information |
|
|
4. |
Other concerns regarding the Aadhaar Act: Misconceptions regarding the efficacy of biometric information |
|
|
5. |
No access to biometric records in database |
|
|
6. |
Biometric locking |
|
|
7. |
Key takeaways |
|
G |
|
Legitimate state aim |
|
|
G.I |
Directive Principles |
|
|
G.2 |
Development and freedom |
|
|
G.3 |
Identity and Identification |
|
H |
|
Proportionality |
|
|
H.I |
Harmonising conflicting rights |
|
|
H.2 |
Proportionality standard in Indian jurisprudence |
|
|
H.3 |
Comparative jurisprudence |
|
|
H.4 |
Aadhaar: The proportionality analysis |
|
|
H.5 |
Dignity and financial exclusion |
|
|
H.6 |
Constitutional validity of Section 139AA of the Income Tax Act 1961 |
|
|
H.7 |
Linking of SIM cards and Aadhaar numbers |
|
I |
|
Money laundering rules |
|
J |
|
Savings in Section 59 |
|
K |
|
Rule of law and violation of interim orders |
|
L |
|
Conclusion |
Dr Dhananjaya Y Chandrachud, J
A Introduction: technology, governance and freedom
1 Technology and biometrics are recent entrants to litigation. Individually, each presents specific claims: of technology as the great enabler; and of biometrics as the unique identifier. As recombinant elements, they create as it were, new genetic material. Combined together, they present unforeseen challenges for governance in a digital age. Part of the reason for these challenges is that our law evolved in a radically different age and time. The law evolved instruments of governance in incremental stages. They were suited to the social, political and economic context of the time. The forms of expression which the law codified were developed when paper was ubiquitous. The limits of paper allowed for a certain freedom: the freedom of individuality and the liberty of being obscure. Governance with paper could lapse into governance on paper. Technology has become a universal language which straddles culture and language. It confronts institutions of governance with new problems. Many of them have no ready answers.
2 Technology questions the assumptions which underlie our processes of reasoning. It reshapes the dialogue between citizens and the state. Above all, it tests the limits of the doctrines which democracies have evolved as a shield which preserves the sanctity of the individual.
3 In understanding the interface between governance, technology and freedom, this case will set the course for the future. Our decision must address the dialogue between technology and power. The decision will analyse the extent to which technology has reconfigured the role of the state and has the potential to reset the lines which mark off no-fly zones: areas where the sanctity of the individual is inviolable. Our path will define our commitment to limited government. Technology confronts the future of freedom itself.
4 Granville Austin, the eminent scholar of the Indian Constitution had prescient comments on the philosophy of the Indian Constitution. He found it in three strands:
“The Constitution…may be summarized as having three strands: protecting and enhancing national unity and integrity; establishing the institutions and spirit of democracy; and fostering a social revolution to better the mass of Indians…the three strands are mutually dependent and inextricably intertwined. Social revolution could not be sought or gained at the expense of democracy. Nor could India be truly democratic unless the social revolution had to establish a just society. Without national unity, democracy would be endangered and there would be little progress toward social and economic reform. And without democracy and reform, the nation would not hold together. With these three strands, the framers had spun a seamless web. Undue strain on, or slackness in any one strand would distort the web and risk its destruction and, with it, the destruction of the nation. Maintaining harmony between the strands predictably would present those who later work the Constitution with great difficulties…”2 These three strands are much like the polycentric web of which Lon Fuller has spoken.3 A pull on one strand shakes the balance between the others. The equilibrium between them preserves the equilibrium of the Constitution.
5 This Court has been tasked with adjudicating on the constitutional validity of the Aadhaar project. The difficulties that Granville Austin had predicted would arise in harmonising the strands of the “seamless web” are manifested in the present case. This case speaks to the need to harmonise the commitment to social welfare while safeguarding the fundamental values of a liberal constitutional democracy.
6 To usher in a social revolution, India espoused the framework of a welfare state. The Directive Principles are its allies. The state is mandated to promote the welfare of its citizens by securing and protecting as effectively as possible a social order in which there is social, economic and political justice. Government plays a vital role in the social and economic upliftment of the nation’s citizenry by espousing equitable distribution of resources and creating equal opportunities. These are ideals that are meant to guide and govern State action. The State’s commitment to improve welfare is manifested through the measures and programmes which it pursues.
7 The Constitution of India incorporated a charter of human freedoms in Part III and a vision of transformative governance in Part IV. Through its rights jurisprudence, this Court has attempted to safeguard the rights in Part III and to impart enforceability to at least some of the Part IV rights by reading them into the former, as intrinsic to a constitutionally protected right to dignity. The Directive Principles are a reminder of the positive duties which the state has to its citizens. While social welfare is a foundational value, the Constitution is the protector of fundamental human rights. In subserving both those ideals, it has weaved a liberal political order where individual rights and freedoms are at the heart of a democratic society. The Constitution seeks to fulfil its liberal values by protecting equality, dignity, privacy, autonomy, expression and other freedoms.
8 Two recent books have explored the complexities of human identity. In “The Lies That Bind: Rethinking Identity”4, Kwame Anthony Appiah states that a liberal constitutional democracy is not a fate but a project. He draws inspiration from the Roman playwright Terence who observes: “I am human. I think nothing human alien to me.” Francis Fukuyama, on the other hand has a distinct nuance about identity. In “Identity: The Demand for Dignity and the Politics of Enlightenment5, he writes about how nations can facilitate “integrative national identities” based on liberal democratic values. Reviewing the books, Anand Giridharadas noted that Fukuyama’s sense of identity is
“large enough to be inclusive but small enough to give people a real sense of agency over their society.”6. Appiah and Fukuyama present two variants – for Appiah it has a cosmopolitan and global nature while it is more integrated with a nation state, for Fukuyama, though firmly rooted in a liberal constitutional order.
9 India has participated in and benefited from the reconfiguring of technology by the global community. We live in an age of information and are witness to a technological revolution that pervades almost every aspect of our lives. Redundancies and obsolescence are as ubiquitous as technology itself. Technology is a great enabler. Technology can be harnessed by the State in furthering access to justice and fostering good governance.
10 In an age symbolised by an information revolution, society is witnessing a shift to a knowledge economy7. In a knowledge economy, growth is dependent on the ‘quantity, quality, and accessibility’8 of information. The quest for digital India must nonetheless be cognisant of the digital divide. Access confronts serious impediments. Large swathes of the population have little or no access to the internet or to the resources required for access to information. With the growth of the knowledge economy, our constitutional jurisprudence has expanded privacy rights. A digital nation must not submerge 11 the identities of a digitised citizen. While data is the new oil, it still eludes the life of the average citizen. If access to welfare entitlements is tagged to unique data sets, skewed access to informational resources should not lead to perpetuating the pre-existing inequalities of access to public resources. An identification project that involves the collection of the biometric and demographic information of 1.3 billion people9, creating the largest biometric identity project in the world, must be scrutinized carefully to assess its compliance with human rights.
11 Empowered by the technology that accompanied the advent of the information age, the Aadhaar project was envisioned and born. The project is a centralised nation-wide identification system based on biometric technology. It aims to be a game changer in the delivery of welfare benefits through the use of technology. The project seeks to facilitate de-duplication, prevent revenue leakages and ensure a more cost and time efficient procedure for identification. Conceptualised on the use of biometrics and authentication, the Aadhaar identity card was originally introduced as a matter of voluntary choice. It was made a requirement for state subsidies and benefits for which, expenses are incurred from the Consolidated Fund of India. It was later expanded to become necessary to avail of a host of other services. The project is multifaceted and expansive. Perhaps no similar national identity program exists in the world. The Aadhaar project has multifarious aspects, all of which have been the subject of a detailed challenge by the Petitioners. They have been met with an equally strong defence from the government, which has argued that the programme is indispensable to curb corruption, fraud and black money.
12 The Aadhaar project raises two crucial questions: First, are there competing interests between human rights and ‘welfare furthering technology’ in democratic societies? Can technologies which are held out to bring opportunities for growth, also violate fundamental human freedoms? Second, if the answer to the first is in the affirmative, how should the balance be struck between these competing interests?
13 Efficiency is a significant facet of institutional governance. But efficiencies can compromise dignity. When efficiency becomes a universal mantra to steam-roll fundamental freedoms, there is a danger of a society crossing the line which divides democracy from authoritarian cultures. At the heart of the grounds on which the Aadhaar project has been challenged, lies the issue of power. Our Constitution is a transformative document in many ways. One of them is in defining and limiting the State’s powers, while expanding the ambit of individual rights and liberties. It protects citizens from totalitarian excesses and establishes order between the organs of the State, between the State and citizens and between citizens. Most importantly, it reaffirms the position of the individual as the core defining element of the polity. That is the justification to restrain power by empowering all citizens to be authors of their destiny. According to the Petitioners, the technological potential as well as the actual implementation of the Aadhaar project alters the balance between the state and its citizens in this relational sphere and has the potential to permanently redistribute power within the constitutional framework.
14 As far as citizen-state relations are concerned, the Constitution was framed to balance the rights of the individual against legitimate State interests. Being transformative, it has to be interpreted to meet the needs of a changing society. As the interpreter of the Constitution, it is the duty of this Court to be vigilant against State action that threatens to upset the fine balance between the power of the state and rights of citizens and to safeguard the liberties that inhere in our citizens.
15 The present case involves issues that travel to the heart of our constitutional structure as a democracy governed by the rule of law. Among them is the scope of this Court’s power of judicial review. The Aadhaar legislation was passed as a money bill in the Lok Sabha. Whether it was permissible, in constitutional terms, to by-pass the Rajya Sabha, is the question. The role of the Rajya Sabha in a bicameral legislative structure, the limits of executive power when it affects fundamental rights and the duty of the state to abide by interim orders of this Court are matters which will fall for analysis in the case.
16 The case is hence as much about the rule of law and institutional governance. Accountability is a key facet of the rule of law. Professor Upendra Baxi has remarked: “The problem of human rights, in situations of mass poverty, is thus one of redistribution, access and needs. In other words, it is a problem of “development”, a process of planned social change through continuing exercise of public power.
As there is no assurance that public power will always, or even in most cases, be exercised in favour of the deprived and dispossessed, an important conception of development itself is accountability, by the wielders of public power, to the people affected by it and people at large. Accountability is the medium through which we can strike and maintain a balance between the governors and the governed.”10 These are some of the unique challenges of this case. They must be analysed in the context of our constitutional framework. The all-encompassing nature of the Aadhaar project, its magnitude and the resultant impact on citizens’ fundamental rights, make it imperative to closely scrutinize the structure and effect of the project. For this will determine the future of freedom.
B The Puttaswamy11 principles
17 A unanimous verdict by a nine judge Bench declared privacy to be constitutionally protected, as a facet of liberty, dignity and individual autonomy. In a voluminous judgment, the Court traced the origins of privacy and its content. The decision lays down the test of proportionality to evaluate the constitutional validity of restrictions on the right to privacy.
18 The protection of privacy emerges both from its status as a natural right inhering in every individual as well as its position as “a constitutionally protected right”. As a constitutional protection, privacy traces itself to the guarantee of life and personal liberty in Article 21 of the Constitution as well as to other facets of freedom and dignity recognized and guaranteed by the fundamental rights contained in Part III.
B.I Origins: privacy as a natural right
19 Puttaswamy holds that the right to privacy inheres in every individual as a natural right. It is inalienable and attaches to every individual as a precondition for being able to exercise their freedom. The judgment of four judges (with which Justice Sanjay Kishan Kaul concurred) held :
“42. Privacy is a concomitant of the right of the individual to exercise control over his or her personality. It finds an origin in the notion that there are certain rights which are natural to or inherent in a human being. Natural rights are inalienable because they are inseparable from the human personality.”
(Emphasis supplied)
“319. Life and personal liberty are not creations of the Constitution. These rights are recognised by the Constitution as inhering in each individual as an intrinsic and inseparable part of the human element which dwells within.”13
(Emphasis supplied)
In his concurring opinion, S A Bobde, J. opined:
“392…Privacy, with which we are here concerned, eminently qualifies as an inalienable natural right, intimately connected to two values whose protection is a matter of universal moral agreement: the innate dignity and autonomy of man.”14
(Emphasis supplied)
Similarly, in his concurring opinion, Nariman, J. opined:
“532…It was, therefore, argued before us that given the international conventions referred to hereinabove and the fact that this right inheres in every individual by virtue of his being a human being, such right is not conferred by the Constitution but is only recognized and given the status of being fundamental. There is no doubt that the petitioners are correct in this submission.”
(Emphasis supplied)
In his concurring opinion, Abhay Manohar Sapre, J. opined:
“557. In my considered opinion, “right to privacy of any individual” is essentially a natural right, which inheres in every human being by birth…It is indeed inseparable and inalienable from human being.”16
(Emphasis supplied)
The judgment authoritatively settles the position. While privacy is recognized and protected by the Constitution as an intrinsic and inseparable part of life, liberty and dignity, it inheres in every individual as a natural right.
B.2 Privacy as a constitutionally protected right : liberty and dignity
20 The judgment placed the individual at the centre of the constitutional rights regime. The individual lies at the core of constitutional focus. The ideals of justice, liberty, equality and fraternity animate the vision of securing a dignified existence to the individual. The Court held that privacy attaches to the person and not the place where it is associated. Holding that privacy protects the autonomy of the individual and the right to make choices, the judgment of four judges held:
“108….The individual is the focal point of the Constitution because it is in the realisation of individual rights that the collective well being of the community is determined. Human dignity is an integral part of the Constitution.17 “266. Our Constitution places the individual at the forefront of its focus, guaranteeing civil and political rights in Part III and embodying an aspiration for achieving socio-economic rights in Part IV.”
(Emphasis supplied)
It was held that privacy rests in every individual “irrespective of social class or economic status” and that every person is entitled to the intimacy and autonomy that privacy protects:
“271…It is privacy as an intrinsic and core feature of life and personal liberty which enables an individual to stand up against a programme of forced sterilization. Then again, it is privacy which is a powerful guarantee if the State were to introduce compulsory drug trials of non-consenting men or women. The sanctity of marriage, the liberty of procreation, the choice of a family life and the dignity of being are matters which concern every individual irrespective of social strata or economic well being. The pursuit of happiness is founded upon autonomy and dignity. Both are essential attributes of privacy which makes no distinction between the birth marks of individuals.”18
(Emphasis supplied)
21 Recognizing that civil-political rights are not subservient to socioeconomic rights, the Court held that “conditions necessary for realizing or fulfilling socio-economic rights do not postulate the subversion of political freedom.”
“266…The refrain that the poor need no civil and political rights and are concerned only with economic well-being has been utilised through history to wreak the most egregious violations of human rights. Above all, it must be realised that it is the right to question, the right to scrutinize and the right to dissent which enables an informed citizenry to scrutinize the actions of government. Those who are governed are entitled to question those who govern, about the discharge of their constitutional duties including in the provision of socioeconomic welfare benefits. The power to scrutinize and to reason enables the citizens of a democratic polity to make informed decisions on basic issues which govern their rights.19
267… Conditions of freedom and a vibrant assertion of civil and political rights promote a constant review of the justness of socio-economic programmes and of their effectiveness in addressing deprivation and want. Scrutiny of public affairs is founded upon the existence of freedom. Hence civil and political rights and socio-economic rights are complementary and not mutually exclusive.”20 Significantly, the Court rejected the submission that there is a conflict between civil-political rights and socio-economic rights. Both in the view of the Court are an integral part of the constitutional vision of justice.
22 Privacy, it was held, reflects the right of the individual to exercise control over his or her personality. This makes privacy the heart of human dignity and liberty. Liberty and dignity are complementary constitutional entities. Privacy was held to be integral to liberty. Privacy facilitates the realization of constitutional freedoms. This Court held thus:
“119. To live is to live with dignity. The draftsmen of the Constitution defined their vision of the society in which constitutional values would be attained by emphasising, among other freedoms, liberty and dignity. So fundamental is dignity that it permeates the core of the rights guaranteed to the individual by Part III. Dignity is the core which unites the fundamental rights because the fundamental rights seek to achieve for each individual the dignity of existence. Privacy with its attendant values assures dignity to the individual and it is only when life can be enjoyed with dignity can liberty be of true substance. Privacy ensures the fulfilment of dignity and is a core value which the protection of life and liberty is intended to achieve.”21
127…The right to privacy is an element of human dignity. The sanctity of privacy lies in its functional relationship with dignity. Privacy ensures that a human being can lead a life of dignity by securing the inner recesses of the human personality from unwanted intrusion. Privacy recognises the autonomy of the individual and the right of every person to make essential choices which affect the course of life. In doing so privacy recognises that living a life of dignity is essential for a human being to fulfil the liberties and freedoms which are the cornerstone of the Constitution.”22 The assurance of human dignity enhances the quality of life. The “functional relationship” between privacy and dignity secures the “inner recesses of the human personality from unwanted intrusion”. Privacy by recognizing the autonomy of an individual, protects the right to make choices essential to a dignified life. It thus enables the realization of constitutional liberties and freedoms. It was held in the judgment:
“322. Privacy is the constitutional core of human dignity. Privacy has both a normative and descriptive function. At a normative level privacy sub-serves those eternal values upon which the guarantees of life, liberty and freedom are founded. At a descriptive level, privacy postulates a bundle of entitlements and interests which lie at the foundation of ordered liberty.23
298…Dignity cannot exist without privacy. Both reside within the inalienable values of life, liberty and freedom which the Constitution has recognised. Privacy is the ultimate expression of the sanctity of the individual. It is a constitutional value which straddles across the spectrum of fundamental rights and protects for the individual a zone of choice and self-determination.”24
24 Privacy is founded on the autonomy of the individual. The ability to make choices is at the core of the human personality. Its inviolable nature is manifested in the ability to make intimate decisions about oneself with a legitimate expectation of privacy. Privacy guarantees constitutional protection to all aspects of personhood. Privacy was held to be an “essential condition” for the exercise of most freedoms. As such, given that privacy and liberty are intertwined, privacy is necessary for the exercise of liberty. Bobde J, in his separate opinion held that:
“409…Liberty and privacy are integrally connected in a way that privacy is often the basic condition necessary for exercise of the right of personal liberty. There are innumerable activities which are virtually incapable of being performed at all and in many cases with dignity unless an individual is left alone or is otherwise empowered to ensure his or her privacy.25
411… Both dignity and privacy are intimately intertwined and are natural conditions for the birth and death of individuals, and for many significant events in life between these events. Necessarily, then, the right of privacy is an integral part of both ‘life’ and ‘personal liberty’ under Article 21, and is intended to enable the rights bearer to develop her potential to the fullest extent made possible only in consonance with the constitutional values expressed in the Preamble as well as across Part III.”26
25 Apart from being a natural law right, the right to privacy was held to be a constitutionally protected right flowing from Article 21. Privacy is an indispensable element of the right to life and personal liberty under Article 21 and as a constitutional value which is embodied in the fundamental freedoms embedded in Part III of the Constitution. Tracing out the course of precedent in Indian jurisprudence over the last four decades, the view of four judges holds:
“103. The right to privacy has been traced in the decisions which have been rendered over more than four decades to the guarantee of life and personal liberty in Article 21 and the freedoms set out in Article 19.”27 “320. Privacy is a constitutionally protected right which emerges primarily from the guarantee of life and personal liberty in Article 21 of the Constitution…”28 In a similar vein, Chelameswar J. while concurring with the view of four judges held:
“375. The right to privacy is certainly one of the core freedoms which is to be defended. It is part of liberty within the meaning of that expression in Article 21.”29
26 Being indispensable to dignity and liberty, and essential to the exercise of freedoms aimed at the self-realization of every individual, privacy was held to be a common theme running across the freedoms and rights guaranteed not just by Article 21, but all of Part III of the Constitution. Bobde J. in his separate opinion held that:
“406. It is not possible to truncate or isolate the basic freedom to do an activity in seclusion from the freedom to do the activity itself. The right to claim a basic condition like privacy in which guaranteed fundamental rights can be exercised must itself be regarded as a fundamental right. Privacy, thus, constitutes the basic, irreducible condition necessary for the exercise of ‘personal liberty’ and freedoms guaranteed by the Constitution. It is the inarticulate major premise in Part III of the Constitution.30
415. Privacy is the necessary condition precedent to the enjoyment of any of the guarantees in Part III. As a result, when it is claimed by rights bearers before constitutional courts, a right to privacy may be situated not only in Article 21, but also simultaneously in any of the other guarantees in Part III. In the current state of things, Articles 19(1), 20(3), 25, 28 and 29 are all rights helped up and made meaningful by the exercise of privacy.”
(Emphasis supplied)
B.3 Contours of privacy
27 Privacy has been held to have distinct connotations including
(i) spatial control;
(ii) decisional autonomy; and
(iii) informational control. The judgment of four judges held that:
“248. Spatial control denotes the creation of private spaces. Decisional autonomy comprehends intimate personal choices such as those governing reproduction as well as choices expressed in public such as faith or modes of dress. Informational control empowers the individual to use privacy as a shield to retain personal control over information pertaining to the person.” Similarly, Nariman J. in his separate opinion held:
“521. In the Indian context, a fundamental right to privacy would cover at least the following three aspects:
Privacy that involves the person i.e. when there is some invasion by the State of a person’s rights relatable to his physical body, such as the right to move freely;
Informational privacy which does not deal with a person’s body but deals with a person’s mind, and therefore recognizes that an individual may have control over the dissemination of material that is personal to him. Unauthorised use of such information may, therefore lead to infringement of this right; and
The privacy of choice, which protects an individual’s autonomy over fundamental personal choices.”31
28 However, it was held that this is not an exhaustive formulation of entitlements. In recording its conclusions, the opinion of four judges held:
“324. This Court has not embarked upon an exhaustive enumeration or a catalogue of entitlements or interests comprised in the right to privacy. The Constitution must evolve with the felt necessities of time to meet the challenges thrown up in a democratic order governed by the rule of law. The meaning of the Constitution cannot be frozen on the perspectives present when it was adopted. Technological change has given rise to concerns which were not present seven decades ago and the rapid growth of technology may render obsolescent many notions of the present. Hence the interpretation of the Constitution must be resilient and flexible to allow future generations to adapt its content bearing in mind its basic or essential features.”32
(Emphasis supplied)
Additionally, Bobde J., in his separate opinion held that the right to privacy may also inhere in other parts of the Constitution beyond those specified in the judgment:
“415. Therefore, privacy is the necessary condition precedent to the enjoyment of any of the guarantees in Part III. As a result, when it is claimed by rights bearers before constitutional courts, a right to privacy may be situated not only in Article 21, but also simultaneously in any of the other guarantees in Part III. In the current state of things, Articles 19(1), 20(3), 25, 28 and 29 are all rights helped up and made meaningful by the exercise of privacy. This is not an exhaustive list. Future developments in technology and social ordering may well reveal that there are yet more constitutional sites in which a privacy right inheres that are not at present evident to us.”33
(Emphasis supplied)
B.4 Informational privacy
29 Puttaswamy held that informational privacy is an essential aspect of the fundamental right to privacy. It protects an individual’s free, personal conception of the ‘self.’ Justice Nariman held that informational privacy “deals with a person’s mind, and therefore recognizes that an individual may have control over the dissemination of material that is personal to him”. Any unauthorised use of such information may therefore lead to infringement of the right to privacy. In his concurring judgment, Justice Kaul held that informational privacy provides the right to an individual “to disseminate certain personal information for limited purposes alone”. Kaul J. in his separate opinion held:
“620…The boundaries that people establish from others in society are not only physical but also informational. There are different kinds of boundaries in respect to different relations. Privacy assists in preventing awkward social situations and reducing social frictions. Most of the information about individuals can fall under the phrase “none of your business”. … An individual has the right to control one’s life while submitting personal data for various facilities and services. It is but essential that the individual knows as to what the data is being used for with the ability to correct and amend it. The hallmark of freedom in a democracy is having the autonomy and control over our lives which becomes impossible, if important decisions are made in secret without our awareness or participation.”34
(Emphasis supplied)
30 A reasonable expectation of privacy requires that data collection does not violate the autonomy of an individual. The judgment of four judges noted the centrality of consent in a data protection regime. This was also highlighted in the separate concurring opinion of Justice Kaul:
“625. Every individual should have a right to be able to exercise control over his/her own life and image as portrayed to the world and to control commercial use of his/her identity. This also means that an individual may be permitted to prevent others from using his image, name and other aspects of his/her personal life and identity for commercial purposes without his/her consent.”35 Consent, transparency and control over information are crucial to informational privacy. In this structure, Court has principally focused on the “individual” as central to our jurisprudence.
B.5 Restricting the right to privacy
31 There is an inherent importance of giving a constitutional status to privacy. Justice Nariman dealt with this:
“490…The recognition of such right in the fundamental rights chapter of the Constitution is only a recognition that such right exists notwithstanding the shifting sands of majority governments. Statutes may protect fundamental rights; they may also infringe them. In case any existing statute or any statute to be made in the future is an infringement of the inalienable right to privacy, this Court would then be required to test such statute against such fundamental right and if it is found that there is an infringement of such right, without any countervailing societal or public interest, it would be the duty of this Court to declare such legislation to be void as offending the fundamental right to privacy.”36 A constitutional right may embody positive and negative ‘aspects’.
They signify mandates. At an affirmative level, they emphasise the content and diversity of our liberties. As a ‘negative’, they impose restraints on the state and limit the power of the state to intrude upon the area of personal freedom. ‘Negative’ in this sense reflects a restraint: the fundamental rights are a restraining influence on the authority of power. In addition to keeping itself within the bounds of its authority, the state may have a positive obligation to perform. Rights such as informational privacy and data protection mandate that the state must bring into being a viable legal regime which recognizes, respects, protects and enforces informational privacy. Informational privacy requires the state to protect it by adopting positive steps to safeguard its cluster of entitlements.
The right to informational privacy is not only vertical (asserted and protected against state actors) but horizontal as well. Informational privacy requires legal protection because the individual cannot be left to an unregulated market place. Access to and exploitation of individual personal data – whether by state or non-state entities – must be governed by a legal regime built around the principles of consent, transparency and individual control over data at all times. 32 Privacy, being an intrinsic component of the right to life and personal liberty, it was held that the limitations which operate on those rights, under Article 21, would operate on the right to privacy. Any restriction on the right to privacy would therefore be subjected to strict constitutional scrutiny. The constitutional requirements for testing the validity of any encroachment on privacy were dealt with in the judgment as follows:
“325… In the context of Article 21 an invasion of privacy must be justified on the basis of a law which stipulates a procedure which is fair, just and reasonable. The law must also be valid with reference to the encroachment on life and personal liberty under Article 21. An invasion of life or personal liberty must meet the three-fold requirement of
(i) legality, which postulates the existence of law;
(ii) need, defined in terms of a legitimate state aim; and
(iii) proportionality which ensures a rational nexus between the objects and the means adopted to achieve them.”37 These three-fold requirements emerge from the procedural and content-based mandate of Article 21. The first requirement is the enactment of a valid law, which justifies an encroachment on privacy. The second requirement of a legitimate State aim ensures that the law enacted to restrict privacy is constitutionally reasonable and does not suffer from manifest arbitrariness. The third requirement of proportionality ensures that the nature and quality of the encroachment on the right to privacy is not disproportionate to the purpose of the law. Proportionality requires the State to justify that the means which are adopted by the legislature would encroach upon the right to privacy only to the minimum degree necessary to achieve its legitimate interest. Justice Nariman held thus:
“495…Statutory provisions that deal with aspects of privacy would continue to be tested on the ground that they would violate the fundamental right to privacy, and would not be struck down, if it is found on a balancing test that the social or public interest and the reasonableness of the restrictions would outweigh the particular aspect of privacy claimed. If this is so, then statutes which would enable the State to contractually obtain information about persons would pass muster in given circumstances, provided they safeguard the individual right to privacy as well… in pursuance of a statutory requirement, if certain details need to be given for the concerned statutory purpose, then such details would certainly affect the right to privacy, but would on a balance, pass muster as the State action concerned has sufficient inbuilt safeguards to protect this right – viz. the fact that such information cannot be disseminated to anyone else, save on compelling grounds of public interest.”38 33 While five judges of the Court adopted the “proportionality” standard to test a law infringing privacy, Justice Chelameswar discussed the need to apply of a “compelling state interest” standard, describing it as the “highest standard of scrutiny that a court can adopt”. Describing Article 21 as the “bedrock” of privacy, the learned Judge held:
“379…If the spirit of liberty permeates every claim of privacy, it is difficult if not impossible to imagine that any standard of limitation, other than the one under Article 21 applies.39 380. The just, fair and reasonable standard of review under Article 21 needs no elaboration. It has also most commonly been used in cases dealing with a privacy claim hitherto. Gobind resorted to the compelling state interest standard in addition to the Article 21 reasonableness enquiry. From the United States where the terminology of ‘compelling state interest’ originated, a strict standard of scrutiny comprises two things- a ‘compelling state interest’ and a requirement of ‘narrow tailoring’ (narrow tailoring means that the law must be narrowly framed to achieve the objective).
As a term, compelling state interest does not have definite contours in the US. Hence, it is critical that this standard be adopted with some clarity as to when and in what types of privacy claims it is to be used. Only in privacy claims which deserve the strictest scrutiny is the standard of compelling State interest to be used. As for others, the just, fair and reasonable standard under Article 21 will apply. When the compelling State interest standard is to be employed must depend upon the context of concrete cases.”40
(Emphasis supplied)
Justice Chelameswar’s view accepts the ‘fair, just and reasonable’ standard in the generality of cases, carving an exception in cases of a certain category where a heightened scrutiny must apply. Those categories of exception are not spelt out. They would, as the judge opined, be evolved on a case by case basis. The Bench of nine judges had held that the contours of privacy exist across the spectrum of constitutionally protected freedoms. Privacy was held to be a necessary condition precedent to the enjoyment of the guarantees in Part III. This has enhanced the scope of the protection guaranteed to privacy. Consequently, privacy infringements will generally have to satisfy the other tests applicable apart from those under Article 21. In his concurring opinion, Justice S A Bobde held:
“427. Once it is established that privacy imbues every constitutional freedom with its efficacy and that it can be located in each of them, it must follow that interference with it by the state must be tested against whichever one or more Part III guarantees whose enjoyment is curtailed. As a result, privacy violations will usually have to answer to tests in addition to the one applicable to Article 21, Such a view would be wholly consistent with R. C. Cooper v. Union of India.”41
(Emphasis supplied)
Any attempt by the State to restrict privacy must therefore meet the constitutional requirements prescribed for each provision of Part III, which the restriction infringes. In his concurring opinion, Justice Nariman held thus:
“488… Every State intrusion into privacy interests which deals with the physical body or the dissemination of information personal to an individual or personal choices relating to the individual would be subjected to the balancing test prescribed under the fundamental right that it infringes depending upon where the privacy interest claimed is founded.”42
(Emphasis supplied)
Justice Nariman further held: “526…when it comes to restrictions on this right, the drill of various Articles to which the right relates must be scrupulously followed. For example, if the restraint on privacy is over fundamental personal choices that an individual is to make, State action can be restrained under Article 21 read with Article 14 if it is arbitrary and unreasonable; and under Article 21 read with Article 19(1)(a) only if it relates to the subjects mentioned in Article 19(2) and the tests laid down by this Court for such legislation or subordinate legislation to pass muster under the said Article. Each of the tests evolved by this Court, qua legislation or executive action, under Article 21 read with Article 14; or Article 21 read with Article 19(1) (a) in the aforesaid examples must be met in order that State action must pass muster.”43
(Emphasis supplied)
The constitutional guarantee on protection of privacy was placed on a sure foundation. Since emanations of privacy are traceable to various rights guaranteed by Part III, a law or executive action which encroaches on privacy must meet the requirements of the constitutionally permissible restriction in relation to each of the fundamental rights where the claim is founded.
B.6 Legitimate state interests
35 Recognizing that the right to privacy is not absolute, the judgment recognizes that legitimate state interests may be a valid ground for the curtailment of the right subject to the tests laid down for the protection of rights. Justice Nariman held:
“526…This right is subject to reasonable regulations made by the State to protect legitimate State interests or public interest. However, when it comes to restrictions on this right, the drill of various Articles to which the right relates must be scrupulously followed.”44 Recognizing that a legitimate state aim is a pre-requisite for any restriction on the right, the judgment of four judges held:
“310…the requirement of a need, in terms of a legitimate state aim, ensures that the nature and content of the law which imposes the restriction falls within the zone of reasonableness mandated by Article 14, which is a guarantee against arbitrary state action. The pursuit of a legitimate state aim ensures that the law does not suffer from manifest arbitrariness.”
36 The judgment sets out illustrations of legitimate State interests. The provisos to various fundamental rights were held to be an obvious restriction on the right to privacy. It was held that the State does have a legitimate interest in collection and storage of private information when it is related to security of the nation. Apart from the concerns of national security, an important State interest, it was held, lies in ensuring that scarce public resources reach the beneficiaries for whom they are intended. It was held thus:
“311…Allocation of resources for human development is coupled with a legitimate concern that the utilisation of resources should not be siphoned away for extraneous purposes… Data mining with the object of ensuring that resources are properly deployed to legitimate beneficiaries is a valid ground for the state to insist on the collection of authentic data.”45 Prevention and investigation of crime, protection of the revenue and public health were demarcated as being part of other legitimate aims of the State.
The judgment places an obligation on the State to ensure that while its legitimate interests are duly preserved the data which the State collects is used only for the legitimate purposes of the State and is “not to be utilised unauthorizedly for extraneous purposes.”
37 However, reiterating that every facet of privacy is to be protected, the judgment held that there should be a careful balance between individual interests and legitimate concerns of the state. Justice Nariman, in his separate opinion held: “488. Every State intrusion into privacy interests which deals with the physical body or the dissemination of information personal to an individual or personal choices relating to the individual would be subjected to the balancing test prescribed under the fundamental right that it infringes depending upon where the privacy interest claimed is founded.”46
38 The judgment in Puttaswamy recognizes the right to privacy as a constitutional guarantee protected as intrinsic to the freedoms guaranteed by Part III of the Constitution. Privacy is integral to the realization of human dignity and liberty. A society which protects privacy, values the worth of individual self-realization. For it is in the abyss of solitude that the innermost recesses of the mind find solace to explore within and beyond.
C Submissions
C.I Petitioners’ submissions
The petitioners challenge the constitutional validity of:
a. The Aadhaar programme that operated between 28.01.2009 till the coming into force of the Aadhaar Act, 2016 on 12.07.2016;
b. The Aadhaar Act, 2016 (and alternatively certain provisions of the Act);
c. Regulations framed under the Aadhaar Act, 2016;
d. Elements of the Aadhaar programme that continue to operate without the cover of the Act;
e. Subordinate legislation including the Money Laundering (Amendment) Rules, 2017;
f. All notifications issued under Section 7 of the Aadhaar Act in so far as they make Aadhaar mandatory for availing of certain benefits, services and subsidies; and g. Actions which made Aadhaar mandatory even where the activity is not covered by Section 7 of the Act. Mr Shyam Divan, learned Senior Counsel submitted that the Aadhaar project and Act are ultra vires on the following grounds:
i The project and the Act violate the fundamental right to privacy; PART C 35
ii The architecture of the Aadhaar project enables pervasive surveillance by the State;
iii The fundamental constitutional feature of a ‘limited government’ – which is the sovereignty of the people and limited government authority- is changed completely post Aadhaar and reverses the relationship between the citizen and the State;
iv Due to the unreliability of biometric technology, there are authentication failures which lead to the exclusion of individuals from welfare schemes;
v A citizen or resident in a democratic society has a choice to identify herself through different modes in the course of her interactions generally in society, as well as in her interactions with the State. Mandating identification by only one mode is highly intrusive, excessive and disproportionate and violates Articles 14, 19 and 21; and
vi The procedure adopted by the State before and after the enactment of the law is violative of Articles 14 and 21 because:
a. There is no informed consent at the time of enrolment;
b. UIDAI does not have control over the enrolling agencies and requesting entities that collect sensitive personal information which facilitates capture, storage and misuse of information; and
c. The data collected and uploaded into the CIDR is not verified by any government official designated by UIDAI. Mr Kapil Sibal, learned Senior Counsel submits that the provisions of the Aadhaar Act are unconstitutional for the following reasons:
i The aggregation and concentration of sensitive personal information under the Aadhaar Act is impermissible because it is capable of being used to affect every aspect of an individual’s personal, professional, religious and social life. It is therefore violative of the individual freedoms guaranteed under Articles 19(1)(a) to 19(1)(g), 21 and 25 of the Constitution;
ii Such aggregation of information is also an infringement of informational privacy, which has been recognised in Puttaswamy;
iii Making Aadhaar mandatory unreasonably deprives citizens of basic rights and entitlements and infringes Article 21 of the Constitution;
iv Use of Aadhaar as an exclusive identity for availing of subsidies, benefits and services is disproportionate and violates Article 14 for being arbitrary and discriminatory against persons otherwise entitled to such benefits;
v Collection and storage of data with the government under the Aadhaar Act is violative of the right to protection from self-incrimination, and the right to PART C 37 privacy and personal dignity and bodily Integrity envisaged under Article 20(3) and Article 21 of the Constitution;
vi To prescribe that Aadhaar is the only identity that enables a person to receive entitlements is contrary to the right of an individual under the Constitution to identify the person through other prescribed documentation such as electoral rolls or passports;
vii Section 7 of the Aadhaar Act is applicable only to such subsidies, benefits and services, for which the entire expenditure is directly incurred from the Consolidated Fund of India or from which the entire receipts directly form part of the Consolidated Fund of India;
viii Use of Aadhaar as the sole identity will not prevent pilferage and diversion of funds and subsidies, as faulty identification is only one of the factors that contributes to it; and
ix The Aadhaar project conditions the grant of essential benefits upon the surrender of individual rights.
Mr Gopal Subramanium, learned Senior Counsel, made the following submissions:
i The Aadhaar project violates dignity under Article 21 of the Constitution as recognised in the judgments- in Puttaswamy, NALSA47 and Subramanian Swamy48;
ii The Aadhaar project is unconstitutional as it seeks a waiver of fundamental rights;
iii The Aadhaar project violates the guarantees of substantive and procedural reasonableness under Articles 14,19 and 21;
iv Aadhaar perpetrates exclusion from social security schemes and is therefore discriminatory under Article 14;
v The Aadhaar Act lacks legitimacy in its object in so far as it validates a breach of fundamental rights retrospectively;
vi Rights and entitlements conferred under the Constitution cannot be based on algorithmic probabilities which UIDAI cannot control;
vii No consequence is prescribed for non-authentication under the Aadhaar Act;
viii The Aadhaar Act violates Part IX of the Constitution, which provides for decentralisation (to Panchayats), while the Aadhaar scheme strikes at the federal structure of the Constitution; and
ix Breaches under the Aadhaar Act cannot be cured. Mr Arvind Datar, learned Senior Counsel has submitted:
i Rule 9 of the PMLA (Second Amendment) Rules, 2017 which requires mandatory linking of Aadhaar with bank accounts is unconstitutional and violates Articles 14, 19(1)(g), 21 and 300A of the Constitution, Sections 3, 7 and 51 of the Aadhaar Act, and is also ultra vires of the provisions of the PMLA Act, 2002 on the following grounds:
a. Under the impugned amended Rules, linkage of Aadhaar numbers to bank accounts is mandatory and persons not enrolling for Aadhaar cannot operate a bank account, which violates the spirit of Article 14 in entirety in so far it arbitrarily metes out unequal treatment based on unreasonable classification;
b The impugned Rules are violative of Article 19(1)(g) as the Rules refer to companies, firms, trusts, etc., whereas the Aadhaar Act is only to establish identity of “individuals”;
c Non-operation of a bank account, even for a temporary period, leads to deprivation of an individual’s property and therefore constitutes a violation under Article 300A of the Constitution, which provides that deprivation can be done only by primary legislation; and PART C 40
d The Rule has no nexus to the object of the PMLA Act, as the Act has no provision to make bank accounts non-operational; ii Section 139AA of the Income Tax Act, 1961 is liable to be struck down as violative of Articles 14, 21 and 19(g) of the Constitution;
iii The decision in Binoy Viswam v Union of India49 requires reconsideration in view of the nine judge Bench decision in Puttaswamy;
iv In view of serious deficiencies in the Aadhaar Act, there is a need for guidelines under Article 142 to protect inter alia, the right to privacy and to implement the mandate of the nine judge Bench in Puttaswamy;
v If the Aadhaar project is not struck down, it should be confined only for identification or authentication of persons who are entitled to subsidies, benefits and services for which expenditure is incurred from the Consolidated Fund of India;
vi Sections 2(g), 2(j) 7, 57 and 59 of the Aadhaar Act violate Articles 14, 21 and 300A of the Constitution; and
vii PMLA Rule 9 is arbitrary as it is contrary to the RBI Master Circular (issued in 2013), which provided a list of documents that were to be treated as ‘identity proof’, in relation to proof of name and proof of residence Mr P Chidambaram, learned Senior Counsel argued that the Aadhaar Act could not have been passed as a Money Bill.
Thus, he submitted:
i The only difference between financial bills and money bills is the term “only” in Article 110 of the Constitution which implies that the scope of money bills is narrower than the scope of financial bills and provisions relating to money bills must thus be construed strictly;
ii The Aadhaar Act, which was passed as a money bill, should be struck down since many of its provisions such as Section 57 have no relation to the nature of a Money Bill and bear no nexus to the Consolidated Fund of India;
iii Since Money Bills can only be introduced in the Lok Sabha, on account of the curtailment of the powers of the Rajya Sabha and the President, the relevant provisions must be accorded a strict interpretation;
iv While Article 110(3) provides that the decision of the Speaker of the Lok Sabha as to whether a Bill is a ‘Money Bill’ shall be final, the finality is only with regard to the Parliament and does not exclude judicial review; and
v Since the legislative procedure is illegal and the power of the Rajya Sabha has been circumvented to disallow legislative scrutiny of the PART C 42 Aadhaar bill, provisions of the Act cannot be severed to save the Act and the Act is liable to be struck down as a whole by the Court.
Mr KV Vishwanathan, learned Senior Counsel made the following submissions:
i All acts done prior to the passage of the Act are void ab initio and are not saved or validated by Section 59. In any event, Section 59 is invalid;
ii Collection, storage and use of data under the Aadhaar project and Act are invalid for the following reasons:
a. The Aadhaar Act and the surrounding infrastructure has made the possession of Aadhaar de facto mandatory;
b. Compulsory collection of identity information violates various facets of the right to privacy – bodily privacy, informational privacy and decisional autonomy;
c. The Act is unconstitutional since it collects the identity information of children between 5-18 years without parental consent;
d. Centralised storage of identity information and the unduly long period of retention of transaction data and authentication records is disproportionate;
e. The Act and Regulations preclude Aadhaar number holders from accessing or correcting their identity information stored on the CIDR; and
f. The Act and Regulations lack safeguards to secure sensitive personal data.
iii Services like health related services, and those related to food, pensions and daily wages claimed under Section 7 of the Act have been denied because of biometric failure. Biometric infrastructure operates on a probabilistic system, which cannot be ‘one hundred percent infallible’. Thus, the State needs to take steps to prevent the denial of benefits by adopting alternate methods for verification of identity. This is absent at present, resulting in a violation of Articles 14 & 21;
iv No provision is made for a hearing against omission and deactivation of the Aadhaar number, which violates the principles of natural justice; and v Sections 2(g), 2(j), 2(k) and 23(2) of the Aadhaar Act suffer from excessive delegation and the allied regulations are vague, manifestly arbitrary and unreasonable.
Mr Anand Grover, learned Senior Counsel has submitted thus:
i The Aadhaar project extends far beyond the scope of the Aadhaar Act with no procedural safeguards. Hence it violates Article 21 in as much as it is without the support and sanction of law. The data collected is unauthorised, excessive and being illegally shared;
ii The use of biometric technology to establish identity is uncertain, unproven and unreliable leading to exclusion and a violation of Articles 14 and 21;
iii The lack of security in the Aadhaar project violates the right to privacy under Article 21;
iv Excessive powers have been delegated to the UIDAI through the Aadhaar Act; and v Sections 33(2) and 57 of the Act are vague, overbroad and constitutionally invalid. Ms Meenakshi Arora, learned Senior Counsel contended that:
i The general and indiscriminate retention of personal data, including metadata, and the ensuing possibility of surveillance by the State has a chilling effect on fundamental rights like the freedom of speech and expression, privacy, and dignity;
ii Making Aadhaar the sole means of identification for various services impinges upon dignity as it amounts to requiring a license for the exercise of fundamental rights; and
iii The Aadhaar project does not contain any specific provisions for data protection, apart from a mere general obligation on UIDAI, which is a violation of the obligation of the State to ensure that the right to life, liberty, dignity and privacy of every individual is not breached under Part III of the Constitution. Mr Sajjan Poovayya, learned Senior Counsel has urged the following submissions:
i The Aadhaar Act fails to satisfy the constitutional test of a just, fair and reasonable law; ii Maintenance of Aadhaar records by the State under Section 32 is an unwarranted intrusion by the State;
iii Use of personal information under Section 33 is an unwarranted intrusion by the State; iv Section 57 of the Act is contrary to the principle of purpose limitation; and PART C 46 v Sections 2(g) and 2(j), the proviso to Section 3(1), Section 23(2)(g) and Section 23(2)(n) read with Section 54(2)(l), and Section 29(4) of the Act suffer from the vice of excessive delegation. Mr CU Singh, learned Senior Counsel, argued that the rights of the child are violated through the Aadhaar project. A child has no right to give consent or to enter into a contract.
A child in India, under law, has no power or right to bind herself to anything, to consent or enter into contracts. In this background, there is no compelling state interest to mandate Aadhaar for children. The fundamental right of a child to education cannot be made subject to production of Aadhaar. These requirements are not only contrary to domestic legislation protecting the rights of children but also against India’s international obligations. Learned counsel also spoke of the violation of the rights of homeless people who are denied benefits due to the lack of a fixed abode. Mr Sanjay Hegde, learned Senior Counsel has urged that since there is no ‘essential practice’ involved, exemptions must be allowed from the mandatory nature of the Aadhaar Act on the grounds of freedom of conscience under Article 25 of the Constitution.
Ms Jayna Kothari, learned Counsel arguing on behalf of an intervenor organization for transgender persons and sexual minorities urged that the Aadhaar Act discriminates against sexual minorities. Aadhaar Regulations require demographic information. The enrolment form has a third gender, but there is no uniformity across the board, and the documents that have to be produced to get an Aadhaar card do not always have that option. Aadhaar is being made mandatory for almost everything but transgender persons cannot get an Aadhaar because they do not have the gender identity documents that Aadhaar requires.
This non-recognition of gender identity leads to denial of benefits which is violative of both Articles 14 and 21. It has also been argued before us in an intervention application that denial of Aadhaar to Non-Resident Indians leads to discrimination when NRIs seek to avail of basic services in India.
C.2 Respondents’ submissions
Mr KK Venugopal, Learned Attorney General for India, has submitted thus:
i. For the period prior to coming into force of the Aadhaar Act, because of the interim orders passed by the SC, obtaining an Aadhaar number or enrollment number was voluntary, and hence there was no violation of any right; ii. Section 59 of the Aadhaar Act protects all actions taken from the period between 2010 till the passage of the Aadhaar Act in 2016;
iii. The judgments in MP Sharma and Kharak Singh being those of 8 and 6 judges respectively, holding that the right to privacy is not a fundamental right, judgments of smaller benches delivered during the period upto Puttaswamy would be per incuriam. Hence, the State need not have proceeded on the basis that a law was required for the purpose of getting an Aadhaar number or an enrolment number. As a result, the administrative actions taken would be valid as well as the receipt of benefits and subsidies by the beneficiaries;
iv. Subsequent to the Aadhaar Act, the petitioners would have to establish that one or more of the tests laid down by the nine judge bench in Puttaswamy render the invasion of privacy resulting from the Aadhaar Act unconstitutional. The tests laid down in Puttaswamy have been satisfied and hence the Aadhaar Act is not unconstitutional for the following reasons:
a. The first condition in regard to the existence of a law has been satisfied;
b. Legitimate state interests such as preventing the dissipation of social welfare benefits, prevention of money laundering, black money and tax evasion, and protection of national security are satisfied through the Act;
c. The Aadhaar Act satisfies the test of proportionality by ensuring that a “rational nexus” exists between the objects of the Act and the means adopted to achieve its objects; and d. For the purpose of testing legitimate State interest and proportionality, the Court must take note of the fact that each one of the subsidies and benefits under Section 7 is traceable to rights under Article 21 of the Constitution – such as the right to live with human dignity, the right to food, right to shelter, right to employment, right to medical care and education. If these rights are juxtaposed with the right to privacy, the former will prevail over the latter.
v. The Aadhaar Act was validly passed as a Money Bill on the following grounds:
a. The term ‘targeted delivery of subsidies’ contemplates an expenditure of funds from the Consolidated Fund of India, which brings the Aadhaar Act within the purview of a Money Bill under Art. 110 of the Constitution; b. Sections 7, 24, 25 and the Preamble of the Act also support its classification as a Money Bill;
c. The Aadhaar Act has ancillary provisions, but they are related to the pith and substance of the legislation which is the targeted delivery of subsidies and benefits; and d. Section 57 of the Act is saved by Article 110 (1) (g) of the Constitution as it is a standalone provision and even if a Bill is not covered under PART C 50 clauses (a) to (f) of Article110(1), it can still be covered under Article110 (1) (g).
Mr Tushar Mehta, learned Additional Solicitor General, submitted:
i. Section 139AA of the Income Tax Act, was examined in Binoy Viswam in the context of Article 19 and fulfills the three tests laid down under Puttaswamy as well as the test of manifest arbitrariness laid down in Shayara Bano v Union of India50;
ii. The demographic information that is required for Aadhaar enrollment is already submitted while obtaining a PAN card and therefore individuals do not have a legitimate interest in withholding information;
iii. Linking Aadhaar to PAN is in public interest on the following grounds:
a. The State has a legitimate interest in curbing the menace of black money, money laundering and tax evasion, often facilitated by duplicate PAN cards, and the linking of Aadhaar to the PAN card will ensure that one person holds only one PAN Card, thereby curbing these economic offences;
b. Aadhaar-PAN linking is in public interest and satisfies the test of proportionality and reasonableness;
c. The individual interest gives way to a larger public interest and a statutory provision furthering state interest will take precedence over fundamental rights;
d. The Court must not interfere with the Legislature’s wisdom unless the statutory measure is shockingly disproportionate to the object sought to be achieved;
e. India is a signatory to various international treaties under which it has obligations to take action to curb the menace of black money and money laundering in pursuance of which measures including the amendments to inter alia the Income Tax Act and the PMLA Act and Rules thereunder, have been brought about by the legislature;
f. Statutory provisions under Aadhaar Act and Income Tax Act are distinct and standalone. Moreover, the validity of one provision cannot be examined in the light of the other;
g. Ascribing a (mandatory or voluntary) character to the provisions of a statute is Parliament’s prerogative and cannot be questioned by courts; and
h. Rule 9 of the amended PMLA Rules that mandates furnishing of an Aadhaar number to open a bank account is not ultra vires the Aadhaar Act. Similarly, the Rule that an existing bank account will become nonoperational if not linked with Aadhaar within six months is not a penalty but a consequence to render the accounts of money launderers non-operational. Mr Rakesh Dwivedi, learned Senior Counsel, has submitted:
i. The right to privacy exists when there is a reasonable expectation of privacy. However, this reasonable expectation of privacy differs from one dataset to another since the Aadhaar Act draws a distinction between demographic information, optional demographic information (eg. mobile number), core biometric information (fingerprints and iris scans) and biometric information such as photographs;
ii. Alternatively, the applicability of Article 21 has to be confined and limited to core biometric information;
iii. Fundamental rights are not absolute and can be restricted if permitted specifically. Article 21 expressly envisages deprivation by laws which seek to carry out legitimate objectives and are reasonable and proportionate;
iv. The Aadhaar Act does not cause exclusion because if authentication fails after multiple attempts, then the subsidies, benefits and services, can be availed of by proving the possession of an Aadhaar number, either by producing the Aadhaar card or by producing the receipt of the application for enrolment and producing the enrolment ID number;
v. Section 7 of the Aadhaar Act protects the right to human dignity recognized by Article 21 of the Constitution by providing services, benefits and subsidies. The Aadhaar Act is a welfare scheme in pursuance of the State’s obligation to respect the fundamental rights to life and personal liberty; to ensure justice (social, political and economic) and to eliminate inequality (Article 14) with a view to ameliorate the lot of the poor and the Dalits;
vi. Socio-economic rights must be read into Part III of the Constitution since civil and political rights cannot be enjoyed without strengthening socio – economic rights;
vii. A welfare State has a duty to ensure that each citizen has access at least to the basic necessities of life. The idea of a socialist state under a mandate to secure justice- social, economic and political – will be completely illusory if it fails to secure for its citizens the basic necessities in life. There cannot be any dignity for those who suffer starvation, subjugation, deprivation and marginalization and those who are compelled to do work which is intrinsically below human dignity;
viii. The Aadhaar number does not convert individuals to numbers. The Aadhaar number is necessary for authentication and it is solely used for that purpose. The petitioners have conflated the concepts of identity and identification. Authentication through a number is merely a technological requirement which does not alter the identity of an individual;
ix. Even if there is a conflict between the right to privacy and the right to food and shelter, the Aadhaar Act strikes a fair balance. The Aadhaar Act ensures human dignity and the right to life and liberty, hence there would be no reasonable expectation of privacy and autonomy;
x. The requirement to obtain an Aadhaar number under the Aadhaar Act does not reflect a lack of trust in citizens. Authentication by the State does not presume that all its citizens are dishonest. The provisions of the Aadhaar Act are merely regulatory in nature – similar to the process of frisking at airports or other offices – since there is no effective method to ensure targeted delivery;
xi. The “least intrusive test” is not applicable in the present case. The requirement that the least intrusive means of achieving the State object must be adopted, has been rejected by Indian courts in a catena of decisions as it involves a value judgment and second guessing the wisdom of the legislature. Such a test violates the separation of powers between the legislature and the judiciary;
xii. Even assuming that the ‘least intrusive method’ test applies, the exercise of determining the least intrusive method of identification is a technical exercise and cannot be undertaken in a court of law;
xiii. The Petitioners who have furnished smartcards as an alternative to the Aadhaar card, have not established that smartcards are less intrusive than the Aadhaar card authentication process;
xiv. The ‘strict scrutiny test’ does not apply to the Aadhaar Act. That test is conceptualised in the United States, to be only applied to ‘suspect classifications’;
xv. Section 7 of the Aadhaar Act does not involve any waiver of fundamental rights;
xvi. There can be no assumption of mala fide against the government or the legislature. A mere possibility of abuse is not a ground to invalidate the Aadhaar Act;
xvii. Through Section 57, Parliament intended to make the use of the Aadhaar number available for other purposes due to the liberalization and privatization of the economy in areas earlier occupied by the government and public sector. Many private corporate bodies are operating parallel to and in competition with the public sector such as in banking, insurance, defence, and health. These are core sectors absolutely essential for national integrity, to the national economy and the life of people;
xviii. Sections 2(g), and (j) read with Section 54(2)(a) and Section 54(1) do not suffer from excessive delegation of power to UIDAI and there are sufficient guidelines coupled with restrictions. The regulation making power of the Authority under the Act is limited by the use of the expression ‘such other biological attribute’ which will be interpreted ejusdem generis with the categories of information mentioned before namely, fingerprints and iris scan. These categories have certain characteristics: firstly, they do not contain genetic information; secondly, they are non-intrusive; thirdly, apart from carrying out authentication they do not reveal any other information of the individual; fourthly, these are modes of identification used for identifying a person even without digital technology; fifthly, they are capable of being used for instantaneous digital authentication; and sixthly, they are biological attributes enabling digital authentication. The addition of biological attributes, under Section 54, must mandatorily be laid before the Parliament under Section 55. This is an additional check on the regulation making power of UIDAI;
xix. Under Section 2(k), which defines demographic information, certain sensitive categories of information such as ‘race, religion, caste, tribe, ethnicity, language, records of entitlement, income or medical history’ of the person are excluded. The term ‘other relevant information’ has to be construed ejusdem generis and would have to be necessarily demographic in nature as contrasted with biometric information;
xx. Aadhaar is necessary, as 3% of India’s GDP amounting to trillions of rupees is allocated by Governments towards subsidies, scholarships, pensions, education, food and other welfare programmes. But approximately half of if does not reach the intended beneficiaries. Aadhaar is necessary for fixing this problem as no other identification document is widely and commonly possessed by the residents of the country and most of the other identity documents do not enjoy the quality of portability;
xxi. The enrolment and authentication processes under the Aadhaar Act are strongly regulated so that the data is secure;
xxii. The security of the CIDR is also ensured through adequate measures and safeguards;
xxiii. The Aadhaar Act ensures that UIDAI has control over the requesting entity during the authentication process;
xxiv. Enrolment Regulations ensure that the requirement of informed consent of individuals is fulfilled while securing the Aadhaar card in the following ways:
a. Firstly, the resident is given an opportunity of verifying his or her information for accuracy before uploading;
b. Secondly, the details and the supporting documents are provided by the resident, or an introducer (in specific cases);
c. Thirdly, the enrolling agency is obliged to inform the individual about the manner in which the information shall be used, the nature of recipients with whom the information is to be shared during authentication; and the existence of a right to access information, the procedure for making request for such access and details of the person/ department to whom a request can be made; and d. Fourthly, the uploading of information is done in the presence of the individual.
xxv. When an individual makes a choice to enter into a relational sphere then his or her choice as to mode of identification would automatically get restricted on account of the autonomy of the individuals or institution with whom they wish to relate. This is more so where the individual seeks employment, service, subsidy or benefits;
xxvi. The Central government has the power to direct the linking of Aadhaar card, with SIM card, as it is proportional to the object sought to be achieved in the interest of national security;
xxvii. Regarding the process of authentication and metadata retained under the Act, it is submitted:
a. The only purpose of the Aadhaar project is authentication and there is no power under the Act to analyze data;
b. The Aadhaar Act does not involve big data or learning algorithms. It merely utilizes a matching algorithm for the purpose of authentication;
c. Metadata contemplated is process or technical metadata and does not reveal anything about the individual. Section 2(d) of the Act defines “authentication record” to mean the record of the time of authentication, identity of the RE and the response provided by the Authority”, and the relevant authentication regulation, Regulation 26, does not go beyond the scope of Section 2(d) of the Act;
d. Moreover, Regulation 26 and Section 32(3) of the Act prohibit the Authority from collecting or storing any information about the purpose of authentication; and e. Only limited technical metadata is required to be stored in an effort to exercise control over REs by way of audits.
xxviii. Regarding the security of the Aadhaar data, it is submitted:
a. The provisions of the Information Technology Act, 2000 and the punitive measures provided there are made applicable to Aadhaar data under Section 30 of the Aadhaar Act; and
b. Anyone attempting to gain unauthorized access to the CIDR faces stringent punishment, including imprisonment upto 10 years.
xxix. On the control exercised by the Authority over the Requesting Entities (RE), the following was urged before the Court:
a. The standard of control exercised by the Authority on the Requesting Entities is ‘fair and reasonable’ as laid down under Article 21 of the Constitution;
b. This control includes requirements that the RE’s procure the fingerprint device from vendors controlled by the Authority, with the Authority also providing the hardware and software of the device. The device is subject to quality checks, and must be certified by the Authority before being used by the RE. The Authority also takes measures to ensure that data is sent to it in an encrypted form;
c. The license is given to the RE from the Authority only after an audit of the RE is conducted, and the audit report is approved; and d. The data collected by these REs is segregated and there exists no way of aggregating this data. During authentication requests, the full identity information of the individual will never be transmitted back to the REs by the Authority as there exists a statutory bar from sharing Biometric information under Sections 29 (1) (a) and 29(4) of the Act.
xxx. UIDAI has entered into licensing agreements with foreign biometric solution providers (BSP) for software. Even though the source code of the software is retained by the BSP as it constitutes their intellectual property, the data in the server rooms is secure as the software operates automatically and the biometric data is stored offline. There is no opportunity available to the BSP to extract data as they have no access to it;
xxxi. Prior to the enactment of the Aadhaar Act, the Aadhaar project was governed by the provisions of the Information Technology Act, 2000. Section 72A of the Information Technology Act, 2000 provides for punishment for disclosure of information in breach of law or contract;
xxxii. The architecture of the Aadhaar Act does not enable any real possibility, proximate or remote, of mass surveillance in real time by the State;
xxxiii. The giving of identity information and undergoing authentication has no direct and inevitable effect on Article 19(1)(a). Alternatively, even if Article 19(1)(a) is attracted, Article 19(2) would protect Section 7 of the Aadhaar Act as it has a direct and proximate nexus to public order and security of the State;
xxxiv. In response to the argument that the requirements of Aadhaar number and authentication for benefits, services and subsidies would be ultra PART C 62 vires Article 243-G and items 11, 12, 16, 17, 23, 25 and 28 of the XIth Schedule, it is submitted that the Panchayats get only such powers as are given to it by the legislature of the State. Article 243-G is merely enabling. There is no compulsion upon the State to endow the Panchayats with powers relating to the items specified in the XIth Schedule;
xxxv. On the validity and purpose of Section 57, it is urged: a. Section 57 is not an enabling provision. It merely provides, as it states, that the provisions of the Act would not prevent the use of Aadhaar for other purposes;
b. However, Section 57 imposes a limitation on any such use for other purposes, that the use must be sanctioned by any law in force or any contract;
c. Another limitation is presented by the proviso to Section 57, which says that the use of the Aadhaar number shall be subject to the procedure and obligations under Section 8 and Chapter VI, which would necessarily also subject it to the operation of Chapter VII (dealing with Offences & Penalties) of the Act;
d. Under Section 57, the State, a body corporate or any other person cannot become Requesting Entities unless the limitations provided for under Section 57 are complied with;
e. Section 57 imposes limitations, and the use is backed by authentication, protection of information and punitive measures;
f. The expressions ‘pursuant to any law or any contract’, and ‘to this effect’- necessarily entail that where the State makes a law or any body corporate enters into a contract, the law or contract should be prior in point of time to the making of any application for becoming a Requesting Entity or a Sub-Authentication User Agency under Regulation 12 of the Authentication Regulations; and
g. A large number of small service providers simply cannot become Requesting Entities under Section 57, as they will not meet the rigorous standard demanded by the eligibility conditions which are prescribed by the Regulations to become Authentication User Agencies (AUA)/ KYC User Agencies (KUA). Therefore, this provision does not create a situation whereby the common man is required to undergo authentication in all activities.
xxxvi. The Aadhaar Act is not exclusionary but inclusionary since it provides all citizens the bare necessities for a dignified existence; xxxvii. Having the option to opt-out is not a constitutional requirement. Mr Neeraj Kishan Kaul, learned Senior Counsel, made the following submissions:
i. Aadhaar is a speedy and reliable tool for identification and authentication and there is no reason to hold it invalid;
ii. Private entities and AUAs/KUAs that have built their businesses around it should be allowed to use Aadhaar authentication services;
iii. Section 57 is an enabling provision and private players should be given the choice to use the Aadhaar authentication services as a tool for verification if there is a consensus between private players’ and their customers;
iv. Aadhaar authentication has benefited women in villages and migrants and increased the reach of microfinance institutions, thus reducing predatory financing; and
v. A statute cannot be struck down on the ground that there is scope for misuse.
Mr Jayant Bhushan, learned Senior Counsel appearing for the Reserve Bank of India urged the following submissions before the Court:
i. RBI, in exercise of its powers under the Banking Regulation Act, 1949 and Rule 9 of the PMLA Rules, 2005 issued an amended Master Circular on April 20, 2018 which mandates that Aadhaar has to be submitted to a Reporting Entity. This circular conforms with the PMLA rules;
ii. Rule 9(14) of the PMLA Rules provides that the Regulator- the RBI in this case, lay down guidelines incorporating the requirements of sub-rules 9(1)-(13), which would include enhanced or simplified measures to verify identity; and
iii. The requirement of submission of Aadhaar to the RE is in exercise of this power under Rule 9(14). Mr Gopal Sankarnarayanan, learned counsel, has submitted:
i. The Aadhaar Act as a whole does not violate the fundamental right to privacy;
ii. The factors that save the Aadhaar Act from failing the proportionality test are
(a) Voluntariness to subject one ‘s identity information to obtain the Aadhaar ;
(b) Informed consent when such identity information is utilized; and
(c) A draw on the Consolidated Fund of India; iii. Right to identity is a fundamental right as a part of the right to dignity, which is being realized by the Aadhaar Act;
iv. The right to identity is also recognized under India’s international obligations under instruments such as the UDHR and ICCPR;
v. In view of the large scale enrolments that have already taken place and the expenditure incurred by the Government out of public funds, it would be in overarching public interest to give Section 59 full effect. If this were not done, the only avenue available to the Government would be to undertake the mammoth enrolment task all over again under a new regime, affording only a pyrrhic victory to the Petitioners, while there would be substantial revenue losses to the Government and deprivation of beneficial schemes to those eligible, in the meanwhile;
vi. Certain provisions of the Aadhaar Act have to be struck down or read down so that the Act as a whole can continue to serve its essential purpose – namely Sections 47, Section 8(4) and Section 29(2) of the Act; and vii. Section 139AA of the Income Tax Act, 1961 violates Article 14 and 21 of the Constitution. Mr Zoheb Hossain, learned Counsel, made the following submissions:
i. The right to privacy cannot be asserted vicariously on behalf of others in a representative capacity in a Public Interest Litigation, because unlike other constitutional rights, right to privacy is a personal right. No Section 7 beneficiary has claimed a violation of their right to privacy despite the pendency of the petitions for 6 years before this Court and therefore, the Petitioners’ challenge, in a representative capacity, to section 7 on the ground of a violation of the right to privacy of third parties is not maintainable;
ii. There is no increased threat to privacy due to Aadhaar at the level of requesting entities (RE) for the following reasons: a. REs are already in possession of personal information of individuals and inclusion of Aadhaar does not in any manner increase the threat to privacy; b. Any information disclosed by REs will not be on account of Aadhaar and will have to be dealt with under domain specific legislations, or a data protection regime or agreements between the REs and their customers; and
c. REs have data of their own customers and not of other REs’ customers, so there is no possibility of surveillance.
iii. Safeguards against disclosure of information in the Aadhaar Act are superior to the safeguards laid down in the PUCL case51. Sections 8, 28 and 29 along with Chapter VII which deals with Offences and Penalties, provide for protection of information and Section 33 lays down a strict procedure for disclosure. Even though the Aadhaar Act is not required to meet the same standard as laid down in PUCL, the safeguards in the Act are not only adequate with regard to identity information and authentication records, but far exceed the safeguards laid down PUCL;
iv. The petitioners cannot contend that Section 33(2) of the Aadhaar Act goes against the principles of natural justice and is disproportionate (as it does not define the term “national security”) for the following reasons: a. What is in the interest of “national security” is not a question of law but that of policy lying in the executive domain; and b. Principles of natural justice cannot be observed strictly in a situation implicating national security. In such cases, it is the duty of the court to read into and provide for statutory exclusion.
v. The laws, which are under challenge, are a part of a concerted scheme to promote redistributive justice and ensure substantive equality, in furtherance of Articles 14, 38, 39B and 39C. These laws ensure a more transparent and a cleaner system, root out revenue leakages and evasion of taxes, thereby giving genuine beneficiaries their rightful share in subsidies; vi. The object of the Aadhaar Act, contrary to what the petitioners have argued, is totally unrelated to suppression of freedom of speech and any incidental effect, if at all, would not implicate the right under Article 19(1)(a);
vii. The petitioners cannot contend that Section 47 of the Aadhaar Act is arbitrary or unreasonable for the following reasons:
a. The offences and penalties under the Act are intended to maintain the purity of data of the Aadhaar number holder and the integrity of the CIDR, which are integral in achieving the object of the Act;
b. Enrolment, storage of data in CIDR, and authentications are so vast and inherently technical that any breach of the provisions, can be effectively dealt with by the UIDAI;
c. The individual has not been left remediless, as he/she can make a complaint to the UIDAI directly or through the grievance redressal centre [Regulation 32 of the Aadhaar (Enrolment and Update) Regulations, 2016]. After a complaint has been made, the UIDAI would be obliged to examine the complaint and accordingly lodge a complaint in a Court in terms of Section 47 of the Aadhaar Act;
d. Section 56 of the Aadhaar Act makes it clear that application of other laws, like the IT Act, is not barred.
viii. Aadhaar must be made mandatory under Section 7 of the Aadhaar Act for the following reasons:
a. Because of the involvement of biometrics, it is almost impossible for one person to obtain two Aadhaar numbers. This will help in checking the entry of fake and duplicate beneficiaries into any welfare scheme;
b. Other methods which were employed over the last 70 years to check duplication, siphoning of money in welfare schemes, large-scale tax evasion, generation of black money, and appearance and rePART C 70 appearance of duplicates, have turned out to be futile. If Aadhaar is made voluntary, the same problems are likely to creep back into the system; and
c. The State is bound to deploy the best technology available to it to ensure proper allocation of resources as there is a constitutional mandate upon the State under Article 14 to efficiently utilize its resources. ix. There is no conflict between the Aadhaar Act and the Income Tax Act as they are both stand alone laws and their scope of operation is different;
x. Through the Aadhaar Act, the State is furthering the following obligations under Part III and Part IV of the Constitution and international obligations:
a. The State has a positive obligation for securing socio-economic rights like the basic right to food, shelter and livelihood of people arising out of Article 21, even though it is worded negatively;
b. The Supreme Court has observed that civil & political rights and socioeconomic rights in India are placed on the same pedestal [PUCL]. Aadhaar is a means of achieving the latter set of rights. The proportionality analysis would therefore require a balancing of rights in this context;
c. Articles 38, 39(b), (c), (e), (f), 41, 43, 47 and 51(c) impose a constitutional mandate on the State to ensure effective and efficient utilization of public resources;
d. The State is the trustee of public resources towards people, and inaction of the State to plug the continuous leakage of public resources and revenues would violate both, the principle of nonarbitrariness and reasonableness envisaged by Article 14 as well as the constitutional doctrine of public trust; and e. The creation of Aadhaar infrastructure and enactment of the Aadhaar Act is a step towards the government pursuing India’s international obligations under the ICESCR.
xi. While testing proportionality, reasonableness of a restriction has to be determined in an objective manner from the standpoint of the interests of the general public and not from the perspective of an individual right bearer claiming invasion52; and
xii. With regard to the alleged conflict between Section 29(2) of the Aadhaar Act and Section 4(b)(xii) of the RTI Act, the former cannot be struck down as unconstitutional for the following reasons:
a. A provision can be struck down only if it is in violation of the Constitution or if the legislature lacks competence, not on the ground that it is in conflict with another law;
b. In any case, the obligations of public authorities under both these provisions are different, as the public authority under the RTI Act can publish the details of beneficiaries from the existing database and the information received by the UIDAI is not required to be shared or displayed publicly. However, if any information is displayed publicly, it can be challenged by an aggrieved person on the ground of privacy which would be completely unrelated to the present challenge;
c. The two laws operate in their distinct fields and there is no conflict between them; and
d. A conflict between two statutes is required to be reconciled through harmonious construction. However, since there is no conflict between these two laws, there is no need for harmonious construction.
D Architecture of Aadhaar: analysis of the legal framework
39 The architecture of the Aadhaar Act envisages the creation of a unique identity for residents on the basis of demographic and biometric information. The Act envisages a process of identification by which the unique identity assigned to each individual is verified with the demographic and biometric information pertaining to that individual which is stored in a centralised repository of data known as the Central Identities Data Repository (CIDR). The former part of the legislative design is implemented by its regulatory provisions governing enrolment53 of individuals who would be allotted a unique identity number. The latter part of the legislative design consists of the process of ‘authentication’.
40 In order to facilitate an understanding of the key aspects of the law, Section 2 provides a dictionary of meanings. ‘Aadhaar number’ is defined in Section 2(a) as the identification number issued to the individual under subsection (3) of Section 3. The individual to whom an Aadhaar number is issued is described in Section 2(b) as the ‘Aadhaar number holder’. The expression ‘authentication’ is defined in Section 2(c) thus: “(c) “Authentication” means the process by which the Aadhaar number alongwith demographic information or biometric information of an individual is submitted to the Central Identities Data Repository for its verification and such Repository verifies the correctness or lack thereof, on basis of information available with it.”
Section 2(d) speaks of the ‘authentication record’ as the record of the time of authentication, the identity of the requesting entity and the response provided by UIDAI. The crucial definitions are those of ‘biometric information’, ‘core 53 Section 2(m) states: “enrolment” means the process, as may be specified by regulations, to collect demographic and biometric information from individuals by the enrolling agencies for the purpose of issuing Aadhaar numbers to such individuals under this Act. biometric information’, ‘demographic information’ and ‘identity information’. These are as follows:
“(g) “biometric information” means photograph, finger print, Iris scan, or other such biological attributes of an individual as may be specified by regulations; …
(j) “core biometric information” means finger print, Iris scan, or such other biological attribute of an individual as may be specified by regulations; (k) “demographic information” includes information relating to the name, date of birth, address and other relevant information of an individual, as may be specified by regulations for the purpose of issuing an Aadhaar number, but shall not include race, religion, caste, tribe, ethnicity, language, records of entitlement, income or medical history. …
(n) “identity information” in respect of an individual, includes his Aadhaar number, his biometric information and his demographic information.” The largest subset of the above definitions consists of ‘identity information’ which is defined in an inclusive sense to comprehend the Aadhaar number, biometric information and demographic information. Demographic information is defined as information related to the name, date of birth and address and other information pertaining to an individual as is specified by the regulations.
Significantly, Section 2(k) excludes, by a mandate, race, religion, caste, tribe, ethnicity, language, records of entitlement, income or medical history from the purview of demographic information. Biometric information consists, under Section 2(g), of the photograph, fingerprint, Iris scan, or other such biological attributes of an individual as may be specified by regulations. Core biometric information in Section 2(j) excludes photographs (which form part of biometric information). Apart from photographs, other biometric information is comprehended within core biometric information and may be expanded to include other biological attributes specified in the regulations to be made under the Act.
41 The identity information of an individual is stored in a central depository. Section 2(h) defines “Central Identities Data Repository” as a centralised database in one or more locations containing all Aadhaar numbers issued to Aadhaar number holders along with the corresponding demographic information and biometric information of such individuals and other related information. The CIDR is the backbone of the Aadhaar Act. All the information collected or created under the Act is stored in it. For the establishment and maintenance of the CIDR, it has been provided54 under the Act that UIDAI may engage one or more entities, which can also perform any other functions as may be specified by regulations. The Act does not prohibit the engagement of private entities for the establishment and maintenance of the CIDR.
42 Section 3, pertains to the entitlement to obtain an ‘Aadhaar Number’, which forms a part of Chapter II titled ‘enrolment’. Section 3 comprises of three parts:
(i) an entitlement of every resident to obtain an Aadhaar number;
(ii) a requirement of submitting demographic and biometric information to be enrolled; and
(iii) a process of undergoing enrolment. Section 3 provides thus:
“Section (3): Aadhaar Number.-
(1) Every resident shall be entitled to obtain an Aadhaar number by submitting his demographic information and biometric information by undergoing the process of enrolment:
Provided that the Central Government may, from time to time, notify such other category of individuals who may be entitled to obtain an Aadhaar number.
(2) The enrolling agency shall, at the time of enrolment, inform the individual undergoing enrolment of the following details in such manner as maybe specified by regulations, namely:-
(a) The manner in which the information shall be used;
(b) The nature of recipients with whom the information is intended to be shared during authentication; and
(c) The existence of a right to access information, the procedure for making requests for such access and details of the person or department in-charge to whom such requests can be made.
(3) On receipt of the demographic information and biometric information under sub-section (1), the Authority shall, after verifying the information, in such manner as may be specified by regulations, issue an Aadhaar number to such individual.” Significantly, sub-section (1) of Section 3 recognises an entitlement, of every resident55 to obtain an Aadhaar number. An entitlement postulates a right. A right contemplates a liberty, for it is in the exercise of the liberty that the individual asserts a right. What is a matter of an entitlement is evidently a matter of option and not a compulsion. That constitutes the fundamental postulate of Section 3.
However, the entitlement to obtain the Aadhaar number is conditioned by the requirement of submitting demographic and biometric information and participating in the process of enrolment.
43 The collection of demographic and biometric information is carried out by an enrolling agency. “Enrolling agency” has been defined under Section 2(l) of the Act as an agency, appointed by UIDAI or a Registrar56, for collecting demographic and biometric information of individuals under the Act. The enrolling agency need not be an entity of the state. The definition opens the space for engagement of private entities in the collection of individual information for the process of enrolment. The enrolling agencies have to set up enrolment centers and they have to function in accordance with the procedure specified by UIDAI.57 Sub-section (2) of Section 3 requires the enrolling agency to disclose to the individual, who is undergoing enrolment, three important facets.
The first is the manner in which the information which is disclosed by the individual would be used. The second relates to the nature of the recipients with whom the information is likely to be shared during the course of authentication. The third is founded upon the individual’s right of access to the information disclosed. All these three facets are crucial to the legislative design because they try to place individual autonomy at the forefront of the process. An individual who discloses biometric and demographic information has a statutory entitlement to fully understand how the information which is disclosed is going to be used and with whom the information is likely to be shared during authentication.58 Access of the information supplied to the individual, it has been argued, is an integral feature of the design created by the statute. These three facets are conditions precedent to the disclosure of information by the individual. Before the individual does so, he or she must have a full disclosure which would enable them to form an informed decision on the exercise of the choice which underlies an entitlement to an Aadhaar number.
The entitlement which is recognised by sub-section (1) is enforced by the mandatory requirements of sub-section (2). Before an Aadhaar number is issued, sub-section (3) requires the authority to verify the information disclosed, in the manner prescribed by regulations. The Act leaves it to regulations to specify how verification will be carried out. 44 Sections 4, 5 and 6 indicate the characteristics which are attributed to Aadhaar numbers, legislative recognition of the steps necessary to ensure financial inclusion and the requirement of periodical updation of information. Under Section 4, three important features attach to the possession of an Aadhaar number.
The first is that the number is unique to one individual and to that individual alone. Once assigned, the Aadhaar number cannot be reassigned to any other individual. The second feature is that an Aadhaar number is random and bears no relation to the attributes or identity of its holder. The third feature of Section 4 is that once assigned, an Aadhaar number can be accepted as proof of identify of its holder “for any purpose”. Under Section 5, UIDAI is under a mandate to adopt special measures to issue Aadhaar numbers to women, children, senior citizens, the differently abled, unskilled and unorganised workers, nomadic tribes, persons who do not have permanent places of abode and to other categories which may be defined by the regulations. Section 6 contains an enabling provision by which the authority may require holders to update their demographic and biometric information periodically, as specified under regulations. An Aadhaar number also does not, by itself, constitute a conferment of a right of citizenship, or domicile (Section 9).
45 Chapter III provides for Authentication. By virtue of Section 7, an enabling provision has been made by which the Union or state governments may require proof of an Aadhaar number for receiving subsidies, benefits and services for which the expenditure is incurred from (or the receipts form part of) the Consolidated Fund of India. Section 7 is in the following terms:
“7. Proof of Aadhaar number necessary for receipt of certain subsidies, benefits and services, etc.- The Central Government or, as the case may be, the State Government may, for the purpose of establishing identity of an individual as a condition for receipt of a subsidy, benefit or service for which the expenditure is incurred from, or the receipt therefrom forms part of, the Consolidated Fund of India, require that such individual undergo authentication, or furnish proof of possession of Aadhaar number or in the case of an individual to whom no Aadhaar number has been assigned, such individual makes an application for enrolment: Provided that if an Aadhaar number is not assigned to an individual, the individual shall be offered alternate and viable means of identification for delivery of the subsidy, benefit or service.”
Section 3 (as explained earlier) postulates an entitlement to an Aadhaar number. An entitlement envisages a right which may (or may not) be exercised by the resident. An entitlement is, after all, an option. Section 7, however, contemplates a requirement. It covers subsidies, benefits or services that are charged to the Consolidated Fund of India; the connect being either in regard to the source of expenditure or the receipts. The statutory definitions of the expressions ‘benefit’, ‘service’ and ‘subsidy’ are contained in clauses (f),(w) and (x) of Section 2 which provide as follows:
“(f) “benefit” means any advantage, gift, reward, relief, or payment, in cash or kind, provided to an individual or a group of individuals and includes such other benefits as may be notified by the Central Government;” (w) “service” means any provision, facility, utility or any other assistance provided in any form to an individual or a group of individuals and includes such other services as may be notified by the Central Government;
(x) “subsidy” means any form of aid, support, grant, subvention, or appropriation, in cash or kind, to an individual or a group of individuals and includes such other subsidies as may be notified by the Central Government.” 46 Section 7 encapsulates a purpose, a condition and a requirement. The purpose incorporated in the provision is to establish the identity of an individual. The condition which it embodies is for the receipt of a subsidy, benefit or service for which the expenditure is incurred or the receipts form part of the Consolidated Fund of India. Where the purpose and condition are fulfilled, the central or state governments may require that the individual should (i) undergo authentication; or (ii) furnish proof of possession of an Aadhaar number; or
(iii) provide proof of an application for enrolment where 81 the Aadhaar number has not been assigned. Three alternatives are stipulated in Section 7. Where the purpose and condition (noted above) are fulfilled, the individual has to undergo authentication. Alternately, the individual has to furnish proof that he or she possesses an Aadhaar number. However, if an Aadhaar number has not been assigned to the individual, he or she would have to make an application for enrolment. In a situation where no Aadhaar number has been assigned as yet, the proviso stipulates that alternate and viable means of identification would be provided to the individual for the delivery of subsidies, benefits or services.
Section 7 indicates that while the central or state governments can mandate that an individual must undergo authentication as a condition for the receipt of a subsidy, benefit or service, a failure of authentication cannot be held out as a ground to deny benefits, subsidies or services. That is for the reason that in the absence of authentication, possession of an Aadhaar number would suffice. Moreover, even if an individual does not possess an Aadhaar number, the mandate of Section 7 would be subserved by producing an application for enrolment. Section 3 which speaks of an entitlement to obtain an Aadhaar number stands in contrast to Section 7 under which an Aadhaar number may be required as a condition for the receipt of a subsidy, benefit or service. As an entitlement, Section 3 makes the possession of an Aadhaar number optional. Section 7 is an enabling power by which the central or state governments may make the requirement of an Aadhaar number compulsive or mandatory where a person desires a subsidy, benefit or service for which expenditure is incurred from or the receipt of which forms part of the Consolidated Fund of India. Section 7 acts as an overriding provision over Section 3.
47 The manner in which an authentication is carried out is elaborated upon by Section 8. Section 8 is in the following terms:
“Authentication of Aadhaar number.-
(1) The Authority shall perform authentication of the Aadhaar number of an Aadhaar number holder submitted by any requesting entity, in relation to his biometric information or demographic information, subject to such conditions and on payment of such fees and in such manner as may be specified by regulations.
(2) A requesting entity shall –
(a) unless otherwise provided in this Act, obtain the consent of an individual before collecting his identity information for the purposes of authentication in such manner as may be specified by regulations; and (b) ensure that the identity information of an individual is only used for submission to the Central Identities Data Repository for authentication.
(3) A requesting entity shall inform, in such manner as may be specified by regulations, the individual submitting his identify information for authentication, the following details with respect to authentication, namely:-
(a) the nature of information that may be shared upon authentication;
(b) the uses to which the information received during authentication may be put by the requesting entity; and
(c) alternatives to submission of identity information to the requesting entity.
(4) The Authority shall respond to an authentication query with a positive, negative or any other appropriate response sharing such identity information excluding any core biometric information.”
As we have noticed earlier, authentication involves a process in which the Aadhaar number, together with the demographic or biometric information, is submitted to the CIDR for verification and is verified to be correct or otherwise by the repository on the basis of the information available with it. Under subsection (1) of Section 8 authentication has to be performed on a request submitted by a requesting entity. The expression ‘requesting entity’ is defined in Section 2(u) as follows: “(u) “requesting entity” means an agency or person that submits the Aadhaar number, and demographic information or biometric information, of an individual to the Central Identities Data Repository for authentication.”
This definition also does not prohibit the engagement of private agencies for the process of authentication. Under sub-section (2) of Section 8, every requesting entity is bound to obtain the consent of the individual before collecting his or her identity information for the purpose of authentication. Moreover, the requesting entity must ensure that the identity information is submitted only for the purpose of authentication to the CIDR. Before the requesting entity submits the identity information for authentication, it is under a mandate of law to disclose (i) the nature of the information that may be shared upon authentication;
(ii) the use to which information received during authentication may be put; and
(iii) alternatives to the submission of identity information.59 During the course of authentication, UIDAI is required to respond to an authentication query with a positive, negative or appropriate response sharing such identity information excluding core biometric information.60 Core biometric information cannot be shared. The modes of authentication are as mentioned in Regulation 4 of the Aadhaar (Authentication) Regulations 2016.
It can be based on
(i) demographic information;
(ii) a one-time password with limited time validity;
(iii) biometrics or
(iv) multi-factor authentication (a combination of two or more of the above). The Requesting Agency chooses the mode according to its requirement. 48 UIDAI is the umbrella entity under the Aadhaar Act. The statutory backing to the authority of UIDAI to undertake the responsibility for the processes of enrolment and authentication and maintenance of CIDR has been provided under Chapter IV of the Act. Section 11 provides that the Central Government shall, by notification, establish UIDAI, a body corporate61, to be responsible for the processes of enrolment and authentication and perform such other functions as are assigned to it under the Act. The composition of UIDAI has been provided under Section 12: a Chairperson (appointed on part-time or full-time basis); two part-time Members, and the chief executive officer who shall be the Member- Secretary, to be appointed by the Central Government. Section 23 enunciates the powers and functions of the UIDAI. Sub-section (1) of Section 23 requires UIDAI to develop the policy, procedure and systems for issuing Aadhaar numbers to individuals and to perform authentication. Section 23(2) provides an inclusive list of the powers and functions of UIDAI: “(2) Without prejudice to sub-section (1), the powers and functions of the Authority, inter alia, include-
(a) specifying, by regulations, demographic information and biometric information required for enrolment and the processes for collection and verification thereof;
(b) collecting demographic information and biometric information from any individual seeking an Aadhaar number in such manner as may be specified by regulations;
(c) appointing of one or more entities to operate the Central Identities Data Repository;
(d) generating and assigning Aadhaar numbers to individuals;
(e) performing authentication of Aadhaar numbers;
(f) maintaining and updating the information of individuals in the Central Identities Data Repository in such manner as may be specified by regulations;
(g) omitting and deactivating of an Aadhaar number and information relating thereto in such manner as may be specified by regulations;
(h) specifying the manner of use of Aadhaar numbers for the purposes of providing or availing of various subsidies, benefits, services and other purposes for which Aadhaar numbers may be used;
(i) specifying, by regulations, the terms and conditions for appointment of Registrars, enrolling agencies and service providers and revocation of appointments thereof;
(j) establishing, operating and maintaining of the Central Identities Data Repository;
(k) sharing, in such manner as may be specified by regulations, the information of Aadhaar number holders, subject to the provisions of this Act;
(l) calling for information and records, conducting inspections, inquiries and audit of the operations for the purposes of this Act of the Central Identities Data Repository, Registrars, enrolling agencies and other agencies appointed under this Act;
(m) specifying, by regulations, various processes relating to data management, security protocols and other technology safeguards under this Act;
(n) specifying, by regulations, the conditions and procedures for issuance of new Aadhaar number to existing Aadhaar number holder;
(o) levying and collecting the fees or authorising the Registrars, enrolling agencies or other service providers to collect such fees for the services provided by them under this Act in such manner as may be specified by regulations;
(p) appointing such committees as may be necessary to assist the Authority in discharge of its functions for the purposes of this Act;
(q) promoting research and development for advancement in biometrics and related areas, including usage of Aadhaar numbers through appropriate mechanisms;
(r) evolving of, and specifying, by regulations, policies and practices for Registrars, enrolling agencies and other service providers;
(s) setting up facilitation centres and grievance redressal mechanism for redressal of grievances of individuals, Registrars, enrolling agencies and other service providers;
(t) such other powers and functions as may be prescribed.” Under Section 54, UIDAI is empowered to make regulations and rules consistent with the Act, for carrying out the provisions of the Act. Sub-section (2) of Section 54 provides that UIDAI may make regulations covering any of the following matters:
“(a) the biometric information under clause (g) and the demographic information under clause (k), and the process of collecting demographic information and biometric information from the individuals by enrolling agencies under clause (m) of section 2;
(b) the manner of verifying the demographic information and biometric information for issue of Aadhaar number under subsection (3) of section 3;
(c) the conditions for accepting an Aadhaar number as proof of identity of the Aadhaar number holder under sub-section (3) of section 4;
(d) the other categories of individuals under section 5 for whom the Authority shall take special measures for allotment of Aadhaar number;
(e) the manner of updating biometric information and demographic information under section 6;
(f) the procedure for authentication of the Aadhaar number under section 8;
(g) the other functions to be performed by the Central Identities Data Repository under section 10;
(h) the time and places of meetings of the Authority and the procedure for transaction of business to be followed by it, including the quorum, under sub-section (1) of section 19;
(i) the salary and allowances payable to, and other terms and conditions of service of, the chief executive officer, officers and other employees of the Authority under sub-section (2) of section 21;
(j) the demographic information and biometric information under clause (a) and the manner of their collection under clause (b) of sub-section (2) of section 23;
(k) the manner of maintaining and updating the information of individuals in the Central Identities Data Repository under clause (f) of sub-section (2) of section 23;
(l) the manner of omitting and deactivating an Aadhaar number and information relating thereto under clause (g) of sub-section (2) of section 23;
(m) the manner of use of Aadhaar numbers for the purposes of providing or availing of various subsidies, benefits, services and other purposes for which Aadhaar numbers may be used under clause (h) of sub-section (2) of section 23;
(n) the terms and conditions for appointment of Registrars, enrolling agencies and other service providers and the revocation of appointments thereof under clause (i) of subsection (2) of section 23;
(o) the manner of sharing information of Aadhaar number holder under clause (k) of sub-section (2) of section 23;
(p) various processes relating to data management, security protocol and other technology safeguards under clause (m) of sub-section (2) of section 23;
(q) the procedure for issuance of new Aadhaar number to existing Aadhaar number holder under clause (n) of subsection (2) of section 23;
(r) manner of authorising Registrars, enrolling agencies or other service providers to collect such fees for services provided by them under clause (o) of sub-section (2) of section 23;
(s) policies and practices to be followed by the Registrar, enrolling agencies and other service providers under clause (r) of sub-section (2) of section 23;
(t) the manner of accessing the identity information by the Aadhaar number holder under the proviso to sub-section (5) of section 28; (u) the manner of sharing the identity information, other than core biometric information, collected or created under this Act under sub-section (2) of section 29;
(v) the manner of alteration of demographic information under sub-section (1) and biometric information under sub-section (2) of section 31;
(w) the manner of and the time for maintaining the request for authentication and the response thereon under sub-section (1), and the manner of obtaining, by the Aadhaar number holder, the authentication records under sub-section (2) of section 32;
(x) any other matter which is required to be, or may be, specified, or in respect of which provision is to be or may be made by regulations.”
Section 11(1), read with Sections 23(2) and 54(2), indicates that UIDAI is the sole authority vested with the power and responsibility of carrying out numerous functions. These functions include:
(i) collection of demographic information and biometric information from individuals;
(ii) generating and assigning Aadhaar numbers to individuals;
(iii) performing authentication of Aadhaar numbers;
(iv) maintaining and updating the information of individuals in the CIDR;
(v) omitting and deactivating of an Aadhaar number;
(vi) specifying the manner of use of Aadhaar numbers for the purposes of providing or availing of various subsidies, benefits, services and other purposes;
(vii) specifying the terms and conditions for appointment of Registrars, enrolling agencies and service providers and revocation of appointments;
(viii) specifying various processes relating to data management, security protocols and other technological safeguards under the Act;
(ix) setting up facilitation centres and mechanisms for the redressal of the grievances of individuals, Registrars, enrolling agencies and other service providers; and
(x) other functions prescribed by the Central government. The Act does not set any limits within which the sole authority of UIDAI may operate. UIDAI has been conferred with discretionary powers as provided in the above provisions. The architecture of Aadhaar keeps UIDAI at the centre of all processes.
49 For the purpose of performing the functions of collecting, storing, securing, processing of information, delivery of Aadhaar numbers to individuals or performing authentication, clause (a) of Section 23(3) contemplates that UIDAI may enter into Memoranda of Understanding or agreements with the central or state governments, Union territories or other agencies. In discharging its functions, UIDAI may appoint, by notification, a number of Registrars, engage and authorise such agencies to collect, store, secure and process information or perform authentication or such other functions in relation to it, as may be necessary for the purposes of the Act (Section 23 (3) (b)). For the efficient discharge of its functions, UIDAI may also engage consultants, advisors and other persons as may be required (Section 23(4)).
These, like many other provisions, open the scope for the involvement of private entities in the Aadhaar project. This is also evident from Section 57 of the Act, which allows the use of the Aadhaar number, by the state, corporate entities or persons to establish the identity of an individual:
“57. Act not to prevent use of Aadhaar number for other purposes under law.- Nothing contained in this Act shall prevent the use of Aadhaar number for establishing the identity of an individual for any purpose, whether by the State or any body corporate or person, pursuant to any law, for the time being in force, or any contract to this effect:
Provided that the use of Aadhaar number under this section shall be subject to the procedure and obligations under section 8 and Chapter VI.” 50 The responsibility to ensure the security of identity information and authentication records of individuals has been placed on UIDAI.62 UIDAI is also required to ensure confidentiality of identity information and authentication records of individuals,63 except in circumstances, where disclosure of information is permitted by the Act.64 Section 28(3) requires UIDAI to take all necessary measures to ensure that the information in its possession or control, including information stored in the CIDR, is secured and protected against access, use or disclosure not permitted under the Act or regulations, and against accidental or intentional destruction, loss or damage.
For the purpose of maintaining the security and confidentiality of the information of individuals, UIDAI is also required, under Section 28(4), to:
“(a) adopt and implement appropriate technical and organisational security measures;
(b) ensure that the agencies, consultants, advisors or other persons appointed or engaged for performing any function of the Authority under this Act, have in place appropriate technical and organisational security measures for the information; and
(c) ensure that the agreements or arrangements entered into with such agencies, consultants, advisors or other persons, impose obligations equivalent to those imposed on the Authority under this Act, and require such agencies, consultants, advisors and other persons to act only on instructions from the Authority.”
Except where it has otherwise been provided in the Aadhaar Act, a burden is placed (under Section 28(5)) upon UIDAI, its officers, other employees (whether during service or thereafter), and any agency that maintains the CIDR not to reveal any information stored or the authentication record to anyone. An Aadhaar number holder, however, may request UIDAI to provide access to identity information excluding core biometric information in the manner as may be specified by regulations (proviso to Section 28(5)). Section 29 puts restrictions on sharing of information, collected or created under the Act. Sub-section (1) of Section 29 provides that:
“(1) No core biometric information, collected or created under this Act, shall be-
(a) shared with anyone for any reason whatsoever; or (b) used for any purpose other than generation of Aadhaar numbers and authentication under this Act.”
92 Sub-section (2) contemplates that the identity information, other than core biometric information, collected or created under the Act may be shared only in accordance with the provisions of the Act and in the manner as may be specified by regulations. A burden is placed, under Section 29(3), upon a requesting entity to ensure that any identity information available with it, is neither used for any purpose, other than that specified to the individual at the time of submitting identity information for authentication; nor disclosed further, except with the prior consent of the individual to whom such information relates. Sub-section (4) prohibits publishing, display or posting publicly of any Aadhaar number or core biometric information collected or created under the Act in respect of an Aadhaar number holder, except for such purposes as may be specified by the regulations. Section 30 contemplates that the biometric information collected and stored in an electronic form is to be deemed “sensitive personal data or information”.
The provision specifically relates to biometric information. The provision dilutes the protection that should be given to demographic information. Further, a statutory duty has been placed upon UIDAI to maintain authentication records in the manner and for a time period prescribed by regulations.65 The issue of maintenance of authentication records by UIDAI has been contentious and is dealt in a subsequent section titled “Proportionality”. A statutory right is provided to every Aadhaar number holder to obtain his authentication record in the manner specified by regulations.66 Section 32(3) prohibits UIDAI (either by itself or through any entity under its control) to collect, keep or maintain any information about the purpose of authentication.
51 The Aadhaar Act allows disclosure of individual information in limited circumstances. The manner and purpose for which information of individuals, including identity information or authentication records, can be disclosed has been provided under Section 33 of the Act. Section 33 states:
“(1) Nothing contained in sub-section (2) or sub-section (5) of section 28 or sub-section (2) of section 29 shall apply in respect of any disclosure of information, including identity information or authentication records, made pursuant to an order of a court not inferior to that of a District Judge: Provided that no order by the court under this sub-section shall be made without giving an opportunity of hearing to the Authority. (2) Nothing contained in sub-section (2) or sub-section (5) of section 28 and clause (b) of sub-section (1), sub-section (2) or sub-section (3) of section 29 shall apply in respect of any disclosure of information, including identity information or authentication records, made in the interest of national security in pursuance of a direction of an officer not below the rank of Joint Secretary to the Government of India specially authorised in this behalf by an order of the Central Government:
Provided that every direction issued under this sub-section, shall be reviewed by an Oversight Committee consisting of the Cabinet Secretary and the Secretaries to the Government of India in the Department of Legal Affairs and the Department of Electronics and Information Technology, before it takes effect:
Provided further that any direction issued under this subsection shall be valid for a period of three months from the date of its issue, which may be extended for a further period of three months after the review by the Oversight Committee.” The Aadhaar Act provides two categories: a “court order” and “in the interest of national security”, where the personal information of an individual can be disclosed. Under Section 31, in case any demographic information or biometric information of an Aadhaar number holder is found to be incorrect, is lost or changes subsequently, the Aadhaar number holder is required to request UIDAI to make an alteration in his or her record in the CIDR in the manner specified by regulations.
On receipt of a request for alteration of demographic or biometric information, UIDAI is vested with the power, subject to its satisfaction, to make alterations as required in the record relating to the Aadhaar number holder and to intimate the alteration to the holder. Subsection (4) of Section 31 prohibits alteration of any identity information in the CIDR except in the manner provided in the Act or regulations made in this behalf.
52 Chapter VII provides offences and penalties. Under Section 34, a penalty has been provided for impersonation at the time of enrolment. Section 35 creates a penalty for impersonation of the Aadhaar number holder by changing demographic or biometric information. Section 37 provides a penalty for disclosing identity information (which was collected in the course of enrolment or authentication). Under Section 38, a penalty for unauthorised access to the CIDR has been provided.
Section 38 provides thus: “Whoever, not being authorised by the Authority, intentionally,-
(a) accesses or secures access to the Central Identities Data Repository;
(b) downloads, copies or extracts any data from the Central Identities Data Repository or stored in any removable storage medium;
(c) introduces or causes to be introduced any virus or other computer contaminant in the Central Identities Data Repository;
(d) damages or causes to be damaged the data in the Central Identities Data Repository; (e) disrupts or causes disruption of the access to the Central Identities Data Repository;
(f) denies or causes a denial of access to any person who is authorised to access the Central Identities Data Repository;
(g) reveals any information in contravention of sub-section (5) of section 28, or shares, uses or displays information in contravention of section 29 or assists any person in any of the aforementioned acts;
(h) destroys, deletes or alters any information stored in any removable storage media or in the Central Identities Data Repository or diminishes its value or utility or affects it injuriously by any means; or
(i) steals, conceals, destroys or alters or causes any person to steal, conceal, destroy or alter any computer source code used by the Authority with an intention to cause damage, shall be punishable with imprisonment for a term which may extend to three years and shall also be liable to a fine which shall not be less than ten lakh rupees.”
Section 39 imposes a penalty for tampering with data in the CIDR. Sections 40 and 41 impose penalties on requesting and enrolment agencies in case they act in contravention of the obligations imposed upon them under the Act. Section 42 provides for a general penalty for an offence under the Act or the rules or regulations made thereunder, for which no specific penalty is provided under the Act. Under Section 43, when an offence has been committed by a company, every person who at the time the offence was committed was in charge of, and was responsible to the company for the conduct of the business of the company, as well as the company, shall be deemed to be guilty of the offence and shall be liable to be proceeded against and punished accordingly.
Section 44 indicates that the provisions of the Act would apply to any offence or contravention committed outside India by any person, irrespective of nationality. The power to investigate offences under the Act has been placed, under Section 45, on a police officer not below the rank of Inspector of Police. Section 47(1) of the Act puts a bar on the courts from taking cognizance of any offence punishable under the Act, except when a complaint is made by UIDAI or any officer or person authorised by it. The provision indicates that the scope of cognizance is limited. It does not allow an individual who finds that there is any violation under the Act, to initiate criminal proceedings.
The scope of grievance redressal under the Act is restrictive and works only on the action of UIDAI or a person authorised by it. UIDAI has set up a grievance redressal mechanism as contemplated by Section 23(2)(s) of the Aadhaar Act. There is no grievance redressal mechanism if any breach or offence is committed by UIDAI itself. The right of an individual to seek remedy under the Act if his/her rights are violated will be discussed subsequently. Under sub-Section (2), no court inferior to that of a Chief Metropolitan Magistrate or a Chief Judicial Magistrate can try any offence punishable under the Act. Section 48 empowers the Central Government to supersede UIDAI, in certain situations.
Under Section 50, UIDAI, in exercise of its powers or performance of its functions under the Act, shall be bound by the written directions on questions of policy of the Central Government. Section 51 vests power in UIDAI to delegate to any member, officer or any other person, its powers and functions under the Act (except the power under section 54) as it may deem necessary. Section 51 grants a wide discretion to the UIDAI to delegate any of its powers and functions. Section 55 requires every rule and regulation made under the Aadhaar Act to be laid down before each House of Parliament.
The Section states:
“55. Laying of rules and regulations before Parliament.- Every rule and every regulation made under this Act shall be laid, as soon as may be after it is made, before each House of Parliament, while it is in session, for a total period of thirty days which may be comprised in one session or in two or more successive sessions, and if, before the expiry of the session immediately following the session or the successive sessions aforesaid, both Houses agree in making any modification in the rule or regulation, or both the Houses agree that the rule or regulation should not be made, the rule or regulation shall thereafter have effect only in such modified form or be of no effect, as the case may be; so, however, that any such modification or annulment shall be without prejudice to the validity of anything previously done under that rule or regulation.” UIDAI needs to place the regulations framed by it before Parliament.
53 The architecture of Aadhaar is integral to the exercise of analyzing the reasonableness of the entire project. Whether the architecture addresses the concerns raised by the petitioners is an essential component of this exercise. The architecture of Aadhaar must pass the constitutional requirements of reasonableness and proportionality. This aspect will be dealt under the heading of “proportionality” in a subsequent part of this judgment.
E Passage of Aadhaar Act as a Money Bill
54 The petitioners challenge the constitutionality of the Aadhaar Act, contending that it could not have been passed as a Money Bill. According to the submission, the Aadhaar Act did not qualify as a Money Bill under Article 110 of the Constitution, and it legislates on matters which fall outside that provision. The Attorney General for India submitted that the Constitution accords finality to the decision of the Speaker as to whether a Bill is a Money Bill and hence the question whether the Aadhaar Act fulfils the requirements of being categorized as Money Bill is not open to judicial review. The Attorney General also urged that the Aadhaar Act does fall under Article 110. Article 110 provides thus:
“(1) For the purposes of this Chapter, a Bill shall be deemed to be a Money Bill if it contains only provisions dealing with all or any of the following matters, namely:-
(a) the imposition, abolition, remission, alteration or regulation of any tax;
(b) the regulation of the borrowing of money or the giving of any guarantee by the Government of India, or the amendment of the law with respect to any financial obligations undertaken or to be undertaken by the Government of India;
(c) the custody of the Consolidated Fund or the Contingency Fund of India, the payment of moneys into or the withdrawal of moneys from any such Fund;
(d) the appropriation of moneys out of the Consolidated Fund of India;
(e) the declaring of any expenditure to be expenditure charged on the Consolidated Fund of India or the increasing of the amount of any such expenditure;
(f) the receipt of money on account of the Consolidated Fund of India or the public account of India or the custody or issue of such money or the audit of the accounts of the Union or of a State; or
(g) any matter incidental to any of the matters specified in sub-clauses (a) to (f).
(2) A Bill shall not be deemed to be a Money Bill by reason only that it provides for the imposition of fines or other pecuniary penalties, or for the demand or payment of fees for licences or fees for services rendered, or by reason that it provides for the imposition, abolition, remission, alteration or regulation of any tax by any local authority or body for local purposes.
(3) If any question arises whether a Bill is a Money Bill or not, the decision of the Speaker of the House of the People thereon shall be final.
(4) There shall be endorsed on every Money Bill when it is transmitted to the Council of States under article 109, and when it is presented to the President for assent under article 111, the certificate of the Speaker of the House of the People signed by him that it is a Money Bill.”
55 The key questions before this Court are:
(i) Whether under Article 110(3), the decision of the Speaker of the Lok Sabha, that a Bill is a Money Bill, is immune from judicial review;
(ii) If the answer to
(i) is in the negative, whether the Aadhaar Act is a Money Bill under Article 110(1) of the Constitution; and
(iii) If the Bill to enact the Aadhaar Act was not a Money Bill, whether a declaration of unconstitutionality will result from its legislative passage as a Money Bill in the Lok Sabha.
E.I Judicial Review of the Speaker’s Decision
56 Article 109 provides for a special procedure in respect of Money Bills. It provides that a Money Bill shall not be introduced in the Council of States, the Rajya Sabha. After a Money Bill is introduced in the Lok Sabha and passed by it, the Bill has to be transmitted to the Rajya Sabha for its recommendations. Article 110(4) provides that when a ‘Money Bill’ is transmitted from the Lower House to the Upper House, it must be endorsed with a certificate by the Speaker of the Lower House that it is a Money Bill.
From the date of the receipt of the Money Bill, the Rajya Sabha is bound to return the Bill to the Lok Sabha, within a period of fourteen days, with its recommendations. The Lok Sabha has the discretion to “either accept or reject all or any of the recommendations” made by the Rajya Sabha.67 If the Lok Sabha accepts any of the recommendations of the Rajya Sabha, the Money Bill is deemed to have been passed by both Houses of the Parliament “with the amendments recommended” by the Rajya Sabha and accepted by the Lok Sabha.68
However, when the Lok Sabha “does not accept any of the recommendations” of the Rajya Sabha, the Money Bill is said to have been passed by both Houses in the form in which it was originally passed by the Lok Sabha.69 If a Money Bill after being passed by the Lok Sabha and transmitted to the Rajya Sabha for its recommendations is not returned to the Lok Sabha within a period of fourteen days, it is then deemed to have been passed by both the Houses of the Parliament in the form in which it was originally passed by the Lok Sabha.70 When a Money Bill has been passed by the Houses of the Parliament, Article 111 requires it to be presented to the President along with the Lok Sabha Speaker’s certificate for assent71. Article 117(1) also provides that a Bill “making provision for any of the matters specified in sub-clauses (a) to (f) of clause (1) of article 110” shall also not be introduced in the Rajya Sabha.
57 The Constitution contains corresponding provisions for Money Bills introduced in and passed by a state legislative assembly. Article 198 provides a special procedure for Money Bills in the state legislative assembly. Article 199(3) provides for the finality of the decision of the Speaker of the Legislative Assembly. Under Article 200, when a Money Bill has been passed by the State Legislature, it is to be presented to the Governor, along with the Speaker’s certificate, for assent.72 Article 107 contains provisions for the introduction and passing of Bills in general and provides thus:
“(1) Subject to the provisions of articles 109 and 117 with respect to Money Bills and other financial Bills, a Bill may originate in either House of Parliament.
(2) Subject to the provisions of articles 108 and 109, a Bill shall not be deemed to have been passed by the Houses of Parliament unless it has been agreed to by both Houses, either without amendment or with such amendments only as are agreed to by both Houses.
(3) A Bill pending in Parliament shall not lapse by reason of the prorogation of the Houses.
(4) A Bill pending in the Council of States which has not been passed by the House of the People shall not lapse on a dissolution of the House of the People.
(5) A Bill which is pending in the House of the People, or which having been passed by the House of the People is pending in the Council of States, shall, subject to the provisions of article 108, lapse on a dissolution of the House of the People.” 58 Ordinary bills can be passed only when they are agreed to by both Houses. Amendments suggested by one House have to be agreed upon by both the Houses for the bill to be passed.
Both Houses of Parliament have a vital role assigned by the Constitution in the passage of ordinary bills. Deviating from the important role which it assigns to the Rajya Sabha in the passage of legislation, the Constitution carves out a limited role for the Rajya Sabha in the passage of Money Bills.
59 The Constitution confers special powers on the Speaker of the Lok Sabha in the passage of a Money Bill. Ordinary bills (other than Money Bills) can originate in either House of Parliament. They can be scrutinised, debated in and amended in both the Houses of Parliament during the course of passage. A Bill is not regarded as being passed by Parliament until both the Houses agree to its passage without amendments or with the amendments as proposed. A constitutional discretion is conferred on the Speaker of the Lok Sabha to decide whether a Bill is a Money Bill.
When the Speaker of the Lok Sabha declares a Bill to be a Money Bill, the Rajya Sabha is left only with the option to make recommendations to the Bill within the deadline of fourteen days. Being only recommendations, they do not bind the Lok Sabha. They may either be accepted or rejected by the Lok Sabha. 60 The Rajya Sabha is a constitutional body in a bicameral legislature. The makers of the Constitution adopted bicameralism from Britain. The origin of the limited role that the Upper House has in the passing of a Money Bill can be traced to the British Parliament Act, 1911, which will be discussed in a subsequent part of this analysis.
The draftspersons of the Constitution were conscious of the impact of a misuse of institutional power. They provided for a detailed blue print of the architecture of constitutional governance. It is necessary to understand our constitutional history in order to comprehend the scope of the finality attributed to the Speaker’s decision on whether or not a Bill is a Money Bill. 61 The origins of the procedure of passing Money Bills in the United Kingdom are older than the Parliament Act of 1911.
The authoritative 104 treatise73, by Thomas Erskine May, on the law, privileges, proceedings and usage of Parliament in Britain dwells on the history of the evolution of the relationship between the House of Commons and the House of Lords with regard to their powers of taxation and in relation to national revenue and public expenditure.74 A grant imposed by the House of Commons would become law in effect, only after the assent of the House of Lords and of the Queen.75 While the House of Commons enjoyed the legal right to originate grants for nearly 300 years, the House of Lords was originally not precluded from amending a Bill. But in 167176 and 167877 respectively, the Commons passed two resolutions to curtail the powers of the House of Lords so that only the Commons had the sole right to direct or limit the scope of a Bill regarding taxation and government expenditure.
The House of Lords was excluded from altering any such Bill. The exclusion of the Lords was so strictly followed that the Commons even denied to the former, the power of authorising the taking of fees, imposing pecuniary penalties or of varying the mode of suing for them, or of applying them when recovered, though such provisions were necessary to give effect to the general enactments of a Bill.78 Since this strict enforcement was found to be “attended with unnecessary inconvenience”, it led to the adopting of a Standing Order in 1849 which accommodated space to the House of Lords for suggesting amendments on legislative issues.79 However, the constitutional skirmishes continued.
They eventually led to the passage of the Parliament Act of 1911, which essentially deprived the House of Lords of the right to reject Money Bills. 62 The Parliament Act 1911 was explicitly aimed at “regulating the relations between the two Houses of Parliament”80. The Preamble of the Act indicates that it was enacted for “restricting the existing powers of the House of Lords”81. Section 1(1) provides for the power of the House of Lords on Money Bills: “If a Money Bill, having been passed by the House of Commons, and sent up to the House of Lords at least one month before the end of the session, is not passed by the House of Lords without amendment within one month after it is so sent up to that House, the Bill shall, unless the House of Commons direct to the contrary, be present to His Majesty and become an Act of Parliament on the Royal Assent being signified, notwithstanding that the House of Lords have not consented to the Bill.” “Money Bill” was defined statutorily for the first time.
Section 1(2) provided: “A Money Bill means a Public Bill which in the opinion of the Speaker of the House of Commons contains only provisions dealing with all or any of the following subjects, namely, the imposition, repeal, remission, alteration, or regulation of taxation; the imposition for the payment of debt or other financial purposes of charges on the Consolidated Fund, [the National Loans Fund] or on money provided by Parliament, or the variation or repeal of any such charges; supply; the appropriation, receipt, custody, issue or audit of accounts of public money; the raising or guarantee of any loan or the repayment thereof; or subordinate matters incidental to those subjects or any of them.
In this subsection the expressions “taxation”, “public money”, and “loan” respectively do not include any taxation, money, or loan raised by local authorities or bodies for local purposes.” The use of the expression “means” in the definition of a Money Bill indicates it was exhaustively defined. A Bill would be a Money Bill, if the Speaker of the House of Commons opined that it contains “only” certain specific provisions. Under Section 1(3), when a Money Bill is sent up to the House of Lords and to Her Majesty for assent, it should be endorsed by a certificate of the Speaker of the House of Commons that it is a Money Bill. This sub-section also provides that before giving his certificate, the Speaker may consult “two members to be appointed from the Chairman’s Panel at the beginning of each Session by the Committee of Selection”. Therefore, the Speaker has to certify any bill which in his or her opinion falls within the definition of a Money Bill. Any bill containing provisions outside the definition would not be certified as a Money Bill. The Speaker does not certify a Bill until it has reached the form in which it will leave the House of Commons, that is, at the end of its Commons stage.
The Speaker can only decide whether or not to certify a Bill once it has passed the House.82 Section 3 of the 1911 Act provides finality to the certificate issued by the Speaker and renders it immune from judicial review. According to it: “Any certificate of the Speaker of the House of Commons given under this Act shall be conclusive for all purposes, and shall not be questioned in any court of law.”
(Emphasis supplied)
The Act provides finality to the decision of the Speaker of the House of Commons. By using the phrase “shall not be questioned in any court of law”, the Act grants immunity to the Speaker’s decision from judicial review.
The statutory concept of a ‘Money Bill’ and the Speaker’s certification of a Bill as a ‘Money Bill’ introduced by the Parliament Act, 1911 ultimately found its way into the Constitution of India, but with significant modifications. 63 In India, the categorization of Money Bills can be said to have begun from the Commonwealth of India Bill 1925, which was drafted by a National Convention comprised of 250 members, with Tej Bahadur Sapru as its Chairman. Article 36 of the Commonwealth Bill provided:
“36. (a) Any Bill which appropriates revenue or moneys for the ordinary annual services of the Government shall deal only with such appropriation.
(b) Bills imposing taxation
shall deal only with the imposition of taxes, and any provision therein dealing with any other matter shall be of no effect.
(c) Bills for the appropriation of revenues or moneys or imposing taxation shall be introduced only by a member of the Cabinet, and can only originate in the Legislative Assembly.” The Bill neither provided a definition of a Money Bill nor did it discuss the role of the Speaker of the Assembly of elected representatives. In its Madras session of December 1927, the Indian National Congress, as a response to the setting up of the Simon Commission (which did not have any Indian members) decided to set up an All Parties’ Conference to draft a Constitution for India. With Motilal Nehru as the Chairman of the Committee constituted by the All Parties’ Conference, a Report was prepared. Article 17 of the Nehru Report provided a definition of a Money Bill:
“17. A money bill means a bill which contains only provisions dealing with all or any of the following subjects, namely the imposition, repeal, remission, alteration or regulation of taxation; the imposition, for the payment of debt or other financial purposes, of charges on public revenues or monies, or the variation or repeal of any such charges; the supply, appropriation, receipt, custody, issue or audit of accounts of public money; the raising of any loan or the repayment thereof; or subordinate matters incidental to those subjects or any of them. In this definition the expression “taxation”, “public money” and “loan” respectively do not include any taxation, money or loan raised by local authorities or bodies for local purposes.”
The definition of a Money Bill in the Nehru Report, was drawn from the Parliament Act, 1911 in Britain. Article 18 of the Report provided that the “question whether a bill is or is not a money bill will be decided by the president of the House of Representatives”. The House of Representatives (the Lower House) was provided the final authority to either accept or reject the recommendations made by the Senate (the Upper House). Article 19 of the Report provided thus: “A money bill passed by the House of Representatives shall be sent to the Senate for its recommendations and it shall be returned not later than… days therefrom to the House of Representatives, which may pass it, accepting or rejecting all or any of the recommendations of the Senate; and the bill so passed shall be deemed to have been passed by both chambers.” While the Constituent Assembly of India was in session, the Socialist Party of India came up with a “Draft Constitution of the Republic of India”, based on its ideologies. Article 147 of its Draft Constitution provided:
“147.
(1) A Bill making provision-
(a) for imposing, abolishing, remitting, altering or regulating any tax ; or
(b) for regulating the borrowing of money, or giving any guarantee by the Government, or for amending the law with respect to any financial obligations undertaken or to be undertaken by the Government; or
(c) for declaring any expenditure to be expenditure charged on the public revenues, or for increasing the amount of any such expenditure shall be deemed as a money Bill and shall not be introduced or moved except on the recommendation of the Government.
(2) A Bill or amendment shall not be deemed to make provision for any of the purposes aforesaid by reason only that it provides for the Imposition of fines or other pecuniary penalties, or for the demand and payment of fees for licenses or fees for services rendered, or by reason that it provides for the imposition, abolition, remission, alteration, or regulation of tax by any local authority or body for local purposes.
(3) In case of dispute whether a Bill is a money Bill or not, the decision of the Speaker, or in his absence of the Deputy Speaker, shall be final.”
The Draft Constitution of the Socialist Party conferred a discretion on the Speaker of the Lower House, and in his absence, on the Deputy Speaker, to decide whether a Bill is a Money Bill. 64 There was another model present before the makers of the Indian Constitution. British India was governed by the provisions of the Government of India Act, 1935, which provided for two Houses of Parliament – the Council of States (Upper House) and Federal Assembly (Lower House). Section 37 of the Government of India Act 1935 made special provisions for financial bills:
“37.-(1) A Bill or amendment making provision- (a) for imposing or increasing any tax; or
(b) for regulating the borrowing of money or the giving of any guarantee by the Federal Government, or for amending the law with respect to any financial obligations undertaken or to be undertaken by the Federal Government ; or (c) for declaring any expenditure to be expenditure charged on the revenues of the Federation, or for increasing the amount of any such expenditure, shall not be introduced or moved except on the recommendation of the Governor-General, and a Bill making such provision shall not be introduced in the Council of State.”
Under the 1935 Act, there was no provision for a Speaker’s certificate regarding a Financial Bill. Section 38(1) authorized each House to make rules regulating its procedure and for the conduct of its business, subject to the provisions of the Act. A Financial Bill could be introduced only “on the recommendation of the Governor-General”. Section 41 provided a general immunity from judicial review on the “ground of any alleged irregularity of procedure”:
“41(1). The validity of any proceedings in the Federal Legislature shall not be called in question on the ground of any alleged irregularity of procedure.
(2) No officer or other member of the Legislature in whom powers are vested by or under this Act for regulating procedure or the conduct of business, or for maintaining order, in the Legislature shall be subject to the jurisdiction of any court in respect of the exercise by him of those powers.” The Constituent Assembly evidently had these legislative precedents relating to Money Bills which it would have considered while formulating its drafts.
65 While the proceedings of the Constituent Assembly were in motion, Sir B N Rau, as its constitutional advisor, prepared a memorandum of the Draft Constitution for the Union Constitution Committee. It envisaged a Parliament of the Union consisting of the President and two Houses-the Senate and the House of Representatives.83 One of the proposals discussed in the meetings of the Union Constitution Committee was that “Money Bills would originate in the House of the People and the power of the other House would be limited to making suggestions for amendment, which the House of the People could accept or reject”.
84 B Shiva Rao has recorded what transpired during the course of the proceedings of the Constituent Assembly: “The Draft also included provisions regarding legislative procedure, procedure in financial matters and general procedure for the conduct of business. No Bill could be submitted for the President’s assent unless it had been passed in identical form by both Houses. Except in the case of Money Bills, both Houses enjoyed equal powers; and difference between the two Houses were to be settled by a majority vote in a joint sitting of both Houses convened by the President… Money Bills were defined in the Draft as comprising Bills proposing the imposition or increase of any tax, regulating the borrowing of money by the Government of India or the giving of financial guarantees, or declaring any item of expenditure as ”charged” on the revenues, i.e. placing it outside the vote of the House of the People.
The general principle approved by the Constituent Assembly was that financial control over the executive would’ be – exercised by the House of the People. Accordingly the Draft provided that Money Bills could originate only in that House. The powers of the Council of States in the case of Money Bills were restricted to making suggestions for amendment. If these suggestions were, not accepted by the House of the People, or if the Council of States did not return a Bill within thirty days with its suggestions for amendment, the Bill would be ‘deemed to have been’ passed by both Houses in the form in which it was passed’ by the House of the People” and submitted to the President for his assent’.”85
66 The draft prepared by the Constitutional Advisor provided a definition of a Money Bill, which was inspired by Section 37 of the Government of India Act 1935, Section 53 of the Commonwealth of Australia Constitution Act 190086 and Article 22 of the Constitution of Ireland 1937.87 Article 75 of this draft of the Constitution provided that “if any question arises whether a Bill is a ‘money bill’ or not, the decision of the Speaker of the House of the People thereon shall be final.”88 Neither Section 37 of the Government of India Act 1935 nor Section 53 of the Commonwealth of Australia Constitution Act 1900 has a similar provision which accords legal finality to the decision of the Speaker.
The draft provision was similar to Article 22 of the Constitution of Ireland 1937, which provides:
“1. The Chairman of Dáil Éireann89 shall certify any Bill which, in his opinion, is a Money Bill to be a Money Bill, and his certificate shall, subject to the subsequent provisions of this section, be final and conclusive.
2. Seanad Éireann90, by a resolution, passed at a sitting at which not less than thirty members are present, may request the President to refer the question whether the Bill is or is not a Money Bill to a Committee of Privileges.
3. If the President after consultation with the Council of State decides to accede to the request he shall appoint a Committee of Privileges consisting of an equal number of members of Dáil Éireann and of Seanad Éireann and a Chairman who shall be a Judge of the Supreme Court: these appointments shall be made after consultation with the Council of State. In the case of an equality of votes but not otherwise the Chairman shall be entitled to vote.
4. The President shall refer the question to the Committee of Privileges so appointed and the Committee shall report its decision thereon to the President within twenty-one days after the day on which the Bill was sent to Seanad Éireann.
5. The decision of the Committee shall be final and conclusive.
6. If the President after consultation with the Council of State decides not to accede to the request of Seanad Éireann, or if the Committee of Privileges fails to report within the time hereinbefore specified the certificate of the Chairman of Dáil Éireann shall stand confirmed.”
(Emphasis supplied)
67 The draft prepared by the Advisor to the Constituent Assembly did not adopt the above provision in its entirety. It adopted the part on the finality of the certification of the Speaker on whether a Bill is a Money Bill. The Irish model of dispute resolution, which provided for a mechanism to review the Speaker’s certification, was not adopted.
Subsequently, in its report submitted to the President of the Constituent Assembly on 5 December 1947, the Expert Committee on Financial Provisions suggested an amendment to the draft provision, to the effect that: “When a Money Bill is sent from the Lower House to the Upper, a certificate of the Speaker of the Lower House saying that it is a Money Bill should be attached to, or endorsed on, the bill and a provision to that effect should be made in the Constitution on the lines of the corresponding provision in the Parliament Act, 1911. This will prevent controversies about the matter outside the Lower House.”91
(Emphasis supplied)
Certification of any Bill by the Speaker of the Lower House as a Money Bill, was envisaged for procedural simplicity to avoid causing confusion in the Upper House of Parliament. 68 The final provision which has assumed the form of Article 110 of the Constitution, does not contain the exact language used in the Act of 1911. The 1911 Act of the British Parliament consciously excluded judicial review of the certificate of the Speaker of the House of Commons. The intention of the British Parliament is clear from the specific language used in Section 3 of the Act. Section 3 accords finality to the decision of the Speaker by providing that any certificate of the Speaker of the House of Commons “shall be conclusive for all purposes, and shall not be questioned in any court of law”.
The certification of the Speaker is both conclusive and immune from judicial review. The framers of the Indian Constitution did not adopt this language. Rather, they chose to adopt the phrase “shall be final”. The phrase used in the Act of 1911 expressly excluded courts from exercising their power of judicial review over the decision of the Speaker of the House of Commons.
This language was used in the 1911 Act to put an end to the constitutional skirmishes experienced by the House of Lords and the House of Commons in Britain for more than five hundred years, leading to the enactment of the 1911 Act.92 The deviation from incorporating the language, used in the 1911 Act, into the Indian Constitution is reflective of the intention of our Constitution makers that they did not want to confer the same status on the power assigned to the Speaker of the Lok Sabha, as is provided to the Speaker of the House of Commons. Had their intention been otherwise, they would have used the same language as that provided under the 1911 Act.
Finality would operate as between the Houses of Parliament. It did not exclude judicial review by a constitutional Court. 69 The British legal system adopts the principle of parliamentary sovereignty. That is not so in India. Ours is a system founded on the supremacy of the Constitution. Judicial review is an essential component of constitutional supremacy. A Constitution Bench of this Court in Kalpana Mehta v Union of India93 has, while noticing this distinction, held:
“…The fundamental difference between the two systems lies in the fact that parliamentary sovereignty in the Westminster form of government in the UK has given way, in the Indian Constitution, to constitutional supremacy. Constitutional supremacy mandates that every institution of governance is subject to the norms embodied in the constitutional text.
The Constitution does not allow for the existence of absolute power in the institutions which it creates. Judicial review as a part of the basic features of the Constitution is intended to ensure that every institution acts within its bounds and limits.”94 70 The purpose of judicial review is to ensure that constitutional principles prevail in interpretation and governance. Institutions created by the Constitution are subject to its norms. No constitutional institution wields absolute power. No immunity has been attached to the certificate of the Speaker of the Lok Sabha from judicial review, for this reason. The Constitution makers have envisaged a role for the judiciary as the expounder of the Constitution.
The provisions relating to the judiciary, particularly those regarding the power of judicial review, were framed, as Granville Austin observed, with “idealism”95. Courts of the country are expected to function as guardians of the Constitution and its values. Constitutional courts have been entrusted with the duty to scrutinize the exercise of power by public functionaries under the Constitution. No individual holding an institutional office created by the Constitution can act contrary to constitutional parameters. Judicial review protects the principles and the spirit of the Constitution. Judicial review is intended as a check against arbitrary conduct of individuals holding constitutional posts.
It holds public functionaries accountable to constitutional duties. If our Constitution has to survive the vicissitudes of political aggrandisement and to face up to the prevailing cynicism about all constitutional institutions, notions of power and authority must give way to duties and compliance with the rule of law. Constitutional institutions cannot be seen as focal points for the accumulation of power and privilege. They are held in trust by all those who occupy them for the moment. The impermanence of power is a sombre reflection for those who occupy constitutional offices. The Constitution does not contemplate a debasement of the institutions which it creates.
The office of the Speaker of the House of People, can be no exception. The decision of the Speaker of the Lok Sabha in certifying a Bill as a Money Bill is liable to be tested upon the touchstone of its compliance with constitutional principles. Nor can such a decision of the Speaker take leave of constitutional morality.
71 Our Constitution does not provide absolute power to any institution. It sets the limits for each institution. Our constitutional scheme envisages a system of checks and balances. The power of the Speaker of the Lok Sabha, to decide whether a Bill is a Money Bill, cannot be untrammelled. The contention that the decision of Speaker is immune from judicial review and cannot be questioned, is contrary to the entire scheme of the Constitution, which is premised on transparency, non-arbitrariness and fairness. The phrase “shall be final” used in Article 110(3) has been adopted, as mentioned earlier, from Article 22 of the Irish Constitution. The provisions of Article 22 of the Irish Constitution provide a mechanism for review of the certificate issued by the Speaker. Recourse is provided under the Irish Constitution by which the members of the Upper House of the Irish Parliament can request the President of Ireland to refer the question of whether a Bill is a Money Bill, to a Committee of Privileges.
If the President refers the question to this Committee, the decision of the Committee stands “final and conclusive”. The members of the Constituent Assembly did not adopt this mechanism. Absence of this mechanism does not mean that the decision of the Speaker of the Lok Sabha cannot be subject to checks and balances, of which judicial review is an indispensable facet. The Speaker has to act within the domain, which the Constitution accords to the office of the Speaker. The power conferred on the Speaker of the Lok Sabha cannot be exercised arbitrarily, for it could damage the scheme of the Constitution. Judicial review is the ultimate remedy to ensure that the Speaker does not act beyond constitutional entrustment.
72 The scope of the phrase “shall be final” can also be understood by looking at the proceedings of the Constituent Assembly. The constitutional foundation of Article 110(4) is based upon a suggestion of the Expert Committee on Financial Provisions that when a Money Bill is transmitted from the Lower House to the Upper House, it should be endorsed by the Speaker’s certificate, so as to prevent any controversy “about the matter outside the Lower House”. Therefore, the finality provided to the decision of the Speaker as to whether a Bill is a Money Bill or not, is aimed at avoiding any controversy on the issue in the Rajya Sabha and before the President. Had it been intended to prevent the court from adjudicating upon the validity of the decision of the Speaker, the language of the Article would have made it explicit. Where a constitutional provision evinces a specific intent to exclude judicial review, clear words to that effect are used. Articles 243O(a)96, 243ZG(a)97 and 329(a) specifically use the phrase – “shall not be called in question in any court”. For instance, Article 329(a) provides thus: “Notwithstanding anything in this Constitution –
(a) the validity of any law relating to the delimitation of constituencies or the allotment of seats to such constituencies, made or purporting to be made under article 327 or article 328, shall not be called in question in any court.”
(Emphasis supplied)
73 In N P Ponnuswami v Returning Officer, Namakkal Constituency, Namakkal, Salem District98, a six judge Bench of this Court, while construing the provisions of Article 329, compared it to the preceding Articles, and held thus: “5…A notable difference in the language used in articles 327 and 328 on the one hand, and article 329 on the other, is that while the first two articles begin with the words “subject to the provisions of this Constitution”, the last article begins with the words “notwithstanding anything in this Constitution”. It was conceded at the Bar that the effect of this difference in language is that whereas any law made by Parliament under article 327, or by the State Legislature under article 328, cannot exclude the jurisdiction of the High Court under article 226 of the Constitution, that jurisdiction is excluded in regard to matters provided for in article 329.”99
74 In order to understand the scope of the finality attached to the Speaker’s decision under Article 110(3), it would be useful to analyse how in the case of other constitutional provisions, the words “shall be final” have been interpreted by this Court. Articles 217(3)100, 311(3)101 and paragraph 6(1) of the Tenth Schedule102 contain the phrase “shall be final”. In Union of India v Jyoti Prakash Mitter103, this Court held that it can examine the legality of an order passed by the President on the determination of the age of a Judge of the High Court under Article 217 (3) of the Constitution. The six judge Bench held:
“32…The President acting under Article 217(3) performs a judicial function of grave importance under the scheme of our Constitution.
He cannot act on the advice of his Ministers. Notwithstanding the declared finality of the order of the President the Court has jurisdiction in appropriate cases to set aside the order, if it appears that it was passed on collateral considerations or the rules of natural justice were not observed, or that the President’s judgment was coloured by the advice or representation made by the executive or it was founded on no evidence…Appreciation of evidence is entirely left to the President and it is not for the Courts to hold that on the evidence placed before the President on which the conclusion is founded, if they were called upon to decide the case they would have reached some other conclusion.”
104 The President was held to perform a judicial function in making a determination under Article 217(3). The question of finality under Article 311(3) was dealt with by a Constitution Bench of this Court in Union of India v Tulsiram Patel105. The Court held that the finality given to the decision of the disciplinary authority by Article 311(3) that it is not reasonably practicable to hold an enquiry, is not binding upon the Court so far as its power of judicial review is concerned. The constitutional validity of the provisions contained in the Tenth Schedule to the Constitution came up for consideration before a Constitution Bench of this Court in Kihoto Hollohan v Zachillhu106.
The Constitution Bench held that the power vested in the Speaker or the Chairman under the Schedule, is a judicial power, and was amenable to judicial review: “111…That Paragraph 6(1) of the Tenth Schedule, to the extent it seeks to impart finality to the decision of the Speakers/Chairmen is valid. But the concept of statutory finality embodied in Paragraph 6(1) does not detract from or abrogate judicial review under Articles 136, 226 and 227 of the Constitution in so far as infirmities based on violations of constitutional mandates, mala fides, noncompliance with Rules of Natural Justice and perversity, are concerned.”107
(Emphasis supplied)
The Bench had also clarified that:
“101…The principle that is applied by the courts is that in spite of a finality clause it is open to the court to examine whether the action of the authority under challenge is ultra vires the powers conferred on the said authority. Such an action can be ultra vires for the reason that it is in contravention of a mandatory provision of the law conferring on the authority the power to take such an action. It will also be ultra vires the powers conferred on the authority if it is vitiated by mala fides or is colourable exercise of power based on extraneous and irrelevant considerations…”
108 Undoubtedly, the finality clauses contained in Article 217(3), 311(3) and in paragraph 6(1) of the Tenth Schedule were held not to exclude judicial review since the essential nature of the power is judicial. A constitutional function is entrusted to the Speaker to certify a Bill as a Money Bill under Article 110(3), to which the attributes of a judicial power do not apply. Indeed, the power which is entrusted to the Speaker under Article 110(3) is integral to the legislative process. But, the fact that the authority which a constitutional functionary exercises is not of a judicial character, is not sufficient to lead to the conclusion that a finality clause governing the exercise of that power makes it immune from judicial review. Where the entrustment of the power is subject to the due fulfilment of constitutional norms, the exercise of jurisdiction is amenable to judicial review, to the extent necessary to determine whether there has been a violation of a constitutional mandate.
The nature and extent of judicial review would undoubtedly vary from a situation where finality has been attached to a judicial, administrative or quasi-judicial power. However, a clause on finality notwithstanding, it is open to the constitutional court to determine as to whether there has been a violation of a constitutional mandate as a result of which the decision suffers from a constitutional infirmity. The entrustment of a constitutional function to the Speaker under Article 110(3) to certify a Bill as a Money Bill is premised on the fulfilment of the norms stipulated in Article 110(1). A certification can be questioned on the ground that the Bill did not fulfil the conditions stipulated in Article 110(1) to be designated as a Money Bill. If that is established, the certification would be contrary to constitutional mandate. Whether that is so can be judicially scrutinized.
75 The notion that an entrustment of power is absolute has a colonial origin. Law under a colonial regime was not just an instrument to maintain order but was a source of subordination. Recognition of the vesting of absolute authority was but a reflection of the premise that those who ruled could not be questioned. Those who were ruled had to accept the authority of the ruler. Nothing can be as divorced from constitutional principle as these normative foundations of colonial law and history. The notion that power is absolute is inconsistent with a Constitution which subjects the entrustment of functions to public functionaries to the restraints which accompany it.
Our law must recognise the need to liberate its founding principles from its colonial past. The Court should not readily accept the notion that the authority vested in a constitutional functionary is immune from judicial review. In the absence of a specific exclusion of judicial review, none can be implied. Moreover, any exclusion of judicial review must be tested on the anvil of its functionality. A specific exclusion of judicial review, in order to be valid, must serve a constitutional function.
The test of functionality must relate to whether an exclusion of review is necessary to fulfil the overarching need for the proper discharge of a constitutional role. Exclusion of review, to be valid, must fulfil the requirement of a constitutional necessity. Its purpose cannot be to shield an excess of power from being questioned before the Court. Nor is the fact that a power is vested in a high functionary a ground to shield it from scrutiny. The ultimate test is whether the exclusion of judicial review is express and specific and, whether such an exclusion is designed to achieve a constitutional purpose that meets the test of functionality, assessed in terms of a constitutional necessity. In the seventh decade of the republic, our interpretation of the Constitution must subserve the need to liberate it from its colonial detritus.
This approach was adopted by a seven judge Bench of this Court in Krishna Kumar Singh v State of Bihar109. While interpreting the ordinance making power of the Governor, the Court held that the interpretation of the Constitution must be “carefully structured” to ensure that the power remains what the framers of our Constitution intended it to be.
The Bench held: “91…The issue which needs elaboration is whether an ordinance which by its very nature has a limited life can bring about consequences for the future (in terms of the creation of rights, privileges, liabilities and obligations) which will enure beyond the life of the ordinance. In deciding this issue, the court must adopt an interpretation which furthers the basic constitutional premise of legislative control over ordinances. The preservation of this constitutional value is necessary for parliamentary democracy to survive on the sure foundation of the Rule of law and collective responsibility of the executive to the legislature. The silences of the Constitution must be imbued with substantive content by infusing them with a meaning which enhances the Rule of law.
To attribute to the executive as an incident of the power to frame ordinances, an unrestricted ability to create binding effects for posterity would set a dangerous precedent in a parliamentary democracy. The court’s interpretation of the power to frame ordinances, which originates in the executive arm of government, cannot be oblivious to the basic notion that the primary form of law making power is through the legislature…”110
(Emphasis supplied)
The ordinance making power was held to be an exceptional power to meet a “constitutional necessity”. 76 The marginal note to Article 122 is: “Courts not to inquire into proceedings of Parliament”. The Article reads thus:
“122. (1) The validity of any proceedings in Parliament shall not be called in question on the ground of any alleged irregularity of procedure.
(2) No officer or member of Parliament in whom powers are vested by or under this Constitution for regulating procedure or the conduct of business, or for maintaining order, in Parliament shall be subject to the jurisdiction of any court in respect of the exercise by him of those powers.” This Court must deal with the question whether the Speaker’s decision under Article 110(3) is protected by Article 122. Article 122 prohibits courts from examining the validity of any proceedings in Parliament on the ground that there was “any alleged irregularity of procedure”.
The content of the expression “procedure” referred to in the Article, is indicated in Article 118 of the Constitution. The marginal note to Article 118 provides for “Rules of procedure”. Article 118 provides as follows:
118. (1) Each House of Parliament may make rules for regulating, subject to the provisions of this Constitution, its procedure and the conduct of its business.
(2) Until rules are made under clause (1), the rules of procedure and standing orders in force immediately before the commencement of this Constitution with respect to the Legislature of the Dominion of India shall have effect in relation to Parliament subject to such modifications and adaptations as may be made therein by the Chairman of the Council of States or the Speaker of the House of the People, as the case may be.
(3) The President, after consultation with the Chairman of the Council of States and the Speaker of the House of the People, may make rules as to the procedure with respect to joint sittings of, and communications between, the two Houses.
(4) At a joint sitting of the two Houses the Speaker of the House of the People, or in his absence such person as may be determined by rules of procedure made under clause (3), shall preside.”
(Emphasis supplied)
77 Articles 118 to 122 are covered under the rubric of the general heading- “Procedure Generally”. Article 118 provides for rules to be made by each House of Parliament for regulating the procedure and conduct of its business. The Article subjects these contemplated rules to the provisions of the Constitution. The provision does not indicate that these rules will stand above the Constitution. They are, on the contrary, subject to the Constitution. The rules framed under Article 118, are procedural in nature. The procedure contemplated under Articles 118 to 122 is distinct from substantive constitutional requirements.
The obligation placed on the Speaker of the Lok Sabha to certify whether a Bill is a Money Bill is not a mere matter of “procedure” contemplated under Article 122. It is a constitutional requirement, which has to be fulfilled according to the norms set out in Article 110. Article 122 will not save the action of the Speaker, if it is contrary to constitutional norms provided under Article 110. The Court, in the exercise of its power of judicial review, can adjudicate upon the validity of the action of the Speaker if it causes constitutional infirmities. Article 122 does not envisage exemption from judicial review, if there has been a constitutional infirmity. The Constitution does not endorse a complete prohibition of judicial review under Article 122.
It is only limited to an “irregularity of procedure”. 78 This Court has on several occasions restricted the scope of the bar provided under Article 122 (and under corresponding Article 212 for the States) and has distinguished an “irregularity of procedure” from “illegality”. In Special Reference No. 1 of 1964111, a seven judge Bench of this Court brought home that distinction in the context of Article 212(1) with the following observations:
“61…Article 212(2) confers immunity on the officers and members of the Legislature in whom powers are vested by or under the Constitution for regulating procedure or the conduct of business, or for maintaining order, in the Legislature from being subject to the jurisdiction of any court in respect of the exercise by him of those powers.
Art. 212(1) seems to make it possible for a citizen to call in question in the appropriate court of law the validity of any proceedings inside the legislative chamber if his case is that the said proceedings suffer not from mere irregularity of procedure, but from an illegality. If the impugned procedure is illegal and unconstitutional, it would be open to be scrutinised in a court of law, though such scrutiny is prohibited if the complaint against the procedure is no more than this that the procedure was irregular…”
(Emphasis supplied)
In Ramdas Athawale v Union of India112 (“Ramdas Athawale”), a Constitution Bench of this Court extended the above formulation to Article 122 of the Constitution:
“36.This Court Under Article 143, Constitution of India, In re (Special Reference No. 1 of 1964) [AIR 1965 SC 745 : (1965) 1 SCR 413] (also known as Keshav Singh case [AIR 1965 SC 745 : (1965) 1 SCR 413] ) while construing Article 212(1) observed that it may be possible for a citizen to call in question in the appropriate Court of law, the validity of any proceedings inside the Legislature if his case is that the said proceedings suffer not from mere irregularity of procedure, but from an illegality. If the impugned procedure is illegal and unconstitutional, it would be open to be scrutinized in a Court of law, though such scrutiny is prohibited if the complaint against the procedure is no more than this that the procedure was irregular.
The same principle would equally be applicable in the matter of interpretation of Article 122 of the Constitution.”113 A Constitution Bench of this Court reaffirmed the distinction between a “procedural irregularity” and an “illegality” in Raja Ram Pal v Hon’ble Speaker, Lok Sabha114 (“Raja Ram Pal”). The Bench held that courts are not prohibited from exercising their power of judicial review to examine any illegality or unconstitutionality in the procedure of Parliament: “386…Any attempt to read a limitation into Article 122 so as to restrict the court’s jurisdiction to examination of the Parliament’s procedure in case of unconstitutionality, as opposed to illegality would amount to doing violence to the constitutional text. Applying the principle of “expressio unius est exclusio alterius” (whatever has not been included has by implication been excluded), it is plain and clear that prohibition against examination on the touchstone of “irregularity of procedure” does not make taboo judicial review on findings of illegality or unconstitutionality…115 398… the Court will decline to interfere if the grievance brought before it is restricted to allegations of “irregularity of procedure”.
But in case gross illegality or violation of constitutional provisions is shown, the judicial review will not be inhibited in any manner by Article 122, or for that matter by Article 105.”116 The Court distinguished the constitutional background in India from that of England, holding that while England has adopted a regime of exclusive parliamentary dominance, India is governed by a system of checks and balances provided in the Constitution: “366.The touchstone upon which Parliamentary actions within the four-walls of the Legislature were examined was both the constitutional as well as substantive law.
The proceedings which may be tainted on account of substantive illegality or unconstitutionality, as opposed to those suffering from mere irregularity thus cannot be held protected from judicial scrutiny by Article 122(1) in as much as the broad principle laid down in Bradlaugh [(1884) 12 QBD 271] acknowledging exclusive cognizance of the Legislature in England has no application to the system of governance provided by our Constitution wherein no organ is sovereign and each organ is amenable to constitutional checks and controls, in which scheme of things, this Court is entrusted with the duty to be watchdog of and guarantor of the Constitution.”117
(Emphasis supplied)
The principle which emerges from these decisions is that the decision of the Speaker is amenable to judicial review, if it suffers from illegality or from a violation of constitutional provisions.
79 The Attorney General advanced the submission that this Court has on previous occasions refrained from scrutinizing the decision of the Speaker on whether a Bill is a Money Bill. Those decisions require discussion for adjudicating the present case. In Mangalore Ganesh Beedi Works v State of Mysore118 (“Mangalore Beedi”), a new system of coinage was introduced by amending the Indian Coinage Act. Under the new system, while one rupee was divided into a hundred naya paisas, the old legal tender of sixteen annas or sixty four pice remained legal tender equivalent to one hundred naya paisas.
The appellant, which was a firm registered under the Mysore Sales Tax Act, had to pay an additional amount as sales tax due to change in the currency. It was argued that by the substitution of 2 naya paisas (the new currency) in place of 3 pies (the old currency) as tax, there was a change in the tax imposed by the Mysore Sales Tax Act, which could only have been done by passing a Money Bill under Articles 198, 199 and 207 of the Constitution and since no Money Bill was introduced or passed for the enhancement of the tax, the tax was illegal and invalid. The contention, therefore, was that the procedure envisaged for passing a Money Bill ought to have been, but was not, followed. The Constitution Bench dismissed the appeal, holding that the substitution of a new coinage i.e. naya paisas in place of annas, pice and pies did not amount to an enhancement of tax.
It was held to be merely a substitution of one coinage by another of equivalent value. This Court held that the levy of tax in terms of naya paisas was not unconstitutional nor was it a taxing measure but it dealt merely with the conversion of the old coinage into new coinage. Having held this, the Bench also remarked:
“5…Even assuming that it is a taxing measure its validity cannot be challenged on the ground that it offends Arts. 197 to 199 and the procedure laid down in Art. 202 of the Constitution. Article 212 prohibits the validity of any proceedings in a legislature of a State from being called in question on the ground of any alleged irregularity of procedure and Art. 255 lays down that requirements as to recommendation and previous sanction are to be regarded as matters of procedure only…” The Court having found that a substitution of coinage did not result in an enhancement of tax, Article 199 was not attracted. The legislative measure was not a Money Bill. Once that was the case, the subsequent observations (extracted above) proceeded on an assumption: that even if it were a taxing measure, it would be saved by Article 255.
The court having held that no enhancement of tax was involved in a mere substitution of coinage, the alternative hypothesis is not a part of the ratio and was unnecessary. The ratio was that substitution of a new coinage did not amount to a Money Bill. The decision of the Constitution Bench in Mangalore Beedi dealt with the contention that a Money Bill was unconstitutionally passed as an ordinary Bill. The Bench held that substitution of coinage did not make it a Money Bill. The decision contains a general observation regarding the immunity of proceedings in a state legislature. A scholarly article119 has correctly referred to the general remarks made in Mangalore Beedi as unnecessary and not the ratio since the issue was already decided on merits, by holding that the substitution of coinage was not an enhancement of tax.
80 A three judge Bench of this Court in Mohd Saeed Siddiqui v State of Uttar Pradesh120 (“Mohd Saeed Siddiqui”) dealt with the constitutional validity of the Uttar Pradesh Lokayukta and Up-Lokayuktas (Amendment) Act, 2012. Section 5(1) of the unamended Act provided a term of six years for the Lokayukta. Section 5(3) provided that on ceasing to hold office, the Lokayukta or Up-Lokayukta shall be ineligible for further appointment.
The new State government, which came in office, introduced a Bill which was passed as the Uttar Pradesh Lokayukta and Up-Lokayuktas (Amendment) Act, 2012, by which the term of the U.P. Lokayukta and Up-Lokayukta was extended from six years to eight years or till the successor enters upon office. The Amendment Act also limited the ineligibility of the Lokayuktas or Up- Lokayuktas for further appointment under the Government of Uttar Pradesh. The Amendment Act was challenged on the ground that it was passed as a Money Bill when, on the face of it, it could never have been called a Money Bill under Article 199 of the Constitution. The Bench rejected the petition holding that the question “whether a Bill is a Money Bill or not can be raised only in the State Legislative Assembly by a member thereof when the Bill is pending in the State Legislature and before it becomes an Act”. It relied upon the observations made in Mangalore Beedi, to formulate following principles:
“(i) the validity of an Act cannot be challenged on the ground that it offends Articles 197 to 199 and the procedure laid down in Article 202;
(ii) Article 212 prohibits the validity of any proceedings in a Legislature of a State from being called in question on the ground of any alleged irregularity of procedure; and
(iii) Article 255 lays down that the requirements as to recommendation and previous sanction are to be regarded as a matter of procedure only. It is further held that the validity of the proceedings inside the Legislature of a State cannot be called in question on the allegation that the procedure laid down by the law has not been strictly followed and that no Court can go into those questions which are within the special jurisdiction of the Legislature itself, which has the power to conduct its own business.” The judgment also made a reference to the seven judge Bench decision in Pandit MSM Sharma v Dr Shree Krishna Sinha121 (“MSM Sharma”). The “proceedings of the Legislature” were held to include “everything said or done in either House” in the transaction of parliamentary business. Relying upon Articles 212 and 255, the Bench accorded finality to the decision of the Speaker:
“43. As discussed above, the decision of the Speaker of the Legislative Assembly that the Bill in question was a Money Bill is final and the said decision cannot be disputed nor can the procedure of the State Legislature be questioned by virtue of Article 212. Further, as noted earlier, Article 255 also shows that under the Constitution the matters of procedure do not render invalid an Act to which assent has been given to by the President or the Governor, as the case may be. Inasmuch as the Bill in question was a Money Bill, the contrary contention by the Petitioner against the passing of the said Bill by the Legislative Assembly alone is unacceptable.”122
Making a passing reference to the decision of the Constitution Bench in Raja Ram Pal, the Bench opined that even if it is established that there was some infirmity in the procedure in the enactment of the Amendment Act, it will be protected by Article 255 of the Constitution. 81 Subsequently, a two judge Bench of this Court in Yogendra Kumar Jaiswal v State of Bihar123 (“Yogendra Kumar”) dealt with the constitutional validity of the Orissa Special Courts Act, 2006. The law was enacted by the State legislature, keeping in view the accumulation of properties disproportionate to their known sources of income by persons who have held or hold high political and public offices. The legislature provided special courts for speedy trial of certain classes of offences and for confiscation of properties. The appellants, who were public servants and facing criminal cases, challenged the Act on the ground that it was introduced in the State Assembly as a Money Bill though it did not have any characteristics of a Money Bill under Article 199 of the Constitution. The Court dismissed the petitions, following the decision in Mohd Saeed Siddiqui. It held that:
“43. In our considered opinion, the authorities cited by the learned Counsel for the Appellants do not render much assistance, for the introduction of a bill, as has been held in Mohd. Saeed Siddiqui (supra), comes within the concept of “irregularity” and it does come with the realm of substantiality. What has been held in the Special Reference No. 1 of 1964 (supra) has to be appositely understood. The factual matrix therein was totally different than the case at hand as we find that the present controversy is wholly covered by the pronouncement in Mohd. Saeed Siddiqui (supra) and hence, we unhesitatingly hold that there is no merit in the submission so assiduously urged by the learned Counsel for the Appellants.”124 Special Reference No. 1 of 1964 was distinguished in Yogendra Kumar. Article 255 provides: “No Act of Parliament or of the Legislature of a State, and no provision in any such Act, shall be invalid by reason only that some recommendation or previous sanction required by this Constitution was not given, if assent to that Act was given-
(a) where the recommendation required was that of the Governor, either by the Governor or by the President;
(b) where the recommendation required was that of the Rajpramukh, either by the Rajpramukh or by the President;
(c) where the recommendation or previous sanction required was that of the President, by the President.” 82 Article 255 speaks about a situation where a “recommendation or previous sanction” is required to be given by the Governor, Rajpramukh or, as the case may be, by the President. The absence of a recommendation or previous sanction will not invalidate the law, where the Act has received the assent of the Governor or the President. Subsequent assent, in other words, cures the absence of recommendation or sanction. Article 255 is in no way related to the decision or certificate of the Speaker of the Lok Sabha or of the State Legislative Assembly on whether a Bill is a Money Bill.
Moreover, Article 255 does not apply to Articles 110 for the simple reason that the latter does not embody either a previous sanction or recommendation. Article 255 does not envisage superseding the role of the Upper House of Parliament or the State Legislature. Mohd Saeed Siddiqui proceeds on an erroneous understanding of Article 255. Mohd Saeed Siddiqui was followed in Yogendra Kumar. These two judgments cite the same three articles – Articles 199,125 212,126 and 255, to refrain from questioning the conduct of the Speaker, without noticing that Article 255 does not apply there. Further, MSM Sharma, which was referred in Mohd Saeed Siddiqui was discussed in the Special Reference to hold that the validity of any proceedings in a legislative chamber can be questioned if such proceedings suffer from illegality. The consistent thread which emerges from the judgments in Special Reference, Ramdas Athawale and Raja Ram Pal is that the validity of proceedings in Parliament or a State Legislature can be subject to judicial review on the ground that there is an illegality or a constitutional violation.
Moreover, the judgment in Yogendra Kumar followed Mohd Saeed Siddiqui. Siddiqui was based on an erroneous understanding of Mangalore Beedi. The decision of the Speaker under Articles 110(3) and 199(3) is not immune from judicial review. The three judge Bench decision in Mohd Saeed Siddiqui and the two judge Bench decision in Yogendra Kumar are overruled. 83 Barring judicial review of the Lok Sabha Speaker’s decision would render a certification of a Bill as a Money Bill immune from scrutiny, even where the Bill does not, objectively speaking, deal only with the provisions set out in Article 110(1). The decision of the Speaker of the Lok Sabha whether a Bill is a Money Bill impacts directly upon the constitutional role which will be discharged by the Rajya Sabha in relation to it.
The Lok Sabha alone does not represent Parliament. The Indian Parliament is bicameral. The Constitution envisages a special role for the Rajya Sabha. In order to truly understand the relevance of the Rajya Sabha in the Indian context, an analysis of major bicameral systems is necessary, as an exercise in comparative law.
84 Bicameral legislatures are not unique to either the Presidential or Parliamentary forms of government. Democracies with a Presidential form of government have adopted bicameral legislatures, the United States being the leading example. Among Parliamentary democracies, India and the UK have adopted bicameral legislatures. They are predominant in federal countries. Where second chambers exist, they vary in terms of powers and composition. Together, their powers and composition shape the impact that they have on legislation.
127 The phenomenon of the bicameral system has two different historic origins. It was first established in England, and later in the US.
128 Both these models have been replicated across the globe. 85 Britain developed some of the earliest institutional practices that came to be emulated through the Western world. A separate powerful legislature was initiated when King John in 1215 gave a written commitment to seek the consent of Parliament to levy taxes to which he was entitled by feudal prerogative. Over the next five centuries, the British Parliament was transformed from an institution summoned at the desire of the ruler to one which met on regular occasions to develop policy inclinations independent of the wishes of the ruler.
129 In the fourteenth century, Parliament was divided into two chambers: one chamber (the House of Lords) in which debate took place with the feudal lords and a second chamber (the House of Commons) where the citizens were represented.130 The upper chamber of the British Parliament, the Lords, comprised of hereditary peers (whose number varied with the discretion of the King to create them).
The lower chamber, the Commons, represented individuals satisfying a substantial property requirement. The two chambers in Britain reflected a kind of class division. Before the beginning of the eighteenth century, several factors such as civil war, regicide, experimentation with a republic, and the restoration of the titular monarch caused power to be permanently shifted from the King to Parliament.131 Around the same time, the British colonies in North America were crafting institutions of their own. Colonial legislatures were being conceptualized on similar lines, with some exceptions, to British Parliament. The Constitution for the newly formed United States adopted a bicameral system.132
The legislature in the United States was innovative, for it created a bicameral arrangement that replaced a class basis (as was in existence in Britain) for chamber representation with a modified federal basis. The Constitutional Convention of 1787 had provided for a lower chamber, a directly-elected House of Representatives, where each voter had an equal vote in elections, and an upper chamber, a Senate, to which each state could send two members, elected indirectly by the state parliaments. The Convention was a compromise between those who wanted a parliament in which the states, irrespective of their population size, would have an equal voice, and those who wanted a Parliament for the newly formed federal nation where the participating states were represented in proportion to the size of their population. A system with two differently composed chambers was ultimately chosen to be the only way out of the deadlock.133
The rationale for a bicameral legislature comprising of a directly elected Lower House and an indirectly elected Upper House was best articulated by James Madison, in the Federalist Papers:
“First… a senate, as a second branch of the legislative assembly, distinct from, and dividing the power with, a first, must be in all cases a salutary check on the government. It doubles the security to the people, by requiring the concurrence of two distinct bodies in schemes of usurpation or perfidy, where the ambition or corruption of one would otherwise be sufficient… Second.
The necessity of a senate is not less indicated by the propensity of all single and numerous assemblies to yield to the impulse of sudden and violent passions, and to be seduced by factious leaders into intemperate and pernicious resolutions…
Third. Another defect to be supplied by a senate lies in a want of due acquaintance with the objects and principles of legislation. It is not possible that an assembly of men called for the most part from pursuits of a private nature, continued in appointment for a short time, and led by no permanent motive to devote the intervals of public occupation to a study of the laws, the affairs, and the comprehensive interests of their country, should, if left wholly to themselves, escape a variety of important errors in the exercise of their legislative trust… A good government implies two things: first, fidelity to the object of government, which is the happiness of the people; secondly, a knowledge of the means by which that object can be best attained…
Fourth. The mutability in the public councils arising from a rapid succession of new members, however qualified they may be, points out, in the strongest manner, the necessity of some stable institution in the government…”
134 Madison conceptualized that the second chamber would fulfil significant roles:
(a) it would provide the certainty that the government will not neglect its obligations to its constituents, as the chamber provides an extra check on it;
(b) it can curb the actions of the other chamber if it gives into the urge to follow ‘sudden and pronounced sentimental reactions’;
(c) it can meet the need for expertise in the framing of laws and the interests of the country, and thus help to avoid legislative mistakes; and
(d) it can be a factor for stability that ensures continuity in the administration of the country.
86 Bicameralism, in both systems, emerged as a development associated with the changing conceptions of the state. The literature on bicameralism has highlighted the importance of having a second chamber in the legislature of a state. William Riker has emphasized that a bicameral structure acts as a control over the tyranny of a majority.135 Levmore similarly echoes this thought:
“At the very least, if the two chambers consider an issue simultaneously, one chamber’s agenda setter will be at the mercy of the order of consideration in the second chamber. Bicameralism can thus be understood as an antidote to the manipulative power of the convenor, or agenda setter, when faced with cycling preferences.”136
A study137 commissioned by the Dutch Ministry of the Interior and Kingdom Relations analysed the design of the bicameral system in several countries. The study consulted constitutional texts and literature on the evolution of bicameralism and came to the finding that: “Historically, the creation of bicameral systems, both in the federal and the aristocratic variant, always was a concession to those (states or estates) who risked losing power in the new setting. In emerging democracies, and up until the present day, the choice of a bicameral system appears as a means of dispelling fear about the consequences of democratisation and reconciling established elites with the democratisation process.
In developed democracies, the rationale of a bicameral system is now sought primarily in the possibility of combining different systems of representation (particularly in federal systems) and in the possibility of reconsideration by a different chamber in the legislative, making it possible to avoid making mistakes and enhancing both the quality and the stability of the legislation. In majority systems of the Westminster model – where the government is part of the lower house and it tends to have a stable majority – a senate moreover is sometimes ascribed the role of giving more independent input into the parliamentary work, less determined by party discipline, and of paying more attention to the interests of minorities.
A bicameral system is, for that reason, sometimes recommended as a means to protect minorities against a tyranny of the majority… Finally, a bicameral system may also increase efficiency because it is possible to divide the legislative workload between two chambers. That can be the case when the two chambers absorb a sort of division of labour (e.g. an emphasis on technical legal quality in the senate). In many bicameral systems, moreover, it can be decided to put bills to either house, and the senate also has a right of initiative.”138
87 The importance of the second chamber increases when there is no single party rule in Parliament. Governments that lack Upper-House majority support find it difficult to pass Bills.139 Elliot Bulmer notes pertinently that in a democracy, a second chamber addresses the inability of the elected chamber to adequately represent a diverse society. In this view, a second chamber may enable a “more nuanced and complete representation of society, with greater representation for territorial, communal or other minorities”.
140 While discussing the advantage of second chambers in republican legislatures, Rogers observes that the institution of a second chamber generates legislative advantage only “if the chambers differ significantly from one another”.141 Quoting from the work of various scholars, he observes: “Hammond and Miller find that “The stability-inducing properties of bicameralism are . . . dependent on the existence of distinctly different viewpoints in the two chambers”… Buchanan and Tullock conclude similarly that, “unless the bases for representation are significantly different in the two houses, there would seem to be little excuse for the two-house system”…
Because two “congruent” chambers would ostensibly not significantly affect policy outcomes, Lijphart described bicameral systems with congruent chambers as “weak” forms of bicameralism…”142
88 Bicameralism, when entrenched as a principle in a constitutional democracy, acts as a check against the abuse of power by constitutional means or its use in an oppressive manner. As a subset of the constitutional principle of division of power, bicameralism is mainly a safeguard against the abuse of the constitutional and political process. A bicameral national parliament can hold the government accountable and can check or restrain the misuse of government power. Among its other roles is that of representing local state units, acting as a body of expert review, and providing representation for diverse socio-economic interests or ethno-cultural minorities. While deliberating over the necessity of having a second chamber, the Constituent Assembly had the benefit of examining the constitutional history of several other nations.
The constitutional advisor, B N Rau, found the issue of second chambers to be “one of the most vexing questions of political science”.
143 Under colonial rule, bicameralism had already been introduced. The first bicameral legislature as the national assembly for India was established by the Government of India Act 1919. The Government of India Act, 1935 had created an Upper House in the federal legislature which consisted of members elected by the provincial legislatures as well as representatives sent by numerous princely states that were not under the direct control of the British government. The 1935 Act became the blueprint for the structure of Parliament in the new Constitution.
The Rajya Sabha, as the Upper House of the Parliament, was adopted into the Constitution. The vision of the Constitution makers behind the establishment of the Upper House of Parliament has found expression in the classic work of Granville Austin: “The members of the Constituent Assembly had one predominant aim when framing the Legislative provisions of the Constitution: to create a basis for the social and political unity of the country… The goals of the Constituent Assembly… were to bring popular opinion into the halls of government, and, by the method of bringing it there, to show Indians that although they were many peoples, they were but one nation.
“144 89 Article 80 of the Constitution deals with the composition of the Rajya Sabha. The maximum strength of this chamber is 250 members, out of which up to 238 members are elected representatives from the states and union territories. 12 members are nominated by the President among persons with a special knowledge or practical experience in literature, science, art and social service. Members representing the states are elected by the state legislatures through proportional representation by means of a single transferable vote145. The method of electing representatives from Union territories has been left to prescription by Parliament.
146 In a departure from the American model of equal representation for the states, the allocation of seats in the Rajya Sabha to the States and Union territories is in accordance with the division provided in the Fourth Schedule of the Constitution (read with Articles 4(1) and 80(2)). The reason behind this division of seats is “to safeguard the interests of the smaller states while at the same time ensuring the adequate representation of the larger states, so that the will of the representatives of a minority of the electorate does not prevail over that of those who represented the majority”147. In this sense, the Rajya Sabha has a special structure.
90 The institutional structure of the Rajya Sabha has been developed to reflect the pluralism of the nation and its diversity of language, culture, perception and interest. The Rajya Sabha was envisaged by the makers of the Constitution to ensure a wider scrutiny of legislative proposals. As a second chamber of Parliament, it acts as a check on hasty and ill-conceived legislation, providing an opportunity for scrutiny of legislative business. The role of the Rajya Sabha is intrinsic to ensuring executive accountability and to preserving a balance of power. The Upper Chamber complements the working of the Lower Chamber in many ways.
The Rajya Sabha acts as an institution of balance in relation to the Lok Sabha and represents the federal structure148 of India. Both the existence and the role of the Rajya Sabha constitute a part of the basic structure of the Constitution. The architecture of our Constitution envisions the Rajya Sabha as an institution of federal bicameralism and not just as a part of a simple bicameral legislature. Its nomenclature as the ‘Council of States’ rather than the ‘Senate’ appropriately justifies its federal importance.
149 Seervai has observed that the federal principle is dominant in our Constitution. While adverting to several of its federal features, Seervai emphasises the position of the Rajya Sabha as an integral element:
“First and foremost, Parliament (the Central Legislature) is dependent upon the States, because one of its Houses, the Council of States, is elected by the Legislative Assemblies of the States. Where the ruling party, or group of parties, in the House of the People has a majority but not an overwhelming majority, the Council of States can have a very important voice in the passage of legislation other than financial Bills.
Secondly, a Bill to amend the Constitution requires to be passed by each House of Parliament separately by an absolute majority in that House and by not less than twothirds of those present and voting. Since the Council of States is indirectly elected by the State Legislatures, the State Legislatures have an important say in the amendment of the Constitution because of the requirement of special majorities in each House.
Thirdly, the very important matters mentioned in the proviso to Article 368 (Amendment of the Constitution) cannot be amended unless the amendments passed by Parliament are ratified by not less than half the number of Legislatures of the States…
Fourthly, the amendment of Article 352 by the 44th Amendment gives the Council of States a most important voice in the declaration of Emergency, because a proclamation of emergency must be approved by each House separately by majorities required for an amendment of the Constitution… Fifthly, the executive power of the Union is vested in the President of India who is not directly elected by the people but is elected by an electoral college consisting of
(a) the elected members of the Legislative Assemblies of the States and
(b) the elected members of both Houses of Parliament… Directly the State Legislatures have substantial voting power in electing the President; that power is increased indirectly through the Council of States, which is elected by the Legislative Assemblies of States.”150 91 The Rajya Sabha represents the constituent states of India. It legitimately holds itself as the guardian of the interest of the component states in a federal polity. It endeavours to remain concerned and sensitive to the aspirations of the states, thereby strengthening the country’s “federal fabric” and “promotes national integration”.
151 Being the federal chamber of Parliament, the Rajya Sabha enjoys some special powers, which are not even available to the Lok Sabha, under the Constitution152:
“(i) Article 249 of the Constitution provides that Rajya Sabha may pass a resolution, by a majority of not less than twothirds of the Members present and voting to the effect that it is necessary or expedient in the national interest that Parliament should make a law with respect to any matter enumerated in the State List. Then, Parliament is empowered to make a law on the subject specified in the resolution for the whole or any part of the territory of India. Such a resolution remains in force for a maximum period of one year but this period can be extended by one year at a time by passing a further resolution;
(ii) Under Article 312 of the Constitution, if Rajya Sabha passes a resolution by a majority of not less than two-thirds of the Members present and voting declaring that it is necessary or expedient in the national interest to create one or more All India Services common to the Union and the States, Parliament has the power to create by law such services; and
(iii) Under the Constitution, President is empowered to issue Proclamations in the event of national emergency (Article 352), in the event of failure of constitutional machinery in a State (Article 356), or in the case of financial emergency (Article 360).
Normally, every such Proclamation has to be approved by both Houses of Parliament within a stipulated period. Under certain circumstances, however, Rajya Sabha enjoys special powers in this regard. If a Proclamation is issued at a time when the dissolution of the Lok Sabha takes place within the period allowed for its approval, then the Proclamation can remain effective if a resolution approving it, is passed by Rajya Sabha.”
92 The Rajya Sabha is a permanent body as it is not subject to dissolution.153 Being an indirectly elected House, it has no role in the making or unmaking of the Government and therefore it is comparatively “free from compulsions of competitive party politics”.154 As a revising chamber, the Constitution makers envisioned that it will protect the values of the Constitution, even if it is against the popular will. The Rajya Sabha is a symbol against majoritarianism.
A Constitution Bench of this Court in Kuldip Nayar v Union of India155 highlighted the importance of the Rajya Sabha:
“47. The Rajya Sabha is a forum to which experienced public figures get access without going through the din and bustle of a general election which is inevitable in the case of Lok Sabha. It acts as a revising chamber over the Lok Sabha. The existence of two debating chambers means that all proposals and programmes of the Government are discussed twice. As a revising chamber, the Rajya Sabha helps in improving Bills passed by the Lok Sabha…”156 93 Participatory governance is the essence of democracy.
It ensures responsiveness and transparency. An analysis of the Bills revised by the Rajya Sabha reveals that in a number of cases, the changes recommended by the Rajya Sabha in the Bills passed by the Lok Sabha were eventually carried out.157 The Dowry Prohibition Bill is an example of a legislation in which the Rajya Sabha’s insistence on amendments led to the convening of a joint sitting158 of the two Houses and in that sitting, one of the amendments suggested by the Rajya Sabha was adopted without a division.
159 The Rajya Sabha has a vital responsibility in nation building, as the dialogue between the two houses of Parliament helps to address disputes from divergent perspectives. The bicameral nature of Indian Parliament is integral to the working of the federal Constitution. It lays down the foundations of our democracy. That it forms a part of the basic structure of the Constitution, is hence based on constitutional principle. The decision of the Speaker on whether a Bill is a Money Bill is not a matter of procedure. It directly impacts on the role of the Rajya Sabha and, therefore, on the working of the federal polity.
94 There is a constitutional trust which attaches to the empowerment of the Speaker of the Lok Sabha to decide whether a legislative measure is a Money Bill.
Entrustment of the authority to decide is founded on the expectation that the Speaker of the Lok Sabha will not dilute the existence of a co-ordinate institution in a bicameral legislature. A constitutional trust has been vested in the office of the Speaker of the Lok Sabha.
By declaring an ordinary Bill to be a Money Bill, the Speaker limits the role of the Rajya Sabha. This power cannot be unbridled or bereft of judicial scrutiny. If the power of the Speaker is exercised contrary to constitutional norms, it will not only limit the role of the Rajya Sabha, but denude the efficacy of a legislative body created by the Constitution. Such an outcome would be inconsistent with the scheme of the Indian Constitution. Judicial review is necessary to ensure that the federal features of the Constitution are not transgressed.
E.2 Aadhaar Act as a Money Bill
This Court must now deal with whether the Aadhaar Act was validly passed as a Money Bill. 95 Article 110(1) of the Constitution defines a Money Bill. For a Bill to be a Money Bill, it must contain “only provisions” dealing with every or any one of the matters set out in sub-clauses (a) to (g) of clause 1 of Article 110. The expression “if it contains only provisions dealing with all or any of the following matters, namely…” is crucial. Firstly, the expression “if” indicates a condition and it is only upon the condition being fulfilled that the deeming fiction of a Bill being a Money Bill for the purposes of the Chapter will arise. Secondly, to be a Money Bill, the Bill should have only those provisions which are referable to clauses (a) to (g).
The condition is much more stringent than stipulating that the Bill should incorporate any of the matters spelt out in clauses (a) to (g). The words “only provisions” means that besides the matters in sub clauses (a) to (g), the Bill shall not include anything else. Otherwise, the expression “only” will have no meaning. The word “only” cannot be treated to be otiose or redundant. Thirdly, the two expressions “if it contains only provisions” and “namely” indicate that sub-clauses (a) to (g) are exhaustive of what a Money Bill may contain. The contents of a Money Bill have to be confined to all or any of the matters specified in sub-clauses (a) to (g). Fourthly, sub-clause (g) covers any matter incidental to sub-clauses (a) to (f). A matter is incidental when it is ancillary to what is already specified. Sub-clause (g) is not a residuary entry which covers all other matters other than those specified in sub-clauses (a) to (f). If sub-clause (g) were read as a catch-all residuary provision, it would defeat the purpose of defining a class of Bills as Money Bills. What is incidental under sub-clause (g) is that which is ancillary to a matter which is already specified in sub-clauses (a) to (f).
The test is not whether it is incidental to the content of a Bill but whether it is incidental to any of the matters specifically enumerated in sub-clauses (a) to (f). The Attorney General would request the court to read the word “only” before “if” and not where it occurs. If the submission were to be accepted, it would lead to the consequence that the Bill would be a Money Bill if it contained provisions dealing with clause (a) to (g), even if it contained other provisions not relatable to these clauses. We cannot rewrite the Constitution, particularly where it is contrary to both text, context and intent.
Clause (2) of Article 110 provides that a Bill shall not be deemed to be a Money Bill just for the reason that it provides for the imposition of fines or other pecuniary penalties, or for the demand or payment of fees for licences or fees for services rendered, or by reason that it provides for the imposition, abolition, remission, alteration or regulation of any tax by any local authority or body for local purposes. Like in the Parliament Act of 1911, the definition of a Money Bill provided under Article 110(1) is exhaustive in nature. A Bill can be a Money Bill if it contains “only provisions” dealing with all or any of the matters listed under sub-clauses (a) to (g) of Article 110(1). 96 A Financial Bill is different from a Money Bill. Article 117 provides for special provisions relating to Financial Bills. Clause (1) of Article 117 states:
“(1) A Bill or amendment making provision for any of the matters specified in sub-clauses (a) to (f) of clause (1) of article 110 shall not be introduced or moved except on the recommendation of the President and a Bill making such provision shall not be introduced in the Council of States.” A Financial Bill does not need to have “only provisions” dealing with Subclauses (a) to (f) of Article 110. The provisions of Article 110(1) are therefore narrow and exhaustive.
97 As a matter of interpretation, the use of the word “only” indicates that a particular entry is exhaustive and is inapplicable to anything which falls outside its scope. This Court has interpreted the expression “only” as a word of exclusion and restriction.160 The interpretation of Article 110(1) as being restrictive in nature is also supported by the proceedings in the Constituent Assembly of India. Article 110 corresponds to Article 90 of the Draft Constitution. On 20 May 1949, a member of the Constituent Assembly, Ghanshyam Singh Gupta, proposed an amendment in clause (1) of Article 90 to delete the word “only”. He stated that a Bill can be a Money bill even while containing other provisions. Gupta argued:
“This article is a prototype of Section 37 of the Government of India Act which says that a Bill or amendment providing for imposing or increasing a tax or borrowing money, etc. shall not be introduced or moved except on the recommendation of the Governor-General. This means that the whole Bill need not be a money Bill: it may contain other provisions, but if there is any provision about taxation or borrowing, etc. It will come under this Section 37, and the recommendation of the Governor-General is necessary. Now article 90 says that a Bill shall be deemed to be a money Bill if it contains only provisions dealing with the imposition, regulation, etc., of any tax or the borrowing of money, etc.
This can mean that if there is a Bill which has other provisions and also a provision about taxation or borrowing etc., it will not become a money Bill. If that is the intention I have nothing to say; but that if that is not the intention I must say the word “only” is dangerous, because if the Bill does all these things and at the same time does something else also it will not be a money Bill. I do not know what the intention of the Drafting Committee is but I think this aspect of the article should be borne in mind.”161
(Emphasis supplied)
Another member Naziruddin Ahmad also emphasized on the deletion of the word “only”. The concern of these two members was that the word “only” restricts the scope of a Bill being passed as a Money Bill. Their apprehension was that if a Bill has other provisions which are unrelated to the clauses mentioned in draft Article 90, the Bill would not qualify to be a Money Bill in view of the word “only”. The amendment suggested by these members was listed to be put to vote on a later date. The amendment was rejected when it was put to vote on 8 June 1949. The framers of the Indian Constitution consciously rejected the said amendment.
98 When a Bill is listed as a Money Bill, it takes away the power of the Rajya Sabha to reject or amend the Bill. The Rajya Sabha can only make suggestions to a Money Bill, which are not binding on the Lok Sabha. The Constitution makers would have been aware about the repercussions of a Bill being introduced as a Money Bill. As the role of the Rajya Sabha is limited in the context of Money Bills, the scope of what constitutes a Money Bill was restricted by adopting the word “only” in Draft Article 90. A Bill to be a Money Bill must not contain any provision which falls outside clauses (a) to (g) of Article 110(1). The Constitution has carefully used the expression “dealing with” in Article 110 (1) and not the wider legislative form “related to”.
A Bill, which has both – certain provisions which fall within sub-clauses (a) to (g) of Article 110(1) and other provisions which fall outside will not qualify to be a Money Bill. It is for this reason that there cannot also be any issue of the severability of the provisions of a Bill, which has certain provisions relating to sub-clauses (a) to (g) of Article 110(1), while also containing provisions which fall beyond. Any other interpretation would result in rewriting the Constitution. If a Bill contains provisions which fall outside sub-clauses (a) to (g), it is not a Money Bill. The Rajya Sabha is entitled as part of its constitutional function to legislative participation. The entirety of the Bill cannot be regarded as a Money Bill, once it contains any matters which fall beyond sub-clauses (a) to (g). Once that is the position, it could be impossible to sever those parts which fall within sub-clauses (a) to (g) and those that lie outside.
The presence of matters which travel beyond sub-clauses (a) to (g) has consequences in terms of the nature of the Bill and the legislative participation of the Rajya Sabha. If the constitutional function of the Rajya Sabha has been denuded on the hypothesis that this Bill was a Money Bill, the consequence of a finding in judicial review that the Bill is not a Money Bill must follow. Any other construction will reduce bicameralism to an illusion. This interpretation is also supported by the judgment of a Bench of seven judges of this Court in Krishna Kumar Singh v State of Bihar162, where it held that the ordinance making power conferred upon the President and the Governors is limited by the requirements set out by Articles 123 and 213. This Court had held:
“59…The constitutional conferment of a power to frame ordinances is in deviation of the normal mode of legislation which takes place through the elected bodies comprising of Parliament and the state legislatures. Such a deviation is permitted by the Constitution to enable the President and Governors to enact ordinances which have the force and effect of law simply because of the existence of circumstances which can brook no delay in the formulation of legislation. In a parliamentary democracy, the government is responsible collectively to the elected legislature. The subsistence of a government depends on the continued confidence of the legislature. The ordinance making power is subject to the control of the legislature over the executive.
The accountability of the executive to the legislature is symbolised by the manner in which the Constitution has subjected the ordinance making power to legislative authority. This, the Constitution achieves by the requirements of Article 213…”163
(Emphasis supplied)
99 The authority of the Lok Sabha to pass a Money Bill is based on the requirements set out under Article 110. The framers of the Indian Constitution deliberately restricted the scope of Article 110(1) to ensure that the provision is not an avenue to supersede the authority of the Rajya Sabha. The intention of the Constitution makers is clear. The Lok Sabha cannot introduce and pass a legislative measure in the garb of a Money Bill, which could otherwise have been amended or rejected by the Rajya Sabha. Bicameralism is a founding value of our democracy. It is a part of the basic structure of the Constitution. Introduction and passing of a Bill as a Money Bill, which does not qualify to be a Money Bill under Article 110(1) of the Constitution, is plainly unconstitutional.
The Lok Sabha is not entrusted with the entire authority of Parliament. The Lok Sabha, the Rajya Sabha and the President together constitute the Parliament of India. The Lok Sabha is a body of elected representatives and represents the aspirations of citizens. Yet, like every constitutional institution, it is part of this basic structure of the Constitution. A political party or a coalition which holds the majority in the Lok Sabha cannot subvert the working of the Constitution, against which Dr B R Ambedkar had warned164 in the Constituent Assembly. A ruling government has to work within constitutional parameters and has to abide by constitutional morality. 100 The Constitution of India is not a mere parchment of paper. It was written with the vision of those who gave blood and sweat to freedom: political personalities, social reformers and constitution framers. It symbolises a faith in institutions, justice and good governance. That vision cannot be belied.
The Speaker of the Lok Sabha has an onerous constitutional duty to ensure that a Bill, which is not a Money Bill is not passed as a Money Bill. The Speaker of the Lok Sabha, the Chairman of the Rajya Sabha, the members of the Lok Sabha and the Rajya Sabha, and the President need to work in constitutional solidarity to ensure that no provision of the Constitution is diluted or subverted. 101 The Aadhaar Act was passed as a Money Bill. The provisions of the Act need to be analysed to determine whether the Act is a Money Bill. The Preamble of the Act states that it is: “An Act to provide for, as a good governance, efficient, transparent, and targeted delivery of subsidies, benefits and services, the expenditure for which is incurred from the Consolidated Fund of India, to individuals residing in India through assigning of unique identity numbers to such individuals and for matters connected therewith or incidental thereto.”
The Preamble focuses on the delivery of subsidies, benefits and services for which the expenditure is borne from the Consolidated Fund of India. But the essential issue is whether the Act confines itself to matters which fall within the ambit of Article 110. 102 Section 3 entitles every resident165 in India to obtain an Aadhaar number by submitting his or her demographic information, by undergoing the process of enrolment. Section 2(m) defines “enrolment” as the process to collect demographic and biometric information from individuals by the enrolling agencies for the purpose of issuing Aadhaar numbers to such individuals. After receiving the demographic and biometric information of the individual, the Unique Identification Authority of India (UIDAI) would verify the information and shall issue an Aadhaar number to such an individual.166 Section 4(3) provides that the Aadhaar number may be accepted as proof of identity for “any purpose”.
Section 5 requires UIDAI to take special measures to issue Aadhaar numbers to “women, children, senior citizens, persons with disability, unskilled and unorganised workers, nomadic tribes or to such other persons who do not have any permanent dwelling house and such other categories of individuals”. Under Section 6, UIDAI may require Aadhaar number holders to update their demographic information and biometric information, from time to time so as to ensure continued accuracy of their information in the Central Identities Data Repository (“CIDR”). The Aadhaar Act defines CIDR as a centralised database containing all Aadhaar numbers issued to Aadhaar number holders along with the corresponding demographic information and biometric information of such individuals and other related information.167 103 Section 7 requires proof of an Aadhaar number as a necessary condition to avail subsidies, benefits and services, for which the expenditure is borne from the Consolidated Fund of India.
The proviso to Section 7 states that if an Aadhaar number is not assigned to an individual, the individual shall be offered alternate and viable means of identification for delivery of the subsidy, benefit or service. Section 8(1) requires UIDAI to perform authentication168 of the Aadhaar number of an Aadhaar number holder, in relation to his or her biometric information or demographic information submitted by any requesting entity169. Under Section 8(2), a requesting entity is required to obtain the consent of an individual before collecting his or her identity information for the purposes of authentication.
The requesting entity must ensure that the identity information of an individual collected by it is only used for submission to the CIDR for authentication. Section 8(3) requires a requesting entity to inform the individual submitting identity information for authentication certain details with respect to authentication. 104 Chapter IV of the Act deals with UIDAI. Section 11 establishes UIDAI as the body responsible for the processes of enrolment and authentication and for performing functions assigned to it under the Act. The Act provides for the composition of UIDAI170, qualifications of its members171, terms of office172 of its chairperson and members, their removal173 and functions174.
Section 23, which deals with the powers and functions of UIDAI, authorizes it to develop the policy, procedure and systems for issuing Aadhaar numbers to individuals and to perform authentication. Section 23(h) states that UIDAI has the power to specify the “manner of use of Aadhaar numbers” for the purposes of providing or availing of various subsidies, benefits, services and “other purposes” for which Aadhaar numbers may be used.
Under Section 23(3), UIDAI may enter into a Memorandum of Understanding or agreement with the Central Government or State Governments or Union territories or other agencies for the purpose of performing any of the functions in relation to collecting, storing, securing or processing of information or delivery of Aadhaar numbers to individuals or performing authentication. 105 Chapter V deals with grants, accounts and audit and annual reports of UIDAI. Section 25 provides that the fees or revenue collected by UIDAI shall be credited to the Consolidated Fund of India.
Chapter VI deals with protection of information collected from individuals for authentication. Section 28(3) requires UIDAI to take all necessary measures to ensure that the information in its possession or control, including information stored in the CIDR, is secured and protected against access, use or disclosure (not permitted under the Act or the regulations), and against accidental or intentional destruction, loss or damage. Section 29 imposes restrictions on sharing of core biometric information, collected or created under the Act. Section 32(2) entitles every Aadhaar number holder to obtain his or her authentication record in such manner as may be specified by regulations. Section 33 provides for disclosure of information pursuant to a court order or in the interest of national security.
106 Chapter VII of the Act (Sections 34 to 47) provides for offences and penalties. Section 34 provides for penalty for impersonation at the time of enrolment. Section 35 provides a penalty for impersonation of an Aadhaar number holder by changing demographic or biometric information. Under Section 37, a penalty for disclosing identity information (which was collected in the course of enrolment or authentication) is provided. Section 38 provides a penalty for unauthorised access to the CIDR. Section 39 imposes a penalty for tampering with data in the CIDR. Under Sections 40 and 41, a penalty has been provided for requesting entities and enrolment agencies, in case they act in contravention of the obligations imposed upon them under the Act. Section 44 indicates that the provisions of the Act would apply to any offence or contravention committed outside India by any person, irrespective of nationality.
107 Section 48 empowers the Central Government to supersede UIDAI in certain situations. Section 50 states that UIDAI is bound by directions on questions of policy given by the Central Government. Section 51 authorizes the UIDAI to delegate to any member, officer of the Authority or any other person, such of its powers and functions (except the power under section 54) as it may deem necessary. Section 53 empowers the Central Government to make rules to carry out the provisions of the Act. Under Section 54(2)(m), UIDAI can make regulations providing the manner of use of Aadhaar numbers for the purposes of providing or availing of various subsidies, benefits, services and “other purposes” for which Aadhaar numbers may be used.
Section 57 authorizes the State or any body corporate or person to use an Aadhaar number for establishing the identity of an individual “for any purpose”, subject to the procedure and obligations under Section 8 and Chapter VI of the Act. Section 59 seeks to validate the actions taken by the Central Government pursuant to the notifications dated 28 January 2009 and 12 September 2015, and prior to the enactment of the Aadhaar Act. This broad description of the provisions of the Aadhaar Act indicates that the Act creates a framework for obtaining a unique identity number – the Aadhaar number – by submitting demographic and biometric information and undergoing the process of enrolment and authentication.
The Act indicates that the Aadhaar number may be accepted as proof of identity for any purpose. The Act, in other words, creates a platform for one pan-India and nationally acceptable identity. It creates a central database (CIDR) for storage of identity information collected from individuals. Sections 3 to 6 specifically deal with the process of enrolment. Section 3 entitles every resident to hold an Aadhaar number. Section 4(3) states that the Aadhaar number so generated may be used as a proof of identity “for any purpose”. The primary object of the legislation is to create one national identity for every resident. It seeks to do so by legislating a process for collecting demographic and biometric information.
The Act has created an authority to oversee the fulfilment of its provisions. In its primary focus and initiatives, the law traverses PART E 163 beyond the territory reserved by Article 110 for a Money Bill. Sections 7 to 10 deal with authentication of information submitted at the time of enrolment. Section 8 creates obligations on requesting entities to ensure that consent is obtained from individuals before collecting their identity information and that the identity information of such individual is only used for submission to the CIDR for authentication. Sections 11 to 23 create a statutory authority (UIDAI) and assign responsibilities to it for the processes of enrolment and authentication and to discharge other functions assigned to it under the Act, including developing the policy, procedure and systems for issuing Aadhaar numbers to individuals.
Section 23(2)(h) provides that apart from availing of various subsidies, benefits, and services, Aadhaar numbers may be used for “other purposes”. Sections 28 to 33 deal with protection of information, and provide for security and confidentiality of identity information and restrictions on sharing of information. Section 28 imposes obligations on the UIDAI to ensure the security and confidentiality of identity information and authentication records of individuals, which are in its possession or control, including information stored in CIDR. Disclosure of identity information and authentication records can be made under Section 33, pursuant to a court order (not below the rank of District Judge) or in the interest of national security in pursuance of a direction of an officer (not below the rank of Joint Secretary to the Government of India).
Sections 34 to 47 deal with substantive offences and penalties created under the Act. Sections 54(2)(m) states that regulations can be made by UIDAI specifying the manner of use of Aadhaar PART E 164 numbers for the purposes of providing or availing of various subsidies, benefits, services and “other purposes” for which Aadhaar numbers may be used. Section 57 authorizes the use of Aadhaar number by anyone (whether by the State or any body corporate or person under law or contract) for establishing the identity of an individual “for any purpose”. 108 Section 7 makes the use of the Aadhaar number mandatory for availing subsidies, benefits or services, for which expenditure is incurred from the Consolidated Fund of India. The scheme of the Act deals with several aspects relating to the unique identity number.
The unique identity is capable of being used for multiple purposes: availing benefits, subsidies and services, for which expenses are incurred from the Consolidated Fund of India, is just one purpose, among others. The Preamble to the Aadhaar Act indicates that the main objective was to achieve an efficient and “targeted delivery of subsidies, benefits and services, the expenditure for which is incurred from the Consolidated Fund of India”. The substantive provisions of the Act are, however, not confined to the object specified in the Preamble. Indeed, they travel far beyond the boundaries of a money bill under Article 110(1).
The enrolment on the basis of demographic and biometric information, generation of Aadhaar number, obtaining consent of individuals before collecting their individual information, creation of a statutory authority to implement and supervise the process, protection of information collected during the process, disclosure of information in certain circumstances, creation of offences and penalties for disclosure or loss of information, and the use of the Aadhaar number for any purpose lie outside the ambit of Article 110. These themes are also not incidental to any of the matters covered by sub-clauses (a) to (f) of Article 110(1). The provisions of Section 57 which allow the use of an Aadhaar number by bodies corporate or private parties for any purpose do not fall within the ambit of Article 110. The legal framework of the Aadhaar Act creates substantive obligations and liabilities which have the capability of impacting on the fundamental rights of residents. 109 A Bill, to be a Money Bill, must contain only provisions which fall within the ambit of the matters mentioned in Article 110. Section 7 of the Act allows the Aadhaar number to be made mandatory for availing of services, benefits and subsidies for which expenditure is incurred from the Consolidated Fund of India.
Under clause (e) of Article 110(1) the money bill must deal with the declaring of any expenditure to be expenditure charged on the Consolidated Fund of India (or increasing the amount of expenditure). Significantly, Section 7 does not declare the expenditure incurred on services, benefits or subsidies to be a charge on the Consolidated Fund of India. What Section 7 does is to enact a provision allowing for Aadhaar to be made mandatory, in the case of services, benefits or subsidies which are charged to the Consolidated Fund. Section 7 does not declare them to be a charge on the Consolidated Fund. It provides that in the case of services, benefits or subsidies which are already charged to the Consolidated Fund, Aadhaar can be made mandatory to avail of them. Section 7, in other words, is a provision for imposing a requirement of authentication and not declaring any expenditure to be a charge on the Consolidated Fund of India. Hence, even Section 7 is not within the ambit of Article 110(1)(e).
However, even if Section 7 were to be held to be referable to Article 110, that does not apply to the other provisions of the Act. The other provisions of the Act do not in any event fall within the ambit of Article 110(1). Introducing one provision – Section 7 – does not render the entirety of the Act a Money Bill where its other provisions travel beyond the parameters set out in Article 110. Section 57 of the Act in particular (which creates a platform for the use of the Aadhaar number by the private entities) can by no stretch of logic be covered under Article 110(1). The other provisions of the Act do not deal with that which has been provided under Sub-clauses (a) to (g) of Article 110.
As regards the ‘incidental’ provision under Article 110(1)(g), the provisions of the Aadhaar Act are not “incidental to any of the matters specified in subclauses (a) to (f)”. Even if it is assumed that there is one provision (Section 7) which is relatable to sub-clause (e) of Article 110(1), the other provisions of the Act are unrelated to Article 110(1). 110 This Court must also advert to the legislative history prior to the enactment of the Aadhaar Act. An attempt to provide a legislative framework governing the Aadhaar project was first made by introducing the National Identification Authority of India Bill, 2010 (“NIA Bill”). The NIA Bill was PART E 167 introduced in the Rajya Sabha on 3 December 2010.
The Preamble of the Bill indicated its purpose: “A Bill to provide for the establishment of the National Identification Authority of India for the purpose of issuing identification numbers to individuals residing in India and to certain other classes of individuals and manner of authentication of such individuals to facilitate access to benefits and services to such individuals to which they are entitled and for matters connected therewith or incidental thereto.”
The main objective of the Bill was to establish the National Identification Authority of India to issue unique identification numbers (called ‘Aadhaar’) to residents of India and to any other category of people for the purpose of facilitating access to benefits and services. Chapter II (Clauses 3 to 10) of the Bill dealt with Aadhaar numbers. Clause 3 of the Bill entitled every resident to obtain an Aadhaar number on providing demographic and biometric information to the Authority in such manner as may be specified. Clause 4(3) stated that an Aadhaar number shall be accepted, subject to authentication, as proof of identity of the Aadhaar number holder. Chapter III (Clauses 11 to 23) dealt with the National Identification Authority of India. Clause 11 provided for establishment of the Authority by the Central Government.
Clause 23 empowered the Authority to develop the policy, procedure and systems for issuing Aadhaar numbers to residents and to perform authentication. Clause 23(2)(h) stated that the Authority may specify the usage and applicability of the Aadhaar number for delivery of various benefits and services. Establishing, operating and maintaining of the Central Identities Data Repository (CIDR) by the Authority was provided under Clause 23(2)(j). Chapter IV (Clauses 24 to 27) provide for grants, accounts and audit and annual reports related to the Authority.
Clause 25 stated that the fees or revenue collected by the Authority shall be credited to the Consolidated Fund of India and the entire amount would be transferred to the Authority. Chapter V (Clauses 28 and 29) dealt with creation of an Identity Review Committee and its functions. The functions of the Review Committee included ascertaining the extent and pattern of usage of Aadhaar numbers across the country and preparing a report annually along with recommendations. Chapter VI (Clauses 30 to 33) dealt with the protection of individual identity information and authentication records. Clause 30(1) required the Authority to ensure the security and confidentiality of identity information and authentication records of individuals. Clause 30(2) required the Authority to take measures (including security safeguards) to ensure that the information in the possession or control of the Authority (including information stored in the Central Identities Data Repository) is secured and protected against any loss or unauthorised access or use or unauthorised disclosure. Clause 33 stated that individual information may be disclosed pursuant a court order or in the interest of national security. Chapter VII (Clauses 34 to 46) created offences and penalties under the law.
Clause 47 empowered the Central Government to supersede the Authority. Clause 50 authorized the Authority to delegate to any Member, officer of the Authority or any other person such of its powers and functions (except the power under Clause 53). Clause 57 sought to validate PART E 169 actions taken by the Central Government under the Planning Commission’s notification of 2009. 111 Since the UID programme involved complex issues, the NIA Bill was referred, on 10 December 2010, to the Standing Committee on Finance, chaired by Mr Yashwant Sinha, for examination and report. The Standing Committee comprised of 21 members from the Lok Sabha and 10 members from the Rajya Sabha. The Standing Committee submitted its Report175 on 11 December 2011. The Report raised several objections to the Bill, which included those summarised below:
(i) Since law making was underway, the bill being pending, any executive action is as violative of Parliament’s prerogatives as promulgation of an ordinance while one of the Houses of Parliament is in session;
(ii) While the country is facing a serious problem of illegal immigrants and infiltration from across the borders, the National Identification Authority of India Bill, 2010 proposes to entitle every resident to obtain an Aadhaar number, apart from entitling such other category of individuals as may be notified from time to time. This will, it is apprehended, make even illegal immigrants entitled for an Aadhaar number;
(iii) The issue of a unique identification number to individuals residing in India and other classes of individuals under the Unique Identification (UID) Scheme is riddled with serious lacunae and concern areas. For example, the full or near full coverage of marginalized sections for issuing Aadhaar numbers could not be achieved mainly due to two reasons viz.
(a) the UIDAI doesn’t have the statistical data relating to them; and
(b) estimated failure of biometrics is expected to be as high as 15% because a large chunk of population is dependent on manual labour;
(iv) Despite the presence of serious differences of opinion within the Government on the UID scheme, the scheme continues to be implemented in an overbearing manner without regard to legalities and other social consequences;
(v) The UID scheme lacks clarity on many issues including even the basic purpose of issuing an “Aadhaar” number. Although the scheme claims that obtaining an Aadhaar number is voluntary, an apprehension has developed in the minds of people that in future, services / benefits including food entitlements would be denied in case they do not an have an Aadhaar number;
(vi) It is also not clear as to whether possession of an Aadhaar number would be made mandatory in future for availing of benefits and services. Even if the Aadhaar number links entitlements to targeted beneficiaries, it may not ensure that beneficiaries have been correctly identified. Thus, the present problem of proper identification would persist;
(vii) Though there are significant differences between the identity system of other countries and the UID scheme, yet there are lessons from the global experience to be learnt before proceeding with the implementation of the UID scheme, which the Ministry of Planning has ignored completely;
(viii) Considering the huge database and possibility of misuse of information, the enactment of a national data protection law is a pre-requisite for any law that deals with large scale collection of information from individuals and its linkages across separate databases. In the absence of data protection legislation, it would be difficult to deal with issues like access to and misuse of personal information, surveillance, profiling, linking and matching of data bases and securing confidentiality of information;
(ix) The Standing Committee strongly disapproved of the hasty manner in which the UID scheme was approved. Unlike many other schemes / projects, no comprehensive feasibility study, which ought to have been done before approving such an expensive scheme, was done involving all aspects of the UID scheme including a cost-benefit analysis, comparative costs of Aadhaar numbers and various existing forms of identity, financial implications and prevention of identity theft, for example, using hologram enabled ration cards to eliminate fake and duplicate beneficiaries;
(x) The UID scheme may end up being dependent on private agencies, despite contractual agreements made by the UIDAI with several private vendors. As a result, the beneficiaries may be forced to pay over and above the charges to be prescribed by the UIDAI for availing of benefits and services, which are now available free of cost;
(xi) The scheme is full of uncertainty in technology as a complex scheme is built up on untested and unreliable technology and on several assumptions. It is also not known as to whether the proof of concept studies and assessment studies undertaken by the UIDAI have explored the possibilities of maintaining accuracy to a large level of enrolment of 1.2 billion people; and
(xii) The Committee felt that entrusting the responsibility of verification of information of individuals to the registrars to ensure that only genuine residents get enrolled into the system may have far reaching consequences for national security. Given the limitation of any mechanism such as a security audit by an appropriate agency that would be set up for verifying the information, it is not evident as to whether a complete verification of information of all Aadhaar number holders is practically feasible; and whether it would deliver the intended results without compromising national security.
With these apprehensions about the UID scheme, the Standing Committee on Finance categorically conveyed that the National Identification Authority of India Bill, 2010 was not acceptable. The Committee urged the Government to reconsider and review the UID scheme and the proposals contained in the Bill and bring forth a fresh legislation before Parliament. Ultimately, the NIA Bill was withdrawn from the Rajya Sabha on 3 March, 2016. 112 A comparison of the Aadhaar Act 2016 and NIA Bill 2010 reveals that both have a common objective and framework – establishing a system of unique identity numbers, which would be implemented and monitored by a statutory authority. The NIA Bill was not a Money Bill.
It was never passed by the Rajya Sabha. The Bill was scrutinized by a Standing Committee on Finance, which had 10 members from the Rajya Sabha and 21 from the Lok Sabha. The NIA Bill did not contain a provision, similar to Section 7 of the Aadhaar Act. Yet, as discussed earlier, the presence of Section 7 does not make the Aadhaar Act a Money Bill. Introducing the Aadhaar Act as a Money Bill deprived the Rajya Sabha of its power to reject or amend the Bill. Since the Aadhaar Act in its current form was introduced as a Money Bill in the Lok Sabha, the Rajya Sabha had no option other than of making recommendations to the Bill.
The recommendations made by the Rajya Sabha (which also included deletion of Section 57) were rejected by the Lok Sabha. The legislative history is a clear pointer to the fact that the subsequent passage of the Bill as a Money Bill by-passed the constitutional authority of the Rajya Sabha. The Rajya Sabha was deprived of its legitimate constitutional role by the passage of the Bill as a Money Bill in the Lok Sabha.
113 The Court must also address the contention of the Respondents that the Aadhaar Act is “in pith and substance” a Money Bill. The learned Attorney General for India has submitted that though the Act has ancillary provisions, its main objective is the delivery of subsidies, benefits and services flowing out of the Consolidated Fund of India and that the other provisions are related to the main purpose of the Act which was giving subsidies and benefits. It has been submitted that the real test to be applied in the present dispute is the doctrine of pith and substance.
114 This Court has applied the doctrine of pith and substance when the legislative competence of a legislature to enact a law is challenged. The doctrine is applied to evaluate whether an enactment which is challenged falls within an entry in one of the three Lists in the Seventh Schedule over which the legislature has competence under Article 246 of the Constitution. The Seventh Schedule to the Constitution distributes legislative powers between the Union and the States. When a law enacted by a legislature is challenged on the ground of a lack of legislative competence, the doctrine of pith and substance is invoked. Under the doctrine, the law will be valid if in substance, it falls within the ambit of a legislative entry on which the legislature is competent to enact a law, even if it incidentally trenches on a legislative entry in a separate list.
The constitutional rationale for the application of this doctrine has been explained in a Constitution Bench decision of this Court in A S Krishna v State of Madras176: “8…But then, it must be remembered that we are construing a federal Constitution. It is of the essence of such a Constitution that there should be a distribution of the legislative powers of the Federation between the Centre and the Provinces. The scheme of distribution has varied with different Constitutions, but even when the Constitution enumerates elaborately the topics on which the Centre and the States could legislate, some overlapping of the fields of legislation is inevitable.
The British North America Act, 1867, which established a federal Constitution for Canada, enumerated in Sections 91 and 92 the topics on which the Dominion and the Provinces could respectively legislate. Notwithstanding that the lists were framed so as to be fairly full and comprehensive, it was not long before it was found that the topics enumerated in the two sections overlapped, and the Privy Council had time and again to pass on the constitutionality of laws made by the Dominion and Provincial legislatures.
It was in this situation that the Privy Council evolved the doctrine, that for deciding whether an impugned legislation was intra vires, regard must be had to its pith and substance. That is to say, if a statute is found in substance to relate to a topic within the competence of the legislature, it should be held to be intra vires, even though it might incidentally trench on topics not within its legislative competence…”
(Emphasis supplied)
The decision of a three judge Bench of this Court in State of Maharashtra v Bharat Shanti Lal Shah177 has summarized the process of reasoning which must be followed by the Court while applying the doctrine of pith and substance. The Court held:
“43…If there is a challenge to the legislative competence the courts will try to ascertain the pith and substance of such enactment on a scrutiny of the Act in question. In this process, it is necessary for the courts to go into and examine the true character of the enactment, its object, its scope and effect to find out whether the enactment in question is genuinely referable to the field of legislation allotted to the respective Legislature under the constitutional scheme. Where a challenge is made to the constitutional validity of a particular State Act with reference to a subject mentioned in any entry in List I, the court has to look to the substance of the State Act and on such analysis and examination, if it is found that in the pith and substance, it falls under an entry in the State List but there is only an incidental encroachment on topics in the Union List, the State Act would not become invalid merely because there is incidental encroachment on any of the topics in the Union List.”178
(Emphasis supplied )
115 The doctrine of pith and substance is mainly used to examine whether the legislature has the competence to enact a law with regard to any of the three Lists provided under the Constitution. It cannot be applied to sustain as a Money Bill, a Bill which travels beyond the constitutional boundaries set out by Article 110 Whether a Bill is validly passed as a Money Bill has nothing to do with the legislative competence of the legislature under Article 246 of the Constitution. Whether a Bill is a Money Bill has to be tested within the boundaries of Article 110. The submission of the Attorney General boils down to this: ‘ignore the expression “only provisions dealing with all or any of the following matters” and hold the Bill to be a Money Bill by treating Section 7 as its dominant provision’.
This cannot be accepted. This would ignore the express and clear language of Article 110. As we have emphasised earlier, the submission of the Attorney General requires the court to transpose the word “only” from its present position to a place before “if”. That would be to rewrite the Constitution to mean that a Bill would be a Money Bill if it contained some provisions which fall under sub-clauses (a) to (g). The Constitution says to the contrary: a Bill is a Money Bill if it contains “only provisions” dealing with one or more of the matters set out in sub-clauses (a) to (g). Looked at in another way, all the provisions of the Aadhaar Act (apart from Section 7) cannot be read as incidental to Section 7. Such a view is belied by a plain reading of the Act, as indicated earlier. Moreover, we have also indicated reasons why even Section 7 cannot be held to be referable to Article 110.
Section 7 does not deal with the declaring of any expenditure as expenditure charged to the Consolidated Fund. Section 7 allows for making Aadhaar mandatory for availing of subsidies, benefits or services the expenditure incurred on which is charged to the Consolidate Fund. Section 7 does not charge any expenditure to the Consolidated Fund. It deals with making Aadhaar mandatory. In support of their contention, the Respondents have also relied upon a two judge Bench decision in Union of India v Shah Goverdhan L Kabra Teachers’ College179 to submit that the doctrine of pith and substance can be used in any context. The Court held:
“7. It is further a well-settled principle that entries in the different lists should be read together without giving a narrow meaning to any of them. Power of the Parliament as well as the State legislature are expressed in precise and definite terms. While an entry is to be given its widest meaning but it cannot be so interpreted as to over-ride another entry or make another entry meaningless and in case of an apparent conflict between different entries, it is the duty of the court to reconcile them. When it appears to the Court that there is apparent overlapping between the two entries the doctrine of “pith and substance” has to be applied to find out the true nature of a legislation and the entry with which it would fall. In case of conflict between entries in List I and List II, the same has to be decided by application of the principle of “pith and substance”.
The doctrine of “pith and substance” means that if an enactment substantially falls within the powers expressly conferred by the Constitution upon the legislature which enacted it, it cannot be held to be invalid, merely because it incidentally encroaches on matters assigned to another legislature. When a law is impugned as being ultra-vires of the legislative competence, what is required to be ascertained is the true character of the legislation. If on such an examination it is found that the legislation is in substance one on a matter assigned to the legislature then it must be held to be valid in its entirety even though it might incidentally trench on matters which are beyond its competence.
In order to examine the true character of the enactment, the entire Act, its object and scope and effect, is required to be gone into. The question of invasion into the territory of another legislation is to be determined not by degree but by substance. The doctrine of “pith and substance’ has to be applied not only in cases of conflict between the powers of two legislatures but in any case where the question arises whether a legislation is covered by particular legislative power in exercise of which it is purported to be made.”180
(Emphasis supplied)
The decision is of no assistance to the submission in the present dispute. The observations made by the Court are in relation to the power to legislate under Article 246 of the Constitution.
It is unconnected to the question of a Money Bill. Therefore, the argument that the Aadhaar Act is “in pith and substance” a Money Bill is rejected. 116 Introducing the Aadhaar Act as a Money Bill has bypassed the constitutional authority of the Rajya Sabha. The passage of the Aadhaar Act as a Money Bill is an abuse of the constitutional process. It deprived the Rajya Sabha from altering the provisions of the Bill by carrying out amendments. On the touchstone of the provisions of Article 110, the Bill could not have been certified as a Money Bill. In his last address to the Constituent Assembly on 25 November 1949, Dr B R Ambedkar had stated: “The working of a Constitution does not depend wholly upon the nature of the Constitution.
The Constitution can provide only the organs of State such as the Legislature, the Executive and the Judiciary. The factors on which the working of those organs of the State depends are the people and the political parties they will set up as their instruments to carry out their wishes and their politics.”181 117 The Rajya Sabha has an important role in the making of laws. Superseding the authority of the Rajya Sabha is in conflict with the constitutional scheme and the legitimacy of democratic institutions. It constitutes a fraud on the Constitution. Passing of a Bill as a Money Bill, when it does not qualify for it, damages the delicate balance of bicameralism which is a part of the basic structure of the Constitution.
The ruling party in power may not command a majority in the Rajya Sabha. But the legislative role of that legislative body cannot be obviated by legislating a Bill which is not a Money Bill as a Money Bill. That would constitute a subterfuge, something which a constitutional court cannot countenance. Differences in a democratic polity have to be resolved by dialogue and accommodation. Differences with another constitutional institution cannot be resolved by the simple expedient of ignoring it. It may be politically expedient to do so. But it is constitutionally impermissible.
This debasement of a democratic institution cannot be allowed to pass. Institutions are crucial to democracy. Debasing them can only cause a peril to democratic structures. The Act thus fails to qualify as a Money Bill under Article 110 of the Constitution. Since the Act was passed as a Money Bill, even though it does not qualify to be so, the passage of the Act is an illegality. The Aadhaar Act is in violation of Article 110 and therefore is liable to be declared unconstitutional.
F Biometrics, Privacy and Aadhaar
“Any situation that allows an interaction between man and machine is capable of incorporating biometrics”182 118 The term ‘biometric’ is derived from the Greek nouns ‘ß???’ (life) and ‘µ?t???’ (measure) and means ‘measurement of living species’.
183 Biometric technologies imply that “unique or distinctive human characteristics of a person are collected, measured and stored for the automated verification of a claim made by that person for the identification of that person.”
184 These systems thus identify or verify the identity or a claim of persons on the basis of the automated measurement and analysis of their biological traits (such as fingerprints, face and iris) or behavioral characteristics (such as signature and voice).
119 The idea that parts of our body can be used to identify our unique selves is not new. Prints of hand, foot and finger have been used since ancient times because of their unique characteristics. Before the advent of biometric systems, however, human characteristics were compared in a manual way. Today’s biometric systems hence differ from manual verification methods in that technology allows for automated comparison of human characteristic(s) in place of a regime of manual verification that existed earlier. It must be understood that biometric systems themselves do not identify individuals.
For identification, additional information which is already stored in databases is needed since biometric systems can only compare information which is already submitted.185 Integral to such a system is the matching of a claim of identity with biometric data collected and stored earlier. In general, biometric applications are referred to as systems which allow one to authenticate claims. The verb ‘to authenticate’ can be described as ‘making authentic, legally valid’.
186 Originally, fingerprints were the most commonly known and used biometric traits, but with improvements in technology, multiple sources of biometric information have emerged. These include data related to facial features, iris, voice, hand geometry and DNA. Each trait is collected using different technologies and can be used for different purposes separately or in combination, to strengthen and improve the accuracy and reliability of the identification process.
187 In general, biometric information is developed by processing extractable key features of an individual into an ‘electronic digital template’, which is then encrypted and stored in a database. When an individual connects with the system to verify his/her identity for any purpose, the information is used by matching the ‘electronic digital template’ saved with the biometric information presented, based on which comparison, the individual’s identity will be confirmed or rejected.
The intended purpose of biometric technology is to confirm the identity of individuals through a “one to one” identification check. This system compares a source of biometric data with existing data for that specific person.
F.I Increased use of biometric technology
120 There had been an initial increase in the usage of biometric technology in both developed and developing countries by both the private and the public sector.
However, despite the increased adoption of biometric technologies by developed countries in the 1980s and 1990s, recent trends depict their reluctance to deploy biometric technology – or at least mass storage of biometric data – because of privacy concerns.188 Key instances included the scrapping of the National Identity Register and ID cards in the UK, and Germany’s decision to reject a centralised database when deploying biometric passports.189 By contrast, in developing countries there is a rise in the deployment of biometric technology since it is being portrayed to citizens as a means to establishing their legal identity and providing them access to services, as well as a tool for achieving economic development.
However, too often these goals are prioritised at the expense of their right to privacy and other human rights.190 Simon Davies, an eminent privacy expert, points out that it is not an accident or coincidence that biometric systems are most aggressively tried out with welfare recipients since they are not in a position to resist the State-mandated intrusion.
191 There has been a particular increase in the use of biometric technology in identification programs in developing countries. This is because “biometrics include a wide range of biological measures which are considered sufficiently unique at a population level to allow individual identification with high rates of accuracy”.192 Lack of formal identification and official identity documentation in the developing world is a serious challenge which impedes the ability of governments as well as development organisations to provide essential goods and services to the populations they serve.193 Further, identification is also essential to the gathering of accurate data which is required for monitoring the progress of government programmes.194 However, while biometric technology brings many advantages, the flip side is that the same technology can also lead to human rights violations:
“When adopted in the absence of strong legal frameworks and strict safeguards, biometric technologies pose grave threats to privacy and personal security, as their application can be broadened to facilitate discrimination, profiling and mass surveillance. The varying accuracy and failure rates of the technology can lead to misidentification, fraud and civic exclusion.”195 121 The adoption of biometric technologies in developing countries in particular poses unique challenges since the implementation of new technologies in these countries is rarely preceded by the enactment of robust legal frameworks. Assessments of countries where a legal mechanism to regulate new technologies or protect data has followed as an afterthought have shown that there exists a huge risk of mass human rights violations where individuals are denied basic fundamental rights, and in extreme cases, even their identity.
122 Technology today brings with it tremendous power and is much like two sides of a coin. When applied productively, it allows individuals around the world to access information, express themselves and participate in local and global discussions in real-time in ways previously thought unimaginable. The flip side is the concern over the abuse of new technology, including biometrics, by the State and private entities by actions such as surveillance and large-scale profiling. This is particularly acute, given the fact that technological advancements have far outpaced legislative change. As a consequence, the safeguards necessary to ensure protection of human rights and data protection are often missing. The lack of regulatory frameworks, or the inadequacy of existing frameworks, has societal and ethical consequences and poses a constant risk that the concepts of privacy, liberty and other fundamental freedoms will be misunderstood, eroded or devalued.
123 Privacy has been recognized as a fundamental human right in various national constitutions and numerous global and regional human rights treaties. In today’s digital age, the right to privacy is “the cornerstone that safeguards who we are and supports our on-going struggle to maintain our autonomy and self-determination in the face of increasing state power.”198 124 The proliferation of biometric technology has facilitated the invasion of individual privacy at an unprecedented scale. The raw information at the heart of biometrics is personal by its very nature.199 The Aadhaar Act recognises this as sensitive personal information. Biometric technology is unique in the sense that it uses part of the human body or behaviour as the basis of authentication or identification and is therefore intimately connected to the individual concerned. While biometric technology raises some of the same issues that arise when government agencies or private firms collect any personal information about citizens, there are specific features that distinguish biometric data from other personal data, making concerns about biometric technology of particular importance with regard to privacy protection.200 125 There are two main groups of privacy- related interests that are directly pertinent to the contemporary discussion on the ethical and legal implications of biometrics.
201 The first group falls under ‘informational privacy’ and is concerned with control of personal information. The ability to control personal information about oneself is closely related to the dignity of the individual, selfrespect and sense of personhood. The second interest group falls under the rubric of ‘physical privacy’. This sense of privacy transcends the purely physical and is aimed essentially at protecting the dignity of the human person. It is a safeguard against intrusions into persons’ physical bodies and spaces. Another issue is of property rights with respect to privacy, which concerns the appropriation and ownership of interests in human personality. In many jurisdictions, the basis of informational privacy is the notion that all information about an individual is in some fundamental way their own property, and it is theirs to communicate or retain as they deem fit.
126 The collection of most forms of biometric data requires some infringement of the data subject’s personal space. Iris and fingerprint scanners require close proximity of biometric sensors to body parts such as eyes, hands and fingertips. Even in the context of law enforcement and forensic identification, the use of fingerprinting is acknowledged to jeopardise physical privacy. Many countries have laws and regulations which are intended to regulate such measures, in order to protect the individual’s rights against infringement by state powers and law enforcement. However, biometrics for the purpose of authentication and identification is different as they do not have a specific goal of finding traces related to a crime but are instead conducted for the purpose of generating identity information specific to an individual. This difference in purpose actually renders the collection of physical biometrics a more serious breach of integrity and privacy.
It indicates that there may be a presumption that someone is guilty until proven innocent. This would be contrary to generally accepted legal doctrine that a person is innocent until proven guilty and will bring a lot of innocent people into surveillance schemes.
127 Concerns about physical privacy usually take a backseat as compared to concerns about informational privacy. The reason for this is that physical intrusion resulting from the use of biometric technology usually results from the collection of physical information. However, for some people of specific cultural or religious backgrounds, even the mental harm resulting from physical intrusion maybe quite serious.202 Another concern is that the widespread usage of biometrics substantially undermines the right to remain anonymous.203 People desire anonymity for a variety of reasons, including that it is fundamental to their sense of freedom and autonomy. Anonymity may turn out to be the only tool available for ordinary people to defend themselves against being profiled.
Thus, it is often argued that biometric technology should not be the appropriate choice of technology as biometrics by its very nature is inconsistent with anonymity. Given the manner in which personal information can be linked and identified using biometric data, the ability to remain anonymous is severely diminished. While some argue that “it is not obvious that more anonymity will be lost when biometrics are used”, this argument may have to be evaluated in light of the fact that there is no existing identifier that can be readily equated with biometrics.204 No existing identifier can expose as much information as biometric data nor is there any other identifier that is supposed to be so universal, long-lasting and intimately linked as biometrics.
To say that the use of biometrics will not cause further loss of anonymity may thus be overly optimistic. Semi-anonymity maybe possible, provided that the biometric system is carefully designed from the inception. Another significant change brought about by biometric technology is the precipitous decline of ‘privacy by obscurity’, which is essentially “a form of privacy afforded to individuals inadvertently by the inefficiencies of paper and other legacy recordkeeping.” 205 Now that paper records worldwide are giving way to more efficient digital record-keeping and identification, this form of privacy is being extinguished, and sometimes without commensurate data privacy protections put in place to remedy the effects of the changes.”206
128 Biometrically enhanced identity information, combined with demographic data such as address, age and gender, among other data, when used in increasingly large, automated systems creates profound changes in societies, particularly in regard to data protection, privacy, and security. Biometrics are at the very heart of identification systems. There are numerous instances in history where the persecution of groups of civilians on the basis of race, ethnicity and religion was facilitated through the use of identification systems. There is hence an alarming need to ensure that the on-going development of identification systems be carefully monitored, while taking into account lessons learnt from history.
129 It is important to justify the usage of biometric technology given the invasion of privacy. When the purpose of collecting the biometric data is just for authentication and there is little or no benefit in having stronger user identification, it is difficult to justify the collection of biometric information. The potential fear is that there are situations where there are few or no benefits to be gained from strong user verification / identification and this is where biometric technology may be unnecessary.207 (Example: When ascertaining whether an individual is old enough to go to a bar and drink alcohol, it is unnecessary to know who the person is, when all that is needed to be demonstrated is that the individual is of legal age). Fundamental rights are likely to be violated in case biometrics are used for applications merely requiring a low level of security.
130 Biometric data, by its very nature, is intrinsically linked to characteristics that make us ‘humans’ and its broad scope brings together a variety of personal elements. It is argued that the collection, analysis and storage of such innate data is dehumanising as it reduces the individual to but a number. Ultimately, organisations and governmental agencies must demonstrate that there is a compelling legitimate interest in using biometric technology and that an obligatory fingerprint requirement is reasonably related to the objective for which it is required. One way of avoiding unnecessary collection of biometric data is to set strict legal standards to ensure that the intrusion into privacy is commensurate with and proportional to the need for the collection of biometric data.208
F.2 Consent in the collection of biometric data
131 Rules on the collection of physical data by government agencies usually specify under what conditions a person can be required to provide fingerprints and/or bodily tissues. If consent is required, rules are in place to regulate the scope of consent. If forced searches are allowed, specifications are usually provided as to how and by whom the search will be performed. Therefore, the legal questions surrounding the issue should be:
(a) If required, what exactly should be the extent of coverage of the consent?
(b) When is the compulsory collection of biometric information required and who is eligible to conduct it?
(c) What is the procedure to do so?
(d)What exactly should be filed and stored?
132 Biometric technology is far from being a mature technology and a variety of errors inevitably occur. Mature technology is a popular term for any technology for which any improvements in deployment are evolutionary rather than revolutionary.209 Once a biometric system is compromised, it is compromised forever. In the event of biometric identity theft, there would appear to be no alternative but to withdraw the user from the system. Passwords and numbers can be changed, but how does one change the basic biological features that compromise biometrics in the event that there is a theft?
All of these parameters need to be applied to test the validity of the Aadhaar legislation in a two-part inquiry: First, reports and steps taken by the Government of India that guided the introduction and role of biometrics before the enactment of the Aadhaar Act will be analysed, which will be followed by an analysis of relevant provisions concerning the intersection of biometric technology and privacy, as they are enshrined in the Aadhaar Act, 2016 and supporting Regulations made under it.
F.3 Position before the Aadhaar legislation
Summary of Pre-Enactment Events 133 On 3 March 2006, the Department of Information Technology, Ministry of Communications & Information Technology, gave its approval for implementation of the project ‘Unique ID for Below Poverty Line Families’ (BPL) by the National Informatics Centre over a period of 12 months.210 This was followed by a Processes Committee being set up a few months later on 3 July 2006, to suggest the processes for updation, modification, addition and deletion of data from the core database to be created under the Unique ID (“UID”) for BPL Families Project.211 The Processes Committee prepared a paper titled ‘Strategic Vision: Unique Identification of Residents’212.
The paper recommended the linkage of the UID database with other databases which would ensure continuous updation and user-based validation and use of the Election Commission’s database as the base database.213 The document inter-alia, also stated that statutory backing would be required for adoption of UID in the long term;214 focus and conviction would be required on security and privacy to ensure adoption by different stakeholders;215 while ‘transparency vs. right to privacy’ was another challenge that would have to be addressed.216 Biometrics, however, found no mention in the paper at this stage.
Thereafter, on 4 December 2006, an Empowered Group of Ministers (“EGoM”), was constituted with the approval of the Prime Minister to collate the National Population Register (“NPR”) under the Citizenship Act 1955 and the Unique Identification Number Project.217 In its meeting held on 27 April 2007, the Processes Committee decided that the UID database would evolve in three stages: initial, intermediate and final. Biometrics was mentioned for the first time in the context of UID, when the committee agreed that if the infrastructure was available and the photograph and/or biometrics of a resident was obtainable along with other information, it would be captured in the initial and intermediate stages as well.218 Subsequently, the EGoM approved the establishment of a UID Authority under the Planning Commission on 28 January 2008.219 while the strategy to collate NPR and UID was also approved.
The EGoM also agreed that the collection of data under the NPR exercise could include collection of photographs and biometrics to the extent feasible, while it was also resolved that the data collected under the NPR would be handed over to the UID Authority for maintenance and updation. The EGoM, in its fourth meeting dated 4 November 2008 decided that initially, the UIDAI will be established as an executive body under the Planning Commission for a period of 5 years. UIDAI, it was envisaged, will create its database from the electoral roll of the ECI and verify it through Below Poverty Line and Public Distribution System data, but it would also have the authority to take its own decisions as to how a database should be built.220 Consequently, the Government of India issued a notification on 28 January 2009 constituting the UIDAI as an attached office and executive authority under the aegis of the Planning Commission.
134 Following the constitution of UIDAI, the Secretary, Planning Commission addressed a letter to Chief Secretaries of all States/ UTs on 6 May 2009 enclosing a brief write up on UIDAI and UID numbers for resident Indians.
The letter included the concept, implementation strategy, model of the project along with the role and responsibilities of the states/ UTs.221 It was also decided that partner databases for two-way linkages between the UID database and the partner databases for maintenance and continuous updation of the UID databases would be ECI database, Ministry of Rural Developmentrural household survey database and the State ration card (PDS) databases. 135 The first meeting of the PM’s Council of UIDAI, was held on 12 August 2009. Various proposals were approved by the Council,222 by which it was decided, among other things, that the proposal to designate UIDAI as an apex body to set standards in the area of biometrics and demographic data structures be approved. On 29 September 2009, UIDAI set up the Biometrics Standards Committee (“BSC”) to frame biometric standards for UIDAI. The Committee was assigned with the following mandate:223
· To develop biometric standards that will ensure interoperability of devices, systems and processes used by various agencies that use the UID system.
· To review the existing standards of Biometrics and, if required, modify/extend/enhance them so as to serve the specific requirements of UIDAI relating to de-duplication and Authentication. This was followed by the creation of the Demographic Data Standards and Verification Procedure Committee (“DDSVPC”) on 9 October 2009, with the following mandate:224
· Review/ modify/ extend/ enhance the existing standards of Demographic data and recommend the Demographic Data standards (The data fields and their formats/structure, etc.) that will ensure interoperability and standardization of basic demographic data and their structure used by various agencies that use the UID system; and
· Recommend the Process of Verification of this demographic data in order to ensure that the data captured, at the time of enrolment of the residents into the UID system, is correct.
136 The DDSVPC in its report dated 9 December 2009, stated that UIDAI had selected biometrics features as the primary method to check for duplicate identity. In order to ensure that an individual was uniquely identified in an easy and cost-effective manner, it was necessary to ensure that the captured biometric information was capable of carrying out de-duplication at the time when information was collected.225 The Know Your Resident (“KYR”) verification procedure was introduced to ensure that “key demographic data is verified properly so that the data within UID system can be used for authentication of identity by various systems”. Three distinct methods of verification were to be acceptable under UID. Verification could be based on
· Supporting documents;
· An introducer system under which a network of “approved” introducers can introduce a resident and vouch for the validity of the resident’s information; and (This idea was borrowed from the account opening procedure in the banks.)
· The process adopted for public scrutiny in the National Population Register.
137 In order to verify the correctness of certain mandatory fields, such as name, date-of-birth, and address, a “Proof of Identity” (PoI) and “Proof of Address” (PoA) would be required. This would comprise of documents containing the resident’s name and photograph and the name and address, respectively. On 9 April 2010, the collection of iris biometrics for the NPR exercise was approved.226 138 A strategy overview issued by UIDAI in April 2010 described the features, benefits, revenue model and timelines of the project.227 The survey outlined that UIDAI would collect the following demographic and biometric information from residents in order to issue a UID number:
· Name
· Date of birth
· Gender
· Father’s/ Husband’s/ Guardian’s name and UID number (optional for adult residents)
· Mother’s/ Wife’s/ Guardian’s name and UID number (optional for adult residents)
· Introducer’s name and UID number ( in case of lack of documents)
· Address
· All ten fingerprints, photograph and both iris scans On 12 May 2010, a note outlining the background of UIDAI, and proposing an approach for collection of demographic and biometric attributes of residents for the UID project was submitted to the Cabinet Committee on UIDAI.228 Permission of the Union Cabinet was sought to ensure that the approach which was proposed should be adhered to by the Registrar General of India for the NPR exercise and by all other Registrars in the UID system.
The rationale behind the inclusion of iris biometrics and the need for capturing iris scans at the time of capturing biometric details was also explained. This was followed by the introduction of the National Identification Authority of India Bill, 2010 (NIAI Bill) in the Rajya Sabha on 3 December 2010. On 13 February 2011, the one millionth Aadhaar card was delivered. Thereafter, on 11 April 2011, the Central Government notified the Information Technology (Reasonable security practices and procedures and sensitive personal data or information) Rules, 2011 [“IT Rules”] under Section 43A of the IT Act, 2000. On 29 September 2011, the Aadhaar project completed one year.
An announcement was made of the generation of ten crore enrolments and of more than 3.75 crore Aadhaar numbers. Analysis of UIDAI Reports & Rights of Registrars A. Biometrics Standards Committee (BSC) Report 139 BSC in its report dated 30 December 2009 stated that it held extensive meetings and discussions with international experts and technology suppliers. A technical sub-group was formed to collect Indian fingerprints and analyze quality. Over 2,50,000 fingerprint images from 25,000 persons were sourced from the districts of Delhi, UP, Bihar and Orissa.
Nearly all the images were from rural regions, and were collected by different agencies using different capture devices, and through different operational processes. The BSC report is silent about the pretext on which fingerprints of 25,000 people were collected. This action of UIDAI raises privacy concerns especially since the fingerprints were collected from rural regions where people may not have been aware or made aware by UIDAI before collection of fingerprints, of the possible privacy harms of giving up biometrics.
BSC after reviewing international standards and current national recommendations, concluded that a fingerprints-based biometric system was to be at the core of UIDAI’s de-duplication efforts and that the ISO 19794 series of biometrics standards for fingerprints, face and iris set by the International Standards Organization (ISO) were most suitable for the UID project.229 BSC also observed that while a fingerprints-based biometric system shall be at the core of UIDAI’s de-duplication efforts, its accuracy in the Indian context could not predicted in the absence of empirical data: “The Committee notes that face is the most commonly captured biometric, and frequently used in manual checking. However, stand-alone, automatic face recognition does not provide a high level of accuracy, and can only be used to supplement a primary biometric modality.
Fingerprinting, the oldest biometric technology, has the largest market share of all biometrics modalities globally. … Based on these factors, the Committee recognizes that a fingerprints-based biometrics system shall be at the core of the UIDAI’s deduplication efforts… The Committee, however, is also conscious of the fact that de-duplication of the magnitude required by the UIDAI has never been implemented in the world. In the global context, a de-duplication accuracy of 99% has been achieved so far, using good quality fingerprints against a database of up to fifty million.
Two factors, however, raise uncertainty about the accuracy that can be achieved through fingerprints. First, retaining efficacy while scaling the database size from fifty million to a billion has not been adequately analyzed. Second, fingerprint quality, the most important variable for determining de-duplication accuracy, has not been studied in depth in the Indian context.”230 140 In its report for discussion titled “Technical Standards for Digital Identity Systems for Digital Identity”, the Identification for Development (ID4D) initiative, a cross-departmental effort report of the World Bank, noted that UIDAI had not implemented “an important security standard, ISO 24745, which provides guidance for the protection of biometric information for confidentiality and integrity during storage or managing identities … due to the complexity of applicable compliance procedures” for the Aadhaar system.231 Proponents of the program argue that in all fairness to UIDAI, it has to be noticed that the ISO 24745 standard was published in August 2011 whereas the report of BSC had already been submitted to UIDAI in January 2010. However, Mr. Myung Geun Chun, the Project Editor of ISO 24745, is reported to have stated that ISO 24745 standard is an ‘invaluable tool’ for addressing ‘unique privacy concerns’ like ‘unlawful processing and use of data’ raised by biometric identification because of its binding nature ‘which links biometrics with personally identifiable information’.232 ISO 24745 seeks to “safeguard the security of a biometric system and the privacy of data subjects with solid countermeasures”.233 ISO 24745 standard specifies:
· “Analysis of threats and countermeasures inherent in biometric and biometric system application models;
· Security requirements for binding between a biometric reference and an identity reference;
· Biometric system application models with different scenarios for the storage and comparison of biometric references;
· Guidance on the protection of an individual’s privacy during the processing of biometric information.
B. Strategy Overview of 2010
In this report, a balance was sought to be struck between ‘privacy and purpose’ in respect of the information of the residents which was collected. The report states that ‘agencies’ may store the information of the residents at the time of enrolment, but they will not have access to the information stored in the UID database.
235 Further, for the purposes of authentication, requests made by the agencies would be answered through a ‘Yes’ or a ‘No’ response only.
236 Under the sub-heading “Protecting Privacy and Confidentiality”, the report stated that the additional information which was being sought from people was only biometric information like fingerprints and iris scans, as other information was already available with public and private agencies in the country.
237 Right to privacy and confidentiality were sought to be protected by putting necessary provisions “in place”.
238 It was also observed in the context of privacy that loss of biometric information of a resident who is a victim of identity theft, especially when such information is linked to banking, social security and passport records, risks financial and other assets and the reputation of the resident.
239 According to the review, the envisaged UIDAI Act (which was still under contemplation at the time of publishing of this report and had not yet been legislated) would have remedies for the following offences:
· “Unauthorized disclosure of information by anyone in UIDAI, Registrar or the Enrolling agency;
· Disclosure of information violating the protocols set in place by UIDAI;
· Sharing any of the data on the database with anyone;
· Engaging in or facilitating analysis of the data for anyone;
· Engaging in or facilitating profiling of any nature for anyone or providing information for profiling of any nature for anyone;
· All offences under the Information Technology Act shall be deemed to be offences under UIDAI if directed against UIDAI or its database.
“240 However, according to the report, UIDAI was to concern itself only with identity fraud and any grievances in respect of document fraud (counterfeit/ misleading documents) were to be left to the Registrar enrolling the resident.241 141 The following conclusions emerge from the UIDAI’s strategy overview: Firstly, the UIDAI was aware of the importance of biometric information before the Aadhaar programme had been rolled out. Secondly, UIDAI had itself contemplated a scenario of identity theft which could occur at the time of enrollment for Aadhaar cards. However, it had no solution to the possible harms which could result after the identity theft of a person, more so when the potential ‘UIDAI Act’ was still in the pipeline and was not eventually enacted until 2016.
C. Registrars
142 The term ‘Registrar’ was first defined by UIDAI in its DDSVPC Report as “any government or private agency that will partner with UIDAI in order to enroll and authenticate residents”.242 In the Strategy Overview, the term was defined as “agencies such as central and state departments and private sector agencies who will be ‘Registrars’ for the UIDAI”.243 The Strategy Overview also stated that: “Registrars will process UID applications, and connect to the CIDR to de-duplicate resident information and receive UID numbers.
These Registrars can either be enrollers, or will appoint agencies as enrollers, who will interface with people seeking UID numbers. The Authority will also partner with service providers for authentication. If the Registrar issues a card to the resident, the UIDAI will recommend that the card contain the UID number, name and photograph. They will be free to add any more information related to their services (such as Customer ID by bank). They will also be free to print/ store the biometric collected from the applicant on the issued card. If more registrars store such biometric information in a single card format, the cards will become interoperable for offline verification. But the UIDAI will not insist on, audit or enforce this.”244
(Emphasis supplied)
143 In the ‘Aadhaar Handbook for Registrars 2010′ (“2010 Handbook”), following policy guidelines were laid down in respect of Registrars: 1. “Registrars may retain the biometric data collected from residents enrolled by them. However, the Registrar will have to exercise a fiduciary duty of care with respect to the data collected from residents and will be responsible for loss, unauthorized access to and misuse of data in their custody. 2. In order to ensure data integrity and security, the biometrics captured shall be encrypted upon collection by using the encryption key defined by the Registrar. It is the responsibility of the Registrar to ensure the safety, security and confidentiality of this data which is in their custody. The Registrar must protect the data from unauthorized access and misuse. The UIDAI will define guidelines for the storage of biometric data in order to give the Registrar some guidance on ensuring security of the data.
The Registrar shall have to define their own security policy and protocols to ensure safety of the Biometric data. The Registrars shall bear liability for any loss, unauthorized access and misuse of this data. In the interest of transparency, it is recommended that the Registrar inform the resident that they will be keeping the biometric data and also define how the data will be used and how it will be kept secure.”245
(Emphasis supplied)
In the ‘Aadhaar Handbook for Registrars 2013′ (“2013 Handbook”), it was stated that “UIDAI has defined security guidelines for the storage of biometric data”.246 While it is indicated in the handbook that guidelines for storage were defined by UIDAI, it is evident that this took place only after 2010 before which the registrars were functioning without guidelines mandating how the biometric data was to be kept secure. The following guideline finds mention both in the Handbook of 2010 and 2013: “In the interest of transparency, it is recommended that the Registrar inform the resident that they will be keeping the biometric data and also define how the data will be used and how it will be kept secure”.247 However, it is apparent from this guideline that it was merely a recommendation to the Registrars, and no obligation was cast upon the Registrars, to inform residents that their biometric data will be stored by them and how the data was to be used and kept secure. In contrast, Regulation 5 of the Aadhaar (Sharing of Information) Regulations 2016, states: “Responsibility of any agency or entity other than requesting entity with respect to Aadhaar number. —
(1) Any individual, agency or entity which collects Aadhaar number or any document containing the Aadhaar number, shall:
(a) collect, store and use the Aadhaar number for a lawful purpose;
(b) inform the Aadhaar number holder the following details:—
i. the purpose for which the information is collected;
ii. whether submission of Aadhaar number or proof of Aadhaar for such purpose is mandatory or voluntary, and if mandatory, the legal provision mandating it; iii. alternatives to submission of Aadhaar number or the document containing Aadhaar number, if any;
(c) obtain consent of the Aadhaar number holder to the collection, storage and use of his Aadhaar number for the specified purposes.
(2) Such individual, agency or entity shall not use the Aadhaar number for any purpose other than those specified to the Aadhaar number holder at the time of obtaining his consent.
(3) Such individual, agency or entity shall not share the Aadhaar number with any person without the consent of the Aadhaar number holder.”
(Emphasis supplied)
144 What the Registrar is obliged to do under law after the enactment of the Aadhaar Act, was a recommendation to the Registrar prior to the enactment of the Aadhaar Act. Thus, it is uncertain whether residents were informed about where and how their data would be kept secure since the guidelines to the Registrars were only recommendatory in nature. Similarly, in a UIDAI document titled ‘Roles and Responsibilities of Enrollment Staff, 2017′, one of the ‘Fifteen Commandments that an Operator must remember during Resident Enrollment’ is “Make sure that the resident is well informed that his/her PART F 207 biometric will only be used for Aadhaar Enrolment/Update and no other purpose”.248
However, in the UIDAI document titled ‘Enrollment Process Essentials, 2012′, there is no mention of any such obligation being placed upon the enrolment staff.249 In the absence of informed consent for the collection of data, a shadow of potential illegality is cast.
F.4 Privacy Concerns in the Aadhaar Act
1 Consent during enrolment and authentication & the right to access
information under the Aadhaar Act 145 Section 3(2) of the Aadhaar Act requires enrolment agencies to inform the individual being enrolled about:
a) the manner in which information shall be used;
b) the nature of recipients with whom the information is to be shared during authentication; and c) the existence of a right to access information. However, the Enrolment Form in Schedule I of the Enrolment Regulations does not offer any clarification or mechanism on how the mandate of Section 3(2) is to be fulfilled. The right of an individual to access information related to his or her authentication record is recognized in Section 3(2)(c) and Section 32(2) of the Aadhaar Act. However, the supplementary regulations that complement the Act are bereft of detail on the procedure to access such information.
Similarly, Regulation 9(c) of the Enrolment Regulations states that the procedure for accessing data would be provided to residents through the enrolment form, which is found in Schedule I to the Enrolment Regulations. However, all that Schedule I states is: “I have a right to access my identity information (except core biometrics) following the procedure laid down by UIDAI”, without any such procedure actually being laid down. 146 Section 2(I) of the Act, which defines an enrolling agency read with Regulation 23 of the Aadhaar (Enrolment and Update) Regulations allows for the collection of sensitive personal data (demographic and biometric information) of individuals by private agencies, which also have to discharge the burden of explaining the voluntary nature of Aadhaar registration and obtaining an individual’s informed consent.
The Authentication Regulations, framed under sub-section (1), and subclauses (f) and (w) of sub-section (2) of Section 54 of the Aadhaar Act deal with the authentication framework for Aadhaar numbers, the governance of authentication agencies and the procedure for collection, storage of authentication data and records. Regulation 5 (1) states what details shall be made available to the Aadhaar number holder at the time of authentication which are
a) the nature of information that will be shared by the Authority upon authentication,
(b) the uses to which the information received during authentication may be put; and
(c) alternatives to submission of identity information. Regulation 6 (2) mandates that a requesting entity shall obtain the consent of an Aadhaar number holder for authentication in physical or, preferably, in electronic form and maintain logs or records of the consent obtained in the manner and form as may be specified by the Authority for this purpose. Although Regulation 5 mentions that at the time of authentication, requesting entities shall inform the Aadhaar number holder of alternatives to submission of identity information for the purpose of authentication, and Regulation 6 mandates that the requesting entity shall obtain the consent of the Aadhaar number holder for the authentication, in neither of the above circumstances do the regulations specify the clearly defined options that should be made available to the Aadhaar number holder in case they do not wish to submit identity information, nor do the regulations specify the procedure to be followed in case the Aadhaar number holder does not provide consent. This is a significant omission. Measures for providing alternatives must be defined in all identity systems, particularly those that are implemented on a large scale.
2 Extent of information disclosed during authentication & sharing of core biometric information
147 Section 8(4) of the Act permits the Authority to respond to an authentication query with a “positive, negative or any other appropriate response sharing such identity information excluding any core biometric information”. The petitioners have argued that the wide ambit of this provision gives the Authority discretion to respond to the requesting entity with information including an individual’s photograph, name, date of birth, address, mobile number, email address and any other demographic information that was disclosed at the time of enrolment. Moreover, it must be realized that even if core biometric information cannot be shared, demographic information is nonetheless, sensitive.
Regulation 2(j) of the Authentication Regulations250 provides that a digitally signed response with e-KYC data251 [which is defined in Regulation 2(k)] can be returned to the requesting entity, while Regulation 3(ii)252 provides for this form of authentication (e-KYC) by UIDAI.
148 Section 29(1) of the Aadhaar Act expressly states that ‘core biometric information can never be shared with anyone for any reason whatsoever or be used for any purpose other than generation of Aadhaar numbers and authentication under this Act’. However, this provision which seemingly protects an individual’s core biometric information from being shared is contradicted by Section 29(4)253 of the Act, the proviso to which grants UIDAI the power to publish, display or post core biometric information of an individual for purposes specified by the regulations. The language of this section is overbroad and which could lead to transgressions and abuse of power.
Moreover, sub-sections 29(1) and (2), in effect, create distinction between two classes of information (core biometric information and identity information), which are integral to individual identity. Identity information requires equal protection as provided to core biometric information.
3 Expansive scope of biometric information
149 Definitions of biometric information [Section 2(g)], core biometric information [Section 2(j)] and demographic information [Section 2(k)] under the Aadhaar Act are inclusive and expansive. Section 2(g) defines ‘biometric information’ as “photograph, fingerprint, iris scan, or such other biological attributes of an individual as may be specified by regulations”. Section 2(j) defines ‘core biometric information’ as “fingerprint, Iris scan, or such other biological attribute of an individual as may be specified by regulations”. Section 2(t) explains that the regulations are to be made by UIDAI, which is the supreme authority under the Act. Sections 2(g), (j), (k) and (t) give discretionary power to UIDAI to define the scope of biometric and demographic information. Although the Act specifically provides what information can be collected, it does not specifically prohibit the collection of further biometric information.
The scope of what can, in addition, be collected, has been left to regulations. These provisions empower UIDAI to expand on the nature of information already collected at the time of enrolment, to the extent of also collecting ‘such other biological attributes’ that it may deem fit by specifying it in regulations at a future date. The definitions of these sections provide the government with unbridled powers to add to the list of biometric details that UIDAI can require a citizen to part with during enrolment which might even amount to an invasive collection of biological attributes including blood and urine samples of individuals.
4 Other concerns regarding the Aadhaar Act: Misconceptions regarding the efficacy of biometric information
150 The uniqueness of a fingerprint in forensic science remains an assumption without watertight proof. The uniqueness of biometric data is not absolute, it is relative. Not everyone will have a particular biometric trait, or an individual’s biometric trait may be significantly different from the ‘normal’ expected trait. Some people may be missing fingerprints due to skin or other disease, which may cause further problems when enrolling a large population in a fingerprint-based register. Discrimination concerns may also be raised in such a case. Therefore, a large scale biometric scheme will usually need to utilise more than one biometric. For example- both fingerprint and face to ensure all people can be enrolled.254 The stability of even so called stable types of biometric data is not absolute.
Each time an individual places a fingerprint on a fingerprint reader, the pattern may appear to be the same from a short distance, but there are actually small differences in the pattern due to dryness, moisture and elasticity of the skin. Moreover, cuts and scratches can alter the pattern. Similarly, even the iris, a popular biometric measurement suffers from difficulties in obtaining a valid image. The iris can also be hindered by specula reflections in uncontrolled lighting situations. These problems also apply to other relatively stable biometric identifiers.255 151 Sections 6256 and 31(2)257 of the Aadhaar Act place an additional onus on individual Aadhaar holders to update their information. These provisions create a legal mandate on individuals to ensure that their information is accurate within the CIDR.
It is an acknowledgement that an individual’s biometric information may change from time to time. Natural factors like ageing, manual labour, injury and illness can cause an individual’s biometric information to be altered over the course of a lifetime. Critics of the Aadhaar program however point to the fact that provisions for updation fly in the face of UIDAI’s repeated advertisements that Aadhaar enrolment is a “one-time” affair, as it is not and will never be. Moreover, there is no way in which a person can estimate that he or she is due for an update, as this is not something that can be discerned by actions as innocuous as looking in the mirror or at one’s fingers, and therefore there remains no objective means of complying with the above sections. In fact, an authentication failure and a subsequent denial of welfare benefits, a subsidy or a service that an individual is entitled to might be the only way one comes to the conclusion that his or her biometrics need to be updated in the CIDR.258 Moreover, since the promise of Aadhaar as a unique identity hinges on the uniqueness of biometrics, it would be logical to assume that any update to biometric data should go through the same rigour as a new enrolment. Regulation 19(a), entitled ‘Modes of Updating Residents Information’ under Chapter IV of the Aadhaar (Enrolment and Update) Regulations, 2016 provides: “19. Mode of Updating Residents Information:
a) At any enrolment centre with the assistance of the operator and/or supervisor. The resident will be biometrically authenticated and shall be required to provide his Aadhaar number along with the identity information sought to be updated.” This raises the question as to how an individual will update his/her biometric information. If the biometric information stored in CIDR has changed, the present biometrics will lead to mismatch during authentication. This Regulation does not provide any real clarity on how updation should be taking place in practice for the following reasons:
1. As required by the regulation, can an individual be asked to undergo biometric authentication, when the purpose is to update the biometrics?
2. Does the provision amount to an implied expectation that an individual is supposed to revisit the enrolment centre before all ten fingers and two irises (core biometric information) are rendered inaccurate for the purposes of authentication?259 This is also evidence of the fact that an Aadhaar enrolment is not a one-time affair.
5 No access to biometric records in database
152 The proviso to Section 28(5)260 of the Aadhaar Act disallows an individual access to the biometric information that forms the core of his or her unique ID (Aadhaar). The lack of access is problematic for the following reasons: First, verification of whether the biometrics have been recorded correctly or not in the first place is not possible. This becomes critical when that same information forms the basis of identity and is the basis of authentication and subsequent access to welfare benefits and other services.
Second, there is a great potential for fraudulently replacing a person’s biometric identity in the database, as the individual has no means to verify the biometric information that has been recorded at the time of enrolment. Even an entity like the enrolment operator (with a software hack) could upload someone else’s biometrics against another person.261 Denial of access to the individual violates a fundamental principle of data protection: ownership of the data must at all times vest with the individual. Overlooking this fundamental principle is manifestly arbitrary and violative of Article 14.
6 Biometric locking
153 Authentication Regulations 11 (1) and (4) provide for the facility of Biometric Locking. Regulation 11(1) provides:
Regulation 11(4) provides:
“The Authority may make provisions for Aadhaar number holders to remove such permanent locks at any point in a secure manner.” The provision allowing biometric locking is salutary to the extent that it allows Aadhaar number holders to permanently lock their biometrics and temporarily unlock them only when needed for biometric authentication. But the regulation is problematic to the extent that it also empowers the UIDAI to make provisions to remove such locking without any specified grounds for doing so.262
7 Key takeaways
154 The use of biometric technology is only likely to grow dramatically both in the private and public sector.
On our part, we can only ensure that the strides made in technology are accompanied by stringent legal and technical safeguards so that biometrics do not become a threat to privacy.263 155 There is no unique concept of privacy and there maybe trade-offs between privacy and other objectives.264 The challenge regarding privacy is best put in the following words:
“The definition of privacy in any jurisdiction must take into account cultural, historical, legal, religious and other local factors. One size may not fit all countries, regions, or cultures when it comes to privacy or to some elements of privacy. In addition, views of privacy change as time passes and technology advances. However, different perspectives are not a barrier to evaluating privacy but a challenge.
“265 The relationship between biometrics and privacy is completely shaped by the design of the systems and the framework within which private and personal data is handled. Unfortunately, particularly in developing countries the adoption of biometrics has not been accompanied by an adequate discussion of privacy concerns.266 Biometrics can also be a “staunch friend of privacy” when the technology is used for controlling access and to restrict unauthorized personnel from gaining access to sensitive personal information.267
While evaluating privacy consequences of biometric technology, it is also important to bear in mind that there cannot be an assumption that current privacy protections which may be appropriate for the present state of technology will also be sufficient in the future.268 Technology will continue to develop as will the need to develop corresponding privacy protections. Concerns around privacy and data protection will have to be addressed. “Fair Information Practices (FIPs), Privacy by Design (PbD), and Privacy Impact Assessments (PIAs)”269 might be useful in addressing these concerns. FIPs offer the substantive content for a privacy policy. PbD offers a proactive approach to the protection of privacy that relies on advance planning rather responding to problems after they arise. PIAs offer a formal way to consider and assess the privacy consequences of technology or other choices, including consideration of alternatives early in the planning stages. These three methodologies are not mutually exclusive and can be combined to achieve the just and optimal result for society.270 156 of particular significance is the “Do Not Harm” principle which means that biometrics and digital identity should not be used by the issuing authority, typically a government, or adjacent parties to serve purposes that could harm the individuals holding the identification.271 Identity systems, whether in paper or digital, must work for the public good and must do no harm. However, identity systems due to their inherent power, can cause harm when placed into hostile hands and used improperly. Great care must be taken to prevent this misuse. “Do No Harm” requires rigorous evaluation, foresight, and continual oversight.272 157 There are many adversarial actors – from private espionage groups to foreign governments, who may try to exploit data vulnerabilities.
There is also the threat of abuse of power by future governments. However, creating and instilling strong privacy protection laws and safeguards may decrease these risks- such as the framework provided by the EUGDPR273. In order to uphold democratic values, the government needs to curtail its own powers concerning the tracking of all citizens and prevent the needless collection of data. Such protections may assuage the fears and uphold the long-term legitimacy of Aadhaar.
If the legislative process takes into account public feedback and addresses the privacy concerns regarding Aadhaar, it would provide a solid basis for more digital initiatives, which are imminent in today’s digital age. However, in its current form, the Aadhaar framework does not address the privacy concerns issues discussed in this section of the judgment.
G Legitimate state aim
G.I Directive Principles
158 The Union government has contended that the legitimate state interest in pursuing the Aadhaar project flows from the solicitous concern shown in the text and spirit of the Constitution for realising socio-economic rights. The right to food must, according to the view proposed before the Court, trump over the right to privacy. The Aadhaar project, it has been urged, seeks to fulfil socioeconomic entitlements.
159 The Constituent Assembly did not work in a vacuum. The idealism with which the members of the Assembly drafted the Constitution was the result of the “social content of the Independence movement”274, which came from the awareness of the members about the existing conditions of the Indian masses. Granville Austin has therefore referred to the Constitution as a “social document” and a “modernizing force”, whose provisions reflect “humanitarian sentiments”.275 The Constitution was the medium through which the nascent Indian democracy was to foster many goals. Austin observes:
“Transcendent among [the goals] was that of social revolution. Through this revolution would be fulfilled the basic needs of the common man, and, it was hoped, this revolution would bring about fundamental changes in the structure of Indian society.”276
(Emphasis supplied)
Austin has further observed: “The first task of [the] Assembly… [was] to free India through a new constitution, to feed the starving people, and to clothe the naked masses, and to give every Indian the fullest opportunity to develop himself according to his capacity.”277 In his work titled “The Constitution of India: A Contextual Analysis”, Arun K Thiruvengadam identified one such goal of the Constitution as follows: “The Indian Constitution sought to lay the blueprint for economic development of the vast subcontinental nation, which was an imperative for a populace that was largely illiterate, poor and disproportionately situated in rural societies that had limited access to many essential social goods and infrastructural facilities.278” .
“By establishing these positive obligations of the state, the members of the Constituent Assembly made it the responsibility of future Indian governments to find a middle way between individual liberty and the public good, between preserving the property and the privilege of the few and bestowing benefits on the many in order to liberate ‘the powers of all men equally for contributions to the common good’.”279
(Emphasis supplied)
160 The draftpersons of the Constitution believed that the driving force to bring social change rested with the State.
This is evident from an instance during the proceedings of the Constituent Assembly. Dr. B R Ambedkar had submitted to the Assembly a social scheme to be incorporated into the Constitution, which included provisions to cover every adult Indian by life insurance. However, his social scheme was rejected on the ground that such provisions should be left to legislation and need not be embodied into the Constitution.280 161 The social and economic goals which were contemplated at the time of Independence remain at the forefront of the State’s agenda even today. Certain parts of the Constitution play a leading role in declaring the blueprint of its social intent. Directive Principles were specifically incorporated into the Constitution for this purpose.
Though not enforceable in courts, the principles are “fundamental in the governance of the country” and it is the duty of the State to apply these principles while making laws.281 The essence of the Directive Principles lies in Article 38 of the Constitution, which places an obligation on the State to secure a social order for the promotion of the welfare of the people. Titled as Part IV of the Constitution, the Directive Principles are symbolic of the welfare vision of the Constitution makers. Article 38 of the Constitution provides that :
“(1) The State shall strive to promote the welfare of the people by securing and protecting as effectively as it may a social order in which justice, social economic and political, shall inform all the institutions of the national life.
(2) The State shall, in particular, strive to minimize the inequalities in income, and endeavor to eliminate inequalities in status, facilities and opportunities, not only amongst individuals but also amongst groups of people residing in different areas or engaged in different vocations.” Clauses (b), (c), (e) and (f) of Article 39 provide thus :
“39. The State shall, in particular, direct its policy towards securing – …
(b) that the ownership and control of the material resources of the community are so distributed as best to subserve the common good;
(c) that the operation of the economic system does not result in the concentration of wealth and means of production to the common detriment; ..
(e) that the health and strength of workers, men and women, and the tender age of children are not abused and that citizens are not forced by economic necessity to enter avocations unsuited to their age or strength;
(f) that children are given opportunities and facilities to develop in a healthy manner and in conditions of freedom and dignity and that childhood and youth are protected against exploitation and against moral and material abandonment.” Article 41 speaks of the right to work, to education, and to public assistance : “41. The State shall, within the limits of its economic capacity and development, make effective provision for securing the right to work, to education and to public assistance in cases of unemployment, old age, sickness and disablement, and in other cases of undeserved want.” Article 43 contemplates a living wage and conditions of work which provide a decent standard of life:
“43. The State shall endeavour to secure, by suitable legislation or economic organisation or in any other way, to all workers, agricultural, industrial or otherwise, work, a living wage, conditions of work ensuring a decent standard of life and full enjoyment of leisure and social and cultural opportunities and, in particular, the State shall endeavour to promote cottage industries on an individual or co-operative basis in rural areas.” Article 47 casts a positive obligation upon the State to raise the level of nutrition and the standard of living and to improve public health, as among its primary duties. Reflecting a constitutional vision of socio-economic justice, the values adopted in the Directive Principles are to be progressively realised in the course of social and economic development.
162 In a recently published book titled “Supreme Court of India: The Beginnings”, George H Gadbois, Jr. observes that the Indian Constitution, “easily the lengthiest fundamental law in the world, probably ranks also as one of the most eclectic ever produced”.282 Reflecting upon the constitutional models from which the draftspersons of India’s Constitution drew sustenance, Gadbois states: “The Constitution makes provision for a parliamentary system adapted from the British model, a federation patterned after the Government of India Act of 1935 and the Canadian Constitution, a set of emergency powers similar to those set forth in the Weimar Constitution, a lengthy list of fundamental rights adapted from the American experience with a Bill of Rights, a Supreme Court endowed with express powers of judicial review for which the American Supreme Court served as the model, and list of “Directive Principles of State Policy” patterned after the Constitution of Eire.”283 Reflecting on the Directive Principles, Gadbois observes: “Suffice to say that the directive principles have provided the constitutional basis and justification for the Government’s efforts to establish a welfare state, or, to use the designation preferred by Indian leaders, a “socialist pattern of society”.284 The sanction behind the Directives, according to him “is political and not juridical”. On the other hand, the fundamental rights are justiciable because Article 13 provides that a law which takes them away or abridges them will be void.
The conflict as Gadbois sees it is this: “the directive principles are a set of instructions to the Government of the day to legislate into being a welfare state, which means, of course, an emphasis on the social and economic uplift of the community at large and a corresponding subtraction from individual rights. It is the duty of the Government to apply these principles in making laws. In short, the Constitution confers upon the Supreme Court the task of making the fundamental rights meaningful against possible infringements by the legislatures and executives, and makes it obligatory for the Government to bring about changes in the social and economic life of the nation, changes which were bound to affect adversely some private rights. It is conceivable at least, that both the Supreme Court and the Government could have pursued their respective tasks without conflict, but this did not happen.
The legislatures, purporting to be doing no more than carrying out the duties prescribed in the directive principles, enacted legislation which the Supreme Court found to be in conflict with some of the fundamental rights.”285 This formulation by Gadbois formed part of a dissertation in April 1965. The evolution of jurisprudence in India since then has altered the Constitutional dialogue. Over time, the values enshrined in the Directive Principles have been read into the guarantees of freedom in Part III. In incremental stages, the realisation of economic freedom has been brought within the realm of justiciability, at least as a measure of the reasonableness of legislative programmes designed to achieve social welfare.
163 As our constitutional jurisprudence has evolved, the Directive Principles have been recognised as being more than a mere statement of desirable goals. By a process of constitutional interpretation, the values contained in them have been adopted as standards of reasonableness to expand the meaning and ambit of the fundamental rights guaranteed by Part III of the Constitution.286 In doing so, judicial interpretation has attempted to imbue a substantive constitutional content to the international obligations assumed by India in the Universal Declaration of Human Rights and the International Covenant on Economic and Social and Cultural Rights. Eradicating extreme poverty and hunger is a significant facet of the Millennium Development Goals of the United Nations. Social welfare legislation is but a step to achieve those goals.
The enactment of the National Food Security Act 2013 constituted a milestone in legislative attempts to provide food security at the household level. The Act discerns a targeted Public Distribution System for providing food-grains to those below the poverty line. The rules contemplated in Section 12(2)(b), incorporate the application of Information and Communication Technology tools to ensure transparency of governance and prevent a diversion of benefits. Another important piece of legislation has been the Mahatma Gandhi National Rural Employment Guarantee Act (MGNREGA) Act 2005 which was enacted for the enhancement of livelihood and security of rural households. The Act guarantees a hundred days of wage employment in every financial year to at least one able-bodied member of every household in rural areas in public works programmes designed to create public assets.
Both the National Food Security Act 2013 and the MGNREGA Act 2005 follow a rights-based approach in dealing with endemic problems of poverty and deprivation in rural areas. Leveraging Aadhaar for biometric identification of beneficiaries, it has been argued by the respondents, is an intrinsic part of the legislative effort to ensure that benefits in terms of food security and employment guarantee are channelised to those for whom they are meant.
G.2 Development and freedom
164 Many scholars have delved into the substantive themes of the Indian Constitution. Upendra Baxi has argued that the Indian Constitution has four sovereign virtues: “rights, justice, development, and governance”287. Baxi notes that they are “intertwined and interlocked with the rest and, in contradictory combination/recombinations with both the constitutional and social past and their future images”.288 Development is a leading aspect of our constitutional vision.
Development in the constitutional context is not only economic development assessed in terms of conventional indicators such as the growth of the gross domestic product or industrial output. The central exercise of development in a constitutional sense is addressing the “deprivation, destitution and oppression”289 that plague an individual’s life.
165 In a traditional sense, freedom and liberty mean an absence of interference by the state into human affairs. Liberty assumes the character of a shield. The autonomy of the individual is protected from encroachment by the state. This formulation of political rights reflects the notion that the state shall not be permitted to encroach upon a protected sphere reserved for individual decisions and choices. What the state is prevented from doing is couched in a negative sense. Civil and political rights operate as restraints on state action. They postulate a restriction on the state. Isaiah Berlin formulates the negative conception of liberty thus: “I am … free to the degree to which no man or body of man interferes with my activity. Political liberty is simply the area within which a man can act unobstructed by others.”290
166 Individual freedom, in this conception, imposes a duty of restraint on the state. Modern ideas of neo liberalism have funnelled this notion. Neoliberalism postulates that the increasing presence of the state is a threat to individual autonomy. A free market economy with minimum state control, in this view, is regarded as integral to protecting individual rights and freedoms. FA Hayek construes the content of liberty as meaning the absence of obstacles. Resultantly, this notion of liberty regards the role of the state in a narrow jurisprudential frame. Attempts by the state to pursue social justice or to use its authority for redistribution of wealth would in this conception not be a legitimate use of state power.291
167 The notion that liberty only consists of freedom from restraint does not complete the universe of its discourse. Broader notions of liberty are cognizant of the fact that individuals must be enabled to pursue their capacities to the fullest degree. Social and economic discrimination poses real barriers to access education, resources and the means to a dignified life. This approach to understanding the content of freedom construes the ability to lead a dignified existence as essential to the conception of liberty and freedom. The integral relationship between removal of socio-economic inequality and freedom has been eloquently set out by Amartya Sen in “Development as Freedom”292:
“Development requires the removal of major sources of unfreedom: poverty as well as tyranny, poor economic opportunities as well as systematic social deprivation, neglect of public facilities as well as intolerance or overactivity of repressive states.
Despite unprecedented increases in overall opulence, the contemporary world denies elementary freedoms to vast numbers – perhaps even the majority-of people. Sometimes the lack of substantive freedoms relates directly to economic poverty, which robs people of the freedom to satisfy hunger, or to achieve sufficient nutrition, or to obtain remedies for treatable illnesses, or the opportunity to be adequately clothed or sheltered, or to enjoy clean water or sanitary facilities. In other cases, the unfreedom links closely to the lack of public facilities and social care, such as the absence of epidemiological programs, or of organized arrangements for health care or educational facilities, or of effective institutions for the maintenance of local peace and order. In still other cases, the violation of freedom results directly from a denial of political and civil liberties by authoritarian regimes and from imposed restrictions on the freedom to participate in the social, political and economic life of the community.” In Sen’s analysis, human development is influenced by economic opportunities, political liberties, social powers, and the enabling conditions of good health, basic education, and the encouragement and cultivation of initiatives.
Taking it further, Sen has recognized an important co-relation in terms of the non-availability of basic economic conditions: “Economic unfreedom, in the form of extreme poverty, can make a person a helpless prey in the violation of other kinds of freedom… Economic unfreedom can breed social unfreedom, just as social or political unfreedom can also foster economic unfreedom.”293
168 The notion of freedom as an agency has been developed by Sen as part of the ‘capability theory’. The necessary consequence of focusing upon major sources of unfreedom, in a social and economic perspective, is that the removal of these restraints is essential to the realization of freedom. If true freedom is to be achieved through the removal of conditions which cause social and economic deprivation, the role of the state is not confined to an absence of restraint. On the contrary, the state has a positive obligation to enhance individual capabilities. Martha Nussbaum294 argues that realising freedom requires the state to discharge positive duties. Nussbaum expresses a threshold level of capability below which true human functioning is not available. Freedom is seen in terms of human development and is the process by which individuals can rise above capability thresholds. In the realisation of basic rights, the state is subject to positive duties to further the fulfilment of freedom.
169 The broader conception of freedom and liberty which emerges from the writings of Sen and Nussbaum has direct consequences upon how we view civil and political rights and socio-economic rights. The distinction between the two sets of rights becomes illusory once civil and political rights are regarded as comprehending within their sweep a corresponding duty to take such measures as would achieve true freedom. Henry Shue295 suggests that rights give rise to corresponding duties. These duties include: (i) a duty to respect; (ii) a duty to protect; and (iii) a duty to fulfil.
Duties of respect embody a restraint on affecting the rights of others. Duties to protect mandate that the state must restrain others in the same manner as it restrains itself. The state’s duty of non-interference extends to private individuals. The duty to fulfil connotes aiding the deprived in the realisation of rights. This imposes a corresponding duty to create the conditions which will facilitate the realisation of the right.
The right which is protected for the individual will also signify an expectation that the state must create institutions enabling the exercise of facilitative measures or programmes of action, of an affirmative nature. The state has affirmative obligations to fulfil in the realisation of rights. These positive duties of the state are readily apparent in the context of welfare entitlements when the state must adopt affirmative steps to alleviate poverty and the major sources of economic and social nonfreedom. But the thesis of Nussbaum and Shue have an important role for the state to discharge in ensuring the fulfilment of political rights as well. In a highly networked and technology reliant world, individual liberty requires the state to take positive steps to protect individual rights.
Data protection and individual privacy mandate that the state put in place a positive regime which recognises, respects and protects the individual from predatory market places. The state has a positive duty to create an autonomous regulatory framework in which the individual has access to remedies both against state and nonstate actors, both of whom pose grave dangers of assault on the individual as an autonomous entity. Failure to discharge that duty is a failure of the state to respect, protect and fulfil rights. Dr Ambedkar’s prophetic final address to the Constituent Assembly elaborates that vision: “On the social plane, we have in India a society based on the principle of graded inequality with elevation for some and degradation for others. On the economic plane, we have a society in which there are some who have immense wealth as against many who live in abject poverty.
On the 26th of PART G 233 January 1950, we are going to enter into a life of contradictions. In politics we will have equality and in social and economic life we will have inequality…How long shall we continue to live this life of contradictions? How long shall we continue to deny equality in our social and economic life? If we continue to deny it for long, we will do so only by putting our political democracy in peril. We must remove this contradiction at the earliest possible moment or else those who suffer from inequality will blow up the structure of political democracy which [this] Assembly has [so] laboriously built up.”296
The pursuit of social welfare and security is a central aspect of development. The State, in Ambedkar’s vision, would be the main instrumentality in the debate on development, which has to revolve around the social, economic and political spheres and would be guided by the values of the Constitution. 170 Social opportunities are the facilities and “arrangements that society makes” for education, healthcare and nutrition, which “influence the individual’s substantive freedom to live better”.297 Social security measures include programmes which intend to promote the welfare of the population through assistance measures guaranteeing access to sufficient resources.
The social security framework is not only important for individual development, but also for effective participation in economic and political activities. Social security programmes flow from ‘economic and social rights’- also called as “welfare rights” 298 or second generation rights. These rights, recognized for the first time under the Universal Declaration on Human Rights, 1948 include a large list of freedoms and claims under its “protective umbrella”.
They include not only basic political rights, but the right to work, the right to education, protection against unemployment and poverty, the right to join trade unions and even the right to just and favourable remuneration.299 Social security programmes as an instrument for the removal of global poverty and other economic and social deprivations are at the centre stage in the global discourse. Article 22 of the Universal Declaration of Human Rights expressly recognises that every member of society is entitled to the right to social security and to the realisation of economic, social and cultural rights. Those rights are stated to be indispensable for dignity and to the free development of personality.
The realisation of these rights has to be facilitated both through national efforts and international co-operation and in accordance with the organisation and the resources of each state. Article 22 stipulates that: “Article 22 Everyone, as a member of society, has the right to social security and is entitled to realization, through national effort and international co-operation and in accordance with the organization and resources of each State, of the economic, social and cultural rights indispensable for his dignity and the free development of his personality.” In a similar vein, Article 23 comprehends a conglomeration of rights including
(i) the right to work;
(ii) free choice of employment;
(iii) just and favourable conditions of work;
(iv) protection against unemployment;
(v) equal pay for equal work without any discrimination;
(vi) just and favourable remuneration for work; and
(vii) formation and membership of trade unions. Article 23 construes these rights as a means of ensuring both for the individual and the family, an “existence worthy of human dignity” supplemented if necessary “by other means of social protection”. India having adopted the UDHR, its principles can legitimately animate our constitutional conversations. Both Articles 22 and 23 are significant in recognising economic rights and entitlements in matters of work and social security. Both the articles recognise the intrinsic relationship between human dignity and the realisation of economic rights. Measures of social protection are integral to the realisation of economic freedom and to fulfil the aspiration for human dignity.
171 India adopted and ratified the Covenant on Civil and Political Rights as well as the Covenant on Economic, Social and Cultural Rights. India acceded to the Covenant on Economic, Social and Cultural Rights on 10 April 1979. According to the Preamble, the states who are parties to the Covenant have recognized that: “the ideal of free human beings enjoying freedom from fear and want can only be achieved if conditions are created whereby everyone may enjoy his economic, social and cultural rights, as well as his civil and political rights.” Freedom is thus defined in terms of the absence of fear and want. Moreover, freedom consists in the enjoyment of a conglomeration of rights: economic, social and cultural as well as civil and political rights. There is in other words no dichotomy between the two sets of rights. Article 11 of the Covenant on Economic, Social and Cultural Rights imposes positive obligations on the covenanting states:
“Article 11.
1. The States Parties to the present Covenant recognize the right of everyone to an adequate standard of living for himself and his family, including adequate food, clothing and housing, and to the continuous improvement of living conditions. The States Parties will take appropriate steps to ensure the realization of this right, recognizing to this effect the essential importance of international cooperation based on free consent.
2. The States Parties to the present Covenant, recognizing the fundamental right of everyone to be free from hunger, shall take, individually and through international cooperation, the measures, including specific programmes, which are needed:
(a) To improve methods of production, conservation and distribution of food by making full use of technical and scientific knowledge, by disseminating knowledge of the principles of nutrition and by developing or reforming agrarian systems in such a way as to achieve the most efficient development and utilization of natural resources;
(a) Taking into account the problems of both food-importing the food-exporting countries, to ensure an equitable distribution of world food supplies in relation to need.”
172 The Masstricht Guidelines on Violations of Economic, Social and Cultural Rights (January 1997) stipulate that: “It is now undisputed that all human rights are indivisible, interdependent, interrelated and of equal importance for human dignity. Therefore, states are as responsible for violations of economic, social and cultural rights as they are for violations of civil and political rights.” The Guidelines also stipulate that like civil and political rights, economic, social and cultural rights impose three different types of obligations on states : the obligation to respect, protect and fulfil. The guidelines recognize that violations of economic, social and cultural rights can occur through acts of commission and omission on the part of states.
The omission or failure of states to take measures emanating from their legal obligations may result in such violations. Among them is the failure to enforce legislation or to put into effect policies designed to implement the provisions of the Covenant. In similar terms, the Limburg Principles on the Implementation of the International Covenant on Economic, Social and Cultural Rights cast affirmative duties on states to take immediate steps towards realizing the rights contained in the Covenant. Clauses 16, 21 and 27 of the guidelines are thus:
“16. All States parties have an obligation to begin immediately to take steps towards full realization of the rights contained in the Covenant.
21. The obligation “to achieve progressively the full realization of the rights” requires States parties to move as expeditiously as possible towards the realization of the rights. Under no circumstances shall this be interpreted as implying for States the right to defer indefinitely efforts to ensure full realization. On the contrary all States parties have the obligation to begin immediately to take steps to fulfil their obligations under the Covenant.
27. In determining whether adequate measures have been taken for the realization of the rights recognized in the Covenant attention shall be paid to equitable and effective use of and access to the available resources.” The office of the UN High Commissioner for Human Rights notified General Comment No. 3, which was adopted at the fifth session of the Committee on PART G 238 Economic, Social and Cultural Rights on 14 December 1990. The Comment states: “…while the full realization of the relevant rights may be achieved progressively, steps towards that goal must be taken within a reasonably short time after the Covenant’s entry into force for the States concerned.
Such steps should be deliberate, concrete and targeted as clearly as possible towards meeting the obligations recognized in the Covenant.” Similarly, General Comment No. 12 on the right to adequate food was adopted at the twentieth session of the Committee on Economic, Social and Cultural Rights on 12 May 1999. It states : “The Committee observes that while the problems of hunger and malnutrition are often particularly acute in developing countries, malnutrition, under-nutrition and other problems which relate to the right to adequate food and the right to freedom from hunger also exist in some of the most economically developed countries, Fundamentally, the roots of the problem of hunger and malnutrition are not lack of food but lack of access to available food, inter alia because of poverty, by large segments of the world’s population.” The emphasis on the lack of access to available food is significant to the present discourse. It indicates that access to food requires institutional mechanisms to ensure that the available resources reach the beneficiaries for whom they are intended.
173 Section 2(1)(f) of the Protection of Human Rights Act 1993 specifically adverts to the Covenant on Economic, Social and Cultural Rights: “2.(1)(f) “International Covenants” means the International Covenant on Civil and Political Rights and the International Covenant on Economic, Social and Cultural Rights adopted by the General Assembly of the United Nations on 16th December, 1996 and such other Covenant or Convention PART G 239 adopted by the General Assembly of the United Nations as the Central Government may, by notification, specify;” Under Section 12(f), the National Human Rights Commission has been entrusted with the function of studying treaties and other international instruments of human rights and to make recommendations for their effective implementation. Parliament has statutorily incorporated India’s obligations at international law under the above covenants as a part of the national effort to realise fundamental human freedoms. Achieving economic freedom is integral to that mission.
In his classic work “The Idea of Justice”, Amartya Sen has observed in this regard: “The inclusion of second-generation rights makes it possible to integrate ethical issues underlying general ideas of global development with the demands of deliberative democracy, both of which connect with human rights and quite often with an understanding of the importance of advancing human capabilities.”300 174 Social security thus acts as an underpinning link with development. There is also a two-way relationship between development and social security (expansion of human capability). Dreze and Sen have dealt with this relationship in their following observation: “Growth generates resources with which public and private efforts can be systematically mobilized to expand education, health care, nutrition, social facilities, and other essentials of fuller and freer human life for all.
And the expansion of human capability, in turn, allows a faster expansion of resources and production, on which economic growth ultimately depends… Well-functioning public services, especially (but not only) in fields such as education and health, are also critical in fostering participatory growth as well as in ensuring that growth leads to rapid improvements in people’s living conditions.
“301 The authors have further observed that apart from education and healthcare, India faces larger issues of accountability in the “public sector as a whole”.302 The lack of progress in public services acts as a huge barrier to improve the quality of life of people.303 It has been observed: “The relative weakness of Indian social policies on school education, basic healthcare, child nutrition, essential land reform and gender equity reflects deficiencies of politically engaged public reasoning and social pressure, not just inadequacies in the official thinking of the government.”304 The future of Indian democracy therefore depends on how it engages itself with the issues of accountability in transfer of basic human facilities to the common man.
175 The State has a legitimate aim to ensure that its citizens receive basic human facilities. In order to witness development, the huge amount of expenditure that the State incurs in providing subsidies and benefits to the common citizens, must be accompanied by accountability and transparency. Legislative and institutional changes are often capable of creating an atmosphere of transparency and accountability. The most visible example of a legislative enactment which brought institutional changes is the Right to Information Act, 2005. Commentators have often highlighted the importance of this legislation by deliberating upon how it has been successful at “curbing corruption and restoring accountability in public life”305. According to the State, though the Aadhaar programme is not in itself a social security programme, the institutional framework established by the Act, seeks to act, in a way, as an extension of social security programmes. The State has a legitimate concern to check that the welfare benefits which it marks for those, who are entitled, reach them without diversion.
The Aadhaar programme, it is argued, acts as an instrument for the realization of the benefits arising out of the social security programmes. The Aadhaar programme, it was further contended, fulfils the State’s concern that its resources are utilised fully for human development. It has been contended by the Respondents that since the establishment of the UIDAI in 2009, its basic mandate is to provide a unique identity number to residents. The number would subserve two purposes. First, it would serve as a proof of identity. Second, it would be used for the purpose of identifying beneficiaries for the transfer of social welfare benefits, provided by the state. The rationale for establishing a method of identification is to ensure that the benefits provided by social welfare programmes formulated by the State reach the beneficiaries for whom they are intended. As a policy intervention, a unique measure of identification is intended, it has been argued, to secure financial inclusion.
A significant hurdle in the success of social welfare programmes is that benefits do not reach the targeted population. The reason for this may have something to do intrinsically with the condition of the individuals as much as with their larger socio-economic circumstances. Migrant labour and labour in the unorganised sector lacks fixity of abode. The nature of their work renders their lives peripatetic. Nomadic tribes, particularly in inaccessible areas, may not have fixed homes. In many cases, traditional occupations require individuals to move from place to place, dependent on seasonal changes. Then again, groups of citizens including women, children and the differently abled may face significant difficulties in accessing benefits under publicly designed social welfare programmes as a result of factors such as gender, age and disability.
176 Unequal access to welfare benefits provided by the State becomes a significant source of deprivation resulting in a denial of the means to sustain life and livelihood. Before the adoption of Aadhaar based-identity, there were multiple platforms for identification of residents. They created a situation where those with no identity had no access to the means of sustaining a dignified life. Equally significant, as a policy intervention, was the issue of capture. While on the one hand, large swathes of the population had no access to welfare assistance, benefits could be captured by persons not entitled to them either by the assertion of fake or multiple identities. Setting up a fake identity enables an individual to pass off as another and to secure a benefit to which that individual is not entitled. Fake identities compound the problem of capture by allowing individuals to receive multiple benefits through shell identities. Policy makers were confronted with the serious problems posed by fake and multiple identities since they imposed a burden on the exchequer while at the same time diluting the efficacy of state designed social welfare measures.
The burden on the exchequer is illustrated by situations where persons who are not entitled to benefits secure them in the guise of being persons entitled to them. When imposters secure benefits which are not meant for them, they deprive in the process, persons who are genuinely entitled to benefits. The class of beneficiaries of social welfare programmes is, so to speak, adulterated by the capture of benefits by those not entitled to them. This raises serious concerns of the deprivation of human rights. The capture of benefits has the consequence of depriving those to whom these benefits should legitimately flow, of the measures designed by the state to protect its populace from human want and need. The resources deployed by the state are from its public revenues. When designing a unique measure of identification, the state must be guided by the necessity of ensuring financial inclusion and of protecting against financial exclusion.
Every citizen who is eligible for social welfare benefits should obtain them. No person who is entitled should be excluded. Individuals who do not qualify for social welfare benefits should not capture them by passing off as individuals entitled. Enforcing and implementing a robust platform for identification of beneficiaries must ensure that social welfare benefits reach the hands of those who fulfil the conditions of eligibility and are not captured by rent-seeking behaviour of those to whom social welfare benefits are not designed. This constitutes a PART G 244 legitimate object of state policy. Reaching out to the targeted population is a valid constitutional purpose. Social welfare measures are an intrinsic part of state policy designed to facilitate dignified conditions of existence to the marginalised, especially those who live below the poverty line. Identification of beneficiaries is crucial to the fulfilment of social welfare programmes.
177 These concerns form the basis of the Aadhaar (Targeted Delivery of Financial and other Subsidies, Benefits and Services) Act, 2016. As its Statement of Objects and Reasons explains: “The correct identification of targeted beneficiaries for delivery of various subsides, benefits, services, grants, wages and other social benefits schemes which are funded from the Consolidated Fund of India has become a challenge for the Government. The failure to establish identity of an individual has proved to be a major hindrance for successful implementation of these programmes.
This has been a grave concern for certain categories of persons, such as women, children, senior citizens, persons with disabilities, migrant unskilled and unorganised workers, and nomadic tribes. In the absence of a credible system to authenticate identity of beneficiaries, it is difficult to ensure that the subsidies, benefits and services reach to intended beneficiaries.” The Statement of Objects and Reasons indicates that the enactment is designed to ensure “the effective, secure and accurate delivery of benefits, subsidies and services from the Consolidated Fund of India to targeted beneficiaries”. The architecture of the law contemplates regulating the following aspects:
“(a) issue of Aadhaar numbers to individuals on providing .. demographic and biometric information to the Unique Identification Authority of India;
(b) requiring, Aadhaar numbers for identifying an individual for delivery of benefits, subsidies, and PART G 245 services (where) the expenditure is incurred from or the receipt therefrom forms part of the Consolidated Fund of India;
(c) authentication of the Aadhaar number of an Aadhaar number holder in relation to his demographic and biometric information;
(d) establishment of the Unique Identification Authority of India… to perform functions in pursuance of the objectives above;
(e) maintenance and updating the information of individuals in the Central Identities Data Repository in such manner as may be specified by regulations;
(f) measures pertaining to security, privacy and confidentiality of information in possession or control of the Authority including information stored in the Central Identities Data Repository; and
(g) offences and penalties for contravention of relevant statutory provisions.”
The Preamble to the enactment indicates that Parliament designed the legislation as an instrument of good governance, to secure an “efficient, transparent and targeted delivery of subsidies, benefits and services” for which the expenditure is incurred from the Consolidated Fund to resident individuals.
178 The Aadhaar platform is not a social welfare benefit in itself. Essentially, what it seeks to achieve is to provide a unique identity to every resident. This identity, in the form of an Aadhaar number, is obtained upon the submission of demographic and biometric information in the course of enrolment. The legislative design envisages that the identity of the individual is verified through the process of authentication by which the biometric data stored in the central repository is matched with the biometric information submitted for authentication. Aadhaar is a platform for verification of identity based principally on biometric information.
In facilitating the process of establishing the identity of the individual who seeks social welfare benefits envisaged in Section 7, Aadhaar has an instrumental role. It is instrumental in the sense that as a measure of state policy, it seeks to bring about financial inclusion by providing a means of identification to every segment of the population including those who may not have been within the coverage of traditional markers of identity. As an instrument for verifying identity, Aadhaar seeks to ensure that social welfare benefits are obtained by persons eligible to do so and are not captured by the ineligible. Relying on an asserted reliability of biometric markers, the Aadhaar platform attempts to eliminate, or at least to curb rent-seeking behaviour.
The rationale underlying Section 7 is the targeted delivery of services, benefits and subsidies which are funded from the Consolidated Fund of India. In the seven decades since Independence, the Union Government has put into place social welfare measures including the public distribution system, free education, scholarships, mid-day meals and LPG subsidies to ameliorate the conditions of existence of the poor and marginalised. There is a state interest in ensuring that the welfare benefits which the state provides reach those for whom they are intended.
G.3 Identity and Identification
179 Identity is inseparable from the human personality. An identity is a statement of who an individual is. Our identities define who we are. They express what we would wish the world to know us as. The human personality is, at a certain level, all about identity, for it is through the assertion of identity that each individual seeks to preserve the core of his or her humanity. An identity is the persona which an individual puts forth in a multitude of relationships. The significance of our identity lies in our ability to express the core of our beings. When the Constitution protects our right to be and to be what we are, it creates a space where the individual is immune from interference.
By recognizing our liberty as autonomous persons, the Constitution recognizes our ability to preserve and shape our identities in interactions with others. Identity may be, but is not always based upon immutable characteristics that are defined at birth. What is immutable may not be or, at any rate, is not generally understood as being capable of change. But even here, the immutability of our features is relative to our own existence and is capable of being shaped by the social milieu in which human beings lead their lives. Features about our biological being which are defined at birth are, after all, not as constraining upon our identities as is often assumed to be the case.
That is because these immutable features are also constantly engaged with our social and cultural environment. They shape and are influenced by that environment.
180 There is a distinction between identity and identification. Identification is a matter of proof- of establishing that a person is actually, the individual who claims a right or entitlement. In their daily interactions, individuals have to distinguish themselves from others, whether it be in the course of employment, travel, civil union, location, community perspectives, revenue obligations or access to benefits. Identification is a proof of identity or evidence of identity. Identification is mandatory in numerous activities of day to day life: a passport is necessary for international travel, a voter ID is required for exercising electoral rights, a driving license is necessary to ply a vehicle and an arms license is needed to possess a fire arm. The holder of a policy of medical insurance will have a card depicting his or her identity which is a proof of holding a valid policy for availing medical benefits.
181 Under international law, recognition of identity is an obligation of a nation state. Article 6 of the Universal Declaration of Human Rights provides that “everyone has the right to recognition everywhere as a person before the law”. Article 16 of the International Covenant on Civil and Political Rights is in similar terms. Article 8 of the UN Convention on the Rights of the Child mandates that State parties undertake to respect the right of the child to PART G 249 preserve his or her identity, including nationality, name and family relations as recognized by law without unlawful interference. The importance of identity is recognized by Article 3 of the American Convention on Human Rights. The Inter-American Juridical Committee (IAJC) of the Organisation of American States (OAS) has in fact provided that:
“12. The right to identity is consubstantial to the attributes and human dignity. Consequently it is an enforceable basic human right erga omnes as an expression of a collective interest of the overall international community that does not admit derogation or suspension in cases provided in the American Convention on Human Rights. … 15. The Committee considers that the right to identity is, among its most relevant implications and scope, to constitute an autonomous right that is based on the regulations of international law and those that derive from the actual cultural elements considered in the domestic legal systems of the States, in order therefore to satisfy the specificity of the individual, with his or her rights that are unique, singular and identifiable.
“306 182 In National Legal Services Authority v Union of India307, this Court held that gender identity is fundamental to and an essential component for the enjoyment of civil rights by the transgender community. Self-determination of identity has been held to be an essential facet of Article 21. In the view of this Court: “74. The recognition of one’s gender identity lies at the heart of the fundamental right to dignity. Gender, as already indicated, constitutes the core of one’s sense of being as well as an integral part of a person’s identity. Legal recognition of gender identity is, therefore, part of right to dignity and freedom guaranteed under our Constitution.
75. Article 21, as already indicated, guarantees the protection of “personal autonomy” of an individual. In Anuj Garg v. Hotel Association of India33 (SCC p. 15, paras 34-35), this Court held that personal autonomy includes both the negative right of not to be subject to interference by others and the positive right of individuals to make decisions about their life, to express themselves and to choose which activities to take part in. Self-determination of gender is an integral part of personal autonomy and self-expression and falls within the realm of personal liberty guaranteed under Article 21 of the Constitution of India.” Identity assumes a complex character in a networked society. Shah adopts the following definition of a networked society308: “a network society is a society where the key social structures and activities are organized around electronically processed information networks.
So it’s not just about networks or social networks, because social networks have been very old forms of social organization. It’s about social networks which process and manage information and are using microelectronic based technologies”309. 183 In a networked society, an individual is a data subject and a quantified self. The individual is a data subject since his or her data is stored in a database. Shah notes that there is an ambivalence about whether the data subject is the individual whose identity becomes the basis of validating the data or whether the data subject is the identity of the individual as it gets constructed through data sets.
The individual becomes a quantified self where data which is distributed across various systems is “curated” to form a comprehensive profile of an individual.
184 The Aadhaar project was intended to allow a unique identity to enable individuals to “navigate through disconnected and often hostile governmental database systems”.
Shah notes that ever since 2009, the terms ‘identity’ and ‘identification’ were used as part of the Aadhaar project inter-changeably, introducing “a curious conflation and interoperability”310 between these notions. ‘Identification’ is the ability of a network device to identify an individual by scanning unique data sets, from personal information to biometric details such as finger print and iris scan, which would be stored in a massive centralized database. UIDAI posited that identification took place through its yes/no mechanism by which the centralised database would provide a response to whether the biometric details submitted for authentication match those in the repository.
Technologically, at this level, Aadhaar was to be a means of identification. Yet at another level, the Aadhaar project also offered itself as providing a documentary identity to persons who may not have possessed one at all. Shah, in the course of his article, has this to state about the conflation between identity and identification in the Aadhaar project: “This ambiguity and conflation cannot merely be attributed to a semantic slip of the keyboard, but to a much larger phenomenon which points to the construction of a new notion of the individual, through big data streams and measures of self-quantification.
It offers us a techno-social framework where the machine function of identification is wedded to the human expression of identity, and thus offers an inroad into looking at what happens when our identities are mediated, mitigated, facilitated, and contained by the ways in which the networked technologies of authentication and verification operate. It is a crucial shift where the identity of a person is ontologically defined through the logics and logistics of networked computation that form the Aadhaar project.
This is why the Aadhaar enrolment system, for instance, does not check the veracity of the information that the individual gives it. For the enrolment, the individual needs no proof to substantiate or validate the information provided. The name, the address, the description, etc. are empty signifiers and it is possible for anybody to assume any identity as long as they give the inviolable data of biometric recognition. Thus, the identity of the person being enrolled and registered is almost insignificant and has value only in how it would now always identify the individual through the credentials or information provided. The Aadhaar network governance system is concerned only with the identifiers rather than the narrative, iterative, forms of identity and expression, and this is where we begin examining the ways in which identity is shaped, understood, and used to construct the notion of an individual in computation systems.”311
185 Identity includes the right to determine the forms through which identity is expressed and the right not to be identified. That concept is now “flipped” so that identification through identifiers becomes the only form of identity in the time of database governance. This involves a radical transformation in the position of the individual. The submission which has been urged on behalf of the petitioners is that an individual entitled to the protection of the freedoms and liberties guaranteed by Part III of the Constitution must have the ability to assert a choice of the means of identification for proving identity. Requiring an individual to prove identity on the basis of one mode alone will, it is submitted, violate the right of self-determination and free choice.
186 The Aadhaar (Enrolment and Update) Regulations, 2016 stipulate in Regulation 4, the demographic information which is required for enrolment. Regulation 4 is in the following terms:
“4. Demographic information required for enrolment.-
(1) The following demographic information shall be collected from all individuals undergoing enrolment (other than children below five years of age):
(i) Name;
(ii) Date of Birth;
(iii) Gender;
(iv) Residential Address.
(2) The following demographic information may also additionally be collected during enrolment, at the option of the individual undergoing enrolment:
(i) Mobile number;
(ii) Email address.
(3) In case of Introducer-based enrolment, the following additional information shall be collected:
(i) Introducer name;
(ii) Introducer’s Aadhaar number.
(4) In case of Head of Family based enrolment, the following additional information shall be collected:
(i) Name of Head of Family;
(ii) Relationship;
(iii) Head of Family’s Aadhaar number;
(iv) One modality of biometric information of the Head of Family.
(5) The standards of the above demographic information shall be as may be specified by the Authority for this purpose.
(6) The demographic information shall not include race, religion, caste, tribe, ethnicity, language, record of entitlement, income or medical history of the resident.” Regulation 9 postulates that at the time of enrolment, the enrolling agency shall inform the individual who is undergoing enrolment of
(i) the manner in which the information shall be used;
(ii) the nature of recipients with whom the information is intended to be shared during authentication; and
(iii) the existence of a right to access information. Under Regulation 10, a resident seeking enrolment has to submit an application for enrolment together with copies of supporting documents for proof of identity, address and date of birth. Schedule II indicates a list of supporting documents which are accepted for verification of identity, address and date of birth. If a resident does not possess the supporting documents, enrolment is contemplated through an introducer or a Head of Family. Schedule II contains as many as eighteen documents which are accepted towards proof of identity and thirty three documents as proof of address. The Aadhaar Act, it has been contended, allows the resident to identify herself through any of the stipulated documents for the purpose of availing an Aadhaar number.
The Aadhaar number can be availed of to secure a subsidy, benefit or service under Section 7, the expenditure of which is drawn from the Consolidated Fund of India. Article 266 of the Constitution provides as follows:
“266. Consolidated Funds and public accounts of India and of the States PART G 255 (1) Subject to the provisions of Article 267 and to the provisions of this Chapter with respect to the assignment of the whole or part of the net proceeds of certain taxes and duties to States, all revenues received by the Government of India, all loans raised by that Government by the issue of treasury bills, loans or ways and means advances and all moneys received by that Government in repayment of loans shall form one consolidated fund to be entitled the “Consolidated Fund of India”, and all revenues received by the Government of a State, all loans raised by that Government by the issue of treasury bills, loans or ways and means advances and all moneys received by that Government in repayment of loans shall form one consolidated fund to be entitled “the Consolidated Fund of the State”.
(2) All other public moneys received by or on behalf of the Government of India or the Government of a State shall be credited to the public account of India or the public account of the State, as the case may be
(3) No moneys out of the Consolidated Fund of India or the Consolidated Fund of a State shall be appropriated except in accordance with law and for the purposes and in the manner provided in this Constitution.”
187 The Union Government is the custodian of the Consolidated Fund under Article 266. All revenues received by the government form part of the Consolidated Fund. No part of its proceeds can be “appropriated except in accordance with law and for the purpose and in the manner” which is provided by the Constitution. As the custodian of the fund, the Union Government, it has been submitted by the respondents, had the Aadhaar Act enacted through Parliament. The Act places a restriction on the right of the individual to utilize any other identification save and except for the Aadhaar number, for the purpose of availing of a subsidy, benefit or service that involves an expenditure from the Consolidated Fund.
The purpose of making an Aadhaar number mandatory for the delivery of benefits, services and subsidies funded from the Consolidated Fund is to confirm the identity of the individual to whom the benefit is being transferred. This was in order to ensure that the benefits under social welfare programmes funded by the Consolidated Fund reach the hands of targeted beneficiaries. The Union Government which expends huge sums of money in its welfare schemes was apprised of the fact that money which was meant for the beneficiaries was being siphoned off through ghosts and duplicates.
As a result, genuine beneficiaries would be deprived of their basic rights. Cornering of benefits by the creation of bogus identities seriously impacted upon social welfare measures adopted by the Union Government as an instrument of fostering social and economic development. It was to deal with this evil that the Aadhaar project assumed a statutory character in 2016. Through the provisions of the law, Parliament intended that Aadhaar should become an effective instrument of de-duplication. This is premised on the view of the legislating body that the use of biometrics would render it difficult, if not impossible, to obtain fake identities. Aadhaar, in other words, was adopted as a matter of legislative policy to curb the evil of shell companies and ghost identities.
Where the State expends large sums on social welfare projects, it has a legitimate interest in ensuring that the resources which it deploys reach the hands of those for whom they are meant. Thus, there are two important facets of the Aadhaar regime which must be noticed. The first is that under Section 3, it is a voluntary option of the individual to choose Aadhaar as a form of identification. However, if the individual seeks a subsidy, benefit or service for which the expenditure is incurred from the Consolidated Fund of India, Aadhaar becomes a mandatory requirement. The second important feature is the requirement of informed consent when the individual parts with identity information.
The mandate of Section 7 must be understood from the perspective of the obligation imposed on the State to ensure effective and efficient utilization of public resources. Article 266 reinforces that mandate in its stipulation that all monies out of the Consolidated Fund of India can only be appropriated in accordance with law, for the purpose of and in the manner provided by the Constitution. The State is a trustee of public resources.
The adoption of Aadhaar is in fulfilment of the doctrine of public trust. The state is under a bounden obligation to ensure that its revenues which are placed in the Consolidated Fund are appropriated in accordance with law and are not diverted for extraneous purposes. These principles have been elucidated in the decisions of this Court in Natural Resources Allocation, In Re, Special Reference No.1 of 2012312, Centre for Public Interest Litigation v Union of India313, Reliance Telecom Limited v Union of India314. The mandate of Section 7 is founded on a legitimate state interest. The state has a vital interest in ensuring that public revenues are duly accounted, that the Consolidated Fund is utilized for purposes authorized by law; that funds for development reach genuine beneficiaries and that scarce public resources meant for those at the foot of the socio-economic ladder are not mis-utilized by rent-seeking behavior.
H Proportionality
188 The petitioners have challenged the constitutional validity of the Aadhaar project and the Aadhaar Act on various grounds including the violation of the fundamental rights of citizens including the right to privacy and dignity. The respondents, in defense, have argued that Aadhaar is an enabler of identity and empowers citizens to realise various facets of the right to life, such as the right to food and livelihood. 189 The learned Attorney General has argued that the use and authentication of the Aadhaar number is a necessary and proportionate measure to ensure targeted delivery of financial benefits and services and to prevent ‘leakages’.
He submits that the Aadhaar scheme satisfies the test of proportionality: it has a rational nexus with the goal that it seeks to achieve, and since welfare benefits enhance the right to live with dignity, the latter will prevail over the right to privacy. Mr Rakesh Dwivedi, learned Senior Counsel has argued that the “least intrusive test” is not accepted in Indian jurisprudence. He submits that even if the test were to be accepted, the exercise of determining whether a measure is the least intrusive is a technical issue for which the Court lacks the requisite expertise. He states that this exercise “cannot be undertaken in the courts with the assistance of lawyers who equally have no expertise in the field” and that “such an exercise involves research, study by the experts and courts cannot substitute the same”.
Mr Gopal Sankaranarayanan, learned Counsel, submits that the means adopted “at the moment” are no more than is necessary for ensuring that the “avowed objects” are served, and that they balance individual interests (fundamental rights) with societal interests (directive principles). He further submits that the fact there are various limitations in place ensure that “some balance” is achieved between the breach of privacy and the object sought to be achieved. This Court must now perform the delicate task of ‘balancing’ these competing interests by subjecting the Aadhaar Act to the proportionality test.
H.I Harmonising conflicting rights
190 In the 2003 edition of his celebrated work, Granville Austin recounts the words of Prime Minister Morarji Desai that freedom and bread are not incompatible, but further adds, ‘Neither could they easily be sought together’.315 As mentioned earlier, Granville Austin had insightfully spoken about how the strands of the Constitution of unity-integrity, democracy and social revolution could come in conflict with one another creating challenges for those who work with the Constitution.316 Some of the questions inherent in the Constitution according to him are “Democracy for whom? Justice for whom? What is Justice? What are the appropriate means of employing the Constitution’s means’ among citizens, between them and their government?”317 It was due to the foresight of the framers of the Constitution that they insisted that neither the strand of social revolution nor the strand of democracy was to be pursued at the expense of the other.318 The ostensible conflict between bread and freedom has also been explored in the works of Professor Upendra Baxi.
In a seminal essay on human rights in 1984 which he calls the “the great gift of classical and contemporary human thought to culture and civilization”319, he discusses the widening sphere of human rights thought and action to new arenas and constituencies as “New rights arise from the womb of the old.”320 He draws on the distinction between basic human needs and human rights and argues that the constant struggle between these two forces is the essence of the difference between the right to be human approach and the human rights approach.321 It is rightly pointed out that a discussion on human rights will always constitute an inherent aspect of the larger debate of development.
He opines that whatever meaning maybe ascribed to the term “development”, it must ensure that people will not be deprived of the right to remain human: “Whatever it may be made to mean, “development” must at least mean this: people will be given the right to be and remain human. Total and continuing destitution and impoverishment exposes people to a loss of their humanity. In no society that takes human rights seriously should there be allowed a state of affairs where human beings become subhuman- that is, when they perforce have to surrender even those sonorously recited “inalienable” rights of man… The expression “human rights” presupposes a level at which biological entities are bestowed with the dignity of being called human.
The bearers of human rights must have an implicit right to be and remain human, allowing them some autonomy of choice in planning survival.”322 Thus, the broader matrix of human rights includes within it the inalienable and fundamental right to always ‘be and remain human’. Professor Upendra Baxi notes that this broader debate between human rights and the ‘right to be human’ is reflective of the bread vs freedom conflict. It is noted that historically, freedom might have been chosen over bread due to the vast enumeration of liberal rights it includes, despite the acute awareness that without bread, freedom of speech and assembly, of association, of conscience and religion, of political participation, symbolic adult suffrage may all be meaningless.323 At the same time, Baxi points out the danger in choosing bread at the cost of freedom, given that historically in the absence of freedom, human beings have been subject to the most egregious indignities: “The provision of “bread” may justify indefinite postponement of the provision of any kind of “freedom”. In the absence of such freedom, even the promised “bread” may not be realized by the masses; indeed, they even lose, in the process, their power to protest at the indignity of regime sponsored starvation.
This, indeed, is a possibility which has materialized more often than not.”324 Baxi concludes that the choice between bread and freedom is a false antithesis. The challenge is not a choice in the abstract between bread and freedom but rather the balancing of the two:325 “But the issues are not really “bread” and/or “freedom” in the abstract, but rather who has how much of each, for how long, at what cost to others, and why. Some people have both “bread” and “freedom”; others have “freedom” but little “bread” or none at all; yet others have half a loaf (which is better than none, surely!) with or without freedom; and still others have a precarious mix where “bread” is assured if certain (not all) freedoms are bartered.
“326 It is the foremost duty of the State to work towards achieving and maintaining a fine balance, taking into account these myriad considerations. The State must always be guided by the knowledge and sense of duty that in a true democracy, the citizens cannot be made to choose between rights and needs, as they are equally entitled to both. As the sentinel of justice and protector of fundamental rights, it is the responsibility of this Court to act as a check and ensure that government action or inaction does not endanger or threaten to disturb the balance that the Constitution seeks to achieve. It is imperative to remember that both ‘bread’ and ‘freedom’ play a vital role in the guaranteeing to our citizens the gamut of human rights and freedoms that make human existence meaningful.
191 While exercising judicial review, courts are often confronted with situations involving conflicts between rights, tensions between individuals arising from the assertion of rights and discord arising out of the assertion of the same right by two or more individuals. Conflicts between rights arise when the assertion of a fundamental human right by an individual impacts upon the exercise of distinct freedoms by others. The freedom of one individual to speak and to express may affect the dignity of another. A person may be aggrieved when the free exercise of the right to speak by someone impinges upon his or her reputation, which is integral to the right to life under Article 21.
A conflict will, in such a situation, arise between a right which is asserted under Article 19(1)(a) by one citizen and the sense of injury of another who claims protection of the right to dignity under Article 21. Conflicts also arise when the exercise of rights is perceived to impact upon the collective identity of another group of persons. Conflicts may arise when an activity or conduct of an individual, in pursuit of a freedom recognised by the Constitution, impinges upon the protection afforded to another individual under the rubric of the same human right. Such a situation involves a conflict arising from a freedom which is relatable to the same constitutional guarantee. Privacy is an assertion of the right to life under Article 21.
The right to a dignified existence is also protected by the same Article. A conflict within Article 21 may involve a situation when two freedoms are asserted as political rights. A conflict may also envisage a situation where an assertion of a political right under the umbrella of the right to life stands in conflict with the assertion of an economic right which is also comprehended by the protection of life under the Constitution. Such conflicts require the court to embark on a process of judicial interpretation. The task is to achieve a sense of balance.
An ideal situation would be one which would preserve the core of the right for both sets of citizens whose entitlements to freedom appear to be in conflict. Realistically, drawing balances is not a simple task. Balances involve sacrifices and the foregoing of entitlements. In making those decisions, a certain degree of value judgment is inevitable. The balance which the court draws may be open to criticism in regard to its value judgment on the relative importance ascribed to the conflicting rights in judicial decision making. In making those fine balances, the court can pursue an objective formulation by relying upon those values which the Constitution puts forth as part of its endeavour for a just society.
Our Constitution has in Part III recognised the importance of political freedom. In Part IV, the Constitution has recognised our social histories of discrimination and prejudice which have led to poverty, deprivation and the absence of a dignified existence to major segments of society. Holding Part III in balance with Part IV is integral to the vision of social and economic justice which the Constitution has sought to achieve consistent with political democracy. Difficult as this area is, a balancing of rights is inevitable, when rights asserted by individuals are in conflict.
192 Several decisions of this Court over the last two decades have sought to bring order to the clash between fundamental rights. In People’s Union for PART H 265 Civil Liberties (PUCL) v Union of India327, this Court was called upon to balance the right to information of voters (requiring the disclosure of the assets of candidates and their spouses at an election) with the right to privacy implicit in Article 21. In drawing the balance, a bench of three Judges of this Court gave primacy to the entitlement of citizens to be informed about the affairs of those who would represent them in electoral democracy. As the Court held:
“121…By calling upon the contesting candidate to disclose the assets and liabilities of his/her spouse, the fundamental right to information of a voter/citizen is thereby promoted. When there is a competition between the right to privacy of an individual and the right to information of the citizens, the former right has to be subordinated to the latter right as it serves the larger public interest. The right to know about the candidate who intends to become a public figure and a representative of the people would not be effective and real if only truncated information of the assets and liabilities is given.”328 The Court held that the provision contained in the Representation of People Act 1951 for a disclosure of assets and liabilities only to the Speaker or to the Chairman of the House did not adequately protect the citizen’s right to information, resulting in a violation of the guarantee of free speech and expression.
193 In Thalappalam Service Cooperative Bank Limited v State of Kerala329, this Court dealt with a conflict between the right to information [(protected by Article 19(1)(a)] and the right to privacy (protected by Article 21). The Court observed:
“61. The right to information and right to privacy are, therefore, not absolute rights, both the rights, one of which falls under Article 19(1)(a) and the other under Article 21 of the Constitution of India, can obviously be regulated, restricted and curtailed in the larger public interest. Absolute or uncontrolled individual rights do not and cannot exist in any modern State. Citizens’ right to get information is statutorily recognised by the RTI Act, but at the same time limitations are also provided in the Act itself, which is discernible from the Preamble and other provisions of the Act.”330 The Court held that the balance between the right to information and the right to privacy is drawn under the Right to Information Act 2005: if the information which is sought is personal and has no relationship with a public activity or interest, a public authority is not legally bound to provide such information.
If the information which is sought is to be made available in the larger public interest, reasons have to be recorded because the person from whom the information is sought has a right to privacy guaranteed by Article 21. Thalappalam considered a conflict arising between two fundamental rights, the right to information protected by Article 19(1)(a) and the right to privacy which is protected by Article 21. 194 More recently, in G Sundarrajan v Union of India331, a two judge Bench considered a challenge to the establishment of a nuclear power plant on the ground that it would violate the right to life guaranteed by Article 21. Noting that there was a need to draw a balance between the assertion of several rights including the protection of the environment, the Court observed that the larger public interest must prevail:
“198. We have to resolve the issue whether the establishment of NPP would have the effect of violating the right to life guaranteed under Article 21 to the persons who are residing in and around Kudankulam or by establishing the NPP, it will uphold the right to life in a larger sense. While balancing the benefit of establishing KKNPP Units 1 to 6, with right to life and property and the protection of environment including marine life, we have to strike a balance, since the production of nuclear energy is of extreme importance for the economic growth of our country, alleviate poverty, generate employment, etc.
While setting up a project of this nature, we have to have an overall view of larger public interest rather than smaller violation of right to life guaranteed under Article 21 of the Constitution.”332 In Subramanian Swamy v Union of India333, the learned Chief Justice, speaking for a Bench of two judges emphasised the need for a sense of balance when the assertion of fundamental rights by two citizens is in conflict: “137…One fundamental right of a person may have to coexist in harmony with the exercise of another fundamental right by others and also with reasonable and valid exercise of power by the State in the light of the directive principles in the interests of social welfare as a whole.
The Court’s duty is to strike a balance between competing claims of different interests.”334 Noting that the “balancing of fundamental rights is a constitutional necessity”, the Court has attempted to harmonise reputation as an intrinsic element of the right to life under Article 21 with criminal defamation as a restriction under Article 19(2).
195 In Asha Ranjan v Chandrakeshwar Prasad335, this Court dealt with a case involving a conflict between the fundamental rights of two individuals within Article 21. There was on the one hand an assertion of the right to life on the part of an individual accused of an offence, who claimed a right to a fair trial, and the protection of the interests of the victim which was also relatable to the same fundamental right under Article 21. In resolving the conflict, the Court gave expression to the need to preserve “paramount collective interests”:
“61…circumstances may emerge that may necessitate for balancing between intra-fundamental rights. It has been distinctly understood that the test that has to be applied while balancing the two fundamental rights or inter fundamental rights, … may be different than the principle to be applied in intra-conflict between the same fundamental right. To elaborate, as in this case, the accused has a fundamental right to have a fair trial under Article 21 of the Constitution. Similarly, the victims who are directly affected and also form a part of the constituent of the collective, have a fundamental right for a fair trial. Thus, there can be two individuals both having legitimacy to claim or assert the right. The factum of legitimacy is a primary consideration. It has to be remembered that no fundamental right is absolute and it can have limitations in certain circumstances.
Thus, permissible limitations are imposed by the State. The said limitations are to be within the bounds of law. However, when there is intraconflict of the right conferred under the same article, like fair trial in this case, the test that is required to be applied, we are disposed to think, it would be “paramount collective interest” or “sustenance of public confidence in the justice dispensation system”.336
196 These decisions indicate that the process of resolving conflicts arising out of the assertion of different fundamental rights and conflicts within the same fundamental right, necessarily involves judicial balancing. In finding a just balance this Court has applied norms such as the ‘paramount public interest’. In seeking to draw the balance between political freedoms and economic freedoms, the Court must preserve the euphony between fundamental rights and directive principles. It is on their co-existence that the edifice of the Constitution is founded. Neither can exist without the other. Democracy rejects the totalitarian option of recognising economic entitlements without political liberty. Economic rights have become justiciable because of the constitutional guarantees founded on freedom and the rule of law. The Constitution is founded on democratic governance and is based on the protection of individual freedom. Freedom comprehends both fundamental political freedoms as well as basic human rights. A just balance between the two is integral to the fulfilment of India’s constitutional commitment to realise human liberty in a social context which is cognizant of the histories of discrimination and prejudice suffered by large segments of our society. Where the question is related to the limiting the right to privacy, Puttaswamy requires the test of proportionality. It has, therefore, to be tested whether the Aadhaar scheme fulfils the test of proportionality.
197 The test of proportionality, which began as an unwritten set of general principles of law, today constitutes the dominant “best practice” judicial standard for resolving disputes that involve either a conflict between two rights claims or between a right and a legitimate government interest.337 It has become a “centrepiece of jurisprudence” across the European continent as well as in common law jurisdictions including the United Kingdom, South Africa and Israel.338 Proportionality is the “defining doctrinal core of a transnational rights-based constitutionalism”339.
It has been raised to the rank of a fundamental constitutional principle,340 and represents a global shift from a culture of authority to a culture of justification.341 Servin argues that jurisprudence on privacy has evolved from the “right to be let alone”, to now being centered around the principle of proportionality.342 198 Subjecting the Aadhaar scheme to the test of proportionality does not mean that the Court is second-guessing the wisdom of the legislature. State action must be subjected to judicial scrutiny to ensure that it passes constitutional muster.
The test of proportionality stipulates that the nature and extent of the State’s interference with the exercise of a right (in this case, the rights to privacy, dignity, choice, and access to basic entitlements) must be proportionate to the goal it seeks to achieve (in this case, purported plugging of welfare leakage and better targeting).
Within the framework of constitutional interpretation, proportionality serves as a test to determine the extent to which fundamental rights can be limited in the face of legislative intervention which purports to further social and public interest aims. Aharon Barak, the former Chief Justice of the Supreme Court of Israel has described the importance of the proportionality test as thus:343 “Examination of the test of proportionality (in the narrow sense) returns us to first principles that are the foundation of our constitutional democracy and the human rights
… Our democracy is characterized by the fact that it imposes limits on the ability to violate human rights; that it is based on the recognition that surrounding the individual there is a wall protecting his right, which cannot be breached even by majority.” In applying the proportionality test, the Court cannot mechanically defer to the State’s assertions. Especially given the intrusive nature of the Aadhaar scheme, such deference to the legislature is inappropriate. The State must discharge its burden by demonstrating that rights-infringing measures were necessary and proportionate to the goal sought to be achieved.
H.2 Proportionality standard in Indian jurisprudence
199 In India, the principle of proportionality has a long jurisprudential history which has been adverted to in a judgment344 of this Court: “On account of a Chapter on Fundamental Rights in Part III of our Constitution right from 1950, Indian Courts did not suffer from the disability similar to the one experienced by English Courts for declaring as unconstitutional legislation on the principle of proportionality or reading them in a manner consistent with the charter of rights.
Ever since 1950, the principle of ‘proportionality’ has indeed been applied vigorously to legislative (and administrative action) in India. While dealing with the validity of legislation infringing fundamental freedoms enumerated in Article 19(1) of the Constitution of India…this court had occasion to consider whether the restrictions imposed by legislation were disproportionate to the situation and were not the least restrictive of the choices.”
(Emphasis supplied)
The early decisions of this Court may not have used the expression “proportionality”. But the manner in which the court explained what would be a permissible restraint on rights indicates the seeds or the core of the proportionality standard. Proportionality has been the core of reasonableness since the 1950s. Chintaman Rao v State of Madhya Pradesh345 concerned a State legislation which empowered the government to prohibit people in certain areas from manufacturing bidis. The object of the law was to ensure the supply of adequate labour for agricultural purposes in areas where bidi manufacturing was an alternative source of employment for persons likely to be engaged in agricultural labour. The Court held that the State need not have prohibited all labourers from engaging in bidi manufacturing throughout the year in order to satisfy the objective. Justice Mahajan, on behalf of a Constitution Bench held:
“6.The phrase “reasonable restriction” connotes that the limitation imposed on a person in enjoyment of the right should not be arbitrary or of an excessive nature, beyond what is required in the interests of the public. The word “reasonable” implies intelligent care and deliberation, that is, the choice of a course which reason dictates. Legislation which arbitrarily or excessively invades the right cannot be said to contain the quality of reasonableness and unless it strikes a proper balance between the freedom guaranteed in article 19(1)(g) and the social control permitted by clause (6) of article 19, it must be held to be wanting in that quality.”
(Emphasis supplied)
200 State of Madras v V G Row346 considered whether the action of the Tamil Nadu government in declaring an association unlawful violated Article 19(1)(c) of the Constitution. Chief Justice Patanjali Sastri, speaking for the Constitution Bench, propounded what has come to be regarded as a classic statement of the principle of proportionality in our law:
“15…the test of reasonableness, wherever prescribed, should be applied to each individual statute impugned, and no abstract standard, or general pattern of reasonableness can be laid down as applicable to all cases. The nature of the right alleged to have been infringed, the underlying purpose of the restrictions imposed, the extent and urgency of the evil sought to be remedied thereby, the disproportion of the imposition, the prevailing conditions at the time, should all enter into the judicial verdict…”
(Emphasis supplied)
The decision of the Constitution Bench in State of Bihar v Kamla Kant Misra347 concerned a challenge to the second part of sub-section (6) of Section 144 of the Code of Criminal Procedure on the ground that it violated sub-clauses (b), (c) and (d) of Clause (1) of Article 19 of the Constitution. Justice K S Hegde, speaking for the majority, observed: “15.One of the important tests to find out whether a restriction is reasonable is to see …whether the restriction is in excess of the requirement or whether it is imposed in an arbitrary manner”.348
(Emphasis supplied)
201 In Mohammed Faruk v State of Madhya Pradesh349 a Constitution Bench of this Court held that in determining the proportionality of a measure restricting an individual’s right under Article 19(1)(g) of the Constitution, the factors to be taken into consideration would include whether a less drastic restriction would have served the purpose. As the Court held:
“10…The Court must in considering the validity of the impugned law imposing a prohibition on the carrying on of a business or profession, attempt an evaluation of its direct and immediate impact upon the fundamental rights of the citizens affected thereby and the larger public interest sought to be ensured in the light of the object sought to be achieved, the necessity to restrict the citizen’s freedom, […],the possibility of achieving the object by imposing a less drastic restraint , […] or that a less drastic restriction may ensure the object intended to be achieved.”350
(Emphasis supplied)
In Bishambhar Dayal Chandra Mohan v State of Uttar Pradesh351, “reasonable restriction” was held to mean that the limitation imposed on the enjoyment of a right should not be arbitrary or of an excessive nature, beyond what is required in the interests of the public. 202 The decision in Om Kumar v Union of India352 concerned the quantum of punishment imposed in departmental disciplinary proceedings. Justice M. Jagannadha Rao, speaking for a two judge Bench, defined proportionality in the following terms:
“28. By ‘proportionality’, we mean the question whether, while regulating exercise of fundamental rights, the appropriate or least restrictive choice of measures has been made by the legislature or the administrator so as to achieve the object of the legislation or the purpose of the administrative order, as the case may be. Under the principle, the Court will see that the legislature and the administrative authority ‘maintain a proper balance between the adverse effects which the legislation or the administrative order may have on the rights, liberties or interests of persons keeping in mind the purpose which they were intended to serve’. The legislature and the administrative authority are however given an area of discretion or a range of choices but as to whether the choice made infringes the rights excessively or not is for the Court. That is what is meant by proportionality.”353
(Emphasis supplied)
In Teri Oat Estates v U.T., Chandigarh354, this Court adopted a similar interpretation of proportionality. 203 In Modern Dental College and Research Centre v State of Madhya Pradesh,355 a Constitution Bench of this Court while dealing with a challenge to the vires of the Madhya Pradesh Niji Vyavasayik Shikshan Sanstha (Pravesh Ka Viniyaman Avam Shulk Ka Nirdharan) Adhiniyam, 2007, held that proportionality is the correct test to apply in the context of Article 19(6). Justice A K Sikri, speaking for the Court, held thus : “60…Thus, while examining as to whether the impugned provisions of the statute and Rules amount to reasonable restrictions and are brought out in the interest of the general public, the exercise that is required to be undertaken is the balancing of fundamental right to carry on occupation on the one hand and the restrictions imposed on the other hand.
This is what is known as ‘Doctrine of Proportionality’. Jurisprudentially, ‘proportionality’ can be defined as the set of Rules determining the necessary and sufficient conditions for limitation of a constitutionally protected right by a law to be constitutionally permissible…”356
(Emphasis supplied)
While expounding on the theory of proportionality, Justice AK Sikri referred to Aharon Barak’s seminal book357 on proportionality: “60…A limitation of a constitutional right will be constitutionally permissible if:
(i) it is designated for a proper purpose;
(ii) the measures undertaken to effectuate such a limitation are rationally connected to the fulfilment of that purpose;
(iii) the measures undertaken are necessary in that there are no alternative measures that may similarly achieve that same purpose with a lesser degree of limitation; and finally
(iv) there needs to be a proper relation (‘proportionality stricto sensu’ or ‘balancing’) between the importance of achieving the proper purpose and the social importance of preventing the limitation on the constitutional right.”358 Justice Sikri held that laws limiting constitutional rights must satisfy the test of proportionality:
“63…The law imposing restrictions will be treated as proportional if it is meant to achieve a proper purpose, and if the measures taken to achieve such a purpose are rationally connected to the purpose, and such measures are necessary….359
64. The exercise which, therefore, to be taken is to find out as to whether the limitation of constitutional rights is for a purpose that is reasonable and necessary in a democratic society and such an exercise involves the weighing up of competitive values, and ultimately an assessment based on proportionality i.e. balancing of different interests.”360
(Emphasis supplied)
204 In KS Puttaswamy v Union of India361, one of us (Chandrachud J.), speaking for four judges, laid down the tests that would need to be satisfied under our Constitution for violations of privacy to be justified. This included the test of proportionality: “325…A law which encroaches upon privacy will have to withstand the touchstone of permissible restrictions on fundamental rights. In the context of Article 21 an invasion of privacy must be justified on the basis of a law which stipulates a procedure which is fair, just and reasonable. The law must also be valid with reference to the encroachment on life and personal liberty under Article 21.
An invasion of life or personal liberty must meet the three-fold requirement of
(i) legality, which postulates the existence of law;
(ii) need, defined in terms of a legitimate state aim; and
(iii) proportionality which ensures a rational nexus between the objects and the means adopted to achieve them.”362 The third principle (iii above) adopts the test of proportionality to ensure a rational nexus between the objects and the means adopted to achieve them.
The essential role of the test of proportionality is to enable the court to determine whether a legislative measure is disproportionate in its interference with the fundamental right. In determining this, the court will have regard to whether a less intrusive measure could have been adopted consistent with the object of the law and whether the impact of the encroachment on a fundamental right is disproportionate to the benefit which is likely to ensue.
The proportionality standard must be met by the procedural and substantive aspects of the law. Justice Sanjay Kishan Kaul, in his concurring opinion, suggested a fourpronged test as follows363:
“(i)The action must be sanctioned by law;
(ii) The proposed action must be necessary in a democratic society for a legitimate aim;
(iii) The extent of such interference must be proportionate to the need for such interference;
(iv) There must be procedural guarantees against abuse of such interference.” The ‘test of proportionality’ is a judicially-entrenched principle which has invigorated fundamental rights jurisprudence in the country. The application of the proportionality standard in rights-based adjudication is well-recognised across diverse jurisdictions.
H.3 Comparative jurisprudence
205 Since some of the concerns raised by the Aadhaar scheme have arisen for the first time in India, it would be appropriate to discuss judgments of foreign jurisdictions which have inquired into the proportionality of measures many of them similar to those prescribed under the Aadhaar Act. 206
The Privy Council formulated the parameters of proportionality in Elloy de Freitas v Permanent Secretary of Ministry of Agriculture, Fisheries, Lands and Housing,364 elaborating a three-fold test: “whether:
(i) the legislative objective is sufficiently important to justify limiting a fundamental right;
(ii) the measures designed to meet the legislative objective are rationally connected to it; and
(iii) the means used to impair the right or freedom are no more than is necessary to accomplish the objective.” Subsequently in Huang (FC) v Secretary of State for the Home Department,365 the House of Lords added a fourth parameter which is “the need to balance the interests of society with those of individuals and groups.”
207 In the Federal Census Act Case (Volkszählungsurteil),366 the Federal Constitutional Court of the Federal Republic of Germany dealt with a challenge to the German Federal Census Act, 1983, which provided for collection of citizens’ basic personal information, including, inter alia, source of income, occupation, supplementary employment, educational background and hours of work. Certain provisions provided for transmission of statistical data to local governments for the purposes of regional planning, surveying, environmental protection, and redrawing of election districts. The Court struck down provisions permitting transfer of statistical data to local authorities on the ground that they enabled authorities to compare census data with local housing registries.
The Court observed that the combination of statistical data and a personalized registry could lead to the identification of particular persons, which would lead to a chilling effect upon individuals’ right to informational self-determination. The Court developed a ‘fundamental right of informational self-determination’ drawing from Articles 1(1) and 2(1) of the German Constitution, which protect the fundamental right to human dignity and the right to freely develop one’s personality. Explaining the importance of this right in the context of risks occasioned by modern data processing, the Court noted that:
“The freedom of individuals to make plans or decisions in reliance on their personal powers of self-determination may be significantly inhibited if they cannot with sufficient certainty determine what information on them is known in certain areas of their social sphere and in some measure appraise the extent of knowledge in the possession of possible interlocutors. A social order in which individuals can no longer ascertain who knows what about them and when and a legal order that makes this possible would not be compatible with the right to informational self-determination…This would not only restrict the possibilities for personal development of those individuals but also be detrimental to the public good since self-determination is an elementary prerequisite for the functioning of a free democratic society predicated on the freedom of action and participation of its members…
The fundamental right guarantees in principle the power of individuals to make their own decisions as regards the disclosure and use of their personal data.”367 The Court, while recognizing the right to informational self-determination, observed that distinct silos of data “can be pieced together with other data collections particularly when individual integrated information systems are built up – to add up to a partial or virtually complete personality profile,” and that too with, “the person concerned having no means of controlling its truth and application.”368 of crucial importance is the Court’s observation that the right to informational self-determination is particularly endangered because in reaching decisions, one no longer has to rely on manually collected registries and files. Today, the technical means of storing individual statements about personal or factual situations of a certain or verifiable person with the aid of automatic data processing are practically unlimited and can be retrieved in a matter of seconds irrespective of distances.369 The Court noted, however, that the right to informational self-determination is not absolute and that public sector entities could collect personal data under certain conditions.
The Court held that there must be a statutory basis for this informational activity, and that it must satisfy the principle of proportionality. On the need for a statutory basis, the Court held that: “The use of the data is limited to the purpose specified by law. If for no other reason than because of the dangers associated with automated data processing, protection is required against unauthorized use – including protection against such use by other governmental entities – through a prohibition on the transfer and use of such data”370 “Clearly defined conditions must be created for processing to ensure that individuals do not become mere data subjects in the context of the automated collection and processing of the information pertaining to their person. Both the absence of a connection with a specific purpose that can be recognized and verified at all times and the multifunctional use of data, reinforce the tendencies that are to be checked and restricted by data-protection legislation, which represents the concrete manifestation of the constitutionally guaranteed right to informational self-determination.
“371 On the principle of proportionality, the Court held that: “The legislature must in its statutory regulations respect the principle of proportionality. This principle, which enjoys constitutional status, follows from the nature of the fundamental rights themselves, which, as an expression of the general right of the public to freedom from interference by the state, may be restricted by the public powers in any given case only insofar as indispensable for the protection of public interests … In view of the threats described above that arise from the use of automated data processing, the legislature must more than was the case previously, adopt organizational and procedural precautions that work counter to the threat of violation of the right of personality …”372 “The survey program of the 1983 Census Act also satisfies, to the extent relevant to the matter under review, the principle of proportionality.
A measure to achieve the intended purpose must therefore be suitable and necessary; the intensity of the attendant action may not be disproportionate to the importance of the matter and the compromises imposed upon the public.”373 The Court concluded that according to the principles of purpose specification and proportionality, not only must the purpose for which data is being collected be specified at the time of collection, but the data acquired must also not exceed that which is absolutely necessary for accomplishing the specified purpose. In light of this, the Court directed the German Parliament to amend the law in certain particulars before the census could be carried out, and to close all loopholes in the law that may lead to abuses in the collection, storage, use and transfer of personal data.
208 The ECtHR dealt with whether retention of DNA samples of individuals who were arrested but who were later acquitted or had charges against them dropped was a violation of the right to privacy. In S and Marper v United Kingdom,374 the ECtHR noted the “blanket and indiscriminate nature of the power of retention”: “The material may be retained irrespective of the nature or gravity of the offence with which the individual was originally suspected or of the age of the suspected offender; fingerprints and samples may be taken-and retained-from a person of any age, arrested in connection with a recordable offence, which includes minor or non-imprisonable offences. The retention is not time-limited; the material is retained indefinitely whatever the nature or seriousness of the offence of which the person was suspected.
Moreover, there exist only limited possibilities for an acquitted individual to have the data removed from the nationwide database or the materials destroyed; in particular, there is no provision for independent review of the justification for the retention according to defined criteria, including such factors as the seriousness of the offence, previous arrests, the strength of the suspicion against the person and any other special circumstances.”375 The Court concluded that the retention constituted a disproportionate interference with the Applicants’ right to privacy:
“125…That the blanket and indiscriminate nature of the powers of retention of the fingerprints, cellular samples and DNA profiles of persons suspected but not convicted of offences, as applied in the case of the present applicants, fails to strike a fair balance between the competing public and private interests and that the respondent State has overstepped any acceptable margin of appreciation in this regard. Accordingly, the retention at issue constitutes a disproportionate interference with the applicants’ right to respect for private life and cannot be regarded as necessary in a democratic society…”
(Emphasis supplied)
The Court rejected the government’s arguments that fingerprints constituted neutral, objective, irrefutable and unintelligible material, holding that they contained unique information about an individual, allowing their precise identification in certain circumstances. The Court concluded that the collection of fingerprints was therefore capable of affecting private life, and retention of such information without consent “cannot be regarded as neutral or insignificant.” 209 In 2012, the French Constitutional Council (“Council”) – the body that reviews the constitutionality of French laws – declared four provisions of the Identity Protection Act, which proposed the introduction of a new national biometric ID for citizens, to be unconstitutional.376 Articles 3 and 5 were among the provisions that were struck down. Article 3 authorized that the national ID card may contain data which would enable the holder to identify himself or herself on electronic communication networks or use his or her electronic signature.
The Article stated that: “If requested by its holder, the national identity card may also contain data, stored separately, enabling it to identify itself on electronic communication networks and to affix its electronic signature. Upon each use, the interested party shall decide which identification data are to be transmitted electronically.” The Council observed that Article 3 did not stipulate the nature of the data that was being collected, nor did it provide any guarantee of maintaining confidentiality. Thus, the Council declared Article 3 to be unconstitutional: “that the provisions of Article 3 do not specify either the nature of the “data” through which these functions may be implemented or the guarantees ensuring the integrity and confidentiality of this data; that they do not define in any greater detail the conditions under which the persons implementing these functions are to be authenticated, especially when they are minors or are subject to legal protection; that accordingly, Parliament acted in excess of its powers; that accordingly Article 3 must be ruled unconstitutional;”
Article 5 allowed for the establishment of a database of personal information which would include, in addition to the marital status and residence of the holder, their height, eye colour, fingerprints and photograph for the issuance of French passports and national ID cards and for conducting investigations involving certain offences if authorised by a public prosecutor or a judge. The Council relied on Article 34 of the French Constitution to hold that it was incumbent upon the Parliament to strike a balance between safeguarding public order and bringing offenders to justice on one hand, and the right to privacy on the other. The Council placed reliance on the Declaration of the Rights of Man and the Citizen of 1789. Article 2 of the Declaration states “The aim of every political association is the preservation of the natural and imprescriptible rights of Man. These rights are liberty, property, safety and resistance to oppression”.
The Council held that the liberty proclaimed by Article 2 includes the right to respect for private life, and accordingly, that “the collection, registration, conservation, consultation and communication of personal data must be justified on grounds of general interest and implemented in an adequate manner, proportionate to this objective.”
The Council held that Article 5 violated the French Constitution as the nature of the data collected was such that it would facilitate the identification of French PART H 286 citizens on the basis of their fingerprints, thus breaching the right to respect for private life: “Considering however that, given its object, this database containing personal data is intended to collect data relating to almost all of the population of French nationality; that since the biometric data registered in this file, including in particular fingerprints, are themselves liable to be compared with physical traces left involuntarily by an individual or collected unbeknown to him, they are particularly sensitive; that the technical characteristics of this database as defined by the contested provisions enable it to be consulted for purposes other than the verification of an individual’s identity; that the provisions of the act referred authorise this database to be consulted or viewed not only in relation to the issue or renewal of identity and travel documents or to verify the holder of such a document, but also for other purposes of an administrative nature or by the investigating police;… …having regard to the nature of the data registered, the scope of this processing, its technical characteristics and the conditions under which it may be consulted, the provisions of Article 5 violate the right to respect for privacy in a manner which cannot be regarded as proportionate to the goal pursued; that accordingly, Articles 5 and 10 of the act must be ruled unconstitutional…”
(Emphasis supplied)
Subsequently, Law 2012-410 of March 27, 2012, on Identity Protection was published in the official gazette of France, without Articles 3 and 5, which had been rendered unconstitutional by the Council.377 210 Aycaguer v France378 concerned the applicant’s refusal to undergo biological testing, the result of which was to be included in the national computerised DNA database. As a result of his refusal, he was convicted. The ECtHR held that the regulations on the storage of DNA profiles did not provide individuals with sufficient protection, due to its duration and the fact that the data could not be deleted. The Court concluded that the regulations failed to strike a balance between competing public and private interests and held, unanimously, that there had been a violation of Article 8 (right to respect for private life) of the European Convention on Human Rights.
211 The Conseil d’Etat379 in Association pour la promotion de l’image380 was asked whether a decree regulating the use and storage of data from biometric passports was lawful. One of the stipulations of the decree was that eight fingerprints were stored by the authorities, while only two were required for the passport. The Conseil d’Etat stated that the collection and retention of six more fingerprints to be centrally stored was irrelevant and excessive in relation to the purpose of the computerized database.
212 In Digital Rights Ireland Ltd v Minister,381 the Court of Justice of the European Union held that the EU legislature had exceeded the limits of the principle of proportionality in relation to certain provisions of the Charter of Fundamental Rights of the European Union – Articles 7, 8 and 52(1) – by adopting the Data Retention Directive. According to the Directive, member states were obliged to store citizens’ telecommunications data for a minimum of 6 months and a maximum of 24 months.
The Directive empowered police and security agencies to request access to details such as IP address and time of use of all e-mails, phone calls and text messages sent or received. The Court applied the test of proportionality to the measures. It was noted that metadata allows officials to make precise conclusions about a person’s private life, and dragnet data collection creates a chilling effect based on the sense that one’s life is subject to surveillance at all times.
On the nature of metadata, the Court observed that: “Taken as a whole, [metadata] may allow very precise conclusions to be drawn concerning the private lives of the persons whose data has been retained, such as the habits of everyday life, permanent or temporary places of residence, daily or other movements, the activities carried out, the social relationships of those persons and the social environments frequented by them.”382 The Court found that surveillance serves an important public interest – public security – and that the right to security is itself a fundamental right under Article 6 of the Charter.383 However, the Court adopted a two-pronged proportionality test to conclude that the Directive’s retention and access requirements were not proportional to that interest.
“…According to the settled case-law of the Court, the principle of proportionality requires that acts of the EU institutions be appropriate for attaining the legitimate objectives pursued by the legislation at issue and do not exceed the limits of what is appropriate and necessary in order to achieve those objectives.”384 The retention measure was held to be unnecessary to fulfill the objective of fighting against serious crime: “As regards the necessity for the retention of data required by Directive 2006/24, it must be held that the fight against serious crime, in particular against organised crime and terrorism, is indeed of the utmost importance in order to ensure public security and its effectiveness may depend to a great extent on the use of modern investigation techniques. However, such an objective of general interest, however fundamental it may be, does not, in itself, justify a retention measure such as that established by Directive 2006/24 being considered to be necessary for the purpose of that fight.
(Emphasis supplied)”
The Court criticized the Directive for failing to lay down any clear or precise rules governing the extent of the interference with the fundamental rights enshrined in Articles 7 and 8 of the Charter. It observed that the Directive was overbroad because it applied to all data, regardless of the existence of suspicion, and contained no criteria for limiting government access or safeguards for preventing abuse: “…Directive 2006/24 covers, in a generalised manner, all persons and all means of electronic communication as well as all traffic data without any differentiation, limitation or exception being made in the light of the objective of fighting against serious crime…
…Whilst seeking to contribute to the fight against serious crime, Directive 2006/24 does not require any relationship between the data whose retention is provided for and a threat to public security and, in particular, it is not restricted to a retention in relation (i) to data pertaining to a particular time period and/or a particular geographical zone and/or to a circle of particular persons likely to be involved, in one way or another, in a serious crime, or (ii) to persons who could, for other reasons, contribute, by the retention of their data, to the prevention, detection or prosecution of serious offences.”386
“Not only is there a general absence of limits in Directive 2006/24 but Directive 2006/24 also fails to lay down any objective criterion by which to determine the limits of the access of the competent national authorities to the data and their subsequent use for the purposes of prevention, detection or criminal prosecutions concerning offences that, in view of the extent and seriousness of the interference with the fundamental rights enshrined in Articles 7 and 8 of the Charter, may be considered to be sufficiently serious to justify such an interference.
On the contrary, Directive 2006/24 simply refers, in Article 1(1), in a general manner to serious crime, as defined by each Member State in its national law.”387 The Court concluded that the Directive failed to set out “clear and precise rules”388 for access or for how states should judge the period of time for which data should be held, and “entails a wide-ranging and particularly serious interference with those fundamental rights in the legal order of the EU, without such an interference being precisely circumscribed by provisions to ensure that it is actually limited to what is strictly necessary.”389
The Court struck down the Directive on the basis of the scope of the data to be retained,390 the lack of limits imposed on state access,391 and the failure to distinguish between the treatment of data based on its usefulness and relevance.392 of crucial importance is the Court’s emphasis that the judicial review of the EU legislature’s discretion “should be strict” because of “the important role played by the protection of personal data in the light of the fundamental right to respect for private life and the extent and seriousness of the interference with that right caused by Directive 2006/24”.393 In addition, the Court emphasized that even highly important objectives such as the fight against serious crime and terrorism cannot justify measures which lead to forms of interference that go beyond what is ‘strictly necessary’.394
213 In Michael Schwarz v Stadt Bochum,395 the Court of Justice of the European Union was called upon to examine the validity of a provision in a Council Regulation that obliged persons applying for a passport to provide fingerprints which would be stored in that passport. In considering whether this regulation was valid and necessary, the Court observed: “…Article 1(2) of Regulation No 2252/2004 does not provide for the storage of fingerprints except within the passport itself, which belongs to the holder alone.396 The regulation not providing for any other form or method of storing those fingerprints, it cannot in and of itself…be interpreted as providing a legal basis for the centralised storage of data collected thereunder or for the use of such data for purposes other than that of preventing illegal entry into the European Union.397
In those circumstances, the arguments put forward by the referring court concerning the risks linked to possible centralisation cannot, in any event, affect the validity of that regulation and would have, should the case arise, to be examined in the course of an action brought before the competent courts against legislation providing for a centralised fingerprint base. In the light of the foregoing, it must be held that Article 1(2) of Regulation No 2252/2004 does not imply any processing of fingerprints that would go beyond what is necessary in order to achieve the aim of protecting against the fraudulent use of passports.
It follows that the interference arising from Article 1(2) of Regulation No 2252/2004 is justified by its aim of protecting against the fraudulent use of passports.”398 The Court held that although the taking and storing of fingerprints in passports constituted an infringement of the right to respect for private life and the right to protection of personal data, Article 1(2) of Regulation No 2252/2004 did not imply any processing of fingerprints that would go beyond what is necessary in order to achieve the aim of protecting against the fraudulent use of passports and was therefore valid.
214 In Madhewoo v The State of Mauritius,399 the Judicial Committee of the Privy Council heard an appeal from a judgment of the Supreme Court of Mauritius regarding the constitutionality of the provisions of The National Identity Card (Miscellaneous Provisions) Act, 2013. The Act required biometric information including fingerprints, to be stored in a central register in which particulars of the identity of every citizen of Mauritius were to be recorded. The Supreme Court upheld provisions of the Act that provided for the compulsory taking of fingerprints. However, the Court struck down those provisions that provided for the biometric data to be stored in a central register. The Appellant appealed to the Committee, contending that the provisions providing for the compulsory taking of fingerprints should also be struck down as unconstitutional. The appellant challenged the following provisions of the Act:
(i) the storage of data in a register in electronic data under Section 3;
(ii) the obligation to provide biometric information under Section 4;
(iii) the collection of information, in electronic form, for a national ID card under Section 5;
(iv) the compulsory production of an identity card to a policeman under Section 7(1A) in response to a request under Section 7(1)(b); and (v) the gravity of the potential penalties for non-compliance under Section 9(3), before the Mauritian Supreme Court. The challenge was on the ground that the implementation of the biometric identity card and the permanent storage of biometric data contravened provisions of the Mauritian Constitution and the Civil Code. Regarding the challenge to Section 4 (2)(c) of the Act, which provided that, “every person who applies for an identity card shall allow his fingerprints, and other biometric information about himself, to be taken and recorded … for the purpose of the identity card,” the Supreme Court noted that the right to privacy under Section 9(1) of the Constitution was not an absolute right and interference with that right could be permitted under Section 9(2), if a law that interfered with that right was in the interest, inter alia, of public order.
The Committee noted the Supreme Court’s approach to determining whether Section 4(2)(c) fell foul of the Constitution, which was based on the test laid down in S and Marper v The United Kingdom400: “In addressing the question whether section 4(2)(c) of the 1985 Act (as amended) was reasonably justifiable in a democratic society the Supreme Court drew on jurisprudence of the European Court of Human Rights in S v The United Kingdom…In substance the Court asked whether the measure pursued a legitimate aim, whether the reasons given by the national authorities for the interference in pursuit of that aim were relevant and sufficient, and whether the measure was proportionate to the aim pursued.
This evaluation is essentially the same as that adopted by the courts in the United Kingdom in relation to article 8(2) of the ECHR, in which the courts ask themselves (a) whether the measure is in accordance with the law, (ii) whether it pursues a legitimate aim, and (iii) whether the measure will give rise to interferences with fundamental rights which are disproportionate, having regard to the legitimate aim pursued. In relation to (iii), the courts ask themselves: (a) whether the objective is sufficiently important to justify a limitation of the protected right, (b) whether the measure is rationally connected to the objective, (c) whether a less intrusive measure could have been used without compromising the achievement of the objective (in other words, whether the limitation on the fundamental right was one which it was reasonable for the legislature to impose), and (d) whether the impact of the infringement of the protected rights is disproportionate to the likely benefit of the measure”
The Committee reproduced the Mauritian Supreme Court’s holding that the provisions of the Act which enforced the compulsory taking and recording of fingerprints interfered with the Appellant’s rights guaranteed under section 9(1) of the Constitution,401 but that the law was justifiable on grounds of public interest and public order: “We find that it can hardly be disputed that the taking of fingerprints within the applicable legal framework pursues the legitimate purpose of establishing a sound and secure identity protection system for the nation and thus answers a pressing social need affording indispensable protection against identity fraud. Such a purpose, as has been amply demonstrated, is vital for proper law enforcement in Mauritius.
Furthermore, taking into consideration the appropriate safeguards in the taking of fingerprints for their insertion in the cards, and the relatively limited degree of interference involved, we are led to conclude that such interference is proportionate to the legitimate aim pursued.”402 Thus, the Mauritian Supreme Court upheld provisions of the Act which provided for the compulsory taking of fingerprints. The Appellant also challenged Section 3 of the Act, which provided for biometric data to be stored in a register.
The Supreme Court, after taking into consideration witness testimonies on the purpose of data collection, noted that though there may have been a legitimate aim for storing and collecting this data, “sufficiently strong reasons…to establish that such storage and retention of data for an indefinite period is proportionate to the legitimate aim pursued” were not established.403 Thus, the Court held that: “… it is inconceivable that there can be such uncontrolled access to personal data in the absence of the vital safeguards afforded by judicial control.
The potential for misuse or abuse of the exercise of the powers granted under the law would be significantly disproportionate to the legitimate aim which the defendants have claimed in order to justify the retention and storage of personal data under the Data Protection Act.”404 Thus, while the Supreme Court noted that the law providing for the storage and retention of personal biometric data constituted a permissible derogation under Section 9(2) of the Constitution,405 it held that since the Respondent had not established that provisions dealing with storage and retention were reasonably justifiable in a democratic society, they were unconstitutional.
The Judicial Committee did not interfere with the Supreme Court’s decision. However, it noted an inconsistency in the Supreme Court’s order wherein it held that the law providing for the storage and retention of fingerprints and other biometric data constitutes a permissible derogation under section 9(2) of the Constitution, whilst simultaneously holding the same provisions to be unconstitutional. The Committee reconciled the holding to be: “A law providing for the storage and retention of fingerprints and other personal biometric data regarding the identity of a person in principle constitutes a permissible derogation, in the interests of public order, under section 9(2) of the Constitution.”
(Emphasis supplied)
215 The learned Attorney General has relied on cases from other jurisdictions to buttress his contention that the collection and use of biometric information for various services have been found to be legal. ‘Biometric data406’ is defined in the General Data Protection Regulation thus: “personal data resulting from specific technical processing relating to the physical, physiological or behavioural characteristics of a natural person, which allow or confirm the unique identification of that natural person, such as facial images or dactyloscopic data.”
The learned Attorney General cited the following judgments of the US Supreme Court: Vernonia School District 47J v Acton (“Acton”),407 Skinner v Railway Labor Executives’ Association (“Skinner”),408 Whalen v Roe (“Whalen”),409 United States v Dionisio (“Dionisio”)410 and Bowen v Roy (“Bowen”).411 Only Acton, Skinner and Dionisio were decided in the context of biometrics, which as we have found before, forms the bedrock of the Aadhaar program. In Acton, the court held that the action of the authorities conducting random drug testing of high school athletes was legal since the conditions of collection were nearly identical to those typically encountered in public restrooms. As a result, it was found that, privacy interests of the students were negligibly affected.
In Skinner, the court found the actions of the Federal Railroad Administration (“FRA”) requiring mandatory blood and urine testing of employees involved in train accidents to be constitutional. The court observed that railroad accidents, if not prevented, could cause massive loss of life and property. Further, it was held that FRA’s regulations fulfilled a “special need” because of the interest of the government in ensuring safety of railroads and were therefore, not “an undue infringement on the justifiable expectations of privacy of covered employees”.
In Whalen, the Court found that retention of patients’ information such as their name, address and age, under the New York State Controlled Substances Act, 1972, was not in violation of the constitutional right to privacy as the Court was satisfied that the statute provided for proper safeguards and redressal against theft and loss of information. In Dionisio, the Court found no constitutional infirmity with the issuance of a subpoena to procure voice recording exhibits by tapping telephones in order to investigate crimes.
The Court held that “neither the summons to appear before the grand jury, nor its directive to make a voice recording, infringed upon any interest protected by the Fourth Amendment”. The Court observed that a compelled display of identifiable physical characteristics does not infringe upon an “interest protected by the privilege against compulsory self-incrimination”. In Bowen, the Court upheld the provisions of a welfare scheme which required citizens to furnish their social security number, rejecting the argument that the use of a social security number violated the Appellant’s Native American beliefs. The Court held that the Free Exercise Clause of the First Amendment could not be construed to place a requirement on the government to conduct its internal affairs in consonance with the religious beliefs of particular citizens.
In re Crawford,412 the Ninth Circuit upheld provisions of the Bankruptcy Code which mandated public disclosure of a Bankruptcy Petition Preparers’ Social Security Number on documents submitted to the Court, noting that the provision had been enacted to serve governmental interests of preventing fraud and providing public access to judicial proceedings. 216 Some decisions of lower courts in the US which have considered the validity of laws or actions of the State deploying biometrics and which have been cited by the respondents are: Haskell v Harris (“Haskell”),413 Utility Workers Union of America v Nuclear Regulatory Commission (“UWUA”),414 Nicholas A Iacobucci v City of Newport (“Iacobucci”),415 Thom v New York Stock Exchange (“Thom”),416 Perkey v Department of Motor Vehicles (“Perkey”),417 Buchanan v Wing (Buchanan),418 People v Stuller (“Stuller”),419 United States v Kelly (“Kelly”)420 and Brown v Brannon (“Brannon”).421
At first blush, it does seem that these cases support the Respondents’ stand, however, we cannot lose sight of the context in which the courts came to the conclusion emphasised by the respondents in support of their submissions. In Haskell, the Ninth Circuit found a Californian law which authorized law enforcement officers to collect DNA in the form of a sample from the buccal swab of the mouth of felony arrestees, who had not been convicted, to be constitutional.
The Court noted that the arrestees had reduced privacy interests; the physical intrusion of collecting a buccal swab was de minimis in nature; there were stringent limits on the manner in which the information was to be used; and the interest of the State in deterring future criminal acts to exculpate innocent arrestees aided in prison administration and law enforcement. For the above reasons, the Court found that the infringement of privacy of the felony arrestees was justified. In UWUA, the Ninth Circuit ruled that a law requiring individuals working in nuclear power facilities to submit their fingerprints for identification and criminal history record checks was not unconstitutional.
In Iacobucci, an ordinance which required employees of liquor selling establishments which permitted nude dancing, to be fingerprinted and photographed by the police department, was held constitutional. The Court observed that fingerprinting and photographing of employees of retail liquor establishments bore a rational relationship to the legitimate aim of elimination of crime.
In Thom, a New York statute, which as a condition of employment, required all the employees of member firms of national stock exchanges to be fingerprinted, was upheld. The Court ruled that fingerprinting was a necessary means of verifying the existence or nonexistence of a prior criminal record, in order to avert any threat posed by an employee who was in a position to commit theft of securities. In Perkey, the Californian Supreme Court upheld the actions of the state mandating an individual to provide a fingerprint in order to obtain a driver’s license. The Court held that fingerprint technology was the only reliable means of ensuring the integrity of the records of the department of motor vehicles as other methods such as handwriting specimens and photographs were not reliable.
Thus, the submission of fingerprints as part of the license application process, bore a rational relationship to the State’s goal of promoting safe and lawful use of highways. In Buchanan, the Court upheld the eligibility requirement for a welfare aid scheme which mandated participation in an identity verification procedure known as Automated Finger Imaging System (AFIS), rejecting the challenge based on religious beliefs of the Petitioner. The Court held that the Petitioner had failed to prove that the AFIS involved any invasive procedures, noting that she had acknowledged that she had never seen finger imaging performed and had no idea whether a laser was involved.
In Stuller, the constitutionality of a law which required “temporary and itinerant classes of employees” to undergo fingerprinting in order to protect “visitors and residents” of a resort city from crime and loss, both against people and against property, was upheld. In Kelly, the Circuit Court of Appeals rejected a claim for return of fingerprints of the defendant which had been obtained after he had been arrested by prohibition agents, holding that there was no reason to interfere with a method of identifying persons “charged with a crime”. In Brannon, the court held that a law requiring “massagists” to submit their fingerprints, photographs and reports of their medical examinations in order to obtain licenses was valid, noting that the fingerprints and photographs would aid in their identification as well as in the enforcement of criminal statutes relating to public morality and decency.
217 The cases cited by the learned Attorney General would not be applicable in the context of the Aadhaar program. The cases cited dealt with narrowly tailored legislations set out to achieve very specific objectives. For instance, courts upheld statutes aimed at protecting a nuclear facility or to prevent theft of securities, where incidents of sabotage or breach of security would have led to national disasters. These national disasters in turn would have resulted in the immediate loss of human life or in a situation of financial emergency. Such laws, were therefore, enacted in order to assuage security concerns which, if not implemented, could lead to incidents of massive losses of life and property.
Some of the statutes upheld, permitted collection of DNA samples, fingerprints and photographs for identification. The objective behind these laws was prevention of crime, albeit on a comparatively smaller scale. Moreover, the courts in these cases were also satisfied that the procedures involved in collecting biometrics were not invasive enough to strike them down as unconstitutional or that there were adequate safeguards to prevent misuse. The aforementioned cases will not apply in the backdrop of the Aadhaar program because they were rendered broadly in the context of prevention of crime. It needs no reiteration that an entire population cannot be presumed to be siphoning huge sums of money in welfare schemes or viewed through the lens of criminality, and therefore, considered as having a diminished expectation of privacy.
The judgments cited by the respondents which were decided in the context of crime, require the State to at least form a reasonable belief about the criminal antecedents of individuals or their potential to commit crimes. On the contrary, by collecting identity information, the Aadhaar program treats every citizen as a potential criminal without even requiring the State to draw a reasonable belief that a citizen might be perpetrating a crime or an identity fraud. When the State is not required to have a reasonable belief and judicial determination to this effect, a program like Aadhaar, which infringes on the justifiable expectations of privacy of citizens flowing from the Constitution, is completely disproportionate to the objective sought to be achieved by the State.
The fundamental precepts of proportionality, as they emerge from decided cases can be formulated thus:
1. A law interfering with fundamental rights must be in pursuance of a legitimate state aim;
2. The justification for rights-infringing measures that interfere with or limit the exercise of fundamental rights and liberties must be based on the existence of a rational connection between those measures, the situation in fact and the object sought to be achieved;
3. The measures must be necessary to achieve the object and must not infringe rights to an extent greater than is necessary to fulfil the aim;
4. Restrictions must not only serve a legitimate purposes; they must also be necessary to protect them; and
5. The State must provide sufficient safeguards relating to the storing and protection of centrally stored data. In order to prevent arbitrary or abusive interference with privacy, the State must guarantee that the collection and use of personal information is based on the consent of the individual; that it is authorised by law and that sufficient safeguards exist to ensure that the data is only used for the purpose specified at the time of collection. Ownership of the data must at all times vest in the individual whose data is collected. The individual must have a right of access to the data collected and the discretion to opt out.
219 Privacy and proportionality are two interlocking themes that recur consistently in the above judgements. Privacy, also construed as “informational self-determination”, is a fundamental value. There is a consistent emphasis on the impact on personal dignity if private information is widely available and individuals are not able to decide upon its disclosure and use. This right of controlling the extent of the availability and use of one’s personal data is seen as a building block of data protection – especially in an environment where the state of technology facilitates ease of collection, analysis and dissemination of information.
220 The blanket and indiscriminate collection of information is seen as a violation of privacy, which is a constituent of the right to liberty. An extensive power to retain collected data is also seen as a disproportionate interference with the right to privacy and not necessary in a democratic society. The judgments hold that unlimited data retention and unrestricted state access both constitute a disproportionate interference with privacy and data protection. They also emphasize the need to clearly stipulate the nature of the data being collected and ensure its confidentiality. Provisions where these principles are not respected cannot be regarded as valid. While courts do recognize the need for public order and security, they emphasize the need to strike a balance between safeguarding public order and the right to privacy.
221 The principle of proportionality also recurs through these judgments, which note that the collection and use of information must be limited to the purpose specified by law and to the extent indispensable for the protection of public interest. The striking of a balance between public and private interests is crucial to proportionality. The judgments hold that there must be a protection against unauthorized use and clearly defined conditions for processing of data collected. Those conditions must not be excessive and must be justified on grounds of public interest and implemented in a manner proportionate to the objective. Too broad a scope of data collected and retained, the lack of limits imposed on access to data by authorities and a failure to distinguish between the treatment of data based on its usefulness and relevance are seen by Courts as constituting grounds for striking down the measure. While the State’s imperatives are seen as relevant, emphasis is laid on retention and access requirements being proportionate to those imperatives and the need to prevent against abuse. Courts have upheld regulations that are necessary to achieve the legitimate aims and not excessive in their nature or impact. The issue is whether the Aadhaar project and the Act, Rules and Regulations meet the test of proportionality.
H.4 Aadhaar: the proportionality analysis
222 Under Aadhaar, the State has put forth an objective of transferring subsidies and entitlements to its citizens. The aim was to curb leakages and to increase transparent and efficient “targeted delivery of subsidies, benefits and services”. However, the Act in the present form has surpassed a tailored objective and has sought to administer every facet of the citizen-state engagement through mandatory biometric-enabled Aadhaar linking. The violations of fundamental rights that result from the operation of the Aadhaar scheme will have to be evaluated on the touchstone of legitimate state interest and proportionality. Since biometric systems have been employed, it is fundamental to understand that the right to privacy and its protection must be at the centre of the debate, from the very onset of the decision to use biometric data.
It is vital that adequate safeguards are set down for every step of the process from collection to retention of biometric data. At the time of collection, individuals must be informed about the collection procedure, the intended purpose of the collection, the reason why the particular data set is requested and who will have access to their data. Additionally, the retention period must be justified and individuals must be given the right to access, correct and delete their data at any point in time, a procedure familiar to an opt-out option. The intended purpose should always act as a shining light and adequate caution must be PART H 307 taken to ensure that there is no function creep with the lapse of time, in order to prevent the use of the data for new, originally unintended purposes.
Measures to protect privacy would include enacting more entrenched and specific legislation so that the right to privacy is not only recognized but protected in all its aspects. Meeting this obligation would necessarily mean enactment of data protection legislation as well. The choice of particular techniques and the role of components in the architecture of the technology also have a strong impact on the privacy protections provided by the biometric system. During the course of the hearing, the CEO of UIDAI, Mr Ajay Bhushan Pandey was permitted on the request of the learned Attorney General to make a power-point presentation before the Court, explaining the architecture and working of the Aadhaar project.
On the basis of the presentation, Mr Shyam Divan, counsel for the petitioners had served a list of questions to the respondents. Responses to these questions have been filed by UIDAI. Analysing the power-point presentation by the CEO, questions addressed by Mr Divan and the responses filed by the respondents will facilitate an understanding of the architecture of the Aadhaar project. Our analysis indicates that the correctness of the documents submitted by an individual at the stage of enrolment or while updating information is not verified by any official of UIDAI or of the Government.
UIDAI does not take institutional responsibility for the correctness of the information entering its database. It delegates this task to the enrolment agency or the Registrar. The following response has been submitted by the respondents to the queries addressed specifically on this aspect: “As per UIDAI process, the verification of the documents is entrusted to the Registrar. For Verification based on Documents, the verifier present at the Enrolment Centre will verify the documents. Registrars/Enrolment agency must appoint personnel for the verification of documents.”
223 UIDAI does not identify the persons who enrol within the Aadhaar system. Once the biometric information is stored in the CIDR during enrolment, it is only matched with the information received at the time of authentication. Biometric authentication of an Aadhaar number holder is performed as a “one to one” biometric match against the biometric information of the Aadhaar number holder in CIDR. Based on the match, UIDAI provides a ‘yes’ or ‘no’response. Whether the information which is entering into CIDR is correct or not is a task entrusted to the enrolling agency or the Registrars. UIDAI does not assume responsibility for it. The task of verifying whether a person is an illegal resident has also been left to the enrolling agencies. At the stage of enrolment, a verification of whether a person has been residing in India for 182 days or more in the past twelve months is done on the basis of a ‘self-declaration’ of the individual.
The declaration which has been provided in the Aadhaar enrolment forms is thus: “Disclosure under section 3(2) of The Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Servìces Act, 2016 I confirm that I have been residing in India for at least 182 days in the preceding 12 months & information (including biometrics) provided by me to the UIDAI Ìs my own and is true, correct and accurate. I am aware that my information including biometrics will be tested for generation of Aadhaar and authentication. I understand that my identity information (except core biometric) may be provided to an agency only with my consent during authentication or as per the provisions of the Aadhaar Act. I have a right to access my identity information (except core biometrics) following the procedure laid down by UIDAI.”422
224 The petitioners have argued that persons who were enrolled under the Aadhaar programme before the Act came into force on 12 September 2016 (more than a hundred crore) were not even required to make this declaration. The authenticity of the documents submitted (along with the declaration) is not checked by UIDAI. The exception handling process permitting the use of alternative modes of identification if the Aadhaar authentication fails, is also left to the discretion of the Requesting Entity. On this aspect, the response which has been provided to the Court is thus: “As per Regulation 14(i) of Aadhaar (Authentication) Regulations 2016, requesting entities shall implement exception-handling mechanisms and back-up identity authentication mechanisms to ensure seamless provision of authentication services to Aadhaar number holders.
Therefore, this exception handling mechanism is to be implemented and monitored by the requesting entities and in case of the government, their respective ministries.”
Forty-nine thousand enrolment operators have been blacklisted by UIDAI. In reply to the question of the petitioners asking the reasons for blacklisting of the enrolment operators, UIDAI has stated that a data quality check is done during the enrolment process and if any Aadhaar enrolment is found to be not to be compliant with the UIDAI process, the enrolment gets rejected and an Aadhaar number is not generated. An operator who crosses a threshold defined in the policy, is blacklisted/ removed from the UIDAI ecosystem. UIDAI has provided information that forty-nine thousand operators were blacklisted/removed from the UIDAI ecosystem for the following reasons:
(a) illegally charging residents for Aadhaar enrolment;
(b) poor demographic data quality;
(c) invalid biometric exceptions; and (d) other process malpractices. Once an operator is blacklisted or suspended, further enrolments cannot be carried out by it until the order of blacklisting/suspension is valid.
225 The Aadhaar architecture incorporates the role of Authentication User Agencies (AUAs) and Authentication Service Agencies (ASAs). ASAs, under the Aadhaar (Authentication) Regulations, have been defined as entities providing necessary infrastructure for ensuring secure network connectivity and related services for enabling a requesting entity to perform authentication using the authentication facility provided by UIDAI.423 AUAs have been defined under the Aadhaar (Authentication) Regulations as requesting entities that use the Yes/No authentication facility provided by UIDAI.424 “Yes/No authentication facility” is a type of authentication facility in which the identity information and Aadhaar number securely submitted with the consent of the Aadhaar number holder through a requesting entity, are matched against the data available in the CIDR, and the Authority responds with a digitally signed response containing a “Yes” or “No”, along with other technical details related to the authentication transaction, excluding identity information.425
The other type of authentication facility is the e-KYC authentication facility, in which the biometric information and/or OTP and Aadhaar number securely submitted with the consent of the Aadhaar number holder through a requesting entity, are matched against the data available in the CIDR, and the Authority returns a digitally signed response containing e-KYC data along with other technical details related to the authentication transaction.
A requesting entity which, in addition to being an AUA, uses e-KYC authentication facility provided by UIDAI is called a “e-KYC User Agency” or “KUA”.426 Under Regulation 15(2), a requesting agency may permit any other agency or entity to perform Yes/ No authentication by generating and sharing a separate license key for every such entity through the portal provided by UIDAI to the said requesting entity. It has also been clarified that sharing of a license key is only permissible for performing Yes/ No authentication, and is prohibited in case of e-KYC authentication.427 The petitioners have contended that the points of service (PoS) biometric readers are capable of storing biometric information.
The response which UIDAI has provided is extracted below: “UIDAI has mandated use of Registered Devices (RD) for all authentication requests. With Registered Devices biometric data is signed within the device/ RD service using the provider key to ensure it is indeed captured live. The device provider RD Service encrypts the PID block before returning to the host application. This RD Service encapsulates the biometric capture, signing and encryption of biometrics all within it. Therefore, introduction of RD in Aadhaar authentication system rules out any possibility of use of stored biometric and replay of biometrics captured from other source. Requesting entities are not legally allowed to store biometrics captured for Aadhaar authentication under Regulation 17(1)(a) of Aadhaar (Authentication) Regulations 2016.”
226 A PID block is defined in Regulation 2(n) of Aadhaar (Authentication) Regulations, 2016 as the Personal Identity Data element, which includes necessary demographic and/or biometric and/or OTP collected from the Aadhaar number holder during authentication. Regulation 17(1)(c) allows the requesting entity to store the PID block when “it is for buffered authentication where it may be held temporarily on the authentication device for a short period of time, and that the same is deleted after transmission”.
Thus, under the Aadhaar project, requesting entities can hold the identity information of individuals, even if for a temporary period. It was further contended by the petitioners that authentication entities in the Aadhaar architecture are capable of recording the date and time of the authentication, the client IP, the device ID and purpose of authentication. In PART H 313 response, UIDAI stated that it does not ask requesting entities to maintain any logs related to the IP address of the device, GPS coordinates of the device and purpose of authentication. It was, however, admitted that in order to ensure that their systems are secure and frauds are managed, AUAs like banks and telecom providers may store additional information according to their requirement to secure their system.
227 The process of sending authentication requests has been dealt with in Regulation 9 of the Aadhaar (Authentication) Regulations. It provides that after collecting the Aadhaar number or any other identifier provided by the requesting entity which is mapped to the Aadhaar number and necessary demographic and / or biometric information and/ or OTP from the Aadhaar number holder, the client application immediately packages and encrypts the input parameters into the PID block before transmission and sends it to the server of the requesting entity using secure protocols. After validation, the server of a requesting entity passes the authentication request to the CIDR, through the server of the Authentication Service Agency.
The Regulation further provides that the authentication request must be digitally signed by the requesting entity and/or by the Authentication Service Agency, pursuant to the mutual agreement between them. Based on the mode of authentication requested, the CIDR validates the input parameters against the data stored and returns a digitally signed Yes or No authentication response, or a digitally signed e-KYC authentication response with encrypted e-KYC data, as the case may be, along with other technical details related to the authentication transaction.
In all modes of authentication, the Aadhaar number is mandatory and is submitted along with the input parameters such that authentication is always reduced to a 1:1 match. Clause (5) of Regulation 9 provides that a requesting entity shall ensure that encryption of PID Block takes place at the time of capture on the authentication device according to the processes and specifications laid down by UIDAI. Regulation 18(1) provides that a requesting entity would maintain logs of the authentication transactions processed by it, containing the following transaction details:
(a) the Aadhaar number against which authentication is sought;
(b) specified parameters of authentication request submitted;
(c) specified parameters received as authentication response;
(d) the record of disclosure of information to the Aadhaar number holder at the time of authentication; and
(e) record of consent of the Aadhaar number holder for authentication.
The provision excludes retention of PID information in any case. Regulations 18(2) and 18(3) allow the retention of the logs of authentication transactions by the requesting entity for a period of two years. Upon the expiry of two years the logs have to be archived for a period of five years or the number of years required by the laws or regulations governing the entity, whichever is later. Upon the expiry of this period, the logs shall be deleted except those records which are required to be retained by a court or for any pending disputes.
Regulation 20(1) provides that an Authentication Service Agency would maintain logs of the authentication transactions processed by it, containing the following transaction details:
(a) identity of the requesting entity;
(b) parameters of authentication request submitted; and
(c) parameters received as authentication response.
The Regulation excludes retention of Aadhaar number, PID information, device identity related data and e-KYC response data. Under Regulations 20(2) and 20(3), authentication logs shall be maintained by the ASA for a period of two years, during which period the Authority and/or the requesting entity may require access to such records for grievance redressal, dispute redressal and audit in accordance with the procedure specified in the regulations. The authentication logs shall not be used for any purpose other than that stated. Upon the expiry of the period of two years, the authentication logs shall be archived for a period of five years.
Upon the expiry of five years or the number of years required by the laws or regulations governing the entity whichever is later, the authentication logs shall be deleted except those logs which are required to be retained by a court or for pending disputes. Section 2(d)428 of the Aadhaar Act allows storage of the record of the time of authentication. These provisions permit the storage of logs of authentication transactions for a specific time period. The power-point presentation made by the CEO of UIDAI states that: “With registered devices every biometric device will have a unique identifier allowing traceability, analytics and fraud management and biometric data will be signed within the device.”
The response further indicates that UIDAI gets the AUA code, ASA code, unique device code, registered device code used for authentication, and that UIDAI would know from which device the authentication has happened and through which AUA/ASA. The response provided by the respondents states: “UIDAI does not get any information related to the IP address or the GPS location from where authentication is performed as these parameters are not the part of authentication (v2.0) and e-KYC (v2.1) API. UIDAI would only know from which device the authentication has happened, through which AUA/ASA etc. This is what the slides meant by traceability.
UIDAI does not receive any information about at what location the authentication device is deployed, its IP address and its operator and the purpose of authentication. Further, the UIDAI or any entity under its control is statutorily barred from collecting, keeping or maintaining any information about the purpose of authentication under Section 32(3) of the Aadhaar Act.” However, Regulation 26, which deals with the storage and maintenance of Authentication Transaction Data clearly provides that UIDAI shall store and maintain authentication transaction data, which shall contain the following information:
(a) authentication request data received including PID block;
(b) authentication response data sent;
(c) meta data429 related to the transaction; and
(d) any authentication server side configurations430 as necessary.
The only data, which has been excluded from retention under this provision, like Section 32(3) of the Aadhaar Act, is the purpose of authentication. Regulation 27 provides that the authentication transaction data shall be retained by UIDAI for a period of six months, and will thereafter be archived for five years, upon which, the authentication transaction data shall be deleted except when it is required to be maintained by a court or in connection with any pending dispute.
These provisions indicate that under the Aadhaar architecture, UIDAI stores authentication transaction data. This is in violation of the widely recognized data minimisation principles which seek that data collectors and processors delete personal data records when the purpose for which it has been collected is fulfilled. The lack of specification of security standards and the overall lack of transparency and inadequate grievance redressal mechanism under the Aadhaar program greatly exacerbate the overall risk associated with data retention.
In the Aadhaar regime, an Authentication User Agency (AUA) connects to the CIDR and uses Aadhaar authentication to validate a user and enable its services. The responsibility for the logistics of service delivery rests with the AUAs. In this federated model, Authentication Service Agencies (ASAs) transmit authentication requests to CIDR on behalf of one or more AUAs. However, any device that communicates via the Internet is assigned an IP address. Using the metadata related to the transaction, the location of the authentication can easily be traced using the IP address.
228 The petitioners have also brought the attention of this Court to bear on an expert report, with respect to security and Aadhaar, which was filed along with an Additional Affidavit dated 09 March 2018. The report dated 4 March 2018 is titled as “Analysis of Major Concern about Aadhaar Privacy and Security” and has been authored by Professor Manindra Agrawal. Professor Agrawal is the N Ramarao Professor at IIT Kanpur and is a member of the Technology and Architecture Review Board (TARB) and of the Security Review Committee of UIDAI. Professor Agarwal’s Report deals with the notion of differential privacy. Differential privacy makes it possible for tech entities to collect and share aggregate information about user habits, while maintaining the privacy of individual users.
The Report states that differential privacy of a protocol is the change in the privacy of people when the protocol is introduced without altering any other protocol present. If the differential privacy of a protocol is “non-negative”, the protocol does not compromise privacy in any way. There are four existing Aadhaar databases:
(i) The ‘person database’ stores personal attributes of a person (name, address, age, etc.) along with his/her Aadhaar number;
(ii) The reference database stores the Aadhaar number of a person along with a unique reference number (which has no relationship with the Aadhaar number of an individual);
(iii) The biometric database stores biometric information of a person along with the unique reference number; and
(iv) The verification log records all ID verifications done in the past five years.
For each verification, it stores the biometric data, Aadhaar number, and ID of the device on which verification was done. The report analyses the situation if any of the databases gets leaked. The report remarks: “Finally, let us turn attention to Verification Log. Its leakage may affect both the security and the privacy of an individual as one can extract identities of several people (and hence can keep changing forged identities) and also locate the places of transactions done by an individual in the past five years. Note that differential privacy of this becomes negative since without access to this database it is not possible to track locations of an individual in past five years (as opposed to tracking current location which is possible).
Therefore, Verification Log must be kept secure.” The Report underlines the importance of ensuring the security of verification logs in the Aadhaar database. The leakage of verification logs is capable of damaging the security and privacy of individuals since the report notes that from the verification log, it is possible to locate the places of transactions by an individual in the past five years. A breach in verification log would allow a third party to access the location of the transactions of an individual over the past five years. The report indicates that it is possible through the Aadhaar database to track the location of an individual. The Aadhaar database is different from other databases such as PAN Card or driving license. The Aadhaar database is universal and contains the biometrics of an individual.
The threshold to scrutinize the effects of this database is therefore much higher as compared to that of other databases.
229 In Puttaswamy, Justice Kaul (in his concurring judgment) emphasized upon the concerns regarding surveillance of individuals. The learned Judge held: “The growth and development of technology has created new instruments for the possible invasion of privacy by the State, including through surveillance, profiling and data collection and processing. Surveillance is not new, but technology has permitted surveillance in ways that are unimaginable… One such technique being adopted by States is ‘profiling’. The European Union Regulation of 2016 on data privacy defines ‘Profiling’ as any form of automated processing of personal data consisting of the use of personal data to evaluate certain personal aspects relating to a natural person, in particular to analyse or predict aspects concerning that natural person’s performance at work, economic situation, health, personal preferences, interests, reliability, behaviour, location or movements.
Such profiling can result in discrimination based on religion, ethnicity and caste.”431 Justice Kaul also dealt with the need to regulate the conduct of private entities vis-a-vis profiling of individuals: “The capacity of non-State actors to invade the home and privacy has also been enhanced. Technological development has facilitated journalism that is more intrusive than ever before…432 …[I]n this digital age, individuals are constantly generating valuable data which can be used by non-State actors to track their moves, choices and preferences.
Data is generated not just by active sharing of information, but also passively… These digital footprints and extensive data can be analyzed computationally to reveal patterns, trends, and associations, especially relating to human behavior and interactions and hence, is valuable information. This is the age of ‘big data’. The advancement in technology has created not just new forms of data, but also new methods of analysing the data and has led to the discovery of new uses for data. The algorithms are more effective and the computational power has magnified exponentially.”433
230 Section 2(c) of the Aadhaar Act is capable of revealing the identity of an individual to UIDAI. Section 2(d) permits storage of record of the time of authentication.
Through meta data and in the light of the observations made in the Professor Manindra Agarwal Report, it can easily be concluded that it is possible through the UIDAI database to track the location of an individual. Further, the verification logs reveal the details of transactions over the past five years. The verification logs are capable of profiling an individual. Details of the transaction include what the transaction was (whether authentication request was accepted/rejected), where it was sent from, and how it was sent. The only thing not stored in the transaction is its purpose.
231 The threat to privacy arises not from the positive identification that biometrics provide, but the ability of third parties to access this in an identifiable form and link it to other information, resulting in secondary use of that information without the consent of the data subject. This erodes the personal control of an individual over the uses of his or her information. The unauthorised secondary use of biometric data is perhaps the greatest risk that biometric technology poses to informational privacy.434 The Manindra Agarwal Report acknowledges that the biometric database in the CIDR is accessible by third-party vendors providing biometric search and de-duplication algorithms.
The other three databases are stored, in encrypted form, by UIDAI. In this regard, it would be necessary to deal with the Contract (dated 24 August 2010) signed between UIDAI and L1 Identity Solutions (the foreign entity which provided the source code for biometric storage). It has been submitted by the petitioners that the contract gives L1 Identity Solutions free access to all personal information about all residents in India.
The contract specifies that UIDAI (‘the purchaser’) has the right in perpetuity to use all original newly created processes “identified” by M/S L-1 Identity Solutions “solely during execution” of the contract to the purchaser’s unique specifications and which do not contain any pre-existing intellectual property right belonging to L-1 Identity Solutions.435 UIDAI was provided the license of the software (proprietary algorithms) developed by L-1 Identity Solutions.
However, it has been clarified in the Contract that: “The Contract and the licenses granted herein are not a sale of a copy of the software and do not render Purchaser the owner of M/S L-1 Identity Solutions Operating Company’s proprietary ABIS and SDK software.”436 The Contract authorises L-1 Identity Solutions to retain proprietary ownership of all intellectual property rights in and to goods, services and other deliverables to the purchaser under the Contract that are modifications or derivative works to their pre-existing technologies, software, goods, services and other works.
If a modification or derivative work made by L-1 Identity Solutions or its consortium members contains unique confidential information of the purchaser, then, the contract provides that the former shall not further license or distribute such modification or derivative to any other customer or third party other than the purchaser without the purchaser’s prior written permission.437 Clause 13.3 provides: “M/S L-1 Identity Solutions Operating Company/ The team of M/S L-1 Identity Solutions Operating Company shall ensure that while it uses any software, hardware, processes, document or material in the course of performing the Services, it does not infringe the Intellectual Property Rights of any person and M/S L-1 Identity Solutions Operating Company shall keep the Purchaser indemnified against all costs, expenses and liabilities howsoever, arising out any illegal or unauthorized use (piracy) or in connections with any claim or proceedings relating to any breach or violation of any permission/license terms or infringement of any Intellectual Property Rights by M/S L-1 Identity Solutions Operating Company or the team of M/S L-1 Identity Solutions Operating Company during the course of performance of the Services.
In case of infringement by M/S L-1 Identity Solutions Operating Company/ The team of M/S L-1 Identity Solutions Operating Company, M/S L-1 Identity Solutions Operating Company shall have sole control of the defense and all related settlement negotiations.” Clause 13.4 deals with information privacy. It provides: “M/S L-1 Identity Solutions Operating Company/ The team of M/S L-1 Identity Solutions Operating Company shall not carry any written/printed document, layout diagrams, floppy diskettes, hard disk, storage tapes, other storage devices or any other goods/material proprietary to Purchaser into/out of Datacenter Sites and UIDAI Locations without written permission from the Purchaser.” Clause 15, titled as “data and hardware”, provides:
“15.1 By virtue of this Contract, M/s L-1 Identity Solutions Operating Company/The team of M/s L-1 Identity Solutions Operating Company may have access to personal information of the Purchaser [UIDAI] and/or a third party or any resident of India, any other person covered within the ambit of any legislation as may be applicable. The purchaser shall have the sole ownership of and the right to use all such data in perpetuity including any data or other information pertaining to the residents of India that may be in the possession of M/s L-1 Identity Solutions Operating Company or the Tram of M/s L-1 Identity Solutions Operating Company in the course of performing.
15.2 The purchaser shall have the sole ownership of and the right to use, proprietary Biometric templates of residents of India as created and maintained by M/S L-1 Identity Solutions Operating Company in the course of performing the Services under this Contract. In the event of termination or expiry of contract, M/S L-1 Identity Solutions Operating Company shall transfer all the proprietary templates to UIDAI in an electronic storage media in a form that is freely retrievable for reference and usage in future. 15.3 The Data shall be retained by M/S L-1 Identity Solutions Operating Company not more than a period of 7 years as per Retention Policy of Government of India or any other policy that UIDAI may adopt in future.” Under the Contract, L-1 Identity Solutions retains the ownership of the biometric software. UIDAI has been given only the license to use the software. Neither the Central Government nor the UIDAI have the source code for the de-duplication technology which is at the heart of the programme.
The source code belongs to a foreign corporation. UIDAI is merely a licensee. It has also been provided that L-1 Identity Solutions can be given access to the database of UIDAI and the personal information of any individual. 232 This Court in Puttaswamy had emphasized on the centrality of consent in protection of data privacy: “307…Apart from safeguarding privacy, data protection regimes seek to protect the autonomy of the individual. This is evident from the emphasis in the European data protection regime on the centrality of consent. Related to the issue of consent is the requirement of transparency which requires a disclosure by the data recipient of information pertaining to data transfer and use.”
Prior to the enactment of the Aadhaar Act, an individual had no right of informed consent. Without the consent of individual citizens, UIDAI contracted with L-1 Identity Solutions to provide any information to it for the performance of the Contract. It has been provided in the Contract that L-1 Identity Solutions would indemnify UIDAI against any loss caused to it. However, the leakage of sensitive personal information of 1.2 billion citizens, cannot be remedied by a mere contractual indemnity. The loss of data is irretrievable. In a digital society, an individual has the right to protect herself by maintaining control over personal information. The protection of data of 1.2 billion citizens is a question of national security and cannot be indemnified by a Contract.
233 Mr Shyam Divan, learned senior counsel for the petitioners, has also drawn the attention of this Court to the Memorandum of Understanding (MoU) signed between UIDAI and various entities for carrying out the process of enrolment. Before the enactment of the Aadhaar Act, UIDAI existed as an executive authority, under the erstwhile Planning Commission and then under the Union Ministry of Communications and Information Technology. Mr. Divan has argued that the activities of the private parties engaged in the process of enrolment had no statutory or legal backing. It was his contention that MOUs signed between UIDAI and Registrars are not contracts within the purview of Article 299 of the Constitution, and therefore, do not cover the acts done by the private entities engaged by the Registrars for enrolment.
In Monnet Ispat and Energy Ltd v Union of India438, this Court had held:
“290. What the appellants are seeking is in a way some kind of a specific performance when there is no concluded contract between the parties. An MOU is not a contract, and not in any case within the meaning of Article 299 of the Constitution of India.”439 The MoUs entered into by UIDAI do not fall within the meaning of Article 299 of the Constitution. There is no privity of contract between UIDAI and the Enrolling agencies.
234 This Court held in Puttaswamy that any law which infringes the right to privacy of an individual needs to have stringent inbuilt safeguards against the abuse of the process. The Aadhaar Act envisages UIDAI as the sole authority for the purpose of the Act. It entrusts UIDAI with a wide canvass of functions, both administrative and adjudicatory. It performs the functions of appointing enrolling agencies, registrars and requesting entities. Currently, there are 212 Registrars and 755 enrolling agencies in different states of the country.440 Monitoring the actions of so many entities is not a task easily done. Responsibility has also been placed on UIDAI to manage and secure the central database of identity information of individuals. UIDAI is also required to ensure that data stored in CIDR is kept secure and confidential. It has been placed with the responsibility for the protection of the identity information of 1.2 billion citizens. UIDAI is entrusted with discretionary powers under the architecture of Aadhaar, including the discretion to share the personal information of any individual with the biometric service providers (BSPs) for the performance of contracts with them.
235 The proviso to Section 28(5) provides only for a request to UIDAI for access to information and does not make access to information a right of the individual. This would mean that it would be entirely upon the discretion of the UIDAI to refuse to grant access to the information once a request has been made. It is also not clear how a person is supposed to know that the biometric information contained in the database has changed if he/she does not have access to it. UIDAI is also empowered to investigate any breach under the Act, as a result of which any offence under the Act will be cognizable only if a complaint is filed by UIDAI. UIDAI is not an independent monitoring agency. Under the Aadhaar architecture, UIDAI is the only authority which carries out all the functions, be it administrative, adjudicatory, investigative, or monitoring of the project. While the Act confers such major functions on UIDAI, it does not place any institutional accountability upon UIDAI to protect the database of citizens’ personal information.
The Act is silent on the liability of UIDAI and its personnel in case of non-compliance of the provisions of the Act or the regulations made under it. Under Section 23(2)(s) of the Act, UIDAI is required to establish a grievance redressal mechanism. Making the authority administering a project, also responsible for providing for the framework to PART H 328 address grievances arising from the project, severely compromises the independence of the grievance redressal body.441 Section 47 of the Act violates the right to seek remedy. Under Section 47(1), a court can take cognizance of an offence punishable under the Act only on a complaint made by UIDAI or any officer or person authorised by it.
There is no grievance redressal mechanism if any breach or offence is committed by UIDAI itself. The law must specify who is to be held accountable. The Act lacks a mechanism through which any individual can seek speedy redressal for his/her data leakage and identity theft. Compensation must be provided for any loss of data of an individual. A stringent and independent redressal mechanism and options for compensation must be incorporated in the law. Section 47 is arbitrary as it fails to provide a mechanism to individuals to seek efficacious remedies for violation of their right to privacy. Whether it is against UIDAI or a private entity, it is critical that the individual retains the right to seek compensation and justice. This would require a carefully designed structure.442
236 An independent and autonomous authority is needed to monitor the compliance of the provisions of any statute, which infringes the privacy of an individual. A fair data protection regime requires establishment of an independent authority to deal with the contraventions of the data protection framework as well as to proactively supervise its compliance. The independent monitoring authority must be required to prescribe the standards against which compliance with the data protection norms is to be measured. It has to independently adjudicate upon disputes in relation to the contravention of the law. Data protection requires a strong regulatory framework to protect the basic rights of individuals.
The architecture of Aadhaar ought to have, but has failed to embody within the law the establishment of an independent monitoring authority (with a hierarchy of regulators), along with the broad principles for data protection.443 The principles should include that the means of collection of data are fair and lawful, the purpose and relevance is clearly defined, user limitations accompanied by intelligible consent requirements are specified and subject to safeguards against risks such as loss, unauthorised access, modification and disclosure.444
The independent authority needs to be answerable to Parliament. In the absence of a regulatory framework which provides robust safeguards for data protection, the Aadhaar Act does not pass muster against a challenge on the ground of Article 14. The law fails to meet the norms expected of a data protection regime which safeguards the data of 1.2 billion Indians. The absence of a regulatory framework leaves the law vulnerable to challenge on the ground that it has failed to meet the requirements of fair institutional governance under the rule of law.
237 The scheme of the Aadhaar Act is postulated on the norms enunciated in Chapter VI for the protection of information and their enforcement under a regime of criminal offences and penalties under Chapter VII. Providing a regime under law for penalizing criminal wrongdoing is necessary. But, criminal offences are not a panacea for a robust regulatory framework under the auspices of an autonomous regulatory body. Violations in regard to the integrity of data may be incremental.
Millions of data transactions take place in the daily lives of a community of individuals. Violations in regard to the integrity of data are numerous. Some of them may appear to be trivial, if looked at in isolation. However, cumulatively, these violations seriously encroach on the dignity and autonomy of the individual. A regime of criminal law may not in itself be adequate to deal with all these violations in terms of their volume and complexity.
It is hence necessary that the criminal law must be supplemented by an independent regulatory framework. In its absence, there is a grave danger that the regime of data protection, as well as the administration of criminal justice will be rendered dysfunctional. Unfortunately, a regulatory framework of the nature referred to above is completely absent. UIDAI which is established and controlled by the Union Government possesses neither the autonomy nor the regulatory authority to enforce the mandate of the law in regard to the protection of data. The absence of a regulatory framework renders the legislation largely ineffective in dealing with data violations. Data protection cannot be left to an unregulated market place. Nor can the law rest in the fond hope that organized structures within or outside government will be self-compliant.
The Aadhaar Act has manifestly failed in its legislative design to establish and enforce an autonomous regulatory mechanism. Absent such a mechanism, the state has failed to fulfil the obligation cast upon it to protect the individual right to informational selfdetermination. 238 Section 33(2), which permits disclosure of identity information and authentication records in the interest of national security, specifies a procedure for oversight by a committee. However, no substantive provisions have been laid down as guiding principles for the oversight mechanism such as the principle of data minimisation.
239 Privacy concerns relating to the Aadhaar project have been the subject of wide ranging deliberation. Biometric data offers strong evidence of one’s identity since it represents relatively unique biological characteristics which distinguish one person from another. As biometric data can be usually linked to only one individual it acts as a powerful, unique identifier that brings together disparate pieces of personal information about an individual.
As a relatively unique identifier, biometric data not only allows individuals to be tracked, but it also creates the potential for the collection of an individual’s information and its incorporation into a comprehensive profile. Central databases, data matching/linking and profiling are technical factors that facilitate ‘function creep’ (the slippery slope according to which information can be used for functions other than that for which it was collected). Privacy advocates believe that any identification scheme can be carried out with a hidden agenda and that the slippery slope effect can be relevant to several factors such as motivations of governments and business, and on the existence of safeguards.
The special nature of biometric data makes function creep more likely and even attractive. The legal measures possible to control function creep are still limited. However, there are several ways in which function creep can be curtailed. They include
(i) limiting the amount of data that is collected for any stated purpose;
(ii) enabling regulation to limit technological access to the system;
(iii) concerted debates with all stakeholders and public participation;
(iv) dispersion of multiple enablers for a system; and
(v) enabling choices for user participation.
240 This Court held in Puttaswamy that a reasonable expectation of privacy requires that data collection must not violate the autonomy of an individual. The Court has held consent, transparency, and control over information as the cornerstones over which the fundamentals of informational privacy stand. The Court had made it clear that an individual has the right to prevent others from using his or her image, name and other aspects of personal life and identity for commercial purposes without consent. An Aadhaar number is a unique attribute of an individual. It embodies unique information associated with an individual. The manner in which it is to be used has to be dependent on the consent of the individual.
241 Section 57 of the Aadhaar Act allows the use of an Aadhaar number for establishing the identity of an individual “for any purpose” by the state, private entities and persons. Allowing private entities to use Aadhaar numbers will lead to commercial exploitation of an individual’s personal data without his/her consent and could lead to individual profiling. The contention is that Section 57 fails to meet the requirements set out in the Puttaswamy judgment. In this regard, reference must be drawn to a 2010 policy paper. A group of officers was created by the Government of India to develop a framework for a privacy legislation that would balance the need for privacy protection with security and sectoral interests, and respond to the need for domain legislation on the subject.
An approach paper for the legal framework for a proposed legislation on privacy was prepared by the group and was uploaded on the website of the Government of India. The paper noted the repercussions of having a project based on a database of unique individual IDs: “Data privacy and the need to protect personal information is almost never a concern when data is stored in a decentralized manner. However, all this is likely to change with the implementation of the UID Project. One of the inevitable consequences of the UID Project will be that the UID Number will unify multiple databases. As more and more agencies of the government sign on to the UID Project, the UID Number will become the common thread that links all those databases together.
Over time, private enterprise could also adopt the UID Number as an identifier for the purposes of the delivery of their services or even for enrolment as a customer…Once this happens, the separation of data that currently exists between multiple databases will vanish… Such a vast interlinked public information database is unprecedented in India. It is imperative that appropriate steps be taken to protect personal data before the vast government storehouses of private data are linked up and the threat of data security breach becomes real.”445 The Paper highlighted the potential of exploitation that the UID project possessed. The potential was that the UID data could be used directly or indirectly by market forces for commercial exploitation as well as for intrusions by the State into citizens’ privacy. The Paper contained an incisive observation in regard to the exploitation of citizens’ data by private entities: “Similarly, the private sector entities such as banks, telecom companies, hospitals etc are collecting vast amount of private or personal information about individuals.
There is tremendous scope for both commercial exploitation of this information without the consent/ knowledge of the individual consent and also for embarrassing an individual whose personal particulars can be made public by any of these private entities. The IT Act does provide some safeguards against disclosure of data / information stored electronically, but there is no legislation for protecting the privacy of individuals for all information that may be available with private entities In view of the above, privacy of individual is to be protected both with reference to the actions of Government as well as private sector entities.”446 The Paper highlighted the need for a stringent privacy protection mechanism, which could prevent individual data from commercial exploitation as well as individual profiling.
242 Reference must also be drawn to Chapter V of the National Identification Authority of India Bill, 2010, which provided for the constitution of an Identity Review Committee. The proposed Committee was to be entrusted to carry out the function of ascertaining the extent and pattern of usage of Aadhaar numbers across the country. The Committee was required to prepare a report annually in relation to the extent and pattern of usage of the Aadhaar numbers along with its recommendations thereon and submit it to the Central Government. The idea behind the establishment of such a Committee was to limit the extent to which Aadhaar numbers could be used. These provisions have not been included in the Aadhaar Act, 2016.
Instead, the Act allows the use of Aadhaar number for any purpose by the State as well as private entities. This is a clear case of overbreadth and an instance of manifest arbitrariness. 243 Section 57 indicates that the legislature has travelled far beyond its stated object of ensuring targeted delivery of social welfare benefits. Allowing the Aadhaar platform for use by private entities overreaches the purpose of enacting the law. It leaves bare the commercial exploitation of citizens data even in purported exercise of contractual clauses. This will result in a violation of privacy and profiling of citizens.
An article titled “Privacy and Security of Aadhaar: A Computer Science Perspective”447 underlines the risk of profiling and identification that is possible by the use of Aadhaar numbers. It states: “The Aadhaar number is at the heart of the Aadhaar scheme and is one of the biggest causes of concern. Recall that the Aadhaar number is a single unique identifier that must function across multiple domains. Given that the Aadhaar number must necessarily be disclosed for obtaining services, it becomes publicly available, not only electronically but also often in human readable forms as well, thereby increasing the risk that service providers and other interested parties may be able to profile users across multiple service domains. Once the Aadhaar number of an individual is (inevitably) known, that individual may be identified without consent across domains, leading to multiple breaches in privacy.”
244 The risks which the use of Aadhaar “for any purpose” carries is that when it is linked with different databases (managed by the State or by private entities), the Aadhaar number becomes the central unifying feature that connects the cell phone with geo-location data, one’s presence and movement with a bank account and income tax returns, food and lifestyle consumption with medical records. This starts a “causal link” between information which was usually unconnected and was considered trivial.448 Thus, linking Aadhaar with different databases carries the potential of being profiled into a system, which could be used for commercial purposes. It also carries the capability of influencing the behavioural patterns of individuals, by affecting their privacy and liberty. Profiling individuals could be used to create co-relations between human lives, which are generally unconnected.
If the traces of Aadhaar number are left in every facet of human life, it will lead to a loss of privacy. The repercussions of profiling individuals were anticipated in 1966 by Alexander Solzhenitsyn in ‘Cancer Ward’449. His views are prescient to our age: “As every man goes through life he fills in a number of forms for the record, each containing a number of questions. A man’s answer to one question on one form becomes a little thread, permanently connecting him to the local centre of personnel records administration.
There are thus hundreds of little threads radiating from every man, millions of threads in all. If these threads were suddenly to become visible, the whole sky would look like a spider’s web, and if they materialised as elastic bands, buses, trams and even people would all lose the ability to move, and the wind would be unable to carry torn newspapers or autumn leaves along the streets of the city. They are not visible, they are not material, but every man is constantly aware of their existence… Each man, permanently aware of his own invisible threads, naturally develops a respect for the people who manipulate the threads…”
The invisible threads of a society networked on biometric data have grave portents for the future. Unless the law mandates an effective data protection framework, the quest for liberty and dignity would be as ephemeral as the wind. 245 A novelist’s vision is threatening to become a reality in our times. Profiling can impact individuals and their behaviour. Since data collection records the preferences of an individual based on the entities which requested for proof of identity, any such pattern in itself is crucial data that could be used to predict the emergence of future choices and preferences of individuals. 449 Aleksandr Solzhenitsyn, Cancer Ward,
The Bodley Head (1968) These preferences could also be used to influence the decision making of the electorate in choosing candidates for electoral offices. Such a practice would be unhealthy for the working of a democracy, where a citizen is deprived of free choice. In the modern digital era, privacy protection does not demand that data should not be collected, stored, or used, but that there should be provable guarantees that the data cannot be used for any purpose other than those that have been approved. In any of the programmes employed, it is imperative that the state takes strong data privacy measures to prevent theft and abuse. Moreover, it must be realized that an identification system like Aadhaar, which is implemented nationwide, will always be more prone to external threats.
The State is always open to threat from its adversaries, and a national level identification system can become an easy target for anyone looking to cause serious damage as individuals’ biometric credentials are at risk in the process. Therefore, it is vital that state action ascertain security vulnerabilities while developing an identification system. These issues have not been dealt with by the Aadhaar Act. There is currently limited legislative or other regulatory guidance to specify whether private or public organisations are prevented from sharing or selling biometric information to others.
Section 57 cannot be applied to permit commercial exploitation of the data of individuals or to affect their behavioural patterns. Section 57 does not pass constitutional muster. It is manifestly arbitrary, suffers from overbreadth and violates Article 14. PART H 339 246 At its core, the Aadhaar Act attempts to create a method for identification of individuals so as to provide services, subsidies and other benefits to them. The Preamble of the Act explains that the architecture of the Act seeks to provide “efficient, transparent and targeted delivery of subsidies, benefits and services” for which the expenditure is incurred from the Consolidated Fund to resident individuals. Section 7 of the Act makes the proof of possession of Aadhaar number or Aadhaar authentication as a mandatory condition for receipt of a subsidy, benefit or service, which incurs expenditure from the Consolidated Fund of India.
The scope of Section 7 is very wide. It leaves the door open for the government to route more benefits, subsidies and services through the Consolidated Fund of India and expand the scope of Aadhaar. Any activity of the government paid for from the Consolidated Fund of India ranging from supply of subsidised grains and LPG, to use of roads and civic amenities, healthcare, and even rebates to tax payers could come under such an umbrella. The scope of Section 7 could cover every basic aspect of the lives of citizens. The marginalized sections of society, who largely depend upon government’s social security schemes and other welfare programmes for survival could be denied basic living conditions because of a mismatch in biometric algorithms.
The notifications issued by government under Section 7 of the Act, which require mandatory proof of possession of an Aadhaar number or requiring authentication, cover 252 schemes, including schemes for children (such as benefits under the Sarva Shiksha Abhiyan or getting meals under the Mid-day meal scheme, painting and essay competitions for children, scholarships on merit), schemes relating to rehabilitation of bonded labour and human trafficking, scholarship schemes for SC/ST students, universal access to tuberculosis care, pensions, schemes relating to labour and employment, skill development, personnel and training, agriculture and farmers’ welfare, primary and higher education, social justice, benefits for persons with disabilities, women and child development, rural development, food distribution, healthcare, panchayati raj, chemicals & fertilizers, water resources, petroleum and natural gas, science and technology, sanitation, textiles, urban development, minority affairs, road transport, culture, tourism, urban housing, tribal affairs and stipends for internship for students. The list is ever expanding and is endless. These notifications cover a large number of facilities provided by the government to its citizens. Every conceivable facility can be brought under the rubric of Section 7.
From delivery to deliverance, almost every aspect of the cycle of life would be governed by the logic of Aadhaar. 247 When Aadhaar is seeded into every database, it becomes a bridge across discreet data silos, which allows anyone with access to this information to re-construct a profile of an individual’s life. It must be noted while Section 2(k) of the Aadhaar Act excludes storage of individual information related to race, religion, caste, tribe, ethnicity, language, income or medical history into CIDR, the mandatory linking of Aadhaar with various schemes allows the same result in effect.
For instance, when an individual from a particular caste engaged in manual scavenging is rescued and in order to take benefit of rehabilitation schemes, she/he has to link the Aadhaar number with the scheme, the effect is that a profile as that of a person engaged in manual scavenging is created in the scheme database. The stigma of being a manual scavenger gets permanently fixed to her/his identity. What the Aadhaar Act seeks to exclude specifically is done in effect by the mandatory linking of Aadhaar numbers with different databases, under cover of the delivery of benefits and services.
Moreover, the absence of proof of an Aadhaar number would render a resident non-existent in the eyes of the State, and would deny basic facilities to such residents. Section 7 thus makes a direct impact on the lives of citizens. If the requirement of Aadhaar is made mandatory for every benefit or service which the government provides, it is impossible to live in contemporary India without Aadhaar. It suffers from the vice of being overbroad. The scope of subsidies provided by the government (which incur expenditure from the Consolidated Fund) is not the same as that of other benefits and services which the government provides to its citizens.
Therefore, benefits and services cannot be measured with the same yardstick as subsidies. The inclusion of services and benefits in Section 7 is a precursor to the kind of function creep which is inconsistent with privacy and informational self-determination. The broad definitions of the expressions ‘services and ‘benefits’ would enable government to regulate almost every facet of its engagement with citizens under the Aadhaar platform. Section 7 suffers from clear overbreadth in its uncanalised application to services and benefits.
248 The open-ended nature of the provisions of Section 7 is apparent from the definition of ‘benefit’ in Section 2(f) and of ‘service’ in Section 2(w). ‘Benefit’ is defined to mean any advantage, gift, reward, relief or payment in cash or kind provided to an individual or a group of individuals. ‘Service’ is defined to mean any provision, facility, utility, or any other assistance provided in any form to an individual or a group of individuals. These are broad and unstructured terms under which the government can cover the entire gamut of its activities involving an interface with the citizen. The provision has made no requirement to determine whether in the first place biometric identification is necessary in each case and whether a less intrusive modality should suffice. Both the definitions include such other services as may be notified by the Central government.
The residuary clause is vague and ambiguous and leaves it to the Central government at its uncharted discretion to expand on what benefits and services would be covered by the legislation. The manner in which these definitions have been expansively applied to cover a wide range of activities is attributable to the vagueness implicit in Section 7. Can the provisions of Section 7 be applied with any justification to pensions payable on account of the past service rendered by a person to the state? PART H 343 Pension, it is well settled, is not a largesse or bounty conferred by the state. Pension, as a condition of service, attaches as a recompense for the long years of service rendered by an individual to the state and its instrumentalities. Pensioners grow older with passing age. Many of them suffer from the tribulations of old age including the loss of biometrics.
It is unfair and arbitrary on the part of the state to deny pension to a person entitled to it by linking pensionary payments to the possession of an Aadhaar number or to its authentication. A right cannot be denied on the anvil of requiring one and only one means of identification. The pension disbursing authority is entitled to lay down regulations (which are generally speaking, already in place) to ensure the disbursal of pension to the person who is rightfully entitled. This aim of the government can be fulfilled by other less intrusive measures. The requirement of insisting on an Aadhaar number for the payment of pensionary benefits involves a breach of the principle of proportionality. Such a requirement would clearly be contrary to the mandate of Article 14.
Similarly, the state as a part of its welfare obligations provides numerous benefits to school going children, including mid-day meals or scholarships, to children belonging to the marginalised segments of the society. Should the disbursal of these benefits be made to depend upon a young child obtaining an Aadhaar number or undergoing the process of authentication? The object of the state is to ensure that the benefits which it offers are being availed of by genuine students who are entitled to them. This legitimate aim can be fulfilled PART H 344 by adopting less intrusive measures as opposed to the mandatory enforcement of the Aadhaar scheme as the sole repository of identification.
The state has failed to demonstrate that a less intrusive measure other than biometric authentication will not subserve its purposes. That the state has been able to insist on adherence to the Aadhaar scheme without exception is a result of the overbreadth of Section 7. Consequently, the inclusion of benefits and services in Section 7 suffers from a patent ambiguity, vagueness and overbreadth which renders the inclusion of services and benefits arbitrary and violative of Article 14. 249 Various entities are involved in the Aadhaar project. Their interdependencies require a greater onus to be put on them so as to match privacy and security requirements.
The architecture of Aadhaar treats individuals as data. However, the core must be about personhood. The architecture of Aadhaar is destroyed by a lack of transparency, accountability and limitations. Safeguards for protection of individual rights ought to have been explicitly guaranteed by design and default.450 The presence of accountability and transparency within the Aadhaar architecture ought to be a necessary requirement so as to overcome the fear of the loss of privacy and liberty. Without these safeguards, the legislation and its architecture cannot pass muster under proportionality.
It is also important to highlight that identity is a vital facet of personality and hence of the right to life under Article 21 of the Constitution. Identity is essential and inalienable to human relationships and in the dealings of an individual with the State. The notion that individuals possess only one, or at the least, a dominant identity is not sound constitutional principle.
The Constitution has been adopted for a nation of plural cultures. It is accepting of diversity in every walk of life. Diversity of identity is an expression of the plurality which constitutes the essence of our social culture. Amartya Sen in ‘The Argumentative Indian’451 demonstrates the untenability of the notion that identity is exclusive. He rejects the notion of an exclusive identity as “preposterous”, observing that in different settings, individuals rely upon and assert varying identities: “Each of us invokes identities of various kinds in disparate contexts. The same person can be of Indian origin, a Parsee, a French citizen, a US resident, a woman, a poet, a vegetarian, an anthropologist, a university professor, a Christian, a bird watcher, and an avid believer in extraterrestrial life and of the propensity of alien creatures to ride around the cosmos in multicoloured UFOs.
Each of these collectivities, to all of which this person belongs, gives him or her a particular identity. They can all have relevance, depending on the context.”452 Sen’s logic, drawn from how individuals express their personalities in the real world, has a strong constitutional foundation. In the protection which it grants to a diverse set of liberties and freedoms, the Constitution allows for the assertion of different identities. The exercise of each freedom may generate a distinct identity. Combinations of freedoms are compatible with composite identities. Sen also rejects the notion that individuals “discover their identities with little room for choice”.
The support for such a notion, as he observes, comes from communitarian philosophy, according to which identity precedes choice: “As Professor Michael Sandel has explained this claim (among other communitarian claims) : ‘community describes not just what they have as fellow citizens but also what they are, not a relationship they choose (as in a voluntary association) but an attachment they discover, not merely an attribute but a constituent of their identity In this view, identity comes before reasoning and choice.”453 Sen rejects the above idea on the ground that it does not reflect a universally valid principle. Undoubtedly, some identities are ‘given’. But even here, as Sen explains, the issue is not whether an identity can be selected by an individual in all cases but whether the individual has a choice over the relative weight to be ascribed to different identities:
“The point at issue is not whether any identity whatever can be chosen (that would be an absurd claim), but whether we have choices over alternative identities or combinations of identities, and perhaps more importantly, whether we have some freedom in deciding what priority to give to the various identities that we may simultaneously have. People’s choices may be constrained by the recognition that they are, say, Jewish or Muslim, but there is still a decision to be made by them regarding what importance they give to that particular identity over others that they may also have (related, for example, to their political beliefs, sense of nationality, humanitarian commitments or professional attachments).”454 Sen reasons that identity is a plural concept and the relevance of different identities depends on the contexts in which they are asserted: “Identity is thus a quintessentially plural concept, with varying relevance of different identities in distinct contexts.
And, most importantly, we have choice over what significance to attach to our different identities. There is no escape from reasoning just because the notion of identity has been invoked. Choices over identities do involve constraints and connections, but the choices that exist and have to be made are real, not illusory. In particular, the choice of priorities between different identities, including what relative weights to attach to their respective demands, cannot be only a matter of discovery. They are inescapably decisional, and demand reason-not just recognition.”455 250 The Constitution recognizes, through the rights which it protects, a multitude of identities and the myriad forms of its expression. Our political identities as citizens define our relationship with the nation state.
The rights which the Constitution recognizes as fundamental liberties constitute a reflection of the identity of the self. As we speak, so we profess who we are. An artist who paints, the writer who shares a thought, the musician who composes, the preacher who influences our spirituality and the demagogue who launches into human sensibilities are all participants in the assertion of identity. In this participative process, the identities of both the performer and the audience are continuously engaged. Identity at a constitutional level is reflected in the entitlement of every individual, protected by its values, to lead a way of life which defines the uniqueness of our beings.
The Constitution recognizes a multitude of identities, based on the liberties which it recognizes as an inseparable part of our beings. To be human is to have a multitude of identities and be guaranteed the right to express it in various forms. The state which must abide by a written Constitution cannot require any person to forsake one or more identities. Constitutional freedoms compel the state to respect them.
251 Technologies that affect how our identities function must be subject to constitutional norms. The existence of individual identity is the core of a constitutional democracy. Addressing the Constituent Assembly on 4th November 1948, Dr B.R. Ambedkar had emphasised on the importance of individual identity in our constitutional framework: “I am glad that the Draft Constitution has… adopted the individual as its unit.”456 Having an individual identity is an important part of the human condition. The negation of identity is the loss of personhood, which in turn affects the freedom of choice and free will. Personhood constructs democracy. It represents the quality of democracy. Our decided cases have recognized the intimate relationship between human liberty and identity.
The traveller in Maneka Gandhi v Union of India457, the employee complaining of sexual harassment in Vishaka v State of Rajasthan458, the guardian of the minor in Githa Hariharan (Ms) v Reserve Bank of India459, the bar employee in Anuj Garg v Hotel Association of India460, the transgender in National Legal Services Authority v Union of India461, the tribal worker in Madhu Kishwar v State of Bihar462 and the oppressed victim of state violence in Nandini Sundar v State of Chattisgarh463 are all engaged in the assertion of identity. Puttaswamy recognizes the role of the individual as “the core of constitutional focus” and “the focal point of the Constitution”. Justice Kaul’s concurring opinion recognised that the individual has the right to control her identity.464
It was submitted by the petitioners that a unique identity number infringes the identity of the individual since it reduces every resident to a number. Ascribing to the holder of an Aadhaar card, a unique identity number must not infringe constitutional identities. The Aadhaar Act indicates, in its Statement of Objects and Reasons, that correct identification of targeted beneficiaries is necessary and that a failure to establish the identity of an individual is a major hindrance in the disbursal of welfare benefits. Section 3(1) recognizes the entitlement of every resident to obtain an Aadhaar number. Section 4(3) provides that an Aadhaar number may be accepted as proof of identity. Section 7(1) indicates that its purpose is for establishing the identity of an individual for the receipt of services, benefits or subsidies drawn from the Consolidated Fund. These provisions cannot be allowed to displace constitutional identities. Nor can the provisions of Section 7 reduce an individual to a nameless or faceless person.
252 Aadhaar is about identification and is an instrument which facilitates a proof of identity. It must not obliterate constitutional identity. The definition of demographic information in Section 2(k) excludes race, religion, caste, tribe, ethnicity, language, records of entitlement, income or medical history. However, as has been specifically discussed before, the linking of the Aadhaar number to different databases is capable of profiling an individual, which could include information regarding her/his race, religion, caste, tribe, ethnicity, language, records of entitlement, income or medical history. Thus, the impact of technology is such that the scheme of Aadhaar can reduce different constitutional identities into a single identity of a 12-digit number and infringe the right of an individual to identify herself/himself with choice. 253 Social security schemes and programmes are a medium of existence of a large segment of society.
Social security schemes in India, such as the PDS, were introduced to protect the dignity of the marginalized. Exclusion from these schemes defeats the rationale for the schemes which is to overcome chronic hunger and malnutrition. Exclusion is violative of human dignity. As discussed previously in detail, the statistics recorded in government records and the affidavits filed by the petitioners point out glaring examples of exclusion due to technical errors in Aadhaar. The authentication failures in the Aadhaar scheme have caused severe disruptions particularly in rural India. Exclusion as a consequence of biometric devices has a disproportionate impact on the lives of the marginalized and poor. This Court PART H 351 cannot turn a blind eye to the rights of the marginalized.
It may be the fashion of the day to advance the cause of a digital nation. Technology is undoubtedly an enabler. It has become a universal unifier of our age. Yet, the interface between technology and basic human rights cannot be oblivious to social reality. Compulsive linking of biometrics to constitutional entitlements should not result in denial to the impoverished. There exists a digital divide. To railroad those on one side of that divide unconcerned about social and technical constraints which operate in society is to defeat the purpose of social welfare. The Court has to be specifically conscious of the dignity of the underprivileged. The Court must fulfill its role of protecting constitutional values even if it affects a small percentage of the population. The exclusion errors in this case have led to grave injustice to the marginalized. The Court, therefore, has to play an active role in protecting their dignity.
254 The institution of rights places a heavy onus on the State to justify its restrictions. No right can be taken away on the whims and fancies of the State. The State has failed to justify its actions and to demonstrate why facilitating the targeted delivery of subsidies, which promote several rights such as the right to food for citizens, automatically entails a sacrifice of the right to privacy when both these rights are protected by the Constitution. One right cannot be taken away at the behest of the other especially when the State has been unable to satisfy this Court that the two rights are mutually exclusive.
The State has been unable to respond to the contention of the petitioners that it has failed to consider that there were much less rightsinvasive measures that could have furthered its goals. The burden of proof on the State was to demonstrate that the right to food and other entitlements provided through the Aadhaar scheme could not have been secured without the violating the fundamental rights of privacy and dignity. Dworkin in his classical book “Taking Rights Seriously”, while answering the question whether some rights are so important that the State is justified in doing all it can to maintain even if it abridges other rights, states that: “But no society that purports to recognize a variety of rights, on the ground that a man’s dignity or equality may be invaded in a variety of ways, can accept such a principle… If rights make sense, then the degrees of their importance cannot be so different that some count not at all when others are mentioned.”465
(Emphasis supplied)
255 There is no antinomy between the right to privacy and the legitimate goals of the State. An invasion of privacy has to be proportional to and carefully tailored for achieving a legitimate aim. While the right to food is an important right and its promotion is a constitutional obligation of the State, yet the right to privacy cannot simply and automatically yield to it. No legitimate goal of the State can be allowed at the cost of infringement of a fundamental right without passing the test of constitutionality. While analysing the architecture of Aadhaar, this Court has demonstrated how the purported safeguards in the Aadhaar architecture are inadequate to protect the integrity of personal data, the right of informational self-determination and above all rights attributable to the privacy-dignity-autonomy trilogy. It is also concluded that the Aadhaar scheme is capable of destroying different constitutional identities.
The financial exclusion caused due to errors in Aadhaar based authentication violate the individual’s right to dignity. The Aadhaar scheme causes an unwarranted intrusion into fundamental freedoms guaranteed under the Indian Constitution since the respondents have failed to demonstrate that these measures satisfy the test of necessity and proportionality.
H.5 Dignity and financial exclusion
256 Our jurisprudence reflects a keen awareness of the need to achieve dignity. The nine judge Bench decision in Puttaswamy also emphasized the seminal value of dignity in our constitutional scheme. Human dignity is a strengthening bond in the relationship between Parts III and IV of the Constitution. Reading the Directive Principles contained in Part IV in the context of the right to life (in Part III of the Constitution) has significant implications both for the substantive content of the right and on the ability of the state in pursuit of its positive obligation to secure conditions of a dignified existence. Dignity is an integral element of natural law and an inalienable constitutional construct.
To lead a dignified life is a constitutional assurance to an individual. Dr Ambedkar conceptualized four basic premises on which a political democracy can rest: “Political Democracy rests on four premises which may be set out in the following terms: PART H 354
(i) The individual is an end in himself.
(ii) That the individual has certain inalienable rights which must be guaranteed to him by the Constitution.
(iii) That the individual shall not be required to relinquish any of his constitutional rights as a condition precedent to the receipt of a privilege.
(iv) That the State shall not delegate powers to private persons to govern others.”466
(Emphasis supplied)
Interpreting the words of Dr Ambedkar in a constitutional context, any action on the part of the State which forces an individual to part with her or his dignity or any other right under Part III will not be permissible.
257 The experience of living with chronic hunger; recurring uncertainty about the availability of food; debt bondage; low and highly underpaid work; self-denial; and sacrifice of other survival needs, being discriminated against467 are instances of the loss of dignity for the marginalized. The State has social security programmes and legislation to improve the living conditions of the marginalized and to protect their dignity and means of livelihood. However, as documented in the works of Sainath, Dreze, Sen and other authors, India has “utterly poor standards of the social services provided to common folk, whether it is the Mid-day Meal Scheme, the Sarva Shiksha Abhiyan, Integrated Child Development Services, Public Distribution system, healthcare at the primary health centres, district hospitals and even public hospitals in the state capitals”468.
This manner of addressing the deprivations faced by the marginalized crushes their dignity. Any action or inaction on the part of the State which is insensitive to and unconcerned about protecting the dignity of the marginalized is constitutionally impermissible. Denial of benefits arising out of any social security scheme which promotes socio-economic rights of the marginalized, would not be legitimate under the Constitution, for the reason that such denial violates human dignity. No individual can be made to part with his or her dignity. Responsibility for protection of dignity lies not only with governments but also with individuals, groups and entities. It is in the above background that this Court must deal with the next contention of the petitioners.
The submission of the petitioners is that identity recognition technology may be based on a system which is deterministic or probabilistic. Biometric authentication systems work on a probabilistic model. For the purposes of authentication, a comparison is through a template which reduces the finger print to a scale and then, a minutea. The claim of the petitioners is that as a result, identities are reduced from certainty to a chance.
258 Section 7 of the Aadhaar Act makes it mandatory for an individual to undergo authentication or furnish proof of possession of an Aadhaar number in order to avail a subsidy, benefit or service, which incurs expenditure from the Consolidated Fund of India. In the Aadhaar based Biometric Authentication, the Aadhaar number and biometric information submitted by an Aadhaar number holder are matched with the biometric information stored in the CIDR.
This may be fingerprints-based or iris-based authentication or other biometric modalities based on biometric information stored in the CIDR.469 It has been submitted that failure of the authentication process results in denial of a subsidy, benefit or service contemplated under Section 7 of the Act. It has been contended that non-enrolment in the Aadhaar scheme and non-linking of the Aadhaar number with the benefit, subsidy or service causes exclusion of eligible beneficiaries. It is the submission of the petitioners that authentication of biometrics is faulty, as biometrics are probabilistic in nature. It is the case of the petitioners that Aadhaar based biometric authentication often results in errors and thus leads to exclusion of individuals from subsidies, benefits and services provided under Section 7.
Across the country, it has been urged, several persons are losing out on welfare entitlements because of a biometric mis-match. Mr Divan has argued in his written submissions, that “the project is not an ‘identity’ project but ‘identification’ exercise and unless the biometrics work, a person in flesh and blood, does not exist for the state”. In order to deal with this contention, it is necessary to understand whether biometrics authentication can result in errors in matching. People are identified by three basic means: “by something they know, something they have, or something they are”.470 Biometrics fall within the last category, and, as such, should presumably be less susceptible to being copied or forged.
However, various factors can reduce the probability of accurate human identification, and this increases the probability of a mismatch. Human fallibility can produce errors.471 259 In the United States of America, the National Academy of Science published a report in 2010 on biometrics titled “Biometric Recognition: Challenges & Opportunities”472. The report was based on a study carried out by several reputed scientists and researchers under the aegis of the National Research Council, the National Academy of Engineering and the Institute of Medicine.
This report highlights the nature of biometrics as follows: “Biometric recognition systems are inherently probabilistic and their performance needs to be assessed within the context of this fundamental and critical characteristic. Biometric recognition involves matching, within a tolerance of approximation, of observed biometric traits against previously collected data for a subject. Approximate matching is required due to the variations in biological attributes and behaviors both within and between persons.”473
(Emphasis supplied)
The report also took note of how changes in an individual’s biometrics may occur due to a number of factors: “Biometric characteristics and the information captured by biometric systems can be affected by changes in age, environment, disease, stress, occupational factors, training and prompting, intentional alterations, sociocultural aspects of the situation in which the presentations occurs, changes in human interface with the system, and so on. As a result, each interaction of the individual with the system (at enrolment, identification and so on) will be associated with different biometric information. Individuals attempting to thwart recognition for one reason or another also contribute to the inherent uncertainty in biometric systems.”474
(Emphasis supplied)
The report had also stated that biometrics can result in exclusion of people if it is used for claiming entitlement to a benefit: “When used in contexts where individuals are claiming enrollment or entitlement to a benefit, biometric systems could disenfranchise people who are unable to participate for physical, social, or cultural reasons. For these reasons, the use of biometrics-especially in applications driven by public policy, where the affected population may have little alternative to participation-merits careful oversight and public discussion to anticipate and minimize detrimental societal and individual effects and to avoid violating privacy and due process rights. Social, cultural, and legal issues can affect a system’s acceptance by users, its performance, or the decisions on whether to use it in the first place-so it is best to consider these explicitly in system design. Clearly, the behavior of those being enrolled and recognized can influence the accuracy and effectiveness of virtually any biometric system, and user behavior can be affected by the social, cultural, or legal context. Likewise, the acceptability of a biometric system depends on the social and cultural values of the participant populations.”475
(Emphasis supplied)
The report underlines that the relationship between an individual’s biometric traits and data records has the potential to cause disenfranchisement, when a section of the population is excluded from the benefits of positive claim systems. The report thus states that: “Policies and interfaces to handle error conditions such as failure to enroll or be recognized should be designed to gracefully avoid violating the dignity, privacy, or due process rights of the participants.”
(Emphasis supplied)
260 Els Kindt in a comprehensive research titled “Privacy and Data Protection Issues of Biometric Applications: A Comparative Legal Analysis”476, deals with the nature of biometrics. The book notes that error rates in biometric systems lead to a situation where entitled data subjects will be falsely rejected from the process of database matching. This will adversely affect the rights of individuals. It has been observed that: “The error rates imply also that the system will allow impostors. This is equally important because the security of biometric systems should be questioned in case of high false accept rates. This element should be given sufficient weight in the decision to implement a biometric system for security purposes… Other tests clearly indicated increased error rates for young persons, in case of aging, in particular for face and for disabled persons.
Individuals with health problems may also be falsely rejected or no longer be recognized, although they were previously enrolled. In some cases, (non-)enrolment will be a significant problem. It is clear that these data subjects need additional protection.”477 The book underlines the risk inherent in the limited accuracy of biometrics.478 261 A recently published book titled “Automating Inequality: How High- Tech Tools Profile, Police, and Punish the Poor”479, authored by Virginia Eubanks, deals with the impact of data mining, policy algorithms, and predictive risk models on economic inequality and democracy in America.
Eubanks outlines the impacts of automated decision-making on public services in the USA through three case studies relating to welfare provision, homelessness and child protection services. Eubanks looks at these three areas in three different parts of the United States: Indiana, Los Angeles and Pittsburgh, to examine what technological automation has done in determining benefits and the problems it causes. The author records that in Indiana, one million applications for health care, food stamps, and cash benefits in three years were denied, because a new authentication system interpreted any application mistake as “failure to cooperate”. In Los Angeles, an algorithm calculates the comparative vulnerability of thousands of homeless people so as to prioritize them for an inadequate pool of housing resources. In Pittsburgh, child services use an algorithm to predict future behaviour.
Statistics are used to predict which children might be future victims of abuse or neglect.
Eubanks shows how algorithms have taken over for human interaction and understanding. She has argued that automated decisionmaking is much wider in reach and is likely to have repercussions unknown to non-digital mechanisms, such as nineteenth-century poorhouses in America. Poorhouses were tax-supported residential institutions to which people were required to go if they could not support themselves.480 People who could not support themselves (and their families) were put up for bid at public auction. The person who got the contract (which was for a specific time-frame) got the use of the labour of the poor individual(s) for free in return for feeding, clothing, housing and providing health care for the individual and his/her family. The practice was a form of indentured servitude and hardly had any recourse for protection against abuse.
Eubanks considers the technology based decision-making for poverty management as the extension of the poorhouses of the 19th century: “America’s poor and working-class people have long been subject to invasive surveillance, midnight raids, and punitive public policy that increase the stigma and hardship of poverty. During the nineteenth century, they were quarantined in county poorhouses. During the twentieth century, they were investigated by caseworkers, treated like criminals on trial. Today, we have forged what I call a digital poorhouse from databases, algorithms, and risk models. It promises to eclipse the reach and repercussions of everything that came before.
Like earlier technological innovations in poverty management, digital tracking and automated decision-making hide poverty from the professional middle-class public and give the nation the ethical distance it needs to make inhuman choices: who gets food and who starves, who has housing and who remains homeless, and which families are broken by the state. The digital poorhouse is a part of a long American tradition. We manage the individual poor in order to escape our shared responsibility for eradicating poverty.”481
The author further remarks: “While poorhouses have been physically demolished, their legacy remains alive and well in the automated decisionmaking systems that encage and entrap today’s poor. For all their high-tech polish, our modern systems of poverty management – automated decision-making, data mining, and predictive analysis – retain a remarkable kinship with the poorhouses of the past. Our new digital tools spring from punitive, moralistic views of poverty and create a system of high-tech containment and investigation. The digital poorhouse deters the poor from accessing public resources; polices their labor, spending, sexuality, and parenting; tries to predict their future behavior; and punishes and criminalizes those who do not comply with its dictates. In the process, it creates ever-finer moral distinctions between the ‘deserving’ and ‘undeserving’ poor, categorizations that rationalize our national failure to care for one another.”482
(Emphasis supplied)
Eubanks builds the argument that automated decision-making technology does not act as a facilitator for welfare schemes for the poor and only acts as a gatekeeper: “New high-tech tools allow for more precise measuring and tracking, better sharing of information, and increased visibility of targeted populations. In a system dedicated to supporting poor and working-class people’s self-determination, such diligence would guarantee that they attain all the benefits they are entitled to by law. In that context, integrated data and modernized administration would not necessarily result in bad outcomes for poor communities. But automated decisionmaking in our current welfare system acts a lot like older, atavistic forms of punishment and containment. It filters and diverts.
It is a gatekeeper, not a facilitator.”483 The crux of the book is reflected in the following extract: “We all live in the digital poorhouse. We have always lived in the world we built for the poor. We create a society that has no use for the disabled or the elderly, and then are cast aside when we are hurt or grow old. We measure human worth based only on the ability to earn a wage, and suffer in a world that undervalues care and community. We base our economy on exploiting the labor of racial and ethnic minorities, and watch lasting inequities snuff out human potential.
We see the world as inevitably riven by bloody competition and are left unable to recognize the many ways we cooperate and lift each other up. But only the poor lived in the common dorms of the county poorhouse. Only the poor were put under the diagnostic microscope of scientific clarity. Today, we all live among the digital traps we have laid for the destitute.”484
(Emphasis supplied)
Automating Inequality demonstrates the problems with authentication and algorithmic technology and indicates that the system, which was intended to provide assistance for the short term and help people out of poverty, has become a system to perpetuate poverty and injustice. 262 Errors in biometrics matching imply that an individual will not be considered a part of the biometrics database. If a benefit or service is subject to the matching of biometrics, then any mismatch would result in a denial of that benefit or service. Exclusion based on technological errors, with no fault of the individual, is a violation of dignity.
The fate of individuals cannot be left to the vulnerabilities of technological algorithms or devices. ‘To live is to live with dignity’.485 Arbitrary exclusion from entitled benefits or subsidies is a violation of dignity. If any such project has to survive, then it has to be ensured that individual dignity is protected. These concerns have to be addressed. As mentioned earlier, concerns regarding the application of biometrics in the Aadhaar project were discussed in 2009 by the Biometrics Standards Committee of UIDAI486, which was of the view that the large magnitude of the Aadhaar project raised uncertainty about the accuracy of biometrics.487 The Strategy Overview488 published by UIDAI, in 2010, had discussed the risks associated with biometrics perceived by UIDAI itself.
Under the heading of ‘Project Risk’, the overview stated the UID project does face certain risks in its implementation, which have to be addressed through its architecture and in the design of its incentives. It stated: “1) Adoption Risks: There will have to be sufficient, early demand from residents for the UID number. Without critical mass among key demographic groups (the rural and the poor) the number will not be successful in the long term. To ensure this, the UIDAI will have to model de-duplication and authentication to be both effective and viable for participating agencies and service providers…
3) Enrolment Risks:
The project will have to be carefully designed to address risks of low enrolment – such as creating sufficient touch points in rural areas, enabling and motivating Registrars, ensuring that documentary requirements don’t derail enrolment in disadvantaged communities – as well as managing difficulties in address verification, name standards, lack of information on date of birth, and hard to record fingerprints.
4) Risks of Scale: The project will have to handle records that approach one billion in number. This creates significant risks in biometric de-duplication as well as in administration, storage, and continued expansion of infrastructure.
5) Technology risks: Technology is a key part of the UID program, and this is the first time in the world that storage, authentication and de-duplication of biometrics are being attempted on this scale. The authority will have to address the risks carefully – by choosing the right technology in the architecture, biometrics, and data management tools; managing obsolescence and data quality; designing the transaction services model and innovating towards the best possible result.
6) Privacy and security risks: The UIDAI will have to ensure that resident data is not shared or compromised.”489
(Emphasis supplied)
Technological error would result in authentication failures. The concerns raised by UIDAI ought to have been resolved before the implementation of the Aadhaar project. Poor connectivity in rural India was a major concern. The majority of the Indian population lives in rural areas. Even a small percentage of error results in a population of crores being affected. Denial of subsidies and benefits to them due to the infirmities of biometric technology is a threat to good governance and social parity.
263 The issue of exclusion needs to be considered at three different levels:
(i) before the implementation of the Aadhaar Act, when biometrics were being used since 2009;
(ii) under the provisions of the Act; and (iii) at the practical level during the implementation of the Aadhaar programme. Before the enactment of the Aadhaar Act in 2016, the Standing Committee on Finance, which examined the NIA Bill, was concerned about the impact of Aadhaar on marginalized sections of society. Since the availing of subsidies and benefits was to depend upon Aadhaar based authentication, any error in the authentication would result in a denial of the benefits of social security schemes for the marginalized. In 2011, the report of the Standing Committee noted, thus: “The full or near full coverage of marginalized sections for issuing Aadhaar numbers could not be achieved mainly owing to two reasons viz.
(i) the UIDAI doesn’t have the statistical data relating to them; and (ii) estimated failure of biometrics is expected to be as high as 15% due to a large chunk of population being dependent on manual labour.”490
(Emphasis supplied)
The Economic Survey 2016-17 has adverted to authentication failures while discussing the concept of Universal Basic Income (UBI). The Survey, which is an official document of the Union government, states that UBI is premised on the idea that a just society needs to guarantee to each individual a minimum income which they can count on, and which provides the necessary material foundation for a life with access to basic goods and a life of dignity.491 UBI was to be implemented by providing cash transfers (for availing benefits of social security schemes) to the bank accounts of beneficiaries. The implementation of UBI was to be undertaken through what is described as the JAM trinity: Jan-Dhan Bank Accounts, Aadhaar data and Mobile phones. However, the Survey noted that while Aadhaar is designed to solve the identification problem, it cannot solve the “targeting problem” on its own. The Survey emphasized the need to build state capacity and that “the state will still have to enhance its capacities to provide a whole range of public goods”.492 The Survey has recorded the statistics of authentication failures of Aadhaar in several regions of the country:
“While Aadhaar coverage speed has been exemplary, with over a billion Aadhaar cards being distributed, some states report authentication failures: estimates include 49 percent failure rates for Jharkhand, 6 percent for Gujarat, 5 percent for Krishna District in Andhra Pradesh and 37 percent for Rajasthan. Failure to identify genuine beneficiaries results in exclusion errors.”493 No failure rate in the provision of social welfare benefits can be regarded as acceptable. Basic entitlements in matters such as foodgrain, can brook no error. To deny food is to lead a family to destitution, malnutrition and even death. 264 A recent Office Memorandum dated 19 December 2017 issued by the Cabinet Secretariat of the Union government494 acknowledges that the Aadhaar enrolment process has not been completed and that infrastructure constraints are capable of posing difficulties in online authentication.
The Memorandum provides that those beneficiaries who do not possess Aadhaar, shall be provided a subsidy, benefit or service based on alternate identification documents as contemplated by Section 7 of the Aadhaar Act. It also requires efforts to be made to ensure that all beneficiaries are facilitated to get enrolment under the Aadhaar programme. The Memorandum creates a mechanism for availing subsidies, benefits or services in cases where Aadhaar authentication fails:
(i) Departments and Bank Branches may make provisions for IRIS scanners along with fingerprint scanners wherever feasible;
(ii) In cases of failure due to lack of connectivity, offline authentication systems such as QR code based coupons, Mobile based OTP or TOTP may be explored; and
(iii) In all cases where online authentication is not feasible, the benefit/service may be provided on the basis of possession of Aadhaar, after duly recording the transaction in a register, to be reviewed and audited periodically. The figures from the Economic Survey of India indicate that there are millions of eligible beneficiaries across India who have suffered financial exclusion. The Cabinet Secretariat has pro-actively acknowledged the need to address matters of exclusion by implementing alternate modalities, apart from those set out in Section 7.
Options (i) and (ii) above were to be implemented in future. This exercise should have been undertaken by the government in advance. Problems have to be anticipated when a project is on the drawing PART H 369 board, not after severe deprivations have been caused by the denial of social welfare benefits. 265 Exclusion of citizens from availing benefits of social security schemes because of failures or errors in Aadhaar based biometric authentication has also been documented in research studies and academic writings published by members of civil society, including Reetika Khera and Jean Dreze. Similar testimonies have been recorded in affidavits submitted before this Court by civil society activists.
Hearing the voices of civil society must be an integral part of the structural design of a project, such as Aadhaar. In the absence of a credible mechanism to receive and respond to feed-back, the state has to depend on its own personnel who may not always provide reliable and candid assessments of performance and failure. 266 ABBA (Aadhaar based biometric authentication) refers to the practice of installing a Point of Sale (PoS) machine equipped with a fingerprint reader and authenticating a person each time she accesses her entitlements.495 Dreze has stated that for successful authentication in PDS outlets, several technologies need to work simultaneously.496 These are497:
(a) Seeding of Aadhaar numbers: An eligible individual can become a beneficiary and access the PDS system only if her Aadhaar number is correctly seeded onto the PDS database and added to the household ration card;
(b) Point of Sale (PoS) machines: The process at the PDS outlet is dependent on the PoS machine. If it malfunctions, no transaction can be made. The first step in the process requires the dealer to enter the ration card number of the beneficiary’s household onto the PoS machine;
(c) Internet connection: Successful working of the PoS machine depends on internet connectivity as verification of the ration card number and the beneficiary’s biometric fingerprint is carried out over the internet;
(d) Remote Aadhaar servers: Remote Aadhaar servers verify the ration card number and initiate fingerprint authentication; and
(e) Fingerprint recognition software: The beneficiary proves her identity by submitting to fingerprint recognition in the PoS machine. Upon verification, the PoS machine indicates that the beneficiary is genuine and that foodgrains can be distributed to her household. The above procedure requires that at the time of purchase of PDS grains each month, any one person listed on the ration card needs to authenticate themselves. Similarly, for pensions, elderly persons must go to the point of delivery to authenticate themselves. Reetika Khera has observed that since ABBA on PoS machines is currently a monthly activity, so each of its
associated technologies (correct Aadhaar-seeding, mobile connectivity, electricity, functional PoS machines and UIDAI servers and fingerprint recognition) needs to work for a person to get their entitlement.498 Dreze has referred to the above procedure as “a wholly inappropriate technology for rural India”499. Network failures and other glitches routinely disable this sort of technology. Dreze has further observed that in villages with poor connectivity, it is a “recipe for chaos”500. 267 A government-commissioned sample study501 in Andhra Pradesh to ascertain the efficiency of Aadhaar-based social programmes in the case of subsidised grains indicated that technical deficiencies are depriving the poor of their access to food. The study was commissioned by the state government after it was found that 22% of the PDS beneficiaries did not take the ration in the month of May 2015.
The sample study, which covered five PDS outlets in three districts, found that half of the beneficiaries of PDS in the surveyed areas could not access their ration quota due to glitches, lack of training and mismatches linked to Aadhaar. In the survey, a majority of beneficiaries reported fingerprint mismatches and the inability of fair-price shop owners to operate point-of-sale (POS) devices correctly as major hurdles. Aadhaar numbers did not match with ration card numbers in many cases. Another survey502 of 80 households conducted in Hyderabad finds that despite the introduction of technology-intensive authentication and payment systems, a significant number of those vulnerable and dependent on Public Distribution System (PDS) for food grains are failing to realise their right to food. The survey revealed that among 80 surveyed households, 89% reported receiving full entitlements at correct prices even before the introduction of Aadhaarbased biometric authentication (ABBA). In contrast, 10% of households were excluded due to authentication failures due to reported errors with one or more of its five technological components.
268 An article titled “Aadhaar and Food Security in Jharkhand: Pain without Gain?”503, based on a household survey in rural Jharkhand, examines various issues related to compulsory ABBA for availing PDS benefits. The article notes the impact of PDS on the lives of the rural poor, who visit the ration shop every month. In “their fragile and uncertain lives”, the PDS provides a “modicum of food and economic security”. The article notes that in ABBA, the failure of authentication results in denial of food from ration shops. The household is unable to get food rations for no fault of its own.
The article comes to the conclusion that the imposition of ABBA on the PDS in Jharkhand is a case of “pain without gain”, as it has led to serious problems of exclusion (particularly for vulnerable groups such as widows, the elderly and manual workers). The article further notes that ABBA has neither failed to reduce quantity fraud (which is the main form of PDS corruption in Jharkhand), nor has it helped to address other critical shortcomings of the PDS in Jharkhand, such as the problem of missing names in ration cards, the identification of Antyodaya (poorest of the poor) households, or the arbitrary power of private dealers.
The article identifies poor internet connectivity as one of the reasons for authentication failures and eventual exclusion: “Sporadic internet connectivity is another major hurdle. Sometimes, light rain is enough to disrupt connectivity or the electricity supply. Every step in the ABBA process-ration card verification, biometric authentication, electronic upload of transactions, updating NFSA [National Food Security Act] lists and entitlements on the PoS504 [Point of Sale] machine- depends on internet connectivity. Further, even with stable connectivity, biometric authentication is not always easy. Biometric failures are especially common for two groups: the elderly, and manual labourers. Both are particularly vulnerable to food insecurity.”505
The article regards the denial of basic services to the poor due to failure of ABBA as a form of grave injustice: 504 Ibid, at page 51. The article states: “[PoS] is a handheld device installed at every PDS outlet (“ration shop”) and connected to the Internet. The list of ration cards attached to that outlet, and their respective entitlements, are stored in the PoS machine and updated every month. When a cardholder turns ups, the PoS machine first “authenticates” her by matching her fingerprints with the biometric data stored against her Aadhaar number in the Central Identities Data Repository (CIDR). The machine then generates a receipt with the person’s entitlements, which are also audible from a recorded message… The transaction details are also supposed to be entered by the dealer in the person’s ration card.” 505 Ibid, at page 55 “Imposing a technology that does not work on people who depend on it for their survival is a grave injustice.”506
(Emphasis supplied)
As we have noted in an earlier part of this judgment, even the Economic Survey of India 2016-17 found a 49% failure rate for beneficiaries in Jharkhand and 37% in Rajasthan. Those at the receiving end are the poorest of the poor. Reetika Khera looks at the impact of Aadhaar-integration with security schemes (primarily in MGNREGA, PDS and social security pensions).507 The author also discusses briefly the impact of Aadhaar on liquefied petroleum gas (LPG) subsidy and the application of Aadhaar in the mid-day meal (MDM) scheme.
In coming to its conclusions, the article has relied upon quantitative data from primary field studies, secondary data from government portals, figures obtained through queries made under the Right to Information (RTI) Act, and responses to questions in Parliament. In Khera’s words, Aadhaar is becoming a “tool of exclusion”: “Savings or exclusion? The government claimed that Aadhaar integration saved 399 crore up to 31 December 2016 (GoI 2017c). At a given level of benefits, a reduction in government expenditure in any particular transfer scheme can be on two counts: removal of ghosts and duplicates (“efficiency”); and a fall in the number of genuine beneficiaries (“shrinkage”), for instance, if they do not link their Aadhaar numbers when required.
Across welfare schemes, the government has been treating any reduction in expenditure as “savings,” even when it comes from shrinkage. This is true for SSP [social security pension] as well. For instance, in Rajasthan, pensioners were “mistakenly” recorded as dead and this was presented as Aadhaar-enabled savings (Yadav 2016f). In Jharkhand too, pensioners’ names have been deleted because they did not complete Aadhaar-seeding formalities or pensions stopped due to seeding errors (Sen 2017a). Studying 100 pensioners, selected from 10 randomlyselected villages from five blocks of Ranchi district in February 2017, Biswas (2017) finds that 84% of her respondents receive pensions but irregularity in payments was a big issue. The remaining 16% were not receiving it due to Aadhaar-related issues.”508 Puja Awasthi documents the plight of individuals suffering from leprosy, who have been denied pensions due to not being able to get enrolled into the Aadhaar system. Leprosy can damage fingerprints and thus make an individual incapable of providing biometrics. Awasthi’s article509 notes that Aadhaar is capable of causing a denial of benefits or services to 86,000 citizens, who suffer from leprosy.
These writings show how in most cases, an authentication failure means that the individual/household was denied the benefit of a social security programme for no fault of their own. Some have gone hungry. Some reportedly lost their lives.510
269 A person’s biometrics change over time. For persons, who are engaged in manual labour, and persons who are disabled or aged, fingerprints actually cannot be captured by biometric devices.
The material which has been relied upon in this segment originates from government’s official documents as well as from distinguished academics and researchers from civil society. There exist serious issues of financial exclusion. Pensions for the aged particularly in cases where a pension is earned for past service – are not charity or doles. They constitute legal entitlements. For an old age pensioner, vicissitudes of time and age obliterate fingerprints. Hard manual labour severely impacts upon fingerprints. The elderly, the disabled and the young are the most vulnerable and a denial of social welfare entitlements verily results in a deprivation of the right to life. Should the scholarship of a girl child or a midday meal for the young be made to depend on the uncertainties of biometric matches?
Our quest for technology should not be oblivious to the country’s real problems: social exclusion, impoverishment and marginalisation. The Aadhaar project suffers from crucial design flaws which impact upon its structural probity. Structural design in delivering welfare entitlements must be compliant with structural due process, to be in accord with Articles 14 and 21. The Aadhaar project has failed to account for and remedy the flaws in its framework and design which lead to serious issues of exclusion. Dignity and rights of individuals cannot be based on algorithms or probabilities. Constitutional guarantees cannot be subject to the vicissitudes of technology.
270 Structural due process imposes requirements on public institutions and projects at the macro level. Structural due process requires that the delivery of social welfare benefits must be effective and timely. Those who are eligible for the benefits must not face exclusion. Procedures for the disbursal of benefits must not be oppressive. They must be capable of compliance both by those who disburse and by those who receive the benefits. Deployment of technology must factor in the available of technological resources in every part of the coverage area and the prevailing levels of literacy and awareness.
Above all, the design of the project will be compliant with structural due process only if it is responsive to deficiencies, accountable to the beneficiaries and places the burden of ensuring that the benefits reach the marginalised on the state and its agencies.
H.6 Constitutional validity of Section 139AA of the Income Tax Act 1961
271 Section 139AA of the Income Tax Act 1961 which was inserted by the Finance Act 2017, mandates the quoting of an Aadhaar number in the application for a Permanent Account Number (PAN) and in the return of income tax. Failure to intimate an Aadhaar number results in the PAN being deemed invalid retrospectively. Section 139AA reads thus: “Quoting of Aadhaar number.-
(1) Every person who is eligible to obtain Aadhaar number shall, on or after the 1st day of July, 2017, quote Aadhaar number-
(i) in the application form for allotment of permanent account number;
(ii) in the return of income:
Provided that where the person does not possess the Aadhaar Number, the Enrolment ID of Aadhaar application form issued to him at the time of enrolment shall be quoted in the application for permanent account number or, as the case may be, in the return of income furnished by him.
(2) Every person who has been allotted permanent account number as on the 1st day of July, 2017, and who is eligible to obtain Aadhaar number, shall intimate his Aadhaar number to such authority in such form and manner as may be prescribed, on or before a date to be notified by the Central Government in the Official Gazette: Provided that in case of failure to intimate the Aadhaar number, the permanent account number allotted to the person shall be deemed to be invalid and the other provisions of this Act shall apply, as if the person had not applied for allotment of permanent account number.
(3) The provisions of this Section shall not apply to such person or class or classes of persons or any State or part of any State, as may be notified by the Central Government in this behalf, in the Official Gazette.
Explanation. – For the purposes of this section, the expressions –
(i) “Aadhaar number”, “Enrolment” and “resident” shall have the same meanings respectively assigned to them in Clauses (a), (m) and (v) of Section 2 of the Aadhaar (Targeted Delivery of Financial and other Subsidies, Benefits and Services) Act, 2016 (18 of 2016);
(ii) “Enrolment ID” means a 28 digit Enrolment Identification Number issued to a resident at the time of enrolment.”
272 In Binoy Viswam v Union of India (“Binoy Viswam”),511 a two judge Bench (consisting of Dr Justice AK Sikri and Justice Ashok Bhushan) upheld the constitutional validity of Section 139AA. Since the issue of whether privacy is a constitutionally guaranteed right was pending before a Bench of nine judges (the decision in Puttaswamy was still to be delivered), the two judge Bench did not dwell on the challenge to the legislation on the ground of privacy and under Article 21. The Bench examined other submissions based on Articles 14 and 19 and on the competence of Parliament to enact the law.
273 The decision in Binoy Viswam holds that in assessing the constitutional validity of a law, two grounds of judicial review are available: (i) The legislative competence of the law-making body which has enacted the law, over the subject of legislation; and (ii) Compliance with Part III of the Constitution, which enunciates the fundamental rights, and with the other provisions of the Constitution. Holding that a third ground of challenge – that the law in question is arbitrary – is not available, the decision in Binoy Viswam placed reliance on the enunciation of law by a three judge Bench in State of A P v McDowell & Co (Mcdowell).512 McDowell ruled that while a challenge to a statute on the ground that it violates the principle of equality under Article 14 is available, a statute cannot be invalidated on the ground that it is arbitrary:
“43…In other words, say, if an enactment is challenged as violative of Article 14, it can be struck down only if it is found that it is violative of the equality clause/equal protection clause enshrined therein… No enactment can be struck down by just saying that it is arbitrary or unreasonable. Some or other constitutional infirmity has to be found before invalidating an Act.”513 In Binoy Viswam, the two judge Bench observed that the “contours” of judicial review had been spelt out in State of Madhya Pradesh v Rakesh Kohli,514 and more recently in Rajbala v State of Haryana.515 Reiterating the same position, Binoy Viswam holds: “81.Another aspect in this context, which needs to be emphasised, is that a legislation cannot be declared unconstitutional on the ground that it is “arbitrary” inasmuch as examining as to whether a particular Act is arbitrary or not implies a value judgment and the courts do not examine the wisdom of legislative choices and, therefore, cannot undertake this exercise.”516
274 In the decision of the Constitution Bench in Shayara Bano v Union of India (“Shayara Bano”),517 Justice Rohinton Nariman speaking for himself and Justice Uday U Lalit noticed that the dictum in McDowell, to the effect that “no enactment can be struck down by just saying it is arbitrary or unreasonable” had failed to notice the judgment of the Constitution Bench in Ajay Hasia v Khalid Mujib Sehravardi (“Ajay Hasia”),518 and a three judge Bench decision in Dr K R Lakshmanan v State of T N (“Lakshmanan”).519 In Ajay Hasia, the Constitution Bench traced the evolution of the doctrine of equality beyond its origins in the doctrine of classification.
Ajay Hasia ruled that since the decision in E P Royappa v State of Tamil Nadu,520 it had been held that equality had a substantive content which, simply put, was the antithesis of arbitrariness. Consequently: “16…Wherever therefore there is arbitrariness in State action whether it be of the legislature or of the executive or of an “authority” under Article 12, Article 14 immediately springs into action and strikes down such State action. In fact, the concept of reasonableness and nonarbitrariness pervades the entire constitutional scheme and is a golden thread which runs through the whole of the fabric of the Constitution.”521
(Emphasis supplied)
The principle of arbitrariness was applied for invalidating a State law by the three judge Bench decision in Lakshmanan. It was, in this context that Justice Nariman speaking for two Judges in the Constitution Bench in Shayara Bano held that manifest arbitrariness is a component of Article 14. Hence, a law which is manifestly arbitrary would violate the fundamental right to equality: “87. The thread of reasonableness runs through the entire fundamental rights chapter. What is manifestly arbitrary is obviously unreasonable and being contrary to the rule of law, would violate Article 14. Further, there is an apparent contradiction in the three-Judge Bench decision in McDowell when it is said that a constitutional challenge can succeed on the ground that a law is “disproportionate, excessive or unreasonable”, yet such challenge would fail on the very ground of the law being “unreasonable, unnecessary or unwarranted”.
The arbitrariness doctrine when applied to legislation obviously would not involve the latter challenge but would only involve a law being disproportionate, excessive or otherwise being manifestly unreasonable. All the aforesaid grounds, therefore, do not seek to differentiate between State action in its various forms, all of which are interdicted if they fall foul of the fundamental rights guaranteed to persons and citizens in Part III of the Constitution.”522 Justice Nariman has observed that even after McDowell, challenges to the validity of legislation have been entertained on the ground of arbitrariness (Malpe Vishwanath Acharya v State of Maharashtra,523 Mardia Chemicals Ltd. v Union of India,524 State of Tamil Nadu v K Shyam Sunder,525 Andhra Pradesh Dairy Development Corporation Federation v B Narasimha Reddy526 and K T Plantation Private Limited v State of Karnataka527).
275 In Shayara Bano, Justice Nariman has adverted to the decisions which have followed McDowell including the two judge Bench decision in Binoy Viswam. These decisions, in the view of Justice Nariman, are therefore no longer good law: “99. However, in State of Bihar v. Bihar Distillery Ltd., SCC at para 22, in State of M.P. v. Rakesh Kohli, SCC at paras 17 to 19, in Rajbala v. State of Haryana, SCC at paras 53 to 65 and in Binoy Viswam v. Union of India, SCC at paras 80 to 82, McDowell was read as being an absolute bar to the use of “arbitrariness” as a tool to strike down legislation under Article 14. As has been noted by us earlier in this judgment, McDowell itself is per incuriam, not having noticed several judgments of Benches of equal or higher strength, its reasoning even otherwise being flawed.
The judgments, following McDowell are, therefore, no longer good law.”528 In the above extract, Justice Nariman has specifically held that the McDowell test which barred a challenge to a law on the ground of arbitrariness ignored a binding Constitution Bench view in Ajay Hasia and that of a three judge Bench in Lakshmanan. Moreover, the above extract from Shayara Bano disapproves of the restriction on judicial review in Binoy Viswam, which follows McDowell. Justice Kurian Joseph, in the course of his decision has specifically agreed with the view expressed by Justice Nariman: “5…However, on the pure question of law that a legislation, be it plenary or subordinate, can be challenged on the ground of arbitrariness, I agree with the illuminating exposition of law by Nariman J. I am also of the strong view that the constitutional democracy of India cannot conceive of a legislation which is arbitrary.” 276 In Puttaswamy, the judgment delivered on behalf of four Judges expressly recognized the impact of Article 14 in determining whether a law which is challenged on the ground that it violates Article 21 meets both the procedural as well as the substantive content of reasonableness.
The Court held: “291… the evolution of Article 21, since the decision in Cooper indicates two major areas of change. First, the fundamental rights are no longer regarded as isolated silos or watertight compartments. In consequence, Article 14 has been held to animate the content of Article 21. Second, the expression “procedure established by law” in Article 21 does not connote a formalistic requirement of a mere presence of procedure in enacted law.
That expression has been held to signify the content of the procedure and its quality which must be fair, just and reasonable. The mere fact that the law provides for the deprivation of life or personal liberty is not sufficient to conclude its validity and the procedure to be constitutionally valid must be fair, just and reasonable. The quality of reasonableness does not attach only to the content of the procedure which the law prescribes with reference to Article 21 but to the content of the law itself.
In other words, the requirement of Article 21 is not fulfilled only by the enactment of fair and reasonable procedure under the law and a law which does so may yet be susceptible to challenge on the ground that its content does not accord with the requirements of a valid law. The law is open to substantive challenge on the ground that it violates the fundamental right.”529 The same principle has been emphasized in the following observations: “294…Article 14, as a guarantee against arbitrariness, infuses the entirety of Article 21.
The interrelationship between the guarantee against arbitrariness and the protection of life and personal liberty operates in a multi-faceted plane. First, it ensures that the procedure for deprivation must be fair, just and reasonable. Second, Article 14 impacts both the procedure and the expression “law”. A law within the meaning of Article 21 must be consistent with the norms of fairness which originate in Article 14. As a matter of principle, once Article 14 has a connect with Article 21, norms of fairness and reasonableness would apply not only to the procedure but to the law as well.”530
277 In Binoy Viswam, the two judge Bench held that while enrolment under the Aadhaar Act is voluntary, it was legitimately open to the Parliament, while enacting Section 139AA of the Income Tax Act to make the seeding of the Aadhaar number with the PAN card mandatory. The court held that the purpose of making it mandatory under the Income Tax Act was to curb black money, money laundering and tax evasion. It was open to Parliament to do so and its legislative competence could not be questioned on that ground. The court held that the legislative purpose of unearthing black money and curbing money laundering furnished a valid nexus with the objective sought to be achieved by the law:
“105. Unearthing black money or checking money laundering is to be achieved to whatever extent possible. Various measures can be taken in this behalf. If one of the measures is introduction of Aadhaar into the tax regime, it cannot be denounced only because of the reason that the purpose would not be achieved fully. Such kind of menace, which is deep-rooted, needs to be tackled by taking multiple actions and those actions may be initiated at the same time. It is the combined effect of these actions which may yield results and each individual action considered in isolation may not be sufficient. Therefore, rationality of a particular measure cannot be challenged on the ground that it has no nexus with the objective to be achieved. of course, there is a definite objective. For this purpose alone, individual measure cannot be ridiculed.
We have already taken note of the recommendations of SIT on black money headed by Justice M.B. Shah. We have also reproduced the measures suggested by the Committee headed by Chairman, CBDT on “Measures to Tackle Black Money in India and Abroad”. They have, in no uncertain terms, suggested that one singular proof of identity of a person for entering into finance/business transactions, etc. may go a long way in curbing this foul practice. That apart, even if solitary purpose of de-duplication of PAN cards is taken into consideration, that may be sufficient to meet the second test of Article 14. It has come on record that 11.35 lakh cases of duplicate PAN or fraudulent PAN cards have already been detected and out of this 10.52 lakh cases pertain to individual assessees. Seeding of Aadhaar with PAN has certain benefits which have already been enumerated.
Furthermore, even when we address the issue of shell companies, fact remains that companies are after all floated by individuals and these individuals have to produce documents to show their identity. It was sought to be argued that persons found with duplicate/bogus PAN cards are hardly 0.4% and, therefore, there was no need to have such a provision. We cannot go by percentage figures. The absolute number of such cases is 10.52 lakhs, which figure, by no means, can be termed as miniscule, to harm the economy and create adverse effect on the nation. The respondents have argued that Aadhaar will ensure that there is no duplication of identity as biometrics will not allow that and, therefore, it may check the growth of shell companies as well.
106. Having regard to the aforesaid factors, it cannot be said that there is no nexus with the objective sought to be achieved.”531 The court observed that it was a harsh reality of our times that the benefit of welfare measures adopted by the State does not reach the segments of society for whom they are intended:
“125.1.3… However, for various reasons including corruption, actual benefit does not reach those who are supposed to receive such benefits. One of the main reasons is failure to identify these persons for lack of means by which identity could be established of such genuine needy class. Resultantly, lots of ghosts and duplicate beneficiaries are able to take undue and impermissible benefits. A former Prime Minister of this country has gone on record to say that out of one rupee spent by the Government for welfare of the downtrodden, only 15 paisa thereof actually reaches those persons for whom it is meant.
It cannot be doubted that with UID/Aadhaar much of the malaise in this field can be taken care of.”532 In this context, the court also noted that as a result of de-duplication exercises, 11.35 lakh cases of duplicate PANs / fraudulent PANs had been detected out of which 10.52 lakh cases pertained to individual assesses. The court upheld the decision of Parliament as the legislating body of seeding PANs with Aadhaar as “the best method, and the only robust method of deduplication of PAN database”.
278 The edifice of Section 139AA is based on the structure created by the Aadhaar Act. Section 139AA of the Income Tax Act 1962 is postulated on the requirement of Aadhaar having been enacted under a valid piece of legislation. The validity of the legislation seeding Aadhaar to PAN is dependent upon and cannot be segregated from the validity of the parent Aadhaar legislation. In fact, that is one of the reasons why in Binoy Viswam, the Article 21 challenge was not adjudicated upon since that was pending consideration before a larger Bench. The validity of seeding Aadhaar to PAN under Section 139AA must therefore depend upon the constitutional validity of the Aadhaar Act as it is determined by this Court. Further Rule 114B of the Income Tax Rules 1962 provides for a list of transactions for which a person must quote a PAN card number. Rule 114B requires that a person must possess a PAN card for those transactions. These are summarized below:
“Sale or purchase of a motor vehicle or vehicle, as defined in clause (28) of section 2 of the Motor Vehicles Act, 1988 (59 of 1988) which requires registration by a registering authority under Chapter IV of that Act, other than two wheeled vehicles.
Opening an account [other than a time-deposit and a Basic Savings Bank Deposit Account] with a banking company or a co-operative bank to which the Banking Regulation Act, 1949 (10 of 1949), applies (including any bank or banking institution referred to in section 51 of that Act).
Making an application to any banking company or a cooperative bank to which the Banking Regulation Act, 1949 (10 of 1949), applies (including any bank or banking institution referred to in section 51 of that Act) or to any other company or institution, for issue of a credit or debit card.
Opening of a demat account with a depository, participant, custodian of securities or any other person registered under sub-section (1A) of section 12 of the Securities and Exchange Board of India Act, 1992 (15 of 1992).
Payment to a hotel or restaurant against a bill or bills at any one time.
Payment in connection with travel to any foreign country or payment for purchase of any foreign currency at any one time.
Payment to a Mutual Fund for purchase of its units.
Payment to a company or an institution for acquiring debentures or bonds issued by it.
Payment to the Reserve Bank of India, constituted under section 3 of the Reserve Bank of India Act, 1934 (2 of 1934) for acquiring bonds issued by it.
Deposit with,-
banking company or a co-operative bank to which the Banking Regulation Act, 1949 (10 of 1949), applies (including any bank or banking institution referred to in section 51 of that Act);
Post Office.
Purchase of bank drafts or pay orders or banker’s cheques from a banking company or a co-operative bank to which the Banking Regulation Act, 1949 (10 of 1949), PART H 388 applies (including any bank or banking institution referred to in section 51 of that Act).
A time deposit with, –
a banking company or a co-operative bank to which the Banking Regulation Act, 1949 (10 of 1949), applies (including any bank or banking institution referred to in section 51 of that Act);
a Post Office;
a Nidhi referred to in section 406 of the Companies Act, 2013 (18 of 2013); or
a non-banking financial company which holds a certificate of registration under section 45-IA of the Reserve Bank of India Act, 1934 (2 of 1934), to hold or accept deposit from public.
Payment for one or more pre-paid payment instruments, as defined in the policy guidelines for issuance and operation of pre-paid payment instruments issued by Reserve Bank of India under section 18 of the Payment and Settlement Systems Act, 2007 (51 of 2007), to a banking company or a co-operative bank to which the Banking Regulation Act, 1949 (10 of 1949), applies (including any bank or banking institution referred to in section 51 of that Act) or to any other company or institution.
Payment as life insurance premium to an insurer as defined in clause (9) of section 2 of the Insurance Act, 1938 (4 of 1938).
A contract for sale or purchase of securities (other than shares) as defined in clause (h) of section 2 of the Securities Contracts (Regulation) Act, 1956 (42 of 1956).
Sale or purchase, by any person, of shares of a company not listed in a recognised stock exchange.
Sale or purchase of any immovable property.
Sale or purchase, by any person, of goods or services of any nature other than those specified above.”
The decision in Puttaswamy has recognised that protection of the interests of the revenue constitutes a legitimate state aim in the three-pronged test of proportionality. The circumstances which have been adverted to in the decision in Binoy Viswam are a sufficient indicator of the legitimate concerns of the revenue to curb tax evasion, by embarking upon a programme for deduplication of the Pan data base. A legitimate state aim does exist.
However, that in itself is not sufficient to uphold the validity of the law, which must meet the other parameters of proportionality spelt out in Puttaswamy. The explanation to Section 139AA adopts the definition of the expressions ‘Aadhaar number’, ‘enrolment’ and ‘resident’ from the parent Aadhaar legislation. The seeding of Aadhaar with Pan cards must depend for its validity on the constitutional validity of the Aadhaar legislation. Hence, besides affirming that the object of the measure in Section 139AA constitutes a legitimate state aim, the decision of this Court in regard to the validity of Aadhaar will impact upon the seeding of PAN with Aadhaar, which Section 139AA seeks to achieve.
H.7 Linking of SIM cards and Aadhaar numbers
279 In Avishek Goenka v Union of India533, a three judge Bench of this Court dealt with a public interest litigation seeking to highlight the nonobservance of norms, regulations and guidelines relating to subscriber verification by Telecom Service Providers (TSPs). The Department of Telecommunications (DoT), in the course of the proceedings, filed its instructions stating its position in regard to the verification of prepaid and postpaid mobile subscribers. While concluding the proceedings, this Court directed the constitution of an expert committee comprising of representatives of TRAI and DoT. The court mandated that the following issues should be examined by the Committee:
“(a) Whether re-verification should be undertaken by the service provider/licensee, DoT itself or any other central body?
(b) Is there any need for enhancing the penalty for violating the instructions/guidelines including sale of preactivated SIM cards?
(c) Whether delivery of SIM cards may be made by post? Which is the best mode of delivery of SIM cards to provide due verification of identity and address of a subscriber?
(d) Which of the application forms i.e. the existing one or the one now suggested by TRAI should be adopted as universal application form for purchase of a SIM card?
(e) In absence of Unique ID card, whether updating of subscriber details should be the burden of the licensee personally or could it be permitted to be carried out through an authorised representative of the licensee?
(f) In the interest of national security and the public interest, whether the database of all registered subscribers should be maintained by DoT or by the licensee and how soon the same may be made accessible to the security agencies in accordance with law?”534 In pursuance of the above directive, DoT issued instructions on the verification of new mobile subscribers on 9 August 2012. On 6 January 2016, TRAI addressed a communication to DoT recommending that the new procedure for subscriber verification was “cumbersome and resource intensive” and hence should be replaced by an Aadhaar linked e-KYC mechanism.
Following this, DoT issued a directive on 16 August 2016 to launch an Aadhaar e-KYC service across all licenced service areas for issuance of mobile connections. However, it was stated that the e-KYC process was an alternative, in addition to the existing process of issuing mobile connections to subscribers and would not be applicable for bulk, outstation and foreign customers.
280 A public interest litigation was filed before this Court under Article 32 in Lokniti Foundation v Union of India535.
The relief which claimed was that there should be a definite mobile phone subscriber verification to ensure a hundred per cent verification of subscribers. Responding to the petition, the Union Government informed this Court that DoT had launched an Aadhaar based e-KYC for issuing mobile connections on 16 August 2016, by which customers as well as point of sale agents of TSPs will be authenticated by UIDAI. A statement was made by the learned Attorney General that an effective programme for verification of prepaid connections would be devised within one year. In view of the statement of the AG, the petition was disposed of by a two judge Bench in terms of the following directions:
“5. In view of the factual position brought to our notice during the course of hearing, we are satisfied, that the prayers made in the writ petition have been substantially dealt with, and an effective process has been evolved to ensure identity verification, as well as, the addresses of all mobile phone subscribers for new subscribers. In the near future, and more particularly, within one year from today, a similar verification will be completed, in the case of existing subscribers. While complimenting the petitioner for filing the instant petition, we dispose of the same with the hope and expectation, that the undertaking given to this Court, will be taken seriously, and will be given effect to, as soon as possible.
“536 Following the decision, DoT issued a directive on 23 March 2017 to all licensees stating that a way forward had been found to implement the directions of the Supreme Court. Based on the hypothesis that this Court had directed an E-KYC verification, DoT proceeded to implement it on 23 March 2017.
281 Mr Rakesh Dwivedi, learned Senior Counsel appearing on behalf of UIDAI and the State of Gujarat supported the measure. He submitted that the licences of all TSPs are issued under Section 4 of the Indian Telegraph Act 1885.
Since the Central Government has the exclusive privilege of establishing, maintaining and working telegraphs, TSPs, it was urged, have to operate the telegraph under a license and the Central Government is entitled to impose conditions on the licensee. The instruction issued by DoT on 23 March 2017 has, it is urged, the sanction of Section 4 of the Indian Telegraph Act 1885. 282 We must at the outset note the ambit of the proceedings before this Court in Lokniti Foundation. In response to the public interest litigation, it was the Union Government which relied on its decision of 16 August 2016 to implement e-KYC verification for mobile subscribers.
The petition was disposed of since the prayers were substantially dealt with and the court perceived that an effective process had been adopted to ensure identity verification together with verification of addresses. Existing subscribers were directed to be verified in a similar manner within one year. The issue as to whether the seeding of Aadhaar with mobile SIM cards was constitutionally valid did not fall for consideration. 283 The decision to link Aadhaar numbers with SIM cards and to require e- KYC authentication of mobile subscribers has been looked upon by the Union PART H 393 government purely as a matter of efficiency of identification.
TRAI’s letter dated 6 January 2016 states that the new procedure for subscriber verification which it had adopted was “cumbersome and resource intensive”. The issue as to whether Aadhaar linked e-KYC authentication would seriously compromise the privacy of mobile subscribers did not enter into the decision making calculus. In applying the test of proportionality, the matter has to be addressed not just by determining as to whether a measure is efficient but whether it meets the test of not being disproportionate or excessive to the legitimate aim which the state seeks to pursue. TRAI and DoT do have a legitimate concern over the existence of SIM cards obtained against identities which are not genuine. But the real issue is whether the linking of Aadhaar cards is the least intrusive method of obviating the problems associated with subscriber verification.
The state cannot be oblivious to the need to protect privacy and of the dangers inherent in the utilization of the Aadhaar platform by telecom service providers. In the absence of adequate safeguards, the biometric data of mobile subscribers can be seriously compromised and exploited for commercial gain. While asserting the need for proper verification, the state cannot disregard the countervailing requirements of preserving the integrity of biometric data and the privacy of mobile phone subscribers. Nor can we accept the argument that cell phone data is so universal that one can become blasé about the dangers inherent in the revealing of biometric information.
284 The submission that a direction of this nature could have been given to TSPs under Section 4 of the Indian Telegraph Act 1885 does not answer the basic issue of its constitutional validity, which turns upon the proportionality of the measure. Having due regard to the test of proportionality which has been propounded in Puttaswamy and as elaborated in this judgment, we do not find that the decision to link Aadhaar numbers with mobile SIM cards is valid or constitutional. The mere existence of a legitimate state aim will not justify the means which are adopted. Ends do not justify means, at least as a matter of constitutional principle. For the means to be valid, they must be carefully tailored to achieve a legitimate state aim and should not be either disproportionate or excessive in their encroachment on individual liberties.
285 Mobile technology has become a ubiquitous feature of our age. Mobile phones are not just instruments to facilitate a telephone conversation. They are a storehouse of data reflecting upon personal preferences, lifestyles and individual choices. They bear upon family life, the workplace and personal intimacies. The conflation of biometric data with SIM cards is replete with grave dangers to personal autonomy. A constitution based on liberal values cannot countenance an encroachment of this nature. The decision to link Aadhaar numbers to SIM cards and to enforce a regime of e-KYC authentication clearly does not pass constitutional muster and must stand invalidated.
All TSPs shall be directed by the Union government and by TRAI to forthwith delete the biometric data and Aadhaar details of all subscribers PART I 395 within two weeks. The above data and Aadhaar details shall not be used or purveyed by any TSP or any other person or agency on their behalf for any purpose whatsoever.
I Money laundering rules
286 Parliament enacted a law on money-laundering as part of a concerted effort by the international community to deal with activities which constitute a threat to financial systems and to the integrity and sovereignty of nations. The Statement of Objects and Reasons accompanying the introduction of the Bill contains an elucidation of the reasons for the enactment: “Introduction Money-laundering poses a serious threat not only to the financial systems of countries, but also to their integrity and sovereignty.
To obviate such threats international community has taken some initiatives. It has been felt that to prevent money-laundering and connected activities a comprehensive legislation is urgently needed. To achieve this objective the Prevention of Money-laundering Bill, 1998 was introduced in the Parliament. The Bill was referred to the Standing Committee on Finance, which presented its report on 4th March 1999 to the Lok Sabha. The Central Government broadly accepted the recommendation of the Standing Committee and incorporated them in the said Bill along with some other desired changes. Statement of Objects and Reasons It is being realized, world over, that money-laundering poses a serious threat not only to the financial systems of countries, but also to their integrity and sovereignty. Some of the initiatives taken by the international community to obviate such threat are outlined below:-
(a) the United Nations Convention Against Illicit Traffic in Narcotic Drugs and Psychotropic Substances, to which India is a party, calls for prevention of laundering of proceeds of drug crimes and other connected activities and confiscation of proceeds derived from such offence.
(b) the Basle Statement of Principles, enunciated in 1989, outlined basic policies and procedures that banks should PART I 396 follow in order to assist the law enforcement agencies in tackling the problem of money laundering.
(c) the Financial Action Task Force established at the summit of seven major industrial nations, held in Paris from 14th to 16th July 1989, to examine the problem of moneylaundering has made forty recommendations, which provide the foundation material for comprehensive legislation to combat the problem of money-laundering. The recommendations were classified under various heads. Some of the important heads are-
(i) declaration of laundering of monies carried through serious crimes a criminal offence;
(ii) to work out modalities of disclosure by financial institutions regarding reportable transactions;
(iii) confiscation of the proceeds of crime; (iv) declaring money-laundering to be an extraditable offence; and
(v) promoting international co-operation in investigation of money-laundering.
(d) the Political Declaration and Global Programme of Action adopted by United Nations General Assembly by its Resolution No. S-17/2 of 23rd February 1990, inter alia, calls upon the member States to develop mechanism to prevent financial institutions from being used for laundering of drug related money and enactment of legislation to prevent such laundering.
(e) the United Nations in the Special Session on countering World Drug Problem Together concluded on the 8th to the 10th June 1998 has made another declaration regarding the need to combat money-laundering. India is a signatory to this declaration.”
287 The expressions “beneficial owner, reporting entity and intermediary” are defined respectively in clauses (fa), (wa) and (n) of the Act thus: “(fa) “beneficial owner” means an individual who ultimately owns or controls a client of a reporting entity or the person on whose behalf a transaction is being conducted and includes a person who exercises ultimate effective control over a juridical person. (wa) “reporting entity” means a banking company, financial institution, intermediary or a person carrying on a designated business or profession.
(n) “intermediary” means,-
(i) a stock-broker, sub-broker share transfer agent, banker to an issue, trustee to a trust deed, registrar to an issue,
merchant banker, underwriter, portfolio manager, investment adviser or any other intermediary associated with securities market and registered under section 12 of the Securities and Exchange Board of India Act, 1992 (15 of 1992); or
(ii) an association recognised or registered under the Forward Contracts (Regulation) Act, 1952 (74 of 1952) or any member of such association; or
(iii) intermediary registered by the Pension Fund Regulatory and Development Authority; or
(iv) a recognised stock exchange referred to in clause (f) of section 2 of the Securities Contracts (Regulation) Act, 1956 (42 of 1956).” The Prevention of Money-Laundering (Maintenance of Records) Rules 2005 were amended by the Prevention of Money-Laundering (Maintenance of Records) Second Amendment Rules 2017. By the amendment, several definitions were introduced with reference to the provisions of the Aadhaar Act. These are: “‘(aaa) “Aadhaar number” means an identification number as defined under sub-section (a) of section 2 of the Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Act, 2016; (aab) “authentication” means the process as defined under sub-section (c) of section 2 of the Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Act, 2016;
(aac) “Resident” means an individual as defined under subsection (v) of section 2 of the Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Act, 2016; (aad) “identity information” means the information as defined in sub-section (n) of section 2 of the Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Act, 2016; (aae) “e – KYC authentication facility” means an authentication facility as defined in Aadhaar (Authentication) Regulations, 2016; (aaf) “Yes/No authentication facility” means an authentication facility as defined in Aadhaar (Authentication) Regulations, 2016…”
Similarly, the expression “officially valid document” was amended to read as follows: “(d) “officially valid document” means the passport, the driving licence, the Permanent Account Number (PAN) Card, the Voter’s Identity Card issued by [Election Commission of India, job card issued by NREGA duly signed by an officer of the State Government, the letter issued by the Unique Identification Authority of India containing details of name, address and Aadhaar number or any other document as notified by the Central Government in consultation with the [Regulator]: [Provided that where simplified measures are applied for verifying the identity of the clients the following documents shall be deemed to be officially valid documents:-
(a) identity card with applicant’s Photograph issued by the Central/State Government Departments, Statutory/ Regulatory Authorities, Public Sector Undertakings, Scheduled Commercial Banks and Public Financial Institutions;
(b) letter issued by a gazette officer, with a duly attested photograph of the person].”
288 Rule 9 of the 2005 Rules requires every reporting entity to carry out client due diligence at the time of the commencement of an account-based relationship. Due diligence requires a verification of the identity of the client and a determination of whether the client is acting on behalf of a beneficial owner, who then has to be identified. Rule 9(3) defines the expression “beneficial owner” for the purpose of sub-rule 1. Rule 9(4) requires an individual client to submit an Aadhaar number. Rule 9(3) and Rule 9(4) are extracted below:
“9. Client Due Diligence.-
(1) Every reporting entity shall-
xxxxx xxxxx
(3) The beneficial owner for the purpose of sub-rule (1) shall be determined as under- (a) where the client is a company, the beneficial owner is the natural person(s), who, whether acting alone or PART I 399 together, or through one or more juridical person, has a controlling ownership interest or who exercises control through other means.
Explanation.-For the purpose of this sub-clause- 1. “Controlling ownership interest” means ownership of or entitlement to more than twenty-five per cent. of shares or capital or profits of the company;
2. “Control” shall include the right to appoint majority of the directors or to control the management or policy decisions including by virtue of their shareholding or management rights or shareholders agreements or voting agreements;
(b) where the client is a partnership firm, the beneficial owner is the natural person(s) who, whether acting alone or together, or through one or more juridical person, has I ownership of/ entitlement to more than fifteen per cent. of capital or profits of the partnership;
(c) where the client is an unincorporated association or body of individuals, the beneficial owner is the natural person(s), who, whether acting alone or together, or through one or more juridical person, has ownership of or entitlement to more than fifteen per cent. of the property or capital or profits of such association or body of individuals;
(d) where no natural person is identified under (a) or (b) or (c) above, the beneficial owner is the relevant natural person who holds the position of senior managing official;
(e) where the client is a trust, the identification of beneficial owner(s) shall include identification of the author of the trust, the trustee, the beneficiaries with fifteen per cent. or more interest in the trust and any other natural person exercising ultimate effective control over the trust through a chain of control or ownership; and
(f) where the client or the owner of the controlling interest is a company listed on a stock exchange, or is a subsidiary of such a company, it is not necessary to identify and verify the identity of any shareholder or beneficial owner of such companies.
(4) Where the client is an individual, who is eligible to be enrolled for an Aadhaar number, he shall for the purpose of sub-rule (1) submit to the reporting entity, –
(a) the Aadhaar number issued by the Unique Identification Authority of India; and
(b) the Permanent Account Number or Form No. 60 as defined in Income-tax Rules, 1962, and such other documents including in respect of the nature of business and financial status of the client as may be required by the reporting entity:
Provided that where an Aadhaar number has not been assigned to a client, the client shall furnish proof of application of enrolment for Aadhaar and in case the PART I 400 Permanent Account Number is not submitted, one certified copy of an ‘officially valid document’ shall be submitted. Provided further that photograph need not be submitted by a client falling under clause (b) of sub-rule (1).”
(Emphasis supplied)
Sub-rule 15 of Rule 9 requires the reporting entity to carry out authentication at the time of receipt of the Aadhaar number: “(15) Any reporting entity, at the time of receipt of the Aadhaar number under provisions of this rule, shall carry out authentication using either e-KYC authentication facility or Yes/No authentication facility provided by Unique Identification Authority of India.” Sub-rule 17 allows a period of six months for a client who is eligible to be enrolled for Aadhaar and to obtain a PAN to submit it upon the commencement of the account-based relationship. Failure to do so, would result in the account ceasing to be operational until the Aadhaar number and PAN are submitted. Clauses a and c of sub-rule 17 provide as follows :
“(17) (a) In case the client, eligible to be enrolled for Aadhaar and obtain a Permanent Account Number, referred to in subrules (4) to (9) of rule 9 does not submit the Aadhaar number or the Permanent Account Number at the time of commencement of an account based relationship with a reporting entity, the client shall submit the same within a period of six months from the date of the commencement of the account based relationship: Provided that the clients, eligible to be enrolled for Aadhaar and obtain the Permanent Account Number, already having an account based relationship with reporting entities prior to date of this notification, the client shall submit the Aadhaar number and Permanent Account Number by 31st December, 2017.
(c) In case the client fails to submit the Aadhaar number and Permanent Account Number within the aforesaid six months period, the said account shall cease to be operational till the time the Aadhaar number and Permanent Account Number is submitted by the client:
Provided that in case client already having an account based relationship with reporting entities prior to date of this notification fails to submit the Aadhaar number and Permanent Account Number by 31st December, 2017, the said account shall cease to be operational till the time the Aadhaar number and Permanent Account Number is submitted by the client.” 289 The statutory mandate for the framing these rules is contained in Sections 12, 15 and 73 of the PMLA. Insofar as is material, Section 12 provides as follows:
“12. Reporting entity to maintain records:-
(1) Every reporting entity shall-
(a) maintain a record of all transactions, including information relating to transactions covered under clause (b), in such manner as to enable it to reconstruct individual transactions;
(b) furnish to the Director within such time as may be prescribed, information relating to such transactions, whether attempted or executed, the nature and value of which may be prescribed;
(c) verify the identity of its clients in such manner and subject to such conditions, as may be prescribed;
(d) identify the beneficial owner, if any, of such of its clients, as may be prescribed;
(e) maintain record of documents evidencing identity of its clients and beneficial owners as well as account files and business correspondence relating to its clients.
(2) Every information maintained, furnished or verified, save as otherwise provided under any law for the time being in force, shall be kept confidential.
(3) The records referred to in clause (a) of sub-section (1) shall be maintained for a period of five years from the date of transaction between a client and the reporting entity.
(4) The records referred to in clause (e) of sub-section (1) shall be maintained for a period of five years after the business relationship between a client and the reporting entity has ended or the account has been close, whichever is later.
(5) The Central Government may, by notification, exempt any reporting entity or class of reporting entities from any obligation under this Chapter.”
(Emphasis supplied)
Section 12 imposes a statutory obligation on reporting entities to maintain records and to verify the identity of their clients and beneficial owners in the manner prescribed. The procedure for and manner in which information is furnished by reporting entities is specified under sub-section 1 of Section 12 by the Central Government in consultation with the Reserve Bank of India. Section 15 provides as follows:
“15. Procedure and manner of furnishing information by reporting entities:- The Central Government may, in consultation with the Reserve Bank of India, prescribe the procedure and the manner of maintaining and furnishing information by a reporting entity under sub-section (1) of Section 12 for the purpose of implementing the provisions of this Act.”
(Emphasis supplied)
The rule making power is referable to the provisions of Section 73, which insofar as is material, provides as follows:
“73. Power to make rules-
(1) The Central Government may, by notification, make rules for carrying out the provisos of this Act.
(2) In particular, and without prejudice to the generality of the foregoing power, such rules may provide for all or any of the following matters, namely-
(j) the manner and the conditions in which identity of clients shall be verified by the reporting entities under clause (c) of sub-section (1) of Section 12; (jj) the manner of identifying beneficial owner, if any, from the clients by the reporting entities under clause (d) of sub-section (1) of Section 12;
(k) the procedure and the manner of maintaining and furnishing information under sub-section (1) of Section 12 as required under Section 15;
(x) any other matter which is required to be, or may be, prescribed.” Section 12(1)(c) requires the reporting entity to verify the identity of its clients “in such manner and subject to such conditions” as may be prescribed. The PART I 403 provisions of the rules, including sub-rule 17(c) of Rule 9 have been challenged on the ground that they suffer from the vice of excessive delegation.
290 In Bombay Dyeing and Mfg v Bombay Environmental Action Group537, this Court has re-affirmed the well-settled legal test which determines the validity of delegated legislation. The court held: “104…By reason of any legislation, whether enacted by the legislature or by way of subordinate legislation, the State gives effect to its legislative policy. Such legislation, however, must not be ultra vires the Constitution.
A subordinate legislation apart from being intra vires the Constitution, should not also be ultra vires the parent Act under which it has been made. A subordinate legislation, it is trite, must be reasonable and in consonance with the legislative policy as also give effect to the purport and object of the Act and in good faith.” The essential legislative function consists in the determination of legislative policy and of formally enacting it into a binding rule of conduct. Once this is carried out by the legislature, ancillary or subordinate functions can be delegated. Having laid down legislative policy, the legislation may confer discretion on the executive to work out the details in the exercise of the rule making power, though, in a manner consistent with the plenary enactment (J K Industries Ltd v Union of India538).
291 The Reserve Bank of India had issued a Master Circular dated 25 February 2016 in exercise of its statutory powers under Section 35A of the Banking Regulation Act 1949 (read with Section 56) and Rule 9(14) of the Prevention of Money-Laundering (Maintenance of Records) Rules 2005. Following the amendment of the PMLA Rules, the Master Circular of the Reserve Bank has been updated on 20 April 2018. The basic issue which needs to be addressed is whether the amendments which were brought about to the PMLA Rules in 2017 meet the test of proportionality.
292 In 2005, the Central Government in consultation with the Reserve Bank of India notified the Prevention of Money-Laundering (Maintenance of Records) Rules 2005 under Section 73 of the parent Act. The expression ‘officially valid document’ was defined in Rule 2(d) in the following terms : “(d) “officially valid document” means the passport, the driving licence, the Permanent Account Number (PAN) Card, the Voter’s Identity Card issued by539 [Election Commission of India, job card issued by NREGA duly signed by an officer of the State Government, the letter issued by the Unique Identification Authority of India540 [or the National Population Register] containing details of name, address and Aadhaar number or any other document as notified by the Central Government in consultation with the [Regulator];” Rule 9(4) required the submission to the reporting entity, where the client is an individual, a certified copy of an officially valid document containing details of identity and address. Rule 9(4) read as follows :
“(4) Where the client is an individual, he shall for the purpose of sub-rule (1), submit to the reporting entity, one certified copy of an “officially valid document” containing details of his identity and address, one recent photograph and such other documents including in respect of the nature of business and financial status of the client as may be required by the reporting entity:” Under Rule 9(14), the regulator was empowered to issue guidelines, in terms of the provisions of the rule, and to prescribe enhanced or simplified measures to verify the identity of a client, taking into consideration the type of client, business relationship, and the nature and value of transactions based on the overall money-laundering and terrorist financing risks involved. Under the above rules there were six ‘officially valid documents’ : the passport, driving licence, Permanent Account Number (PAN) Card, NREGA job card, Voter’s Identity Card and a letter of UIDAI containing details of name, address and details of Aadhaar number. or any other document notified by the Central Government in consultation with the Regulator.
293 In the Master Circular issued by the Reserve Bank of India on 25 February 2016, a provision was made for the submission by customers, at their option, of one of the six officially valid documents (OVDs) for proof of identity and address. Rule 3(vi) defined the expression ‘officially valid document’ in similar terms: “(vi) “officially valid document” means the passport, the driving licence, the Permanent Account Number (PAN) Card, the Voter’s Identity Card issued by the Election Commission of India, job card issued by NREGA duly signed by an officer of the State Government, letter issued by the Unique Identification Authority of India containing details of name, address and Aadhaar number.
Explanation: Customers, at their option, shall submit one of the six OVDs for proof of identity and proof of address.” Customer due diligence and on-going due diligence were defined thus: “Customer Due Diligence (CDD)” means indemnifying and verifying the customer and the beneficial owner using ‘Officially Valid Documents’ as a ‘proof of identity’ and a ‘proof of address’. “On-going Due Diligence” means regular monitoring of transactions in accounts to ensure that they are consistent with the customers’ profile and source of funds.”
294 Chapter III of the Master Circular provided for regulated entities (including banks) to specify a customer acceptance policy. Clause 15 of the Master Circular inter alia specified that customers shall not be required to furnish additional OVDs if the OVD already submitted, contained both proof of identity and address. Chapter VI which provided for a due diligence procedure allowed customers to submit one of the six OVDs for proof of identity and address. Under Part V of Chapter VI, banks were required to conduct ongoing due diligence particularly in regard to large and complex transactions above a threshold. Clause 39 of the Circular provided for a partial freezing and closure of accounts:
“39. Partial freezing and closure of accounts
(a) Where REs are unable to comply with the CDD requirements mentioned at Part I to V above, they shall not open accounts, commence business relations or perform transactions. In case of existing business relationship which is not KYC compliant, banks shall ordinarily take step to terminate the existing business relationship after giving due notice.
(b) As an exception to the Rule, banks shall have an option to choose not to terminate business relationship straight away and instead opt for a phased closure of operations in this account as explained below:
i. The option of ‘partial freezing’ shall be exercise after giving due notice of three months to the customers to comply with KYC requirements.
ii. A reminder giving a further period of three months shall also be given. iii. Thereafter, ‘partial freezing’ shall be imposed by allowing credits and disallowing all debits with the freedom to close the accounts in case of the account being KYC non-compliant after six months of issue first notice.
iv. All debits and credits from/to the accounts shall be disallowed, in case of the account being KYC noncompliant after six months of imposing ‘partial freezing’,
v. The account holders shall have the option, to revive their accounts by submitting the KYC documents. (c) When an account is closed whether without ‘partial freezing’ or after ‘partial freezing’, the reason for that shall be communicated to account holder.” Chapter VIII provided for reporting requirements to the Financial Intelligence Unit. Chapter IX dealt with compliance with requirements/obligations under international agreements.
Clause 58 of Chapter X stipulated reporting requirements under the Foreign Account Tax Compliance Act (FATCA) and Common Reporting Standards (CRS). 295 As a result of the amendment to the Rules brought about in 2017, Rule 9(4) mandates that in the case of a client who is an individual, who is eligible to be enrolled for an Aadhaar number, submission of the Aadhaar number is mandatory. Instead of furnishing an option to submit one of six OVDs, submission of Aadhaar number alone is mandated. Where an Aadhaar number has not been assigned, proof of an application for enrolment is required to be submitted. Under Rule 9(15), the reporting entity at the time of receipt of an Aadhaar number is under an obligation to carry out authentication using either the e-KYC authentication facility or the yes/no authentication provided by UIDAI.
If a client who is eligible to be enrolled for Aadhaar and to obtain a PAN card does not submit its details while commencing an account based relationship, there is a period of six months reserved for submission. Those who already have accounts are required to submit their Aadhaar numbers by a stipulated date. Failure to do so, renders the account subject to the consequence that it shall cease to be operational until compliance is effected. Following the amendments to the rules, the Reserve Bank has updated its Master Circular on 20 April 2018 to bring it into conformity with the amended rules. 296 In deciding whether the amendment brought about in 2017 to the rules is valid, it is necessary to bear in mind what has already been set out earlier on the aspect of proportionality.
Does the requirement of the submission or linking of an Aadhaar number to every account- based relationship satisfy the test of proportionality? The state has a legitimate aim in preventing money-laundering. In fact, it is with a view to curb and deal with money-laundering that the original version of the Master Circular as well as its updated version impose conditions for initial and on-going due diligence. The Reserve Bank has introduced several reporting requirements including those required to comply with FATCA norms.
The existence of a legitimate state aim satisfies only one element of proportionality. In its submissions, the Union government has dealt only with legitimate aim, leaving the other elements of proportionality unanswered. Requiring every client in an account based relationship to link the Aadhaar number with a bank account and to impose an authentication requirement, is excessive to the aim and object of the state. There can be no presumption that all existing account holders as well as every individual who seeks to open an account in future is a likely money-launderer. The type of client, the nature of the business relationship, the nature and value of the transactions and the terrorism and laundering risks involved may furnish a basis for distinguishing between cases and clients.
The rules also fail to make a distinction between opening an account and operating an account. If an account has been opened in the past, it would be on the basis of an established identity. The consequences of the non-submission of an Aadhaar number are draconian. Non-submission within the stipulated period will result in a consequence of the account ceasing to be operational. A perfectly genuine customer who is involved in no wrongdoing would be deprived of the use of the moneys and investments reflected in the account, in violation of Article 300A of the Constitution purely on an assumption that he or she has indulged in moneylaundering. The classification is over-inclusive: a uniform requirement of such a nature cannot be imposed on every account based relationship irrespective of the risks involved to the financial system.
The account of a pensioner or of a salaried wage earner cannot be termed with the same brush as a high networth individual with cross-border inflows and outflows. Treating every account holder with a highly intrusive norm suffers from manifest arbitrariness. Moreover, there is no specific provision in the Act warranting a consequence of an account holder being deprived of the moneys standing in the account, even if for a temporary period. Section 12(1)(c) empowers a reporting entity to verify the entity or its client in such a manner and “subject to such conditions” as may be prescribed.
This does not envisage a consequence of an account ceasing to be operational. Blocking an account is a deprivation of property under Article 300A. The Union Government has been unable to discharge the burden of establishing that this was the least intrusive means of achieving its aim to prevent money-laundering or that its object would have been defeated if it were not to impose the requirement of a compulsory linking of Aadhaar numbers with all account based relationships with the reporting entity. Money-laundering is indeed a serious matter and the Union Government is entitled to take necessary steps including by classifying transactions and sources which give rise to reasonable grounds for suspecting a violation of law.
But, to impose a uniform requirement of linking Aadhaar numbers with all account based relationships is clearly disproportionate and excessive. It fails to meet the test of proportionality and suffers from manifest arbitrariness. While we have come to the above conclusion, we clarify that this would not preclude the Union Government in the exercise of its rule making PART J 411 power and the Reserve Bank of India as the regulator to re-design the requirements in a manner that would ensure due fulfillment of the object of preventing money-laundering, subject to compliance with the principles of proportionality as outlined in this judgment.
J Savings in Section 59
297 Section 59 of the Aadhaar Act provides: “Anything done or any action taken by the Central Government under the Resolution of the Government of India, Planning Commission bearing notification number A- 43011/02/2009-Admin.
I, dated the 28th January, 2009, or by the Department of Electronics and Information Technology under the Cabinet Secretariat Notification bearing notification number S.O. 2492(E), dated the 12th September, 2015, as the case may be, shall be deemed to have been validly done or taken under this Act.”
298 The petitioners have submitted that all acts done pursuant to the Notifications dated 28 January 2009 and 12 September 2015, under which the Aadhaar programme was created and implemented, violate fundamental rights and were not supported by the authority of law.
It has been submitted that the collection, storage and use of personal data by the State and private entities, which was done in a legislative vacuum as the State failed to enact the Aadhaar Act for six years, is now being sought to be validated by Section 59. It has been contended that since the acts done prior to the enactment of the Aadhaar Act are in breach of fundamental rights, Section 59 is invalid. Moreover, Section 59 does not operate to validate the collection of biometric data prior to the enforcement of the Aadhaar Act.
It has been submitted that a validating law must remove the cause of invalidity of previous acts: it would not be effective if it simply deems a legal consequence without amending the law from which the consequence could follow. In the present case, it has been contended, Section 59 does not create a legal fiction where the Aadhaar Act is deemed to have been in existence since 2009 and that it only declares a legal consequence of the acts done by the Union since 2009. It has also been submitted that Section 59 is invalid and unconstitutional inasmuch as for Aadhaar enrolments done before 2016, there was neither informed consent nor were any procedural guarantees and safeguards provided under a legal framework. Section 59, it is contended, cannot cure the absence of consent and other procedural safeguards, provided under the Aadhaar Act, to the enrolments done prior to the enactment of the Act.
299 The respondents have submitted that Section 59 protects the actions taken by the Central government. It does not contemplate the maintenance of any data base, containing identity information, by the State governments. The State governments, it is urged, have destroyed the biometric data collected during Aadhaar enrolments before the Act came into force, from their server. It has been contended that Section 59 is retrospective in nature as it states that it shall operate from an earlier date.
The Respondents have relied upon the judgments of this Court in West Ramnad Electric Distribution Co. Ltd. v State of Madras541 (“West Ramnad”), State of Mysore v D. Achiah Chetty, Etc542 (“Chetty”), and Hari Singh v Military Estate Officer543 (“Hari Singh”) to contend that the legislature can, by retrospective operation, cure the invalidity of actions taken under a law which is void for violating fundamental rights. It has also been contended that before the advent of the Aadhaar Act, no individual has been enrolled under compulsion, and since all enrolments were voluntary, they cannot be considered to be in breach of Article 21 or any other fundamental right.
It is further submitted that non-adjudication of the issue of whether collection of identity information violates the right to privacy, does not prevent the Parliament from enacting a validating clause. Reliance has also been placed on State of Karnataka v State of Tamil Nadu544 to submit that Section 59 creates a deemed fiction as a result of which one has to imagine that all actions taken under the notifications were taken under the Act. 300 Section 7 provides that the Central Government or the State Governments may require proof of an Aadhaar number as a necessary condition for availing a subsidy, benefit or service for which the expenditure is incurred from the Consolidated Fund of India. Section 3 provides that the Aadhaar number shall consist of demographic and biometric information of an individual. “Biometric information”, under Section 2(g), means a photograph, finger print, Iris scan, or such other biological attributes of an individual as may be specified by regulations. Section 4(3) provides that an Aadhaar number may be used as a proof of identity “for any purpose”. Section 57 authorizes a body corporate or person to use the Aadhaar number for establishing the identity of an individual “for any purpose”.
The proviso to Section 57 provides that the use of an Aadhaar number under the Section shall be subject to the procedure and obligations under Section 8 and Chapter VI of the Act. Section 8 sets out the procedure for authentication. It states that for authentication, a requesting entity shall obtain the consent of an individual before collecting identity information and shall ensure that the identity information is only used for submission to the Central Identities Data Repository for authentication. It does not envisage collection of identity information for any other purpose. Chapter VI of the Act, which deals with protection of information, provides for security and confidentiality of identity information collected under the Act, imposes restrictions on sharing that information and classifies biometrics as sensitive personal information.
301 The scheme of the Aadhaar Act creates a system of identification through authentication of biometric information and authorises the Central and State governments to assign the task of collecting individual biometric information for the purpose of generation of Aadhaar numbers to private entities. The Act authorises the use of Aadhaar numbers by the Central PART J 415 government, state governments and the private entities for establishing the identity of a resident for any purpose. The Act also contains certain safeguards regarding storage and use of biometric information. The actions taken before the enactment of the Aadhaar Act have to be tested upon the touchstone of the legal framework provided under the Act.
302 Section 59 is a validating provision. It seeks to validate all the actions of the Central Government prior to the Aadhaar Act, which were done under the notifications of 28 January 2009 and 12 September 2015. Section 59 does not validate actions of the state governments or of private entities. Acts undertaken by the State governments and by private entities are not saved by Section 59.
303 The Planning Commission’s notification dated 28 January 2009 created UIDAI, while giving it the responsibility of laying down a plan and policies to implement a unique identity (UID) scheme. UIDAI was only authorized to own and operate the UID database, with a further responsibility for the updation and maintenance of the database on an ongoing basis. Significantly, the 2009 notification did not contain any reference to the use of biometrics for the purpose of the generation of Aadhaar numbers. The notification gave no authority to collect biometrics. Biometrics, finger prints or iris scans were not within its purview. There was no mention of the safeguards and measures relating to the persons or entities who would collect biometric data, how the
416 data would be collected and how it would be used. The website of the Press Information Bureau of the Government of India states that, by the time Aadhaar Act was notified by the Central government, UIDAI had generated about 100 crore Aadhaar numbers.545 The collection of biometrics from individuals prior to the enactment of the Aadhaar Act does not fall within the scope of the 2009 notification. Having failed to specify finger prints and iris scans in the notification, the validating provision does not extend to the collection of biometric data before the Act. The 2009 notification did not provide authority to any government department or to any entity to collect biometrics.
Since the collection of biometrics was not authorised by the 2009 notification, Section 59 of the Aadhaar Act does not validate these actions. 304 The collection of the biometrics of individuals impacts their privacy and dignity. Informed consent is crucial to the validity of a state mandated measure to collect biometric data. Encroachment on a fundamental right requires the enacting of a valid law by the legislature.546 The law will be valid only if it meets the requirements of permissible restrictions relating to each of the fundamental rights on which there is an encroachment. Privacy animates Part III of the Constitution.547 The invasion of any right flowing from privacy places a heavy onus upon the State to justify its actions. Nine judges of this Court in Puttaswamy categorically held that there must be a valid law in existence to encroach upon the right to privacy. An executive notification does not satisfy the requirement of a valid law contemplated in Puttaswamy. A valid law, in this case, would mean a law enacted by Parliament, which is just, fair and reasonable. Any encroachment upon the fundamental right to privacy cannot be sustained by an executive notification.
There is also no merit in the submission of the Respondents that prior to the enactment of the Aadhaar Act, no individual has been enrolled under compulsion, and since all enrolments were voluntary, these cannot be considered to be in breach of Article 21 or any other fundamental right. The format of the first two enrolment forms used by UIDAI, under which around 90 crore enrolments were done, had no mention of informed consent or the use of biometrics. Hence, this submission is rejected.
Apart from the existence of a valid law which authorises an invasion of privacy, Puttaswamy requires that the law must have adequate safeguards for the collection and storage of personal data. Data protection, which is intrinsic to privacy, seeks to protect the autonomy of the individual. The judgment noted the centrality of consent in a data protection regime. The Aadhaar Act provides certain safeguards in Section 3(2) and Section 8(3) for the purposes of ensuring informed consent, and in terms of Section 29 read with Chapter VII in the form of penalties.
The safeguards provided under the Act were not in existence before the enactment of the Act. The collection of biometrics after the 2009 notification and prior to the Aadhaar Act suffers from the absence of adequate safeguards. While a legislature has the power to legislate retrospectively, it cannot retrospectively create a deeming fiction about the existence of safeguards in the past to justify an encroachment on a fundamental right. At the time when the enrolments took place prior to the enactment of the Aadhaar Act in September 2016, there was an absence of adequate safeguards.
Section 59 cannot by a deeming fiction, as it were, extend the safeguards provided under the Act to the enrolments done earlier. This will be impermissible simply because the informed consent of those individuals, whose Aadhaar numbers were generated in that period cannot be retrospectively legislated by an assumption of law. Moreover, it is a principle of criminal law that it cannot be applied retrospectively to acts which were not offences at the time when they took place.
Article 20(1) of the Constitution provides that “No person shall be convicted of any offence except for violation of the law in force at the time of the commission of the act charged as an offence”. The application of the criminal provisions of the Act, provided under Chapter VII of the Act which deals with “Offences and Penalties”, cannot be extended to the period prior to the enactment of the Aadhaar Act. 305 The Respondents submit that the collection of biometrics prior to the Aadhaar Act was adequately safeguarded by the provisions of the Information PART J 419 Technology Act 2000; specifically those provisions, which were inserted or amended by the Information Technology (Amendment) Act, 2008. Section 43A of the Act provides for compensation for failure to protect data:
“Where a body corporate, possessing, dealing or handling any sensitive personal data or information in a computer resource which it owns, controls or operates, is negligent in implementing and maintaining reasonable security practices and procedures and thereby causes wrongful loss or wrongful gain to any person, such body corporate shall be liable to pay damages by way of compensation to the person so affected. Explanation: For the purposes of this section,-
(i) “body corporate” means any company and includes a firm, sole proprietorship or other association of individuals engaged in commercial or professional activities;
(ii) “reasonable security practices and procedures” means security practices and procedures designed to protect such information from unauthorised access, damage, use, modification, disclosure or impairment, as may be specified in an agreement between the parties or as may be specified in any law for the time being in force and in the absence of such agreement or any law, such reasonable security practices and procedures, as may be prescribed by the Central Government in consultation with such professional bodies or associations as it may deem fit.
(iii) “sensitive personal data or information” means such personal information as may be prescribed by the Central Government in consultation with such professional bodies or associations as it may deem fit.”
(Emphasis supplied)
306 Rule 3 of the Information Technology (Reasonable Security Practices and Procedures and Sensitive Personal Data or Information) Rules, 2011 made by the Central government under Section 43A, defines “sensitive personal data or information”: “Sensitive personal data or information of a person means such personal information which consists of information relating to;-
(i) password;
(ii) financial information such as Bank account or credit card or debit card or other payment instrument details ;
(iii) physical, physiological and mental health condition;
(iv) sexual orientation;
(v) medical records and history;
(vi) Biometric information;
(vii) any detail relating to the above clauses as provided to body corporate for providing service; and
(viii) any of the information received under above clauses by body corporate for processing, stored or processed under lawful contract or otherwise. Provided that, any information that is freely available or accessible in public domain or furnished under the Right to Information Act, 2005 or any other law for the time being in force shall not be regarded as sensitive personal data or information for the purposes of these rules.” Section 66C provides a punishment for identity theft:
“66C. Punishment for identity theft.- Whoever, fraudulently548 or dishonestly549 make use of the electronic signature, password or any other unique identification feature of any other person, shall be punished with imprisonment of either description for a term which may extend to three years and shall also be liable to fine which may extend to rupees one lakh.”
(Emphasis supplied)
Section 66E provides for punishment for the violation of the privacy of an individual: “Whoever, intentionally or knowingly captures, publishes or transmits the image of a private area of any person without his or her consent, under circumstances violating the privacy of that person, shall be punished with imprisonment which may extend to three years or with fine not exceeding two lakh rupees, or with both.” The explanation to the Section provides that “transmit” means to electronically send a visual image with the intent that it be viewed by a person or persons.
“Capture”, with respect to an image, has been defined to mean videotaping, photographing, filming or recording by any means. “Private area” means the “naked or undergarment clad genitals, pubic area, buttocks or female breast.” “Publishes” has been defined as reproduction in the printed or electronic form and making it available for public. Section 72A provides for punishment for disclosure of information in breach of a lawful contract:
“Save as otherwise provided in this Act or any other law for the time being in force, any person including an intermediary who, while providing services under the terms of lawful contract, has secured access to any material containing personal information about another person, with the intent to cause or knowing that he is likely to cause wrongful loss or wrongful gain discloses, without the consent of the person concerned, or in breach of a lawful contract, such material to any other person shall be punished with imprisonment for a term which may extend to three years, or with a fine which may extend to five lakh rupees, or with both.”
(Emphasis supplied)
Section 43A applies only to bodies corporate and has no application to government or to its departments.
Explanation (i) defines body corporate to mean any company and to include a firm, sole proprietorship or other association of individuals engaged in professional or commercial activities. Personal information leaked or lost by government agencies will not be covered under Section 43A. The scope of Section 66E is limited. It only deals with the privacy of the “private area” of any person. It does not deal with informational privacy. The scope of Section 72A is also limited. It only penalises acts of disclosing personal information about a person obtained PART J 422 while providing services under a lawful contract. Section 66C deals with identity theft and punishes the dishonest or fraudulent use of the unique identification feature of a person.
The Information Technology Act also does not penalise unauthorised access to the Central Identities Data Repository. Many of the safeguards which were introduced by the Aadhaar Act were not comprehended in the provisions of the Information Technology Act. Indeed, it was the absence of those safeguards in the Information Technology Act which required their introduction in the Aadhaar Act. Hence, the Attorney General is not correct in submitting that India operated under a regime of comprehensive safeguards governing biometric data during the period when the Aadhaar project was governed by an executive notification, in the absence of a legislative framework.
The absence of a legislative framework rendered the collection of biometric data vulnerable to serious violations of privacy. There are two distinct facets here. First, the absence of a legislative framework for the Aadhaar project between 2009 and 2016 left the biometric data of millions of Indian citizens bereft of the kind of protection which a law, as envisaged in Puttaswamy, must provide to comprehensively protect and enforce the right to privacy. Second, the notification of 2009 does not authorise the collection of biometric data. Consequently, the validation of actions taken under the 2009 notification by Section 59 does not save the collection of biometric data prior to the enforcement of the Act. Privacy is of paramount importance.
No invasion of privacy can be allowed without proper, adequate and stringent safeguards providing not only penalties for misuse or loss of one’s personal information, but also for protection of that person. 307 The Respondents have relied upon several judgments where this Court has upheld validating statutes, which, they contend, are similar to Section 59.
The first decision which needs to be discussed is the judgment of the Constitution Bench in West Ramnad, which dealt with a validating statute of the Madras Legislature. Act 43 of 1949 of the Madras Legislature which sought to acquire electricity undertakings in the state was struck down for want of legislative competence. In the meantime, the Constitution came into force, and under the Seventh Schedule, the State acquired legislative competence. A fresh law was enacted in 1954.
Section 24 sought to validate actions done and taken under the 1949 Act. Section 24 provided thus: “Orders made, decisions or directions given, notifications issued, proceedings taken and acts or things done, in relation to any undertaking taken over, if they would have been validly made, given, issued, taken or done, had the Madras Electricity Supply Undertakings (Acquisition) Act 1949 (Madras Act 43 of 1949), and the rules made thereunder been in force on the date on which the said orders, decisions or directions, notifications, proceeding, acts or things were made, given, issued, taken or done are hereby declared to have been validly made, given, issued, taken or done, as the case may be, except to the extent to which the said orders, decisions, directions, notifications, proceedings, acts or things are repugnant to the provisions of this Act.”
(Emphasis supplied)
Section 24 was held to be a provision, which saved and validated actions validly taken under the provisions of the earlier Act, which was invalid from the PART J 424 inception. Justice Gajendragadkar, speaking for the Court, interpreted Section 24 thus: “12. The first part of the section deals, inter alia, with notifications which have been validly issued under the relevant provisions of the earlier Act and it means that if the earlier Act had been valid at the relevant time, it ought to appear that the notifications in question could have been and had in fact been made properly under the said Act. In other words, before any notification can claim the benefit of Section 24, it must be shown that it was issued properly under the relevant provisions of the earlier Act, assuming that the said provisions were themselves valid and in force at that time.
The second part of the section provides that the notifications covered by the first part are declared by this Act to have been validly issued; the expression “hereby declared” clearly means “declared by this Act” and that shows that the notifications covered by the first part would be treated as issued under the relevant provisions of the Act and would be treated as validly issued under the said provisions. The third part of the section provides that the statutory declaration about the validity of the issue of the notification would be subject to this exception that the said notification should not be inconsistent with or repugnant to the provisions of the Act.
In other words, the effect of this section is that if a notification had been issued properly under the provisions of the earlier Act and its validity could not have been impeached if the said provisions were themselves valid, it would be deemed to have been validly issued under the provisions of the Act, provided, of course, it is not inconsistent with the other provisions of the Act. The section is not very happily worded, but on its fair and reasonable construction, there can be no doubt about its meaning or effect.”
(Emphasis supplied)
308 The second decision is a four judge Bench judgment in Chetty, which dealt with the competence of a legislature to remedy a discriminatory procedure retrospectively. There were two Acts in Mysore for acquisition of private land for public purposes – the Mysore Land Acquisition Act, 1894 and the City of Bangalore Improvement Act, 1945. The respondent challenged a notification which was issued under the 1894 Act for the acquisition of his land PART J 425 in Bangalore, on the ground that recourse to the provisions of the Land Acquisition Act was discriminatory because in other cases the provisions of the Improvement Act were applied.
The High Court accepted the contention, against which there was an appeal to this Court. During the pendency of the appeal, the Bangalore Acquisition of Lands (Validation) Act, 1962 was passed. The 1962 Act contained two provisions. Section 2 provided: “2. Validation of certain acquisition of lands and proceedings and orders connected therewith.- (1) Notwithstanding anything contained in the City of Bangalore Improvement Act, 1945 (Mysore Act 5 of 1945), or in any other law, or in any judgment, decree or order of any court:
(a) every acquisition of land for the purpose of improvement, expansion or development of the City of Bangalore or any area to which the City of Bangalore Improvement Act, 1945, extends, made by the State Government acting or purporting to act under the Mysore Land Acquisition Act, 1894 (Mysore Act 7 of 1894), at any time before the commencement of this Act, and every proceeding held, notification issued and order made in connection with the acquisition of land for the said purpose shall be deemed for all purposes to have been validly made, held to issue, as the case may be, and any acquisition proceeding commenced under the Mysore Land Acquisition Act, 1894, for the said purpose before the commencement of this Act but not concluded before such commencement, may be continued under the Land Acquisition Act, 1894 (Central Act 1 of 1894), as extended to the State of Mysore by the Land Acquisition (Mysore Extension and Amendment) Act, 1961, and accordingly no acquisition so made, no proceeding held, no notification issued and no order made by the State Government or by any authority under the Mysore Land Acquisition Act, 1894, or the Land Acquisition Act, 1894, in connection with any such acquisition shall be called in question on the ground that the State Government was not competent to make acquisition of land for the said purpose under the said Act or on any other ground whatsoever; (b) any land to the acquisition of which the provisions of clause (a) are applicable shall, after it has vested in the State Government, be deemed to have been PART J 426 transferred, or stand transferred, as the case may be, to the Board of Trustees for the improvement of the City of Bangalore.”
(Emphasis supplied)
The Act of 1962 validated all acquisitions made, proceedings held, notifications issued or orders made under the Mysore Land Acquisition Act before the validating law came into force. The Validation Act was challenged on the ground that it was discriminatory to provide two Acts which prescribed two different procedures under the acquisition laws in the same field. This Court found that the legislature retrospectively made a single law for the acquisition of properties and upheld the validating Act. It was held: “15. If two procedures exist and one is followed and the other discarded, there may in a given case be found discrimination. But the Legislature has still the competence to put out of action retrospectively one of the procedures leaving one procedure only available, namely, the one followed and thus to make disappear the discrimination. In this way a Validating Act can get over discrimination.
Where, however, the legislative competence is not available, the discrimination must remain for ever, since that discrimination can only be removed by a legislature having power to create a single procedure out of two and not by a legislature which has not that power.” 309 In West Ramnad, the validation depended upon the condition that a notification or act ought to have been validly issued or done under the earlier statute, presuming that the earlier Act was itself valid at that time. In the present case, there was no earlier law governing the actions of the government for the collection of biometric data. The Aadhaar Act was notified in 2016.
The Planning Commission’s notification of 2009 and the Ministry of Information and Technology’s notification of 2015 were not issued under any statute. Therefore, the validating law in West Ramnad was clearly of a distinct genre. West Ramnad will be of no assistance to the Union of India. 310 The decision in Chetty in fact brings out the essential attributes of a validating law. The existence of two legislations governing the field of land acquisition had been found to be discriminatory and hence violative of Article 14 by the High Court (on the basis of the position in law as it then stood). During the pendency of the appeal before this Court, the legislature enacted a validating law which removed the cause for invalidity. The reason the state law had been invalidated by the High Court was the existence of two laws governing the same field. This defect was removed.
To use the words of this Court, the legislature “put out of action retrospectively one of the procedures” as a result of which only one procedure was left in the field. The decision in Chetty thus brings out the true nature of a validating law. A validating law essentially removes the deficiency which is found to exist in the earlier enactment. By curing the defect, it validates actions taken under a previous enactment.
311 The third judgment of seven judges is in Hari Singh. The constitutionality of the Public Premises (Eviction of Unauthorised Occupants) Act, 1958 was challenged on the ground that Section 5(1) contravened Article 14. Section 5(1) conferred power on the Estate Officer to make an order of eviction against persons who were in unauthorised occupation of public PART J 428 premises. During the pendency of the appeal before this Court, the Public Premises (Eviction of Unauthorised Occupants) Act, 1971 was enacted, which validated all actions taken under the Act of 1958. The constitutional validity of the 1971 Act was also challenged. Section 20 of the later Act provided:
“Notwithstanding any judgment, decree or order of any court, anything done or any action taken (including rules or orders made, notices issued, evictions ordered or effected, damages assessed, rents or damages or costs recovered and proceedings initiated) or purported to have been done or taken under the Public Premises (Eviction of Unauthorised Occupants) Act, 1958 shall be deemed to be as valid and effective as if such thing or action was done or taken under the corresponding provisions of this Act which, under Sub-section (3) of Section 1 shall be deemed to have come into force on the 16th day of September, 1958 …”
(Emphasis supplied)
The Court held that the legislature has the power to validate actions under an earlier law by removing its infirmities. In that case, validation was achieved by enacting the 1971 Act with retrospective effect from 1958 and legislating that actions taken under the earlier law will be deemed to be as valid and effective as if they were taken under the 1971 Act. The Court held:
“24. The 1958 Act has not been declared by this Court to be unconstitutional… The arguments on behalf of the appellants therefore proceeded on the footing that the 1958 Act will be presumed to be unconstitutional. It was therefore said that the 1971 Act could not validate actions done under the 1958 Act. The answer is for the reasons indicated above that the Legislature was competent to enact this legislation in 1958 and the Legislature by the 1971 Act has given the legislation full retrospective operation. The Legislature has power to validate actions under an earlier Act by removing the infirmities of the earlier Act. The 1971 Act has achieved that object of validation.” The Court approved the Constitution Bench decision in West Ramnad:
“16. The ruling of this Court in West Ramnad Electric Distribution Co. Ltd. case establishes competence of the legislature to make laws retrospective in operation for the purpose of validation of action done under an earlier Act which has been declared by a decision of the court to be invalid. It is to be appreciated that the validation is by virtue of the provisions of the subsequent piece of legislation.” In Hari Singh, the validating Act retrospectively authorised the actions undertaken under the previous Act, which had been invalidated by a court decision.
The validating law of 1971 was enacted with retrospective effect from 1958. 312 Reliance was placed by the Respondents on the judgments of this Court in Jaora Sugar Mills (P) Ltd. v State of Madhya Pradesh550 (Jaora Sugar Mills), SKG Sugar Ltd. v State of Bihar551 (“SKG Sugar”) and Krishna Chandra Gangopadhyaya v Union of India552 (“Krishna Chandra”), to contend that in the case of fiscal legislation, where an enactment was struck down for violating Article 265 or the fundamental rights, of a citizen, validating Acts were enacted after removing the flaw and that in cases where the state Legislature was held to be incompetent to enact a taxing measure, a validating law was enacted by Parliament by making a substantive provision. In Jaora Sugar Mills, a state law imposing cess was struck down for want of legislative competence. Parliament enacted the Sugarcane Cess (Validation) Act, 1961 to validate the imposition of cess under the invalidated state law. Section 3(1) of the 1961 Act provided:
“12…Notwithstanding any judgment, decree or order of any Court, all cesses imposed, assessed or collected or purporting to have been imposed, assessed or collected under any State Act before the commencement of this act shall be deemed to have been validly imposed, assessed or collected in accordance with law, as if the provisions of the State Acts and of all notifications, orders and rules issued or made thereunder, in so far as such provisions relate to the imposition, assessment and collection of such cess had been included in and formed part of this section and this section had been in force at all material times when such cess was imposed, assessed or collected; ….”
(Emphasis supplied)
The Section was upheld. Speaking for the Constitution Bench, Chief Justice Gajendragadkar held: “14… What Parliament has done by enacting the said section is not to validate the invalid State Statutes, but to make a law concerning the cess covered by the said Statutes and to provide that the said law shall come into operation retrospectively. There is a radical difference between the two positions. Where the legislature wants to validate an earlier Act which has been declared to be invalid for one reason or another, it proceeds to remove the infirmity from the said Act and validates its provisions which are free from any infirmity.”
(Emphasis supplied)
The state law was held to be invalid for want of legislative competence. Parliament, which was competent to enact a law on the subject, did so with retrospective effect and validated actions which were taken under the invalid state law.
314 In SKG Sugar, a state law – Bihar Sugar Factories Control Act, 1937 – was declared unconstitutional. In 1969, during President’s Rule in Bihar, Parliament enacted the Bihar Sugarcane (Regulation of Supply and Purchase) Act, 1969. Section 66(1) of the Act provided: “12…Notwithstanding any judgment, decree or order of any court, all cesses and taxes imposed, assessed or collected or purporting to have been imposed, assessed or collected under any State law, before the commencement of this Act, shall be deemed to have been validly imposed, assessed or collected in accordance with law as if this Act had been in force at all material times when such cess or tax was imposed, assessed or collected and accordingly….”553
(Emphasis supplied)
The Constitution Bench held: “32… By virtue of the legal fiction introduced by the validating provision in Section 66(1), the impugned notification will be deemed to have been issued not necessarily under the Ordinance No. 3 of 1968 but under the President’s Act, itself, deriving its legal force and validity directly from the latter.”554
315 In Krishna Chandra, provisions of the Bihar Land Reforms Act, 1950 were struck down for want of legislative competence. Parliament enacted the Mines and Minerals (Regulation and Development) Act, 1957 to validate those provisions with retrospective effect. Section 2 provided that:
“1…(2). Validation of certain Bihar State laws and action taken and things done connected therewith.-
(1) The laws specified in the schedule shall be and shall be deemed always to have been, as valid as if the provisions contained therein had been enacted by Parliament.
(2) Notwithstanding any judgment, decree or order of any court, all actions taken, things done, rules made, notifications issued or purported to have been taken, done, made or issued and rents or royalties realised under any such laws shall be deemed to have been validly taken, done, made, issued or realised, as the case may be, as if this section had been in force at all material times when such action was taken, things were done, rules were, made, notifications were issued, or rents or royalties were realised, and no suit or other proceedings shall be maintained or continued in any court for the refund of rents or royalties realised under any such laws.
(3) For the removal of doubts, it is hereby declared that nothing in Sub-section (2) shall be construed as preventing any person from claiming refund of any rents or royalties paid by him in excess of the amount due from him under any such laws.”555 ‘
(Emphasis supplied)
The central issue in the case was whether a statute and a rule earlier declared to be unconstitutional or invalid, can be retroactively enacted through fresh validating legislation by the competent Legislature.
The Court held that it could be. 316 Section 59 of the Aadhaar Act is different from the validating provisions in Jaora Sugar Mills, SKG Sugar and Krishna Chandra. In those cases, state laws were invalid for want of legislative competence. Parliament, which undoubtedly possessed legislative competence, could enact a fresh law with retrospective effect and protect actions taken under the state law. The infirmity being that the earlier laws were void for absence of competence in the legislature, the fresh laws cured the defect of the absence of legislative competence.
317 Parliament and the State Legislatures have plenary power to legislate on subjects which fall within their legislative competence. The power is plenary because the legislature can legislate with prospective as well as with retrospective effect. Where a law suffers from a defect or has been invalidated, it is open to the legislature to remove the defect. While doing that, the legislature can validate administrative acts or decisions made under the invalid law in the past.
The true test of a validation is that it must remove the defects in the earlier law. It is not enough for the validating law to state that the grounds of invalidity of the earlier law are deemed to have been removed. The validating law must remove the deficiencies. There were several deficiencies in the collection of biometric data during the period between 2009 and 2016, before the Aadhaar Act came into force. The first was the absence of enabling legislation. As a result, the collection of sensitive personal information took place without the authority of law. Second, the notification of 2009 did not authorize the collection of biometric data. Third, the collection of biometric data was without an enabling framework of the nature which the Aadhaar Act put into place with effect from 2016.
The Aadhaar Act introduced a regime for obtaining informed consent, securing the confidentiality of information collected from citizens, penalties and offences for breach and regulated the uses to which the data which was collected could be put. In the absence of safeguards, the collection of biometric data prior of the enactment of Aadhaar Act 2016 is ultra vires. PART J 434 318 Section 59 does not remove the cause for invalidity. First, Section 59 protects actions taken under the notification of 2009.
The notification does not authorize the collection of biometric data. Hence, Section 59 would not provide legal authority for the collection of biometrics between 2009 and 2016. Second, it was through the Aadhaar Act, that safeguards were sought to be introduced for ensuring informed consent, confidentiality of information collected, restrictions on the use of the data and through a regime of penalties and offences for violation. Section 59 does not cure the absence of these safeguards between 2009 and 2016. Section 59 fails to meet the test of a validating law for the simple reason that the absence of safeguards and of a regulatory framework is not cured merely by validating what was done under the notifications of 2009 and 2016. There can be no dispute about the principle that the legislature is entitled to cure the violation of a fundamental right. But in order to do so, it is necessary to cure the basis or the foundation on which there was a violation of the fundamental right.
The deficiency must be demonstrated to be cured by the validating law. Section 59 evidently fails to do so. It fails to remedy the deficiencies in regard to the conditions under which the collection of biometric data took place before the enforcement of the Aadhaar Act in 2016. The Respondents submitted that Section 59 creates a deemed fiction and cited a few judgments in support of this contention. In Bishambhar Nath PART J 435 Kohli v State of Uttar Pradesh556, an Ordinance repealed another Ordinance. Section 58(3) of the repealing Ordinance stated:
“6…The repeal by this Act of the Administration of Evacuee Property Ordinance, 1949 or the Hyderabad Administration of Evacuee Property Regulation or of any corresponding law shall not affect the previous operation of that Ordinance, Regulation or corresponding law, and subject thereto, anything done or any action taken in the exercise of any power conferred by or under that Ordinance, Regulation or corresponding law, shall be deemed to have been done or taken in the exercise of the powers conferred by or under this Act as if this Act were in force on the day on which such thing was done or action was taken.”
(Emphasis supplied)
319 A Constitution Bench of this Court held that by virtue of Section 58, all things done and actions taken under the repealed ordinance are deemed to be done or taken in exercise of the powers conferred by the repealing Act, as if that Act were in force on the day on which that thing was done or action was taken.
The things done or actions taken under the repealed ordinance are to be deemed by fiction to have been done or taken under the repealing Act. The actions were validated because the Act, in this case, was deemed to be “in force on the day on which such thing was done or action was taken”. Section 59 of the Aadhaar Act does not create this fiction. The Aadhaar Act does not come in force on the date on which the actions, which this Section seeks to validate, were taken. 320 A three judge Bench headed by one of us, Hon’ble Mr Justice Dipak Misra (as the learned Chief Justice then was) in State of Karnataka v State of Tamil Nadu557, was dealing with a batch of civil appeals filed against a final order of the Cauvery Water Disputes Tribunal constituted under the Inter- State River Water Disputes Act, 1956. Section 6(2) of the 1956 Act provides:
“72…6(2).The decision of the Tribunal, after its publication in the Official Gazette by the Central Government under Subsection (1), shall have the same force as an order or decree of the Supreme Court.”558 Relying on Section 6(2), it was contended that the jurisdiction of this Court is ousted as it cannot sit in appeal on its own decree. The Court did not accept the submission and held: “74. The language employed in Section 6(2) suggests that the decision of the tribunal shall have the same force as the order or decree of this Court. There is a distinction between having the same force as an order or decree of this Court and passing of a decree by this Court after due adjudication.
The Parliament has intentionally used the words from which it can be construed that a legal fiction is meant to serve the purpose for which the fiction has been created and not intended to travel beyond it. The purpose is to have the binding effect of the tribunal’s award and the effectiveness of enforceability. Thus, it has to be narrowly construed regard being had to the purpose it is meant to serve…559 81…it is clear as crystal that the Parliament did not intend to create any kind of embargo on the jurisdiction of this Court.
The said provision was inserted to give the binding effect to the award passed by the tribunal. The fiction has been created for that limited purpose.”560
(Emphasis supplied)
The judgment makes it clear that a deeming fiction cannot travel beyond what was originally intended. As stated earlier, the action of collecting and authentication of biometrics or the requirement of informed consent finds no mention in the 2009 notification. Therefore, Section 59 cannot be held to create a deeming fiction that all the actions taken under the notifications issued were done under the Act and not under the aforesaid notifications.
321 This Court must also deal with the Respondents’ submission that Parliament is not debarred from enacting a validation law even though the Court did not have the opportunity to rule on the validity of the notifications which are purported by Section 59 to have been validated. The Respondents have placed reliance on a two judge Bench decision in Amarendra Kumar Mohapatra v State of Orissa.561 This case involved a challenge to the constitutional validity of the Orissa Service of Engineers (Validation of Appointment) Act, 2002 enacted to regularise ad hoc appointments of employees.
The issue before the Court was whether the Orissa Act was in effect a validation statute to validate any illegality or defect in a pre-existing Act or rule in existence. The Court held that since the Orissa Act merely regularised the appointment of graduate Stipendiary Engineers working as ad hoc Assistant Engineers as Assistant Engineers, it could not be described as a validating law. It was held the legislation did not validate any such nonexistent act, but simply appointed the ad hoc Assistant Engineers as substantive employees of the State by resort to a fiction. This Court held:
“31…a prior judicial pronouncement declaring an act, proceedings or rule to be invalid is not a condition precedent for the enactment of a Validation Act. Such a piece of legislation may be enacted to remove even a perceived invalidity, which the Court has had no opportunity to adjudge. Absence of a judicial pronouncement is not, therefore, of much significance for determining whether or not the legislation is a validating law.”562
The Court further held that: “25. … when the validity of any such Validation Act is called in question, the Court would have to carefully examine the law and determine whether (i) the vice of invalidity that rendered the act, rule, proceedings or action invalid has been cured by the validating legislation (ii) whether the legislature was competent to validate the act, action, proceedings or rule declared invalid in the previous judgments and (iii) whether such validation is consistent with the rights guaranteed by Part III of the Constitution. It is only when the answer to all these three questions is in the affirmative that the Validation Act can be held to be effective and the consequences flowing from the adverse pronouncement of the Court held to have been neutralised.”
(Emphasis supplied)
322 The two judge Bench relied upon the Constitution Bench decision of this Court in Shri Prithvi Cotton Mills Ltd v Broach Borough Municipality563 to formulate the following pre-requisites of a piece of legislation that purports to validate any act, rule, action or proceedings:
“(a) The legislature enacting the Validation Act should be competent to enact the law and;
(b) the cause for ineffectiveness or invalidity of the Act or the proceedings needs to be removed.”
These judgments suggest that while there can be no disagreement with the proposition that a legislature has the power, within its competence, to make a law to validate a defective law, the validity of such a law would depend upon whether it removes the cause of ineffectiveness or invalidity of the previous or proceedings. Parliament has the power to enact a law of validation to cure an illegality or defect in the pre-existing law, with or without a judicial determination. But that law should cure the cause of infirmity or invalidity. Section 59 fails to cure the cause of invalidity prior to the enactment of the Aadhaar Act.
K Rule of law and violation of interim orders
323 The rule of law is the cornerstone of modern democratic societies and protects the foundational values of a democracy. When the rule of law is interpreted as a principle of constitutionalism, it assumes a division of governmental powers or functions that inhibits the exercise of arbitrary State power. It also assumes the generality of law: the individual’s protection from arbitrary power consists in the fact that her personal dealings with the State are regulated by general rules, binding on private citizens and public officials alike.564
It envisages a fundamental separation of powers among different organs of the State. Separation of power supports the accountability aspect of the rule of law. Separation of the judicial and executive powers is an essential feature of the rule of law. By entrusting the power of judicial review to courts, the doctrine prevents government officials from having the last word on whether they have acted illegally. The separation of judicial power provides an effective check on the executive branch.565 324 The concepts of the rule of law and separation of powers have been integral to Indian constitutional discourse. While both these concepts have not been specified in as many words in the Constitution, they have received immense attention from this Court in its judgments. Though the Indian Constitution does not follow the doctrine of separation of powers in a rigid sense, the following statement of the law by Chief Justice Mukherjea in Ram Sahib Ram Jawaya Kapur v State of Punjab566 is widely regarded as defining the core of its content:
“12…The Indian Constitution has not indeed recognised the doctrine of separation of powers in its absolute rigidity but the functions of the different parts or branches of the Government have been sufficiently differentiated and consequently it can very well be said that our Constitution does not contemplate assumption, by one organ or part of the State, of functions that essentially belong to another…” Separation of powers envisages a system of checks and balances, which ensures governance by law and not by the caprice of those to whom governance is entrusted for the time being. By curbing excesses of power, it has a direct link with the preservation of institutional rectitude and individual liberty. In S G Jaisinghani v Union of India567, this Court held that:
“14. In this context it is important to emphasize that the absence of arbitrary power is the first essential of the rule of law upon which our whole constitutional system is based. In a system governed by rule of law, discretion, when conferred upon executive authorities, must be confined within clearly defined limits. The rule of law from this point of view means that decisions should be made by the application of known principles and rules and, in general, such decisions should be predictable and the citizen should know where he is. If a decision is taken without any principle or without any rule it is unpredictable and such a decision is the antithesis of a decision taken in accordance with the Rule of law…” The separation of powers between the legislature, the executive and the judiciary has been declared to be part of the basic structure of the Constitution. In Kesavananda Bharati v State of Kerala568, Chief Justice Sikri held that: “292…The basic structure may be said to consist of the following features:
(1) Supremacy of the Constitution;
(2) Republican and Democratic form of Government;
(3) Secular character of the Constitution;
(4) Separation of powers between the legislature, the executive and the judiciary;
(5) Federal character of the Constitution.”569
(Emphasis supplied)
Justice HR Khanna held that the rule of law meant “supremacy of the Constitution and the laws as opposed to arbitrariness”570. The same view is expressed in subsequent decisions of this Court.571 In Smt Indira Nehru Gandhi v Shri Raj Narain572, Chief Justice AN Ray held the rule of law to be the basis of democracy. The functional relationship between separation of powers and the rule of law was discussed by a Constitution Bench of this Court in State of Tamil Nadu v State of Kerala573, as follows:
“98. Indian Constitution, unlike the Constitution of United States of America and Australia, does not have express provision of separation of powers. However, the structure provided in our Constitution leaves no manner of doubt that the doctrine of separation of powers runs through the Indian Constitution. It is for this reason that this Court has recognized separation of power as a basic feature of the Constitution and an essential constituent of the rule of law.
The doctrine of separation of powers is, though, not expressly engrafted in the Constitution, its sweep, operation and visibility are apparent from the Constitution. Indian Constitution has made demarcation without drawing formal lines between the three organs–legislature, executive and judiciary.” This Court has consistently held judicial review to be an essential component of the separation of powers as well as of the rule of law. Judicial review involves determination not only of the constitutionality of law but also of the validity of administrative action. It protects the essence of the rule of law by ensuring that every discretionary power vested in the executive is exercised in a just, reasonable and fair manner.
325 In a reference574 under Article 143 of the Constitution, a seven judge Bench held that irrespective of “whether or not there is distinct and rigid separation of powers under the Indian Constitution”, the judicature has been entrusted the task of construing the provisions of the Constitution and of safeguarding the fundamental rights of citizens. It was held:
“41…When a statute is challenged on the ground that it has been passed by Legislature without authority, or has otherwise unconstitutionally trespassed on fundamental rights, it is for the courts to determine the dispute and decide whether the law passed by the legislature is valid or not… If the validity of any law is challenged before the courts, it is never suggested that the material question as to whether legislative authority has been exceeded or fundamental rights have been contravened, can be decided by the legislatures themselves. Adjudication of such a dispute is entrusted solely and exclusively to the Judicature of this country…”
In his celebrated dissent in Additional District Magistrate, Jabalpur v Shivakant Shukla575, Justice HR Khanna, while referring to the rule of law as the “antithesis of arbitrariness”, held: “527…Rule of law is now the accepted norm of all civilised societies… [E]verywhere it is identified with the liberty of the individual. It seeks to maintain a balance between the opposing notions of individual liberty and public order. In every State the problem arises of reconciling human rights with the requirements of public interest. Such harmonising can only be attained by the existence of independent courts which can hold the balance between citizen and State and compel Governments to conform to the law.”576 326 Judicial review has been held to be one of the basic features of the Constitution. A seven judge Bench of this Court, in L Chandra Kumar v Union of India577, declared:
“78… the power of judicial review over legislative action vested in the High Courts under Article 226 and in the Supreme Court under Article 32 of the Constitution is an integral and essential feature of the Constitution, constituting part of its basic structure.”578 The complementary relationship between judicial review, the rule of law and the separation of powers is integral to working of the Constitution. This Court in I R Coelho v State of Tamil Nadu579 held thus:
“129… Equality, rule of law, judicial review and separation of powers form parts of the basic structure of the Constitution. Each of these concepts are intimately connected. There can be no rule of law, if there is no equality before the law. These would be meaningless if the violation was not subject to the judicial review. All these would be redundant if the legislative, executive and judicial powers are vested in one organ. Therefore, the duty to decide whether the limits have been transgressed has been placed on the judiciary.”580 Judicial review, by protecting individual rights, promotes the foundational values of the Constitution and the rule of law. This Court took note of this aspect in Puttaswamy:
“295. Above all, it must be recognized that judicial review is a powerful guarantee against legislative encroachments on life and personal liberty. To cede this right would dilute the importance of the protection granted to life and personal liberty by the Constitution. Hence, while judicial review in constitutional challenges to the validity of legislation is exercised with a conscious regard for the presumption of constitutionality and for the separation of powers between the legislative, executive and judicial institutions, the constitutional power which is vested in the Court must be retained as a vibrant means of protecting the lives and freedoms of individuals.”581 327 Constitutional adjudication facilitates answers to the silences of the Constitution.
The task of interpretation is to foster the spirit of the Constitution as much as its text. This role has exclusively been conferred on the Supreme Court and the High Courts to ensure that its values are not diminished by the legislature or the executive. Our Court has been conscious of this role. In Krishna Kumar Singh v State of Bihar582, while dealing with the question whether an ordinance (promulgated by the Governor) which has a limited life can bring about consequences for the future (in terms of the creation of rights, privileges, liabilities and obligations) which will enure beyond its life, a seven judge Bench held that:
“91…The silences of the Constitution must be imbued with substantive content by infusing them with a meaning which enhances the Rule of law. To attribute to the executive as an incident of the power to frame ordinances, an unrestricted ability to create binding effects for posterity would set a dangerous precedent in a parliamentary democracy. The court’s interpretation of the power to frame ordinances, which originates in the executive arm of government, cannot be oblivious to the basic notion that the primary form of law making is through the legislature…”583
(Emphasis supplied)
The Court held that the ordinance making power must be carefully structured to ensure that it remains what the framers of our Constitution intended it to be: an exceptional power to meet a constitutional necessity. 328 In a constitutional democracy, the power of government, is defined, limited, and distributed by the fundamental norms of the Constitution. A constitutional democracy holds its political regime accountable, responsible, or answerable for its decisions and actions while in public office.584 A constitutional democracy determines the degree and manner of distribution of political authority among the major organs or parts of the government. The limits of each institution are set by the Constitution.
No institution which has been created by the Constitution can have absolute power. Separation of powers, envisaged by the Constitution between different institutions acts as a check and balance among the institutions and promotes the rule of law by ensuring that no institution can act in an arbitrary manner. Judicial review as a part of the basic structure of the Indian Constitution and as an essential component of the rule of law and separation of powers, is intended to ensure that every institution acts within its limits. Judicial review promotes transparency, consistency and accountability in the administration of law, and notions of equity, justice and fairness585. Constitutionalism thus puts a legal limitation on the government. It envisages the existence of limited government.
Discretion conferred upon an institution of governance, be it the legislature or the executive, is confined within clearly defined limits of the Constitution. Not only are the organs of the State required to operate within their defined legitimate spheres; they are bound to exercise their powers within these spheres without violating the Constitution.586 Judicial review is a sanction and agency to enforce the limitations imposed by the Constitution upon the authority of the organs of the State.
This formulation of the limited power of political authority has been recognized in several judgments of this Court. In State of M P v Thakur Bharat Singh587, a Constitution Bench held: “5…Our federal structure is founded on certain fundamental principles:
(1) the sovereignty of the people with limited Government authority i.e. the Government must be conducted in accordance with the will of the majority of the people. The people govern themselves through their representatives, whereas the official agencies of the executive Government possess only such powers as have been conferred upon them by the people;
(2) There is a distribution of powers between the three organs of the State – legislative, executive and judicial – each organ having some check direct or indirect on the other; and
(3) the rule of law which includes judicial review of arbitrary executive action…”
(Emphasis supplied)
329 In a decision rendered by a Constitution Bench, in S P Sampath Kumar v Union of India588, Chief Justice P.N. Bhagwati, in his concurring opinion, held: “3…It is a fundamental principle of our constitutional scheme that every organ of the State, every authority under the Constitution, derives its power from the Constitution and has to act within the limits of such power. It is a limited government which we have under the Constitution and both the executive and the legislature have to act within the limits of the power conferred upon them under the Constitution…
The judiciary is constituted the ultimate interpreter of the Constitution and to it is assigned the delicate task of determining what is the extent and scope of the power conferred on each branch of government, what are the limits on the exercise of such power under the Constitution and whether any action of any branch transgresses such limits. It is also a basic principle of the rule of law which permeates every provision of the Constitution and which forms its very core and essence that the exercise of power by the executive or any other authority must not only be conditioned by the Constitution but also be in accordance with law and it is the judiciary which has to ensure that the law is observed and there is compliance with the requirements of law on the part of the executive and other authorities…”589
(Emphasis supplied)
330 In I R Coelho v State of Tamil Nadu590, a nine judge Bench held that control over government power ensures that the foundational values of a democracy are not damaged:
“43…The principle of constitutionalism advocates a check and balance model of the separation of powers; it requires a diffusion of powers, necessitating different independent centres of decision-making… The role of the judiciary is to protect fundamental rights. A modern democracy is based on the twin principles of majority rule and the need to protect fundamental rights. According to Lord Steyn, it is job of the judiciary to balance the principles ensuring that the Government on the basis of number does not override fundamental rights.”
The rule of law is an implied limitation on the authority of any institution in a constitutional democracy.591 331 Interim orders of courts are an integral element of judicial review. Interim directions issued on the basis of the prima facie findings in a case are temporary arrangements till the matter is finally decided. Interim orders ensure that the cause which is being agitated does not become infructuous before the final hearing.592 The power of judicial review is not only about the writs issued by superior courts or the striking down of governmental action. Entrustment of judicial review is accompanied by a duty to ensure that judicial orders are complied with.
Unless orders are enforced, citizens will lose faith in the efficacy of judicial review and in the legal system. It is in the background of the above constitutional position that this Court must deal with the contention that the interim orders passed by this Court, during the adjudication of the present dispute were not observed. This Court has consistently insisted, through its interim orders, on a restraint on the mandatory use of Aadhaar. It has been submitted that the interim orders have been violated and several contempt petitions are pending593 before this Court. 332 Prior to the enactment of the Aadhaar Act, the scheme was challenged before this Court. By its interim order dated 23 September 2013594, a two judge Bench directed: “All the matters require to be heard finally.
List all matters for final hearing after the Constitution Bench is over. In the meanwhile, no person should suffer for not getting the Aadhaar card in spite of the fact that some authority had issued a circular making it mandatory and when any person applies to get the Aadhaar Card voluntarily, it may be checked whether that person is entitled for it under the law and it should not be given to any illegal immigrant.” (sic)
This was followed by an order dated 26 November 2013 where the earlier order was continued: “After hearing the matter at length, we are of the view that all the States and Union Territories have to be impleaded as respondents to give effective directions. In view thereof notice be issued to all the States and Union Territories through standing counsel… Interim order to continue, in the meantime.” While considering another petition, Unique Identification Authority of India v Central Bureau of Investigation595, this Court directed in an interim order dated 24 March 2014:
“In the meanwhile, the present petitioner is restrained from transferring any biometric information of any person who has been allotted the Aadhaar number to any other agency without his consent in writing… More so, no person shall be deprived of any service for want of Aadhaar number in case he/she is otherwise eligible/entitled. All the authorities are directed to modify their forms/circulars/likes so as to not compulsorily require the Aadhaar number in order to meet the requirement of the interim order passed by this Court forthwith… Tag and list the matter with main matter i.e. WP(C) No.494/2012.”
On 16 March 2015, while considering WP (Civil) 494 of 2012, this Court noted a violation of its earlier order dated 23 September 2013 and directed thus: “The matters require considerable time for hearing… In the meanwhile, it is brought to our notice that in certain quarters, Aadhaar identification is being insisted upon by the various authorities. We do not propose to go into the specific instances. Since Union of India is represented by learned Solicitor General and all the States are represented through their respective counsel, we expect that both the Union of India and States and all their functionaries should adhere to the Order passed by this Court on 23rd September, 2013.” By an order dated 11 August 2015, a three judge Bench referred the issue as to whether privacy is a fundamental right to a bench of a larger strength of judges. The following interim directions were issued: “Having considered the matter, we are of the view that the balance of interest would be best served, till the matter is finally decided by a larger Bench if the Union of India or the UIDAI proceed in the following manner:-
1. The Union of India shall give wide publicity in the electronic and print media including radio and television networks that it is not mandatory for a citizen to obtain an Aadhaar card;
2. The production of an Aadhaar card will not be condition for obtaining any benefits otherwise due to a citizen;
3. The Unique Identification Number or the Aadhaar card will not be used by the respondents for any purpose other than the PDS Scheme and in particular for the purpose of distribution of foodgrains, etc. and cooking fuel, such as kerosene. The Aadhaar card may also be used for the purpose of the LPG Distribution Scheme;
4. The information about an individual obtained by the Unique Identification Authority of India while issuing an Aadhaar card shall not be used for any other purpose, save as above, except as may be directed by a Court for the purpose of criminal investigation.” On 15 October 2015, a Constitution Bench of this Court partially modified the order dated 11 August 2015, thus: “3…we are of the view that in paragraph 3 of the Order dated 11.08.2015, if we add, apart from the other two Schemes, namely, P.D.S. Scheme and the L.P.G. Distribution Scheme, the Schemes like
The Mahatma Gandhi National Rural Employment Guarantee Scheme (MGNREGS), National Social Assistance Programme (Old Age Pensions, Widow Pensions, Disability Pensions), Prime Minister’s Jan Dhan Yojana (PMJDY) and Employees’ Provident Fund Organisation (EPFO) for the present, it would not dilute earlier order passed by this Court. Therefore, we now include the aforesaid Schemes apart from the other two Schemes that this Court has permitted in its earlier order dated 11.08.2015.
4. We impress upon the Union of India that it shall strictly follow all the earlier orders passed by this Court commencing from 23.09.2013.
5. We will also make it clear that the Aadhaar card Scheme is purely voluntary and it cannot be made mandatory till the matter is finally decided by this Court one way or the other.” After the Aadhaar Act was enacted there was a challenge in All Bengal Minority Students Council v Union of India596, to a letter written to the Chief Secretaries/Administrators of all State Governments/Union territory Administrations by the Under Secretary to the Government of India, by which the requirement of the submission of Aadhaar for claiming benefits under a scheme was made mandatory.
By an order dated 14 September 2016, a two judge Bench directed as follows: “…we stay the operation and implementation of letters dated 14.07.2006 (i.e. Annexure P-5, P-6 and P-7) for Pre-Matric Scholarship Scheme, Post-Matric Scholarship Scheme and Merit-cum-Means Scholarship Scheme to the extent they have made submission of Aadhaar mandatory and direct the Ministry of Electronics and Information Technology, Government of India i.e. Respondent No.2 to remove Aadhaar number as a mandatory condition for student Registration form at the National Scholarship Portal of Ministry of Electronics and Information Technology, Government of India at the website http://scholarships.gov.in/newStudentRegFrm and stay the implementation of clause (c) of the ‘Important Instructions’ of the advertisement dated 20.08.2016 for the Pre-Matric Scholarship Scheme, Post-Matric Scholarship Scheme and Merit-cum-Means Scholarship Scheme, during the pendency of this writ petition.” It has been submitted that the notifications and circulars, which make the application of Aadhaar mandatory, are contrary to the interim orders passed by this Court. It has been contended that the Respondents have flouted the most elementary norms of good governance and have disrespected judicial orders. This contention requires serious consideration. 333 The legislature cannot simply declare that the judgment of a court is invalid or that it stands nullified. In Kalpana Mehta, a Constitution Bench of this Court held:
“255…If the legislature were permitted to do so, it would travel beyond the boundaries of constitutional entrustment. While the separation of powers prevents the legislature from issuing a mere declaration that a judgment is erroneous or invalid, the law-making body is entitled to enact a law which remedies the defects which have been pointed out by the court. Enactment of a law which takes away the basis of the judgment (as opposed to merely invalidating it) is permissible and does not constitute a violation of the separation doctrine. That indeed is the basis on which validating legislation is permitted.
“597 Where a final judgment or order of this Court is sought to be undone by an Act of Parliament, it is imperative that the basis of the Court’s judgment or order is removed. It has been held by this Court in Bhubaneshwar Singh v Union of India598: “11. From time to time controversy has arisen as to whether the effect of judicial pronouncements of the High Court or the Supreme Court can be wiped out by amending the legislation with retrospective effect. Many such Amending Acts are called Validating Acts, validating the action taken under the particular enactments by removing the defect in the statute retrospectively because of which the statute or the part of it had been declared ultra vires.
Such exercise has been held by this Court as not to amount to encroachment on the judicial power of the courts. The exercise of rendering ineffective the judgments or orders of competent courts by changing the very basis by legislation is a well-known device of validating legislation. This Court has repeatedly pointed out that such validating legislation which removes the cause of the invalidity cannot be considered to be an encroachment on judicial power. At the same time, any action in exercise of the power under any enactment which has been declared to be invalid by a court cannot be made valid by a Validating Act by merely saying so unless the defect which has been pointed out by the court is removed with retrospective effect.
The validating legislation must remove the cause of invalidity. Till such defect or the lack of authority pointed out by the court under a statute is removed by the subsequent enactment with retrospective effect, the binding nature of the judgment of the court cannot be ignored.”599
(Emphasis supplied)
When the Aadhaar Act was notified on 25 March 2016, the interim directions issued by this court were in operation. Was it then open to government to launch upon a virtual spree of administrative notifications making Aadhaar a mandatory requirement of virtually every aspect of human existence from birth until death? The position which the Union government has adopted before this court is simply this: interim directions were issued by this court when the Aadhaar project was governed by executive instructions. Once a law was enacted by Parliament, a statutory authorisation was brought into existence to enable government to issue administrative instructions.
Hence, compliance with the interim orders stands obviated upon the enactment of the law.
334 This defence of government can be scrutinized at two levels – the first as a matter of statutory interpretation and the second, on a broader foundation which engages the judicial power of this court. As a matter of statutory interpretation, the Aadhaar Act did not, as it could not have, merely nullified the interim orders of this court. Section 59 has no provision which gives it overriding effect notwithstanding any judgment, decree or order of a court.
The interim orders do not stand superseded. Apart from approaching the issue purely as a matter of statutory interpretation, there are broader concerns which arise from the manner in which the authorities proceeded, oblivious to the interim directions. Interim directions were issued by this court in a situation where a constitutional challenge was addressed in a batch of petitions on the ground that the Aadhaar project was offensive to fundamental rights, including the right to privacy. So significant was the nature of the challenge that it was referred initially to a Constitution Bench and thereafter, to a bench of nine-judges of this Court for resolving the question as to whether privacy is a protected fundamental right.
The collection and storage of biometric data and its use for the purpose of authentication is the subject of a constitutional challenge. Noting the nature of the challenge and after considering the serious issues which have arisen in the case, successive benches of this Court issued a series of interim directions. The purport of those directions is that Aadhaar could not be made mandatory except for specified schemes which were listed by the court. Moreover, in the context of the serious grievance of financial exclusion, the court directed that no individual should be excluded from the receipt of welfare entitlements, such as food-grains, for want of an Aadhaar number. The constitutional challenge was not obviated merely on the enactment of the Aadhaar Act.
The law gave a statutory character to a project which since 2009 was possessed of an administrative or executive nature. The constitutional challenge to some of the basic features underlying the collection of biometric data still remained to be addressed by the court. The proceedings before this Court are testimony to the fact that the issue of constitutionality was indeed live. That being the position, the issuance of a spate of administrative notifications is in defiance of the interim orders passed by this Court. Judicial orders, be they interim or final, cannot simply be wished away. If governments or citizens were allowed to ignore judicially enforceable directions, that would negate the basis of the rule of law.
Both propriety and constitutional duty required Union government to move this Court after the enactment of the Aadhaar Act for variation of the interim orders. Such an application would have required this Court to weigh on the one hand the subsequent development of the law being passed (something which would be relied upon by government) with the constitutional concerns over the entire biometric project. It is not as if that the mere enactment of the law put an end to the constitutional challenge. The existence of law (post 2016) is only one aspect to be considered in deciding the interim arrangement which would hold the field when the constitutional challenge was pending adjudication before this Court. Institutions of governance are bound by a sense of constitutional morality which requires them to abide by judicial orders.
What seems to emerge from the course of action which has been followed in the present case by government is a perception that judicial directions can be ignored on a supposed construction of the statute. Besides the fact that this construction is erroneous in law, it is above all, the fundamental duty of this Court to ensure that its orders are not treated with disdain. If we were not to enforce a punctilious compliance with our own directions by government, that would ring a death – knell of the institutional position of the Supreme Court. If governments were free to ignore judicial directions at will, could a different yardstick be applied to citizens?
The obligation to comply with judicial orders is universal to our polity and admits of no exception. Confronted with a brazen disregard of our interim orders, I believe that we have no course open except to stand firm.
335 The power of judicial review conferred on an independent judiciary requires that other organs of the State respect the authority of Courts. This Court in P Sambamurthy v State of Andhra Pradesh600, while highlighting the importance of judicial review in the rule of law regime, held thus: “4… it is a basic principle of the rule of law that the exercise of power by the executive or any other authority must not only be conditioned by the Constitution but must also be in accordance with law and the power of judicial review is conferred by the Constitution with view to ensuring that the law is observed and there is compliance with the requirement of law on the part of the executive and other authorities. It is through the power of judicial review conferred on an independent institutional authority such as the High Court that the rule of law is maintained and every organ of the State is kept within the limits- of the law.
Now if the exercise of the power of judicial review can be set at naught by the State Government by overriding the decision given against it, it would sound, the death-knell of the rule of law. The rule of law would cease to have any meaning, because then it would be open to the State Government to defy the law and yet get away with it.”601
(Emphasis supplied)
A Bench of two judges in Re: Arundhati Roy602 held that for the courts to protect the rule of law, it is necessary that the dignity and authority of the courts have to be respected and protected.
It was held: “‘Rule of Law’ is the basic rule of governance of any civilised democratic policy. Our Constitutional scheme is based upon the concept of Rule of Law which we have adopted and given to ourselves. Everyone, whether individually or collectively is unquestionably under the supremacy of law. Whoever the person may be, however high he or she is, no-one is above the law notwithstanding how powerful and how rich he or she may be. For achieving the establishment of the rule of law, the Constitution has assigned the special task to the judiciary in the country.
It is only through the courts that the rule of law unfolds its contents and establishes its concept. For the judiciary to perform its duties and functions effectively and true to the spirit with which it is sacredly entrusted, the dignity and authority of the courts have to be respected and protected at all costs.”603
(Emphasis supplied)
The accountability of power, as a component of the rule of law, requires that the power vested in any organ of the State, and its agents, can only be used for promotion of constitutional values and vision.604 Governmental authority may only be exercised in accordance with written laws which are adopted though an established procedure. No action of the legislature or the executive can undermine the authority of the courts, except according to established principles.
Disrespect of court orders results in impairment of the dignity of the courts. Constitutional morality requires a government not to act in a manner which would become violative of the rule of law.605 Constitutional morality requires that the orders of this Court be complied with, faithfully. This Court is the ultimate custodian of the Constitution. The limits set by the Constitution are enforced by this Court. Constitutional morality requires that the faith of the citizens in the constitutional courts of the country be maintained. The importance of the existence of courts in the eyes of citizens has been highlighted in Harper Lee’s classic
“To Kill a Mockingbird”: “But there is one way in this country in which all men are created equal- there is one human institution that makes a pauper the equal of a Rockefeller, the stupid man the equal of an Einstein, and the ignorant man the equal of any college president. That institution, gentlemen, is a court. It can be the Supreme Court of the United States or the humblest J.P. court in the land, or this honorable court which you serve. Our courts have their faults, as does any human institution, but in this country our courts are the great levelers, and in our courts all men are created equal.”
(Emphasis supplied)
Many citizens, although aggrieved, are not in a condition to reach the highest Court. The poorest and socially neglected lack resources and awareness to reach this Court. Their grievances remain unaddressed. Such individuals suffer injury each day without remedy. Disobedience of the interim orders of this Court and its institutional authority, in the present case, has made a societal impact. It has also resulted in denial of subsidies and other benefits essential to the existence of a common citizen. Constitutional morality therefore needs to be enforced as a valid response to these arbitrary acts. Non-compliance of the interim orders of this Court is contrary to constitutional morality. Constitutional morality, as an essential component of the rule of law, must neutralise the excesses of power by the executive.
The brazen manner in which notifications have been issued making Aadhaar mandatory, despite the interim order of this Court is a matter of serious concern. Deference to the institutional authority of the Supreme Court is integral to the values which the Constitution adopts. The postulate of a limited government is enforced by the role of the Supreme Court in protecting the liberties of citizens and holding government accountable for its transgressions. The authority of this Court is crucial to maintaining the fine balances of power on which democracy thrives and survives.
The orders of the Court are not recommendatory – they are binding directions of a constitutional adjudicator. Dilution of the institutional prestige of this Court can only be at the cost of endangering the freedom of over a billion citizens which judicial review seeks to safeguard. 338 Courts – as it is often said- have neither the power of the purse nor the sword. Our authority lies in constitutional legitimacy as much as in public confidence. Combined together they impart moral and institutional authority to the Court. That sense of legitimacy and duty have required me to assert once again the norms of a written Constitution and the rule of law. This judgment has taken a much wider postulation. Having held the Aadhaar Act prior to its passage not to be a Money Bill, I have delved into the merits of the constitutional challenge for two reasons: PART L 461
i. Merits have been argued in considerable detail both by petitioners and the Union of India; and
ii. As a logical consequence of the view that the Aadhaar legislation is not a Money Bill, it would be open to the government to reintroduce fresh legislation.
The principles governing a law regulating the right to data protection and informational privacy have hence been delineated.
L Conclusion
339 The present dispute has required this Court to analyze the provisions of the Aadhaar Act and Regulations, along with the framework as it existed prior to the enactment of the Act, through the prism of the Constitution and the precedents of this Court. My conclusions are outlined below: (1) In order to deal with the challenge that the Aadhaar Act should not have been passed as a Money Bill, this Court was required to adjudicate whether the decision of the Speaker of the Lok Sabha to certify a Bill as a Money Bill, can be subject to judicial review.
The judgment has analyzed the scope of the finality attributed to the Speaker’s decision, by looking at the history of Article 110(3) of the Constitution, by comparing it with the comparative constitutional practices which accord finality to the Speaker’s decision, by analyzing other constitutional provisions which use the phrase
462 “shall be final”, and by examining the protection granted to parliamentary proceedings under Article 122. This judgment holds that: (a) The phrase “shall be final” used under Article 110(3) aims at avoiding any controversy on the issue as to whether a Bill is a Money Bill, with respect to the Rajya Sabha and before the President.
The language used in Article 110(3) does not exclude judicial review of the Speaker’s decision. This also applies to Article 199(3).
(b) The immunity from judicial review provided to parliamentary proceedings under Article 122 is limited to instances involving “irregularity of procedure”. The decisions of this Court in Special Reference, Ramdas Athawale and Raja Ram Pal hold that the validity of proceedings in Parliament or a State Legislature can be subject to judicial review when there is a substantive illegality or a constitutional violation. These judgments make it clear that the decision of the Speaker is subject to judicial review, if it suffers from illegality or from a violation of constitutional provisions.
(c) Article 255 has no relation with the decision of the Speaker on whether a Bill is a Money Bill. The three Judge Bench decision in Mohd Saeed Siddiqui erroneously interpreted the judgment in Mangalore Beedi to apply Articles 212 (or Article 122) and 255 to refrain from questioning the conduct of the Speaker (under Article 199 or 110). The two judge Bench decision in Yogendra Kumar followed Mohd Saeed Siddiqui. The correct position of law is that the decision of the Speaker under Articles 110(3) and 199(3) is not immune from judicial review. The decisions in Mohd Saeed Siddiqui and Yogendra Kumar are accordingly overruled.
(d) The existence of and the role of the Rajya Sabha, as an institution of federal bicameralism in the Indian Parliament, constitutes a part of the basic structure of the Constitution. The decision of the Speaker of the Lok Sabha to certify a Bill as a Money Bill has a direct impact on the role of the Rajya Sabha, since the latter has a limited role in the passing of a Money Bill.
A decision of the Speaker of the Lok Sabha to declare an ordinary Bill to be a Money Bill limits the role of the Rajya Sabha. The power of the Speaker cannot be exercised arbitrarily in violation of constitutional norms and values, as it damages the essence of federal bicameralism, which is a part of the basic structure of the Constitution. Judicial review of the Speaker’s decision, on whether a Bill is a Money Bill, is therefore necessary to protect the basic structure of the Constitution.
(2) To be certified a Money Bill, a Bill must contain “only provisions” dealing with every or any one of the matters set out in sub-clauses (a) to (g) of Article 110(1). A Bill, which has both provisions which fall within subclauses (a) to (g) of Article 110(1) and provisions which fall outside their scope, will not qualify to be a Money Bill. Thus, when a Bill which has been passed as a Money Bill has certain provisions which fall beyond the scope of sub-clauses (a) to (g) of Article 110(1), these provisions cannot be severed. If the bill was not a Money Bill, the role of the Rajya Sabha in its legislative passage could not have been denuded. The debasement of a constitutional institution cannot be countenanced by the Court. Democracy survives when constitutional institutions are vibrant.
(3) The Aadhaar Act creates a statutory framework for obtaining a unique identity number, which is capable of being used for “any” purpose, among which availing benefits, subsidies and services, for which expenses are incurred from the Consolidated Fund of India, is just one purpose provided under Section 7. Clause (e) of Article 110(1) requires that a Money Bill must deal with the declaring of any expenditure to be expenditure charged on the Consolidated Fund of India (or increasing the amount of the expenditure).
Section 7 fails to fulfil this requirement. Section 7 does not declare the expenditure incurred to be a charge on the Consolidated Fund. It only provides that in the case of such services, benefits or subsidies, Aadhaar can be made mandatory to avail of them. Moreover, provisions other than Section 7 of the Act deal with several aspects relating to the Aadhaar numbers: enrolment on the basis of demographic and biometric information, generation of Aadhaar numbers, obtaining the consent of individuals before collecting their individual information, creation of a statutory authority to implement and supervise the process, protection of information collected during the process, disclosure of information in certain circumstances, creation of offences and penalties for disclosure or loss of information, and the use of the Aadhaar number for “any purpose”.
All these provisions of the Aadhaar Act do not lie within the scope of sub-clauses (a) to (g) of Article 110(1). Hence, in the alternate, even if it is held that Section 7 bears a nexus to the expenditure incurred from the Consolidated Fund of India, the other provisions of the Act fail to fall within the domain of Article 110(1). Thus, the Aadhaar Act is declared unconstitutional for failing to meet the necessary requirements to have been certified as a Money Bill under Article 110(1).
(4) The argument that the Aadhaar Act is in pith and substance a Money Bill, with its main objective being the delivery of subsidies, benefits and services flowing out of the Consolidated Fund of India and that the other provisions are ancillary to the main purpose of the Act also holds no ground, since the doctrine of pith and substance is used to examine whether the legislature has the competence to enact a law with regard to any of the three Lists in the Seventh Schedule of the Constitution. The doctrine cannot be invoked to declare whether a Bill satisfies the requirements set out in Article 110 of the Constitution to be certified a Money Bill. The argument of the Union of India misses the point that a Bill PART L 466 can be certified as a Money Bill “only” if it deals with all or any of the matters contained in clauses (a) to (g) of Article 110(1).
(5) Having held that the Aadhaar Act is unconstitutional for having been passed as a Money Bill this judgment has also analysed the merits of the other constitutional challenges to the legislation as well as to the framework of the project before the law was enacted.
(6) The architecture of the Aadhaar Act seeks to create a unique identity for residents on the basis of their demographic and biometric information. The Act sets up a process of identification by which the unique identity assigned to each individual is verified with the demographic and biometric information pertaining to that individual which is stored in a centralised repository of data. Identification of beneficiaries is integral and essential to the fulfilment of social welfare schemes and programmes, which are a part of the State’s attempts to ensure that its citizens have access to basic human facilities. This judgment accepts the contention of the Union of India that there is a legitimate state aim in maintaining a system of identification to ensure that the welfare benefits provided by the State reach the beneficiaries who are entitled, without diversion.
(7) The Aadhaar programme involves application of biometric technology, which uses an individual’s biometric data as the basis of authentication or identification and is therefore intimately connected to the individual. While PART L 467 citizens have privacy interests in personal or private information collected about them, the unique nature of biometric data distinguishes it from other personal data, compounding concerns regarding privacy protections safeguarding biometric information. Once a biometric system is compromised, it is compromised forever.
Therefore, it is imperative that concerns about protecting privacy must be addressed while developing a biometric system. Adequate norms must be laid down for each step from the collection to retention of biometric data. At the time of collection, individuals must be informed about the collection procedure, the intended purpose of the collection, the reason why the particular data set is requested and who will have access to their data. Additionally, the retention period must be justified and individuals must be given the right to access, correct and delete their data at any point in time, a procedure familiar to an opt-out option.
(8) Prior to the enactment of the Aadhaar Act, no mandatory obligation was imposed upon the Registrars or the enrolling agencies, to obtain informed consent from residents before recording their biometric data, to inform them how the biometric data would be stored and used and about the existence of adequate safeguards to secure the data. Moreover, prior to the enactment of the Act, while UIDAI had itself contemplated that an identity theft could occur at the time of enrollment for Aadhaar cards, it had no solution to the possible harms which could result after the identity theft of a person.
(9) The Regulations framed subsequently under the Aadhaar Act also do not provide a robust mechanism on how informed consent is to be obtained from residents before collecting their biometric data. The Aadhaar Act and Regulations are bereft of the procedure through which an individual can access information related to his or her authentication record. The Aadhaar Act clearly has no defined options that should be made available to the Aadhaar number holders in case they do not wish to submit identity information during authentication, nor do the regulations specify the procedure to be followed in case the Aadhaar number holder does not provide consent for authentication.
(10) Sections 29(1) and (2) of the Act create a distinction between two classes of information (core biometric information and identity information), which are integral to individual identity and require equal protection. Section 29(4) suffers from overbreadth as it gives wide discretionary power to UIDAI to publish, display or post core biometric information of an individual for purposes specified by the regulations.
(11) Sections 2(g), (j), (k) and (t) suffer from overbreadth, as these can lead to an invasive collection of biological attributes. These provisions give PART L 469 discretionary power to UIDAI to define the scope of biometric and demographic information and empower it to expand on the nature of information already collected at the time of enrollment, to the extent of also collecting any “such other biological attributes” that it may deem fit.
(12) There is no clarity on how an individual is supposed to update his/her biometric information, in case the biometric information mismatches with the data stored in CIDR. The proviso to Section 28(5) of the Aadhaar Act, which disallows an individual access to the biometric information that forms the core of his or her unique ID, is violative of a fundamental principle that ownership of an individual’s data must at all times vest with the individual. UIDAI is also provided wide powers in relation to removing the biometric locking of residents. With this analysis of the measures taken by the Government of India prior to the enactment of the Aadhaar Act as well as a detailed analysis of the provisions under the Aadhaar Act, 2016 and supporting Regulations made under it, this judgment concludes that the Aadhaar programme violates essential norms pertaining to informational privacy, self-determination and data protection.
(13) The State is under a constitutional obligation to safeguard the dignity of its citizens. Biometric technology which is the core of the Aadhaar programme is probabilistic in nature, leading to authentication failures. These authentication failures have led to the denial of rights and legal entitlements. The Aadhaar project has failed to account for and remedy the flaws in its framework and design which has led to serious instances of exclusion of eligible beneficiaries as demonstrated by the official figures from Government records including the Economic Survey of India 2016-17 and research studies. Dignity and the rights of individuals cannot be made to depend on algorithms or probabilities. Constitutional guarantees cannot be subject to the vicissitudes of technology. Denial of benefits arising out of any social security scheme which promotes socioeconomic rights of citizens is violative of human dignity and impermissible under our constitutional scheme.
(14) The violations of fundamental rights resulting from the Aadhaar scheme were tested on the touchstone of proportionality. The measures adopted by the respondents fail to satisfy the test of necessity and proportionality for the following reasons: (a) Under the Aadhaar project, requesting entities can hold the identity information of individuals, for a temporary period. It was admitted by UIDAI that AUAs may store additional information according to their requirement to secure their system. ASAs have also been permitted to store logs of authentication transactions for a specific time period. It has been admitted by UIDAI that it gets the AUA code, ASA code, unique device code and the registered device code used for authentication, and that UIDAI would know from which device the authentication took place and through which AUA/ASA.
Under the Regulations, UIDAI further stores the authentication transaction data. This is in violation of widely recognized data minimisation principles which mandate that data collectors and processors delete personal data records when the purpose for which it has been collected is fulfilled. Moreover, using the meta-data related to the transaction, the location of the authentication can easily be traced using the IP address, which impacts upon the privacy of the individual.
(b) From the verification log, it is possible to locate the places of transactions by an individual in the past five years. It is also possible through the Aadhaar database to track the current location of an individual, even without the verification log. The architecture of Aadhaar poses a risk of potential surveillance activities through the Aadhaar database. Any leakage in the verification log poses an additional risk of an individual’s biometric data being vulnerable to unauthorised exploitation by third parties.
(c) The biometric database in the CIDR is accessible to third-party vendors providing biometric search and de-duplication algorithms, since neither the Central Government nor UIDAI have the source code for the deduplication technology which is at the heart of the programme.
The source code belongs to a foreign corporation. UIDAI is merely a licensee. Prior to the enactment of the Aadhaar Act, without the consent PART L 472 of individual citizens, UIDAI contracted with L-1 Identity Solutions (the foreign entity which provided the source code for biometric storage) to provide to it any personal information related to any resident of India. This is contrary to the basic requirement that an individual has the right to protect herself by maintaining control over personal information. The protection of the data of 1.2 billion citizens is a question of national security and cannot be subjected to the mere terms and conditions of a normal contract.
(d) Before the enactment of the Aadhaar Act, MOUs signed between UIDAI and Registrars were not contracts within the purview of Article 299 of the Constitution, and therefore, do not cover the acts done by the private entities engaged by the Registrars for enrolment. Since there is no privity of contract between UIDAI and the Enrolling agencies, the activities of the private parties engaged in the process of enrolment before the enactment of the Aadhaar Act have no statutory or legal backing.
(e) Under the Aadhaar architecture, UIDAI is the sole authority which carries out all administrative, adjudicatory, investigative, and monitoring functions of the project. While the Act confers these functions on UIDAI, it does not place any institutional accountability upon UIDAI to protect the database of citizens’ personal information. UIDAI also takes no institutional responsibility for verifying whether the data entered and stored in the CIDR is correct and authentic. The task has been delegated to the enrolment agency or the Registrar. Verification of data being entered in the CIDR is a highly sensitive task for which the UIDAI ought to have taken responsibility. The Aadhaar Act is also silent on the liability of UIDAI and its personnel in case of their non-compliance of the provisions of the Act or the regulations.
(f) Section 47 of the Act violates citizens’ right to seek remedies. Under Section 47(1), a court can take cognizance of an offence punishable under the Act only on a complaint made by UIDAI or any officer or person authorised by it. Section 47 is arbitrary as it fails to provide a mechanism to individuals to seek efficacious remedies for violation of their right to privacy. Further, Section 23(2)(s) of the Act requires UIDAI to establish a grievance redressal mechanism. Making the authority which is administering a project, also responsible for providing a grievance redressal mechanism for grievances arising from the project severely compromises the independence of the grievance redressal body.
(g) While the Act creates a regime of criminal offences and penalties, the absence of an independent regulatory framework renders the Act largely ineffective in dealing with data violations. The architecture of Aadhaar ought to have, but has failed to embody within the law the establishment of an independent monitoring authority (with a hierarchy of regulators), along with the broad principles for data protection. This compromise in the independence of the grievance redressal body impacts upon the possibility and quality of justice being delivered to citizens. In the absence of an independent regulatory and monitoring framework which provides robust safeguards for data protection, the Aadhaar Act cannot pass muster against a challenge on the ground of reasonableness under Article 14.
(h) No substantive provisions, such as those providing data minimization, have been laid down as guiding principles for the oversight mechanism provided under Section 33(2), which permits disclosure of identity information and authentication records in the interest of national security.
(i) Allowing private entities to use Aadhaar numbers, under Section 57, will lead to commercial exploitation of the personal data of individuals without consent and could also lead to individual profiling. Profiling could be used to predict the emergence of future choices and preferences of individuals. These preferences could also be used to influence the decision making of the electorate in choosing candidates for electoral offices. This is contrary to privacy protection norms. Data cannot be used for any purpose other than those that have been approved. While developing an identification system of the magnitude of Aadhaar, security concerns relating to the data of 1.2 billion citizens ought to be addressed. These issues have not been dealt with by the Aadhaar Act. By failing to protect the constitutional rights of citizens, Section 57 violates Articles 14 and 21.
(j) Section 57 is susceptible to be applied to permit commercial exploitation of the data of individuals or to affect their behavioural patterns. Section 57 cannot pass constitutional muster. Since it is manifestly arbitrary, it suffers from overbreadth and violates Article 14.
(k) Section 7 suffers from overbreadth since the broad definitions of the expressions ‘services and ‘benefits’ enable the government to regulate almost every facet of its engagement with citizens under the Aadhaar platform. If the requirement of Aadhaar is made mandatory for every benefit or service which the government provides, it is impossible to live in contemporary India without Aadhaar. The inclusion of services and benefits in Section 7 is a pre-cursor to the kind of function creep which is inconsistent with the right to informational self-determination. Section 7 is therefore arbitrary and violative of Article 14 in relation to the inclusion of services and benefits as defined.
(l) The legitimate aim of the State can be fulfilled by adopting less intrusive measures as opposed to the mandatory enforcement of the Aadhaar scheme as the sole repository of identification. The State has failed to demonstrate that a less intrusive measure other than biometric PART L 476 authentication would not subserve its purposes. That the state has been able to insist on an adherence to the Aadhaar scheme without exception is a result of the overbreadth of Section 7.
(m) When Aadhaar is seeded into every database, it becomes a bridge across discreet data silos, which allows anyone with access to this information to re-construct a profile of an individual’s life. This is contrary to the right to privacy and poses severe threats due to potential surveillance.
(n) One right cannot be taken away at the behest of the other. The State has failed to satisfy this Court that the targeted delivery of subsidies which animate the right to life entails a necessary sacrifice of the right to individual autonomy, data protection and dignity when both these rights are protected by the Constitution.
(15) Section 59 of the Aadhaar Act seeks to retrospectively validate the actions of the Central Government done prior to the Aadhaar Act pursuant to Notifications dated 28 January 2009. and 12 September 2015. Section 59 does not validate actions of the state governments or of private entities. Moreover, the notification of 2009 did not authorise the collection of biometric data. Consequently, the validation of actions taken under the 2009 notification by Section 59 does not save the collection of biometric data prior to the enforcement of the Act. While Parliament possesses the competence to enact a validating law, it must cure the cause of infirmity or invalidity. Section 59 fails to cure the cause of invalidity prior to the enactment of the Aadhaar Act.
The absence of a legislative framework for the Aadhaar project between 2009 and 2016 left the biometric data of millions of Indian citizens bereft of the kind of protection which must be provided to comprehensively protect and enforce the right to privacy. Section 59 therefore fails to meet the test of a validating law since the complete absence of a regulatory framework and safeguards cannot be cured merely by validating what was done under the notifications of 2009 and 2016.
(16) The decision in Puttaswamy recognised that revenue constitutes a legitimate state aim in the three-pronged test of proportionality. However, the existence of a legitimate aim is insufficient to uphold the validity of the law, which must also meet the other parameters of proportionality spelt out in Puttaswamy.
(17) The seeding of Aadhaar with PAN cards depends on the constitutional validity of the Aadhaar legislation itself. Section 139AA of the Income Tax Act 1962 is based on the premise that the Aadhaar Act itself is a valid legislation. Since the Aadhaar Act itself is now held to be unconstitutional for having been enacted as a Money Bill and on the touchstone of proportionality, the seeding of Aadhaar to PAN under Article 139AA does not stand independently.
(18) The 2017 amendments to the PMLA Rules fail to satisfy the test of proportionality. The imposition of a uniform requirement of linking Aadhaar numbers with all account based relationships proceeds on the presumption that all existing account holders as well as every individual who seeks to open an account in future is a potential money-launderer. No distinction has been made in the degree of imposition based on the client, the nature of the business relationship, the nature and value of the transactions or the actual possibility of terrorism and money- laundering.
The rules also fail to make a distinction between opening an account and operating an account. Moreover, the consequences of the failure to submit an Aadhaar number are draconian. In their present form, the rules are clearly disproportionate and excessive. We clarify that this holding would not preclude the Union Government in the exercise of its rule making power and the Reserve Bank of India as the regulator to re-design the requirements in a manner that would ensure due fulfillment of the object of preventing money-laundering, subject to compliance with the principles of proportionality as outlined in this judgment. (19) Mobile phones have become a ubiquitous feature of the lives of people and the linking of Aadhaar numbers with SIM cards and the requirement of e-KYC authentication of mobile subscribers must necessarily be viewed in this light. Applying the proportionality test, the legitimate aim of subscriber verification, has to be balanced against the countervailing requirements of preserving the integrity of biometric data and the privacy of mobile phone subscribers. Mobile phones are a storehouse of personal data and reflect upon individual preferences, lifestyle and choices. The conflation of biometric information with SIM cards poses grave threats to individual privacy, liberty and autonomy. Having due regard to the test of proportionality which has been propounded in Puttaswamy and as elaborated in this judgment, the decision to link Aadhaar numbers with mobile SIM cards is neither valid nor constitutional.
The mere existence of a legitimate state aim will not justify the disproportionate means which have been adopted in the present case. The biometric information and Aadhaar details collected by Telecom Service Providers shall be deleted forthwith and no use of the said information or details shall be made by TSPs or any agency or person or their behalf.
(20) Defiance of judicial orders (both interim and final) be it by the government or by citizens negates the basis of the rule of law. Both propriety and constitutional duty required the Union government to move this Court after the enactment of the Aadhaar Act for variation of this Court’s interim orders. Institutions of governance are bound by a sense of constitutional morality which requires them to abide by judicial orders.
(21) Identity is necessarily a plural concept. The Constitution also recognizes a multitude of identities through the plethora of rights that it safeguards. PART L 480 The technology deployed in the Aadhaar scheme reduces different constitutional identities into a single identity of a 12-digit number and infringes the right of an individual to identify herself/himself through a chosen means. Aadhaar is about identification and is an instrument which facilitates a proof of identity. It must not be allowed to obliterate constitutional identity.
(22) The entire Aadhaar programme, since 2009, suffers from constitutional infirmities and violations of fundamental rights. The enactment of the Aadhaar Act does not save the Aadhaar project. The Aadhaar Act, the Rules and Regulations framed under it, and the framework prior to the enactment of the Act are unconstitutional.
(23) To enable the government to initiate steps for ensuring conformity with this judgment, it is directed under Article 142 that the existing data which has been collected shall not be destroyed for a period of one year. During this period, the data shall not be used for any purpose whatsoever. At the end of one year, if no fresh legislation has been enacted by the Union government in conformity with the principles which have been enunciated in this judgment, the data shall be destroyed. Creating strong privacy protection laws and instilling safeguards may address or at the very least assuage some of the concerns associated with the Aadhaar scheme which severely impairs informational self-determination, individual privacy, dignity and autonomy. In order to uphold the democratic values of the Constitution, the government needs to address the concerns highlighted in this judgment which would provide a strong foundation for digital initiatives, which are imminent in today’s digital age. However, in its current form, the Aadhaar framework does not sufficiently assuage the concerns that have arisen from the operation of the project which have been discussed in this judgment.
………………………………………………….J [Dr Dhananjaya Y Chandrachud]
New Delhi;
September 26, 2018.
1 (2017) 10 SCC 1 5
2 Granville Austin, Working a Democratic Constitution: A History of the Indian Experience, Oxford University Press (2003) at page 6
3 Lon L. Fuller and Kenneth I. Winston, The Forms and Limits of Adjudication, Harvard Law Review, Vol. 92, (1978), at pages 353-409
4 Kwame Anthony Appiah, The Lies That Bind: Rethinking Identity, Liveright Publishing (2018).
5 Francis Fukuyama, Identity: The Demand for Dignity and the Politics of Enlightenment, Farrar, Straus and Giroux (2018).
6 Anand Giridharadas, ‘What is Identity?’, The New York Times, 27 August, 2018. 7 Peter F Drucker, The Age of Discontinuity: Guidelines to Our Changing Society, Harper & Row (1969). Drucker’s book popularized the term ‘Knowledge Economy’.
8 ‘What is Knowledge Economy?’, IGI Global: Disseminator of Knowledge, available at: https://www.igi-global.com/dictionary/indigenous-knowledges-and-knowledge-codification-in-the-knowledgeeconomy/ 16327
9 Krishnadas Rajagopal, ‘Aadhaar in numbers: key figures from UIDAI CEO’s presentation to the Supreme Court’, The Hindu, (March 22, 2018). Aadhaar enrollment as of March 2018 stood at over 1 billion.
10 Upendra Baxi, The Right To Be Human: Some Heresies, India International Centre Quarterly, Vol. 13, (1986).
11 Justice K S Puttaswamy (Retd) v Union of India (“Puttaswamy”), (2017) 10 SCC 1
12 Ibid, at page 365
13 Ibid, at page 508
14 Ibid, at pages 536-537
15 Ibid, at page 605
16 Ibid, at page 614
17 Ibid, at page 403
18 Ibid, at page 484
19 Ibid, at pages 481-482
20 Ibid, at page 482
21 Ibid, at pages 406-407
22 Ibid, at page 413
23 Ibid, at page 508
24 Ibid, at page 499
25 Ibid, at page 543
26 Ibid, at page 544
27 Ibid, at page 401
28 Ibid, at page 508
29 Ibid, at page 531
30 Ibid, at pages 541-542
31 Ibid, at page 598
32 Ibid, at page 509
33 Ibid, at page 545
34 Ibid, at page 627
35 Ibid, at page 629
36 Ibid, at pages 580-581
37 Ibid, at page 509
38 Ibid, at page 583
39 Ibid, at page 532
40 Ibid, at pages 532-533
41 Ibid, at page 549
42 Ibid, at page 580
43 Ibid, at page 601
44 Ibid, at page 601
45 Ibid, at page 505
46 Ibid, at page
47 (2014) 5 SCC 438
48 (2016) 7 SCC 221
49 (2017) 7 SCC 59
50 (2017) 9 SCC 1
51 (2011) 14 SCC 331
52 Modern Dental College and Research Centre v State of Madhya Pradesh, (2016) 7 SCC 353.
54 Section 10, Aadhaar Act
55 Section 2(v) states: “resident” means an individual who has resided in India for a period or periods amounting in all to one hundred and eighty-two days or more in the twelve months immediately preceding the date of application for enrolment
56 Section 2(s) states: “Registrar” means any entity authorised or recognised by the Authority for the purpose of enrolling individuals under this Act
57 Regulation 7, Aadhaar (Enrolment and Update) Regulations, 2016
58 Section 3(2), Aadhaar Act.
59 Section 8(3), Aadhaar Act
60 Section 8(4), Aadhaar Act
61 Section 11(2), Aadhaar Act
62 Section 28(1), Aadhaar Act
63 Section 28(2), Aadhaar Act
64 Section 33, Aadhaar Act
65 Section 32(1), Aadhaar Act
66 Section 32(2), Aadhaar Act
67 Article 109(2), The Constitution of India
68 Article 109(3), The Constitution of India
69 Article 109(4), The Constitution of India
70 Article 109(5), The Constitution of India
71 Article 110(4), The Constitution of India
72 Article 199(4), The Constitution of India
73 Thomas Erskine May, A treatise on the law, privileges, proceedings and usage of Parliament, Ninth Edition (1883)
74 Ibid, at pages 637-638. It notes: “At length, when the Commons had increased in political influence, and the subsidies voted by them had become the principal source of national revenue, they gradually assumed their present position in regard to taxation and supply, and included the Lords as well as themselves in their grants. So far back as 1407, it was stated by King Henry IV, in the ordinance called “The Indemnity of the Lords and Commons”, that grants were “granted by the Commons, and assented to by the Lords”.”
75 Ibid, at page 638
76 Ibid, at page 641. The Resolution stated:
“That in all aids given to the king by the Commons, the rate or tax ought not to be altered”.
77 Ibid. The Resolution stated: “That all aids and supplies, and aids to his Majesty in Parliament, are the sole gift of the Commons ; and all bills for the granting of any such aids and supplies ought to begin with the Commons : and that it is the undoubted and sole right of the Commons to direct, limit, and appoint in such bills the ends, purposes, considerations, conditions, limitations, and qualifications of such grants ; which ought not to be changed or altered by the House of Lords.”
78 Ibid, at pages 642-643
79 Ibid, pages 646-647
80 Preamble of the Parliament Act 1911
81 Ibid
82 House of Lords, Select Committee on the Constitution, Money Bills and Commons Financial Privilege (2011), available at https://publications.parliament.uk/pa/ld201011/ldselect/ldconst/97/97.pdf
83 B Shiva Rao, The Framing of India’s Constitution: A Study, Indian Institution of Public Administration (1968), at page 420
84 Ibid
85 Ibid, at pages 427-428
86 The said provision provides: “Powers of the Houses in respect of legislation. Proposed laws appropriating revenue or moneys, or imposing taxation, shall not originate in the Senate. But a proposed law shall not be taken to appropriate revenue or moneys, or to impose taxation, by reason only of its containing provisions for the imposition or appropriation of fines or other pecuniary penalties, or for the demand or payment or appropriation of fees for licences, or fees for services under the proposed law. The Senate may not amend proposed laws imposing taxation, or proposed laws appropriating revenue or moneys for the ordinary annual services of the Government. The Senate may not amend any proposed law so as to increase any proposed charge or burden on the people. The Senate may at any stage return to the House of Representatives any proposed law which the Senate may not amend, requesting, by message, the omission or amendment of any items or provisions therein. And the House of Representatives may, if it thinks fit, make any of such omissions or amendments, with or without modifications. Except as provided in this section, the Senate shall have equal power with the House of Representatives in respect of all proposed laws.”
87 B Shiva Rao, The Framing of India’s Constitution: Selected Documents, Indian Institution of Public Administration (2012), at page 32, as quoted in Pratik Datta, Shefali Malhotra & Shivangi Tyagi, Judicial Review and Money Bills, NUJS Law Review (2017)
88 Ibid
89 Lower House in Ireland
90 Upper House in Ireland
91 B Shiva Rao, The Framing of India’s Constitution: Selected Documents, Indian Institution of Public Administration, at page 281
92 Pratik Datta, Shefali Malhotra & Shivangi Tyagi, Judicial Review and Money Bills, NUJS Law Review (2017)
93 (2018) 7 SCC 1
94 Ibid, at para 227
95 Granville Austin, The Indian Constitution: Cornerstone of a Nation, Oxford University Press (1966), at page 205
96 Article 243O(a), which is a part of the chapter on Panchayats, provides:
“Notwithstanding anything in this Constitution,-
(a) the validity of any law relating to the delimitation of constituencies or the allotment of seats to such constituencies, made or purporting to be made under article 243K, shall not be called in question in any court.”
97 Article 243ZG(a), which is a part of the chapter on Municipalities, provides: “Notwithstanding anything in this Constitution,-
(a) the validity of any law relating to the delimitation of constituencies or the allotment of seats to such constituencies, made or purporting to be made under article 243ZA shall not be called in question in any court.”
98 1952 SCR 218
99 Ibid, at para 5
100 Article 217 (3) states: “If any question arises as to the age of a Judge of a High Court, the question shall be decided by the President after consultation with the Chief Justice of India and the decision of the President shall be final.”
101 Article 311(3) states: “If, in respect of any such person as aforesaid, a question arises whether it is reasonably practicable to hold such inquiry as is referred to in clause (2), the decision thereon of the authority empowered to dismiss or remove such person or to reduce him in rank shall be final.”
102 Paragraph 6(1) states “If any question arises as to whether a member of a House has become subject to disqualification under this Schedule, the question shall be referred for the decision of the Chairman, or, as the case may be, the Speaker of such House and his decision shall be final:
Provided that where the question which has arisen is as to whether the Chairman or the Speaker of a House has become subject to such disqualification, the question shall be referred for the decision of such member of the House as the House may elect in this behalf and his decision shall be final.”
103 (1971) 1 SCC 396
104 Ibid, at page 397
105 (1985) 3 SCC 398
106 (1992) Supp (2) SCC 651
107 Ibid, at page 711
108 Ibid, at page 708
109 (2017) 3 SCC 1
110 Ibid, at pages 76-77
111 AIR 1965 SC 745
112 (2010) 4 SCC 1
113 Ibid, at pages 13-14
114 (2007) 3 SCC 184
115 Ibid, at page 359
116 Ibid, at page 362
117 Ibid, at page 350
118 1963 Supp (1) SCR 275
119 Pratik Datta, Shefali Malhotra & Shivangi Tyagi, Judicial Review and Money Bills, Vol 10, NUJS Law Review (2017).
120 (2014) 11 SCC 415
121 AIR 1960 SC 1186
122 Mohd Saeed Siddiqui, Ibid, at page 430
123 (2016) 3 SCC 183
124 Ibid, at page 229
125 Corresponding provision for the Union is Article 110 of the Constitution. 126 Corresponding provision for the Union is Article 122 of the Constitution.
127 Fathali M. Moghaddam, The SAGE Encyclopaedia of Political Behaviour (2017).
128 Betty Drexhage, Bicameral Legislatures: An International Comparison, Ministry of the Interior and Kingdom Relations- Netherlands (2015), at page 7 129 Abhinay Muthoo & Kenneth A. Shepsle, The Constitutional Choice of Bicameralism, in Institutions and Economic Performance (Elhanan Helpman ed.), Harvard University Press (2008), at pages 251-252
130 Betty Drexhage, Bicameral Legislatures: An International Comparison, Ministry of the Interior and Kingdom Relations- Netherlands (2015), at page 7 131 Abhinay Muthoo & Kenneth A. Shepsle,
The Constitutional Choice of Bicameralism, in Institutions and Economic Performance (Elhanan Helpman ed.), Harvard University Press (2008), at page 252 132 Betty Drexhage, Bicameral Legislatures: An International Comparison, Ministry of the Interior and Kingdom Relations- Netherlands (2015), at page 8
133 Betty Drexhage, Bicameral Legislatures: An International Comparison, Ministry of the Interior and Kingdom Relations- Netherlands (2015), at page 7
134 James Madison, The Federalist No. 62 – The Senate, The Federalist Papers (1788), available at http://www.constitution.org/fed/federa62.html
135 William H. Riker, The Justification of Bicameralism, International Political Science Review (1992), Vol. 13, Issue 1, at pages 101-16.
136 Saul Levmore, Bicameralism: When Are Two Decisions Better than One?, International Review of Law and Economics (1992), Vol. 12, at pages 147-148.
137 Betty Drexhage, Bicameral Legislatures: An International Comparison, Ministry of the Interior and Kingdom Relations- Netherlands (2015).
138 Ibid, at pages 11-12
139 James N. Druckman & Michael F. Thies, The Importance of Concurrence: The Impact of Bicameralism on Government Formation and Duration, American Journal of Political Science (2002), Vol. 46, No. 4, at pages 760-771.
140 Elliot Bulmer, Bicameralism, International Institute for Democracy and Electoral Assistance (2017), at page 4
141 James R. Rogers, The Advantage of Second Chambers in Republican Legislatures: An Informational Theory, at page 6, available at https://ecpr.eu/Filestore/PaperProposal/beb20221-c2c5-4475-9b9f-74bb3f1512a7.pdf
142 Ibid
143 Granville Austin, The Indian Constitution: Cornerstone of a Nation, Oxford University Press (1966), at page 195
144 Granville Austin, The Indian Constitution: Cornerstone of a Nation, Oxford University Press (1966), at pages 180 & 203
145 Article 80(4), The Constitution of India
146 Article 80(5), The Constitution of India
147 Sidharth Chauhan, Bicameralism: comparative insights and lessons, Seminar (February, 2013) available at http://india-seminar.com/2013/642/642_sidharth_chauhan.html
148 In SR Bommai v Union of India (AIR 1994 SC 1998), a seven-judge Bench of this Court held: “Democracy and federalism are the essential features of our Constitution and are part of its basic structure.”
149 Rajya Sabha Secretariat, Second Chamber In Indian Parliament: Role and Status of Rajya Sabha, (2009), at page 2. See also M.N. Kaul and S.L. Shakdher, Practice and Procedure of Parliament, Lok Sabha Secretariat (2001)
150 H M Seervai, Constitutional Law of India, Universal Law Co. Pvt. Ltd, Vol. 1, (1991), at pages 299-300.
151 Rajya Sabha Secretariat, Second Chamber In Indian Parliament: Role and Status of Rajya Sabha, (2009), at page 6.
152 Rajya Sabha Secretariat, Structure and Functions of Rajya Sabha Secretariat, (2009), at pages 2-3
153 Under Article 83(1), the Rajya Sabha is a permanent body with members being elected for 6 year terms and one-third of the members retiring every 2 years.
154 Rajya Sabha Secretariat, Second Chamber In Indian Parliament: Role and Status of Rajya Sabha, (2009), at pages 7-8
155 (2006) 7 SCC 1
156 Ibid, at page 47 157 Rajya Sabha Secretariat, Second Chamber In Indian Parliament: Role and Status of Rajya Sabha, (2009), at page 5
158 Dr Ambedkar explained that the joint sitting had been kept at the centre because of the federal character of the Central Legislature. See Granville Austin, The Indian Constitution: Cornerstone of a Nation, Oxford University Press (1966), at page 202
159 Rajya Sabha Secretariat, Second Chamber In Indian Parliament: Role and Status of Rajya Sabha, (2009), at page 5
160 Hari Ram v. Baby Gokul Prasad, (1991) Supp (2) SCC 608; M/s Saru Smelting (P) Ltd. v. Commissioner of Sales Tax, Lucknow, (1993) Supp (3) SCC 97.
161 Constituent Assembly Debates (20 May 1949)
162 (2017) 3 SCC 1
163 Ibid, at page 61
164 Constituent Assembly Debates (4 November, 1948). Dr Ambedkar had remarked: “… it is perfectly possible to pervert the Constitution, without changing its form by merely changing the form of the administration and to make it inconsistent and opposed to the spirit of the Constitution.”
165 Section 2(v) provides: “resident” means an individual who has resided in India for a period or periods amounting in all to one hundred and eighty-two days or more in the twelve months immediately preceding the date of application for enrolment.
166 Section 3(3), Aadhaar Act
167 Section 2(h), Aadhaar Act
168 Section 2(c) provides: “authentication” means the process by which the Aadhaar number alongwith demographic information or biometric information of an individual is submitted to the Central Identities Data Repository for its verification and such Repository verifies the correctness, or the lack thereof, on the basis of information available with it.
169 Section 2 (u) provides: “requesting entity” means an agency or person that submits the Aadhaar number, and demographic information or biometric information, of an individual to the Central Identities Data Repository for authentication
170 Section 12, Aadhaar Act
171 Section 13, Aadhaar Act
172 Section 14, Aadhaar Act
173 Section 15, Aadhaar Act
174 Section 17, Aadhaar Act
175 Forty-Second Report, Standing Committee on Finance (2011-12), available at http://www.prsindia.org/uploads/media/UID/uid%20report.pdf
176 1957 SCR 399
177 (2008) 13 SCC 5
178 Ibid, at page 21
179 (2002) 8 SCC 228
180 Ibid, at pages 233-234
181 Constituent Assembly (25 November 1949)
182 Gary Roethenbaugh, (cited in A. Cavoukian, Privacy and Biometrics, Information and Privacy Commissioner, Ontario, Canada, 1999, page 11, available at http://www.ipc.on.ca/images/Resources/pri- biom.pdf
183 Els J. Kindt, Privacy and Data Protection Issues of Biometric Applications: A Comparative Legal Analysis, Springer (2013)
184 Ibid.
185 Ibid.
186 Ibid.
187 Nancy Yue Liu, Bio-Privacy: Privacy Regulations and the Challenge of Biometrics, Routledge (2013).
188 Privacy International, Biometrics: Friend or foe of privacy?, available at https://privacyinternational.org/sites/default/files/2017-11/Biometrics_Friend_or_foe.pdf
189 Ibid
190 Ibid
191 Simon Davies, as cited in John D. Woodward, Biometric Scanning, Law & Policy: Identifying the Concerns – Drafting the Biometric Blueprint, University of Pittsburgh Law Review, (1997)
192 Daniel M. L Storisteanu, Toby L. Norman, Alexandra Grigore and Alain B. Labrique, Can biometrics beat the developing world’s challenges?, Biometric Technology Today (2016)
193 Ibid
194 Ibid
195 Privacy International, Biometrics, available at https://privacyinternational.org/topics/biometrics
196 Privacy International, Biometrics: Friend or foe of privacy?, available at https://privacyinternational.org/sites/default/files/2017-11/Biometrics_Friend_or_foe.pdf
197 Ibid
198 Privacy International, Biometrics:
Friend or foe of privacy?, available at https://privacyinternational.org/sites/default/files/2017-11/Biometrics_Friend_or_foe.pdf
199 Nancy Yue Liu, Bio-Privacy: Privacy Regulations and the Challenge of Biometrics, Routledge (2013)
200 Ibid
201 Ibid
202 Nancy Yue Liu, Bio-Privacy: Privacy Regulations and the Challenge of Biometrics, Routledge (2013).
203 Ibid
204 Ibid
205 Pam Dixon, A Failure to Do No Harm – India’s Aadhaar biometric ID program and its inability to protect privacy in relation to measures in Europe and the U.S., Health and Technology (2017), Vol. 7, at pages 539- 567
206 Ibid.
207 Nancy Yue Liu, Bio-Privacy: Privacy Regulations and the Challenge of Biometrics, Routledge (2013).
208 Ibid
209 Segen’s Medical Dictionary, 2012.
210 Ministry of Communication & Information Technology, Department of Information Technology, Administrative Approval for the project – “Unique ID for BPL families”, dated March 03, 2006 (Annexure R-1, List of Preenactment dates and events for the Aadhaar project submitted by the Learned AG).
211 Department of Information Technology, Notification: Setting up of a Process Committee to suggest the processes for updation, modification, addition & deletion of data and fields from the core database to be created under the Unique ID for BPL families project, dated July 03, 2006 (Annexure R-2, List of Preenactment dates and events for the Aadhaar project submitted by the learned AG).
212 Strategic Vision: Unique Identification of Residents, dated 26 November 2006 (Annexure R-3, List of Preenactment dates and events for the Aadhaar project submitted by the learned AG).
213 Ibid
214 Ibid
215 Ibid
216 Ibid
217 Constitution of an Empowered Group of Ministers to collate two schemes – the National Population Register under the Citizenship Act, 1955 and the Unique Identification Number (UID) project of the Department of Information Technology (Annexure R-4, List of Pre-enactment dates and events for the Aadhaar project submitted by the learned AG).
218 Planning Commission, No. 4(4)/56/2005- C & I, Minutes of the Fifth Meeting of the Unique ID project under the Chairmanship of Dr. Arvind Virmani (Annexure R-6, List of Pre-enactment dates and events for the Aadhaar project submitted by the learned AG).
219 Minutes of the Second Meeting of the EGoM to collate two schemes – The National Population Register under the Citizenship Act, 1955 and the Unique Identification number (UID) project of the Department of Information Technology (Annexure R-10, List of Pre-enactment dates and events for the Aadhaar project submitted by the learned AG).
220 Minutes of the Fourth Meeting of the EGoM to collate two schemes – The National Population Register under the Citizenship Act, 1955 and the Unique Identification Number (UID) project of the Department of Information Technology (Annexure R-12, List of Pre-enactment dates and events for the Aadhaar project submitted by the learned AG).
221 Secretary, Government of India, Planning Commission, D.O. No. A-11016/02/09-UIDAI (Annexure R-22, List of Pre-enactment dates and events for the Aadhaar project submitted by the learned AG).
222 Planning Commission, Minutes of the meeting of the PM’s Council of UIDAI (Annexure R-35, List of Preenactment dates and events for the Aadhaar project submitted by the Learned AG).
223 Planning Commission, UIDAI, Office Memorandum, available at https://www.uidai.gov.in/images/resource/Biometric_Standards_Committee_Notification.pdf.
224 DDSVPC (UIDAI), DDSVPC Report, dated 09 December 2009, available at https://uidai.gov.in/images/UID_DDSVP_Committee_Report_v1.0.pdf ,at pages 5-6. 225 Ibid, at page 4
226 Annexure R-43, Volume II, List of Pre-enactment dates and events for the Aadhaar project, Submissions by the AG 227 UIDAI, UIDAI Strategy Overview, available at http://www.prsindia.org/uploads/media/UID/UIDAI%20STRATEGY%20OVERVIEW.pdf.
228 Annexure R-46, Volume II, List of Pre-enactment dates and events for the Aadhaar project, Submissions by the AG
229 UIDAI Committee on Biometrics, Biometrics Design Standards For UID Applications, at page 4
230 Ibid.”234
231 Identification for Development (World Bank Group), Technical Standards for Digital Identity Systems for Digital Identity Draft for Discussion, available at http://pubdocs.worldbank.org/en/579151515518705630/ID4DTechnical- Standards-for-Digital-Identity.pdf, at page 22.
232 Katie Bird, Is your biometric data safe online? ISO/IEC standard ensures security and privacy, (11 August 2011), available at https://www.iso.org/news/2011/08/Ref1452.html.
233 Ibid.
234 Ibid.
235 UIDAI, UIDAI Strategy Overview, available at http://www.prsindia.org/uploads/media/UID/UIDAI%20STRATEGY%20OVERVIEW. pdf, at page 4
236 Ibid.
237 Ibid, at page 32
238 Ibid.
239 Ibid, at page 33
240 Ibid.
241 Ibid, at page 34
242 DDSVPC (UIDAI), DDSVPC Report, (9 December 2009), available at https://uidai.gov.in/images/UID_DDSVP_Committee_Report_v1.0. pdf , at page 5 243 UIDAI, UIDAI Strategy Overview, available at http://www.prsindia.org/uploads/media/UID/UIDAI%20STRATEGY%20OVERVIEW.pdf, at page 2
244 Ibid, at page 15
245 UIDAI, Aadhaar Handbook for Registrars, available at http://doitc.rajasthan.gov.in/administrator/Lists/Downloads/Attachments/26/aadhaar_handbook_version. pdf, at page 11
246 Annexure R-74, Volume III, List of Pre-enactment dates and events for the Aadhaar project, Submissions by the AG.
247 UIDAI (Planning Commission), Aadhaar Handbook for Registrars (2010), available at http://indiamicrofinance.com/wp-content/uploads/2010/08/Aadhaar-Handbook. pdf, at page 11; UIDAI (Planning Commission), Aadhaar Handbook for Registrars (2013), at page 16 (Annexure R-74, List of Preenactment dates and events for the Aadhaar project submitted by the Learned AG).
248 UIDAI, Roles and Responsibilities of Enrolment Staff, available at https://idai.gov.in/images/annexure_b_roles_and_responsibility_of_enrolment_staff. Pdf , at page 8
249 UIDAI, Enrolment Process Essentials (13 December 2012), available at http://www.nictcsc.com/images/Aadhaar%20Project%20Training%20Module/English%20Training%20Module/ module2_aadhaar_enrolment_process17122012. pdf
250 Regulation 2(j) of Aadhaar (Authentication) Regulations: “e-KYC authentication facility” means a type of authentication facility in which the biometric information and/or OTP and Aadhaar number securely submitted with the consent of the Aadhaar number holder through a requesting entity, is matched against the data available in the CIDR, and the Authority returns a digitally signed response containing e-KYC data along with other technical details related to the authentication transaction.
251 Regulation 2(k) of Aadhaar Authentication Regulations: “e-KYC data” means demographic information and photograph of an Aadhaar number holder.
252 Regulation 3(ii) of Aadhaar (Authentication) Regulations, 2016: “3. Types of Authentication-There shall be two types of authentication facilities provided by the Authority, namely-
(i) Yes/No authentication facility, which may be carried out using any of the modes, (ii) e-KYC authentication facility, which may be carried out only using OTP and/ or biometric authentication modes as specified in regulation 4(2)”.
253 Section 29(4) states: “No Aadhaar number or core biometric information collected or created under this Act in respect of an Aadhaar number holder shall be published, displayed or posted publicly, except for the purposes as may be specified by regulations.”
254 Ramesh Subramanian, Computer Security, Privacy & Politics: Current Issues, Challenges & Solutions, IRM Press, at pages 99-100
255 Ibid, at page 100
256 Section 6 states: “The Authority may require Aadhaar number holders to update their demographic information and biometric information, from time to time, in such manner as may be specified by regulations, so as to ensure continued accuracy of their information in the Central Identities Data Repository.”
257 Section 31(2) states: “In case any biometric information of Aadhaar number holder is lost or changes subsequently for any reason, the Aadhaar number holder shall request the Authority to make necessary alteration in his record in the Central Identities Data Repository in such manner as may be specified by regulations.”
258 L. Vishwanath, Four Reasons You Should Worry About Aadhaar’s Use of Biometrics, The Wire (28 March, 2017), available at https://thewire.in/rights/real-problem-aadhaar-lies-biometrics PART F 215
259 Ibid.
260 Section 28(5) states: “Notwithstanding anything contained in any other law for the time being in force, and save as otherwise provided in this Act, the Authority or any of its officers or other employees or any agency “The Authority may enable an Aadhaar number holder to permanently lock his biometrics and temporarily unlock it when needed for biometric authentication.”
that maintains the Central Identities Data Repository shall not, whether during his service or thereafter, reveal any information stored in the Central Identities Data Repository or authentication record to anyone: Provided that an Aadhaar number holder may request the Authority to provide access to his identity information excluding his core biometric information in such manner as may be specified by regulations.”
261 L. Vishwanath, Four Reasons You Should Worry About Aadhaar’s Use of Biometrics, The Wire (28 March, 2017), available at https://thewire.in/rights/real-problem-aadhaar-lies-biometrics
262 The Centre for Internet & Society, Analysis of Key Provisions of the Aadhaar Act Regulations, (31 March, 2017), available at https://cis-india.org/internet-governance/blog/analysis-of-key-provisions-of-aadhaar-actregulations.
263 A. Cavoukian, Privacy and Biometrics, Information and Privacy Commissioner Canada (1999), available at http://www.ipc.on.ca/images/Resources/pri-biom.pdf
264 Robert Gellman. Privacy and Biometric ID Systems: An Approach Using Fair Information Practices for Developing Countries, CGD Policy Paper 028 Washington DC: Centre for Global Development (1 August 2013), available at https://www.cgdev.org/sites/default/files/privacy-and-biometric-ID-systems_0. pdf
265 Ibid
266 Ibid
267 John D Woodward, Biometrics: Identifying Law & Policy Concerns, in Biometrics (AK Jain A.K, R Bolle, and S Pankanti eds.), Springer (1996)
268 Robert Gellman, Privacy and Biometric ID Systems:
An Approach Using Fair Information Practices for Developing Countries, CGD Policy Paper 028 Washington DC: Centre for Global Development (1 August, 2013), available at https://www.cgdev.org/sites/default/files/privacy-and-biometric-ID-systems_0.pdf
269 Ibid
270 Ibid
271 Pam Dixon, A Failure to Do No Harm – India’s Aadhaar biometric ID program and its inability to protect privacy in relation to measures in Europe and the U.S., Health and Technology, Vol. 7 (2017), at pages 539-567
272 Ibid
273 General Data Protection Regulation, available at https://gdpr-info.eu/
274 Granville Austin, The Indian Constitution: Cornerstone of a Nation, Oxford University Press (1999) at page xxii 275 Ibid, at pages 62, xiii and xxii
276 Ibid, at page xxi
277 Ibid, at page 32
278 Arun K Thiruvengadam, The Constitution of India: A Contextual Analysis, (Bloomsbury 2017), at page 1
279 Granville Austin, The Indian Constitution: Cornerstone of a Nation, Oxford University Press (1999) at page 66
280 Ibid, at page 99
281 Article 37, The Constitution of India
282 George H Gadbois, JR, Supreme Court of India: The Beginnings (Vikram Raghavan and Vasujith Ram eds.), Oxford University Press (2017), at page 193
283 Ibid, at pages 193-194
284 Ibid, at page 195
285 Ibid, at pages 195-196
286 Minerva Mills Ltd. v Union of India, (1980) 3 SCC 625
287Upendra Baxi, “A known but an indifferent judge”: Situating Ronald Dworkin in contemporary Indian jurisprudence, International Journal of Constitutional Law, (2003) at page 582
288 Ibid
289 Amartya Sen, Development as Freedom, Oxford University Press (2000), at page xii
290 Isaiah Berlin, Two Concepts of Liberty, available at http://faculty.www.umb.edu/steven.levine/courses/Fall%202015/What%20is%20Freedom%20Writings/Berlin.pdf
291 F A Hayek, The Constitution of Liberty, Routledge & Kegan Paul, (1960) at pages 11, 207-208
292 Amartya Sen, Development as Freedom, Oxford University Press (2000) at page 3-4
293 Ibid, at page 8
294 Martha Nussbaum, Women and Human Development, Cambridge University Press, (2000)
295 Henry Shue, Basic Rights: Subsistence, Affluence and US Foreign Policy, Princeton University Press, Second Edition (1996)
296 Constituent Assembly Debates (25 November 1949)
297 Amartya Sen, Development as Freedom, Oxford University Press (2000), at page 39
298 Amartya Sen, The Idea of Justice, Penguin (2009) at pages 379-380
299 Ibid, at page 380
300 Amartya Sen, The Idea of Justice, Penguin (2009) at page 381
301 Jean Dreze and Amartya Sen, An Uncertain Glory, Penguin (2013), at pages x and xi
302 Ibid, at page xi
303 Jean Dreze and Amartya Sen, An Uncertain Glory, Penguin (2013), at page 33
304 Amartya Sen,
The Idea of Justice, Penguin (2009) at page 349
305 Jean Dreze and Amartya Sen, An Uncertain Glory, Penguin (2013), at page 100
306 Opinion on the Right to Identity, 2007, available at http://www.oas.org/en/sla/ijc/docs/ijc_current_agenda_Right_to_Identity.pdf
307 (2014) 5 SCC 438
308 Nishant Shah, Identity and Identification – the Individual in the Time of Networked Governance, Socio Legal Review, available at http://www.sociolegalreview.com/wp-content/uploads/2015/12/Identity-and-Identificationthe- Individual-in-the-Time-of-Networked-Governance.pdf
309 Manuel Castells, Conversation with Manuel Castells, Globetrotter, available at http://globetrotter.berkeley.edu/people/Castells/castells-con4.html
310 Nishant Shah, Identity and Identification – the Individual in the Time of Networked Governance, Socio Legal Review, available at http://www.sociolegalreview.com/wp-content/uploads/2015/12/Identity-and-Identificationthe- Individual-in-the-Time-of-Networked-Governance.pdf
311 Ibid
312 (2012) 10 SCC 1
313 (2012) 3 SCC 1
314 (2017) 4 SCC 269
315 Granville Austin, Working a Democratic Constitution: A History of the Indian Experience, Oxford University Press (2003), at page 652
316 Ibid, at page 651
317 Ibid
318 Ibid
319 Upendra Baxi, From Human Rights to the Right to be Human: Some Heresies, India International Centre Quarterly, Vol. 13, No. 3/4, Pg.185, (December 1986)
320 Ibid, at page 185
321 Ibid
322 Ibid, at page 187
323 Ibid, at page 186
324 Ibid, at page 190
325 Ibid, at page 186
326 Ibid, at page 186
327 (2003) 4 SCC 399
328 Ibid, at page 472
329 (2013) 16 SCC 82
330 Ibid, at page 112
331 (2013) 6 SCC 620
332 Ibid, at page 714
333 (2016) 7 SCC 221
334 Ibid, at page 319
335 (2017) 4 SCC 397
336 Ibid, at page 433
337 Jud Mathews and Alec Stone Sweet, All things in Proportion? American Rights Review and the Problem of Balancing, Emory Law Journal, Vol. 60 (2011)
338 Alec Stone Sweet & Jud Mathews, Proportionality Balancing and Global Constitutionalism, Columbia Journal of Transnational Law, Vol. 47 (2008)
339 Jud Mathews and Alec Stone Sweet, All things in Proportion? American Rights Review and the Problem of Balancing, Emory Law Journal, Vol. 60 (2011)
340 Ibid
341 Moshe Cohen-Eliya and Iddo Porat, Proportionality and the Culture of Justification, American Journal of Comparative Law Vol. 59 (2011) (cited in); Etienne Mureinik, A Bridge to Where?
Introducing the Interim Bill of Rights, South African Journal on Human Rights, Vol. 10 (1994)
342 Andrew B. Serwin, Privacy 3.0 – The Principle of Proportionality, University of Michigan Journal of Law Reform, Vol. 42 (2009)
343 Adalah v. The Minister of Interior, HCJ 7052/03, English translation available at http://elyon.court.gov.il/files_eng/03/520/070a47/03070520.a47.pdf 344 Om Kumar v Union of India, (2001) 2 SCC 386
345 1950 SCR 759
346 1952 SCR 597
347 (1969) 3 SCC 337
348 Ibid, at page 345
349 (1969) 1 SCC 853
350 Ibid, at page 857
351 (1982) 1 SCC 39
352 (2001) 2 SCC 386
353 Ibid, at page 399
354 (2004) 2 SCC 130
355 (2016) 7 SCC 353
356 Ibid, at page 412
357 Aharon Barak, Proportionality: Constitutional Rights and their Limitations, Cambridge University Press (2012)
358 Ibid, at page 412
359 Ibid, at page 414
360 Ibid, at page 415
361 (2017) 10 SCC 1
362 Ibid, at page 509
363 Ibid, at para 638
364 [1999] 1 AC 69
365 [2007] UKHL 11
366 (1983) 65 BVerfGE 1
367Jürgen Bröhmer et al., “BVerfGE 65, 1 – Census Act” in 60 Years German Basic Law: The German Constitution and its Court – Landmark Decisions of the Federal Constitutional Court of Germany in the Area of Fundamental Rights (Suhainah Wahiduddin ed.), (2012) at Pages 147-148, available at http://www.kas.de/wf/doc/kas_32858-1522-1-30.pdf?121123115540
368 Census Act Case, (1983)
369 Census Act Case, (1983)
370 Ibid, at page 150.
371 Ibid, at page 151
372 Ibid, at page 149
373 Ibid, at page 154
374 (2008) 48 EHRR 1169
375 Ibid, at Paragraph 119
376 Decision No. 2012-652 DC of 22 March 2012 by Le Conseil Constitutionnel, available at http://www.conseilconstitutionnel. fr/conseil-constitutionnel/english/case-law/sample-of-decisions-in-relevant-areasdc/ decision/decision-no-2012-652-dc-of-22-march-2012.105428.html
377 LOI n° 2012-410 du 27 mars 2012 relative à la protection de l’identité, available at https://www.legifrance.gouv.fr/affichTexte.do?cidTexte=JORFTEXT000025582411&dateTexte=&categorieLien =id.
378 Application no. 8806/12
379 The Conseil d’Etat (Council of State) is a body of the French government that acts as legal advisor of the executive branch and as the supreme court for administrative justice
380 Conseil d’ Etat in France, 26 October 2011
381 C-293/12 and C-594/12
382 Ibid, at para 27
383 Ibid, at para 42
384 Ibid, at para 46
385 Ibid, at para 51
386 Ibid, at paras 57-59
387 Ibid, at para 60
388 Ibid, at para 54
389 Ibid, at para 65
390 Ibid, at paras 56 -58
391 Ibid, at paras 60-62
392 Ibid, at paras 59, 63- 64
393 Ibid, at para 48
394 Ibid, at para 51
395 [2013] EUECJ C-291/12
396 Ibid, at para 60
397 Ibid, at para 61
398 Ibid, at para 62
399 [2016] UKPC 30
400 [2008] ECHR 1581
401 Maharajah Madhewoo v. The State of Mauritius & Anr., 2015 SCJ 177, at page 23
402 [2016] UKPC 30, at page 10
403 Ibid, at page 31 404 Ibid, at page 33 405Article 9. Protection of privacy of home and other property:
(2) Nothing contained in or done under the authority of any law shall be held to be consistent with or in contravention of this section to the extent that the law in question makes provision –
(a) in the interests of defence, public safety, public order, public morality, public health, town and country planning, the development or utilisation of mineral resources or the development or utilisation of any other property in such a manner as to promote the public benefit;
(b) for the purpose of protecting the rights or freedoms of other persons;
(c) to enable an officer or agent of the government or a local authority, or a body corporate established by law for public purpose, to enter on the premises of any person in order to value those premises for the purpose of any tax, rate or due, or in order to carry out work connected with any property that is lawfully on those premises and that belongs to the government, the local authority or that body corporate, as the case may be; or
(d) to authorise, for the purpose of enforcing the judgement or order of a court in any civil proceedings, the search of any person or property by order of a court or the entry upon any premises by such order, Except so far as that provision or, as the case may be, the thing done under its authority is shown not to be reasonably justifiable in a democratic society
406 Article 4(14)
407 515 U.S. 646 (1995)
408 489 U.S. 602 (1989)
409 429 U.S. 589 (1977)
410 410 U.S. 1 (1973)
411 476 U.S. 693 (1986)
412 194 F.3d 954 (9th Cir. 1999)
413 669 F.3d 1049 (9th Cir. 2012)
414 664 F. Supp. 136 (S.D.N.Y. 1987)
415 785 F.2d 1354 (6th Cir. 1986)
416 306 F. Supp. 1002 (S.D.N.Y. 1969)
417 (1986) 42 Cal. 3d 185
418 N.Y.S.2d 865
419 10 Cal. App.3d 582 (1970)
420 55 F.2d 67 (2d Cir. 1932)
421 399 F. Supp. 133 (M.D.N.C. 1975)
423 Regulation 2(f), Aadhaar (Authentication) Regulations
424 Regulation 2(g), Aadhaar (Authentication) Regulations
425 Regulation 2(p), Aadhaar (Authentication) Regulations
426 Regulation 2(l), Aadhaar (Authentication) Regulations
427 Regulation 15, Aadhaar (Authentication) Regulations
428 Section 2(d) states: “authentication record” means the record of the time of authentication and identity of the requesting entity and the response provided by the Authority
429 AUA code, ASA code, unique device code, registered device code used for authentication, and that UIDAI would know from which device the authentication has happened
430 An important configuration could be IP address
431 Puttaswamy at para 585
432 Puttaswamy at para 587
433 Puttaswamy at para 588
434 Nancy Yue Liu, Bio-Privacy: Privacy Regulations and the Challenge of Biometrics, Routledge (2013) at page 76
435 Clause 13.1 of the Contract
436 Ibid
437 Ibid
438 (2012) 11 SCC 1
439 Ibid, at page 153
440 As submitted by Mr Rakesh Dwivedi, learned senior counsel for the State of Gujarat
441 The Centre for Internet & Society, Salient Points in the Aadhaar Bill and Concerns, available at https://cisindia. org/internet-governance/salient-points-in-the-aadhaar-bill-and-concerns. 442 Shankkar Aiyar, Aadhaar:
A Biometric History of India’s 12-Digit Revolution, Westland (2017), at pages 226- 227
443 Subhashis Banerjee, Architecture for privacy, The Indian Express (5 May 2018), available at https://indianexpress.com/article/opinion/columns/architecture-for-privacy-data-protection-facebook-indiaunited- states-5163819/
444 Shankkar Aiyar, Aadhaar: A Biometric History of India’s 12-Digit Revolution, Westland (2017), at page 226
445 Government of India, Approach Paper for a Legislation on Privacy (2010), available at http://www.prsindia.org/uploads/media/UID/aproach_paper.pdf
446 Ibid
447 Shweta Agrawal, Subhashis Banerjee, and Subodh Sharma, Privacy and Security of Aadhaar: A Computer Science Perspective, Economic & Political Weekly (16 September 2017), Vol. 52, available at https://www.epw.in/journal/2017/37/special-articles/privacy-and-security-aadhaar.html
448 Nishant Shah, Digital Native: Cause an effect, The Indian Express (17 June 2018), available at https://indianexpress.com/article/technology/social/digital-native-cause-an-effect-5219977/
449 Aleksandr Solzhenitsyn, Cancer Ward, The Bodley Head (1968)
450 Shankkar Aiyar, Aadhaar: A Biometric History of India’s 12-Digit Revolution, Westland (2017), at page 226
451 Amartya Sen, The Argumentative Indian, Penguin (2005), at page 350
452 Ibid, at page 350
453 Ibid, at page 350
454 Ibid, at page 351
455 Ibid, at page 352
456 Constituent Assembly Debates (4 November, 1948)
457 (1978) 1 SCC 248
458 (1997) 6 SCC 241
459 (1999) 2 SCC 228
460 (2008) 3 SCC 1
461 (2014) 5 SCC 438
462 (1996) 5 SCC 125
463 (2011) 7 SCC 547
464 Ibid
465 Ronald Dworkin, Taking Rights Seriously (1977), at pages 203-204
466 Dr. Babasaheb Ambedkar: Writings and Speeches (Vol. 1), Dr. Ambedkar Foundation (2014)
467 Harsh Mander, Living with Hunger: Deprivation among the Aged, Single Women and People with Disability, Economic & Political Weekly (April 26, 2008), Vol. 43, available at https://www.epw.in/journal/2008/17/special-articles/living-hunger-deprivation-among-aged-single-women-andpeople
468 Dignity, Not Mere Roti, Economic & Political Weekly (10 August, 2013), Vol. 48, available at https://www.epw.in/journal/2013/32/editorials/dignity-not-mere-roti.html
469 UIDAI, Aadhaar Authentication, available at https://uidai.gov.in/authentication.html
470 United States General Accounting Office, Technology Assessment: Using Biometrics for Border Security (2002), available at http://www.gao.gov/new.items/d03174.pdf.
471 Jeremy Wickins, The ethics of biometrics: the risk of social exclusion from the widespread use of electronic identification, Science & Engineering Ethics (2007), at pages 45-54
472 Biometric Recognition: Challenges & Opportunities (Joseph N. Pato and Lynette I. Millett eds.), National Academy of Science- United States of America (2010), available at https://www.nap.edu/read/12720/chapter/1
473 Ibid, at page 3
474 Ibid
475 Ibid, at pages 10-11
476 Els J. Kindt, Privacy and Data Protection Issues of Biometric Applications: A Comparative Legal Analysis, Springer (2013)
477 Ibid, at page 363
478 Ibid
479 Virginia Eubanks, Automating Inequality: How High-Tech Tools Profile, Police, and Punish the Poor, St. Martin’s Press (2018)
480 Tommy L. Gardner, Spending Your Way to the Poorhouse, Authorhouse (2004), at page 221
481 Virginia Eubanks, Automating Inequality: How High-Tech Tools Profile, Police, and Punish the Poor, St. Martin’s Press (2018), at pages 12-13
482 Ibid, at page 16
483 Ibid, at pages 81-82
484 Ibid, at page 188
485 Puttaswamy, at para 119
486 UIDAI Committee on Biometrics, Biometrics Design Standards For UID Applications, at page 4
487 Ibid
488 UIDAI, UIDAI Strategy Overview, (2010), available at http://www.prsindia.org/uploads/media/UID/UIDAI%20STRATEGY%20OVERVIEW.pdf
489 Ibid, at page 38
490 Forty-Second Report of the Standing Committee on Finance (2011), available at http://www.prsindia.org/uploads/media/UID/uid%20report.pdf, at page 30
491 Government of India, Economic Survey 2016-17, available at https://www.thehinducentre.com/multimedia/archive/03193/Economic_Survey_20_3193543a.pdf, at page 173
492 Ibid, at page 174
493 Ibid, at page 194
494 Office Memorandum dated 19 December 2017, available at https://dbtbharat.gov.in/data/om/Office%20Memorandum_Aadhaar.pdf
495 Reetika Khera, Impact of Aadhaar on Welfare Programmes, Economic & Political Weekly, Vol. 52 (16 December 2017), available at https://www.epw.in/journal/2017/50/special-articles/impact-aadhaar-welfareprogrammes. html
496 Jean Dreze, Dark clouds over the PDS, The Hindu (10 September 2016), available at https://www.thehindu.com/opinion/lead/Dark-clouds-over-the-PDS/article14631030.ece
497 Anmol Somanchi, Srujana Bej, and Mrityunjay Pandey, Well Done ABBA? Aadhaar and the Public Distribution System in Hyderabad, Economic & Political Weekly (18 February 2017), Vol. 52, available at https://www.epw.in/journal/2017/7/web-exclusives/well-done-abba.html
498 Reetika Khera, Impact of Aadhaar on Welfare Programmes, Economic & Political Weekly, Vol. 52 (16 December 2017), available at https://www.epw.in/journal/2017/50/special-articles/impact-aadhaar-welfareprogrammes. html
499 Jean Dreze, Dark clouds over the PDS, The Hindu (10 September 2016), available at https://www.thehindu.com/opinion/lead/Dark-clouds-over-the-PDS/article14631030.ece
500 Ibid
501 Society for Social Audit, Accountability and Transparency, FP Shops Left Over Beneficiaries Report, available at http://www.socialaudit.ap.gov.in/SocialAudit/LoadDocument?docName=Fair%20Price%20Work%20%20Shops %20(Ration%20Card%20Holders)%20-%20Beneficiaries%20Report.pdf&type=application. See also Aadhaarbased projects failing the poor, says Andhra govt study, Hindustan Times (7 October 2015), available at https://www.hindustantimes.com/india/aadhaar-based-projects-failing-the-poor-says-andhra-govt-study/story- 7MFBCeJcfl85Lc5zztON6L.html
502 Anmol Somanchi, Srujana Bej, and Mrityunjay Pandey, Well Done ABBA? Aadhaar and the Public Distribution System in Hyderabad, Economic & Political Weekly, Vol. 52 (18 February 2017), available at https://www.epw.in/journal/2017/7/web-exclusives/well-done-abba.html
503 Jean Drèze, Nazar Khalid, Reetika Khera, and Anmol Somanchi, Aadhaar and Food Security in Jharkhand: Pain without Gain?, Economic & Political Weekly, Vol. 52 (16 December 2017).
506 Ibid, at page 58
507 Reetika Khera, Impact of Aadhaar on Welfare Programmes, Economic & Political Weekly, Vol. 52 (16 December 2017), available at https://www.epw.in/journal/2017/50/special-articles/impact-aadhaar-welfareprogrammes. html
508 Ibid, at page 66
509 Puja Awasthi, Good enough to vote, not enough for Aadhaar, People’s Archive of Rural India, available at https://ruralindiaonline.org/articles/good-enough-to-vote-not-enough-for-aadhaar
510 Yet another Aadhaar-linked death? Denied rations for 4 months, Jharkhand woman dies of hunger, Scroll (3 Feb. 2018), available at: https://scroll.in/article/867352/yet-another-aadhaar-linked-death-jharkhand-womandies- of-hunger-after-denial-of-rations; Denied food because she did not have Aadhaar-linked ration card, Jharkhand girl dies of starvation, Scroll (16 Oct 2017), available at: https://scroll.in/article/854225/denied-foodbecause- she-did-not-have-aadhaar-linked-ration-card-jharkhand-girl-dies-of-starvation
511 (2017) 7 SCC 59
512 (1996) 3 SCC 709
513 Ibid, at page 124
514 (2012) 6 SCC 312
515 (2016) 2 SCC 445
516 Ibid, at page 125 5
17 (2017) 9 SCC 1
518 (1981) 1 SCC 722
519 (1996) 2 SCC 226
520 (1974) 4 SCC 3
521 Ajay Hasia at page 741
522 Ibid, at pages 91-92
523 (1998) 2 SCC 1
524 (2004) 4 SCC 311
525 (2011) 8 SCC 737
526 (2011) 9 SCC 286
527 (2011) 9 SCC 1
528 Ibid, at page 97
529 Ibid, at page 495
530 Ibid, at page 496
531 Ibid, at pages 134-135
532 Ibid, at page 146
533 (2012) 5 SCC 275
534 Ibid, at page 283
535 (2017) 7 SCC 155
536 Ibid, at page 156
537 (2006) 3 SCC 434
538 (2007) 13 SCC 673
539 Substituted by G.S.R. 980(E), dated 16-12-2010 (w.e.f. 16-12-2010)
540 Inserted by G.S.R. 544(E)
541 (1963) 2 SCR 747
542 (1969) 1 SCC 248
543 (1972) 2 SCC 239
544 (2017) 3 SCC 362
545 Press Information Bureau, UIDAI generates a billion (100 crore) Aadhaars A Historic Moment for India, available at http://pib.nic.in/newsite/PrintRelease.aspx?relid=138555
546 A Constitution Bench of this Court in State of Madhya Pradesh v. Thakur Bharat Singh (AIR 1967 SC 1170) held:
“All executive action which operates to the prejudice of any person must have the authority of law to support it… Every Act done by the Government or by its officers must, if it is to operate to the prejudice of any person, be supported by some legislative authority.”
547 Puttaswamy, at para 272
548 Section 25, Indian Penal Code states:
“”Fraudulently”.-A person is said to do a thing fraudulently if he does that thing with intent to defraud but not otherwise”
549 Section 24, Indian Penal Code states: “”Dishonestly”- Whoever does anything with the intention of causing wrongful gain to one person or wrongful loss to another person, is said to do that thing “dishonestly”
550 (1966) 1 SCR 523
551 (1974) 4 SCC 827
552 (1975) 2 SCC 302
553 Ibid, at page 831
554 Ibid, at page 835
555 Ibid, at page 306
556 (1966) 2 SCR 158
557 (2017) 3 SCC 362
558 Ibid, at page 405
559 Ibid, at page 406
560 Ibid, at page 408
561 (2014) 4 SCC 583
562 Ibid, at page 604
563 (1969) 2 SCC 283
564 T. R. S. Allan, Constitutional Justice: A Liberal Theory of the Rule of Law (2001), available at http://www.oxfordscholarship.com/view/10.1093/acprof:oso/9780199267880.001.0001/acprof-9780199267880- chapter-2
565 Denise Meyerson, The Rule of Law and the Separation of Powers (2004), available at http://www5.austlii.edu.au/au/journals/MqLJ/2004/1.html
566 (1955) 2 SCR 225
567 (1967) 2 SCR 703
568 (1973) 4 SCC 225
569 Ibid, at page 366
570 Ibid, at para 1529
571 Smt. Indira Nehru Gandhi v. Shri Raj Narain, 1975 (Supp.) SCC 1; State of Bihar v. Bal Mukund Sah, (2000) 4 SCC 640]; I .R. Coelho (Dead) by L.Rs. v. State of Tamil Nadu, (2007) 2 SCC 1.
572 1975 Supp SCC 1
573 (2014)12 SCC 696
574 (1965) 1 SCR 413
575 (1976) 2 SCC 521
576 Ibid, at page 748
577 (1997) 3 SCC 261
578 Ibid, at page 301
579 (2007) 2 SCC 1
580 Ibid, at page 58
581 Ibid, at page 497
582 (2017) 3 SCC 1
583 Ibid, at page 76
584 Almon Leroy Way, Jr., Constitutional Democracy & Other Political Regimes, available at http://www.proconservative.net/CUNAPolSci201PartTWOA.shtml
585 In Sheela Barse v. State of Maharashtra ((1983) 2 SCC 96), the Supreme Court insisted on fairness to women in police lock-up and also drafted a code of guidelines for the protection of prisoners in police custody, especially female prisoners.
In Veena Sethi v. State of Bihar (AIR 1982 S.C. 1470), the Supreme Court extended the reach of rule of law to the poor who constitute the bulk of India by ruling that rule of law does not merely for those who have the means to fight for their rights and expanded the locus standi principle to help the poor 586 Durga Das Basu, Limited Government and Judicial Review, LexisNexis, (2016) at pages 123-124
587(1967) 2 SCR 454
588 (1987) 1 SCC 124
589 Ibid, at pages 128-129
590 (2007) 2 SCC 1
591 K.T. Plantation (P) Ltd. v. State of Karnataka, (2011) 9 SCC 1
592 State of Assam v. Barak Upatyaka DU Karmachari Sanstha, (2009) 5 SCC 694 593 Contempt Petition (Civil) No. 144/2014 in WP (C) No. 494/2012; Contempt Petition (Civil) No. 674/2014 in WP (C) No. 829/2013; Contempt Petition (Civil) No 444/2016 in WP (C) No. 494/2012
594 The interim order was in WP (Civil No. 494 of 2012)
595 SLP (Crl.) No. 2524/2015
596 WP (Civil) No. 686/2016
597 Ibid, at page 126
598 (1994) 6 SCC 77
599 Ibid at pages 83-84
600 (1987) 1 SCC 362
601 Ibid, at page 369
602 (2002) 3 SCC 343
603 Ibid, at page 346
604 Nandini Sundar v State of Chhattisgarh, (2011) 7 SCC 547
605 Manoj Narula v Union of India, (2014) 9 SCC 1
![]()
Justice K.S.Puttaswamy (Retd.) and ANR. Vs. Union of India and Ors.
[Writ Petition (CIVIL) No. 494 of 2012] see below
ASHOK BHUSHAN, J.
The challenge in this batch of cases can be divided in two parts, firstly, the challenge to Executive’s Scheme dated 28.01.2009 notified by the Government of India, by which the Unique Identification Authority of India (hereinafter referred to as “UIDAI”) was constituted to implement the UIDAI Scheme, and secondly challenge to The Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Act, 2016 (hereinafter referred to as “Act, 2016”).
2. The group of cases can be divided into four broad heads. First head consists of the sixteen Writ Petitions filed under Article 32 of the Constitution of India in this Court challenging the notification dated 28.01.2009 and/or the Act, 2016. Second group consists of seven Transfer Cases/Transfer petitions to be heard alongwith Writ Petitions filed under Article 32. Group three consists of only one Special Leave Petition (Criminal) No. 2524 of 2014 filed by UIDAI and Anr. Fourth group consists of seven Contempt 3 Petitions, which have been filed alleging violation of the interim orders passed by this Court in Writ Petitions and SLP (Criminal) as noted above.
3. Before we come to the different prayers made in the Writ Petitions wherein Executive Scheme dated 28.01.2009 as well as Act, 2016 has been challenged, it is useful to notice certain background facts, which lead to issuance of notification dated 28.01.2009 as well as the Act, 2016.
4. India is a country, which caters a sea of population. When the British left our country in 1947, total population of the country was only 330 million, which has rapidly increased into enormous figure of 1.3 billion as on date. The Citizenship Act, 1955 was enacted by the Parliament for the acquisition and determination of Indian Citizenship. Our constitutional framers have provided for adult franchise to every adult citizens. Election Commission of India had taken steps to provide for an identity 4 card to each person to enable him to exercise his franchise. The Citizenship Act, 1955 was amended by the Act 6 of 2004 whereas Section 14A was inserted providing that Central Government may compulsorily register every citizen of India and issue national identity card to him. The Planning Commission of the Government of India conceived a Unique Identification Project for providing a Unique Identity Number for each resident across the country, which was initially envisaged primarily as the basis for the efficient delivery of welfare services.
5. At first, in the year 2006, administrative approval was granted for the project “Unique Identity for BPL Families”. A Process Committee was constituted, which prepared a strategic vision on the Unique Identification Project. The Process Committee furnished a detailed proposal to the Planning Commission in the above regard. The Prime Minister approved the constitution of an empowered Group of Ministers to collate the two spheres, the national 5 population register under the Citizenship Act, 1955 and the Unique Identification Number Project of the Department of Information Technology.
The empowered Group of Ministers recognised the need for creating an identity related resident database and to establish an institutional mechanism, which shall own the database and shall be responsible for its maintenance and updations on ongoing basis. The empowered Group of Ministers held various meetings to which inputs were provided from different sources including Committee of Secretaries. The recommendation of empowered Group of Ministers to constitute Unique Identification Authority of India (hereinafter referred to as “UIDAI”) was accepted with several guidelines laying down the roles and responsibilities of the UIDAI. The UIDAI was constituted under the aegis of Planning Commission of India. The Notification dated 28.01.2009 was issued constituting the UIDAI, providing for its composition, roles and responsibilities.
6. In the year 2010, a bill namely the National Identification Authority of India Bill, 2010 providing for the establishment of the National Identification Authority of India for the purpose of issuing identification numbers to individuals residing in India and to certain other classes of individuals, manner of authentication of such individuals to facilitate access to benefits and services to which they are entitled and for matters connected therewith or incidental thereto was introduced. The Bill was pending in the Parliament when the first Writ Petition i.e. Writ Petition (C) No. 494 of 2012 – Justice K.S. Puttaswamy (Retd.) & Anr. Vs. Union of India & Ors. Was filed.
The Writ Petition under Article 32 was filed on the ground that fundamental rights of the innumerable citizens of India namely Right to Privacy falling under Article 21 of the Constitution of India are adversely affected by the Executive action of the Central Government proceeding to implement an Executive order dated 28.01.2009 and thereby issuing Aadhaar numbers to both citizens as also illegal immigrants presently illegally residing in the country. While the Bill namely “National Identification Authority of India Bill, 2010”, which had already been introduced in the Rajya Sabha on 03.12.2010 and referred to the Standing Committee, had been rejected.
The Writ Petition prayed for following reliefs:
(A) ISSUE a writ in the nature of mandamus restraining the respondents Nos. 1 to 3 from issuing Aadhaar Numbers by way of implementing its Executive order dated 28.01.2009 (Annexure “P1”) which tentamount to implementing the provisions of the National Identification Authority of India Bill, 2010 pending before the Parliament until and unless the said Bill is considered and passed by the Parliament and becomes an Act of Parliament.
(B) Pass such other order/s as this Hon’ble Court may deem fit and proper in the circumstances of the case.
7. Writ Petition (C) No. 829 of 2013 Mr. S.G. Vombatkere & Anr. Vs. Union of India & Ors., was filed by Mr. S.G. Vombatkere and Bezwada Wilson questioning the UID Project and Aadhaar Scheme. The UID Project and Aadhaar Scheme were contended to be illegal and 8 violative of fundamental rights. It was also contended that the Scheme has no legislative sanction. Various other grounds for attacking the Scheme were enumerated in the Writ Petition. Writ Petition (C) No. 833 of 2013 – Ms. Aruna Roy & Anr. Vs. Union of India & Ors., was also filed challenging the UID Scheme. Other Writ Petitions being Writ Petition (C) No. 932 of 2013 and Writ Petition (C) No. 37 of 2015 came to be filed challenging the UID Scheme.
8. S.G. Vombatkere and Bezwada Wilson filed another Writ Petition (C) No. 220 of 2015 challenging the exercise of preparation of the National Population Register. Section 14A of the Citizenship Act, 1955 was also challenged as void and ultra vires. Petitioners have referred to earlier Writ Petition (C) No. 829 of 2013 and adopted the grounds already raised in the earlier Writ Petition. Writ petitioner had also challenged the collection of confidential biometric informations, which is neither sanctioned nor authorised under any Act or Rules.
9. The Parliament enacted the Act, 2016, which contains following preamble:” An Act to provide for, as a good governance, efficient, transparent, and targeted delivery of subsidies, benefits and services, the expenditure for which is incurred from the Consolidated Fund of India, to individuals residing in India through assigning of unique identity numbers to such individuals and for matters connected therewith or incidental thereto.”
10. The Writ Petition (C) No. 231 of 2016Shri Jairam Ramesh Vs. Union of India & Ors., was filed by Shri Jairam Ramesh seeking a direction declaring the Act, 2016 as unconstitutional, null and void and ultra vires. Writ Petition (C) No. 797 of 2016 S. G. Vombatkere & Ors. Vs. Union of India & Ors., was also filed by S.G. Vombatkere and Bezwada Wilson challenging the Act, 2016. The petitioners have also referred to earlier Writ Petition (C) No. 829 of 2013 and Writ Petition (C) No. 220 of 2015. The writ petitioners alleged various grounds for challenging the Act, 2016. Apart from seeking a direction to declare the Act, 2016 ultra vires, unconstitutional and null and void, prayers for declaring various 10 Sections of Act, 2016 as ultra vires, unconstitutional and null and void were also made. The writ petitioners claimed lots of reliefs from a to w, it is useful to quote the reliefs a to d, which are to the following effect:”
a) Issue a Writ, order or direction in the nature of Certiorari or any other appropriate writ/order/direction declaring that the Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Act, 2016 is ultra vires, unconstitutional, null and void and in particular violate Articles 14, 19 and 21 of the Constitution of India;
b) Issue a Writ, order or direction in the nature of Certiorari or any other appropriate writ/order/direction declaring that sections 2(h), 2(l), 2(m), 2(v), 3, 5, 6, 7, 8, 9, 10, Chapter IV, Section 23 read with Section 54, Section 29, Section 30, Section 33, Section 47, Section 57 and Section 59 of the Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Act, 2016 are ultra vires, unconstitutional, null and void and in particular violate Articles 14, 19, 20(3) and 21 of the Constitution of India;
c) Issue a Writ, order or direction in the nature of Certiorari or any other appropriate writ/order/direction declaring that the right to privacy is a fundamental right guaranteed under Part III of the Constitution of India;
d) Issue a Writ, order or direction in the nature of Certiorari or any other appropriate writ/order/direction declaring that no person may be deprived of receiving any financial subsidy or other subsidy or benefit or services from the State on the ground that he or she does not have an Aadhaar number;”
11. Writ Petition (C) No. 342 of 2017 Shantha Sinha & Anr. Vs. Union of India & Anr. Was filed challenging the Act, 2016. Apart from seeking a direction to declare various Sections of Act, 2016 as null and void, writ petitioners also prayed for a direction declaring Sections 2(h), 2(l), 2(m), 2(v), 3, 5, 6, 7, 8, 9, 10, Chapter IV, Section 23 read with Section 54, Section 29, Section 30, Section 33, Section 47, Section 57 and Section 59 of the Act, 2016 as ultra vires, unconstitutional and null and void. Writ Petition (Civil) NO. 372 of 2017 Shankar Prasad Dangi Vs. Bharat Cooking Coal Limited & Another, was filed by Shankar Prasad Dangi, who claims to be employed under the Bharat Cooking Coal Limited.
Petitioner filed the writ petition seeking a mandamus directing the respondents not to compel the petitioner 12 to submit the Aadhaar Card copy. The petitioner placed reliance on Order of this Court dated 14.09.2016 in Writ Petition (C) No. 686 of 2016. Writ Petition (C) No. 841 of 2017 has also been filed by State of West Bengal challenging various notifications issued under Section 7 of the Act, 2016. The petitioner also sought a direction declaring that no person may be deprived of receiving any benefit or services from the State on the ground that he or she does not have an Aadhaar number or Aadhaar enrolment. Writ Petition (C) No. 1058 of 2017 – Mathew Thomas Vs. Union of India & Ors. has been filed challenging the Act, 2016. The writ petitioner also prayed for declaring Prevention of Money Laundering Rules (Second Amendment) 2017 as violative of Articles 14, 19 and 21 of the Constitution. Section 139AA of the Income Tax Act, 1961 was also prayed to be declared as violative of Articles 14, 19 and 21 of the Constitution. 12. Writ Petition (C) No. 966 of 2017 – Raghav Tankha Vs. Union of India through its Secretary & Ors. has been filed seeking following prayers:13
“a) Issue a Writ of Mandamus or any other appropriate writ, order or direction under Article 32 of the Constitution of India, directing the Respondents to declare that Aadhaar is not mandatory for the purpose of authentication while obtaining a mobile connection; or the reverification of Subscribers, being completely illegal, arbitrary and mala fide; and/or b) Issue a Writ of Mandamus or any other appropriate writ, order or direction under Article 32 of the Constitution of India, directing the Respondents Number 2 to 6, to take immediate steps in the present situation, for restraining and banning the transfer of data from UIDAI to Private Telecom Service Providers and Aadhaar being made the only option of authentication; and/or”
13. Writ Petition (C) No. 1014 of 2017 – M.G. Devasahayam and Ors. Vs. Union of India & Anr. has been filed, where following prayers have been made:”
a) This Hon’ble Court may be pleased to issue an appropriate writ, order or direction declaring Rule 9 of the Prevention of Money Laundering Rules, 2017 as amended by the Prevention of Money Laundering (Second Amendment) Rules, 2017 as ultra vires, unconstitutional, null and void and in particular violate Articles 14, 19 and 21 of the Constitution of India;
b) This Hon’ble Court may be pleased to issue an appropriate writ, order or 14 direction declaring that bank accounts will not be denied or ceased on the basis that he or she does not have an Aadhaar number;
c) This Hon’ble Court may be pleased to issue an appropriate writ, order or direction in the nature of mandamus against the Respondents directing them to forthwith forbear from implementing or acting pursuant to or in implementation of Rule 9 of the Prevention of Money Laundering Rules, 2017 as amended by the Prevention of Money Laundering (Second Amendment) Rules, 2017;
d) This Hon’ble Court may be pleased to issue an appropriate writ, order or direction in the nature of mandamus against the Respondents directing them to forthwith clarify by issuing appropriate announcements, circulars and/or directions that no citizen of India is required to obtain an Aadhaar number/Aadhaar card and that the program under the Aadhaar Act is entirely voluntary even for opening or maintaining the bank accounts and carrying financial transactions;
e) This Hon’ble Court may be pleased to award costs relating to the present petition to the petitioners; and
f) This Hon’ble Court may be pleased to issue any other writ/order/direction in the nature of mandamus as this Hon’ble Court may deem fit an proper in the circumstances of the case.”
14. Writ Petition (C) No. 1002 of 2017 – Dr. Kalyani 15 Menon Sen Vs. Union of India and Others, also sought declaration that Rule 2(b) of the Prevention of Money Laundering (Maintenance of Records) Second Amendment Rules, 2017 is ultra vires. Circular dated 23.03.2017 issued by the Department of Telecommunication was also sought to be declared as ultra vires, unconstitutional, null and void. A further direction was sought declaring that pursuant to the Circular dated 23.03.2017, the mobile phone numbers of subscribers will not be made inoperational, and future applicants will not be coerced to submit their Aadhaar numbers. Certain other reliefs have also been claimed in the writ petition.
Writ Petition (C) No. 1056 of 2017 – Nachiket Udupa & Anr. Vs. Union of India & Ors. has been filed challenging the Act, 2016 and with other prayers, which is as follows:
A. Issue a Writ of Declaration and Mandamus or any other appropriate Writ, Direction, Order or such other appropriate remedy to declare the Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Act, 2016 [ACT No. 18 of 2016] as illegal and violative of Articles 14, 19(1)(a) and 21 of the Constitution of India;
B. In the alternative to Prayer (A), issue a Writ of Declaration and Mandamus or any other appropriate Writ, Direction, Order or such other appropriate remedy against Respondent No. 3 to provide ‘optout’ or process to delete identity information from Central Identities Data Repository at the option of Aadhaar Number Holders;
C Issue a Writ of Declaration and Mandamus or any other appropriate Writ, Direction, Order or such other appropriate remedy to declare the Aadhaar (Enrolment and Update) Regulations, 2016 being illegal, and ultra vires the Aadhaar Act and violative of Articles 14 and 21 of the Constitution of India;
D. Issue a Writ of Declaration and Mandamus or any other appropriate Writ, Direction, Order or such other appropriate remedy to declare the Aadhaar (Authentication) Regulations, 2016 as being illegal and ultra vires the Aadhaar Act and violative of Articles 14 and 21 of the Constitution of India;
E. Issue a Writ of Declaration and Mandamus or any other appropriate Writ, Direction, Order or such other appropriate remedy to declare the Aadhaar (Data Security) Regulations, 2016 as being illegal, and ultra vires the Aadhaar Act and violative of Articles 14 and 21 of the Constitution of India;
F. Issue a Writ of Declaration and 17 Mandamus or any other appropriate Writ, Direction, Order or such other appropriate remedy to declare the Aadhaar (Sharing of Information) Regulations, 2016 as being illegal, and ultra vires the Aadhaar Act and violative of Articles 14 and 21 of the Constitution of India;
G. Issue a Writ of Declaration and Mandamus or any other appropriate Writ, Direction, Order or such other appropriate remedy to declare the Direction issued by Respondent No. 2 on 23.03.2017 vide File No. 800262/ 2016AS. II, as being illegal, ultra vires the Aadhaar Act and violative the Articles 14, 19(1)(a) and 21, of the Constitution;
H. In the alternative to Prayer (G) above, issue a Writ of Declaration and Mandamus or any other appropriate Writ, Direction, Order or such other appropriate remedy to Respondent No. 2 to prohibit all Telecom Service Providers from storing, retaining, making copies or in any manner dealing with Aadhaar Number, biometric information or any demographic information received from Respondent No. 3 in the process of authentication and/or identity verification of mobile numbers;
I. Pass such further and other orders as this Hon’ble Court may deem fit and proper in the instant facts and circumstances.”
15. There are seven Transfer Cases/Transfer Petitions 18 to be heard alongwith the Writ Petitions filed under Article 32, where the issues pertaining to UID Scheme and other related issues were also raised before different High Courts. Four Transfer Applications have been filed by Indian Oil Corporation Limited praying for transfer of different writ petitions pending in different High Courts to be heard alongwith Writ Petition (C) No. 494 of 2012 – Justice K.S. Puttaswamy (Retd.) & Anr. Vs. Union of India & Ors., which was considering the same issues.
This Court had passed order in few transfer petitions allowing the same and issued certain directions, rest of transfer petitions are also allowed. 16. One Transfer Petition has also been filed by Union of India for transferring Writ Petition (C) No. 2764 of 2013 – Sri V. Viswanandham Vs. Union of India & Ors., pending in the High Court of Hyderabad. It is not necessary to notice various issues in the pending different writ petitions, which were sought to be transferred by above transfer petitions/transfer 19 cases. Issues pending in different High Courts were more or less same, which have been raised in leading Writ Petition (C) No. 494 of 2012 Justice K.S. Puttaswamy (Retd.) & Anr. Vs. Union of India & Ors. and other writ petitions, which were entertained and pending in this Court. Special Leave Petition (Crl.) No. 2524 of 2014 has been filed by UIDAI and Anr. challenging the interim order dated 18.03.2014 passed by High Court of Bombay at Goa in Criminal Writ Petition No. 10 of 2014 – Unique Identification Authority of India Through its Director General & Anr. Vs. Central Bureau of Investigation.
On an application filed by the Central Bureau of Investigation, a Magistrate passed an order on 22.10.2013 directing the UIDAI to provide certain data with regard to a case of a rape of seven years old child. The Bombay High Court at Goa passed an order dated 18.03.2014 issuing certain interim directions, which were challenged by UIDAI in the aforesaid special leave petition. This Court passed an interim order on 24.03.2014 staying the order passed by Bombay High Court at Goa.
This 20 Court also by the interim order restrained the UIDAI to transfer any biometric information of any person who has been allotted the Aadhaar number to any other agency without his consent in writing. This special leave petition was directed to be listed alongwith Writ Petition (C) No. 494 of 2012.
17. This Court in Writ Petition (C) No. 494 of 2012 has issued various Interim Orders dated 23.09.2013, 24.03.2014, 16.03.2015, 11.08.2015 and 15.10.2015.
18. Seven Contempt Petitions have been filed. Out of seven, five contempt petitions have been filed alleging violation of the aforesaid interim orders and praying for issuing proceedings against the respondents contemnor for willful disobeying the interim orders. One Contempt Petition (C) No. 674 of 2015 in W.P.(C) No.829 of 2013 has been filed for issuing proceedings against the respondents contemnor for wilfully disobeying the orders dated 23.09.2013, 24.03.2014 and 16.03.2015 passed by this Court.
The 21 other Contempt Petition (C) No. 34 of 2018 in W.P.(C) No. 1014 of 2017 has been filed against the respondent contemnors for wilfully disobeying the order dated 03.11.2017 passed by this Court in the aforesaid writ petition. All the contempt applications are pending without any order of issuing notice in the contempt petitions.
19. Writ Petition (C) No.494 of 2012 : Justice K.S. Puttaswamy(Retd.) and another vs. Union of India and others, has been treated as leading petition wherein various orders and proceedings have been taken, few of such orders and proceedings also need to be noted. An interim order dated 23.09.2013 was passed in Writ Petition (C) No.494 of 2012 which is to the following effect: “Issue notice in W.P.(C) No. 829/2013.
Application for deletion of the name of petitioner no. 1 in T.P.(C) Nos. 47 of 2013 is allowed. T.P.(C)nos. 4748 of 2013 and T.P.(C) No. 476 of 2013 are allowed in terms of the signed order. 22 All the matters require to be heard finally. List all matters for final hearing after the Constitution Bench is over. In the meanwhile, no person should suffer for not getting the Aadhaar card inspite of the fact that some authority had issued a circular making it mandatory and when any person applies to get the Aadhaar Card voluntarily, it may be checked whether that person is entitled for it under the law and it should not be given to any illegal immigrant.”
20. By order dated 26.11.2013 all the States and Union Territories were impleaded as respondents to give effective directions. Interim order passed earlier was also continued. On 24.03.2014 following order was passed in SLP(Crl.) No.2524 of 2014: “Issue notice. In addition to normal mode of service, dasti service, is permitted. Operation of the impugned order shall remain stayed. In the meanwhile, the present petitioner is restrained from transferring any biometric information of any person who has been allotted the Aadhaar number to any other agency without his consent in writing. More so, no person shall be deprived of any service for want of Aadhaar number in case he/she is otherwise eligible/entitled. All the authorities are directed to modify their forms/circulars/likes so as to not compulsorily require the Aadhaar number in 23 order to meet the requirement of the interim order passed by this Court forthwith. Tag and list the matter with main matter i.e. WP(C) No.494/2012.”
21. This court on 16.03.2015 in Writ Petition (C) No.494 of 2012 directed both the Union of India and the States and all their functionaries should adhere to the order dated 23.09.2013.
22. A threeJudge Bench on 11.08.2015 passed an order referring the matter to a Bench of appropriate strength. After reference was made on a prayer made by the petitioners, following interim directions were also passed by the Bench : “Having considered the matter, we are of the view that the balance of interest would be best served, till the matter is finally decided by a larger Bench if the Union of India or the UIDA proceed in the following manner:
1. The Union of India shall give wide publicity in the electronic and print media including radio and television networks that it is not mandatory for a citizen to obtain an Aadhaar card;
2. The production of an Aadhaar card will not be condition for obtaining any benefits otherwise due to a citizen;
3. The Unique Identification Number or the Aadhaar card will not be used by the respondents for any purpose other than the PDS Scheme and in particular for the purpose of distribution of food grains, etc. and cooking fuel, such as kerosene. The Aadhaar card may also be used for the purpose of the LPG Distribution Scheme;
4. The information about an individual obtained by the Unique 15 Identification Authority of India while issuing an Aadhaar card shall not be used for any other purpose, save as above, except as may be directed by a Court for the purpose of criminal investigation.
Ordered accordingly.”
23. A Constitution Bench of five Judges on 15.10.2015 passed an order after hearing application filed by the Union of India for seeking certain clarification/modification in the earlier order dated 11.08.2015, part of order, which is relevant for the present case is as follows:
“3. After hearing the learned Attorney General for India and other learned senior counsels, we are of the view that in paragraph 3 of the Order dated 11.08.2015, if we add, apart from the other two Schemes, namely, P.D.S. Scheme and the L.P.G. Distribution Scheme, the Schemes like The Mahatma Gandhi National Rural Employment Guarantee Scheme 12 (MGNREGS), National Social Assistance Programme (Old Age Pensions, Widow Pensions, Disability Pensions) Prime Minister’s Jan Dhan Yojana (PMJDY) and Employees’ Provident Fund 25 Organisation (EPFO) for the present, it would not dilute earlier order passed by this Court. Therefore, we now include the aforesaid Schemes apart from the other two Schemes that this Court has permitted in its earlier order dated 11.08.2015.
5. We will also make it clear that the Aadhaar card Scheme is purely voluntary and it cannot be made mandatory till the matter is finally decided by this Court one way or the other.” 24. A threeJudge Bench of this Court in its reference order dated 11.08.2015 noticed that these cases raise farreaching questions of importance, which involves interpretation of the Constitution. Two earlier decisions of this Court, i.e., M.P. Sharma & Others Vs. Satish Chandra & Others, 1954 AIR SC 300, rendered by eight Judges and another judgment rendered by sixJudges Bench in Kharak Singh Vs. State of U.P. & Others, AIR 1963 SC 1295 were noticed and it was observed that in the event the observations made in the above two judgments are to be read literally and accepted as the law of this country, the fundamental rights guaranteed under the Constitution of India and more particularly right to liberty under Article 21 would be denuded of vigour and vitality. The three26 Judge Bench observed that to give quietus to the kind of controversy raised in this batch of cases once for all, it is better that the ratio decidendi of M.P. Sharma (supra) and Kharak Singh (supra) is scrutinized and the jurisprudential correctness of the subsequent decisions of this Court where the right to privacy is either asserted or referred be examined and authoritatively decided by a Bench of appropriate strength.
25. By order dated 18.07.2017, a Constitution Bench considered it appropriate that the issue be resolved by a Bench of Nine Judge. Following order was passed on 18.07.2017 by a Constitution Bench: “During the course of the hearing today, it seems that it has become essential for us to determine whether there is any fundamental right of privacy under the Indian Constitution. The determination of this question would essentially entail whether the decision recorded by this Court in M.P. Sharma and Ors. vs. Satish Chandra, District Magistrate, Delhi and Ors. 1950 SCR 1077 by an eightJudge Constitution Bench, and also, in Kharak Singh vs. The State of U.P. and Ors. 1962 (1) SCR 332 by a sixJudge Constitution Bench, that there is no such fundamental right, is the correct expression of the constitutional position. 27 Before dealing with the matter any further, we are of the view that the issue noticed hereinabove deserves to be placed before the nineJudge Constitution Bench. List these matters before the NineJudge Constitution Bench on 19.07.2017. Liberty is granted to the learned counsel appearing for the rival parties to submit their written briefs in the meantime.” 26. A nineJudge Constitution Bench proceeded to hear and decide all aspects of right of privacy as contained in the Constitution of India.
27. Dr. D.Y. Chandrachud delivered opinion on his behalf as well as on behalf of Khehar, CJ., Agrawal, J. and Nazeer, J. Jasti Chelameswar, J., Bobde, J., Sapre, J. and Kaul, J. also delivered concurring, but separate opinions. The opinion of all the nine Judges delivered in above cases held that right of privacy is a right which is constitutionally protected and it is a part of protection guaranteed under Article 21 of the Constitution of India. Explaining the essential nature of privacy, Dr. D.Y. Chandrachud, J. in paragraphs 297 and 298 laid down following:
“297. What, then, does privacy postulate? Privacy postulates the reservation of a 28 private space for the individual, described as the right to be let alone. The concept is founded on the autonomy of the individual. The ability of an individual to make choices lies at the core of the human personality. The notion of privacy enables the individual to assert and control the human element which is inseparable from the personality of the individual. The inviolable nature of the human personality is manifested in the ability to make decisions on matters intimate to human life. The autonomy of the individual is associated over matters which can be kept private. These are concerns over which there is a legitimate expectation of privacy.
The body and the mind are inseparable elements of the human personality. The integrity of the body and the sanctity of the mind can exist on the foundation that each individual possesses an inalienable ability and right to preserve a private space in which the human personality can develop. Without the ability to make choices, the inviolability of the personality would be in doubt. Recognising a zone of privacy is but an acknowledgment that each individual must be entitled to chart and pursue the course of development of personality. Hence privacy is a postulate of human dignity itself. Thoughts and behavioural patterns which are intimate to an individual are entitled to a zone of privacy where one is free of social expectations.
In that zone of privacy, an individual is not judged by others. Privacy enables each individual to take crucial decisions which find expression in the human personality. It enables individuals to preserve their beliefs, thoughts, expressions, ideas, ideologies, preferences and choices against societal demands of homogeneity. Privacy is an intrinsic recognition of heterogeneity, of the right of the individual to be different and to stand against the tide of conformity in creating a zone of solitude. Privacy protects the individual from the searching glare of publicity in matters which are personal to his or her life. Privacy attaches to the person and not to the place where it is associated. Privacy constitutes the foundation of all liberty because it is in privacy that the individual can decide how liberty is best exercised. Individual dignity and privacy are inextricably linked in a pattern woven out of a thread of diversity into the fabric of a plural culture.
298. Privacy of the individual is an essential aspect of dignity. Dignity has both an intrinsic and instrumental value. As an intrinsic value, human dignity is an entitlement or a constitutionally protected interest in itself. In its instrumental facet, dignity and freedom are inseparably intertwined, each being a facilitative tool to achieve the other. The ability of the individual to protect a zone of privacy enables the realisation of the full value of life and liberty. Liberty has a broader meaning of which privacy is a subset. All liberties may not be exercised in privacy. Yet others can be fulfilled only within a private space. Privacy enables the individual to retain the autonomy of the body and mind. The autonomy of the individual is the ability to make decisions on vital matters of concern to life.
Privacy has not been couched as an independent fundamental right. But that does not detract from the constitutional protection afforded to it, once the true nature of privacy and its relationship with those fundamental rights which are expressly protected is understood. Privacy lies across the spectrum of protected freedoms. The guarantee of equality is a guarantee against arbitrary State action. It prevents the State from discriminating between individuals. The destruction by the State of a sanctified personal space whether of the body or of the mind is violative of the guarantee against arbitrary State action. Privacy of the body entitles an individual to the integrity of the physical aspects of personhood.
The intersection between one’s mental integrity and privacy entitles the individual to freedom of thought, the freedom to believe in what is right, and the freedom of selfdetermination. When these guarantees intersect with gender, they create a private space which protects all those elements which are crucial to gender identity. The family, marriage, procreation and sexual orientation are all integral to the dignity of the individual. Above all, the privacy of the individual recognises an inviolable right to determine how freedom shall be exercised. An individual may perceive that the best form of expression is to remain silent. Silence postulates a realm of privacy.
An artist finds reflection of the soul in a creative endeavour. A writer expresses the outcome of a process of thought. A musician contemplates upon notes which musically lead to silence. The silence, which lies within, reflects on the ability to choose how to convey thoughts and ideas or interact with others. These are crucial aspects of personhood. The freedoms under Article 19 can be fulfilled where the individual is entitled to decide upon his or her preferences. Read in conjunction with Article 21, liberty enables the individual to have a choice of preferences on various facets of life including what and how one will eat, the way one will dress, the faith one will espouse and a myriad other matters on which autonomy and selfdetermination require a choice to be made within the privacy of the mind. The constitutional right 31 to the freedom of religion under Article 25 has implicit within it the ability to choose a faith and the freedom to express or not express those choices to the world.
These are some illustrations of the manner in which privacy facilitates freedom and is intrinsic to the exercise of liberty. The Constitution does not contain a separate article telling us that privacy has been declared to be a fundamental right. Nor have we tagged the provisions of Part III with an alphasuffixed right to privacy: this is not an act of judicial redrafting. Dignity cannot exist without privacy. Both reside within the inalienable values of life, liberty and freedom which the Constitution has recognised. Privacy is the ultimate expression of the sanctity of the individual. It is a constitutional value which straddles across the spectrum of fundamental rights and protects for the individual a zone of choice and selfdetermination.” 28. Privacy has been held to be an intrinsic element of the right to life and personal liberty Under Article 21 and has a constitutional value which is embodied in the fundamental freedoms embedded in Part III of the Constitution. It was further held that like the right to life and liberty, privacy is not absolute. The limitations which operate on the right to life and personal liberty would operate on the right to privacy. Any curtailment or deprivation of that right would have to take place under a regime of 32 law. The procedure established by law must be fair, just and reasonable.
29. The nineJudge Constitution Bench also noticed the context of right of privacy under the international covenants. The protection of right of privacy as developed in U.K. decision, decisions of US Supreme Court, constitutional right to privacy in South Africa, constitutional right to privacy in Canada, privacy under European convention on human rights and under Charter of fundamental rights of European Union were considered with reference to decision rendered by foreign courts.
30. Justice D.Y. Chandradhud in his judgment traced the right of privacy from the judgments of this Court which were rendered for the last five decades. Referring to International Law on the subject, following observations were made by Justice D.Y. Chandradhud, J.: “103…In the view of this Court, international law has to be construed as a 33 part of domestic law in the absence of legislation to the contrary and, perhaps more significantly, the meaning of constitutional guarantees must be illuminated by the content of international conventions to which India is a party. Consequently, as new cases brought new issues and problems before the Court, the content of the right to privacy has found elaboration in these diverse contexts.”
31. All contours of the right of privacy having been noticed with all its dimensions, precautions and safeguards to be applied to protect fundamental rights guaranteed under the Constitution of India, we while proceeding to decide the issues raised herein have to proceed in the light of nineJudge Constitution Bench of this Court as noticed above.
32. We have been manifestly benefited by able and elaborate submissions raised before us by many eminent learned senior counsel appearing for both the parties. Learned counsel for both the parties have advanced their submissions with clarity, conviction and lot of persuasions. On occasions very passionate arguments were advanced to support the respective submissions.
33. Different aspects of the case have been taken up and advanced by different counsel as per understanding between them which enlightened the Court on varied aspects of the case. The submissions have been advanced on behalf of the petitioners by learned senior Advocates, namely, Shri Kapil Sibal, Shri Gopal Subramanium, Shri P. Chidambaram, Shri Shyam Divan, Shri K.V. Viswanathan, Shri Neeraj Kishan Kaul, Ms. Meenakshi Arora, Shri C.U. Singh, Shri Anand Grover, Shri Sanjay R. Hegde, Shri Arvind P. Datar, Shri V.Giri, Shri Sajan Poovayya and Shri P.V. Surendra Nath. A large number of other counsel also assisted us including Mr. Gopal Sankaranarayanan. On behalf of respondents arguments were led by the learned Attorney General, Shri K.K. Venugopal. We have also heard Shri Tushar Mehta, Additional Solicitor General, Shri Rakesh Dwivedi, learned senior counsel and Shri Zohaib Hossain.
34. We also permitted Dr. Ajay B. Pandey, Chief Executive Officer, UIDAI to give a power presentation 35 to explain actual working of the system. After the power presentation was presented by Dr. Pandey in the presence of the learned counsel for the parties, learned counsel have also thereafter raised certain questions in respect of the power presentation, which the respondents during submissions have tried to explain. In view of the enormity of submissions raised by the different learned counsel appearing for the petitioners, we proceed to notice different part of submissions together. As noted above writ petitions have been filed at two stages, firstly, when UIDAI Scheme was being impleaded by the Executive order dated 28.01.2009. Secondly, challenge was raised when Act, 2016 was enacted.
The challenge to the Scheme dated 24.01.2009 contained almost same grounds on which Act, 2016 has been attacked. Additional ground to challenge the Scheme was that Scheme having not been backed by law, the entire exercise was unconstitutional and violative of fundamental rights guaranteed under the Constitution of India and deserved to be set aside. The Act, 2016 having enacted 36 and now statutory scheme is in place, we shall first proceed to notice the submissions attacking the Act, 2016 which challenge has been substantial and elaborately raised before us. Petitioner’s Submissions
35. The submissions advanced by different learned counsel for the petitioners instead of noticing individually are being noted together in seriatim, which are as follows:36. The Aadhaar project initiated by Executive notification dated 28.01.2009 as well as impugned Act, 2016 violates Article 21. The constitutional rights of a person protected under Articles 19 and 21 of the Constitution is violated as individuals are compelled to part with their demographic and biometric information at the point of collection. Biometric data is part of one’s body and control over one’s body lies on the very centre of the Right of Privacy. Decisional privacy allows individual to make a 37 decision about their own body and is an aspect of right of selfdetermination.
The Aadhaar Project including the Aadhaar Act violate the informational privacy. Data collection at the enrolment centres, the Data retention at Central Identities Data Repositories (CIDR), usage and sharing of data violates Right of Privacy. There is complete absence of safeguards at the stage of collection, retention and use of data. Act, 2016 and Regulations framed thereunder lack safeguards to secure sensitive personal data of a person.
37. The Aadhaar project including Act, 2016 creates an architecture for pervasive surveillance, which again violate fundamental Right to Privacy. Personal data collected under the Executive scheme dated 28.01.2009 was without any individual’s consent. The Act, 2016 although contemplate that enrolment under Aadhaar is voluntary but in actual working of the Act, it becomes defacto compulsory. The Act, 2016 does not pass the threefold test as laid down by Nine Judges Bench in 38 Privacy Judgment K. S. Puttaswamy Vs. Union of India, (2017) 10 SCC 1, hereinafter referred to as “Puttaswamy case”. The Threefold test laid down in Puttaswamy’s case are:
(i) legality, which postulates the existence of law; (ii) need, defined in terms of a legitimate state aim; and
(iii) proportionality which ensures a rational nexus between the objects and the means adopted to achieve them;
38. It is submitted that a law to pass under Article 21 should be a law according to procedure established by law. The Act, 2016 violates both Article 14 and Article 21 of the Constitution of India. A legitimate State aim, which ensure that nature and content of the law, which imposes the restriction falls within the reasonable restrictions mandated by Article 14 is also not fulfilled. State has not been able to discharge its burden that Aadhaar project has been launched for a legitimate State aim.
The third requirement, which require that the means that are adopted by the legislature are proportional to the object sought to be fulfilled by the law is also not fulfilled since the provisions of the Act and Regulations framed thereunder does not satisfy the Proportionality Test. The various provisions of Act, 2016 and Regulations framed thereunder are unconstitutional. Section 6 of the Act, 2016 is unconstitutional inasmuch as it enable the respondents to continually compel residents to periodically furnish demographic and biometric information.
Section 7 of the Act, 2016 is unconstitutional inasmuch as it seeks to render the constitutional and statutory obligations of the State to provide benefits, subsidies and services, conditional upon an individual bartering his or her biometric and demographic information. Section 8 is unconstitutional since it enables tracking, tagging and profiling of individuals through the authentication process. Section 8 delineate a regime of surveillance, which enables persons’ physical 40 movements to be traced. Section 9 of the Act, 2016 is also unconstitutional inasmuch as the Aadhaar number is de facto serving as proof of citizenship and domicile. The provisions of Chapter IV, i.e., Sections 11 to 33 are ultra vires and unconstitutional.
The Constitution does not permit the establishment of an authority that in turn through an invasive programme can claim every Indian citizen/resident to a central data bank and maintain lifelong records and logs of that individual. Sections 23 and 54 of the Act, 2016 are also unconstitutional on the ground of excessive delegation. Section 29 of the Act, 2016 is also liable to be struck down inasmuch as it permits sharing of identity information. Section 33 is unconstitutional inasmuch as it provides for the use of the Aadhaar data base for police investigation pursuant to an order of a competent court. Section 33 violates the protection against selfincrimination as enshrined under Article 20(3) of the Constitution of India.
Furthermore, Section 33 does not afford an 41 opportunity of hearing to the concerned individual whose information is sought to be released by the UIDAI pursuant to the court’s order. This is contrary to the principles of natural justice. Section 47 is also unconstitutional inasmuch as it does not allow an individual citizen who finds that there is a violation of the Act, 2016 to initiate the criminal process. Section 48, which empowers the Central Government to supersede UIDAI is vague and arbitrary.
39. Elaborating submission with regard to Section 7, it is submitted that Section 7 is unconstitutional and violative of Article 14 making Aadhaar mandatory, which has no nexus with the subsidies, benefits and services. A person cannot be forced into parting with sensitive personal information as a condition for availing benefits or services. Section 7 also falls foul of Article 14 since firstly such mandatory authentication has caused, and continues to cause, exclusion of the most marginalised sections of society; and secondly, this exclusion is not simply a question of poor implementation that can be 42 administratively resolved, but stems from the very design of the Act, i.e. the use of biometric authentication as the primary method of identification.
There is large scale exclusion to the mostly marginalised society not being able to identify themselves by identification process. There is sufficient material on record to indicate general deprivation, which itself is sufficient to struck down Section 7 of the Act. 40. Elaborating submission on unconstitutionality of Section 57, it is contended that Section 57 allows an unrestricted extension of the Aadhaar information to users who may be Government agencies or private sector operators. Section 57 enables commercial exploitation of an individual’s biometrics and demographic information by the respondents as well as private entities. The provision also ensures creation of a surveillance society, where every entity assists the State to snoop upon an Aadhaar holder. The use of Aadhaar infrastructure by private entities is unconstitutional.
41. Elaborating submissions on Section 59, it is contended that Section 59 is unconstitutional inasmuch as it seeks to validate all action undertaken by the Central Government pursuant to the notification dated 28.01.2009. Enrolment in pursuance of notification dated 28.01.2009 having been done without an informed consent amounts to deprivation of the intimate personal information of an individual violating the fundamental Right of Privacy. All steps taken under the notification dated 28.01.2009 were not backed by any law, hence unconstitutional and clearly violate Article 21, which cannot be cured in a manner as Section 59 pretend to do.
42. The Act is unconstitutional since it collects the identify information of children between five to eighteen years without parental consent. The Aadhaar architecture adopts foreign technologies, on which UIDAI does not have any control, exposing data leak endangering life of people and security of nation.
43. Rule 9 as amended by PMLA Rules, 2017 is unconstitutional being violative of Articles 14, 19(1)(g), 21 and 300A of the Constitution of India. Rule 9 also violates Sections 3, 7 and 51 of the Act, 2016 and ultra vires to the provisions of PMLA Act, 2002.
44. Section 139AA of the Income Tax Act, 1961 is liable to be struck down as violative of Articles 14, 19(1)(g) and 21 of the Constitution in view of Privacy Judgment – Puttaswamy (supra).
45. The Mobile Linking Circular dated 23.03.2017 issued by Ministry of Communications, Department of Telecommunications is ultra vires.
46. The Aadhaar Act, 2016 has wrongly been passed as a Money Bill. The Aadhaar Act, 2016 is not a Money Bill. The Speaker of Lok Sabha wrongly certified the bill as a Money Bill under Article 110 of the Constitution of India virtually excluding the Rajya Sabha from legislative process and depriving the Hon’ble President of his power of return. Clauses 23(2)(g), Section 54(2)(m) and Section 57 of The 45 Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Bill, 2016 and the corresponding Sections of the Act, 2016 as notified clearly do not fall under any of the Clauses of Article 110 of the Constitution.
The Act of Speaker certifying the bill as a Money Bill is clearly violation of constitutional provisions. Judicial Review of decision of Speaker certifying it as Money Bill is permissible on the ground of illegality. The Aadhaar Bill being not a money bill and having been passed by Parliament as a Money Bill, this ground alone is sufficient to strike down the entire Act, 2016.
47. Learned Attorney General replying the above submissions of the counsel for the petitioners submits:48. In the Privacy Judgment P.S. Puttaswamy case (supra) all nine Judges uniformly agreed that privacy is a fundamental right traceable to the right to liberty under Article 21 of the Constitution and hence 46 subject to the same limitations as applicable to the said Article. It has further been held that right of privacy is not absolute and is subject to limitations. Justice D.Y. Chandrachud in his lead judgment laid down that following three tests are required to be satisfied for judging the permissible limits of the invasion of privacy under Article 21 of the Constitution:
(a) The existence of a law
(b) A legitimate State interest; and
(c) The said Law should pass the test of proportionality.
49. The above tests have also been agreed by other Judges who have delivered the separate judgment. Justice J. Chelameswar and Justice A.N. Sapre have used the test of compelling State interest whereas Justice R.F. Nariman stated that if this test is applied, the result is that one would be entitled to invoke larger public interest in lieu of legitimate State aim. The legitimate State aim obviously will lead to public interest, hence in the event test of legitimate State aim is fulfilled, the test of public interest stands fulfilled. After enactment of Act, 2016, the first condition in regard to the existence of a law stands satisfied. The Act requires only the bare demographic particulars, while eschewing most other demographic particulars. The Act further contains adequate safeguards for protection of information and preventing abuse through a catena of offences and penalties. The provisions of Act ensure that the law is a just, fair and reasonable and not fanciful, oppressive or arbitrary.
50. The legitimate State interest or a larger public interest permeates through the Act, 2016 which is clearly indicated by the following:
A. Preventing the dissipation of subsidies and social welfare benefits which is covered by Section 7 of the Aadhaar Act;
B. Prevention of black money and money laundering by imposing a requirement by law for linking Aadhaar for opening bank accounts;
C. To prevent income tax evasion by requiring, through an amendment to the Income Tax Act, that the Aadhaar number be linked with the PAN; and 48 D. To prevent terrorism and protect national security by requiring that Aadhaar be linked to SIM cards for mobile phones.”
51. The Aadhaar Act, 2016 was enacted with prolonged deliberations and study. The petitioners have failed to establish any arbitrariness in the Act. The right to life under Article 21 is not the right to a mere animal existence, but the right to live with human dignity which would include the right to food, the right to shelter, the right to employment, the right to medical care, education etc. If these rights are juxtaposed against the right to privacy, the former will and prevail over the latter. In so far as implementation of Aadhaar project prior to coming into force of Act, 2016, since obtaining an Aadhaar number or an enrolment number was voluntary, especially because of the interim orders passed by this Court, no issue of violation of any right, leave alone a fundamental right, could arise.
The judgments of this Court in M.P. Sharma and Kharak Singh (supra) being those of eight Judges and six Judges respectively, holding that the right to privacy is not a fundamental 49 right, the judgments of smaller benches delivered during the period upto 2016 would be per incuriam, as a result of which the State need not to have proceeded on the basis that a law was required for the purpose of getting an Aadhaar number or an enrolment number. As a result, the Executive instructions issued for this purpose would be valid as well as the receipt of benefits and subsidies by the beneficiaries. In any view of the matter, Section 59 of the Act protects all actions taken during the period 2010 until the passing of the Aadhaar Act in 2016.
52. Learned Attorney General submitted that Aadhaar Act has rightly been characterised as Money Bill as understood under Article 110 of the Constitution. The heart of the Aadhaar Act is Section 7. It is not the creation of Aadhaar number per se which is the core of the Act, rather, that is only a means to identify the correct beneficiary and ensure ‘targeted delivery of subsidies, benefits and services’, the expenditure for which is incurred from the Consolidated Fund of India. 50 The decision of the Speaker incorporated into a certificate sent to the President is final and cannot be the subject matter of judicial review.
53. The decision and certification of the Speaker being a matter of procedure is included in the Chapter under the head ‘Legislative Procedure’ which clearly excluded judicial review. The present issue is squarely covered by the decisions of this Court.
54. Section 57, which has been attacked as being untraceable to any of the subclauses of (a) to (f) of Article 110 cannot be looked at in isolation. The Bill in its pith and substance should pass the test of being a Money Bill and not isolated provisions.
55. Learned Additional Solicitor General of India, Shri Tushar Mehta, also advanced submissions on few aspects of the matter. On Section 139AA of Income Tax Act, 1961 it is submitted that petitioners can succeed only when they demonstrate that Section 139AA is violative of right to privacy on the following tests 51 as laid down by nineJudge Constitution Bench in Puttaswamy case:
(i) absence of a law;
(ii) absence of legitimate State interest”
(iii) provisions being hit by lack of proportionality;
(iv) the provisions being manifestly arbitrary.
56. It is submitted that twoJudge Bench judgment of this Court in Binoy Biswam Vs. Union of India and others, (2017) 7 SCC 59, had upheld the vires of Section 139AA subject to issue of privacy which at that point of time was pending consideration.
It is further submitted that provision pertaining to Permanent Account Number (PAN) was inserted in the Income Tax Act by Section 139A with effect from 01.04.1989 which obliged every person to quote PAN for different purposes as enumerated in Section 139A. The Petitioners or anyone else never felt aggrieved by requirement of getting PAN under Section 139A and Parliament on considering the legitimate State interest has introduced Section 139AA which is only an extension of Section 139A which requires linking of PAN with Aadhaar number.
57. The Income Tax Act was amended by the Parliament by inserting Section 139AA in the legitimate State interest and in larger public interest. The object of linking was to remove bogus PAN cards by linking with Aadhaar, expose shell companies and thereby curb the menace of black money, money laundering and tax evasion. Problem of multiple PAN cards to same individuals and PAN cards in the name of fictitious individuals are common medium of money laundering, tax evasion, creation and channeling of black money.
58. Linking of Aadhaar with PAN is consistent with India’s international obligations and Goals. India has signed the InterGovernmental Agreement (IGA) with the USA on July, 9, 2015, for improving International Tax Compliance and implementing the Foreign Account Tax Compliance Act. It is submitted that prior to 01.07.2017 already 1.75 crore tax payers had linked their PAN with Aadhaar on a voluntary basis. Replying 53 the arguments based on the interim orders passed by this Court in the present group of petitions, it is submitted that enactment of Aadhaar Act, 2016 has taken away and cured the basis of the interim order passed by this Court since one of the submissions which was made before this Court in passing the interim orders was that there was no law, that Aadhaar project was being implemented without backing of any law and during the said period the interim orders were passed.
The Aadhaar Act addresses the concern of this Court as reflected in the interim orders passed before enactment of the Act. 59. Shri Mehta further contended that there is presumption to the constitutionality of a statute and unless one attacking the statute satisfies the Court that the statute is unconstitutional, the presumption will be there that statute is constitutional. Shri Mehta has further submitted that there is no presumption of criminality or guilt on the requirement to link Aadhaar.
60. Elaborating the doctrine of proportionality, Additional Solicitor General submits that Section 139A fully satisfies the aforesaid test of proportionality.
61. Additional Solicitor General in support of Prevention of Moneylaundering (Maintenance of Records) Second Amendment Rules, 2017 submits that the State has sought to make the provisions of PMLA more robust and ensure that the ultimate object of the Act is achieved. The Amendment Rules, 2017 place an obligation on part of the reporting entity to seek the details with regard to Aadhaar number of every client. It is submitted that the said Rules have to be read in consonance with the object of the PMLA and the principles of “beneficial owner” behind the corporate veil of shell companies, etc. It is submitted that the PMLA empowers the State to utilise the uniqueness of Aadhaar in order to tackle the problem of money laundering. It is submitted that the PMLA Act, with a clear emphasis on the investigation of the biological persons behind the corporate entities, establishes a mechanism wherein receiving benefits through benami or 55 shell companies through related/connected Directors, fictitious persons or other personnel is eliminated.
62. Section 139AA and PMLA Rules amended in 2017 are coordinated in their operation. The PMLA Rules are not ultra vires. Mr. Mehta has also referred to international Conventions declaring money laundering to be a very serious offence. He submits that Prevention of Money Laundering Act, 2002 was enacted in the context of concrete international efforts to tackle the menace of money laundering. Shri Mehta has also emphasised on the necessity of verification of bank accounts with Aadhaar number. He submits that the verification of bank account by way of Aadhaar is done for the reason that often bank accounts are opened in either fictitious names or in the name of wrong persons on the basis of forged identity documents and financial crimes are committed.
It is seen that accommodation entries are mostly provided through the banking channels by bogus companies to convert black money into white. Benami transactions routinely take place through banking channels. All of the above, can 56 to a large extent be checked by verifying Aadhaar with bank accounts to ensure that the account belongs to the person who claims to be the account holder and that he or she is a genuine person. Verification of bank account with Aadhaar also ensures that the direct benefit transfer of subsidies reach the Aadhaar verified bank account and is not diverted to some other account. Shell companies are often used to open bank accounts to hold unaccounted money of other entities under fictitious identities which will also be curbed once Aadhaar verification is initiated.
63. Shri Mehta further contends that impugned PMLA Rules do not violate Article 300A. Amendment Rules, 2017 also cannot be said to be ultra vires to the parent Act since it advances the object of the Act and is not ultra vires of any provision of the Act. The Amendment Rules are required to be placed before the Parliament which serve a purpose of check by the Legislature. As per Section 159 of the Act any notification under Section 29 is to be placed before the Parliament and Parliament may amend or reject the 57 same. The Rules, 2017 are just, fair and reasonable and in furtherance of the object of the Act and do not provide for any arbitrary, uncanalised or unbridled power. 64. Shri Rakesh Dwivedi, learned senior counsel, appearing on behalf of UIDAI and State of Gujarat has made elaborate submissions while replying the arguments of petitioners. The right to privacy is part of Article 21. The autonomy of individual is associated over matters which can be kept private. These are concerns over which there is a reasonable expectation of privacy. The reasonable expectation involves two aspects. Firstly, the individual or individuals claiming a right to privacy must establish that their claim involves a concern about some harm likely to be inflicted upon them on account of the alleged act. This concern should be real and not imaginary or speculative. Secondly, the concern should not be inflated.
65. The Act, 2016 operates in the relational sphere and not in the core, private or personal sphere of residents. It involves minimal identity information for effective authentication. The purpose is limited to authenticate for identification. The Act operates in a public sphere. Section 29 of the Aadhaar Act, 2016 provides protection against disclosure of identity information without the prior consent of the Aadhaar Number holder concerned. Sharing is intended only for authentication purposes.
66. It is submitted that by their very nature the demographic information and photograph sought to be collected cannot be said to be of such a nature as would make it a part of a reasonable expectation paradigm. Today, globally all ID cards and passports contain photographs for identification along with address, date of birth, gender etc. The demographic information is readily provided by individuals globally for disclosing identity while relating with others; while seeking benefits whether provided by government or by private entities. People who get 59 registered for engaging in a profession, who take admissions in Schools/Colleges/university, who seek employment in the government or private concerns and those who engage in various trade and commerce are all required to provide demographic information and even photographs. There is no expectation of privacy in providing those information for the above purposes.
67. There are lot of enactments which require disclosure of demographic information comprising name, address, email address etc., for example Central Motor Vehicle Rules, 1989, Companies Act, 2013, Special Marriage Act, The Registration of Electoral Rules, 1960, The Citizenship (Registration of Citizens and Issue of National Identity Cards) Rules, 2009 and the Passports Act. However, there are certain special contexts in which nondisclosure of demographic information could be considered as raising a reasonable expectation of privacy such as where juveniles in conflict with law are involved or where a rape victim’s identity or medical information is involved. Thus, unless some such special context or 60 aggravating factor is established, there would not be any reasonable expectation of privacy with respect to demographic information.
68. As regards the core biometric information, comprising finger prints and iris scans it would be pertinent to bear in mind that the Aadhaar Act is not dealing with the intimate or private sphere of the individual. The core biometrics are being collected from residents for authentication use in a public sphere and in relational context in which regard there is no reasonable expectation of privacy in relation to fingerprints and iris scans. Iris scan is nothing but a photograph of the eyes taken from a camera. From fingerprints and iris scans nothing is revealed with regard to a person.
69. Use of fingerprints with regard to registration of documents is an accepted phenomena. The use of mandatory requirement of biometric attendance is increasing day by day both in public and private sector. Thus, requirement of fingerprints and iris 61 scan would not attract the fundamental right of privacy. The fingerprint and iris scan have been considered to be most accurate and noninvasive mode of identifying an individual. 70. The information collected under the Act, 2016 does not involve processing for economic and sociological purposes. Further, in the data center deduplication process is based on anonymization and what is stored in the servers for authentication process are simply templates and encrypted information of Aadhaar number and demographics. The identity data collected is stored offline. There is no internet connectivity. Thus, there is more than a reasonable security protection under the Act.
71. The rationale of Section 7 lies in ensuring targeted delivery of services, benefits and subsidies which are funded from the Consolidated Fund of India. In discharge of its solemn Constitutional obligation to enliven the Fundamental Rights of life and personal liberty and to eliminate inequality with a view to 62 ameliorate the lot of the poor and the Dalits, the Central Government has launched several welfare schemes. Some of such schemes are PDS, scholarship, mid day meals, LPG subsidies, free education,etc.
72. The requirement to undergo authentication on the basis of Aadhaar number is made mandatory by Section 7. This requirement is only for “undertaking authentication”. However, if authentication fails, despite more than one attempt then the possession of Aadhaar number can be proved otherwise, i.e., by producing the Aadhaar card, and those who do not have Aadhaar number can make an application for enrolment and produce the enrolment id number (EID). This takes care of nonexclusion.
73. Aadhaar Act truly seeks to secure to the poor and deprived persons an opportunity to live their life and exercise their liberty. By ensuring targeted delivery through digital identification, it not only provides them a nationally recognised identity but also attempts to ensure the delivery of benefits, service 63 and subsidies with the aid of public exchequer/Consolidated Fund of India. And it does so without impacting the Fundamental Right to Privacy of the Indians or at best minimally impacting it with adequate safeguards.
74. Regarding the numerization or numericalization of individual argument, it is submitted that the Aadhaar number does not convert the human being into a number. The objective of the Aadhaar number is to enable authentication which is done on a 1:1 matching basis, i.e., to say when the requesting entity feeds the Aadhaar number along with some identity information then the CIDR picks up the template having that Aadhaar number automatically and matches identity information with the encrypted information in the template. This Aadhaar number is, therefore, absolutely essential for the technological success of authentication.
It is, therefore, a technology requirement and it does not amount to numerization or numericalisation. The contention of the petitioners ignores the distinction between identity and 64 identification. The 12 digit Aadhaar number is not given by UIDAI to alter the identity of the individual. It is provided to the enrolled individual to enable his identification through authentication. Authentication is a multi dimensional identifying process. The Aadhaar number is one element or one identifier in the process of identification through authentication. It is identificational in nature. Section 2(a) of Aadhaar Act defines Aadhaar number to mean “an identification number”. Section 2(c) defines authentication as a process requiring submission of Aadhaar number to CIDR for verification. Further, Section 4(2) provides that the Aadhaar number shall be a random number and shall bear no relation to the attributes or identity of the Aadhaar number holder. It is proof of identity and not identity itself.
75. Replying the submission of the petitioners that fundamental right of privacy/dignity/autonomy under Article 21 could not be waived. It is submitted that Section 7 of Aadhaar Act does not involve any issue of waiver. When an individual undergoes any 65 authentication to establish his identity to receive benefits, services or subsidies, he does so to enliven his fundamental right to life and personal liberty under Article 21.
76. With regard to Section 57, it is submitted that since an infrastructure for establishing identity of residents is available, therefore, Parliament intends to make the use of Aadhaar number available for other purposes provided the need for the service of authentication arises pursuant to any law or contract. The rationale seems to be that due to liberalisation and privatisation in many governmental and public sector zones, private corporate bodies are operating in parallel and in competition with public sector – banking, insurance, defence, health etc.
These are vital core sectors absolutely essential for National integrity, National economy and life of people. In many areas private bodies operate under common regulators such as TRAI, Airport Authority, IRDA etc. Then there is rapidly growing ecommerce.
77. In Reply to the submission of Shri Kapil Sibal that the real object of the Act was to provide data to the digital giants like Google, Facebook and other private players, it is contended that there is no factual foundation for this submission in any writ petition. In the Act there is a complete bar with respect to sharing of core biometric information vide Section 29(1). The noncore biometric information is to be shared only as per the provisions of the Act and Regulations and with prior consent and only for the purpose of authentication.
78. On the submission of the petitioners that power of UIDAI to add identity information by Regulation is unguided and violative of Article 14, it is submitted that clauses (g) and (j) of Section 2 use the expression ‘such other biological attribute’. This general expression needs to be construed by applying the doctrine of ejusdem generis. The use of word ‘such’ implies similarity with what is specifically mentioned before the general expression. The Regulations framed by UIDAI are required to be laid 67 before the Parliament under Section 55. Section 55 is a mandatory provision. The Parliament has power to modify the Regulation and also to reject the Regulation.
This is a legislative check on the Regulation making power.
79. Almost 3% of GDP amounting to trillions of rupees is allocated by Governments towards subsidies, scholarships, pensions, education, food and other welfare programmes. But approximately half of it does not reach the intended beneficiaries. A former Prime Minister said only 15 out of 100 rupees reaches the target person. This was confirmed by the Planning Commission. In the Audit Report No.3 of 2000 CAG stated in “Overview” that programmes suffered from serious targeting problems. It noted that bogus ration cards were being used for diversions (1.93 crores bogus).
80. Even otherwise, there is no other identification document which is widely and commonly possessed by the residents of the country and most of the identity documents do not enjoy the quality of portability. 68 They also do not lend assurance and accuracy on account of existence of fake, bogus and ghost cards. Therefore, there was need of a biometric Aadhaar number which enables deduplication and authentication.
81. Shri Dwivedi submits that security and data privacy is ensured in the following manner:
(i) The data sent to ABIS is completely anonymised. The ABIS systems do not have access to resident’s demographic information as they are only sent biometric information of a resident with a reference number and asked to deduplicate. The deduplication result with the reference number is mapped back to the correct enrolment number by the Authorities own enrolment server.
(ii) The ABIS providers only provide their software and services. The data is stored in UIDAI storage and it never leaves the secure premises.
(iii) The ABIS providers do not store the biometric images (source). They only store template for the purposes of deduplication (with reference number).
(iv) The encrypted enrolment packet sent by the enrolment client software to the CIDR is decrypted by the enrolment server but the decrypted packet is never stored.
(v) The original biometric images of fingerprints, iris and face are archived and stored offline. Hence, they cannot be accessed through an online network.
(vi) The biometric system provides high accuracy of over 99.86%. The mixed biometric have been adopted only to enhance the accuracy and to reduce the errors which may arise on account of some residents either not having biometrics or not having some particular biometric.
82. Biometrics are being used for unique identification in epassports by 120 countries. Out of these many countries use fingerprints and/or iris scans. Additionally 19 European Countries have smart National Identity cards having chips containing 70 biometric information. A number of African and Asian countries are also using biometrics for identification. The ECHR and ECJ have not declared the use of biometrics or the collection and storage of data for the said purpose to be violative of Human Rights. It has infact been upheld in the context of passports, by the ECJ.
83. On the submissions that deduplication/ authentication software has been received from three foreign suppliers and since the source code of the algorithm is with the foreign suppliers, therefore, they can easily obtain the data in the CIDR merely by manipulation of the algorithm, Shri Dwivedi submits that foreign biometric solution providers only provide the software, the server and hardware belongs to UIDAI. So far the software is concerned UIDAI uses the software as licensee. There is no free access to the server room which is wholly secured by security guards. The enrolment data packet, after being received in the data center, is decrypted for a short duration to enable extraction of minutiae and 71 preparation of templates. Once the template is prepared the entire biometric data is stored offline under the complete control of the UIDAI officials.
84. It is correct that the source code for the algorithms provided are retained by the BSPs which constitutes the intellectual property right of the BSP, however, it does not introduce any insecurity of data in the CIDR as the softwares operate automatically in the servers located in the server rooms and also because the software functions only on the basis of the templates whilst the biometric data is stored offline.
85. During the submissions, Shri Dwivedi also emphasised on prohibition of sharing of core biometric information. As per Section 29(1) read with Regulation 17(1) of the Aadhaar (Sharing of Information) Regulations, 2016. Referring to various Regulations of the above Regulations. Shri Dwivedi submitted that the architecture of Aadhaar and its functioning does not permit CIDR to note about parties of any transaction 72 or location of the individual seeking identification of his Aadhaar number. Requesting Agency is strictly restricted to sharing of only demographic information plus photograph and for authentication only, and this is also with express and separate prior consent of the ANH. Requesting Entities cannot share authentication logs with any person other than the ANH or for grievance redressal and resolution of disputes or with the Authority for audit and shall not be used for any purpose other than stated in Regulation 18(5).
86. Elaborating on security Shri Dwivedi submitted that Section 28(4) mandates that the UIDAI shall ensure that the agencies appointed by it have in place the appropriate technical and organizational security measures for the information and ensure that the agreements or arrangements entered into with such agencies impose obligations equivalent to those imposed on the Authority and require such agencies to act only on instructions from the Authority.
87. RE shall ensure that the identity information of 73 the ANH or any other information generated during the authentication is kept confidential, secure and protected against access, use and disclosure not permitted under the Act and regulations.[Regulation 17(1)(e)]. The private key used for digitally signing the authentication request and the license keys are kept secure and access controlled[Regulation 17(1)(f) and 22(3)]. All relevant laws and regulations in relation to data storage and data protection relating to Aadhaar based identity information in their systems, that of their agents and with authentication devices are compiled with [Regulation 17(1)(g)].
88. Regulation 22(4) provides that RE shall adhere to all regulations, information security policies, processes, standards, specifications and guidelines issued from time to time. 89. By virtue of Section 56 and 61 of the Aadhaar Act, 2016, the provisions of IT Act, 2000 are applicable except where it is inconsistent with Aadhaar Act. The regular regime under the IT Act with all its provisions for punishment and penalty are attracted 74 since the biometric information is an electronic record and the data is sensitive personal data or information as defined in the IT Act, 2000. On submission of the petitioner that there is no mechanism for raising any grievance, Shri Dwivedi submits that UIDAI has set up grievance redressal cell as contemplated under Section 23(1)(s) of the Act. Any ANH can make a complaint for redressal of grievance.
90. The petitioner’s submission that Aadhaar Act enables the State to put the entire population of the country in an electronic leash and to track them all the time and it has converted itself as the State into a totalitarian State, it is submitted that none of the four clauses of Regulation 26 entitle the authority to store data about the purpose for which authentication is being done. Section 32(3) of the Aadhaar Act specifically prohibits the authority from collecting, storing or maintaining, whether directly or indirectly any information about the purpose of authentication. The proviso to Regulation 26 is also to the same effect. Here, “the purpose of authentication” means 75 the nature of activity being conducted by ANH in relation to which the authentication is required and is being done.
91. It is submitted that the devices which are used for the purpose of authentication are not geared or designed to record the nature of the activity being done by the ANH which necessitates authentication. The device can only tell the authority about the time of authentication, the identity of the RE, the PID, the time and nature of response, the code of the device and the authentication server side configurations. Hence, with the aid of authentication record it is not possible for the UIDAI to track the nature of activity being engaged into by the ANH. In fact, in overwhelming majority of cases the authentication record would not enable the authority to know even the place/location where the activity is performed by the ANH. The reason is that there are about 350 number of REs.
The REs alone can authenticate with the help of CIDR and this is done by them through the ASA. In a large number of cases, the organizations requiring 76 authentication would be doing so through some RE with whom they have some agreements. To illustrate nic.in is an RE which provides authentication service to large number of government organizations who have agreements with it. The authentication record would only contain information about the identity about the RE. It will give information only about the RE(nic.in) and not about the organization which is requiring authentication through the RE. In most cases the authentication is one time.
92. It is submitted that biometrics is being increasingly resorted to for identification purposes by many countries. At least 19 countries in Europe are using biometric smart cards where data is stored in the chip. These smart cards are similar to the smart cards which were used under the 2006 Act in U.K. The important difference lies in the extent of data of the individual which is stored in the smart card. The European cards unlike the UK, do not store 50 categories of data which was being stored in the UK card that came to be abolished in 2010 by the 77 Repealing Act, 2010. In some European countries the smart cards are issued in a decentralized manner, as in Germany.
But in some other countries the smart cards are issued in a centralized manner. In either case, the State is possessed of all the information which is stored in the chip of the smart card, though it may not involve authentication. These smart cards are considered to be property of the State and the State can require the production of the smart card for identification at any time. Estonia is considered to be a pioneer and leader in the field of the use of biometrics and it has a centralized data base.
93. It is submitted that the architecture of the Aadhaar Act does not lead to any real possibility, proximate or remote of mass surveillance in real time by the State. This is not an Act for empowering surveillance by the State. It merely empowers the State to ensure proper delivery of welfare measures mandated by Directive Principles of State Policy(Part IV of the Constitution) which actually enliven the Fundamental Rights under Article 14, 19 and 21 of the 78 Constitution for a vast majority of the poor and down trodden in the country and thereby to bring about their comprehensive emancipation. It seeks to ensure, justice, social, economic and political for the little Indians.
94. Responding on the arguments raised by the petitioner on Section 47 of the Act, it is submitted that Section 47 has rationale. The offences and penalties under Chapter VII are all intended to maintain the purity and integrity of CIDR which has been established of the ANH. Secondly, the entire enrolment, storage in CIDR and authentication exercise is so vast and that any breach can be handled with efficiency and effectively only by UIDAI. There are similar enactments which contain similar provisions which have been upheld by this Court. An individual can make a complaint to UIDAI directly or through grievance redressal cell. The authority would be obliged to examine the complaints and to lodge the complaint in the Court as per Section 47. Additionally, the individual is generally likely to 79 have a complaint of identity theft, cheating or disclosure. In such a situation he can always invoke the provisions of Sections 66C, 66D and 72A of the IT Act, 2000. The said offences carry identical penalties.
95. Elaborating on Section 59 of the Act, it is submitted that Section 59 purports to provide a statutory basis to the resolution of the Government of India, Planning Commission dated 28.01.2009 and also to validate anything done or any action taken by the Central Government under the said resolution. Section 59 of the Aadhaar Act seeks to continue what was done and the actions which were taken under the Resolution dated 28.01.2009. Section 59 is clearly extending its protection retrospectively to that which was done under the notification dated 28.01.2009.
96. Section 59 provides a deemed fiction. As a result of this deemed fiction one has to imagine that all the actions taken under the aforesaid notifications were done under the Act and not under the aforesaid notifications.
97. Replying the submission of the petitioner that large scale of marginal section of the society is deprived due to exclusion from getting the benefits and the Act violates Article 14 of the Constitution, it is submitted that there is no exclusion on account of deduplication. It cannot be denied that there may be some cases where due to nonidentification, a person may have been put to some disadvantage but on failure of authentication the authorities have clear discretion to accept other means of identification to deliver the subsidies and benefits. In any view of the matter on some administrative lapses and some mistakes in implementation does not lead to conclude that Act is unconstitutional and wrong implementation of the Act does not effect the constitutionality of the statutes.
98. Learned counsel for the parties have placed reliance on several judgments of this Court and Foreign Courts in support of their respective submissions which we shall notice while considering the respective submissions hereinafter.
99. Apart from hearing elaborate submissions made by the learned counsel for the petitioners as well as the respondents, we have also heard several learned counsel for the intervener. The submission made by the intervener has already been covered by learned counsel for the petitioners as well as for the respondents, hence it needs no repetition.
100. We have considered the submissions raised before us. From the pleadings on record and the submissions made following are the main issues which arise for consideration: (1) Whether requirement under Aadhaar Act to give one’s demographic and biometric information is violative of fundamental right of privacy ?
(2) Whether the provisions of Aadhaar Act requiring demographic and biometric information from a resident for Aadhaar number are unconstitutional and do not pass three fold test as laid down in Puttaswamy case ?
(3) Whether collection of data of residents, its storage, retention and use violates fundamental right of privacy ?
(4) Whether Aadhaar Act creates an architecture for pervasive surveillance amounting to violation of fundamental right of privacy ?
(5) Whether the Aadhaar Act provides protection and safety of the data collected and received from individual ?
(6) Whether Section 7 of Aadhaar Act is unconstitutional since it requires that for purposes of establishment of identity of an individual for receipt of a subsidy, benefit or service such individual should undergo authentication or furnish proof of possession of Aadhaar number or satisfy that such person has made an application for enrolment ?
Further the provision deserves to be struck down on account of large number of denial of rightful claims of various marginalised section of society and down trodden?
(7) Can the State while enlivening right to food, right to shelter etc. envisaged under Article 21 encroach upon the rights of privacy of the beneficiaries ?
(8) Whether Section 29 of the Aadhaar Act is liable to be struck down inasmuch as it permits sharing of identity information ?
(9) Whether Section 33 is unconstitutional inasmuch as it provides for the use of Aadhaar data base for Police investigation, which violates the protection against selfincrimination as enshrined under Article 20(3) of the Constitution of India ?
(10) Whether Section 47 of Aadhaar Act is unconstitutional inasmuch as it does not allow an individual who finds that there is a 84 violation of Aadhaar Act to initiate a criminal process ?
(11) Whether Section 57 of Aadhaar Act which allows an unrestricted extension of Aadhaar information of an individual for any purpose whether by the State or any body, corporate or person pursuant to any law or contact is unconstitutional ?
(12) Whether Section 59 is capable of validating all actions taken by the Central Government under notification dated 28.01.2009 or under notification dated 12.09.2015 and all such actions can be deemed to be taken under the Aadhaar Act?
(13) Whether Aadhaar Act is unconstitutional since it collects the identity information of children between 5 to 18 years without parental consent ?
(14) Whether Rule 9 as amended by PMLA (Second Amendment) Rules, 2017 is unconstitutional being violative of Article 14, 19(1)(g), 21 and 300A 85 of Constitution of India and Section 3,7, 51 of Aadhaar Act. Further, whether Rule 9 is ultra vires to the PMLA Act, 2002. itself.
(15) Whether circular dated 23.02.2017 issued by the Department of Telecommunications, Government of India is ultra vires.
(16) Whether Aadhaar Act could not have been passed as Money Bill ? Further, whether the decision of Speaker of Lok Sabha certifying the Aadhaar (Targeted Delivery of Financial and other Subsidies, Benefits and Services) Bill, 2016 as Money Bill is subject to judicial review ?
(17) Whether Section 139AA of the Income Tax Act, 1961 is unconstitutional in view of the Privacy judgment in Puttaswamy case?
(18) Whether Aadhaar Act violates the Interim Orders passed by this Court in Writ Petition (C) No. 494 of 2012 & other connected cases?
Issue Nos.1 and 2
Whether requirement under Aadhaar Act to give one’s demographic and biometric information is violative of fundamental right of privacy ?
And Whether the provisions of Aadhaar Act requiring demographic and biometric information from a resident for Aadhaar number are unconstitutional and do not pass three fold test as laid down in Puttaswamy case ?
101. Before we answer the above issues we need to look into the object and purpose for which Aadhaar Act was enacted. The Statement of Objects and Reasons particularly paragraph 5 of such Statement throws light on the object for which Legislation came into existence. Paragraph 5 of the Statement of Objects and Reasons is as follows:
“5. The Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Bill, 2016, inter alia, seeks to provide for-
(a) issue of Aadhaar numbers to individuals on providing his demographic and biometric information to the Unique Identification Authority of India;
(b) requiring Aadhaar numbers for identifying an individual for delivery of benefits, subsidies, and services the expenditure is incurred from or the receipt therefrom forms 87 part of the Consolidated Fund of India;
(c) authentication of the Aadhaar number of an Aadhaar number holder in relation to his demographic and biometric information;
(d) establishment of the Unique Identification Authority of India consisting of a Chairperson, two Members and a MemberSecretary to perform functions in pursuance of the objectives above;
(e) maintenance and updating the information of individuals in the Central Identities Data Repository in such manner as may be specified by regulations;
(f) measures pertaining to security, privacy and confidentiality of information in possession or control of the Authority including information stored in the Central Identities Data Repository; and
(g) offences and penalties for contravention of relevant statutory provisions.”
102. Preamble to any Act is a key to read and unfold an enactment. The Preamble of Aadhaar Act reads: “An Act to provide for, as a good governance, efficient, transparent, and targeted delivery of subsidies, benefits and services, the expenditure for which is incurred from the Consolidated Fund of India, to individuals residing in India through assigning of unique identity numbers to such individuals and for 88 matters connected therewith or incidental thereto.”
103. Section 2 of the Act is definition clause. Section 2(a) defines “Aadhaar number” in the following manner: “2(a) “Aadhaar number” means an identification number issued to an individual under subsection (3) of section 3;” 104. Sections 2(g) and 2(k) define “biometric information” and “demographic information” which is to the following effect:
“2(g) “biometric information” means photograph, finger print, Iris scan, or such other biological attributes of an individual as may be specified by regulations;
(k) “demographic information” includes information relating to the name, date of birth, address and other relevant information of an individual, as may be specified by regulations for the purpose of issuing an Aadhaar number, but shall not include race, religion, caste, tribe, ethnicity, language, records of entitlement, income or medical history;
105. Section 3 of the Act deals with Aadhaar enrolment. Section 3 is as follows:
“3.(1) Every resident shall be entitled to obtain an Aadhaar number by submitting his demographic information and biometric information by undergoing the process of enrolment: Provided that the Central Government may, from time to time, notify such other category of individuals who may be entitled to obtain an Aadhaar number.
(2) The enrolling agency shall, at the time of enrolment, inform the individual undergoing enrolment of the following details in such manner as may be specified by regulations, namely:-
(a) the manner in which the information shall be used;
(b) the nature of recipients with whom the information is intended to be shared during authentication; and
(c) the existence of a right to access information, the procedure for making requests for such access, and details of the person or department incharge to whom such requests can be made.
(3) On receipt of the demographic information and biometric information under subsection (1), the Authority shall, after verifying the information, in such manner as may be specified by regulations, issue an Aadhaar number to such individual.”
106. The challenge in this batch of cases is challenge to the Act and its various provisions on the ground that the Act and its provisions violate right of privacy which is now recognised as fundamental right. 90 All aspects of privacy right, which is accepted as a fundamental right under Article 21, have been elaborately and authoritatively dealt by nineJudge Constitution Bench of this Court in Puttaswamy case (supra).
107. Alan F. Westin in his work “Privacy and Freedom” defined privacy as “the desire of people to choose freely under what circumstances and to what extent they will expose themselves, their attitudes and their behaviour to others”.
108. Dr. D.Y. Chandrachud, J., in his opinion (which expresses majority opinion) in paragraph 3 of the judgment while analysing the concept of privacy held:
“3. Privacy, in its simplest sense, allows each human being to be left alone in a core which is inviolable. Yet the autonomy of the individual is conditioned by her relationships with the rest of society. Those relationships may and do often pose questions to autonomy and free choice. The overarching presence of State and nonState entities regulates aspects of social existence which bear upon the freedom of the individual. The preservation of constitutional liberty is, so to speak, work in progress. Challenges have to be addressed to existing problems. Equally, new challenges have to be dealt with in terms of a constitutional understanding of where liberty places an individual in the context of a social order.
The emergence of new challenges is exemplified by this case, where the debate on privacy is being analysed in the context of a global information based society. In an age where information technology governs virtually every aspect of our lives, the task before the Court is to impart constitutional meaning to individual liberty in an interconnected world. While we revisit the question whether our Constitution protects privacy as an elemental principle, the Court has to be sensitive to the needs of and the opportunities and dangers posed to liberty in a digital world.”
109. Dwelling on essential nature of privacy in paragraphs 297 and 298 following has been laid down by
Dr. D.Y. Chandrachud, J.:
“297. What, then, does privacy postulate? Privacy postulates the reservation of a private space for the individual, described as the right to be let alone. The concept is founded on the autonomy of the individual. The ability of an individual to make choices lies at the core of the human personality. The notion of privacy enables the individual to assert and control the human element which is inseparable from the personality of the individual. The inviolable nature of the human personality is manifested in the ability to make decisions on matters intimate to human life. The autonomy of the individual is associated over matters which can be kept private. These are concerns over which there is a legitimate expectation of privacy. The body and the mind are inseparable elements of the human personality.
The integrity of the body and the sanctity of the mind can exist on the foundation that each individual possesses an inalienable ability and right to preserve a private space in which the human personality can develop. Without the ability to make choices, the inviolability of the personality would be in doubt. Recognising a zone of privacy is but an acknowledgment that each individual must be entitled to chart and pursue the course of development of personality. Hence privacy is a postulate of human dignity itself….
298. Privacy of the individual is an essential aspect of dignity. Dignity has both an intrinsic and instrumental value. As an intrinsic value, human dignity is an entitlement or a constitutionally protected interest in itself. In its instrumental facet, dignity and freedom are inseparably intertwined, each being a facilitative tool to achieve the other. The ability of the individual to protect a zone of privacy enables the realisation of the full value of life and liberty. Liberty has a broader meaning of which privacy is a subset. All liberties may not be exercised in privacy.
Yet others can be fulfilled only within a private space. Privacy enables the individual to retain the autonomy of the body and mind. The autonomy of the individual is the ability to make decisions on vital matters of concern to life. Privacy has not been couched as an independent fundamental right. But that does not detract from the constitutional protection afforded to it, once the true nature of privacy and its relationship with those fundamental rights which are expressly protected is understood. Privacy lies across the spectrum of protected freedoms.
The guarantee of equality is a guarantee against arbitrary State action. It prevents the State 93 from discriminating between individuals. The destruction by the State of a sanctified personal space whether of the body or of the mind is violative of the guarantee against arbitrary State action. Privacy of the body entitles an individual to the integrity of the physical aspects of personhood. The intersection between one’s mental integrity and privacy entitles the individual to freedom of thought, the freedom to believe in what is right, and the freedom of selfdetermination. When these guarantees intersect with gender, they create a private space which protects all those elements which are crucial to gender identity. The family, marriage, procreation and sexual orientation are all integral to the dignity of the individual. Above all, the privacy of the individual recognises an inviolable right to determine how freedom shall be exercised.”
110. This Court has further held that like the right to life and liberty, privacy is not absolute. Any curtailment or deprivation of that right would have to take place under a regime of law. In paragraph 313 following has been held:
“313. Privacy has been held to be an intrinsic element of the right to life and personal liberty under Article 21 and as a constitutional value which is embodied in the fundamental freedoms embedded in Part III of the Constitution. Like the right to life and liberty, privacy is not absolute. The limitations which operate on the right to life and personal liberty would operate on the right to privacy. Any curtailment or deprivation of that right would have to take 94 place under a regime of law. The procedure established by law must be fair, just and reasonable. The law which provides for the curtailment of the right must also be subject to constitutional safeguards.”
111. Further elaboration of the core of privacy has been stated in the following words in paragraphs 322, 323 and 326:
“322. Privacy is the constitutional core of human dignity. Privacy has both a normative and descriptive function. At a normative level privacy subserves those eternal values upon which the guarantees of life, liberty and freedom are founded. At a descriptive level, privacy postulates a bundle of entitlements and interests which lie at the foundation of ordered liberty.
323. Privacy includes at its core the preservation of personal intimacies, the sanctity of family life, marriage, procreation, the home and sexual orientation. Privacy also connotes a right to be left alone. Privacy safeguards individual autonomy and recognises the ability of the individual to control vital aspects of his or her life. Personal choices governing a way of life are intrinsic to privacy. Privacy protects heterogeneity and recognises the plurality and diversity of our culture. While the legitimate expectation of privacy may vary from the intimate zone to the private zone and from the private to the public arenas, it is important to underscore that privacy is not lost or surrendered merely because the individual is in a public place. Privacy attaches to the person since it is an essential facet of the dignity of the human being. 326. Privacy has both positive and negative content.
The negative content restrains the State from committing an intrusion upon the life and personal liberty of a citizen. Its positive content imposes an obligation on the State to take all necessary measures to protect the privacy of the individual.”
112. The first issue which is under consideration is as to whether requirement under the Aadhaar Act to give one’s biometric and demographic information is violative of fundamental right of privacy. Demographic and biometric information has been defined in Section 2 as noted above. Biometric information and demographic information are two distinct concepts as delineated in the Act itself. We first take up the demographic information which includes information relating to the name, date of birth, address and other relevant information of an individual, as may be specified by regulations for the purpose of issuing an Aadhaar number. There is also injunction in Section 2(k) that demographic information shall not include race, religion, caste, tribe, ethnicity, language, 96 records of entitlement, income or medical history. Thus, demographic information which are contemplated to be given in the Act are very limited information. The Regulations have been framed under Act, namely, Aadhaar (Enrolment and Update) Regulations, 2016. Regulation 4 enumerates demographic information which shall be collected from individuals undergoing enrolment. Regulation 4 is as follows:
“4. Demographic information required for enrolment. –
(1) The following demographic information shall be collected from all individuals undergoing enrolment (other than children below five years of age):
(i) Name;
(ii) Date of Birth;
(iii) Gender;
(iv) Residential Address.
(2) The following demographic information may also additionally be collected during enrolment, at the option of the individual undergoing enrolment:
(i) Mobile number;
(ii) Email address.
(3) In case of Introducerbased enrolment, the following additional information shall be collected:
(i) Introducer name;
(ii) Introducer’s Aadhaar number.
(4) In case of Head of Family based enrolment, the following additional information shall be collected:
(i) Name of Head of Family;
(ii) Relationship;
(iii) Head of Family’s Aadhaar number;
(iv) One modality of biometric information of the Head of Family.
(5) The standards of the above demographic information shall be as may be specified by the Authority for this purpose.
(6) The demographic information shall not include race, religion, caste, tribe, ethnicity, language, record of entitlement, income or medical history of the resident.”
113. A perusal of Regulation 4 indicates that information which shall be collected from individual are his name, date of birth, gender and residential address. The additional information which can be collected at the option of the individual is mobile number and email address. Schedule I of the Regulation contains format of enrolment form which contains columns for information as contemplated under Regulation 4.
114. The information contemplated under Regulation 4 are nothing but information relating to identity of the person.
115. Every person born on earth takes birth at a place at a time with a parentage. In the society person is identified as a person born as son or daughter of such and such. The identity of person from the time of taking birth is an identity well known and generally every person describes himself or herself to be son or daughter of such and such person.
116. Every person, may be a child in school, a person at his workplace, relates himself or herself with his or her parent’s, place of birth etc., in interaction with his near and dear and outside world a person willingly and voluntarily reveals his identity to others in his journey of life. The demographic information are readily provided by individuals globally for disclosing identity while relating with others; while seeking benefits whether provided by government or by private entities.
People who get 99 registered for engaging in a profession, who take admissions in schools/colleges/ university, who seek employment in the government or private concerns, and those who engage in various trade and commerce are all required to provide demographic information. Hence, it can be safely said that there cannot be a reasonable expectation of privacy with regard to such information. There are large number of statutes which provide for giving demographic information by the individuals.
For inclusion of name of a person in the Electoral List as per the Registration of Electoral Rules, 1960 framed under the Representation of People Act, 1950, a person is required to give similar demographic information in Form II, i.e., name, date of birth, gender, current address and permanent address, which also contains optional particulars of email address and mobile number. Under Central Motor Vehicle Rules, 1989 person making an application for driving licence is required to give name, parent, permanent address, temporary address, date of birth, place of birth, educational qualification, etc.
117. Under Special Marriage Act, name, condition, occupation, age, dwelling place, age, etc. are to be given. Thus, providing such demographic information in most of the statutes clearly indicates that those information are readily provided and no reasonable expectation of privacy has ever been claimed or perceived in above respect. 118. It is well settled that breach of privacy right can be claimed only when claimant on the facts of the particular case and circumstances have “reasonable expectation of privacy”.
In Court of Appeal in Regina (Wood) v. Commissioner of Police of the Metropolis, (2009) EWCA Civ 414: (2010) 1 WLR 123, following was held: “22. This cluster of values, summarised as the personal autonomy of every individual and taking concrete form as a presumption against interference with the individual’s liberty, is a defining characteristic of a free society. We therefore need to preserve it even in little cases. At the same time it is important that this core right protected by Article 8, however protean, should not be read so widely that its claims become unreal and unreasonable. For this purpose I think there are three safeguards, or 101 qualifications.
First, the alleged threat or assault to the individual’s personal autonomy must (if Article 8 is to be engaged) attain “a certain level of seriousness”. Secondly, the touchstone for Article 8(1)’s engagement is whether the claimant enjoys on the facts a “reasonable expectation of privacy” (in any of the senses of privacy accepted in the cases). Absent such an expectation, there is no relevant interference with personal autonomy. Thirdly, the breadth of Article 8(1) may in many instances be greatly curtailed by the scope of the justifications available to the State pursuant to Article 8(2). I shall say a little in turn about these three antidotes to the overblown use of Article 8.
24. As for the second a “reasonable expectation of privacy” I have already cited paragraph 51 of Von Hannover, with its reference to that very phrase, and also to a “legitimate expectation” of protection. One may compare a passage in Lord Nicholls’ opinion in Campbell at paragraph 21: “Accordingly, in deciding what was the ambit of an individual’s ‘private life’ in particular circumstances courts need to be on guard against using as a touchstone a test which brings into account considerations which should more properly be considered at the later stage of proportionality. Essentially the touchstone of private life is whether in respect of the disclosed facts the person in question had a reasonable expectation of privacy.” 102 In the same case Lord Hope said at paragraph 99: “The question is what a reasonable person of ordinary sensibilities would feel if she was placed in the same position as the claimant and faced with the same publicity.” In Murray v Big Pictures (UK) Ltd Sir Anthony Clarke MR referred to both of these passages, and stated:
“35… [S]o far as the relevant principles to be derived from Campbell are concerned, they can we think be summarised in this way. The first question is whether there is a reasonable expectation of privacy. This is of course an objective question. … 36. As we see it, the question whether there is a reasonable expectation of privacy is a broad one, which takes account of all the circumstances of the case. They include the attributes of the claimant, the nature of the activity in which the claimant was engaged, the place at which it was happening, the nature and purpose of the intrusion, the absence of consent and whether it was known or could be inferred, the effect on the claimant and the circumstances in which and the purposes for which the information came into the hands of the publisher.”
119. The reasonable expectation of privacy test was also noticed and approved in privacy judgment, Dr. D.Y Chandrachud, J. has referred judgment of US Supreme Court in Katz v. United States, 389 US 347 (1967), following has been observed by this Court in K.S. Puttaswamy (supra) in paragraph 185: “The majority adopted the “reasonable expectation of privacy” test as formulated by Harlan, J. in Katz and held as follows: “7. [The] inquiry, as Mr Justice Harlan aptly noted in his Katz66 concurrence, normally embraces two discrete questions.
The first is whether the individual, by his conduct, has “exhibited an actual (subjective) expectation of privacy” … whether … the individual has shown that “he seeks to preserve [something] as private”. … The second question is whether the individual’s subjective expectation of privacy is “one that society is prepared to recognize as “reasonable” ” … whether … the individual’s expectation, viewed objectively, is “justifiable” under the circumstances. … 8. … Since the pen register was installed on telephone company property at the telephone company’s central offices, petitioner obviously cannot claim that his “property” was invaded or that 104 police intruded into a “constitutionally protected area”.”
Thus the Court held that the petitioner in all probability entertained no actual expectation of privacy in the phone numbers he dialed, and that, even if he did, his expectation was not “legitimate”. However, the judgment also noted the limitations of the Katz test: “Situations can be imagined, of course, in which Katz66 twopronged inquiry would provide an inadequate index of Fourth Amendment protection. … In such circumstances, where an individual’s subjective expectations had been “conditioned” by influences alien to wellrecognised Fourth Amendment freedoms, those subjective expectations obviously could play no meaningful role in ascertaining what the scope of Fourth Amendment protection was.”
(emphasis supplied)
120. After noticing several judgments of US Supreme Court, D.Y.Chandrachud, J. in K.S. Puttaswamy (supra)has noted that the reasonable expectation of privacy test has been relied on by various other jurisdictions while developing the right of privacy. In paragraph 195 following has been held: “195. The development of the jurisprudence on the right to privacy in the United States of 105 America shows that even though there is no explicit mention of the word “privacy” in the Constitution, the courts of the country have not only recognised the right to privacy under various amendments to the Constitution but also progressively extended the ambit of protection under the right to privacy. In its early years, the focus was on property and protection of physical spaces that would be considered private such as an individual’s home. This “trespass doctrine” became irrelevant when it was held that what is protected under the right to privacy is “people, not places”. The “reasonable expectation of privacy” test has been relied on subsequently by various other jurisdictions while developing the right to privacy.”
121. As noted above an individual in interaction with society or while interacting with his close relatives naturally gives and reveals his several information e.g. his name, age, date of birth, residential address, etc. We are of the opinion that in giving of those information there is no reasonable expectation of privacy. Thus, we conclude that demographic information required to be given in the process of enrolment does not violate any right of privacy.
122. Every person born gets a name after his birth. He strives throughout his life to establish himself to 106 be recognised by society. Recognition by fellow man and society at large is cherished dream of all human being, for fulfilling the above dream, he does not hide himself from society rather takes pride in reasserting himself time and again when occasion arises. He proclaims his identity time and again.
123. The right to identity is an essential component of an individual in her relationship with the State. The identification is only the proof of identity and everyone has right to prove his identity by an acceptable means. Aadhaar is contemplated as one PAN INDIA identity, which is acceptable proof of identity in every nook and corner of the country.
124. Reference of International Declaration and covenants have been made to assert that providing for an identity to every resident is an international obligation of India. In this reference following has been referred to:Name of the Convention [Date of Accession] Provision 107 Universal Declaration of Human Rights,1948 [10.12.1948] Article 6: Everyone has the right to recognition everywhere as a person before the law. International Covenant on Civil and Political Rights, 1976 [10.04.1979] Article 16: Everyone shall have the right to recognition everywhere as a person before the law. UN Convention on the Rights of the Child, 1989 [11.12.1992] Article 8: States Parties undertake to respect the right of the child to preserve his or her identity, including nationality, name and family relations as recognized by law without unlawful interference. Article 29(1): States Parties agree that the education of the child shall be directed to:….(c) The development of respect for the child’s parents, his or her own cultural identity, language and values, for the national values of the country in which the child is living, the country from which he or she may originate, and for civilizations different from his or her own;….
125. We may also notice one of the applications filed by an organisation, namely, Swatantra, which works for and represents the interests of the transgender and sexual minorities communities in India. The submission has been made on behalf of organisation that Aadhaar 108 Act and Rules making the Unique Identification Number (UID) or the Aadhaar number mandatory and requiring them to provide their personal demographic and biometric information for enrolment is a serious infringement of the constitutional right to privacy and dignity of transgender persons.
It is submitted that the transgender community has experienced a history of legally and socially sanctioned violence and discrimination from private individuals and State authorities. Reference of Criminal Tribes Act, 1871 and certain State legislations has been made in this regard. The applicant also refers to judgment of this Court in National Legal Services Authority and Union of India and others, 2014 (5) SCC 438, where this Court has held that the freedom of expression includes one’s right to expression of a selfidentified gender identity through dress, action behaviour etc. The submission has been made that making the disclosure of gender under Section 2 of the Aadhaar Act and Regulation 4 of the Aadhaar (Enrolment & Update) Regulations violates Article 14 of the Constitution.
126. Further, the Aadhaar Act amounts to discrimination against transgender persons under Article 15 of the Constitution on the ground of gender. Further, it is contended that disclosure of gender identity violates Article 21 and Article 19(1) (a) of the transgender persons.
127. We having considered the provisions of the Act and Enrolment and Update Regulations and having found that disclosure of demographic information does not violate any right of privacy, the said conclusion shall also be fully applicable with regard to transgender. This Court in NALSA (supra) has held that Article 19(1)(a) which provides that all citizens shall have the right to freedom of speech and expression which includes one’s right to expression and his selfidentified gender, it is the right of a person to identify his gender. In paragraphs 69 and 72 of the judgment following has been laid down:
“69. Article 19(1) of the Constitution guarantees certain fundamental rights, subject to the power of the State to impose restrictions from exercise of those rights.
The rights conferred by Article 19 are not available to any person who is not a citizen of India. Article 19(1) guarantees those great basic rights which are recognized and guaranteed as the natural rights inherent in the status of the citizen of a free country. Article 19(1)(a) of the Constitution states that all citizens shall have the right to freedom of speech and expression, which includes one’s right to expression of his selfidentified gender. Selfidentified gender can be expressed through dress, words, action or behavior or any other form. No restriction can be placed on one’s personal appearance or choice of dressing, subject to the restrictions contained in Article 19(2) of the Constitution.
72. Gender identity, therefore, lies at the core of one’s personal identity, gender expression and presentation and, therefore, it will have to be protected Under Article 19(1) (a) of the Constitution of India. A transgender’s personality could be expressed by the transgender’s behavior and presentation. State cannot prohibit, restrict or interfere with a transgender’s expression of such personality, which reflects that inherent personality. Often the State and its authorities either due to ignorance or otherwise fail to digest the innate character and identity of such persons. We, therefore, hold that values of privacy, selfidentity, autonomy and personal integrity are fundamental rights guaranteed to members of the transgender community Under Article 19(1) (a) of the Constitution of India and the State is bound to protect and recognize those rights. “
128. When this Court has already recognised the 111 constitutional right of transgenders of their selfidentification and it has been further held that selfidentification relates to their dignity. Dignity is a human right which every human being possesses. Article 15 came for consideration in the said judgment where this Court held that Article 15 has used the expression ‘citizen’ and ‘sex’ which expressions are ‘gender neutral’. The protection of fundamental rights is equally applicable to transgenders. Paragraph 82 is as follows: “82. Article 14 has used the expression “person” and the Article 15 has used the expression “citizen” and “sex” so also Article 16. Article 19 has also used the expression “citizen”.
Article 21 has used the expression “person”. All these expressions, which are “gender neutral” evidently refer to humanbeings. Hence, they take within their sweep Hijras/Transgenders and are not as such limited to male or female gender. Gender identity as already indicated forms the core of one’s personal self, based on self identification, not on surgical or medical procedure. Gender identity, in our view, is an integral part of sex and no citizen can be discriminated on the ground of gender identity, including those who identify as third gender. “
129. This Court having recognised the right of 112 transgenders to their selfidentity in which transgenders also feel pride as human being, the mere fact that under Enrolment and Update Regulations they are required to provide demographic information regarding gender does not, in any manner, affect their right of privacy. There is no expectation of right of privacy with regard to gender. The aforesaid right having been clearly recognised by this Court, expression of those rights of selfidentification cannot, in any manner, be said to affect their right to privacy. We, thus, conclude that with regard to transgenders also no right of privacy is breached in giving the demographic information. In so far as biometric information as held above, ample justification has been found which satisfied the three fold test as laid down in Puttaswamy case, which is equally applicable to transgender also.
130. Now, we come to the biometric information as referred to in Section 2(g) and required to be given in the process of enrolment by a person. Biometric information means photographs, fingerprints, iris scan 113 and other such biometric attributes of an individual as may be specified by the regulations. Biometric informations are of physical characteristics of a person. A person has full bodily autonomy and any intrusion in the bodily autonomy of a person can be readily accepted as breach of his privacy. In Regina (Wood) Vs. Commissioner of Police of the Metropolis (supra), in paragraph 21, following has been laid down by Lord LJ.:”
21. The notion of the personal autonomy of every individual marches with the presumption of liberty enjoyed in a free polity: a presumption which consists in the principle that every interference with the freedom of the individual stands in need of objective justification. Applied to the myriad instances recognised in the Article 8 jurisprudence, this presumption means that, subject to the qualifications I shall shortly describe, an individual’s personal autonomy makes him should make him master of all those facts about his own identity, such as his name, health, sexuality, ethnicity, his own image, of which the cases speak; and also of the “zone of interaction” (the Von Hannover case 40 EHRR I, paragraph 50) between himself and others. He is the presumed owner of these aspects of his own self; his control of them can only be loosened, abrogated, if the State shows an objective justification for doing so.”
131. U.S. Supreme Court in United States Vs. Antonio Dionisio, 35 L.Ed. 2D 67 had occasion to consider physical characteristic of a person’s voice in context of violation of privacy rights. With regard to fingerprints, it was noticed that the fingerprinting itself involves none of the probing into an individual’s private life. In paragraph Nos. 21, 22 following was stated:”[ 21,22] In Katz v. United States, supra, we said that the Fourth Amendment provides no protection for what “a person knowingly exposes to the public, even in his own home or office . . ..” 389 U.S., at 351, 19 L Ed 2d 576. The physical characteristics of a person’s voice, its tone and manner, as opposed to the content of a specific conversation, are constantly exposed to the public. Like a man’s facial characteristics, or handwriting, his voice is repeatedly produced for others to hear. No person can have a reasonable expectation that others will not know the sound of his voice, any more than he can reasonably expect that his face will be a mystery to the world. As the Court of Appeals for the Second Circuit stated:
“Except for the rare recluse who chooses to live his life in complete solitude, in our daily lives we constantly speak and write, and while the content of a communication is entitled to Fourth Amendment protection . . . the underlying identifying characteristics-the constant factor throughout both public and private communications-are open for all to see or hear. There is no basis for constructing a wall of privacy against the grand jury which does not exist in casual contacts with strangers. Hence no intrusion into an individual’s privacy results from compelled execution of handwriting or voice exemplars; nothing is being exposed to the grand jury that has not previously been exposed to the public at large.”‘ United States v. Doe (Schwartz), 457 F2d, at 898899.
The required disclosure of a person’s voice is thus immeasurably further removed from the Fourth Amendment protection than was the intrusion into the body effected by the blood extraction in Schmerber. “The interests in human dignity and privacy which the Fourth Amendment protects forbid any such intrusions on the mere chance that desired evidence might be obtained.” Schmerber v. California, 384 US, at 769770, 16L Ed 2d 908. Similarly, a seizure of voice exemplars does not involve the “severe, though brief, intrusion upon cherished personal security,” effected by the “patdown” in Terry-“surely . . . an annoying, frightening and perhaps humiliating experience.” Terry v. Ohio, 392 US, at 2425, 20 L Ed 2d 889. Rather, this is like the fingerprinting in Davis, where, though the initial dragnet detentions were constitutionally impermissible, we noted that the fingerprinting itself “involves none of the probing into an individual’s private life and thoughts that marks an interrogation or search.” Davis v. Mississippi, 394 US, at 727, 22 L Ed 2d 676: cf.
Thom v. New York 116 Stock Exchange, 306 F Supp 1002, 1009.” 132. The petitioners have relied upon S. and Marper Vs. The United Kingdom, a judgment of Grand Chamber of European Court of Human Rights dated 04.12.2008. European Court of Human Rights on an application submitted by Mr. S and Mr. Marper allowed their claim of violation of Article 8 of Convention. Applicants had complained that the authorities had continued to retain their fingerprints and cellular samples and DNA profiles after the criminal proceedings against them had ended with an acquittal or had been discontinued. In the above context, nature of fingerprints and DNA samples came to be examined in reference of breach of Article 8 of the Convention. The retention of DNA samples and fingerprints was held to be interference with the right to respect for private life. In paragraph 84, following was held:”
84. The Court is of the view that the general approach taken by the Convention organs in respect of photographs and voice samples should also be followed in respect of fingerprints. The Government distinguished the latter by arguing that they constituted neutral, objective and irrefutable material 117 and, unlike photographs, were unintelligible to the untutored eye and without a comparator fingerprint. While true, this consideration cannot alter the fact that fingerprints objectively contain unique information about the individual concerned allowing his or her identification with precision in a wide range of circumstances. They are thus capable of affecting his or her private life and retention of this information without the consent of the individual concerned cannot be regarded as neutral or insignificant.”
133. One important observation, which has been made in the above case was that on the question whether the personal information retained by the authorities involves any of the privatelife aspects, due regard has to be given to the specific context in which the information at issue has been recorded. Following was stated in paragraph 67:”
67…………… However, in determining whether the personal information retained by the authorities involves any of the privatelife aspects mentioned above, the Court will have due regard to the specific context in which the information at issue has been recorded and retained, the nature of the records, the way in which these records are used and processed and the results that may be obtained (see, mutatis mutandis, Friedl, cited above, §§4951, and Peck v. the United Kingdom, cited above, §59).”
134. The biometric data as referred to in Section 2(g) thus may contain biological attributes of an individual with regard to which a person can very well claim a reasonable expectation of privacy but whether privacy rights have been breached or not needs to be examined in the subject context under which the informations were obtained.
135. Having found that biometric information of a person may claim a reasonable expectation of privacy, we have to answer as to whether obtaining biometric information in context of enrolment breaches the right of privacy of individual or not. 136. D.Y. Chandrachud, J. in Puttaswamy (supra) held that all restraints on privacy, i.e. whether a person has reasonable expectation of privacy, must fulfill three requirements before a restraint can be held to be justified. In Paragraph 319, following has been held:” 310. While it intervenes to protect legitimate state interests, the state must nevertheless put into place a robust regime that ensures the fulfillment of a threefold 119 requirement. These three requirements apply to all restraints on privacy (not just informational privacy).
They emanate from the procedural and contentbased mandate of Article 21. The first requirement that there must be a law in existence to justify an encroachment on privacy is an express requirement of Article 21. For, no person can be deprived of his life or personal liberty except in accordance with the procedure established by law. The existence of law is an essential requirement. Second, the requirement of a need, in terms of a legitimate state aim, ensures that the nature and content of the law which imposes the restriction falls within the zone of reasonableness mandated by Article 14, which is a guarantee against arbitrary State action.
The pursuit of a legitimate state aim ensures that the law does not suffer from manifest arbitrariness. Legitimacy, as a postulate, involves a value judgment. Judicial review does not reappreciate or second guess the value judgment of the legislature but is for deciding whether the aim which is sought to be pursued suffers from palpable or manifest arbitrariness. The third requirement ensures that the means which are adopted by the legislature are proportional to the object and needs sought to be fulfilled by the law. Proportionality is an essential facet of the guarantee against arbitrary State action because it ensures that the nature and quality of the encroachment on the right is not disproportionate to the purpose of the law.
Hence, the threefold requirement for a valid law arises out of the mutual interdependence between the fundamental guarantees against arbitrariness on the one hand and the protection of life and personal liberty, on the other. The right to privacy, which is an 120 intrinsic part of the right to life and liberty, and the freedoms embodied in Part III is subject to the same restraints which apply to those freedoms. ” 137. We, thus, have to test the provisions of Aadhaar Act in light of threefold test as have been laid down above. The First requirement, which need to be fulfilled is existence of law. Admittedly, Aadhaar Act is a Parliamentary law, hence the existence of law is satisfied. Mere existence of law may not be sufficient unless the law is fair and reasonable.
The Aadhaar Act has been enacted with an object of providing Aadhaar number to individuals for identifying an individual for delivery of benefits, subsidies and services. Several materials have been brought on the record which reflect that in the several studies initiated by the Government as well as the World Bank and Planning Commission, it was revealed that food grains released by the Government for the beneficiaries did not reach the intended beneficiaries and there was large scale leakages due to the failure to establish identity. Reference to 121 Audit Report No. 3 of 2000 of Comptroller & Auditor General of India is made in this regard.
The Planning Commission of India in its Performance Evaluation Report titled “Performance Evaluation Report of Targeted Public Distribution System(TPDS)” dated March, 2005 found as follows:I. Statewise figure of excess Ration Cards in various states and the existence of over 1.52 Crore excess Ration Cards issued.
II. Existence of fictitious households and identification errors leading to exclusion of genuine beneficiaries.
III. Leakage through ghost BPL Ration Cards found to be prevalent in almost all the States under study.
IV. The leakage of food grains through ghost cards has been tabulated and the percentage of such leakage on an All India basis has been estimated at 16.67%. V. It is concluded that a large part of the subsidized foodgrains were not reaching the 122 target group.
138. The Law, i.e., Aadhaar Act, which has been brought to provide for unique identity for delivery of subsidies, benefits or services was a dire necessity, which decision was arrived at after several reports and studies. Aadhaar Act was, thus, enacted for a legitimate State aim and fulfills the criteria of a law being fair and reasonable. Learned Attorney General has also placed reliance on report of United Nations titled “Leaving No One Behind: the imperative of inclusive development”, which has stated as follows:” The decision of India in 2010 to launch the Aadhaar programme to enrol the biometric identifying data of all its 1.2 billion citizens, for example, was a critical step in enabling fairer access of the people to government benefits and services. Programmes such as Aadhaar have tremendous potential to foster inclusion by giving all people, including the poorest and most marginalized, an official identify. Fair and robust systems of legal identity and birth registration are recognised in the new 2030 Agenda for Sustainable Development as an important foundation for promoting inclusive societies.”
139. Learned Attorney General has also relied on Resolution of the United Nations General Assembly dated 25.09.2015 titled “Transforming our World: the 2030 Agenda for Sustainable Development”. It is submitted that by the said resolution, the following goal was adopted”” 16.9 by 2030, provide legal identity for all, including birth registration”
140. In this context, judgment of U.S. Supreme Court in Otis R. Bowen, Secretary of Health and Human Services, et al. Vs. Stephen J. Roy et al., 476 U.S. 693 (1986) is referred where the statutory requirement that an applicant provide a social security number as a condition of eligibility for the benefits in question was held to be not violative. It was held that requirement is facially neutral in religious terms, applies to all applicants for the benefits involved, and clearly promotes a legitimate and important public interest. Chief Justice Burger writing the opinion of the Court stated:” The general governmental interests involved here buttress this conclusion. Governments today grant a broad range of benefits; inescapably at the same time the administration of complex programs requires certain conditions and restrictions.
Although in some situations a mechanism for individual consideration will be created, a policy decision by a government that it wishes to treat all applicants alike and that it does not wish to become involved in casebycase inquiries into the genuineness of each religious objection to such condition or restrictions is entitled to substantial deference. Moreover, legitimate interests are implicated in the need to avoid any appearance of favoring religious over nonreligious applicants.
The test applied in cases like Wisconsin v. Yoder, 406 U.S. 205, 92 S.Ct. 1526, 32 L.Ed.2d 15 (1972), is not appropriate in this setting. In the enforcement of a facially neutral and uniformly applicable requirement for the administration of welfare programs reaching many millions of people, the Government is entitled to wide latitude. The Government should not be put to the strict test applied by the District Court; that standard required the Government to justify enforcement of the use of Social Security number requirement as the least restrictive means of accomplishing a compelling state interest. Absent proof of an intent to discriminate against particular religious beliefs or against religion in general, the Government meets its burden when it demonstrates that a challenged requirement for governmental benefits, neutral and uniform in its application, is a reasonable means of promoting a legitimate public interest. “
141. Repelling an argument that requirement of providing social security account number for obtaining financial aid to dependent children violates the right to privacy, following was held in Doris McElrath Vs. Joseph A. Califano, in Para 11 :”[ 11] The appellants’ principal contention on appeal is that the federal and state regulations requiring dependent children to acquire and submit social security account numbers as a condition of eligibility for AFDC benefits are statutorily invalid as being inconsistent with and not authorized by the Social Security Act. We find the arguments advanced in support of this contention to be without merit and hold that the challenged regulations constitute a legitimate condition of eligibility mandated by the Congress under the Social Security Act. Accord, Chambers v. Klein, 419 F. Supp. 569 (D.N.J. 1976), aff’d mem., 564 F.2d 89 (3d Cir. 1977); Green v. Philbrook, 576 F.2d 440 (2d Cir. 1978); Arthur v. Department of Social and Health Services, 19 Wn. App. 542, 576 P.2d 921 (1978). We therefore conclude that the district court properly dismissed the appellants’ statutory invalidity allegations for failure to state a claim upon which relief could be granted. “
142. Now, we come to third test, i.e., test of proportionality. D.Y. Chandrachud, J. in Puttaswamy (supra) has observed “Proportionality is an essential facet of the guarantee against arbitrary State action 126 because it ensures that the nature and quality of the encroachment on the right is not disproportionate to the purpose of the law”. In Modern Dental College and Research Centre and Others Vs. State of Madhya Pradesh and Others, (2016) 7 SCC 353, Dr. Sikri, J explaining the concept of proportionality laid down following in Paragraphs 64 and 65:”
64. The exercise which, therefore, to be taken is to find out as to whether the limitation of constitutional rights is for a purpose that is reasonable and necessary in a democratic society and such an exercise involves the weighing up of competitive values, and ultimately an assessment based on proportionality i.e. balancing of different interests.
65. We may unhesitatingly remark that this doctrine of Proportionality, explained hereinabove in brief, is enshrined in Article 19 itself when we read Clause (1) along with Clause (6) thereof. While defining as to what constitutes a reasonable restriction, this Court in plethora of judgments has held that the expression “reasonable restriction” seeks to strike a balance between the freedom guaranteed by any of the subclauses of Clause (1) of Article 19 and the social control permitted by any of the clauses (2) to (6). It is held that the expression “reasonable” connotes that the limitation imposed on a person in the enjoyment of the right should not be arbitrary or of an excessive nature beyond what is required in the interests of public.
Further, in order to be reasonable, the restriction must have a 127 reasonable relation to the object which the legislation seeks to achieve, and must not go in excess of that object {See P.P. Enterprises v. Union of India (1982) 2 SCC 33. At the same time, reasonableness of a restriction has to be determined in an objective manner and from the standpoint of the interests of the general public and not from the point of view of the persons upon whom the restrictions are imposed or upon abstract considerations {See Mohd. Hanif Quareshi v. State of Bihar 1959 SCR 629). In M.R.F. Ltd. v. State of Kerala (1998) 8 SCC 227, this Court held that in examining the reasonableness of a statutory provision one has to keep in mind the following factors:
(1) The directive principles of State Policy.
(2) Restrictions must not be arbitrary or of an excessive nature so as to go beyond the requirement of the interest of the general public.
(3) In order to judge the reasonableness of the restrictions, no abstract or general pattern or a fixed principle can be laid down so as to be of universal application and the same will vary from case to case as also with regard to changing conditions, values of human life, social philosophy of the Constitution, prevailing conditions and the surrounding circumstances.
(4) A just balance has to be struck between the restrictions imposed and the social control envisaged by Article 19(6).
(5) Prevailing social values as also social needs which are intended to be satisfied by the restrictions.
(6) There must be a direct and proximate nexus or reasonable connection between the restrictions imposed and the object sought to be achieved. If there is a direct nexus between the restrictions, and the object of the Act, then a strong presumption in favour the constitutionality of the Act will naturally arise. “
143. One of the submissions of the petitioner to contend that proportionality test is not fulfilled in the present case is; State did not adopt an alternative and more suitable and least intrusive method of identification, i.e., smart card or other similar devices. While examining the proportionality of a Statute, it has to be kept in mind that the Statute is neither arbitrary nor of an excessive nature beyond what is required in the interest of public.
The Statutory scheme, which has been brought in place has a reasonable relation to the object which the legislation seeks to achieve and the legislation does not exceed the object. The object of Aadhaar Act 129 as noticed above was to provide for unique identity for purposes of delivery of benefits, subsidies and services to the eligible beneficiaries and to ward of misappropriation of benefits and subsidies, ward of deprivation of eligible beneficiaries. European Court of Justice has taken a view that the proportionality merely involves an assessment that the measures taken was not more than necessary. Reference is made to the judgment of Digital Rights Ireland Ltd. Vs. Minister for Communications [2015] QBECJ, wherein it was held:
“46 In that regard, according to the settled case law of the court, the principle of proportionality requires that acts of the EU institutions be appropriate for attaining the legitimate objectives pursued by the legislation at issue and do not exceed the limits of what is appropriate and necessary in order to achieve those objectives: see Afton Chemical Ltd v Secretary of State for Transport (Case C343/ 09) [2010] ECR I7027, para 45; the Volker case [2010] ECR I11063, para 74; Nelson v Deutsche Lufthansa AG (Joined Cases C581/ 10 and C629/ 10) [2013] 1 All ER (Comm) 385, para 71; Sky Osterreich GmbH v Osterreichischer Rundfunk (Case C283/ 11) [2013] All ER (EC) 633, para 50; and Schaible v Land BadenWiirttemberg (Case C101/ 12) EU:C:2013:66I; 17 October 2013, para 29.”
144. United Kingdom Supreme Court in AB Vs. Her 130 Majesty’s Advocate, [2017] UK SC 25, held that it is not for the Court to identify the alternative measures, which may be least intrusive. In Para 37 and 39, following has been held:” 37. I am not persuaded. It is important to recall that the question of whether the Parliament could have used a less intrusive measure does not involve the court in identifying the alternative measure which is least intrusive. The court allows the legislature a margin of discretion and asks whether the limitation on the article 8 right is one which it was reasonable for the Parliament to propose: Bank Mellat v HM Treasury (No 2) [2013] UKSC 38, [2014] AC 700, para 75 per Lord Reed; 39. The balance, which this court is enjoined to address, is different. It is the question of a fair balance between the public interest and the individual’s right to respect for his or her private life under article 8. The question for the court is, in other words, whether the impact of the infringement of that right is proportionate, having regard to the likely benefit of the impugned provision.”
145. The biometric information which are obtained for Aadhaar enrolment are photographs, fingerprints and iris scan, which are least intrusion in physical autonomy of an individual. U.S. Supreme Court in John Davis Vs. State of Mississippi, 394 US 721 (1969), 131 indicated that Fingerprinting involves none of the probing into an individual’s private life and thoughts that marks an interrogation or search. The physical process by which the fingerprints are taken does not require information beyond the object and purpose. Therefore, it does not readily offend those principles of dignity and privacy, which are fundamental to each legislation of due process. One of the apprehension, which was expressed by petitioners that since as per definition of biometric information contained in Section 2(g), further, biological attributes of an individual may be specified by regulations, which may be more intrusive.
Section 2(g) use the word “such biological attributes”. Thus, applying the principles of ejusdem generis, the biological attributes can be added by the regulations, has to be akin to one those mentioned in Section 2(g), i.e. photographs, fingerprints and iris scan. In event, such biological attributes is added by regulations, it is always open to challenge by appropriate proceedings but the mere fact that by regulations any such biometric attributes 132 can be added, there is no reason to accept the contention that biological attributes, which can be added may be disproportionate to the objective of the Act. Biometric information, thus, which is to be obtained for enrolment are not disproportionate nor the provisions of Aadhaar Act requiring demographic and biometric information can be said to be not passing threefold test as laid down in Puttaswamy (supra) case.
We, thus, answer Issue Nos. 1 and 2 in following manner:Ans. 1 and 2:( i) requirement under Aadhaar Act to give one’s demographic and biometric information does not violate fundamental right of privacy. (ii) The provisions of Aadhaar Act requiring demographic and biometric information from a resident for Aadhaar Number pass threefold test as laid down in Puttaswamy (supra) case, hence cannot be said to be unconstitutional.
133 ISSUE NOS.3,4 AND 5
COLLECTION, STORAGE, RETENTION, USE, SHARING AND SURVEILLACE.
146. The Aadhaar Act provides complete architecture beginning with enrolment. The enrolment means process to collect demographic and biometric information from individuals by enroling agencies. The enroling agencies have to set up enrolment centers and have to function in accordance with the procedure specified by UIDAI. Section 8 contemplates for authentication for Aadhaar number which authentication was done by authority. When a request is made for identification by any requesting entity in respect to biometric or demographic information of Aadhaar number holder, the authority may engage one or more entities to establish and maintain central identity data repository.
Section 28 provides for the security and confidentiality of information which is to the following effect:
28.
(1) The Authority shall ensure the security of identity information and authentication records of individuals.
(2) Subject to the provisions of this Act, the Authority shall ensure confidentiality of identity information and authentication records of individuals.
(3) The Authority shall take all necessary measures to ensure that the information in the possession or control of the Authority, including information stored in the Central Identities Data Repository, is secured and protected against access, use or disclosure not permitted under this Act or regulations made thereunder, and against accidental or intentional destruction, loss or damage.
(4) Without prejudice to subsections (1) and (2), the Authority shall-
(a) adopt and implement appropriate technical and organisational security measures;
(b) ensure that the agencies, consultants, advisors or other persons appointed or engaged for performing any function of the Authority under this Act, have in place appropriate technical and organisational security measures for the information; and
(c) ensure that the agreements or arrangements entered into with such agencies, consultants, advisors or other persons, impose obligations equivalent to those imposed on the Authority under this Act, and require such agencies, consultants, advisors and other persons to act only on instructions from the Authority.
(5) Notwithstanding anything contained in any other law for the time being in force, and save as otherwise provided in this Act, the Authority or any of its officers or other employees or any agency that maintains the Central Identities Data Repository shall not, whether during his service or thereafter, reveal any information stored in the Central Identities Data Repository or authentication record to anyone: Provided that an Aadhaar number holder may request the Authority to provide access to his identity information excluding his core biometric information in such manner as may be specified by regulations.
147. The Act contains specific provision providing that no core biometric information collected under the Act is shared to anyone for any reason whatsoever or use for any purpose other than generation of Aadhaar number or authentication under this Act. The statute creates injunction for requesting entity to use identity information data for any purpose other than that specified to the individual at the time for submitting any identification. Section 29 provides for not sharing information collected or created under this Act, which is to the following effect:
“29. (1) No core biometric information, collected or created under this Act, shall be-
(a) shared with anyone for any reason whatsoever; or
(b) used for any purpose other than generation of Aadhaar numbers and authentication under this Act.
(2) The identity information, other than core biometric information, collected or created under this Act may be shared only in accordance with the provisions of this Act and in such manner as may be specified by regulations.
(3) No identity information available with a requesting entity shall be-
(a) used for any purpose, other than that specified to the individual at the time of submitting any identity information for authentication; or Security and confidentiality of information.
(b) disclosed further, except with the prior consent of the individual to whom such information relates.
(4) No Aadhaar number or core biometric information collected or created under this Act in respect of an Aadhaar number holder shall be published, displayed or posted publicly, except for the purposes as may be specified by regulations.”
148. Section 30 itself contemplates that biometric information are sensitive personal data or information. There are strict conditions envisaged in Section 33 for disclosure of information. The 137 disclosure of information is contemplated only on two contingencies. Firstly, when an order is passed by a Court not inferior to that of District Judge and secondly when the disclosure is made in the interest of national security in pursuance of a direction of the officer not below the rank of Joint Secretary to the Government of India.
149. Chapter VII of the Act deals with the offences and penalties for impersonation at the time of enrolment penalty for disclosing identity information is provided under Sections 34 to 37. Section 38 provides for penalty who accesses or secures access to the Central Identities Data Repository. Section 39 provides for penalty who uses or tampers with the data in the Central Identities Data Repository. Section 40 provides for penalty whoever, being a requesting entity, uses the identity information of an individual in contravention of subsection (3) of section 8. Section 41 deals with penalty for noncompliance by an enrolling agency or requesting 138 entity. Section 42 deals with general penalty. Section 42 is as follows:
“42. Whoever commits an offence under this Act or any rules or regulations made thereunder for which no specific penalty is provided elsewhere than this section, shall be punishable with imprisonment for a term which may extend to one year or with a fine which may extend to twentyfive thousand rupees or, in the case of a company, with a fine which may extend to one lakh rupees, or with both.”
150. Regulations have been framed under the Act, namely,
(1) The Aadhaar (Enrolment and Update) Regulations, 2016,
(2) The Aadhaar (Authentication) Regulations, 2016,
(3) The Aadhaar (Data Security) Regulations, 2016 and
(4) The Aadhaar (Sharing of Information) Regulations, 2016.
151. We have already noticed the detailed submissions of learned counsel for UIDAI. Following are the measures by which Security Data of privacy is ensured. The security and data privacy is ensured in the following manner:
i. The data sent to ABIS is completely anonymised. The ABIS systems do not have access to resident’s demographic information as they are only sent biometric information of a resident with a reference number and asked to deduplicate. The deduplication result with the reference number is mapped back to the correct enrolment number by the Authorities own enrolment server.
ii. The ABIS providers only provide their software and services. The data is stored in UIDAI storage and it never leaves the secure premises.
iii. The ABIS providers do not store the biometric images (source). They only store template for the purpose of deduplication (with reference number)
iv. The encrypted enrolment packet sent by the enrolment client software to the CIDRis decrypted by the enrolment server but the decrypted packet is never stored.
v. The original biometric images of fingerprints, iris and face are archived and stored offline. Hence, they cannot be accessed through an online network. vi. The biometric system provides high accuracy of over 99.86%. The mixed biometric have been adopted only to enhance the accuracy and to reduce the errors which may arise on account of some residents either not having biometrics or not having some particular biometric. 152. After the enrolment and allotting an Aadhaar number to individual the main function of the authority is authentication of an Aadhaar number 140 holder as and when request is made by the requesting agency. The authentication facility provided by the authority is under Section 3 of the Authentication Regulations, 2016 which is to the following effect:
“3. Types of Authentication.- There shall be two types of authentication facilities provided by the Authority, namely- (i) Yes/No authentication facility, which may be carried out using any of the modes specified in regulation 4(2); and (ii) eKYC authentication facility, which may be carried out only using OTP and/ or biometric authentication modes as specified in regulation 4(2).”
153. Various modes of authentication are provided in Regulation 4 of Authentication Regulations 2016, which are: Demographic authentification; One time pinbased authentication; Biometricbased authentification and Multifactor authentification. A requesting entity may choose suitable mode of authentication for particular function or business function as per its requirement.
154. Regulation 7 provides for capturing biometric information by requesting entity which is to the following effect:
“7. Capturing of biometric information by requesting entity.-
(1) A requesting entity shall capture the biometric information of the Aadhaar number holder using certified biometric devices as per the processes and specifications laid down by the Authority.
(2) A requesting entity shall necessarily encrypt and secure the biometric data at the time of capture as per the specifications laid down by the Authority.
(3) For optimum results in capturing of biometric information, a requesting entity shall adopt the processes as may be specified by the Authority from time to time for this purpose.”
155. Regulation 9 deals with process of sending authentification requests. SubRegulation (1) of Regulation 9 contends the safe method of transmission of the authentication requests. 156. The Aadhaar (Data Security) Regulations, 2016 contain detail provisions to ensuring data security. Regulation 3 deals with measures for ensuring information security. Regulation 5 provides security 142 obligations of the agencies, consultants, advisors and other service providers engaged by the Authority for discharging any function relating to its processes.
157. The Aadhaar (Sharing of Information) Regulations, 2016 also contain provisions providing for restrictions on sharing identity information. SubRegulation (1) of Regulation 3 provides that core biometric information collected by the Authority under the Act shall not be shared with anyone for any reason whatsoever.
158. Sharing of Information Regulations, 2016 also contain various other restrictions. Regulation 6 contains restrictions on sharing, circulating or publishing of Aadhaar number which is to the following effect:
“6. Restrictions on sharing, circulating or publishing of Aadhaar number. –
(1) The Aadhaar number of an individual shall not be published, displayed or posted publicly by any person or entity or agency.
(2) Any individual, entity or agency, which is in possession of Aadhaar number(s) of Aadhaar number holders, shall ensure security and confidentiality of the Aadhaar numbers 143 and of any record or database containing the Aadhaar numbers.
(3) Without prejudice to subregulations (1) and (2), no entity, including a requesting entity, which is in possession of the Aadhaar number of an Aadhaar number holder, shall make public any database or record containing the Aadhaar numbers of individuals, unless the Aadhaar numbers have been redacted or blacked out through appropriate means, both in print and electronic form.
(4) No entity, including a requesting entity, shall require an individual to transmit his Aadhaar number over the Internet unless such transmission is secure and the Aadhaar number is transmitted in encrypted form except where transmission is required for correction of errors or redressal of grievances.
(5) No entity, including a requesting entity, shall retain Aadhaar numbers or any document or database containing Aadhaar numbers for longer than is necessary for the purpose specified to the Aadhaar number holder at the time of obtaining consent.”
159. The scheme of the Aadhaar Act indicates that all parts of the entire process beginning from enrolment of a resident for allocation of Aadhaar number are statutory regulated.
160. The Authentication Regulations, 2016 also limit the period for retention of logs by requesting entity. 144 Regulation 18(1) which is relevant in this context is as follows:
“18. Maintenance of logs by requesting entity.
(1) A requesting entity shall maintain logs of the authentication transactions processed by it, containing the following transaction details, namely:-
(a) the Aadhaar number against which authentication is sought;
(b) specified parameters of authentication request submitted;
(c) specified parameters received as authentication response; (d) the record of disclosure of information to the Aadhaar number holder at the time of authentication; and (e) record of consent of the Aadhaar number holder for authentication, but shall not, in any event, retain the PID information.”
161. The residents’ information in CIDR are also permitted to be updated as per provisions of the Aadhaar (Enrolment and Update) Regulations, 2016. An over view of the entire scheme of functions under the Aadhaar Act and Regulations made thereunder indicate that after enrolment of resident, his informations 145 including biometric information are retained in CIDR though in encrypted form. The major function of the authority under Aadhaar Act is authentication of identity of Aadhaar number holder as and when requests are made by requesting agency, retention of authentication data of requesting agencies are retained for limited period as noted above. There are ample safeguards for security and data privacy in the mechanism which is at place as on date as noted above.
162. Shri Shyam Divan, learned senior counsel appearing for the petitioners has passionately submitted that entire process of authentication as is clear from actual working of the Aadhaar programme reveals that Aadhaar Act enables the State to put the entire population of the country in an electronic leash and they are tracked 24 hours and 7 days. He submits that putting the entire population under surveillance is nothing but converting the State into a totalitarian State. Elaborating his submission, Shri Divan submits that process of authentication creates authentication records of (1) time of 146 authentication,
(2) identity of the requesting entity. Both requesting entity and UIDAI have authentication transactions data which record the technical details of transactions. The devices which are used by the requesting entities have IP address which enables knowledge about geographical information of Aadhaar number holder with knowledge of his location, details of transaction, every person can be tracked and by aggregating the relevant data the entire population is put on constant surveillance. Aadhaar programme endeavours all time mass surveillance by the State which is undemocratic and violates the fundamental rights of individual.
163. The meta data regarding authentication transactions which are stored with the authority are potent enough to note each and every transaction of resident and to track his activities is nothing but surveillance. Regulation 26 of Authentication Regulations, 2016 provides storage of meta data related to the transaction. Regulation 26 which is relevant is as follows:
“26. Storage and Maintenance of Authentication Transaction Data. –
(1) The Authority shall store and maintain authentication transaction data, which shall contain the following information:-
(a) authentication request data received including PID block;
(b) authentication response data sent;
(c) meta data related to the transaction;
(d) any authentication server side configurations as necessary Provided that the Authority shall not, in any case, store the purpose of authentication.”
164. We may first notice as to what is meta data which is referred to in Regulation 26 above. The UIDAI receives the requests for authentication of ANH. The request for authentication received by requesting agency does not contain any information as to the purpose of authentication neither requesting agency nor UIDAI has any record pertaining to purpose for which authentication has been sought by Aadhaar number holder. The meta data referred to in Regulation 26(c) is only limited technical meta data.
165. Shri Kapil Sibal had submitted that CIDR holds the entire Aadhaar database retained by CIDR. It has become a soft target for internal/external/ indigenous /foreign attacks and single point of failure. Shri Sibal has referred to a RBI report which states: “Thanks to Aadhaar, for the first time in the history of India, there is now a readily available single target for cyber criminals as well as India’s external enemies. In a few years, attacking UIDAI data can potentially cripple Indian businesses and administration in ways that were inconceivable a few years ago. The loss to the economy and citizens in case of such an attack is bound to be incalculable.”
166. He has further submitted that a digital world is far more susceptible to manipulation than the physical world. No legislation can or should allow an individual’s personal data to be put at risk, in the absence of a technologically assured and safe environment. Such level of assurance is impossible to obtain in the digital space. Biometric, core biometric and demographic information of an individual, once part of the digital world is irretrievable: a genie out of the bottle that cannot be put back. The digital world is a vehicle to benefit the information economy. A move from an information economy to creating an architecture for an information polity has far reaching consequences impacting the most personal rights, protected by the right to privacy. The technology acquired by the UIDAI has also been criticised by the Opaque Foreign Technologies.
167. The above submissions have been strongly refuted by learned Attorney General and learned counsel appearing for the UIDAI. It is submitted by the respondents that the above submissions regarding mass surveillance have been made on misconception regarding actual operation of the entire process. 168. The meta data which is aggregation of authentication transactions does not contain any detail of actual transaction done by ANH. In the event, in a period of 30 days, 30 requesting agencies, may be one or different, have requested for authentication the UIDAI has only the recipient of demographic/biometric of ANH authentication without any information regarding purposes of authentication.
150 Thus, even if authentication details are aggregated, there is no information with the UIDAI regarding purpose of authentication nor authentication leaves for any trail so as to keep any track by UiDAI to know the nature of transaction or to keep any kind of surveillance as alleged. Section 32 subsection (3) of the Aadhaar Act specifically prohibits the authority from collecting or maintaining either directly or indirectly any information for the purpose of authentication.
169. Proviso to Regulation 26 is also to the same effect i.e. provided that the authority shall not, in any case, store the purpose of authentication.
170. Elaborating on CIDR, Shri Dwivedi submits that CIDR is a centralised database which contains all Aadhaar numbers issued with corresponding demographic and biometric information. It is a “Protected System” notified under Section 70 of Information Technology Act, 2000. The storage involves end to end encryption, logical partitioning, fire walling and anonymisation 151 of decrypted biometric data. The encryption system follows a private key/public model and the private key is available only with UIDAI at the processing location. Hence even if data packets are lost or stolen the biometric information regarding the same cannot be accessed.
At the CIDR there is multilayer technological security to afford protection from hacking, and there is also deployment of armed forces to prevent unauthorised physical access into the CIDR Area. Additionally entry is electronically controlled. There are CIDR at two location already and some other locations are likely to be set up to ensure that data is not lost even in the remote eventuality of a disaster. The CIDR is centrally managed. The templates of finger prints and iris data are generated in ISO format and the same along with demographic data and photo are stored securely in the authentication server database. This database is used for authentication in the manner provided in Aadhaar (Authentication) Regulation 2016.
171. In view of above, the apprehension raised by Shri Kapil Sibal that CIDR is a soft target is misplaced.
172. To support his submission, Shri Shyam Divan, learned counsel for the petitioner has placed reliance on judgment of the United States Supreme Court in United States vs. Antoine Jones, 132 S.Ct. 945 (2012).
173. A large number of foreign judgments touching various aspects of accumulation of data, retention of data, surveillance, has been cited by both the parties to support their respective stand. It is necessary to have an over view of the opinion expressed by various Courts in other countries of the world. The present age being the age of technology and information, the issues pertaining to storage and retention of personal data in different contexts have come up before several Courts of different countries which also need to be noted.
174. The petitioners have relied on European Court, Human Rights in S. and Marper vs. The United Kingdom, 153 2008 (48)EHRR 50. The applicants, S and Marper had submitted two applications against the United Kingdom, Great Britain and Northern Ireland under Article 34 of the Convention for the Protection of Human Rights and Fundamental Freedoms (the Convention). The applicants complained that the authorities had continued to retain their fingerprints and cellular samples and DNA profiles after the criminal proceedings against them had ended with an acquittal or had been discontinued. The applicants had applied for judicial review of the police decisions not to destroy the fingerprints and samples which application was rejected. The Court of appeal upheld the decision of the Administrative Court. The House of Lords had also dismissed the appeal on 22nd July, 2004. The House of Lords had taken the view that the mere retention of fingerprints and DNA samples did not constitute an interference with the right to respect for private life but stated that, if he were wrong in that view, he regarded any interference as very modest indeed.
175. BARONESS HALE disagreed with the majority considering that the retention of both fingerprint and DNA data constituted an interference by the State in a person’s right to respect for his private life and thus required justification under the Convention. The application of the applicant was taken by European Court of Human Rights (Strasbourg Court). The Strasbourg Court noticed that majority of the Council of Europe member States allow the compulsory taking of fingerprints and cellular samples in the context of criminal proceedings. The United Kingdom is the only member State expressly to permit the systematic and indefinite retention of DNA profiles and cellur samples of persons who have been acquitted or in respect of whom criminal proceedings have been discontinued.
176. Strasbourg Court held that the mere storing of data relating to the private life of an individual amounts to an interference within the meaning of Article 8. It was further held that in determining whether the personal information retained by the 155 authorities involves any of the privatelife aspects mentioned above, the Court will have due regard to the specific context in which the information at issue has been recorded and retained. In paragraph 67 following has been laid down: “67….However, in determining whether the personal information retained by the authorities involves any of the privatelife aspects mentioned above, the Court will have due regard to the specific context in which the information at issue has been recorded and retained, the nature of the records, the way in which these records are used and processed and the results that may be obtained (see, mutatis mutandis, Friedl, cited above, 4951, and Peck v. The United Kingdom, cited above, 59).”
177. Following was laid down in paragraph 73 & 77: “73. Given the nature and the amount of personal information contained in cellular samples, their retention per se must be regarded as interfering with the right to respect for the private lives of the individuals concerned. That only a limited part of this information is actually extracted or used by the authorities through DNA profiling and that no immediate detriment is caused in a particular case does not change this conclusion (see Aman cited above, 69). 77. In view of the foregoing, the Court concludes that the retention of both cellular samples and DNA profiles discloses an 156 interference with the applicants’ right to respect for their private lives, within the meaning of Article 8(1) of the Convention.”
178. The Court also considered the issue of retention of fingerprints, and held that retention of fingerprints may also give rise to important private life concerns. The Court also held that the domestic law must afford appropriate safeguards to prevent any such use of personal data as may be inconsistent with the guarantees of Article 8. Following was held in paragraph 103: “103. The protection of personal data is of fundamental importance to a person’s enjoyment of his or her right to respect for private and family life, as guaranteed by Article 8 of the Convention. The domestic law must afford appropriate safeguards to prevent any such use of personal data as may be inconsistent with the guarantees of this Article (see mutatis mutandis, Z., cited above, 95).
The need for such safeguards is all the greater where the protection of personal data undergoing automatic processing is concerned, not least when such data are used for police purposes. The domestic law should notably ensure that such data are relevant and not excessive in relation to the purposes for which they are stored; and preserved in a form which permits identification of the data subjects for no 157 longer than is required for the purpose for which those data are stored.”
179. United Kingdom Supreme Court had occasion to consider the issue of retention of data in Regina (Catt) v. Association of Chief Police Officers of England, Wales and Northern Ireland and another,(2015) 2 WLR 664 – (2015) UKSC 9. The UK Supreme Court in the above case also noticed the judgment of Strasbourg in S. and Marper v. The United Kingdom. The appeal before UK Supreme Court was concerned with the systematic collection retention by police authorities of electronic data about individuals and whether it is contrary to Article 8 of the European Convention.
The appellant before the Court had accepted that it was lawful for the police to make a record of the events in question as they occurred, but contends that the police interfered with their rights under Article 8 of the Convention by thereafter retaining the information on a searchable database. After noticing the jurisprudence of the European Court of Human Rights Lord Sumption stated following in paragraph 33: 158 “33. Although the jurisprudence of the European Court of Human Rights is exacting in treating the systematic storage of personal data as engaging article 8 and requiring justification, it has consistently recognised that (subject always to proportionality) public safety and the prevention and detection of crime will justify it provided that sufficient safeguards exist to ensure that personal information is not retained for longer than is required for the purpose of maintaining public order and preventing or detecting crime, and that disclosure to third parties is properly restricted: see Bouchacourt v France, given 17 December 2009, paras 6869, and Brunet v. France (Application No.21010/10) (unreported) given 18 September 2014, para 36. In my opinion, both of these requirements are satisfied in this case. Like any complex system dependent on administrative supervision, the present system is not proof against mistakes.
At least in hindsight, it is implicit in the 2012 report of HMIC and the scale on which the database was weeded out over the next two years that the police may have been retaining more records than the Code of Practice and the MOPI guidelines really required. But the judicial and administrative procedures for addressing this are effective, as the facts disclosed on this appeal suggest.”
180. The preponderance of authorities on the subject of retention of data is that retention of personal data effecting personal life of an individual may interfere in his right of privacy and the State can justify its retention subject to proportionality and 159 subject to there being sufficient safeguards to personal information is not retained for longer than it required.
181. Reverting back to the Aadhaar Act, it is clear that requesting entity as well as authority are required to retain authentication data for a particular period and thereafter it will be archived for five years and thereafter authentication data transaction shall be deleted except such data which is required by the Court in connection with any pending dispute. We had already noticed that data which is retained by the entity and authority for certain period is minimal information pertaining to identity authentication only no other personal data is retained. Thus, provisions of Aadhaar Act and Regulations made thereunder fulfill three fold test as laid down in Puttaswamy case (supra), hence, we conclude that storage and retention of data does not violate fundamental right of privacy.
182. Now, we come to issue of surveillance, which has been very strongly raised by petitioners. Shri Shyam Divan, learned counsel for the petitioners has relied on judgment of U.S. Supreme Court in United States Vs. Antoine Jones, 132 S.Ct. 945 (2012). Antoine Jones, owner and operator of a nightclub was under suspicion of trafficking in narcotics. A warrant was issued authorising installation of an electronic tracking device on the jeep registered in the name of John’s wife. Agents installed a GPS tracking device in the jeep when it was parked in a public parking. On the basis of data obtained from the device, the Government charged Jones for several offences. In trial, Jones found a locational data obtained form the GPS device. A verdict of guilt was returned, which on appeal was reversed by United States, Appeal for District Columbia.
183. Matter was taken to the U.S. Supreme Court. Fourth Amendment provides “the right of the people to be secured in their persons, houses, papers, and effects, against unreasonable searches and seizures, 161 shall not be violated.” Justice Scalia, delivering the opinion of the Court affirmed the judgment of Court of Appeal. Justice Sotomayor concurring wrote:” I join the Court’s opinion because I agree that a search within the meaning of the Fourth Amendment occurs, at a minimum, “[w]here, as here, the Government obtains information by physically intruding on a constitutionally protected area.” Ante, at 950, n. 3. In this case, the Government installed a Global Positioning System (GPS) tracking device on respondent Antoine Jones’ Jeep without a valid warrant and without Jones’ consent, then used that device to monitor the Jeep’s movements over the course of four weeks. The Government usurped Jones’ property for the purpose of conducting surveillance on him, thereby invading privacy interests long afforded, and undoubtedly entitled to, Fourth Amendment protection. See, e.g., Silverman v. United States, 365 U. S. 505, 511512 S1 S.Ct. 679, 5 L.Ed.2d 734 (1961). “
184. The above case was a case where tracking device, i.e., GPS was installed in the vehicle with purpose and motive of surveillance and obtaining data to be used against Jones. Present is not a case where it can be said that Aadhaar infrastructure is designed in a manner as to put a surveillance on Aadhaar number holder (ANH).
185. Another judgment which is relied by Shri Shyam Divan is judgment of European Court of Human Rights in Strasbourg Court in Roman Zakharov Vs. Russia decided on 04.12.2015. In the above case, the applicant alleged that the system of secret interception of mobile telephone communications in Russia violated his right to respect for his private life and correspondence and that he did not have any effective remedy in that respect. In Para 148 of the judgment, the case of the applicant was noted in the following words:”
148. The applicant complained that the system of covert interception of mobile telephone communications in Russia did not comply with the requirements of Article 8 of the Convention, which reads as follows:”
1. Everyone has the right to respect for his private and family life, his home and his correspondence.
2. There shall be no interference by a public authority with the exercise of this right except such as is in accordance with the law and is necessary in a democratic society in the interests of national security, public safety or the economic wellbeing of the country, for the prevention of disorder or crime, for the protection of health or morals, 163 or for the protection of the rights and freedoms of others.”
186. The Court came to the following conclusion:”
175. The Court notes that the contested legislation institutes a system of secret surveillance under which any person using mobile telephone services of Russia providers can have his or her mobile telephone communications intercepted, without ever being notified of the surveillance. To that extent, the legislation in question directly affects all users of these mobile telephone services.”
187. The Strasbourg Court held that there had been violation of Article 8 of the Convention. The above case also does not help the petitioners in reference to Aadhaar structure. Above case was a clear case of surveillance by interception of mobile telecommunication.
188. Another judgment relied by Shri Shyam Divan is Digital Rights Ireland Ltd. Vs. Minister for Communications, Marine and Natural Resources decided on 08.04.2014. Para 1 of the judgment notice:” These requests for a preliminary ruling concern the validity of Directive 2006/24/EC of the European Parliament and of the Council of 15 March 2006 on the retention of data 164 generated or processed in connection with the provision of publicly available electronic communications services or of public communications networks and amending Directive 2002/58/EC(OJ 2006 L 105, p. 54).”
189. Directive 2006/24 laid down the obligation on the providers of publicly available electronic communications services or of public communications networks to retain certain data which are generated or processed by them. Noticing various articles of the Directives, the Court in Paragraph 27 noted:” 27. Those data, taken as a whole, may allow very precise conclusions to be drawn concerning the private lives of the persons whose data has been retained, such as the habits of everyday life, permanent or temporary places of residence, daily or other movements, the activities carried out, the social relationships of those persons and the social environments frequented by them.”
190. The directives were held to be violating the principles of proportionality. The above case was also a case of retaining data pertaining to communications by service providers. The retention of communication data is a clear case of intrusion in privacy. The above is also a case which in no manner 165 help the petitioners when contrasted with the Aadhaar architecture.
191. At this juncture, we may also notice one submission raised by the petitioners that Aadhaar Act could have devised a less intrusive measure/means. It was suggested that for identity purpose, the Government could have devised issuance of a smart card, which may have contained a biometric information and retain it in the card itself, which would not have begged the question of sharing or transfer of the data. We have to examine the Aadhaar Act as it exists. It is not the Court’s arena to enter into the issue as to debate on any alternative mechanism, which according to the petitioners would have been better. Framing a legislative policy and providing a mechanism for implementing the legislative policy is the legislative domain in which Court seldom trench.
192. We may refer to a judgment of U.K. Supreme Court AB Vs. Her Majesty’s Advocate, [2017] UKSC 25, where U.K. Supreme Court has not approved the arguments 166 based on less intrusive means. Court held that whether the Parliament would have used a less intrusive means does not involve the Court in identifying an alternative measure, which is least intrusive. In Para 37, following has been laid down:”
37. I am not persuaded. It is important to recall that the question of whether the Parliament could have used a less intrusive measure does not involve the court in identifying the alternative measure which is least intrusive. The court allows the legislature a margin of discretion and asks whether the limitation on the article 8 right is one which it was reasonable for the Parliament to propose: Bank Mellat v HM Treasury (No 2) [2013] UKSC 38, [2014] AC 700, para 75 per Lord Reed; Animal Defenders International v United Kingdom (2013) 57 EHRR 21, para 110. Had the 2009 Act provided that the reasonable belief defence would not be available if on an earlier occasion the accused had been charged with an offence which itself objectively entailed a warning of the illegality of consensual sexual activity with older children, the fact that there were other options, which were less intrusive, to restrict the availability of that defence would not cause an infringement of the individual’s article 8 right. The problem for the Lord Advocate in this appeal is where to find such a warning. “
193. We may profitably note the judgment of Privy Council arising from a decision of Supreme Court of 167 Mauritius – Madhewoo Vs. State of Mauritius. The case relates to a national identity card, which was brought in effect by an Act namely, the National Identity Card Act, 1985 providing for adult citizens of Mauritius to carry identity cards. The Act was amended in 2013 by which Government introduced a new smart identity card, which incorporates on a chip on the citizen’s fingerprints and other biometric information relating to his/her characteristics.
A citizen of the Republic of Mauritius did not apply for National Identity Card and he challenged the validity of the 2013 Act. The Supreme Court of Mauritius held that the provisions of 1985 Act, which enforce the compulsory taking and recording of fingerprints of a citizen disclosed an interference with the appellant’s rights guaranteed under Section 9(1) of the Constitution. The Section 9(1) provided “except with his own consent, no person shall be subject to the search of his person or his private or the entry by others in his premises.” Supreme Court had rejected the challenge to the other provisions of the 168 Constitution. Matter was taken to the Privy Council. The challenge made before the Privy Council was noticed in Para 7 of the judgment, which is to the following effect:”
7. In this appeal the appellant challenges the constitutionality of (a) the obligation to provide fingerprints and other biometric information under section 4, (b) the storage of that material on the identity card under section 5, (c) the compulsory production of an identity card to a policeman under section 7(1A) in response to a request under section 7(1)(b), and (d) the gravity of the potential penalties under section 9(3) for noncompliance. He claims, first, that the implementation of the new biometric identity card is in breach of sections 1, 2, 3, 4, 5, 7, 9, 15, 16 and 45 of the Constitution coupled with article 22 of the Civil Code (which provides that everyone has the right to respect for his private life and empowers courts with competent jurisdiction to prevent or end a violation of privacy) and, secondly, that the collection and permanent storage of personal biometric data, including fingerprints, on the identity card are in breach of those sections of the Constitution and that article of the Civil Code. “
194. The Privy Council agreed with the decision of the Supreme Court that compulsory taking of fingerprints and the extraction of minutiae involved an interference with the appellant’s Section 9 rights 169 which required to be justified under Section 9(2). The challenge raised before the Privy Council has been noticed in Para 25, which challenges were repelled. Paras 25 and 26 are as follows:”
25. The appellant challenges the Supreme Court’s evaluation because, he submits, the creation of a reliable identity card system does not justify the interference with his fundamental rights. He submits that the obligation to provide his fingerprints interferes with his right to be presumed innocent and also that an innocuous failure to comply with section 4(2)(c) could give rise to draconian penalties under section 9(3) of the Act (para 6 above). He also points out that in India a proposal for a biometric identity card was held to be unconstitutional, and, in the United Kingdom, libertarian political opposition resulted in the repeal of legislation to introduce biometric identity cards. The interference, he submits, is disproportionate.
26. In the Board’s view, these challenges do not undermine the Supreme Court’s assessment. First, the requirement to provide fingerprints for an identity card does not give rise to any inference of criminality as it is a requirement imposed on all adult citizens. It is true that, if circumstances arose in which a police officer was empowered to require the appellant to produce his identity card and the government had issued card readers, the authorities would have access to his fingerprint minutiae which they could use for the purposes of identification in a criminal investigation.
But that does not alter the presumption of innocence. 170 Secondly, the penalties in section 9(3) are maxima for offences, including those in section 9(1), which cover serious offences such as forgery and fraudulent behaviour in relation to identity cards. The subsection does not mandate the imposition of the maximum sentence for any behaviour. Thirdly, while judicial rulings on international instruments and the constitutions of other countries can often provide assistance to a court in interpreting the provisions protecting fundamental rights and freedoms in its own constitution, the degree of such assistance will depend on the extent to which the documents are similarly worded. “
195. As noticed above, learned counsel for the petitioners has raised various issues pertaining to security and safety of data and CIDR. Apprehensions raised by the petitioners does not furnish any ground to struck down the enactment or a legislative policy. This Court in G. Sundarrajan Vs. Union of India and Others. (2013) 6 SCC 620, had occasion to consider India’s National Policy and challenge to a Nuclear Project, which was launched by the Government upholding the legislative policy, the Court laid down following in Paras 15 and 15.1:”
15. India’s National Policy has been clearly and unequivocally expressed by the legislature in the Atomic Energy Act. 171 National and International policy of the country is to develop control and use of atomic energy for the welfare of the people and for other peaceful purposes. NPP has been set up at Kudankulam as part of the national policy which is discernible from the Preamble of the Act and the provisions contained therein. It is not for Courts to determine whether a particular policy or a particular decision taken in fulfillment of a policy, is fair. Reason is obvious, it is not the province of a court to scan the wisdom or reasonableness of the policy behind the Statute.
15.1. Lord MacNaughten in Vacher & Sons Ltd. v. London Society of Compositors (1913) AC 107 HL has stated: “……Some people may think the policy of the Act unwise and even dangerous to the community……But a Judicial tribunal has nothing to do with the policy of any Act which it may be called upon to interpret. That may be a matter for private judgment. The duty of the Court, and its only duty, is to expound the language of the Act in accordance with the settled rules of construction.”
196. This Court also held that a project cannot be stopped merely on the ground of apprehension. In the present case, also lot of apprehensions of possibilities of insecurity of data has been raised. In India, there is no specific data protection laws 172 like law in place in United Kingdom. In Privacy judgment – Puttaswamy (supra), this Court has noticed that Shri Krishna Commission is already examining the issue regarding data protection and as has been stated by learned Attorney General before us, after the report is received, the Government will proceed with taking steps for bringing a specific law on data protection. We need not say anything more on the above subject. After we have reserved the judgment, Srikrishna Commission has submitted its report containing a draft Personal Data Protection Bill, 2018 in July 2018.
The report having been submitted, we hope that law pertaining to Personal Data Protection shall be in place very soon taking care of several apprehensions expressed by petitioners.
197. The Aadhaar architecture is to be examined in light of the statutory regime as in place. We have noticed the regulations framed under Aadhaar Act, which clearly indicate that regulations brings in place statutory provisions for data protection, restriction on data sharing and other aspects of the matter. Several provisions of penalty on data breach and violation of the provisions of the Act and regulations have been provided.
198. We have no reason to doubt that the project will be implemented in accordance with the Act and the Regulations and there is no reason to imagine that there will be statutory breaches, which may affect the data security, data protection etc. In view of foregoing discussions, we are of the considered opinion that Statutory regime as delineated by the Aadhaar Act and the Regulations fulfills the threefold test as laid down in Puttaswamy (supra) and the law, i.e. Aadhaar Act gives ample justification for legitimate aim of the Government and the law being proportional to the object envisaged. The petitioners during their submissions have also attacked various provisions of Enrolment and Update Regulations, Authentication Regulations, Data Security Regulations and Sharing of Information Regulations. All the above regulations have been framed in exercise of power under Section 54 of the Act on the matters covered by 174 the Act. We having held that by collection of data, its retention, storage, use and sharing, no Privacy Right is breached, we are of the view that related regulations also pass the muster of threefold tests as laid down in K.Puttaswamy case.
The provisions of Act in the above regard having passed the muster of threefold tests, the related regulations also cannot be held to breach Right of Privacy. Thus, challenge to regulations relating to collection, storage, use, retention and sharing fails and it is held that they do not violate Constitutional Rights of Privacy. In result, we answer the Issue Nos. 3, 4 and 5 in following manner:
Ans. 3, 4, 5:
(i) Collection of data, its storage and use does not violate fundamental Right of Privacy.
(ii) Aadhaar Act does not create an architecture for pervasive surveillance.
(iii) Aadhaar Act and Regulations provides protection and safety of the data received 175 from individuals.
Issue Nos. 6 and 7
Whether Section 7 of Aadhaar Act is unconstitutional? Whether right to food shelter etc. envisaged under Article 21 shall take precedence on the right to privacy of the beneficiaries?
199. Shri Pandit Jawahar Lal Nehru while concluding debate on “Aims and Objects Resolution” on 22.01.1947 in the Constituent Assembly of India stated: “The first task of this Assembly is to free India through a new constitution to feed the starving people and cloth the naked masses and to give every Indian fullest opportunity to develop himself according to his capacity. This is certainly a great task.”
200. After attaining the freedom the country proceeded to realise the dream and vision which founding fathers of our democratic system envisaged. The Constitution of India apart from enumerating various Fundamental Rights including right to life has provided for Directive Principles of State Policy under Chapter IV of the Constitution which was to find objectives in governess of the country. Article 38 provided that State shall strive to promote the welfare of the people by securing and protecting as effectively as it may a social order in which justice, social, economic and political, shall inform all the institutions of the national life. It further provided that the State shall, in particular, strive to minimise the inequalities in income, and endeavour to eliminate inequalities in status, facilities and opportunities, not only amongst individuals but also amongst groups of people residing in different areas or engaged in different vocations.
201. After enforcement of the Constitution almost all the Governments worked towards the object of elimination of poverty and to empower marginal/poor section of the society. The endeavour of the Government was always to frame policies keeping in view the “little Indian” who is in the centre of all policies and governance.
202. Section 7 of the Aadhaar Act is the most important provision of the Aadhaar Act around which 177 entire architecture of Aadhaar Act has been built. Section 7 is to the following effect: “7. The Central Government or, as the case may be, the State Government may, for the purpose of establishing identity of an individual as a condition for receipt of a subsidy, benefit or service for which the expenditure is incurred from, or the receipt therefrom forms part of, the Consolidated Fund of India, require that such individual undergo authentication, or furnish proof of possession of Aadhaar number or in the case of an individual to whom no Aadhaar number has been assigned, such individual makes an application for enrolment:
Provided that if an Aadhaar number is not assigned to an individual, the individual shall be offered alternate and viable means of identification for delivery of the subsidy, benefit or service.”
203. The objects and reasons of the Act as noticed above as well as the Preamble of the Act focus on targeted delivery of financial and other subsidies, benefits and services which are envisaged in Section 7. The petitioners challenge the constitutionality of Section 7. They submit that Section 7 seeks to render the constitutional and statutory obligations of the State to provide benefits, subsidies and services, conditional upon an individual parting with his or her biometric and demographic information.
An individual’s rights and entitlements cannot be made dependent upon an invasion of his or her bodily integrity and his or her private information which the individual may not be willing to share with the State. The bargain underlying Section 7 is an unconscionable, unconstitutional bargain. An individual has constitutional right to receive benefits, subsidies and services which is fundamental right and it is State’s obligation to provide for fulfillment of that fundamental right. He submitted that there is no rationale in enactment of Section 7 neither there was any legitimate state interest nor the provision is proportionate. The petitioners submit that provision of requiring every person to undergo authentication to avail benefits/services/ entitlements, falls foul of Article 14.
Since, firstly such mandatory authentication has caused, and continues to cause, exclusion of the most marginalised section of society; and secondly this exclusion is not simply a question of poor implementation that can be administratively resolved, but stems from the very design of the Act. Learned counsel for the petitioners have referred to and relied on several materials in support of their submissions that working of Section 7 has caused exclusion. Since a large number of persons who are entitled to receive benefits, subsidies and services are unable to get it due to not being able to authenticate due to various reasons like old age, change of biometric and other reasons. The petitioners have referred to affidavits filed by several individuals and NGOs who after field verification brought materials before this Court to support their submission regarding large scale exclusion. It is further contended that State’s contention that Circular dated 24.10.2017 has resolved implementation issued cannot be accepted.
The authentication system in the Aadhaar Act is probabilistic. Biometric technology does not guarantee 100% accuracy and it is fallible, refers UIDAI’s own Report on “Role of Biometric Technology in Aadhaar Entrolment” (2012) has been made where Report stated that biometric accuracy 180 after accounting for the biometric failure to enrol rate, false positive identification rate, and false negative identification rate, was 99.768% accuracy. For a population over 119.22 crore enrolled in Aadhaar, it is a shocking admission of the fact that there are 27.65 lakh people who are excluded from benefits linked to Aadhaar. It is contended that validity of an act is to be judged not by its object or form, but by its effect on fundamental rights. Mandatory authentication at the point of use violates Article 21. It is contended that the Government has failed to discharge its burden of proof under Article 21. The State has also failed to satisfy the test of proportionality which makes Section 7 unconstitutional.
204. The petitioners further submit that the claim of the Government that by Aadhaar authentication the State has been able to save 11 billion per annum is incorrect and without any basis. It is further submitted that massive savings under Mahatma Gandhi National Rural Employment Guarantee Scheme under 181 Financial Benefits Accrued on account for DBT/Aadhaar since 2014 claims of substantial savings upto 201516 the amount of reported savings is shown as Rs.3000 crores and upto 2016-17 it is shown as Rs.11,741 crores. Referring to the claim of the Government that he submitted facts of job cards could be only 67,637 were found to be job cards linked to more than one Aadhaar number. Thus, maximum saving for this period would be 127.88 crores compared to the inflated figure of Rs.3000 crores.
The Financial Benefits claimed under PAHAL scheme was Rs.14,672 crores which is not correct. Referring to Comptroller and Auditor General Report, it is pointed out that with respect to 2014-15, the real outcome of savings is only 1.33 crores. He submits that major saving was on account of decrease in offtake of domestic subsidised cylinders of consumer and decrease in fuel prices. On Public Distribution System referring to answer to a question in Lok Sabha on 26.07.2016 it is submitted that the Minister of Consumer Affairs, Food and Public 182 Distribution has stated only that approximately 2.33 crores ration cards were deleted during 20132016. 205. Learned Attorney General has referred to material on record to justify the legitimate state aim which led to enactment of Section 7.
Learned Attorney General refers to Report No.3 of 2000 of the Comptroller and Auditor General of India which has been brought on record as Annexure RI to the common additional affidavit on behalf of respondents. He submits that the Comptroller and Auditor General in his Report states that 1.93 crore bogus ration cards were found to be in circulation in 13 States. Report further states that a signification portion of the subsidised foodgrains and other essential commodities did not reach the beneficiaries due to their diversion in the open market. The Performance Report of the Planning Commission of India titled “Performance Evaluation Report of Targeted Public Distribution System (TPDS)” dated March, 2005 which has been brought on record as AnnexureR6 to the 183 common additional affidavit on behalf of respondents notes following:
i. Statewise figure of excess Ration Cards in various states and the existence of over 1.52 crore excess Ration Cards issued [Page 362 of CAA]
ii. Exercise of fictitious households and identification errors leading to exclusion of genuine beneficiaries.
iii. Leakage through ghost BPL Ration Cards found to be prevalent in almost all the states under study.[Pg. 369 of CAA)
iv. The Leakage of food grains through ghost cards has been tabulated and the percentage of such leakage on an All India basis has been estimated at 16.67% [Pg.370 of CAA]. v. It is concluded that a large part of the subsidised food grains were not reaching the target group.
206. Similar reports regarding few subsidies have been referred and relied.
207. Learned Attorney General has also relied on the 184 report submitted by V.V. Giri National Labour Institute and sponsored by the Department of Rural Development, Ministry of Rural Development, Government of India which examined various aspects of National Rural Employment Guarantee Scheme while studying the schedule of rates for National Rural Employment Guarantee Scheme.
In paragraph 12.8 (Annesure R4) to the common additional affidavit on behalf of respondents following has been stated:
2. “There was great fraud in making fake cards, muster rolls were not maintained properly, and work was not provided to job seekers sometimes. In many cases, it was found that workers performed one day’s job, but their attendance was put for 33 days. The workers got money for one day while wages for 32 days were misappropriated by the people associated with the functioning of NREGS.”
208. Another report dated 09.11.2012 of National Institute of Public Finance and Policy’s “A Costbenefit analysis of Aadhaar” estimated that a leakage of approximately 12 percent is being caused to the Government on account of ghost workers and manipulated muster rolls. Thirteenth Finance Commission Report for 185 20102015 dated December, 2000 in Chapter 12 states: “creation of a biometricbased unique identity for all residents in the country has the potential to address need of the government to ensure that only eligible persons are provided subsidies and benefits and that all eligible persons are covered.”
209. Various other reports have been referred to and relied by Learned Attorney General to substantiate his case that there was large leakage and pilferation of subsidies which were allocated by the Government under different schemes. 210. This Court had occasion to consider public distribution system in PUCL vs. Union of India, (2011) 14 SCC 331, the Court noticed the report of High Powered Committee headed by Justice D.P. Wadhwa, retired Judge of this Court who had submitted report on the Public Distribution System. One of the actions suggested by the Committee was noticed in paragraphs 2 and 12 , Component II:
“2. In order to implement this system across the country, the following actions are suggested by the Committee: … … … 186 Component II: Electronic authentication of delivery and payments at the fair price shop level. In order to ensure that each cardholder is getting his due entitlement, computerisation has to reach literally every doorstep and this could take long. Moreover, several States have already started implementing smart cards, food coupons, etc. which have not been entirely successful. Reengineering these legacy systems and replacing it with the online Aadhaar authentication at the time of foodgrain delivery will take time. This is therefore proposed as Component II. 12. As far as possible, the State Governments should be directed to link the process of computerisation of Component 2 with Aadhaar registration. This will help in streamlining the process of biometric collection as well as authentication.
The States/UTs may be encouraged to include the PDs related KYR+ field in the data collection exercise being undertaken by various Registrars across the country as part of the UID (Aadhaar) enrolment.” 211. This Court again in the same proceeding passed another judgment on 16.03.2012 PUCL vs. Union of India, (2013) 14 SCC 368 in which following was stated in paragraphs 2 and 4:
“2. There seems to be a general consensus that computerisation is going to help the public distribution system in the country in a big way. In the affidavit it is stated that the Department of Food and Public Distribution has been pursuing the States to 187 undertake special drive to eliminate bogus/duplicate ration cards and as a result, 209.55 lakh ration cards have been eliminated since 2006 and the annual saving of foodgrain subsidy has worked out to about Rs 8200 crores per annum. It is further mentioned in the affidavit that endtoend computerisation of public distribution system comprises creation and management of digitised beneficiary database including biometric identification of the beneficiaries, supply chain management of TPDS commodities till fair price shops.
4. In the affidavit it is further mentioned that the Government of India has set up a task force under the Chairmanship of Mr Nandan Nilekani, Chairman, UIDAI, to recommend, amongst others, an IT strategy for the public distribution system. We request Mr Nandan Nilekani to suggest us ways and means by which computerisation process of the public distribution system can be expedited. Let a brief report/affidavit be filed by Mr Nandan Nilekani within four weeks from today.”
212. As noted above the figures as claimed by the respondents regarding benefits after implementation of Aadhaar scheme in the MGNREGA and PDS etc. are refuted by the petitioners. Petitioners’ case is that amounts of savings which are claimed are not correct and at best there was only meager benefit of savings from the implementation of the scheme. We need not to enter 188 into the issue regarding respective claims in the above regard. The reasons which led to enactment of Section 7 that benefits and subsidies are substantially diverted and are not able to reach have been made out even if saving were not substantial but meager.
213. The report and material which have been brought on record by the Government fully demonstrate the legitimate aim of the State in enacting Section 7. This Court in Francis Coralie Mullin vs. Administrator, Union Territory of Delhi and others, 1981 (1) SCC 608, while elaborating on right of life under Article 21, held that the right to life includes the right to live with dignity and all that goes along with it namely the bar necessaries of life such as adequate nutrition, clothing and shelter.
214. The United Nation under Universal Declaration of Human Rights also acknowledges everyone has a right to standard of living which includes food, clothing, housing and medical care. Article 25 of the Declaration which was made in 1948 is as follows: 189 “25.1 Everyone has the right to a standard of living adequate for the health and wellbeing of himself and of his family, including food, clothing, housing and medical care and necessary social services, and the right to security in the event of unemployment, sickness, disability, widowhood, old age or other lack of livelihood in circumstances beyond his control.”
215. The English author, JOHN BERGER said: “The poverty of our century is unlike that of any other. It is not, as poverty was before, the result of natural scarcity, but of a set of priorities imposed upon the rest of the world by the rich. Consequently, the modern poor are not pitied…but written off as trash.”
216. The identification of the poor, as was referred by John Berger is the first step to realise the UN Declaration of Human Rights as well as the Fundamental Rights guaranteed under the Constitution of India. The Aadhaar Act brings into existence a process of identification which is more accurate as compared to other identity proofs.
217. At this stage, we need to notice one more submission which was raised by the learned Attorney General. It has been submitted by the learned Attorney General that subsidies and benefits under Section 7 of the Aadhaar Act are traceable to Article 21. It is submitted that if the rights which are sought to be realised by means of Section 7 are juxtaposed against the right of privacy, the former will prevail over the latter. The issue is as to whether the State by enlivening right to food and shelter envisaged under Article 21 encroach upon the right of privacy ? There cannot be a denial that there may be inter se conflict between fundamental rights recognised by the Constitution in reference to a particular person. The Court has to strive a balance to leave enough space for exercise of both the fundamental rights.
218. It cannot be accepted that while balancing the fundamental rights one right has to be given preference. We may notice that privacy judgment i.e. Puttaswamy case has noticed and already rejected 191 this argument raised by the learned Attorney General in paragraph 266 in the following words: “266. The Attorney General argued before us that the right to privacy must be forsaken in the interest of welfare entitlements provided by the State. In our view, the submission that the right to privacy is an elitist construct which stands apart from the needs and aspirations of the large majority constituting the rest of society, is unsustainable. This submission betrays a misunderstanding of the constitutional position. Our Constitution places the individual at the forefront of its focus, guaranteeing civil and political rights in Part III and embodying an aspiration for achieving socioeconomic rights in Part IV. The refrain that the poor need no civil and political rights and are concerned only with economic wellbeing has been utilised through history to wreak the most egregious violations of human rights….”
219. One of the submissions which has been raised by the petitioners targeting the Aadhaar authentication is that biometric system under the Aadhaar architecture is probabilistic. Biometric technology does not guarantee 100% accuracy and it is fallible, with inevitable false positives and false negatives that are design flaws of such a probabilistic system. We have noted above the reliance 192 on UIDAI’s Report of the year 2012 where UIDAI itself has claimed that biometric accuracy was 99.768%. The petitioner is still criticising that since .232% failures are there which comes to 27.65 lakh people who are excluded from benefits linked to Aadhaar. The above submission of the petitioner ignores one aspect of the matter as has been contended by the respondents that in case where there is biometric mismatch of a person even possession of an Aadhaar number is treated sufficient for delivery of subsidies and benefits. Thus, physical possession of Aadhaar card itself may mitigate biometric mismatch.
However, in case of mismatch instruments are there to accept other proof of identity, the respondents have referred to Circular dated 24.10.2017 issued by UIDAI. The Circular dated 24.10.2017 has been criticised by the petitioners stating that violation of right cannot be left to vagaries of administration. There cannot be any dispute to the above propositions. It is the obligation of the State to ensure that there is no violation of fundamental rights of a person. Section 7 193 is an enabling provision which empowers the State Government to require that such individual undergo authentication for receipt of a subsidy, benefit or service but neither Section 7 nor orders issued by the Central Government and State Government can be read that in the event authentication of a person or beneficiary fails, he is not to be provided the subsidies and benefits or services. The provision is couched as an enabling provision but it cannot be read as a provision to negate giving subsidies, benefits or services in the event of failure of authentication. We are of the view that Circular dated 24.10.2017 which fills a gap and is a direction facilitating delivery of benefits and subsidies does not breach by provisions of the Act.
220. Now, we come to arguments of exclusion as advanced by the petitioners in support of their submission that exclusion makes Section 7 arbitrary and violative of Articles 14 and 21. From the material brought on record by the parties, we have no reason to doubt that there has been denial to few persons due to 194 failure of authentication. There is ample material on record to indicate that prior to enforcement of Aadhaar Scheme there had been large number of denial of benefits and subsidies to real beneficiaries due to several reasons as noted above. Functioning of scheme formulated by the Government for delivery of benefits and subsidies to deserving persons is a large scale scheme running into every nook and corner of the country. When such scheme of Government is implemented, it is not uncommon that there may be shortcomings and some denial. There is no material on record to indicate that as compared to nonreceipt of eligible beneficiaries prior to enforcement of the Act, there is increase of failure after the implementation of the Act.
It cannot be accepted that few cases of exclusion as pointed out by the petitioners makes Section 7 itself arbitrary and violative of Articles 14 and 21. Pitfalls and shortcomings are to remove from every system and it has been fairly submitted by the learned Attorney General as well as learned counsel for the UIDAI that 195 as and when difficulties in implementation and cases of denial are brought into the notice, remedial measures are taken. The respondents are still ready to take such remedial measures to ensure that there is no denial of subsidies to deserving persons. We, however, are of the view that denial of delivery of benefits and subsidies to deserving persons is a serious concern and violation of the rights of the persons concerned.
It has to be tackled at all level and the administration has to gear up itself and implementation authority has to gear up itself to ensure that rightful beneficiaries are not denied the constitutional benefits which have been recognised and which are being implemented by the different schemes of the Government. Both the Government and UIDAI are fully empowered to make Rules and Regulations under Sections 53 and 54 of the Aadhaar Act respectively and exclusions have to be taken care by exercising the power under Section 53 by the Central Government and under Section 54 by the UIDAI to remedy such shortcomings and denial. We are sure that both the 196 Central Government and UIDAI shall advert to the exclusionary factors.
221. We may also notice a judgment of the US Supreme Court in Otis R. Bowen, Secretary of Health and Human Services, et al. vs. Stephen J. Roy et al., 476 US 693 (1986). The US Supreme Court held that statutory requirement that a state agency utilise Social Security numbers in administering the programs in question does not violate the Free Exercise Clause. The appellants applied and received benefits under the Aid to Families with Dependent Children program and the Food Stamp program. They, however, refused to comply, with the requirement that participants in these programs furnish their state welfare agencies with the Social Security numbers of the members of their household as a condition of receiving benefits. Appellants had contended that obtaining a Social Security number for their 2yearold daughter, would violate their Native American religious beliefs. On refusal to give Social Number, benefits payable to the appellants were terminated. The claim of the 197 appellants was dismissed.
The challenge raised by the appellants was noticed in the following words: “Appellees raise a constitutional challenge to two features of the statutory scheme here.4 They object to Congress’ requirement that a state AFDC plan “must . . . provide (A) that, as a condition of eligibility under the plan, each applicant for or recipient of aid shall furnish to the State agency his social security account number.” 42 U.S.C. § 602(a)(25)
(emphasis added).
They also object to Congress’ requirement that “such State agency shall utilize such account numbers . . . in the administration of such plan.” Ibid.
(emphasis added).
5 We analyze each of these contentions, turning to the latter contention first.”
222. The U.S. Supreme Court upheld the requirement of providing of Social Security number. Following has been observed: “The general governmental interests involved here buttress this conclusion. Governments today grant a broad range of benefits; inescapably at the same time the administration of complex programs requires certain conditions and restrictions. Although in some situations a mechanism for individual consideration will be created, a policy decision by a government that it wishes to treat all applicants alike and that it does not wish to become involved in casebycase inquiries into the genuineness of each religious objection to such condition or restrictions is entitled to substantial 198 deference. Moreover, legitimate interests are implicated in the need to avoid any appearance of favoring religious over nonreligious applicants.
The test applied in cases like Wisconsin v. Yoder, U.S. 205, 92 S.Ct. 1526, 32 L.Ed.2d 15 (1972), is not appropriate in this setting. In the enforcement of a facially neutral and uniformly applicable requirement for the administration of welfare programs reaching many millions of people, the Government is entitled to wide latitude. The Government should not be put to the strict test applied by the District Court; that standard required the Government to justify enforcement of the use of Social Security number requirement as the least restrictive means of accomplishing a compelling state interest.17 Absent proof of an intent to discriminate against particular religious beliefs or against religion in general, the Government meets its burden when it demonstrates that a challenged requirement for governmental benefits, neutral and uniform in its application, is a reasonable means of promoting a legitimate public interest.”
223. Another case of the Appellate Division of the Supreme Court of the State of New York which needs to be noticed is in the matter of Buchanan v. Wing, 664 N.Y. 2d 865. In the above case petitioners were recipients of Aid to Families with Dependent Children, the facts of the case have been noticed in the following words: 199 “Petitioners and their four minor children are recipients of Aid to Families with Department Children (hereinafter ADC) (Social Services Law 343 et seq.) and food stamps from the Broome County Department of Social Services (hereinafter the Department).
In February 1996, petitioners received notice from the Department that they were to participate in an identity verification procedure known as the automated finger imaging system (hereinafter AFIS) as a condition of eligibility for benefits required by 18 NYCRR 351.2(a)(245 A.D. 2d 635). Petitioners responded that they would not participate because of their religious convictions. Respondent Commissioner of the Department thereafter discontinued their ADC and food stamp entitlements for failure to comply.”
224. The petitioners refused to participate in an identify verification by procedure known as automated finger imaging system which was a condition of eligibility for benefits. Upholding the process of verification by finger imaging following was laid down: “We have examined petitioners’ constitutional claims and find them to be without merit. In our view, petitioners’ failure to articulate a viable claim that they are being required to participate in an invasive procedure that is prohibited by their religious beliefs is dispositive of their arguments claiming a violation of their freedom to exercise their religion pursuant to the Federal and State 200 Constitutions (US Const 1st Amend; NY Const, art I, 3).
We are also unpersuaded by petitioners’ contention that the Department violated NY Constitution, article XVII, 1 (which provides that aid and care of the needy are public concerns and shall be provided by the State) by discontinuing their public assistance benefits. Since petitioners cannot be classified as needy until such time as they are finger imaged to determine whether they are receiving duplicate benefits, no violation of this constitutional provision has been stated. Moreover, contrary to petitioners’ arguments, the discontinuance of public assistance to their entire family unit (see, 18 NYCRR 352.30)(245 A.D. 2d 637) does not infringe the constitutional rights of their children (who are not named petitioners in light of valid legislation premising the eligibility of the children within the family unit upon the eligibility of the entire household (see, Matter of Jessup v D’Elia, 69 N.Y. 2d 1030).”
225. Another judgment which has been relied by the respondents is Doris McElrath v. Joseph A. Califano, Jr., Secretary of Health, Education and Welfare, 615 F.2d 434. Under Social Security Act, 1935, a public assistance program of federal and state cooperation providing financial aid to needy dependent children and the parents or relatives with whom they reside, one of the conditions which was added so that as a condition of eligibility under the plan, each 201 applicant for or recipient of aid shall furnish to the State agency his social security account number.
The contention of the appellant was noticed in paragraph 11 which is to the following effect: “[11] The appellants’ principal contention on appeal is that the federal and state regulations requiring dependent children to acquire and submit social security account numbers as a condition of eligibility for AFDC benefits are statutorily invalid as being inconsistent with and not authorized by the Social Security Act. We find the arguments advanced in support of this contention to be without merit and hold that the challenged regulations constitute a legitimate condition of eligibility mandated by the Congress under the Social Security Act.
Accord, Chambers v. Klein, 419 F. Supp. 569 (D.N.J. 1976), aff’d mem., 564 F.2d 89 (3d Cir. 1977); Green v. Philbrook, 576 F.2d 440 (2d Cir. 1978); Arthur v. Department of Social and Health Services, 19 Wn. App. 542, 576 P.2d 921 (1978). We therefore conclude that the district court properly dismissed the appellants’ statutory invalidity allegations for failure to state a claim upon which relief could be granted.” 226. The appellant had also contended that disclosure of social security account number violates their constitutional rights to privacy. Said argument was 202 rejected.
While rejecting the argument following was stated in paragraph 20: “[20] Finally, the appellants maintain that the social security account number disclosure requirement violates their constitutional rights to privacy and to equal protection of the law. We disagree. The constitutional guarantee of the right to privacy embodies only those personal rights that can be deemed “fundamental” or “implicit in the concept of ordered liberty.” Roe v. Wade, : 410 U.S. 113, 152, 93 S.Ct. 705, 726, 35 L.Ed.2d 147 (1973). It is equally wellsettled that “[w]elfare benefits are not a fundamental right . . . .” Lavine v. Milne, 424 U.S. 577, 584, n. 9, 96 S.Ct. 1010, 1015, 47 L.Ed.2d 249 (1976).
Accordingly, we regard the decision of Mrs. McElrath whether or not to obtain social security account numbers for her two minor children in order to receive welfare benefits as involving neither a fundamental right nor a right implicit in the concept of ordered liberty. Chambers v. Klein, 419 F. Supp. 569, 583 (D.N.J. 1976), aff’d mem. 564 F.2d 89 (3d Cir. 1977). This case is not concerned with a decision impacting the privacy of the appellants on the magnitude of criminal sanctions or an absolute prohibition on the appellants’ conduct. See, e. g., Griswold v. Connecticut, : 381 U.S. 479, 85 S.Ct. 1678, 14 L.Ed.652d 510 (1965); Eisenstadt v. Baird,: 405 U.S. 438, 92 S.Ct. 1029, 31 L.Ed.2d 349 (1972). Rather, it is concerned with a condition of AFDC eligibility and the only sanction for not complying is to forego certain governmental benefits. Simply stated, the claim of the appellants to receive welfare benefits on their own informational terms does not rise to the level of a 203 constitutional guarantee. Moreover, the contention that disclosure of one’s social security account number violates the right to privacy has been consistently rejected in other related contexts.
See, e.g., Cantor v. Supreme Court of Pennsylvania, 353 F. Supp. 1307, 132122 (E.D.Pa. 1973); Conant v. Hill, 326 F. Supp. 25, 26 (E.D.Va. 1971).” 227. The trends of judgments as noted above do indicate that condition for identification or disclosing particular identity number for receiving a benefit from State does not violate any of the Constitutional rights. We, thus, find that Section 7 fulfills the three fold tests as laid down in Puttaswamy case.
228. Shri Gopal Subramanium relying on Article 243G and Eleventh Schedule of the Constitution submits that Aadhaar Scheme and its authentication for benefits, subsidies and services militate against the above Constitution provision and hence are ultra vires to the Constitution. Article 243G deals with powers, authority and responsibilities of Panchayats, which is to the following effect:204 243G.
Powers, authority and responsibilities of Panchayats:Subject to the provisions of this Constitution the Legislature of a State may, by law, endow the Panchayats with such powers and authority and may be necessary to enable them to function as institutions of selfgovernment and such law may contain provisions for the devolution of powers and responsibilities upon Panchayats, at the appropriate level, subject to such conditions as may be specified therein, with respect to( a) the preparation of plans for economic development and social justice; (b) the implementation of schemes for economic development and social justice as may be entrusted to them including those in relation to the matters listed in the Eleventh Schedule. 229. Article 243G(b) refers to Eleventh Schedule to the Constitution. Eleventh Schedule contains list of several matters. Shri Subramanium relies on Item No. 11, 12, 16, 17, 23, 25 and 28, which are as under:11. Drinking Water.
12. Fuel and Fodder. 16. Poverty alleviation programme.
17. Education, including primary and secondary schools. 205
23. Health and Sanitation, including hospitals, primary health centres and dispensaries.
25. Women and child development.
28. Public distribution system.
230. Article 243G is an enabling provision, which enable the State Legislature, by law, to endow the Panchayats with such powers and authorities as may be necessary to enable them to function as institutions of selfgovernment. The Items on which State, by law, can endow Panchayats in Eleventh Schedule are items to deal with subjects enumerated therein. For example, Item No. 16 deals with Poverty alleviation programme and Item No. 28 deals with Public Distribution System. State is fully competent to make laws to authorise the Panchayats to take over all the matters enumerated in Eleventh Schedule.
The question to be considered is as to whether the Aadhaar Act in any manner militate with Constitutional provisions of Article 243G. The Aadhaar Act is an Act enacted by Parliament, which is referable to Entry 97 of List I. The Aadhaar Act has been enacted 206 to provide for efficient, transparent, and targeted delivery of subsidies, benefits and services, the expenditure for which is incurred from the Consolidated Fund of India, to individuals residing in India through assigning of unique identity numbers to such individuals and for matters connected therewith. The Act, thus, has been enacted to regulate the expenditure, which is incurred from the Consolidated Fund of India. No conflict between the Aadhaar Act and any law, which may be enacted by State under List II is seen.
Even if any conflict is supposed, the Doctrine of Pith and Substance has to be applied to find out nature of two legislations. In Pith and Substance, the Aadhaar Act cannot be said to be entrenching upon any law, which may be made by the State under Item No.5 of List II. In this context, reference is made to judgment of this Court in State of Uttar Pradesh and Another Vs. Zila Parishad, Ghaziabad and Another, (2013) 11 SCC 783. In the above case, provisions of Article 243G came to be considered in reference to public distribution orders issued by the State Government in exercise of delegated powers under 207 Essential Commodities Act, 1955.
The Central Government in exercise of power under Section 3 of the Essential Commodities Act, the Government of U.P. issued an order dated 10.8.1999, conferring the power to allot and cancel the fair price shops in rural areas, with certain guidelines, on the Gram Panchayats. Subsequently, the State Government withdrew that order and reinforced the earlier policy dated 03.07.1990 under which the power was vested with the District Magistrate or an authority designated by him to allot or cancel the licenses for Fair Price Shops. The Central Government, in exercise of power under Section 3 of the Essential Commodities Act, issued an order dated 31.8.2001, wherein its powers were delegated to State Government. State Government, in pursuance thereof, issued an order designating the officers of the District level, viz., District Magistrate, SubDivisional Magistrate, District Supply Officer to ensure the proper supply and distribution of such commodities.
Zila Parishad, Ghaziabad filed a Writ Petition in the High Court challenging the Order dated 13.01.2000 by which the power was withdrawn from the Gram 208 Panchayats. The Writ Petition was allowed by the High Court against which State of Uttar Pradesh filed an appeal. The submission was raised before this Court on behalf of the writ petitioner that denuding the power from Panchayats will be against the constitutional provision of Article 243G. Such argument on behalf of petitioner has been noticed in Paragraph 14. This Court after considering the provisions of Article 243G and other relevant provisions has laid down in Paras 23 and 24:”
23. The High Court has considered the nature of the aforesaid constitutional provision and held as under: (Zila Panchayat case1, AWC pp. 398182, para 16) “16. In our opinion, this provision is only an enabling provision. It enables the Legislature of a State to endow the Panchayats with certain powers. … Hence, the Legislature of a State is not bound to endow the Panchayats with the powers referred to Article 243G, and it is in its discretion to do so or not. At any event there is no mention of the public distribution system in Article 243G of the Constitution.” Thus, it is evident that the High Court has taken a view that the provision of Article 243G is merely an enabling provision, and it 209 is not a source of legislation.
This view seems to be in consonance with the law laid down by this Court in U.P. Gram Panchayat Adhikari Sangh v. Daya Ram Saroj4 wherein an observation has been made that Article 243G is an enabling provision as it enables the Panchayats to function as institutions of selfgovernment. Further, this Court noted that such law may contain provisions for the devolution of powers and responsibilities upon Panchayats, subject to such conditions as may be specified therein, with respect to the implementation of schemes for economic development and social justice as may be entrusted to them, including those in relations to the matters listed in the Eleventh Schedule. The enabling provisions are further subject to the conditions as may be specified. Therefore, it is for the State Legislature to consider conditions and to make laws accordingly. It is also open to the State to eliminate or modify the same.
24. Therefore, it is apparent that Article 243G read with the Eleventh Schedule is not a source of legislative power, and it is only an enabling provision that empowers a State to endow functions and devolve powers and responsibilities to local bodies by enacting relevant laws. The local bodies can only implement the schemes entrusted to them by the State.”
231. This Court in the above case has reiterated that Article 243G read with Eleventh Schedule is not a source of legislative power, and it is only an enabling provision that empowers a State to endow functions and 210 devolve powers and responsibilities to local bodies by enacting relevant laws. We, thus, are unable to accept the submission of Shri Gopal Subramanium that Aadhaar Act is ultra vires to Article 243G and Eleventh Schedule to the Constitution.
232. One more submission of the petitioners which needs to be considered is regarding probabilistic nature of biometric solution. We proceed on premise that Aadhaar structure is probabilistic, the petitioners themselves have referred to UIDAI Report where biometric accuracy has been stated to be 99.768%. Stephen Hawkin in his book: “God Created The Integers” states:
“Over the centuries, the efforts of these mathematicians have helped the human race to achieve great insight into nature, such as the realisation that the earth is round, that the same force that causes an apple to fall here on earth is also responsible for the motions of the heavenly bodies, that space is finite and not eternal, that time and space are intertwined and warped by matter and energy, and that the future can only be determined probabilistically. Such revolutions in the way we perceive the world have always gone hand in hand with revolutions in mathematical thought. Isaac Newton could never have formulated his laws without the analytic geometry of Rene Descartes and Newton’s own invention of calculus.
It is hard to imagine the development of either electrodynamics or quantum theory without the methods of Jean Baptiste Joseph Fourier or the work on calculus and the theory of complex functions pioneered by Carl Friedrich Gauss and Augustin Louis Cauchyand it was Henri Lebesgue’s work on the theory of measure that enabled John von Neumann to formulate the rigorous understanding of quantum theory that we have today. Albert Einstein could not have completed his general theory of relativity had it not been for the geometric ideas of Bernhard Riemann. And practically all of modern science would be far less potent (if it existed at all) without the concepts of probability and statistics pioneered by PierreSimon Laplace.” 233. The science and technology keeps on changing with pace of time.
A scientific invention or module which is invented or launched keeps on improving with time. The ready example is improvement in quality and programmes of mobile phone which has seen steep development in the last one decade. Even if authentication under Aadhaar scheme is probabilistic as on date, we have no doubt that the steps will be taken to minimise the misnatch and to attain more accuracy in the result. In view of the foregoing discussion we are of the view that the State has given 212 sufficient justification to uphold the constitutionality of Section 7. We, thus, answer Question Nos.6 and 7 in the following manner:
Ans.6:Section 7 of the Aadhaar is constitutional. The provision does not deserve to be struck down on account of denial in some cases of right to claim on account of failure of authentication.
Ans.7:The State while enlivening right to food, right to shelter etc. envisaged under Article 21 cannot encroach upon the right of privacy of beneficiaries nor former can be given precedence over the latter.
Issue No.8
Whether Section 29 of the Aadhaar Act is liable to be struck down?
234. The ground to challenge Section 29 is that it permits sharing of identity information. It is submitted that sharing of identity information is breach of Right of Privacy. Section 29 is a 213 provision, which contains restrictions on sharing information as is clear from the heading of the section. Section 29 subsection (1) contains prohibition on sharing of any core biometric information collected or created under this Act. Section 29 for ready reference is extracted as below:
29. Restriction on sharing information.
(1) No core biometric information, collected or created under this Act, shall be-
(a) shared with anyone for any reason whatsoever; or
(b) used for any purpose other than generation of Aadhaar numbers and authentication under this Act.
(2) The identity information, other than core biometric information, collected or created under this Act may be shared only in accordance with the provisions of this Act and in such manner as may be specified by regulations.
(3) No identity information available with a requesting entity shall be-
(a) used for any purpose, other than that specified to the individual at the time of submitting any identity information for authentication; or
(b) disclosed further, except with the prior consent of the individual to whom such information relates.
(4) No Aadhaar number or core biometric information collected or created under this Act in respect of an Aadhaar number holder shall be published, displayed or posted publicly, except for the purposes as may be specified by regulations.
235. Subsection (2) permits sharing of identity information, other than core biometric information, only in accordance with the provisions of this Act and in such manner as may be specified by regulations. Further subsection
(3) prohibits requesting entity to use identity information for any purpose other than that specified to the individual or to disclose any information without the consent of individual. Subsection (4) provides that no Aadhaar number or core biometric information shall be published, displayed or posted publicly, except for the purposes as may be specified by regulations. The attack on Section 29 that it permits sharing of information is thus wholly misconceived. The objective of the Act is to protect the information and privacy of an individual and so the Section is not liable to be struck down on the specious ground that it permits sharing of the information.
Further subsection (3) engraft a provision of sharing identity information by requesting entity with consent of the individual. When a person consents about sharing of his identity information, he cannot complain breach of Privacy Right. Petitioners take exception of provision of subsection ( 2), which permits identity information other than core biometric information to be shared in accordance with the provisions of this Act and in such manner as may be specified by the regulations. When an Act or Regulation regulates and controls sharing of the information, the provision is regulatory and has been engrafted to protect individual’s Privacy Right.
The Aadhaar (Sharing of Information) Regulations, 2016 again contains in Chapter II Restrictions on sharing of identity information. Regulation 3 is restriction on Authority. Regulation 4 is restriction on requesting entity. Regulation 5 fixes responsibility of any agency or entity other than requesting entity with respect to Aadhaar number. Regulation 6 provides restriction on sharing, circulating or publishing of 216 Aadhaar number.
236. We, thus, conclude that the provision of Section 29 and the Sharing Regulations contains a restriction and cannot be in any manner be held to violate any of the constitutional rights of a person. Objective of the Act is to put restrictions on the sharing information, which also is a legitimate State aim. The provision under Section 29 which permits sharing of identity information except core biometric information in accordance with the Act and Regulations cannot be said to be disproportionate nor unreasonable. Legislature can very well enumerates circumstances and conditions where sharing of information becomes necessary. One of the circumstances where sharing of the information is specifically engrafted in subsection ( 2) of Section 33, which provides that nothing contained in subsection (3) of Section 29 shall apply in respect of any disclosure of information, including identity information or authentication records, made in the interest of national security in pursuance of a 217 direction of an officer not below the rank of Joint Secretary to the Government of India. Thus, the circumstances which can contemplate for sharing information is reasonable and proportionate. We, thus, held that provisions of Section 29 is constitutional and does not deserves to be struck down. Issue No. 8 is answered in the following manner:
Ans. 8:Provisions of Section 29 is constitutional and does not deserves to be struck down.
Issue No.9
Whether Section 33 is Constitutional ?
237. Section 33 of the Aadhaar Act, 2016 is as follows: “33. Disclosure of information in certain cases.( 1) Nothing contained in subsection (2) or subsection (5) of section 28 or subsection (2) of section 29 shall apply in respect of any disclosure of information, including identity information or authentication records, made pursuant to an order of a court not inferior to that of a District Judge: Provided that no order by the court under this subsection shall be made without giving an opportunity of hearing to the Authority.
(2) Nothing contained in subsection (2) or subsection (5) of section 28 and clause (b) of subsection (1), subsection (2) or subsection (3) of section 29 shall apply in respect of any disclosure of information, including identity information records, made in the interest of national security in pursuance of a direction of an officer not below the rank of Joint Secretary to the Government of India specially authorised in this behalf by an order of the Central Government: Provided that every direction issued under this subsection, shall be reviewed by an Oversight Committee consisting of the Cabinet Secretary and the Secretaries to the Government of India in the Department of Legal Affairs and the Department of Electronics and Information Technology, before it takes effect: Provided further that any direction issued under this subsection shall be valid for a period of three months from the date of its issue, which may be extended for a further period of three months after the review by the Oversight Committee.”
238. The first limb of argument of the petitioner is that Section 33 is unconstitutional since it provides for the use of the Aadhaar data base for Police verification which violates the protection against selfincrimination as enshrined under Article 20(3) of the Constitution of India.
239. Subsection (1) of Section 33 contains an ample restriction in respect of any disclosure information which can be done only in pursuance of an order of the court not inferior to that of a District Judge. The restriction in disclosure of information is reasonable and has valid justification. The authority whose duty is to safeguard the entire data has to be heard before passing an order by the court which amply protects the interest of a person whose data is to be disclosed. An order of the court not inferior to that of a District Judge for disclosure of information itself is an ample protection to that, for no unreasonable purpose data shall be disclosed. Attacking on subsection (2) of Section 33, it is contended that although (i)disclosure of information has been permitted in the interest of the national security but there is no definition of national security, (ii) there is no independent oversight disclosure of such data on the ground of security, (iii)the provision is neither fair nor reasonable. Section (2) of Section 33 is disproportionate and unconstitutional.
240. Section 33 subsection (2) contains two safeguards. Firstly, disclosure of information is to be made in the interest of national security and secondly, in pursuance of a direction of an officer not below the rank of Joint Secretary to the Government, who is specially authorised in this behalf by an order of the Central Government. National security, thus, has to be determined by a higher officer who is specifically authorised in this behalf. This Court in Ex. Armymen’s Protection Services P. Ltd. Vs. Union of India (UOI) and Ors., 2014 (5) SCC 409, has held that what is in the interest of national security is not a question of law but that it is matter of a policy. Following was held in paragraphs 16 and 17:
“16. What is in the interest of national security is not a question of law. It is a matter of policy. It is not for the court to decide whether something is in the interest of State or not. It should be left to the Executive. To quote Lord Hoffman in Secretary of State for the Home Department v. Rehman (2003) 1 AC 153:…in the matter of national security is not a question of law. It is a matter of judgment and policy. Under the Constitution of the United Kingdom and most other countries, decisions as to whether 221 something is or is not in the interest of national security are not a matter for judicial decision. They are entrusted to the executive.
17. Thus, in a situation of national security, a party cannot insist for the strict observance of the principles of natural justice. In such cases it is the duty of the Court to read into and provide for statutory exclusion, if not expressly provided in the rules governing the field. Depending on the facts of the particular case, it will however be open to the court to satisfy itself whether there were justifiable facts, and in that regard, the court is entitled to call for the files and see whether it is a case where the interest of national security is involved. Once the State is of the stand that the issue involves national security, the court shall not disclose the reasons to the affected party.”
241. The International Courts have also dealt the issue. In a case, namely, Census Act(BverfGE 65, 1), judgment of Federal Constitution Court of Germany, judgment dated 11.10.2013, the Court had occasion to consider the case in the context of data processing and protection of individual information against selfincrimination and use of their personal data. Dealing with right of information and selfdetermination the Court held that individuals have no right in the sense of absolute, unrestricted control over their data. 222 Following was held by the Court: “The guarantee of this right to informational selfdetermination” is not entirely unrestricted. Individuals have no right in the sense of absolute, unrestricted control over their data; they are after all human persons who develop within the social Community and are dependent upon communication. Information, even if related to individual persons, represents a reflection of societal reality that cannot be exclusively assigned solely to the parties affected.
The Basic Law, as has been emphasized several times in the case law of the Federal Constitutional Court, embodies in negotiating the tension between the individual and the Community a decision in favour of civic participation and civic responsibility(see BverfGE 4, 7 [15] ; 8, 274 [329]; 27, 344 [351 and 352]; 33, 303 [334]; 50, 290 [353]; 56, 37 [49]). Individuals must therefore in principle accept restriction on their right to informational selfdetermination in the overriding general public interest.” 242. Another judgment of European Commission of Human Rights in M.S. against Sweden was a case that applicant has complained that copies of her medical records containing information on treatment have been forwarded by the clinic without her information to the Insurance Co. The case of the applicant was noticed in paragraph 39 which is to the following effect:
“39. The applicant submits that the women’s clinic’s submission of copies of her medical records to the Social Insurance Office without her knowledge or consent interfered with her right to respect for her private life. She maintains that the information contained in these records were of a highly sensitive and private nature. Allegedly, she could not anticipate, when she claimed compensation from the Office, that information on the abortion performed several years after alleged back injury would be forwarded to the Office. She further refers to the fact that the information in question is not protected by the same level of confidentiality at the Office as at the clinic.”
243. The Commission held that information was rightly submitted to the Insurance Co. in accordance with law. It is also relevant to refer the judgment of this Court in People’s Union for Civil Liberties(PUCL) v. Union of India, 1997 (1) SCC 301, where the writ petition was filed under Article 32 alleging serious invasion of an individual’s privacy on the account of Telephonetapping. The Court adverted to the Indian Telegraph Act, 1885 and the Rules framed thereunder. The Court has noticed that Section 5(2) of the Telegraph Act permits the interception of messages in accordance with the said section, “Occurrence of any 224 public emergency” or “in the interest of public safety”. In paragraph 28 following was held: “28. Section 5(2) of the Act permits the interception of messages in accordance with the provisions of the said Section. “Occurrence of any public emergency” or “in the interest of public safety” are the sine qua non. for the application of the provisions of Section 5(2) of the Apt. Unless a public emergency has occurred or the interest of public safety demands, the authorities have no jurisdiction to exercise the powers under the said Section. Public emergency would mean the prevailing of a sudden condition or state of affairs affecting the people at large calling for immediate action.”
244. This Court issued various directions providing for certain safeguards regarding an order for Telephonetapping. Thus, on fulfillment of statutory conditions when telephonic conversation can be intercepted no exception can be taken for disclosure of information in the interest of national security.
245. The power given under Section 33 to disclose information cannot be said to be disproportionate. The disclosure of information in the circumstances mentioned in Section 33 is reasonable and in the public interest.
246. We are satisfied that the provision fulfills three fold test as laid down in Puttaswamy case. There are no grounds to declare Section 33 as unconstitutional.
247. We also need to advert to one of the submissions of the petitioner that permitting disclosure of information for police investigation violates the protection against selfincrimination as provided under Article 20 subclause (3). It is true that under Section 33 the Court may order for disclosure of information even for a police investigation. But information so received in no manner can be said to violate the protection given under Article 20 subclause (3). The basic information which are with the UIDAI are demographic and biometric information. In this context, reference is made to 11Judge Constitution Bench judgment of this Court in State of Bombay vs. Kathi KALU Oghad, AIR 1961 SC 1808. The Constitution Bench had occasion to consider subclause (3) of Article 20 of the Constitution. In the above case from the accused who was charged under Section 302/34 IPC during the investigation prosecution has obtained three specimen of handwriting which were compared by his handwriting which was part of the evidence. A question was raised as to the admissibility of the specimen of handwriting, it was contended that use of specimen of handwriting violated protection under Article 20(3). This Court in paragraph 16 laid down following:
(16) In view of these considerations, we have come to the following conclusions :
(1) An accused person cannot be said to have been compelled to be a witness against himself simply because he made a statement while in police custody, without anything more. In other words, the mere fact of being in police custody at the time when the statement in question was made would not, by itself, as a proposition of law, lend itself to the inference that the accused was compelled to make the statement, though that fact, in conjunction with other circumstances disclosed in evidence in a particular case, would be a relevant consideration in an enquiry whether or not the accused 227 person had been compelled to make the impugned statement.
(2) The mere questioning of an accused person by a police officer, resulting in a voluntary statement, which may ultimately turn out to be incriminatory, is not ‘compulsion’.
(3) ‘To be a witness’ is not equivalent to ‘furnishing evidence’ in its widest significance; that is to say, as including not merely making of oral or written Dagduas but also production of documents or giving materials which may be relevant at a trial to determine the guilt innocence of the accused.
(4) Giving thumb impressions or impressions of foot or palm or fingers or specimen writings or showing parts of the body by way of identification are not included in the expression ‘to be a witness’.
(5) ‘To be a witness’ means imparting knowledge in respect of relevant facts by an oral statement or a statement in writing, made or given in Court or otherwise.
(6) ‘To be a witness’ in its ordinary grammatical sense means giving oral testimony in Court. Case law has gone beyond this strict literal interpretation of the expression which may now bear a wider meaning, namely, bearing testimony in Court or out of Court by a person accused of an offence, orally or in writing.
(7) To bring the statement in question within the prohibition of 228 Article 20(3), the person accused must have stood in the character of an accused person at the time he made the statement. It is not enough that he should become an accused, any time after the statement has been made.”
248. From what has been held in the above case, it is clear that ‘to be a witness’ is not equivalent to ‘furnishing evidence’ in its widest significance. The use of information retained by the UIDAI given by the order of the Court under Section 33 cannot be said to be violating the protection as contained under Article 20(3). Thus, Article 20(3) is not violated by disclosure of information under Section 33. In view of the foregoing discussion, we hold that Section 33 is constitutional. 249. One of the decisions on which Shri K.V. Viswanathan has placed reliance in support of his submission regarding violation of Article 20(3) as well as Article 21 of the Constitution is Selvi and others vs. State of Karnataka, 2010(7) SCC 263. In the above case this Court had considered as to whether certain scientific techniques, namely, narcoanalysis, 229 polygraph examination and the Brain Electrical Activation Profile (BEAP)test for the purpose of improving investigation efforts in criminal cases violate subclause (3) of Article 20 as well as Article 21. The legal issues and questions of law have been noted in paragraphs 2 and 11 to the following effect:
“2. The legal questions in this batch of criminal appeals relate to the involuntary administration of certain scientific techniques, namely narcoanalysis, polygraph examination and the Brain Electrical Activation Profile (BEAP) test for the purpose of improving investigation efforts in criminal cases. This issue has received considerable attention since it involves tensions between the desirability of efficient investigation and the preservation of individual liberties. Ordinarily the judicial task is that of evaluating the rival contentions in order to arrive at a sound conclusion. However, the present case is not an ordinary dispute between private parties. It raises pertinent questions about the meaning and scope of fundamental rights which are available to all citizens. Therefore, we must examine the implications of permitting the use of the impugned techniques in a variety of settings.
11. At this stage, it will be useful to frame the questions of law and outline the relevant subquestions in the following manner:
I.Whether the involuntary administration of the impugned techniques violates the `right against selfincrimination’ enumerated in Article 20(3) of the Constitution?
IA. Whether the investigative use of the impugned techniques creates a likelihood of incrimination for the subject?
IB. Whether the results derived from the impugned techniques amount to `testimonial compulsion’ thereby attracting the bar of Article 20(3)? II.Whether the involuntary administration of the impugned techniques is a reasonable restriction on `personal liberty’ as understood in the context of Article 21 of the Constitution? “
250. After considering large number of cases of this Court as well as judgments rendered by Foreign Courts, a conclusion was recorded that those tests, since they are a means for imparting personal knowledge about relevant facts, hence, they come within the scope of testimonial compulsion thereby attracting the protective shield of Article 20(3). In paragraph 189 following was held:
“189. In light of the preceding discussion, we are of the view that the results obtained from tests such as polygraph examination and the BEAP test should also be treated as `personal testimony’, since they are a means for `imparting personal knowledge about relevant facts’. Hence, our conclusion is that the results obtained through the involuntary administration of either of the impugned tests (i.e. the narcoanalysis technique, polygraph examination and the BEAP test) come within the scope of `testimonial compulsion’, thereby attracting the protective shield of Article 20(3). “
251. In so far as question of violation of Article 21 is concerned, this Court, in paragraphs 225 and 226 has held:
“225. So far, the judicial understanding of privacy in our country has mostly stressed on the protection of the body and physical spaces from intrusive actions by the State. While the scheme of criminal procedure as well as evidence law mandates interference with physical privacy through statutory provisions that enable arrest, detention, search and seizure among others, the same cannot be the basis for compelling a person `to impart personal knowledge about a relevant fact’. The theory of interrelationship of rights mandates that the right against selfincrimination should also be read as a component of `personal liberty’ under Article 21. Hence, our understanding of the `right to privacy’ should account for its intersection with Article 20(3). Furthermore, the `rule against involuntary confessions’ as embodied in Sections 24, 25, 26 and 27 of the Evidence Act, 1872 seeks to serve both the objectives of reliability as well as voluntariness of testimony given in a custodial setting. A conjunctive reading of Articles 20(3) and 21 of the Constitution along with the principles of evidence law leads us to a clear answer. We must recognise the importance of personal autonomy in aspects such as the choice between remaining silent and speaking. An individual’s decision to make a statement is the product of a private choice and there should be no scope for any other individual to interfere with such autonomy, especially in circumstances where the person faces exposure to criminal charges or penalties.
226. Therefore, it is our considered opinion that subjecting a person to the impugned techniques in an involuntary manner violates the prescribed boundaries of privacy. Forcible interference with a person’s mental processes is not provided for under any statute and it most certainly comes into conflict with the `right against selfincrimination’. However, this determination does not account for circumstances where a person could be subjected to any of the impugned tests but not exposed to criminal charges and the possibility of conviction. In such cases, he/she could still face adverse consequences such as custodial abuse, surveillance, undue harassment and social stigma among others. In order to address such circumstances, it is important to examine some other dimensions of Article 21. “
252. The nature of tests which were under consideration in the aforesaid case, were elaborately noticed by this Court and the tests were found to be in nature of 233 substantial intrusion in the body and mind of an individual, hence, it was held that they violate Article 20(3) as well as Article 21. It is, however, relevant to notice that this Court in Selvi judgment itself has noticed the distinction in so far as use of fingerprints were concerned. This Court had noticed earlier judgment of State of Bombay v. Kathi Kalu Oghad, AIR 1961 SC 1808 with approval. The biometric information that is fingerprints and iris scan can not be equated to the tests which came for consideration in Selvi’s case. Hence, the judgment of this Court in Selvi does not in any manner support the case of the petitioners. Answer to question No.3 is in following Manner: Ans.9: Section 33 cannot be said to be unconstitutional as it provides for the use of Aadhaar data base for police investigation nor it can be said to violate protection granted under Article 20(3). 234
Issue No.10
Whether Section 47 of the Aadhaar Act is Unconstitutional?
253. The Petitioner submits that Section 47 of the Aadhaar Act is unconstitutional since it does not allow an individual who is victim of violation of Aadhaar Act to initiate a criminal process. It is submitted that the person who is victim of an offence under the Aadhaar Act has no remedy to file a complaint and Section 47 of the Act restrict the filing of complaint only by Authorities or Officers or persons authorised by it. 254. The above submission is refuted by the respondent that Section 47 has a rationale. The offences and penalties under Chapter VII of the Aadhaar Act are all intended to maintain the purity and integrity of CIDR and the entire enrolment storage in CIDR and authentication exercise can only be efficiently and effectively handled by UIDAI. Thus, jurisdiction to submit a complaint has been conferred to UIDAI which is the most entrusted entity for maintaining the 235 purity of Aadhaar Scheme and is also affected by offences committed under the Aadhaar Act. Section 47 provides as follows:
“47. Cognizance of Offence ( 1) No court shall take cognizance of any offence punishable under this Act, save on a complaint made by the Authority or any officer or person authorised by it. (2) No court inferior to that of a Chief Metropolitan Magistrate or a Chief Judicial Magistrate shall try any offence punishable under this Act.” 255. Provisions akin to Section 47 are found in most of Statutes which Statutes defines offences under the Statute and provide penalty and punishment thereunder. Following are some of the Statues which contains a provision akin to Section 47 of Aadhaar Act:
“1)Section 22 of Mines and Minerals(Development & Regulation) Act, 1957 – No Court shall take cognizance of any offence punishable under this Act or any rules made thereunder except upon complaint in writing made by a person authorised in this behalf by the Central Government or the State Government.
2) Section 34 of the Bureau of Indian Standards Act, 1986 No Court shall take cognizance of an offence punishable under this Act, save on a complaint made by or under the authority of the Government or 236 Bureau or by any officer empowered in this behalf by the Government or the Bureau, or any consumer or any association recognized in this behalf by the Central or State Government.
3) Section 26(1) of SEBI Act, 1992 – No Court shall take cognizance of any offence punishable under this Act or any rules or regulations made thereunder, save on a complaint made by the Board.
4) Section 34 of Telecom Regulatory Authority of India Act, 1997 – No Court shall take cognizance of any offence punishable under this Act or the rules or regulations made thereunder, save on a complaint made by the Authority.
5) Section 57(1) of Petroleum and Natural gas Regulatory Board Act, 2007 – No Court shall take cognizance of any offence punishable under Chapter IX save on a complaint made by the Board or by any investigating agency directed by the Central Government.
6) Section 47 of Banking Regulation Act, 1949 – No court shall take a cognizance of any offence punishable under subsection (5) of Section 36AA or Section 46 except upon complaint in writing made by an officer of the Reserve Bank or, as the case may be, the National Bank generally or specially authorised in writing in this behalf by the Reserve Bank, or as the case may be, the National Bank and no court other than that of a Metropolitan Magistrate or a Judicial Magistrate of the first class or any court superior thereto shall try any such offence.
7) Section 19 of Environment (Protection) Act, 1986 – No court shall take cognizance of 237 any offence under this Act except on a complaint made by –
(a) the Central Government or any authority or officer authorised in this behalf by that Government, or (b) any person who has given notice of not less than sixty days, in the manner prescribed, of the alleged offence and of his intention to make a complaint, to the Central Government or the authority or officer authorised as aforesaid.
8) Section 43 of The Air (Prevention and Control of Pollution) Act, 1981 –
(1) No Court shall take cognizance of any offence under this Act except on a complaint made by –
(a) a Board or any officer authorised in this behalf by it; or (b) any person who has given notice of not less than sixty days, in the manner prescribed, of the alleged offence and of his intention to make a complaint to the Board or officer authorised as aforesaid, and no court inferior to that of a Metropolitan Magistrate or a Judicial Magistrate of the first class shall try any offence punishable under this Act.”
256. Large number of Special Acts which defines offences under the Act and their penalty contains provision akin to Section 34 of the Aadhaar Act. Special Acts are enacted for serving special objects towards offences under the Act. The initiation and prosecution of offences under the Special Act are kept by the specified authority to keep the initiation and prosecution in the hands of the authorities under the 238 Special Act which acts as deterrent and prosecutions are brought to its logical end. Further, objective of such provisions is to discourage frivolous and vexatious complaints.
257. This Court in Rajkumar Gupta versus Lt.Governor, Delhi and Others, (1997) 1 SCC 556, had occasion to consider Section 34(1) of the Industrial Disputes Act, 1947 and objective behind putting such restriction. Section 34 of Industrial Disputes Act provided that no Court shall take cognizance of any offence punishable under this Act or of the abetment of any such offence, save on complaint made by or under the authority of the appropriate Government. Section 34 of Industrial Disputes Act is pari materia with Section 47 of the Aadhaar Act. This Court noticing the objective of Section 34 laid down following in the paragraph 16. The Court held that Section 34 is in the nature of limitation on the entitlement of workman or trade union or an employer to complain of offences under the Act. Following was laid down in paragraph 16: “
16. At the same time, the provisions of 239 Section 34 are in the nature of a limitation on the entitlement of a workman or a trade union or an employer to complain of offences under the said Act. They should not, in the public interest, be permitted to make frivolous, vexatious or otherwise patently untenable complaints, and to this end Section 34 requires that no complaint shall be taken cognizance of unless it is made with the authorization of the appropriate Government.”
258. In so far as the submission that there is no forum for a person victim of an offence under Aadhaar Act, suffice to say that Section 47 can be invoked by the authority on its own motion or when it receives a complaint from a victim. The authority i.e. UIDAI has varied powers and functions as enumerated in Section 23 of the Act. It is the authority who is most entrusted in ensuring that the provisions of the Act are implemented in accordance with the Act and offenders should be punished. In so far as remedy of victim is concerned, there are few facts which need to be kept in mind.
259. The Information Technology Act, 2000 defines electronic record in Section 2(t) which is to the following effect:240 “Section 2(t)” electronic record” means data, record or data generated, image or sound stored, received or sent in an electronic form or micro film or computer generated micro fiche;”
260. The demographic and biometric information which is collected for enrolment of the resident in electronic data as defined in Section 2(t) of Information Technology Act and expressly stated in Section 30 of Aadhaar Act. Chapter 11 of the Information Technology Act defines offences.
Section 66C, Section 66D and Section 72 of the Information Technology Act defines offences and provides for penalty, which is to the following effect:” 66C. Punishment for identity theftWhoever, fraudulently or dishonestly make use of the electronic signature, password or any other unique identification feature of any other person, shall be punished with imprisonment of either description for a term which may extend to three years and shall also be liable to fine which may extend to rupees one lakh. 66D. Punishment for cheating by personation by using computer resourceWhoever, by means for any communication device or computer resource cheats by personating, shall be punished with imprisonment of either description for a term which may extend to three years and shall also be liable to fine 241 which may extend to one lakh rupees.
72. Penalty for breach of confidentiality and privacy – Save as otherwise provided in this Act or any other law for the time being in force, if any person who, in pursuance of any of the powers conferred under this Act, rules or regulations made thereunder, has secured access to any electronic record, book, register, correspondence, information, document or other material without the consent of the person concerned discloses such electronic record, book, register, correspondence, information, document or other material to any other person shall be punished with imprisonment for a term which may extend to two years, or with fine which may extend to one lakh rupees, or with both.”
261. With regard to an offence which falls within the definition of ‘offences’ a victim can always file complaint or lodge an F.I.R.. Section 46 of the Aadhaar Act clearly provides that the penalties under the Aadhaar Act shall not interfere with other punishments. Section 46 is as follows:
“46. Penalties not to interfere with other punishments. No penalty imposed under this Act shall prevent the imposition of any other penalty or punishment under any other law for the time being in force.” 262. This Court in State (NCT of Delhi) versus Sanjay, (2014) 9 SCC 772, had occasion to consider the 242 provisions of Section 22 of the Mines and Minerals (Development & Regulations) Act, 1957 which provision is similar to Section 47 of the Aadhaar Act. The question arose that whether in case the complaint has not been filed by the authority under Section 22, whether cognizance can be taken of the offence if it falls within definition of any of the offences under the Indian Penal Code.
There was divergence of opinions between the different High Courts. This Court after noticing earlier judgments of this Court, laid down following in paragraphs 17 and 73. “17. Since conflicting views have been taken by the Gujarat High Court, the Delhi High Court, the Kerala High Court, the Calcutta High Court, the Madras High Court and the Jharkhand High Court, and they are in different tones, it is necessary to settle the question involved in these appeals.
73. After giving our thoughtful consideration in the matter, in the light of relevant provisions of the Act visàvis the Code of Criminal Procedure and the Penal Code, we are of the definite opinion that the ingredients constituting the offence under the MMDR Act and the ingredients of dishonestly removing sand and gravel from the riverbeds without consent, which is the property of the State, is a distinct offence under IPC. Hence, for the commission of offence Under Section 378 IPC, on receipt of the police report, the Magistrate having jurisdiction can take cognizance of the said offence without awaiting the receipt of complaint that may be filed by the authorized officer for taking cognizance in respect of violation of various provisions of the MMDR Act. Consequently the contrary view taken by the different High Courts cannot be sustained in law and, therefore, overruled. Consequently, these criminal appeals are disposed of with a direction to the Magistrates concerned to proceed accordingly. “
263. The limitation as contained in Section 47 in permitting taking cognizance of any offence punishable under Aadhaar Act only on a complaint made by the authority or any officer or person authorised by it, has legislative purpose and objective, as noticed above. We thus do not find any unconstitutionality in Section 47 of the Aadhaar Act. In view of the foregoing discussions, the answer to Issue No.10 is in following manner:Ans. 10: Section 47 of the Aadhaar Act cannot be held to be unconstitutional on the ground that it does not allow an individual who finds that there is a violation of Aadhaar Act to initiate any criminal process.
Issue No. 11
Whether Section 57 of Aadhaar Act is unconstitutional?
264. Section 57 of the Act, which contains a heading “Act not to prevent use of Aadhaar Number for other purposes under law” provides:” 57. Act to prevent use of Aadhaar number for other purposes under law. Nothing contained in this Act shall prevent the use of Aadhaar number for establishing the identity of an individual for any purpose, whether by the State or any body corporate or person, pursuant to any law, for the time being in force, or any contract to this effect: Provided that the use of Aadhaar number under this section shall be subject to the procedure and obligations under section 8 and Chapter VI.”
265. Attacking the provision of Section 57, petitioners contends that broad and unlimited scope of activities covered under Section 57 and kinds of private entities permitted to use Aadhaar is entirely disproportionate beyond the means and objectives of the Act and without any compelling State interests. There are no procedural safeguards governing the actions of private entities and no remedy for undertaking’s failure or service denial. The individual, who wish to be 245 enrolled have given their consent only for Aadhaar subsidies, benefits and services, which cannot be assumed for other purposes. Section 57 has to be struck down on the ground of excessive delegation. “Any purpose” indicates absence of guidelines. Any purpose does not mean all purposes and several aspects of human existence. Section 57 violates all principles of proportionality.
266. Refuting the above submission of the petitioners, the respondents submits that, Section 57 is not an enabling provision, it merely provides as it states that the provisions of the Act would not prevent the use of Aadhaar for other purposes. In fact, Section 57 employs limitation on such user for other purposes, which is engrafted in Proviso to Section 59. The use of Aadhaar having been made subject to procedure and obligations under Section 8 and Chapter VI, the contract must provide for authentication under Section 8 and protection and formulation under Chapter VI also obviously entail the operation of Chapter VII (Offences and Penalties). Section 57 does not have 246 any relation to other laws, which may be made by Parliament, the other laws made by Parliament would have to be tested on their own merits. Section 57 is not a provision enabling the making of a law or rather it is actually a limitation or restriction to law, which may be made with respect to use of Aadhaar number. The apprehension expressed by the petitioners is about the wide extension of use of Aadhaar in private spheres is completely misplaced.
267. One of the grounds of attack of the petitioners to Section 57 is that it is disproportionate and does not satisfy the proportionality test as laid down in Privacy Judgment – Puttaswamy case. Before proceeding further, it becomes necessary to look into the proportionality test, its content and parameters. 268. Patanjali Shastri, Chief Justice, as he then was speaking for a Constitution Bench in State of Madras Vs. V.G. Row, AIR 1952 SC 196, while elaborating the expression reasonable restrictions on the exercise of right as occurring in Clause (5) of Article 19 of the 247 Constitution laid down that reasonable restriction should not be disproportionate. Following was observed in Paragraph 15:” 15……..It is important in this context to bear in mind that the test of reasonableness, wherever prescribed, should be applied to each individual statute impugned, and no abstract standard or general pattern, of reasonableness can be laid down as applicable to all cases.
The nature of the right alleged to have been infringed, the underlying purpose of the restrictions imposed, the extent and urgency of the evil sought to be remedied thereby, the disproportion of the imposition, the prevailing conditions at the time, should all enter into the judicial verdict. In evaluating such elusive factors and forming their own conception of what is reasonable, in all the circumstances of a given case, it is inevitable that the social philosophy and the scale of values of the Judges participating in the decision should play an important part, and the limit to their interference with legislative judgment in such cases can only be dictated by their sense of responsibility and selfrestraint and the sobering reflection that the Constitution is meant not only for people of their way of thinking but for all, and that the majority of the elected representatives of the people have, in authorising the imposition of the restrictions, considered them to be reasonable.”
269. A Two Judge Bench of this Court in Om Kumar and Others Vs. Union of India, (2001) 2 SCC 386 248 elaborately considered the concept of proportionality in reference to legislative action. This Court held that ever since the principle of proportionality as noted above applied in India, Jagannadha Rao, J. had referred to judgments of Canadian Supreme Court in R v. Oakes (1986) 26 DLR 2001 and has noticed the three important components of the proportionality test. First, the measures adopted must be carefully designed to achieve the objective in question. They must not be arbitrary, unfair or based on irrational considerations. In short, they must be rationally connected to the objective.
Secondly, the means, must not only be rationally connected to the objective in the first sense, but should impair as little as possible the right to freedom in question. Thirdly, there must be ‘proportionality’ between the effects of the measures and the objective.
270. Again, in Teri Oat Estates (P) Ltd. Vs. U.T. Chandigarh and Others, (2004) 2 SCC 130, Sinha, J. had elaborately reviewed the principle of proportionality. In Paragraph 46, following has been held:249 “46. By proportionality, it is meant that the question whether while regulating exercise of fundamental rights, the appropriate or least restrictive choice of measures has been made by the legislature or the administrator so as to achieve the object of the legislation or the purpose of the administrative order, as the case may be. Under the principle, the court will see that the legislature and the administrative authority “maintain a proper balance between the adverse effects which the legislation or the administrative order may have on the rights, liberties or interests of persons keeping in mind the purpose which they were intended to serve”.
271. The most elaborate consideration of the Doctrine of Proportionality was made in Modern Dental College and Research Centre and Others Vs. State of Madhya Pradesh and Others, (2016) 7 SCC 353. The validity of legislation passed by State of Madhya Pradesh Legislature came for consideration. The Court (speaking through Dr. Justice A.K. Sikri, one of us) held that exercise that is required to be undertaken is the balancing of fundamental right and restrictions imposed, which is known as Doctrine of Proportionality. In Paragraph 60, following has been 250 stated:”
60. ………… Thus, while examining as to whether the impugned provisions of the statute and rules amount to reasonable restrictions and are brought out in the interest of the general public, the exercise that is required to be undertaken is the balancing of fundamental right to carry on occupation on the one hand and the restrictions imposed on the other hand. This is what is known as “doctrine of proportionality”. Jurisprudentially, “proportionality” can be defined as the set of rules determining the necessary and sufficient conditions for limitation of a constitutionally protected right by a law to be constitutionally permissible. According to Aharon Barak (former Chief Justice, Supreme Court of Israel), there are four subcomponents of proportionality which need to be satisfied, a limitation of a constitutional right will be constitutionally permissible if:
(i) it is designated for a proper purpose;
(ii) the measures undertaken to effectuate such a limitation are rationally connected to the fulfilment of that purpose;
(iii) the measures undertaken are necessary in that there are no alternative measures that may similarly achieve that same purpose with a lesser degree of limitation; and finally
(iv) there needs to be a proper relation (“proportionality stricto 251 sensu” or “balancing”) between the importance of achieving the proper purpose and the social importance of preventing the limitation on the constitutional right.” 272. Elaborating the constitutional principles, it was laid down that the Constitution permit constitutional rights to be limited to protect public interests or the rights of others. The conflict between two fundamental aspects, i.e. rights on the one hand and its limitation on the other hand is to be resolved by balancing the two so that they harmoniously coexist with each other. This balancing is to be done keeping in mind the relative social values of each competitive aspects when considered in proper context. What criteria is to be adopted in for a proper balancing has been explained in Paragraphs 63 and 64:”
63. In this direction, the next question that arises is as to what criteria is to be adopted for a proper balance between the two facets viz. the rights and limitations imposed upon it by a statute. Here comes the concept of “proportionality”, which is a proper criterion. To put it pithily, when a law limits a constitutional right, such a limitation is constitutional if it is proportional. The law imposing restrictions will be treated as proportional if it is meant to achieve a proper purpose, and if the measures taken to achieve such a purpose are rationally connected to the purpose, and such measures are necessary. This essence of doctrine of proportionality is beautifully captured by Dickson, C.J. of Canada in R. v. Oakees, (1986) 1 SCR 103 (Can SC), in the following words (at p. 138): “To establish that a limit is reasonable and demonstrably justified in a free and democratic society, two central criteria must be satisfied. First, the objective, which the measures, responsible for a limit on a Charter right or freedom are designed to serve, must be “of” sufficient importance to warrant overriding a constitutional protected right or freedom … Second … the party invoking Section 1 must show that the means chosen are reasonable and demonstrably justified.
This involves “a form of proportionality test…” Although the nature of the proportionality test will vary depending on the circumstances, in each case courts will be required to balance the interests of society with those of individuals and groups. There are, in my view, three important components of a proportionality test. First, the measures adopted must be … rationally connected to the objective. Second, the means … should impair “as little as possible” the right or freedom in question … Third, there must be a proportionality between the effects of the measures which are responsible for limiting the Charter right or freedom, and the objective which has been identified as of “sufficient importance”. The more severe the deleterious effects of a measure, the more important the objective must be if the measure is to be reasonable and demonstrably justified in a free and democratic society.”
64. The exercise which, therefore, is to be taken is to find out as to whether the limitation of constitutional rights is for a purpose that is reasonable and necessary in a democratic society and such an exercise involves the weighing up of competitive values, and ultimately an assessment based on proportionality i.e. balancing of different interests.”
273. The application of Doctrine of Proportionality, while examining validity of the Statute has been accepted in other countries as well. Judgments of the U.S. Supreme Court as well as of United Kingdom, Canadian Supreme Court and Australian Court shows that they have applied proportionality principle while judging a Statute. European Court of Human Rights and other international bodies have recognised the said principle. Privacy judgment in Puttaswamy case has also accepted the proportionality doctrine for judging validity of a Statute. In the threefold test evolved in Privacy Judgment, proportionality is the third 254 component. Dr. D.Y. Chandrachud, J. in Paragraph 310 has stated following in respect of proportionality:”
310. While it intervenes to protect legitimate State interests, the State must nevertheless put into place a robust regime that ensures the fulfilment of a threefold requirement. These three requirements apply to all restraints on privacy (not just informational privacy). They emanate from the procedural and contentbased mandate of Article 21. The first requirement that there must be a law in existence to justify an encroachment on privacy is an express requirement of Article 21. For, no person can be deprived of his life or personal liberty except in accordance with the procedure established by law. The existence of law is an essential requirement. Second, the requirement of a need, in terms of a legitimate State aim, ensures that the nature and content of the law which imposes the restriction falls within the zone of reasonableness mandated by Article 14, which is a guarantee against arbitrary State action.
The pursuit of a legitimate State aim ensures that the law does not suffer from manifest arbitrariness. Legitimacy, as a postulate, involves a value judgment. Judicial review does not reappreciate or second guess the value judgment of the legislature but is for deciding whether the aim which is sought to be pursued suffers from palpable or manifest arbitrariness. The third requirement ensures that the means which are adopted by the legislature are proportional to the object and needs sought to be fulfilled by the law. Proportionality is an essential facet of the guarantee against arbitrary State action because it ensures that the nature and quality of the encroachment on the right is not disproportionate to the purpose of the law.
Hence, the threefold requirement for a valid law arises out of the mutual interdependence between the fundamental guarantees against arbitrariness on the one hand and the protection of life and personal liberty, on the other. The right to privacy, which is an intrinsic part of the right to life and liberty, and the freedoms embodied in Part III is subject to the same restraints which apply to those freedoms.”
274. The third requirement ensures that the means which are adopted by the legislature are proportional to the object and needs sought to be fulfilled by the law. Proportionality is an essential facet of the guarantee against arbitrary state action because it ensures that the nature and quality of the encroachment on the right is not disproportionate to the purpose of the law. 275. European Court of Justice in Michael Schwarz Vs. Stadt Bochum in its judgment dated 17.10.2013, while considering a directive of the European Parliament and on the protection of individuals with regard to the processing of personal data and on the free movement of such data, has applied the proportionality 256 principle. Following was laid down in Paragraph 40:”
40. Fourth, the Court must establish whether the limitations placed on those rights are proportionate to the aims pursued by Regulation No. 2252/2004 and, by extension, to the objective of preventing illegal entry into the European Union. It must therefore be ascertained whether the measures implemented by that regulation are appropriate for attaining those aims and do not go beyond what is necessary to achieve them (see Volker and Markus Schedule and Eifert, paragraph 74).”
276. Court of Justice of the European Union in Digital Rights Ireland Ltd. Vs. Minister for Communications [2015] QBECJ 127 had occasion to consider the validity of Parliament and Council Directive 2006/24/EC on the retention of data generated or processed by them in connection with the provision of publicly available electronic communications services or of public communications networks. Applying the principle of proportionality, it was held that principle of proportionality requires that acts of the EU institutions be appropriate for attaining the legitimate objectives pursued by the legislation at issue and do not exceed the limits of what is appropriate and necessary in order to achieve those objectives. Following was laid down in Paragraph 46:
“46. In summary, Directive 2006/24 is characterised by its functional duality. It is, on the one hand, an entirely traditional Directive which seeks to harmonise national laws that are disparate (recital (5) in the Preamble to Directive 2006/24 states that national laws “vary considerably”) or likely to become so, and was adopted in the interests of the functioning of the internal market and precisely calibrated for that purpose, as the court ruled in Ireland v European Parliament. However, it is also, on the other hand, a Directive which, even in its harmonising function, seeks to establish where appropriate, obligationsin particular data retention obligationswhich constitute, as I shall show later, serious interference with the enjoyment of the fundamental rights guaranteed to European citizens by the Charter, in particular the right to privacy and the right to the protection of personal data.”
277. Another judgment by Court of the Justice of European Union (Grand Chamber) is Tele2 Sverige AB Vs. Postoch telesyrelsen. A directive of European Parliament and of the Council concerning the processing of personal data and the protection of privacy in the electronic communications sector came for consideration. In Paras 95, 96 and 116 following 258 was laid down:” 95. With respect to that last issue, the first sentence of Article 15(1) of Directive 2002/58 provides that Member States may adopt a measure that derogates from the principle of confidentiality of communications and related traffic data where it is a ‘necessary, appropriate and proportionate measure within a democratic society’, in view of the objectives laid down in that provision.
As regards recital 11 of that directive, it states that a measure of that kind must be ‘strictly’ proportionate to the intended purpose. In relation to, in particular, the retention of data, the requirement laid down in the second sentence of Article 15(1) of that directive is that data should be retained ‘for a limited period’ and be ‘justified’ by reference to one of the objectives stated in the first sentence of Article 15(1) of that directive. 96. Due regard to the principle of proportionality also derives from the Court’s settled caselaw to the effect that the protection of the fundamental right to respect for private life at EU level requires that derogations from and limitations on the protection of personal data should apply only in so far as is strictly necessary (judgments of 16 December 2008, Satakunnan Markkinapörssi and Satamedia, C73/ 07,EU:C:2008:727,paragraph 56; of 9 November 2010, Volker und Markus Schecke and Eifert, C92/ 09 and C93/ 09, EU:C:2010:662, paragraph 77; the Digital Rights judgment, paragraph 52, and of 6 October 2015, Schrems, C362/ 14, EU:C:2015:650, paragraph 92).
116 As regards compatibility with the 259 principle of proportionality, national legislation governing the conditions under which the providers of electronic communications services must grant the competent national authorities access to the retained data must ensure, in accordance with what was stated in paragraphs 95 and 96 of this judgment, that such access does not exceed the limits of what is strictly necessary.” 278. The U.S. Supreme Court while considering the said test has repeatedly refused to apply the least intrusive test. Vernonia School District Vs. Wayne Acton, 515 US 646, 132 L.Ed. 2D 564, was a case where a Student Athlete Drug Policy was adopted by the School District, which authorised random urine analysis drug testing of students participating in the District School Athletic Programme. A student was denied participation in Football game since he and his parents had refused to sign the testing consent forms. The Actons filed suit, seeking for a declaratory and injunctive relief from enforcement of the Policy. One of the submissions raised was that Policy is disproportionate since it asks all the athletes to undergo urine analysis, the test is not least intrusive test. Repelling the least intrusive test, 260 following was held:” As to the efficacy of this means for addressing the problem:
It seems to us selfevident that a drug problem largely fueled by the “role model” effect of athletes’ drug use, and of particular danger to athletes, is effectively addressed by making sure that athletes do not use drugs. Respondents argue that a “less intrusive means to the same end” was available, namely, “drug testing on suspicion of drug use.” Brief for Respondents 4546. We have repeatedly refused to declare that only the “least intrusive” search practicable can be reasonable under the Fourth Amendment. Skinner, supra, at 629, n.9, 103 l Ed 2d 639, 109 S Ct. 1402 (collecting cases). 279. To the same effect is another judgment of U.S. Supreme Court in Board of Education of Independent School District Vs. Lindsay Earls, 536 US 822=153 L.Ed.2d. 735.
280. The submission of the respondents that least intrusive test cannot be applied to judge the proportionality of Aadhaar Act has been refuted by petitioners. Petitioners submit that least intrusive test is a test, which was applied in large number of cases and i.e. the test which may ensure that there is a minimal invasion of privacy. It is submitted that 261 the respondents could have switched to a smart card, which itself contain the biometric information of a person. Respondents submitted that least intrusive test has not been approved either in the Modern Dental (supra) or in the Puttaswamy case. We are also of the view that there are several reasons due to which least intrusive test cannot be insisted. For applying the least intrusive test, the Court has to enter comparative analysis of all methods of identification available, which need to be examined with their details and compared. Court has to arrive at finding as to which mode of identity is a least intrusive. We are of the view that comparison of several modes of identity and to come to a decision, which is least intrusive is a matter, which may be better left to the experts to examine. Further, there are no proper pleadings and material with regard to other modes of identification, which could have been adopted by the State, to come to a definite conclusion by this Court.
281. After noticing the parameters of proportionality, we now need to apply proportionality and other tests 262 to find out as to whether Section 57 satisfies the proportionality and other tests. Section 57 begins with the phrase “nothing contained in this Act shall prevent the use of Aadhaar number…..” for establishing the identity of an individual for any purpose. Section 57 reveals following concepts and ides, which can be para phrased in following manner:
( a) Nothing contained in this Act shall prevent the use of Aadhaar number for identifying the identity of an individual for any purpose.
(b) Whether by the State or body corporate or private person.
(c) Pursuant to any law, for the time being in force or any contract to this effect.
282. The basic theme of the Aadhaar Act to implement the Aadhaar programme was for purposes of disbursement of subsidies, benefits or services to individuals entitled for the same. By various notifications issued under Section 7, the Government has made applicable Aadhaar authentication for large number of 263 schemes namely 133 in number. The idea behind Section 57 is that Aadhaar is liberated from the four corners of the Act and it may not be confined to use under Section 7 alone. The Act does not prohibit the use of Aadhaar for any other purpose. Section 57 is thus in a way clarificatory in nature, which enable the use of Aadhaar for any other purposes.
The petitioners have two basic objections. Firstly, they submitted that use of word “any purpose” is unguided and uncontrolled and secondly it can be used by body corporate or persons, pursuant to any law, for the time being in force or any contract to this effect. Puttaswamy judgment has already laid down that any infringement of Privacy right should pass threefold test as noticed above. The first test, which needs to be satisfied for nonintrusion in privacy right is that it should be backed by law. Section 57 cannot be treated as a law, which permit use of Aadhaar number for any purpose.
The law providing for use of Aadhaar for any purpose should be rational and proportional. There has to be some object to be achieved by use of 264 Aadhaar, in a particular case, the legislature has ample power to provide for legislative scheme by an enactment making use of Aadhaar and use of Aadhaar has to be backed by a valid law. In event, it is accepted on the strength of Section 57 that a State or body corporate or person, on the basis of any contract to this effect, are permitted to use Aadhaar it shall be wholly unguided and uncontrolled, which is prone to violate the right of privacy. Section 57 makes use of Aadhaar on two basis.
Firstly, “pursuant to any law, for the time being in force” and secondly “any contract to this effect”. When the legislature uses the phrase “pursuant to any law, for the time being in force”, obviously the word law used in Section 57 is a law other than Section 57 of Aadhaar Act, 2016 and the Regulations framed thereunder. When any law permits user of Aadhaar, its validity is to be tested on the anvil of threefold test as laid down in Puttaswamy case, but permitting use of Aadhaar on any contract to this effect, is clearly in violation of Right of Privacy. A contract entered between two parties, even 265 if one party is a State, cannot be said to be a law.
283. We thus, are of the view that Section 57 in so far as it permits use of Aadhaar on “any contract to this effect” is clearly unconstitutional and deserves to be struck down. We may again clarify that Section 57 has to be read only to mean that it clarifies that nothing contained in Aadhaar Act shall prevent the use of Aadhaar for establishing the identity of an individual for any purpose, in pursuant to any law. Section 57 itself is not a law, which may permit use of Aadhaar for any purpose. There has to be a valid law in existence, which should also pass the threefold test as laid down in Puttaswamy case for making provision for use of Aadhaar. 284. In view of the foregoing discussions, we held that Section 57, to the extent, which permits use of Aadhaar by the State or any body corporate or person, in pursuant to any contract to this effect is unconstitutional and void. Thus, the last phrase in main provision of Section 57, i.e. “or any contract to 266 this effect” is struck down. Issue No. 11 is answered in the following manner:
Ans. 11:Section 57, to the extent, which permits use of Aadhaar by the State or any body corporate or person, in pursuant to any contract to this effect is unconstitutional and void. Thus, the last phrase in main provision of Section 57, i.e. “or any contract to this effect” is struck down.
Issue No.12
Whether Section 59 is void or unconstitutional?
285. Learned counsel for the petitioners have submitted that prior to enactment of Aadhaar Act there was no law and all actions undertaken in pursuance of the executive order dated 28.01.2009 including taking of demographic and biometric information of an individual was not backed by any law violated fundamental right of privacy.
Violation of fundamental right of privacy cannot be cured by any subsequent legislation. It is well settled that Executive 267 actions, which breach fundamental right of a person must have the authority of law to support it. A postconstitutional law or executive act that violates fundamental rights is still born and void ab initio. Further there was no consent, let alone informed consent obtained from individuals at the time of enrolment under the said notification. A validating law must remove the cause of invalidity of previous acts. The cause of invalidity in the present case was the absence of a law governing privacy infringements. However, Section 59 does not create such a legal fiction where the Aadhaar Act is deemed to have been in existence since 2009. It only declares a legal consequence of acts done by Union since 2009, which it cannot do.
No procedural safeguards existed pre2016 and thus, even assuming that Section 59 is validly enacted, it has to be declared unconstitutional for violating Articles 14 and 21. 286. Replying the above submissions, respondents submit that Section 59 is retrospective, saving provision which provides a retrospective effect to the 268 notification dated 28.01.2009 and anything done or action taken by the Central Government under the said Resolution. 287. The expression ‘anything done or any action under the Resolution’ is wide enough to cover all the actions including memorandum of undertaken which UIDAI executed as Department of Central Government. Section 59 seeks to save and continue under the said Act what was done under the executive scheme. The submission that breach of fundamental right cannot be retrospectively cured is incorrect.
The last phrase of Section 59 uses the expression “shall be deemed”, this expression clearly indicates creation of fiction with the object of providing legislative support to the action taken before the Act. That seeks to continue the entire architecture of Aadhaar which established under the Government Resolution dated 28.01.2009. As a result of deeming provision all the actions under the aforesaid scheme shall be deemed to have been done under the Act and not under the aforesaid notification. We may have a look on Section 59 of the 269 Act which provides:
“59. Anything done or any action taken by the Central Government under the Resolution of the Government of India, Planning Commission bearing notification number A43011/ 02/2009Admin. I, dated the 28th January, 2009, or by the Department of Electronics and Information Technology under the Cabinet Secretariat Notification bearing notification number S.O. 2492(E), dated the 12th September, 2015, as the case may be, shall be deemed to have been validly done or taken under this Act.” 288. Justice G.P. Singh in Principles of Statutory Interpretation, 14th Edition, while explaining the legal fiction sum up the Principle in the following words:
“The Legislature is quite competent to create a legal fiction, in other words, to enact a deeming provision for the purpose of assuming existence of a fact which does not really exist provided the declaration of nonexistent facts as existing does not offend the constitution. Although the word ‘deemed’ is usually used, a legal fiction may be enacted without using that word. For instance, the words ‘as if’ can also be used to create a legal fiction. In interpreting a provision creating a legal fiction, the court is to ascertain for what purpose the fiction is created, and after ascertaining this, the Court is to assume all those facts and consequences which are incidental or inevitable corollaries to the giving effect to the fiction. But in so 270 construing the fiction it is not to be extended beyond the purpose for which it is created, or beyond the language of the section by which it is created.”
289. A Constitution Bench judgment of this Court in M/s. West Ramnad Electric Distribution Co. Ltd. vs. The State of Madras and another, AIR 1962 SC 1753, has been heavily relied by the respondents. The Madras Legislature had passed an Act, the Madras Electricity Supply Undertakings (Acquisition) Act, 1949 for supply of electricity in the province of Madras. By an order dated 17.05.1951 appellant undertaking was acquired and possession was directed to be taken. There was challenge to 1949 Act which challenge was upheld by this Court in Rajahmundry Electric Supply Corporation Ltd. v. State of Andhra Pradesh, AIR 1954 SC 251, on the ground that Act was beyond the legislative competence of the Madras Legislature.
The Madras Legislature passed another Act, the Madras Electricity Supply Undertakings (Acquisition) Act, 1949, which also received the Presidential assent. The Act purported to validate the action taken under the 1949 271 Act. A writ petition was filed in Madras High Court challenging the action taken under 1949 Act to continue the possession. The writ petition was dismissed and the matter was taken to this Court. The contention which was raised before this Court has been noticed in paragraph 8 in the following words:
“8….Mr. Nambiar further contends that this notification was invalid for two reasons; it was invalid because it has been issued under the Provisions of an Act which was void as being beyond the legislative competence of the Madras Legislature, and it was void for the additional reason that before it was issued, the Constitution of India had come into force and it offended against the provisions of Art. 31 of the Constitution, and so, Art. 13(2) applied. Section 24 of the Act, no doubt, purported or attempted to validate this notification, but the said attempt has failed because the Act being prospective, s. 24 cannot have retrospective operation. That, in substance, is the first contention raised before us.”
290. Section 24 of the 1949 Act which created a deeming fiction validating the actions taken under the earlier Act has been noticed in paragraph 11 which is to the following effect:
“11. Let us then construe section 24 and decide whether it serves to validate the 272 impugned notification issued by the respondent on the 21st September, 1951. Section 24 reads thus :” Orders made, decisions or directions given, notifications issued, proceedings taken and acts of things done, in relation to any undertaking taken ever, if they would have been validly made, given, issued, taken or done, had the Madras Electricity Supply Undertakings (Acquisition) Act, 1949 (Madras Act XLIII of 1949), and the rules made thereunder been in force on the date on which the said orders, decisions or directions, notifications, proceeding, acts or things, were made, given, issued, taken or done are hereby declared to have been validly made, given, issued, taken or done, as the case may be, except to the extent to which the said orders, decisions, directions, notifications, proceedings, acts or things are repugnant to the provisions of this Acts.””
291. Repelling the submission of counsel for the appellant it was held that Section 24 had been enacted for the purpose of retrospectively validating action taken under the provisions of the earlier Act. Following was held in paragraph 13: 273 “13….If the Act is retrospective in operation and s. 24 has been enacted for the purpose of retrospectively validating actions taken under the provisions of the earlier Act, it must follow by the very retrospective operation of the relevant provisions that at the time when the impugned notification was issued, these provisions were in existence. That is the plain and obvious effect of the retrospective operation of the statute.
Therefore in considering whether Art. 31(1) has been complied with or not, we must assume that before the notification was issued, the relevant provisions of the Act were in existence and so, Art. 31(1) must be held to have been complied with in that sense.” 292. The submission was made that notification issued under the earlier Act contravenes Article 31 which is a fundamental right and cannot be cured by the subsequent law. The contention has been noted in paragraph 15:
15. That takes us to the larger issue raised by Mr. Nambiar in the present appeals. He contends that the power of the legislature to make laws retrospective cannot validly be exercised so as to care the contravention of fundamental rights retrospectively. His contention is that the earlier Act of 1949 being dead and nonexistent, the impugned notification contravened Art. 31(1) and this contravention of a fundamental right cannot be cured by the legislature by passing a subsequent law and making it retrospective. In support of this argument, he has relied on 274 the decision of this Court in Deep Chand v. The State of Uttar Pradesh (1959) Supp. 2 S.C.R. 8.(AIR 1959 SC 648)….”
293. It was held by the Constitution Bench that the Legislature can effectively exercise power of validating action taken under the law which was void for the reason that it contravened fundamental right. In paragraph 16 following has been held: “16….If a law is invalid for the reason that it has been passed by a legislature without legislative competence, and action is taken under its provisions, the said action can be validated by a subsequent law passed by the same legislature after it is clothed with the necessary legislative power.
This position is not disputed. If the legislature can by retrospective legislation cure the invalidity in actions taken in pursuance of laws which were void for want of legislative competence and can validate such action by appropriate provisions, it is difficult to see why the same power cannot be equally effectively exercised by the legislature in validating actions taken under law which are void for the reason that they contravened fundamental rights. As has been pointed out by the majority decision in Deep Chand’s case, the infirmity proceeding from lack of legislative competence as well as the infirmity proceeding from the contravention of fundamental rights lead to the same result and that is that the offending legislation is void and honest.
That being so, if the legislature can validate actions taken under 275 one class of void legislation, there is no reason why it cannot exercise its legislative power to validate actions taken under the other class of void legislation. We are, therefore, not prepared to accept Mr. Nambiar’s contention that where the contravention of fundamental rights is concerned, the legislature cannot pass a law retrospectively validate actions taken under a law which was void because it contravened fundamental rights.”
294. Shri Shyam Divan submits that the above judgment of this Court in M/s. West Ramnad Electric Distribution Co.Ltd. is not applicable. He submits that unlike Section 59 of Aadhaar Act, the provisions in West Ramnad case had no limiting words such as ‘action taken by the Central Government’. Further even under the West Ramnad case principle, the action can be saved would have to be proper under the previous regime. West Ramnad actions were under an earlier statute that was declared ultra vires, which cannot be saved under Section 59 of the Aadhaar Act.
The collection of biometrics from individuals right upto 2016 cannot be described as lawful and intra vires the 2009 notification. If it were ultra vires the 2009 276 notification, Section 59 of the Aadhaar Act cannot validate the action.
295. We have already noticed the ratio of the judgment as stated in paragraph 16 in the judgment in West Ramnad case that even if earlier action which is sought to be validated was ultra vires and violates constitutional right, it could have been very well validated by retrospective statute creating a deeming fiction. We are of the view that ratio laid down in West Ramnad case is fully applicable in the present case.
296. Another Constitution Bench in Bishambhar Nath Kohli and others v. State of Uttar Pradesh and others, AIR 1966 SC 573, had occasion to consider the deeming fiction as contained under Act 31 of 1950. Section 58(3) of Act 31 of 1950 as deeming provision that anything done or action taken in exercise of the power conferred under Ordinance 27 of 1949 is to be deemed to have been done or taken in exercise of the power 277 conferred by or under Act 31 of 1950. In paragraphs 7 and 8 of the judgment following has been laid down:
“7. By Ordinance 27 of 1949 a proceeding commenced under Ordinance 12 of 1949 or anything done or action taken in the exercise of the powers conferred under that Ordinance was to be deemed a proceeding commenced, thing done and action taken under the former Ordinance as if that Ordinance were in force on the date on which the proceeding was commenced, thing was done or action was taken. Section 58(3) of Act 31 of 1950 contained a similar deeming provision that anything done or action taken in exercise of the power conferred under Ordinance 27 of 1949 is to be deemed to have been done or taken in exercise of the power conferred by or under Act 31 of 1950, as if the Act were in force on the day on which such thing was done or action was taken.
8. By this chain of fictions, things done and actions taken under Ordinance 12 of 1949 are to be deemed to have been done or taken in exercise of the powers conferred under Act 31 of 1950, as if that Act we re in force on the day on which such thing was done or action taken. The order passed by the Deputy Custodian under s. 6 of Ordinance 12 of 1949 was, therefore, for the purpose of this proceeding, to be deemed an order made in exercise of the power conferred by Act 31 of 1950 as if that Act were in force on the day on which the order was passed.” 297. The ratio of judgment in West Ramnad(supra) has been repeatedly applied by this Court in several 278 judgments. Reference is made to Hari Singh and others vs. The Military Estate Officer and another, 1972 (2) SCC 239, which was a case rendered by a sevenJudge Constitution Bench. In paragraph 16 following has been held:
“16. The ruling of this Court in West Ramnad Electric Distribution Co. Ltd.(1) case establishes competence of the legislature to make laws retrospective in operation for the purpose of validation of action done under an earlier Act which has been declared by a decision of the court to be invalid. It is to be appreciated that the validation is by virtue of the provisions of the subsequent piece of legislation.” 298. Justice Krishna Iyer, J. in Krishna Chandra Gangopadhyaya and others vs. The Union of India and others, 1975 (2) SCC 302, while considering validation of Act held that the Legislature can retrospectively validate what otherwise was inoperative law or action. In paragraph 25 following has been held: “25. The ratio of West Ramnad (supra) is clear.
The Legislature can retrospectively validate what otherwise was inoperative law or action. Unhappy wording, infelicitous expression or imperfect or inartistic drafting may not necessarily defeat, for that reason alone, the obvious object of the 279 validating law and its retrospective content.”
299. This Court again in ITW Signode India Ltd. vs. Collector of Central Excise, 2004 (3) SCC 48, held that curative statutes by their very nature are intended to operate upon and affect past transaction. In paragraph 61 following has been held:
“61. A statute, it is trite, must be read as a whole. The plenary power of legislation of the Parliament or the State Legislature in relation to the legislative fields specified under Seventh Schedule of the Constitution of India is not disputed. A statutory act may be enacted prospectively or retrospectively. A retrospective effect indisputably can be given in case of curative and validating statute. In fact curative statutes by their very nature are intended to operate upon and affect past transaction having regard to the fact that they operate on conditions already existing. However, the scope of the validating act may vary from case to case.”
300. The argument that an action or provision hit by Article 14 can never be validated was specifically rejected by this Court in The State of Mysore and another vs. d. Achiah Chetty, Etc., (1969) 1 SCC 248, in paragraph 15 following has been held: 280 “15. Mr. S. T. Desai, however, contends that an acquisition hit by Article 14 or anything done previously cannot ever be validated, unless the vice of unreasonable classification is removed and the Validating Act is ineffective for that reason. This argument leads to the logical conclusion that a discrimination arising from selection of one law for action rather than the other, when two procedures are available, can never be righted by removing retrospectively one of the competing laws from the field.
This is a wrong assumption….”
301. A statute creates a legal fiction to achieve a legislative purpose. We may refer to the celebrated judgment of Lord Asquith in East End Dwelling Co.Ltd. And Finsury Borough Council, 1952 AC 109, following is the enunciation of Lord Asquith: “If you are bidden to treat an imaginary state of affairs as real, you must surely, unless prohibited from doing so, also imagine as real the consequences and incidents which, if the putative state of affairs had in fact existed, must inevitably have flowed from or accompanied it… The statute says that you must imagine a certain state of affairs; it does not say that having done so, you must cause or permit your imagination to boggle when it comes to the inevitable corollaries of that state of affairs.”
302. Legislature has often created legal fiction to save several actions which had happened prior to 281 enactment. Reference is made to judgment of this Court in Nar Bahadur Bhandari and another vs. State of sikkim and others, (1998) 5 SCC 39. In the above case deeming fiction was created by Section 30 of Prevention of Corruption Act, 1988. Section 30 provides that any action taken or purported to have been done or taken under or in pursuance of the Acts so repeated shall be deemed to have been done or taken under 1988 Act. Following was stated in paragraph 10:
“10….In the present case, the Act of 1988 is the repealing Act. Subsec. (2) of Section 30 reads as follows: “30(2) Notwithstanding such repeal, but without prejudice to the application of section 6 of the General Clauses Act 1897 (10 of 1897), anything done or any action taken or purported to have been done or taken under or in pursuance of the Acts so repealed shall, in so far as it is not inconsistent with the provisions of this Act, be deemed to have been done or taken under or in pursuance of the corresponding provision of this Act.”
12. The said Subsection while on the one hand ensures that the application of Section 6 of the General Clauses Act is not prejudiced, on the other it expresses a different intention as contemplated by the said Section 6. The last part of the above 282 Subsection introduces a legal fiction whereby anything done or action taken under or in pursuance of the Act of 1947 shall be deemed to have been done or taken under or in pursuance of corresponding provisions of the Act of 1988. That is, the fiction is to the effect that the Act of 1988 had come into force when such thing was done or action was taken.”
303. An elaborate consideration on deeming fiction was made by threeJudge Bench of this Court in State of Karnataka vs. State of Tamil Nadu and others, (2017) 3 SCC 362, one of us, Justice Dipak Misra, as he then was, speaking for the Court in paragraphs 72 to 74: “72. The second limb of submission of Mr. Rohatgi as regards the maintainability pertains to the language employed Under Section 6(2) of the 1956 Act, which reads as follows:
“6(2) The decision of the Tribunal, after its publication in the Official Gazette by the Central Government under Subsection (1), shall have the same force as an order or decree of the Supreme Court.” 73. Relying on Section 6(2), which was introduced by way of Amendment Act 2002 (Act No. 14 of 2002) that came into force from 6.8.2002, it is submitted by Mr. Rohatgi that the jurisdiction of this Court is ousted as it cannot sit over in appeal on its own decree. The said submission is seriously resisted by Mr. Nariman and Mr. Naphade, 283 learned senior Counsel contending that the said provision, if it is to be interpreted to exclude the jurisdiction of the Supreme Court of India, it has to be supported by a constitutional amendment adding at the end of Article 136(2) the words “or to any determination of any tribunal constituted under the law made by Parliament Under Article 262(2)” and, in such a situation, in all possibility such an amendment to the Constitution may be ultra vires affecting the power of judicial review which is a part of basic feature of the Constitution.
Learned senior Counsel for the Respondent has drawn a distinction between the conferment and the exclusion of the power of the Supreme Court of India by the original Constitution and any exclusion by the constitutional amendment. Be that as it may, the said aspect need not be adverted to, as we are only required to interpret Section 6(2) as it exists today on the statute book. The said provision has been inserted to provide teeth to the decision of the tribunal after its publication in the official gazette by the Central Government and this has been done keeping in view the Sarkaria Commission’s Report on CentreState relations (1980). The relevant extract of the Sarkaria Commission’s Report reads as follows:
17.4.19 The Act was amended in 1980 and Section 6A was inserted. This Section provides for framing a scheme for giving effect to a Tribunal’s award. The scheme, inter alia provides for the establishment of the authority, its term of office and other condition of service, etc. but the mere creation of such an agency will not be able to ensure implementation of a Tribunal’s award. Any agency set up Under Section 6A 284 cannot really function without the cooperation of the States concerned.
Further, to make a Tribunal’s award binding and effectively enforceable, it should have the same force and sanction behind it as an order or decree of the Supreme Court. We recommend that the Act should be suitably amended for this purpose. 17.6.05 The InterState Water Disputes Act, 1956 should be amended so that a Tribunal’s Award has the same force and sanction behind it as an order or decree of the Supreme Court to make a Tribunal’s award really binding. 74….Parliament has intentionally used the words from which it can be construed that a legal fiction is meant to serve the purpose for which the fiction has been created and not intended to travel beyond it. The purpose is to have the binding effect of the tribunal’s award and the effectiveness of enforceability. Thus, it has to be narrowly construed regard being had to the purpose it is meant to serve.
304. In paragraphs 75, 76 and 77 following has been laid down: “75. In this context, we may usefully refer to the Principles of Statutory Interpretation, 14th Edition by G.P. Singh. The learned author has expressed thus: “In interpreting a provision creating a legal fiction, the court is to ascertain for what purpose the 285 fiction is created1, and after ascertaining this, the Court is to assume all those facts and consequences which are incidental or inevitable corollaries to the giving effect to the fiction. But in so construing the fiction it is not be extended beyond the purpose for which is created, or beyond the language of the Section by which it is created4. It cannot also be extended by importing another fiction5. The principles stated above are ‘wellsettled’. A legal fiction may also be interpreted narrowly to make the statute workable.”
76. In Aneeta Hada v. Godfather Travels and Tours, (2012) 5 SCC 661, a threeJudge Bench has ruled thus: “37. In State of T.N. v. Arooran Sugars Ltd., (1997) 1 SCC 326 the Constitution Bench, while dealing with the deeming provision in a statute, ruled that the role of a provision in a statute creating legal fiction is well settled. Reference was made to Chief Inspector of Mines v. Karam Chand Thapar, AIR 1961 SC 838, J.K. Cotton Spg. and Wvg. Mills Ltd. v. Union of India, 1987 Supp. SCC 350, M. Venugopal v. LIC, (1994) 2 SCC 323 and Harish Tandon v. ADM, Allahabad, (1995) 1 SCC 537 and eventually, it was held that when a statute creates a legal fiction saying that something shall be deemed to have been done which in fact and truth has not been done, the Court has to examine and ascertain as to for what purpose and between which persons such a statutory fiction is 286 to be resorted to and thereafter, the courts have to give full effect to such a statutory fiction and it has to be carried to its logical conclusion.”
38. From the aforesaid pronouncements, the principle that can be culled out is that it is the bounden duty of the court to ascertain for what purpose the legal fiction has been created. It is also the duty of the court to imagine the fiction with all real consequences and instances unless prohibited from doing so. That apart, the use of the term “deemed” has to be read in its context and further, the fullest logical purpose and import are to be understood. It is because in modern legislation, the term “deemed” has been used for manifold purposes. The object of the legislature has to be kept in mind.”
77. In Hari Ram, the Court has held that in interpreting the provision creating a legal fiction, the court is to ascertain for what purpose the fiction is created and after ascertaining the same, the court is to assume all those facts and consequences which are incidental or inevitable corollaries for giving effect to the fiction.”
305. Applying the ratio of this Court as noticed above, it is clear that Parliamentary legislative intent of Section 59 is to save all actions taken by Central Government under the notification dated 287 28.01.2009 and notification dated 12.09.2015 deeming the same to have been validly done under the Aadhaar Act by creating a legal fiction. The intention to save all actions taken under the aforesaid two notifications and treat them to have done under that Act is clear, it is the purpose and object of Section 59. Section 59 has to be interpreted to give meaning to the legislative intent to hold otherwise shall defeat the purpose of Section 59. As observed, Legislature by legislative device can cover actions taken earlier while creating any legal fiction which has actually been done by Section 59.
306. There is one more submission of the petitioners to be considered. Petitioner’s case is that there was no consent or informed consent obtained from individuals for enrolment made consequent to notification dated 28.01.2009, the notification dated 28.01.2009 and the scheme thereafter does not clearly indicate that the enrolment for Aadhaar was voluntary. This Court has issued an interim order directing the enrolment be treated as voluntary, hence, it cannot be 288 accepted that those got enrolled after 28.01.2009 did not give consent. The individual provided demographic information and gave biometric information and also signed the enrolment form. The residents after the enrolment were required to confirm that information contained were provided by them and are of his own true and correct. On sign slip, he was required to sign or put his thumb impression themselves. It is on the record that more than 100 crores enrolment were completed prior to enforcement of Aadhaar Act 2016.
On the basis of Aadhaar Act large number of persons must have received benefits of subsidies and services, thus, the enrolments prior to enforcement of Act, 2016 cannot be declared illegal and void. In view of the aforementioned discussion, we answer the Issue No.12 in the following manner; Ans.12:Section 59 has validated all actions taken by the Central Government under the notifications dated 28.01.2009 and 289 12.09.2009 and all actions shall be deemed to have been taken under the Aadhaar Act.
Issue No. 13
Whether Collecting the identity information of children between 5 to 18 years is unconstitutional?
307. Section 5 of the Act provides that the Authority shall take special measures to issue Aadhaar number to women, children, senior citizens, persons with disability, unskilled and unorganised workers, nomadic tribes or to such other persons who do not have any permanent dwelling house and such other categories of individuals as may be specified by regulations. Section 5 contemplates special measures for issuance of Aadhaar number to children.
The Aadhaar (Enrolment and Update) Regulations, 2016 contains some special measures. One of the special measures is Regulation 5, which provides for information required for enrolment of children below five years of age. Regulation 5 is as follows:5. Information required for enrolment of 290 children below five years of age. –
(1) For children below the five years of age, the following demographic and biometric information shall be collected:
(a) Name
(b) Date of Birth
(c) Gender
(d) Enrolment ID or Aadhaar number of any one parent, preferably that of the mother in the event both parents are alive, or guardian. The Aadhaar number or EID of such parent or guardian is mandatory, and a field for relationship will also be recorded.
(e) The address of such child which is the same as that of the linked parent / guardian.
(f) Facial image of the child shall be captured. The biometric information of any one parent / guardian shall be captured or authenticated during the enrolment.
(2) The Proof of Relationship (PoR) document as listed in schedule II for establishing the relationship between the linked parent/guardian and the child shall be collected at the time of enrolment. Only those children can be enrolled based on the relationship document (PoR), whose names are recorded in the relationship document.
308. For children below five, no core biometric 291 informations are captured and only biometric information of any one parent/guardian is captured. The objection raised by petitioners is with regard to children between 5 to 18 years on the ground that they being minors, parental consent is not taken. We have noted above that for Aadhaar enrolment, for verification of information consent is obtained from the person submitting for enrolment. Thus, the enrolment for Aadhaar number is on consent basis. Although, it is different matter that for the purpose of obtaining any benefit or service, a person is obliged to enrol for Aadhaar. The petitioners are right in their submissions that for enrolment of a children between 5 and 18 years, there has to be consent of their parents or guardian because they themselves are unable to give any valid consent for enrolment.
We, thus, have to read parental consent in Regulation 4 in so far as children of 5 to 18 years are concerned so that the provision in reference to children between 5 to 18 years may not become unconstitutional. We thus answer Question No. 13 in 292 following manner:Ans. 13:Parental consent for providing biometric information under Regulation 3 & demographic information under Regulation 4 has to be read for enrolment of children between 5 to 18 years to upheld the constitutionality of Regulations 3 & 4 of Aadhaar (Enrolment and Update) Regulations, 2016.
Issue No.14
Whether Rule 9 as amended by the Prevention of MoneyLaundering (Second Amendment) Rules 2017 is unconstitutional?
309. For answering the above issue we need to advert to the objects and scheme of the Prevention of MoneyLaundering Act, 2002(PMLA, 2002).
The scheme as delineated by the Prevention of MoneyLaundering (Maintenance of Records) Rules, 2005 also need to be looked into before coming to the Second Amendment Rules, 2017. The PMLA, 2002 has been enacted to prevent moneylaundering and to provide for confiscation of property derived from, or involved in, 293 moneylaundering and for matters connected therewith or incidental thereto. The Act has long Preamble entire of which needs to be noted, which is as follows:
“An Act to prevent moneylaundering and to provide for confiscation of property derived from, or involved in, moneylaundering and for matters connected therewith or incidental thereto.
WHEREAS the Political Declaration and Global Programme of Action, annexed to the resolution S17/ 2 was adopted by the General Assembly of the United Nations at its seventeenth special session on the twentythird day of February, 1990;
AND WHEREAS the Political Declaration adopted by the Special Session of the United Nations General Assembly held on 8th to 10th June, 1998 calls upon the Member States to adopt national moneylaundering legislation and programme;
AND WHEREAS it is considered necessary to implement the aforesaid resolution and the Declaration; 310. Two international declarations have been specifically mentioned in the Preamble which pave the way for the enactment. The resolution adopted by the General Assembly of the United Nations on 23rd February, 1990 contained the recommendations on 294 moneylaundering of the Financial Action Task Force aforesaid.
The Political Declaration and Action Plan against moneylaundering by the United Nations General Assembly held on 10.06.1998 which called upon the States Members of the United Nations to adopt its declaration to the following effect:
“Political Declaration and Action Plan against Money Laundering
adopted at the Twentieth Special Session of the United Nations General Assembly devoted to “countering the world drug problem together”
New Your, 10 June 1998(excerpts)
“We, the States Members of the United Nations,
… … … …
15. Undertake to make special efforts against the laundering of money linked to drug trafficking and, in that context, emphasize the importance of strengthening international, regional and subregional cooperation, and recommend that States that have not yet done so adopt by the year 2003 national moneylaundering legislation and programmes in accordance with relevant provisions of the United Nations Convention against Illicit Traffic in Narcotic Drugs and Psychotropic Substances of 1988, as well as the measures for countering moneylaundering, adopted at the present session; … … … …
“COUNTERING MONEYLAUNDERING”
The General Assembly, … … … … Emphasizing the enormous efforts of a number of States to draw up and apply domestic legislation that identifies the activity of moneylaundering as a criminal offence, Realizing the importance of progress being made by all States in conforming to the relevant recommendations and the need for States to participate actively in international and regional initiatives designed to promote and strengthen the implementation of effective measures against moneylaundering,
1. Strongly condemns the laundering of money derived from illicit drug trafficking and other serious crimes, as well as the use of the financial systems of States for that purpose;
2. Urges all States to implement the provisions against moneylaundering that are contained in the United Nations Convention against Illicit Trafficking in Narcotic Drugs and Psychotropic Substances of 1988 and the other relevant international instruments on moneylaundering, in accordance with fundamental constitutional principles, by applying the following principles:
(a) Establishment of a legislative framework to criminalize the laundering of money derived from serious crimes in order to provide for the prevention, detection, investigation and prosecution of the crime of moneylaundering through, inter alia:
(i) Identification, freezing, seizure and confiscation of the proceeds of crime;
(ii) International cooperation; and mutual legal assistance in cases involving moneylaundering;
(iii) Inclusion of the crime of moneylaundering in mutual legal assistance agreements for the purpose of ensuring judicial assistance in investigations, court cases or judicial proceedings relating to that crime;
(b) Establishment of an effective financial and regulatory regime to deny criminals and their illicit funds access to national and international financial systems, thus preserving the integrity of financial systems worldwide and ensuring compliance with laws and other regulations against moneylaundering through:
(i) Customer identification and verification requirements applying the principle of “know your customer”, in order to have available for competent authorities the necessary information on the identity of clients and the financial movements that they carry out;
(ii) Financial recordkeeping;
(iii) Mandatory reporting of suspicious activity;
(iv) Removal of bank secrecy impediments to efforts directed at preventing, investigating and punishing moneylaundering;
(v) Other relevant measures;
(c) Implementation of law enforcement measures to provide tools for, inter alia:
(i) Effective detection, investigation, prosecution and conviction of criminals engaging in moneylaundering activity;
(ii) Extradition procedures;
(iii) Informationsharing mechanisms;”
311. The modern world is more focused on economic growth. Every nation tries to march forward in achieving the rapid economic growth. Economics is factor which not only plays a major role in the future of nation but also in all human organisations. Most of the individuals also aspire for their financial well being but for the financial system and working of economic, road blocks are felt both by the nations and human organisations. The siphoning away of huge volumes of money from normal economic growth poses a real danger to the economics and affects the stability of the global market which also empowers corruption organised crime.
Proceeds of moneylaundering are disguised to acquire properties and other assets or to make investments. At some stage moneylaundering involves conversion process with the objective to give the appearance that the money has a legitimate source. The banking and financial secrecy is another bottleneck for countries who genuinely want to counter moneylaundering. It is inherent in the activity of 298 moneylaundering to keep the entire process secret. The Parliament with the objectives outlined in the international declaration enacted the PMLA Act. Para 1 of the Statement of Objects and Reasons of Act is stated as follows:
“STATEMENT of OBJECTS AND REASONS
It is being realised, world over, that moneylaundering poses a serious threat not only to the financial systems of countries, but also to their integrity and sovereignty. Some of the initiatives taken by the international community to obviate such threat are outlined below:-
(a) the United Nations Convention Against Illicit Traffic in Narcotic Drugs and Psychotropic Substances, to which India is a party, calls for prevention of laundering of proceeds of drug crimes and other connected activities and confiscation of proceeds derived from such offence.
(b) the Basle Statement of Principles, enunciated in 1989, outlined basic policies and procedures that banks should follow in order to assist the law enforcement agencies in tackling the problem of moneylaundering.
(c) the Financial Action Task Force established at the summit of seven major industrial nations, held in Paris from 14th to 16th July, 1989, to examine the problem of moneylaundering has made forty recommendations, which provide the foundation material for comprehensive legislation to combat the problem of moneylaundering. The 299 recommendations were classified under various heads. Some of the important heads are-
(i) declaration of laundering of monies carried through serious crimes a criminal offence;
(ii) to work out modalities of disclosure by financial institutions regarding reportable transactions;
(iii) confiscation of the proceeds of crime;
(iv) declaring moneylaundering to be an extraditable offence; and
(v) promoting international cooperation in investigation of moneylaundering.
(d) the Political Declaration and Global Programme of Action adopted by United Nations General Assembly by its Resolution No. S17/ 2 of 23rd February, 1990, inter alia, calls upon the member States to develop mechanism to prevent financial institutions from being used for laundering of drug related money and enactment of legislation to prevent such laundering.
(e) the United Nations in the Special Session on countering World Drug Problem Together concluded on the 8th to the 10th June, 1998 has made another declaration regarding the need to combat moneylaundering. India is a signatory to this declaration. ………………………………”
312. Paragraph two of the Statement of Objects and Reasons noticed the legislative process which was 300 initiated by introducing the Prevention of MoneyLaundering Bill, 1998 which was introduced in the Lok Sabha. The Bill was referred to the Standing Committee on Finance, which submitted its report on 04.03.1999 to the Lok Sabha. Various recommendations of the Standing Committee were accepted by the Central Government and made provisions of the said recommendations in the Bill.
Thereafter, the Bill was presented in the Parliament which after receiving the assent of the President published in the Gazette on 01.07.2005. Act, 2002 has been amended by various Parliamentary Acts. By amendments made in the year 2013 by Act 2 of 2013, the Legislature has attempted to keep the pace with the other countries of the world by making more stringent provision to prevent moneylaundering which is the root as well as the result of the black money economy. Moneylaundering is defined under Section 3 which is to the following effect:
“3. Offence of moneyLaundering. Whosoever directly or indirectly attempts to indulge or knowingly assists or knowingly is a party or is actually involved in any process or activity connected proceeds of crime including its concealment, possession, 301 acquisition or use and projecting or claiming it as untainted property shall be guilty of offence of moneylaundering.”
313. Section 2 (ha) defines client and Section 2(wa) defines reporting entity which are as follows; “2.(ha) “client” means a person who is engaged in a financial transaction or activity with a reporting entity and includes a person on whose behalf the person who engaged in the transaction or activity, is acting; (wa) “reporting entity” means a banking company, financial institution, intermediary or a person carrying on a designated business or profession;”
314. Section 12 lays down various obligations on reporting entity to maintain records. Section 12(1)(c) reads: “Section 12. Reporting entity to maintain records.( l) Every reporting entity shall… … … … (c) verify the identity of its clients in such manner and subject to such conditions, as may be prescribed; ” 302 315. The Central Government in exercise of its rule making power has made Rules, namely, the Prevention of Moneylaundering (Maintenance of Records) Rules, 2005 (hereinafter referred to as “Rules, 2005). In the present case challenge is to Rule 9 as amended by Second Amendment Rules, 2017. We may thus notice the amendments made in Rule 9 by Second Amendment Rules, 2017. By Second Amendment Rules, 2017, subRule (4) to subRule (9) of Rule 9 were substituted in following manner:
“(b) in rule 9, for subrule (4) to subrule (9), the following subrules shall be substituted, namely:-
“(4) Where the client is an individual, who is eligible to be enrolled for an Aadhaar number, he shall for the purpose of subrule (1) submit to the reporting entity,-
(a) the Aadhaar number issued by the Unique Identification Authority of India; and
(b) the Permanent Account Number or Form No. 60 as defined in Incometax Rules, 1962, and such other documents including in respect of the nature of business and financial status of the client as may be required by the reporting entity: 303 Provided that where an Aadhaar number has not been assigned to a client, the client shall furnish proof of application of enrolment for Aadhaar and in case the Permanent Account Number is not submitted, one certified copy of an ‘officially valid document’ shall be submitted. Provided further that photograph need not be submitted by a client falling under clause (b) of subrule (1).
(4A) Where the client is an individual, who is not eligible to be enrolled for an Aadhaar number, he shall for the purpose of subrule (1), submit to the reporting entity, the Permanent Account Number or Form No. 60 as defined in the Incometax Rules, 1962: Provided that if the client does not submit the Permanent Account Number, he shall submit one certified copy of an ‘officially valid document’ containing details of his identity and address, one recent photograph and such other documents including in respect of the nature or business and financial status of the client as may be required by the reporting entity.
(5) Notwithstanding anything contained in subrules (4) and (4A), an individual who desires to open a small account in a banking company may be allowed to open such an account on production of a selfattested photograph and affixation of signature or thumb print, as the case may be, on the form for opening the account: Provided that( i) the designated officer of the banking company, while opening the 304 small account, certifies under his signature that the person opening the account has affixed his signature or thump print, as the case may be, in his presence;
(ii) the small account shall be opened only at Core Banking Solution linked banking company branches or in a branch where it is possible to manually monitor and ensure that foreign remittances are not credited to a small account and that the stipulated limits on monthly and annual aggregate of transactions and balance in such accounts are not breached, before a transaction is allowed to take place;
(iii) the small account shall remain operational initially for a period of twelve months, and thereafter for a further period of twelve months if the holder of such an account provides evidence before the banking company of having applied for any of the officially valid documents within twelve months of the opening of the said account, with the entire relaxation provisions to be reviewed in respect of the said account after twentyfour months;
(iv) the small account shall be monitored and when there is suspicion of money laundering or financing of terrorism or other high risk scenarios, the identity of client shall be established through the production of officially valid documents, as referred to in subrule (4) and the Aadhaar number of the client or where an Aadhaar number has 305 not been assigned to the client, through the production of proof of application towards enrolment for Aadhaar along with an officially valid document; Provided further that if the client is not eligible to be enrolled for an Aadhaar number, the identity of client shall be established through the production of an officially valid document;
(v) the foreign remittance shall not be allowed to be credited into the small account unless the identity of the client is fully established through the production of officially valid documents, as referred to in sub rule (4) and the Aadhaar number of the client or where an Aadhaar number has not been assigned to the client, through the production of proof of application towards enrolment for Aadhaar along with an officially valid document: Provided that if the client is not eligible to be enrolled for the Aadhaar number, the identity of client shall be established through the production of an officially valid document.
(6) Where the client is a company, it shall for the purposes of subrule (1), submit to the reporting entity the certified copies of the following documents:-
(i) Certificate of incorporation;
(ii) Memorandum and Articles of Association; 306
(iii) A resolution from the Board of Directors and power of attorney granted to its managers, officers or employees to transact on its behalf;
(iv) (a) Aadhaar numbers; and
(b) Permanent Account Numbers or Form 60 as defined in the Incometax Rules, 1962. issued to managers, officers or employees holding an attorney to transact on the company’s behalf or where an Aadhaar number has not been assigned, proof of application towards enrolment for Aadhaar and in case Permanent Account Number is not submitted an officially valid document shall be submitted: Provided that for the purpose of this clause if the managers, officers or employees holding an attorney to transact on the company’s behalf are not eligible to be enrolled for Aadhaar number and do not submit the Permanent Account Number, certified copy of an officially valid document shall be submitted.
(7) Where the client is a partnership firm, it shall, for the purposes of subrule (1), submit to the reporting entity the certified copies of the following documents:- (i) registration certificate; (ii) partnership deed; and (iii) (a) Aadhaar number; and (b) Permanent Account Number or Form 60 as defined in the Incometax Rules, 1962. 307 issued to the person holding an attorney to transact on its behalf or where an Aadhaar number has not been assigned, proof of application towards enrolment for Aadhaar and in case Permanent Account Number is not submitted an officially valid document shall be submitted: Provided that for the purpose of this clause, if the person holding an attorney to transact on the company’s behalf is not eligible to be enrolled for Aadhaar number and does not submit the Permanent Account Number, certified copy of an officially valid document shall be submitted.
(8) Where the client is a trust, it shall, for the purposes of subrule (1) submit to the reporting entity the certified copies of the following documents:-
(i) registration certificate; (ii) trust deed; and (iii) (a) Aadhaar number; and
(b) Permanent Account Number or Form 60 as defined in the Incometax Rules, 1962, issued to the person holding an attorney to transact on its behalf or where Aadhaar number has not been assigned, proof of application towards enrolment for Aadhaar and in case Permanent Account Number is not submitted an officially valid document shall be submitted: Provided that for the purpose of this clause if the person holding an attorney to transact on the 308 company’s behalf is not eligible to be enrolled for Aadhaar number and does not submit the Permanent Account Number, certified copy of an officially valid document shall be submitted.
(9) Where the client is an unincorporated association or a body of individuals, it shall submit to the reporting entity the certified copies of the following documents:-
(i) resolution of the managing body of such association or body of individuals;
(ii) power of attorney granted to him to transact on its behalf;
(iii) (a) the Aadhaar number; and
(b) Permanent Account Number or Form 60 as defined in the Incometax Rules, 1962, issued to the person holding an attorney to transact on its behalf or where Aadhaar number has not been assigned, proof of application towards enrolment for Aadhaar and in case the Permanent Account Number is not submitted an officially valid document shall be submitted; and
(iv) such information as may be required by the reporting entity to collectively establish the legal existence of such an association or body of individuals: Provided that for the purpose of this clause if the person holding an attorney to transact on the company’s behalf is not eligible to be enrolled for Aadhaar number and does not 309 submit the Permanent Account Number, certified copy of an officially valid document shall be submitted.”
(c) after subrule
(14), the following subrules shall be inserted, namely,-
“(15) Any reporting entity, at the time of receipt of the Aadhaar number under provisions of this rule, shall carry out authentication using either eKYC authentication facility or Yes/No authentication facility provided by Unique Identification Authority of India.
(16) In case the client referred to in subrules (4) to (9) of rule 9 is not a resident or is a resident in the States of Jammu and Kashmir, Assam or Maghalaya and does not submit the Permanent Account Number, the client shall submit to the reporting entity one certified copy of officially valid document containing details of his identity and address, one recent photograph and such other document including in respect of the nature of business and financial status of the client as may be required by the reporting entity. (17) (a) In case the client, eligible to be enrolled for Aadhaar and obtain a Permanent Account Number, referred to in subrules (4) to (9) of rule 9 does not submit the Aadhaar number or the Permanent Account Number at the time of commencement of an account based relationship with a reporting entity, the client shall submit the same within a period of six months 310 from the date of the commencement of the account based relationship:
Provided that the clients, eligible to be enrolled for Aadhaar and obtain the Permanent Account Number, already having an account based relationship with reporting entities prior to date of this notification, the client shall submit the Aadhaar number and Permanent Account Number by 31st December, 2017.
(b) As per regulation 12 of the Aadhaar (Enrolment and Update) Regulations, 2016, the local authorities in the State Governments or Unionterritory Administrations have become or are in the process of becoming UIDAI Registrars for Aadhaar enrolment and are organising special Aadhaar enrolment camps at convenient locations for providing enrolment facilities in consultation with UIDAI and any individual desirous of commencing an account based relationship as provided in this rule, who does not possess the Aadhaar number or has not yet enrolled for Aadhaar, may also visit such special Aadhaar enrolment camps for Aadhaar enrolment or any of the Aadhaar enrolment centres in the vicinity with existing registrars of UIDAI.
(c) In case the client fails to submit the Aadhaar number and Permanent Account Number within the aforesaid six months period, the said account shall cease to be operational till the time the Aadhaar number and Permanent Account Number is submitted by the client: Provided that in case client already having an account based relationship with reporting entities prior to date of this notification fails to submit the Aadhaar number and Permanent Account Number by 31st December, 2017, the said account shall cease to be operational till the time the Aadhaar number and Permanent Account Number is submitted by the client.
(18) In case the identity information relating to the Aadhaar number or Permanent Account Number submitted by the client referred to in subrules (4) to (9) of rule 9 does not have current address of the client, the client shall submit an officially valid document to the reporting entity.”
316. The challenge to Second Amendment Rules, 2017 is on the ground that it violate Articles 14, 19(1)(g), 21 and 300A of the Constitution of India; Sections 3, 7 and 51 of the Aadhaar Act and also ultra vires to the provisions of PMLA Act, 2002.
317. Elaborating his submissions Shri Arvind P. Datar learned senior counsel submits that Second Amendment Rules violate Article 14 and 21 since persons choosing 312 not to enrol for Aadhaar number cannot operate bank account and valid explanation has to be given as to why all banks have to be authenticated.
318. Violative of Article 19(1)(g) because the Rules refer to companies, firms, trusts, etc. whereas Aadhaar Act is only to establish identity of individuals. Violative of Article 300A since even temporary deprivation can only be done by primary legislation. The Second Amendment Rules do not pass proportionality test. No proper purpose has been established. No explanation has been given that the measures undertaken to such are rationale and connected to the fulfillment of the purpose and there are no alternative measures with a lesser degree of legislation. When the banks have already verified all accounts as per eKYC norms, it is completely arbitrary to make permanent linking/seeding of all Aadhaar numbers with the bank accounts. Second Amendment Rules fail to satisfy the proportionality test, are irrational, and manifestly arbitrary.
319. Shri Tushar Mehta, learned Additional Solicitor General refuting the submission, submits that Second Amendment Rules carry on the object of 2002, Act. The verification of bank account by way of Aadhaar is done for the reason that often bank accounts are opened in either fictitious names or in the name of wrong persons on the basis of forged identity documents and financial crimes are committed. It is seen that accommodation entries are mostly provided through the banking channels by bogus companies to convert black money into white. Benami transactions routinely take place through banking channels. All of the above, can to a large extent be checked by verifying Aadhaar with bank accounts to ensure that the account belongs to the person who claims to be the account holder and that he or she is a genuine person. Verification of bank account with Aadhaar also ensures that the direct benefit transfer of subsidies reach the Aadhaar verified bank account and is not diverted to some other account. Shell companies are often used to open bank accounts to hold unaccounted money of other entities under fictitious identities which will also be curbed once Aadhaar verification is initiated.
320. Now, we come to the respective submissions of the parties. A perusal of the Second Amendment Rules, 2017 indicates that the State has sought to make the provisions of PMLA more robust and ensure that the ultimate object of the Act is achieved. Aadhaar Act, 2016 having been enacted with effect from 01.07.2016, it was decided to get the accounts verified by Aadhaar. Amended Rules help all concerned to detect fictitious, ghost and benami accounts.
The object of the PMLA and the definition of beneficial owner Act seeks to traverse behind the corporate veil of shell companies and spurious Directors in order to ascertain the real natural persons controlling the accounts in the reporting entities. The Amendment Rules applicable to reporting entities and the legitimate aim sought to be achieved by the State that is conclusive identification of a natural person or the beneficial owner. The statutory rules cast an obligation on all account holders to get their identity verified by Aadhaar mechanism and those who are already holding account in the reporting entity they are required to submit the Aadhaar number or proof of their applied Aadhaar identity. When a statute puts obligation on account holder to get identity verification in a particular manner a person chose not to obtain Aadhaar number cannot complain his disentitlement of operating his account.
The submission of the petitioner that there is no valid explanation as to why all bank accounts have to be authenticated also cannot be accepted. Aadhaar provides a mechanism truly identifies an account holder, which eliminates fraudulent accounts existed of nonexisted persons and in ghost names. The object of inserting the Rule is to make it possible to weed out fake and duplicate PANs and false bank accounts. The Second Amendment Rules are step in direction to cure the menace of fake bank accounts held by the shell companies in the name of dummy directors, money laundering, terror financing etc. It is relevant to notice that Aadhaar number is required to be given at the time of opening of the account based relationship and not for every transaction conducted by an account holder of the bank.
Those who have already existing accounts are required to submit only once their Aadhaar number for verification. The requirement of Aadhaar number being given only for once is not any cumbersome or undue burden on an account holder. The object of the Second Amendment Rules is towards the legitimate aim of the State and having nexus with the object sought to be achieved by the enactment. The submission of Aadhaar number only once by an account holder is a proportionate measure. We have already referred to judgments where doctrine of proportionality has been expounded. While adjudging a statutory provision from the angle of the proportionality the Court has to examine as to whether statutory measure contained in statutory provision is not excessive as against the object which seeks to achieve.
The legislature has margin of discretion while providing for one or other measures to achieve an object. Unless the measures foully unreasonable and disproportionate, court doesnot normally substitutes its opinion. On the basis of Rule 9(17)(c), petitioner contends that in the event account holder fails to submit the Aadhaar number and PAN within a period as mentioned in the aforesaid Rules account shall cease to be operational till the time Aadhaar number and PAN is submitted by the client. Petitioner alleged violation of Article 300A. The petitioner’s case is that account of a person is his property to which he cannot be deprived, saved by the authority of law. For nonsubmission of Aadhaar number and PAN only consequence which is contemplated by subrule (c) is that account shall cease to be operational.
We are of the view that the account remains belonging to the account holder and the amount in the account is only his amount and there is no deprivation of the property of account holder. Under the banking rules and procedures, there are several circumstances where account becomes unoperational. A nonoperational account also is an account which belongs to the account holder and amount laying in the nonoperational account is neither forfeited by the 318 bank nor taken out from the said account. Further, account is ceased operational only till the time Aadhaar number and PAN is submitted.
The consequences provided is only to effectuate the purpose of the Act and the Rules i.e. account be verified by Aadhaar mechanism. It is not the intent to deprive the account holder of the amount lying in the account. We, thus, do not find any substance in the submission of the petitioner that Rule 9(17)(c) violates right under Article 300A. Aadhaar number providing for verification of an account also cannot be held to be violating right under Article 21. The reporting entity i.e. banks and financial institutions under various statutes are required to provide information of a bank account to different authorities including income tax authority, account verification by Aadhaar is not for the purpose of keeping a track on the transaction done by an individual. As noted above Aadhaar number has to be given only once for opening of the account or for verification of the account and transactions are not 319 to be made on the basis of Aadhaar verification each time.
321. One of the submissions which has been made by the petitioner also is that Rules violate Article 19(1)(g). It is submitted that Rule refers to companies, firms, trusts etc. whereas Aadhaar Act is only to establish identity of individual. For example subrule (6) of Rule 9 as amended by Second Amendment Rules, 2017 provides that where client is a company, it shall for the purposes of subrule (1), submit to the reporting entity the certified copies of the documents enumerated therein. Rule requiring Aadhaar number and PAN or Form 60 as defined in Income Tax Rules, 1962, issued to managers, officers or employees holding an attorney to transact on the company’s behalf, is for the purpose to find out the beneficial owner behind the company. One of the objects of the Act is to detect moneylaundering wherever it is found. Inquiring details of the company to find out shell companies and ghost companies and the real beneficial owner cannot be said to be foreign to the 320 object of the Act.
Companies, partnership firms, trusts or incorporated institutions or body of individuals cannot complain any violation of rights under Article 19(1)(g). There is no amount of restriction in the right of aforesaid in carrying out any profession, or any trade or business. Petitioners have also contended that amended Rule 9 also violates Section 3, 7 and 51 of the Aadhaar Act. Section 3 provides for enrolment under Aadhaar scheme. Section 7 provides for requirement of proof of Aadhaar number for receipt of certain subsidies, benefits and services, etc. Section 51 relates to delegation by the authority to any Member, officer of the authority or any other person such of the powers and functions under the said Act except the power under Section 54. Rules cannot be held in any manner violating Sections 3, 7 and 51.
The rules provide for use of Aadhaar for verification of bank account by law as contemplated by Section 57 of the Aadhaar Act.
322. It is further submitted that Amendment Rules are also ultra vires to the PMLA, 2002. Shri Arvind P 321 Datar has also referred to judgment of the U.K. Supreme Court in Bank Mellat v. Her Majesty’s Treasury, (2013) UKSC 39. He has relied on principle of proportionality as summed in paragraph 20 which is to the following effect:
“20….The classic formulation of the test is to be found in the advice of the Privy Council, delivered by Lord Clyde, in De Freitas v Permanent Secretary of Ministry of Agriculture, Fisheries, Lands and Housing [1999] 1 AC 69 at 80. But this decision, although it was a milestone in the development of the law, is now more important for the way in which it has been adapted and applied in the subsequent caselaw, notably R (Daly) v Secretary of State for the Home Department [2001] 2 AC 532 (in particular the speech of Lord Steyn), R v Shayler [2003] 1 AC 247 at paras 5759 (Lord Hope of Craighead), Huang v Secretary of State for the Home Department [2007] 2 AC 167 at para 19 (Lord Bingham of Cornhill) and R (Quila) v Secretary of State for the Home Department [2012] 1 AC 621 at para 45.
Their effect can be sufficiently summarised for present purposes by saying that the question depends on an exacting analysis of the factual case advanced in defence of the measure, in order to determine
(i) whether its objective is sufficiently important to justify the limitation of a fundamental right;
(ii) whether it is rationally connected to the objective;
(iii) whether a less intrusive measure could have been used; and (iv) whether, having regard to these matters and to the severity of the consequences, a fair balance has been struck between the rights of 322 the individual and the interests of the community. These four requirements are logically separate, but in practice they inevitably overlap because the same facts are likely to be relevant to more than one of them.”
(emphasis added)
323. The principles of proportionality as noticed in the aforesaid judgment are substantially same which had been laid down in Puttaswamy case and Modern Dental (supra) only one difference in the above two judgments is that although both the judgments noticed the least intrusive test but in ultimate conclusion the said test was not reflected in the ratio of the above two judgments.
324. In the foregoing discussions, we come to the conclusion that Rule 9 of Second Amendment Rules, 2017 fully satisfies threefold test as laid down in Puttaswamy case and the submission that the Rule is unconstitutional has to be rejected. We answer Issue No. 14 in the following manner:Ans. 14:Rule 9 as amended by PMLA (Second Amendment) Rules, 2017 is not unconstitutional and does not violate Articles 14, 19(1)(g), 21 & 300A 323 of the Constitution and Sections 3, 7 & 51 of the Aadhaar Act. Further Rule 9 as amended is not ultra vires to PMLA Act, 2002.
Issue No. 15
Circular dated 23.03.2017 issued by Ministry of Communications Department of Telecommunications
325. The petitioners have attacked the circular dated 23.03.2017 and submitted that the circular is ultra vires. By circular dated 23.03.2017, Department of Telecommunications has directed that all licensees shall reverify all existing mobile subscribers (prepaid and postpaid) through Aadhaar based ekyc process. Petitioners submitted that linking the sim with Aadhaar number is breach of privacy violating Article 21 of the Constitution. Elaborating their challenge, it is contended that circular dated 23.03.2017 is not covered by any of the provisions of Aadhaar Act neither Section 7 nor Section 57.
Circular dated 23.03.2017 is not a law under Part III of the Constitution and thus same cannot put any restriction on privacy right. It is submitted that 324 circular dated 23.03.2017 does not satisfy threefold test as laid down in Privacy judgment. 326. Learned counsel for the respondents justifying the linking of Aadhaar with sim card submits that nonverifying sim cards, have caused serious security threats, which has been noticed by this Court in several judgments. It is submitted that circular dated 23.03.2017 was issued on the basis of recommendation of Telecom Regulatory Authority of India. Respondents further submits that circular dated 23.03.2017 has been issued in reference to this Court’s direction in Lokniti Foundation Vs. Union of India and Another, (2017) 7 SCC 155.
This court having approved the action, no exception can be taken by the petitioner to the circular dated 23.03.2017. It is submitted that the Central Government, which has right to grant license can always put a condition in the license obliging the licensee to verify the sim cards under the Aadhaar verification. To impose such condition is in the statutory power granted to the Government under Section 4 of the Indian Telegraph 325 Act, 1885. 327. We need to scrutinise the circular dated 23.03.2017 on the ground of attack alleged by the petitioners and justification as offered by the respondents. Circular dated 23.03.2017 has been addressed by the Ministry of Communications, Department of Telecommunications to all Unified Licensees/Unified Access Service Licensees/Cellular Mobile Telephone Service Licensees with subject: implementation of orders of Supreme Court regarding 100% EKYC of existing subscribers. Para 1 to 3 of the circular may be noticed, which are to the following effect:” Hon’ble Supreme Court, in its order dated 06.02.2017 passed in Writ Petition (C) No. 607/2016 filed by Lokniti Foundation v/s Union of India, while taking into cognizance of “Aadhaar based EKYC process for issuing new telephone connection” issued by the Department, has interalia observed that “an effective process has been evolved to ensure identity verification, as well as, the addresses of all mobile phone subscribers for new subscribers. In the near future, and more 326 particularly, within one year from today, a similar verification will be completed, in case of existing subscribers.”
This amounts to a direction which is to be completed within a time frame of one year.
2. A meeting was held on 13.02.2017 in the Department with the telecom industry wherein UIDAI, TRAI and PMO representatives also participated to discuss the way forward to implement the directions of Hon’ble Supreme Court. Detailed discussions and deliberations were held in the meeting. The suggestions received from the industry have been examined in the Department.
3. Accordingly, after taking into consideration the discussions held in the meeting and suggestions received from telecom industry, the undersigned is directed to convey the approval of competent authority that all Licensees shall reverify all existing mobile subscribers (prepaid and postpaid) through Aadhaar based EKYC process as mentioned in this office letter no. 80029/ 2010VAS dated 16.08.2016. The instructions mentioned in subsequent paragraphs shall be strictly followed while carrying out the reverification exercise.”
328. The circular of the Department of Telecommunications directing the licensees to mandatorily verify existing sim subscribers in turn resulted in mobile telephone service licensees directing the subscribers to get their sim seeded with Aadhaar. Repeated messages and directions have been issued by Cellular Mobile Telephone Service operators. Compulsory seeding of Aadhaar with mobile numbers has to be treated to be an intrusion in Privacy Right of a person. Any invasion on the Privacy Right of a person has to be backed by law as per the threefold test enumerated in Puttaswamy case (supra). Existence of a law is the foremost condition to be fulfilled for restricting any Privacy Right. Thus, we have to first examine whether circular dated 23.03.2017 can be said to be a ‘law’.
329. The law as explained in Article 13(3) has to be applied for finding out as to what is law. Article 13(3)(a) gives an inclusive definition of law in following words:( a) “law” includes any Ordinance, order, bye328 law, rule, regulation, notification, custom or usage having in the territory of India the force of law;
330. The circular dated 23.03.2017 at best is only an executive instruction issued on 23.03.2017 by the Ministry of Communications, Department of Telecommunications. The circular does not refer to any statutory provision or statutory base for issuing the circular. The subject of circular as noted above indicate that circular has been issued for implementation of orders of Supreme Court regarding 100% EKYC based reverification of existing subscribers. It is necessary to notice the judgment of this Court dated 06.02.2017, a reference to which is made in the circular itself. The order dated 06.02.2017 was issued by this Court in a Writ Petition filed by Lokniti Foundation Vs. Union of India and Another, (2017) 7 SCC 155. The petitioners have filed a writ petition with a prayer that identity of each subscriber and also the members should be verified so that unidentified and unverified subscribers cannot misuse mobile phone. After issuing the notice, Union of India had filed a counter affidavit, where Union of India stated that Department has launched Aadhaar based EKYC for issuing mobile connections on 16.8.2016. 331. Paras 2 to 6 of the judgment, which is relevant for the present purpose are as follows:2. Consequent upon notice being issued to the Union of India, a short counter affidavit has been filed on its behalf, wherein, it is averred as under:
“22. That however, the department has launched `Aadhaar based EKYC for issuing mobile connections’ on 16th August, 2016 wherein the customer as well as Point of Sale (PoS) Agent of the TSP will be authenticated from Unique Identification Authority of India (UIDAI) based on their biometrics and their demographic data received from UIDAI is stored in the database of TSP along with time stamps. Copy of letter No.80029/ 2010VAS dated 16.08.2016 is annexed herewith and marked as Annexure R1/ 10. 23. As on 31.01.2017, 111.31 Crores Aadhaar card has been issued which represent 87.09% of populations. However, still there are substantial number of persons who do not have Aadhaar card because they may not be interested in having Aadhaar being 75 years or more of age or not availing any benefit of pension or Direct Benefit Transfer (DBT). Currently Aadhaar card or biometric authentication is not mandatory for obtaining a new telephone connection.
As a point of information, it is submitted that those who have Aadhaar card/number normally use the same for obtaining a new telephone connection using EKYC process as mobile connection can be procured within few minutes in comparison to 12 days being taken in normal course.
24. That in this process, there will be almost `NIL’ chances of delivery of SIM to wrong person and the traceability of customer shall greatly improve. Further, since no separate document for Proof of Address or Proof of Identity will be taken in this process, there will be no chances of forgery of documents.”
3. The learned Attorney General, in his endeavour to demonstrate the effectiveness of the procedure, which has been put in place, has invited our attention to the application form, which will be required to be filled up, by new mobile subscribers, using eKYC process. It was the submission of the learned Attorney General, that the procedure now being adopted, will be sufficient to alleviate the fears, projected in the writ petition.
4. Insofar as the existing subscribers are concerned, it was submitted on behalf of the Union of India, that more than 90% of the subscribers are using prepaid connections. It was pointed out, that each prepaid connection holder, has to per force renew his connection periodically, by making a deposit for further user. It was submitted, that these 90% existing subscribers, can also be verified by putting in place a mechanism, similar to the one adopted for new subscribers. Learned Attorney General states, that an effective programme for the same, would be devised at the earliest, and the process of identity verification will be completed within one year, as far as possible.
5. In view of the factual position brought to our notice during the course of hearing, we are satisfied, that the prayers made in the writ petition have been substantially dealt with, and an effective process has been evolved to ensure identity verification, as well as, the addresses of all mobile phone subscribers for new subscribers. In the near future, and more particularly, within one year from today, a similar verification will be completed, in the case of existing subscribers. While complimenting the petitioner for filing the instant petition, we dispose of the same with the hope and expectation, that the undertaking given to this Court, will be taken seriously, and will be given effect to, as soon as possible.
6. The instant petition is disposed of, in the above terms.”
332. Para 5 of the judgment contains the operative portion of the order, which states “we dispose of the same with the hope and expectation, that the undertaking given to this Court, will be taken seriously, and will be given effect to, as soon as possible”. The order of this Court as extracted above itself states that the Court itself did not give any direction rather noticed the stand of Union of India where it informed to the Court that the department has already launched Aadhaar based eKYC for issuing mobile connections. For 90 per cent of the existing subscribers, Attorney General has stated that an effective programme would be devised at the earliest and will be completed within one year.
333. We are clear in our mind that this Court on 06.02.2017 only noticed the stand of the Union of India and disposed of the writ petition expecting that undertaking given to this Court shall be given effect to.
334. The circular dated 23.03.2017 cites the order of this Court as a direction, which according to department was to be completed within the time frame of one year. Circular further states that the meeting was held on 13.02.2017 in the Department with the 333 telecom industry wherein UIDAI, TRAI and PMO representatives also participated.
335. This Court thus in Lokniti case (supra) did not examine the Aadhaar based eKYC process in context of right of privacy. Thus, the order of this Court dated 06.02.2017 cannot absolve the Government from justifying its circular as per law. 336. One of the submissions, which has been raised by the respondents to cite a statutory base to the circular is that the circular has been issued in pursuance of recommendation made by TRAI under Section 11(1)(a) of TRAI Act, 1997. Section 11 of the TRAI Act, 1997 provides for function of authority Section 11(1)(a):( a) make recommendations, either suo motu or on a request from the licensor, on the following matters, namely:-
(i) need and timing for introduction of new service provider;
(ii) terms and conditions of licence to a service provider;
(iii) revocation of licence for noncompliance of terms and conditions of licence;
334 xxxxxxxxxxxxxxxx
337. One of the functions of the TRAI is to give recommendations as per Section 11(1)(a) on the matters enumerated therein. The recommendations of TRAI were only recommendations and the mere fact that circular dated 23.03.2017 was issued after the recommendation was sent by TRAI, circular dated 23.03.2017 does not acquire any statutory character. Circular dated 23.03.2017 thus cannot be held to be a law within the meaning of Part III of the Constitution. 338. Shri Rakesh Dwivedi, learned counsel appearing for the respondents has submitted that the Central Government being licensor, it is fully entitled to provide for any condition in its license, which condition becomes binding on the licensee. Referring to license agreement for Unified Licensees, Shri Dwivedi submits that one of the conditions in the agreement was Condition No. 16.1 which is to the following effect:”
16.1 The Licensee shall be bound by the 335 terms and conditions of this License Agreement as well as instructions as are issued by the Licensor and by such orders/directions/regulations of TRAI as per provisions of the TRAI Act, 1997 as amended from time to time.” 339. Shri Dwivedi has also relied on a number of judgments in support of his submissions that conditions can be validly laid down. he has relied on Bagalkot Cement Co. Ltd. Vs. R.K. Pathan and Others, AIR 1963 SC 439, where this Court while considering the Industrial Employment (Standing Orders) Act, 1946 observed that object of the Act was to require the employers to make the conditions of employment precise and definite and the Act ultimately intended to prescribe these conditions in the form of Standing Orders so that what used to be governed by a contract herebefore would now be governed by the Statutory Standing Orders.
340. The above judgment at best can be read to mean that conditions, which are enumerated in the Standing Orders become statutory conditions. No benefit of the judgment can be taken by the respondents in the 336 present case since even if it is put in the condition in the agreement between licensee and subscribers that licensee shall be bound to instructions as issued by licensor, the said condition does not become statutory nor take shape of a law. Sukhdev Singh and Others Vs. Bhagatram Sardar Singh Raghuvanshi and Another, (1975) 1 SCC 421 was relied, where this Court held that rules and regulations framed by ONGC, LIC and Industrial Finance Corporation have the force of law.
There cannot be any denial that rules framed under statutory provisions will have force of law, thus, this case has no application. Similarly, reliance on Lily Kurian Vs. Sr. Lewina and Others, (1979) 2 SCC 124, Alpana V. Mehta Vs. Maharashtra State Board of Secondary Education and Another, (1984) 4 SCC 27, St. Johns Teachers Training Institute Vs. Regional Director, National Council for Teacher Education and Another, (2003) 3 SCC 321 were all cases, where conditions were laid down under the regulations, which were statutory in nature. Those cases in no manner help the respondents.
341. Shri Dwivedi has also relied on judgment of this Court in Union of India and Another Vs. Association of Unified Telecom Service Providers of India and Others, (2011) 10 SCC 543. This Court referring to Section 4 of the Telegraph Act laid down following in paragraph 39:”
39. The proviso to Subsection (1) of Section 4 of the Telegraph Act, however, enables the Central Government to part with this exclusive privilege in favour of any other person by granting a license in his favour on such conditions and in consideration of such payments as it thinks fit. As the Central Government owns the exclusive privilege of carrying on telecommunication activities and as the Central Government alone has the right to part with this privilege in favour of any person by granting a license in his favour on such conditions and in consideration of such terms as it thinks fit, a license granted under proviso to Subsection (1) of Section 4 of the Telegraph Act is in the nature of a contract between the Central Government and the licensee.”
342. There cannot be any dispute to the right of the Central Government to part with exclusive privilege in favour of any person by granting license on such a condition and in consideration of such terms as it 338 thinks fit. But mere issuing an instruction to the licensees to adopt mandatory process of eKYC by Aadhaar verification in no manner exalt the instructions or directives as a law. Circular dated 23.03.2017, thus, cannot be held to be a law and direction to reverification of all existing mobile subscribers through Aadhaar based eKYC cannot be held to be backed by law, hence cannot be upheld.
343. There is one more aspect of the matter, which needs to be looked into. Aadhaar Act has only two provisions under which Aadhaar can be used, i.e. Section 7 and Section 57. Present is not a case of Section 7 since present is not a case of receiving any subsidy, benefit or service. What Section 57 contemplate is that “use of Aadhaar can be provided by a law”. Words “by a law” used in Section 57 obviously mean a valid law framed by competent legislation and other than the Aadhaar Act. No law has been framed by permitting use of Aadhaar for verification of sim of existing subscribers. There being no law framed for such use of Aadhaar, Section 57 is also not attracted.
344. There are only above two contingencies, where Aadhaar can be used and circular dated 23.03.2017 being not covered by any of above contingencies, circular dated 23.03.2017 deserves to be set aside. Ans.15:Circular dated 23.03.2017 being unconstitutional is set aside.
Issue No. 16
Whether Aadhaar Act is a Money Bill and decision of Speaker certifying it as Money Bill is not subject to Judicial Review of this Court?
345. The Aadhaar Act has been passed by Parliament as Money Bill. Shri P. Chidambaram, learned senior counsel appearing for the petitioners contends that Aadhaar Act is not a Money Bill, it being not covered by any of the Clauses under Article 110 of the Constitution of India. He further submits that decision of the Speaker certifying Aadhaar Bill as Money Bill being illegal and contrary to the express constitutional provisions deserves to be interfered with and such decision of the Speaker is also subject to Judicial Review by this Court. The word “only” used in Article 110 has significance and a Bill, which does not contain only, the provisions pertaining to Clause (a) to (f) cannot be regarded as Money Bill. Respondents cannot fall on Clause (g) to support the Money Bill, which clause cannot be invoked unless the provisions of Bill are covered by any of the clauses from (a) to (f).
346. Shri K.K. Venugopal, learned Attorney General refuting the above submission submits that Aadhaar Bill has correctly been passed as Money Bill. He submits that the certification granted by Speaker that Aadhaar Bill is a Money Bill has been made final by virtue of Article 110(3), hence it cannot be questioned in any Court.
The decision of Speaker certifying the Bill as Money Bill is not subject to Judicial Review. It is further submitted by learned Attorney General that even on looking the Aadhaar Bill on merits, it satisfies the conditions as enumerated under Article 110(1). He submits that Aadhaar Bill is clearly referable to Clause(c), Clause(e) and Clause(g) of Article 110(1). He submits that the heart of the Aadhaar Act is Section 7 which is with regard to payment of subsidies, benefits or services and for which the expenditure is incurred form the Consolidated Fund of India. Article 122 also puts an embargo in questioning validity of any proceedings in Parliament. Certification of Bill as Money Bill is matter of Parliamentary procedure hence Article 122 also save the said decision from being questioned in a Court of Law.
347. Article 110 and Article 122, which falls for consideration in the present case are as follows:” 110. Definition of “Money Bills”.
(1) For the purposes of this Chapter, a Bill shall be deemed to be a Money Bill if it contains only provisions dealing with all or any of the following matters, namely:
( a) the imposition, abolition, remission, alteration or regulation of any tax;
(b) the regulation of the borrowing of money or the giving of any guarantee by the Government of India, or the amendment of the law with respect to any financial obligations undertaken or to be undertaken by the Government of India;
(c) the custody of the Consolidated Fund or the Contingency Fund of India, the payment of moneys into or the withdrawal of moneys from any such Fund;
(d) the appropriation of moneys out of the Consolidated Fund of India;
(e) the declaring of any expenditure to be expenditure charged on the Consolidated Fund of India or the increasing of the amount of any such expenditure; (f) the receipt of money on account of the Consolidated Fund of India or the public account of India or the custody or issue of such money or the audit of the accounts of the Union or of a State; or (g) any matter incidental to any of the matters specified in subclauses (a) to (f).
(2) A Bill shall not be deemed to be a Money Bill by reason only that it provides for the imposition of fines or other pecuniary penalties, or for the demand or payment of fees for licences or fees for services rendered, or by reason that it provides for the imposition, abolition, remission, alteration or regulation of any tax by any local authority or body for local purposes.
(3) If any question arises whether a Bill is a Money Bill or not, the decision of the Speaker of the House of the People thereon shall be final. 4) There shall be endorsed on every Money Bill when it is transmitted to the Council of States under article 109, and when it is presented to the President for assent under article 111, the certificate of the Speaker of the House of the People signed by him that it is a Money Bill.
122. Courts not to inquire into proceedings of Parliament.
(1) The validity of any proceedings in Parliament shall not be called in question on the ground of any alleged irregularity of procedure. (2) No officer or member of Parliament in whom powers are vested by or under this Constitution for regulating procedure or the conduct of business, or for maintaining order, in Parliament shall be subject to the jurisdiction of any court in respect of the exercise by him of those powers.”
348. We need to first advert to the submission pertaining to question as to whether decision of Speaker certifying the Bill as Money Bill is subject to Judicial Review of this Court or being related to only procedure, is immuned from Judicial Review under Article 122. Article 110(3) gives finality to the decision of the Speaker of the House of the People on question as to whether a Bill is Money Bill or not. The word occurring in subarticle (3) of Article 110 are “shall be final”. Article 122(1) puts an embargo on questioning the validity of any proceeding in the Parliament on the ground of any alleged irregularity or procedure. The Constitution uses different expressions in different articles like “shall be final”, “shall not be questioned”, “shall not be questioned in any Court of Law” etc.
349. This Court has examined the scope of Judicial Review in reference to Parliamentary proceedings. A similar Constitutional provision giving finality to the decision of the Speaker is contained in Para 6 of Tenth Schedule where a question whether a person has become disqualified or not is to be referred to the decision of the Chairman or the Speaker and his decision shall be final. Para 6 subclause( 1) is quoted as below:”
6. Decision on questions as to disqualification on ground of defection.-
(1) If any question arises as to whether a member of a House has become subject to disqualification under this Schedule, the question shall be referred for the decision of the Chairman or, as the case may be, the Speaker of such House and his decision shall be final: Provided that where the question which has arisen is as to whether the Chairman or the Speaker of a House has become subject to such disqualification, the question shall be referred for the decision of such member of the House as the House may elect in this behalf and his decision shall be final.”
350. The Constitution Bench had occasion to consider Para 6 in Kihoto Hollohan Vs. Zachillhu and Others, 1992 Supp. (2) SCC 651, Justice M.N. Venkatachaliah, as he then was elaborately considered the rival contentions. It was also contended before this Court that in view of the finality of the decision of the Speaker in Para 6 of Tenth Schedule, the decision of the Speaker is beyond Judicial Review. In Para 78, following has been stated:”
78. These two contentions have certain overlapping areas between them and admit of being dealt with together. Paragraph 6(1) of the Tenth Schedule seeks to impart a statutory finality to the decision of the Speaker or the Chairman. The argument is that, this concept of `finality’ by itself, excludes Courts’ jurisdiction. Does the word “final” render the decision of the Speaker immune from Judicial Review? It is now well accepted that a finality clause is not a legislative magical incantation which has that effect of telling off Judicial Review. Statutory finality of a decision presupposes and is subject to its consonance with the statute……………”
In Para 80 to 85, following has been held:80. In Durga Shankar Mehta v. Raghuraj Singh, AIR 1954 SC 520 the order of the Election Tribunal was made final and 346 conclusive by Section 105 of the Representation of the People Act, 1951. The contention was that the finality and conclusiveness clauses barred the jurisdiction of the Supreme Court under Article 136. This contention was repelled. It was observed: (AIR p. 522) …[B]ut once it is held that it is a judicial tribunal empowered and obliged to deal judicially with disputes arising out of or in connection with election, the overriding power of this Court to grant special leave, in proper cases, would certainly be attracted and this power cannot be excluded by any parliamentary legislation. …
But once that Tribunal has made any determination or adjudication on the matter, the powers of this Court to interfere by way of special leave can always be exercised…… … The powers given by Article 136 of the Constitution however are in the nature of special or residuary powers which are exercisable outside the purview of ordinary law, in cases where the needs of justice demand interference by the Supreme Court of the land…. Section 105 of the Representation of the People Act certainly gives finality to the decision of the Election Tribunal so far as that Act is concerned and does not provide for any further appeal but that cannot in any way cut down or effect the overriding powers which this Court can exercise in the matter of granting special leave under 347 Article 136 of the Constitution.
81. Again, in Union of India v. Jyoti Prakash Mitter [1971] 3 SCR 483 a similar finality clause in Article 217(3) of the Constitution camp up for consideration. This Court said: (SCC pp.4101, Para32) …The President acting under Article 217(3) performs a judicial function of grave importance under the scheme of our Constitution. He cannot act on the advice of his Ministers. Notwithstanding the declared finality of the order of the President the Court has jurisdiction in appropriate cases to set aside the order, if it appears that it was passed on collateral considerations or the rules of natural justice were not observed, or that the President’s judgment was coloured by the advice or representation made by the executive or it was founded on no evidence.”
82. Referring to the expression “final” occurring in Article 311(3) of the Constitution this Court in Union of India v. Tulsiram Patel, [1985] Supp. 2 SCR 131 held: (SCC p.507. Para 138) …The finality given by Clause (3) of Article 311 to the disciplinary authority’s decision that it was not reasonably practicable to hold the inquiry is not binding upon the court. The court will also examine the charge of mala fides, if any, made in the writ petition. In examining the relevancy of the reasons, the court will consider the situation which according to the disciplinary authority made it come 348 to the conclusion that it was not reasonably practicable to hold the inquiry. If the court finds that the reasons are irrelevant, then the recording of its satisfaction by the disciplinary authority would be an abuse of power conferred upon it by Clause (b)…. 83. If the intendment is to exclude the jurisdiction of the superior Courts, the language would quite obviously have been different. Even so, where such exclusion is sought to be effected by an amendment the further question whether such an amendment would be destructive of a basic feature of the Constitution would arise. But comparison of the language in Article 363(1) would bring out in contrast the kind of language that may be necessary to achieve any such purpose.
84. In Brundaban Nayak v. Election Commission of India [1965] 3 SCR 53, in spite of finality attached by Article 192 to the decision of the Governor in respect of disqualification incurred by a member of a State Legislature subsequent to the election, the matter was examined by this Court on an appeal by special leave under Article 136 of the Constitution against the decision of the High Court dismissing the writ petition filed under Article 226 of the Constitution. Similarly in Union of India v. Jyoti Prakash Mitter [1971] 3 SCR 483, in spite of finality attached to the order of the President with regard to the determination of age of a Judge of the High Court under Article 217(3) of the Constitution, this Court examined the legality of the order passed by the President during the pendency of an appeal filed under Article 136 of the Constitution.
85. There is authority against the acceptability of the argument that the word 349 “final” occurring in Paragraph 6(1) has the effect of excluding the jurisdiction of the Courts in Articles 136, 226 and 227.” 351. The above Constitution Bench Judgment clearly support the case of the petitioners that finality attached to the decision of the Speaker under Article 110(3) does not inhibit the Court in exercising its Judicial Review. We may also refer to the Constitution Bench judgment of this Court in Special Reference No. 1 of 1964, AIR 1965 SC 745 where this Court had occasion to consider Article 212, which is a provision relating to the legislature of the State para materia to Article 122. Constitution Bench has held that what is protected under Article 212 from being questioned is on the ground of any alleged irregularity or procedure.
The said ground does not apply in case of illegality of the decision. The next case, which needs to be considered is again a Constitution Bench judgment of this Court in Raja Rampal Vs. Hon’ble Speaker, Lok Sabha and Others, (2007) 3 SCC 184. The Constitution Bench in the above case had occasion to 350 consider the question of issue of Judicial Review of a decision of Speaker disqualifying from membership of the Parliament. A submission was raised before the Court by virtue of Article 122 of the Constitution, which puts an embargo on questioning any proceeding of the Parliament, the decision of the Speaker is immuned from the Judicial Review. The above submission has been noticed in Para 364 of the judgment in following words:”
364. The submissions of the learned Counsel for the Union of India and the learned Additional Solicitor General seek us to read a finality clause in the provisions of Article 122(1) in so far as parliamentary proceedings are concerned. On the subject of finality clauses and their effect on power of judicial review, a number of cases have been referred that may be taken note of at this stage. ” 352. In Paras 376, 377, 384 and 386 following has been held:” 376. In our considered view, the principle that is to be taken note of in the aforementioned series of cases is that notwithstanding the existence of finality clauses, this Court exercised its jurisdiction of judicial review whenever and wherever breach of fundamental rights was alleged.
The President of India while determining the question of age of a Judge of a High Court under Article 217(3), or the President of India (or the Governor, as the case may be) while taking a decision under Article 311(3) to dispense with the ordinarily mandatory inquiry before dismissal or removal of a civil servant, or for that matter the Speaker (or the Chairman, as the case may be) deciding the question of disqualification under Para 6 of the Tenth Schedule may be acting as authorities entrusted with such jurisdiction under the constitutional provisions. Yet, the manner in which they exercised the said jurisdiction is not wholly beyond the judicial scrutiny. In the case of the Speaker exercising jurisdiction under the Tenth Schedule, the proceedings before him are declared by Para 6(2) of the Tenth Schedule to be proceedings in Parliament within the meaning of Article 122.
Yet, the said jurisdiction was not accepted as nonjustifiable. In this view, we are unable to subscribe to the proposition that there is absolute immunity available to the Parliamentary proceedings relating to Article 105(3). It is a different matter as to what parameters, if any, should regulate or control the judicial scrutiny of such proceedings.
377. In U.P. Assembly case (Special Reference No.1 of 1964), AIR 1965 SC 745, the issue was authoritatively settled by this Court, and it was held, at SCR pp. 45556, as under: (AIR p.768, para 62) “Article 212(1) seems to make it possible for a citizen to call in question in the appropriate court of law the validity of any proceedings inside the legislative chamber if his case is that the said proceedings suffer not from mere irregularity of procedure, but from an illegality. If the impugned procedure is illegal and unconstitutional, it would be open to be scrutinized in a court of law, though such scrutiny is prohibited if the complaint against the procedure is no more than this that the procedure was irregular.”
(Emphasis supplied)
384. The prohibition contained in Article 122(1) does not provide immunity in cases of illegalities. In this context, reference may also be made to Sarojini Ramaswami v. Union of India, (1992) 4 SCC 506. The case mainly pertained to Article 124(4) read with the Judges (Inquiry) Act, 1968. While dealing, inter alia, with the overriding effect of the rules made under Article 124(5) over the rules made under Article 118, this Court at pp. 18788 made the following observations: (SCC p. 572, para 94) “94. We have already indicated the constitutional scheme in India and the true import of clauses(4) and (5) of Article 124 read with the law enacted under Article 124(5), namely, the Judges (Inquiry) Act, 1968 and the Judges (Inquiry) Rules, 1969, which, inter alia contemplate the provision for an opportunity to the Judge concerned to show cause against the finding of ‘guilty’ in the report before Parliament takes it up for consideration along with the motion for his removal. Along with the decision in U.P. Assembly Case 353 (Special Reference No. 1 of 1964) has to be read the declaration made in SubCommittee on Judicial Accountability, (1991) 4 SCC 699 that ‘a law made under Article 124(5) will override the rules made under Article 118 and shall be binding on both the Houses of Parliament. A violation of such a law would constitute illegality and could not be immune from judicial scrutiny under Article 122(1).’ The scope of permissible challenge by the Judge concerned to the order of removal made by the President under Article 124(4) in the judicial review available after making of the order of removal by the President will be determined on these considerations.”
(Emphasis supplied)
386. Article 122(1) thus must be found to contemplate the twin test of legality and constitutionality for any proceedings within the four walls of Parliament. The fact that the U.P. Assembly case (Special Reference No.1 of 1964) dealt with the exercise of the power of the House beyond its four walls does not affect this view which explicitly interpreted a constitutional provision dealing specifically with the extent of judicial review of the internal proceedings of the legislative body. In this view, Article 122(1) displaces the English doctrine of exclusive cognizance of internal proceedings of the House rendering irrelevant the case law that emanated from courts in that jurisdiction. Any attempt to read a limitation into Article 122 so as to restrict the court’s jurisdiction to examination of the Parliament’s procedure in case of unconstitutionality, as opposed to illegality would amount to doing violence to the constitutional text. Applying the principle of “expressio unius est exclusio alterius” (whatever has not been included has by implication been excluded), it is plain and clear that prohibition against examination on the touchstone of “irregularity of procedure” does not make taboo judicial review on findings of illegality or unconstitutionality.”
353. The above case is a clear authority for the proposition that Article 122 does not provide for immunity in case of illegality. What is protected is only challenge on the ground of any irregularity or procedure. The immunity from calling in question the Parliamentary decision on the ground of violation of procedure as has been provided in the Constitution is in recognition of the principles that Parliament has privilege regarding procedure and any challenge on the ground of violation of any procedure is not permissible.
354. Shri K.K. Venugopal relied on Two Judgments of this Court in support of his submission namely, Mohd. Saeed Siddiqui Vs. State of Uttar Pradesh and Another, 355 (2014) 11 SCC 415 and Yogendra Kumar Jaiswal and Others Vs. State of Bihar and Others, (2016) 3 SCC 183. He submits that in both the decisions, this Court while dealing with the question of challenge to Money Bill has clearly held that the decision of Speaker certifying a Bill as Money Bill is final and cannot be questioned.
355. We need to consider the above decisions in detail. Mohd. Saeed Siddiqui (supra) was a judgment delivered by a Three Judge Bench of this Court. U.P. Lokayukta Act and U.P. Lokayukta (Amendment) Act, 2012 was subject matter of challenge. One of the submissions in that regard has been noted in Para 12, which is to the following effect:”
12. It was further submitted by Mr. Venugopal that the Amendment Act was not even passed by the State Legislature in accordance with the provisions of the Constitution of India and is, thus, a mere scrap of paper in the eye of the law. The Bill in question was presented as a Money Bill when, on the face of it, it could never be called as a Money Bill as defined in Articles 199(1) and 199(2) of the Constitution of India. Since the procedure for an Ordinary Bill was not followed and the assent of the Governor was obtained to an inchoate and incomplete Bill 356 which had not even gone through the mandatory requirements under the Constitution of India, the entire action was unconstitutional and violative of Article 200 of the Constitution of India.”
356. This Court after noticing Articles 199 and 212, which are pari materia to Articles 109 and 122 stated that proceeding in support of legislature cannot be called into question on the ground that they have not been carried on in accordance with the rules of business. This Court considered the issues from Paragraphs 34 to 38, which is to the following effect:”
34. The above provisions make it clear that the finality of the decision of the Speaker and the proceedings of the State Legislature being important privilege of the State Legislature, viz., freedom of speech, debate and proceedings are not to be inquired by the Courts. The “proceeding of the legislature” includes everything said or done in either House in the transaction of the Parliamentary business, which in the present case is enactment of the Amendment Act. Further, Article 212 precludes the courts from interfering with the presentation of a Bill for assent to the Governor on the ground of noncompliance with the procedure for passing Bills, or from otherwise questioning the Bills passed by the House. To put it clear, proceedings inside the legislature cannot be called into question on the ground that they have not been carried on in accordance with the Rules of Business. This is also evident from Article 194 which speaks about the powers, privileges of the Houses of the Legislature and of the members and committees thereof.
35. We have already quoted Article 199. In terms of Article 199(3), the decision of the Speaker of the Legislative Assembly that the Bill in question was a Money Bill is final and the said decision cannot be disputed nor can the procedure of the State Legislature be questioned by virtue of Article 212. We are conscious of the fact that in the decision of this Court in Raja Ram Pal v. Lok Sabha (2007) 3 SCC 184, it has been held that the proceedings which may be tainted on account of substantive or gross irregularity or unconstitutionality are not protected from judicial scrutiny.
36. Even if it is established that there was some infirmity in the procedure in the enactment of the Amendment Act, in terms of Article 255 of the Constitution the matters of procedures do not render invalid an Act to which assent has been given by the President or the Governor, as the case may be.
37. In M.S.M. Sharma v. Shree Krishna Sinha AIR 1960 SC 1186 and Mangalore Ganesh Beedi Works v. State of Mysore, AIR 1963 SC 589, the Constitution Benches of this Court held that:
(i) the validity of an Act cannot be challenged on the ground that it offends Articles 197 to 199 and the procedure laid down in Article 202;
(ii) Article 212 prohibits the validity of any proceedings in a Legislature of a State from being called in question on the ground of any alleged irregularity of procedure; and
(iii) Article 255 lays down that the requirements as to recommendation and previous sanction are to be regarded as a matter of procedure only. It is further held that the validity of the proceedings inside the legislature of a State cannot be called in question on the allegation that the procedure laid down by the law has not been strictly followed and that no Court can go into those questions which are within the special jurisdiction of the legislature itself, which has the power to conduct its own business.
38. Besides, the question whether a Bill is a Money Bill or not can be raised only in the State Legislative Assembly by a member thereof when the Bill is pending in the State Legislature and before it becomes an Act. It is brought to our notice that in the instant case no such question was ever raised by anyone. “
357. This Court came to the conclusion that question pertaining to the procedure in the House could not have been questioned by virtue of Article 212. Another judgment, which has been relied by learned Attorney General is judgment of this Court in Yogendra Kumar Jaiswal (supra). The above judgment was rendered by Two Judge Bench. This Court in the above case examined the question whether introduction of 359 Orissa Special Courts Act, 2006 as a Money Bill could be called in question in a Court. This Court considered the issue in Paragraphs 38 to 43, which are to the following effect:”
38. First, we shall take up the issue pertaining to the introduction of the Bill as a Money bill in the State Legislature. Mr. Vinoo Bhagat, learned Counsel appearing for some of the appellants, has laid emphasis on the said aspect. Article 199 of the Constitution, defines “Money Bills”. For our present purpose, Clause (3) of Article 199 being relevant is reproduced below: “199.(3). If any question arises whether a Bill introduced in the legislature of a State which has a Legislative Council is a Money Bill or not, the decision of the Speaker of the Legislative Assembly of such State thereon shall be final. We have extracted the same as we will be referring to the authorities as regards interpretation of the said clause.
39. Placing reliance on Article 199, the learned Counsel would submit that the present Act which was introduced as a money bill has remotely any connection with the concept of money bill. It is urged by him that the State has made a Sisyphean endeavour to establish some connection. The High Court to repel the challenge had placed reliance upon Article 212 which stipulates that the validity of any proceedings in the Legislature of a State shall not be called in question on the ground of any alleged irregularity of procedure.
40. The learned Counsel for the appellants 360 has drawn inspiration from a passage from Powers, Privileges and Immunities of State Legislatures. In re, Special Reference No. 1 of 1964 AIR 1965 SC 745, wherein it has been held that Article 212(1) lays down that the validity of any proceedings in the legislature of a State shall not be called in question on the ground of any alleged irregularity of procedure and Article 212(2) confers immunity on the officers and members of the legislature in whom powers are vested by or under the Constitution for regulating procedure or the conduct of business, or for maintaining order, in the legislature from being subject to the jurisdiction of any court in respect of the exercise by him of those powers.
The Court opined that Article 212(1) seems to make it possible for a citizen to call in question in the appropriate court of law the validity of any proceedings inside the Legislative Chamber if his case is that the said proceedings suffer not from mere irregularity of procedure, but from an illegality. If the impugned procedure is illegal and unconstitutional, it would be open to be scrutinised in a court of law, though such scrutiny is prohibited if the complaint against the procedure is not more than that the procedure was irregular. Thus, the said authority has made a distinction between illegality of procedure and irregularity of procedure.
41. Our attention has also been drawn to certain paragraphs from the Constitution Bench decision in Raja Ram Pal v. Lok Sabha (2007) 3 SCC 184.
In the said case, in paras 360 and 366, it has been held thus: (SCC pp. 347 & 350) “360. The question of extent of judicial review of parliamentary matters has to be resolved with 361 reference to the provision contained in Article 122(1) that corresponds to Article 212 referred to in M.S.M. Sharma v. Shree Krishna Sinha AIR 1960 SC 1186 [Pandit Sharma (2)]. On a plain reading, Article 122(1) prohibits “the validity of any proceedings in Parliament” from being ‘called in question’ in a court merely on the ground of “irregularity of procedure”.
In other words, the procedural irregularities cannot be used by the court to undo or vitiate what happens within the four walls of the legislature. But then, “procedural irregularity” stands in stark contrast to “substantive illegality’ which cannot be found included in the former. We are of the considered view that this specific provision with regard to check on the role of the judicial organ visàvis proceedings in Parliament uses language which is neither vague nor ambiguous and, therefore, must be treated as the constitutional mandate on the subject, rendering unnecessary search for an answer elsewhere or invocation of principles of harmonious construction. * * *
366. The touchstone upon which parliamentary actions within the four walls of the legislature were examined was both the constitutional as well as substantive law. The proceedings which may be tainted on account of substantive illegality or unconstitutionality, as opposed to those suffering from mere irregularity thus cannot be held 362 protected from judicial scrutiny by Article 122(1) inasmuch as the broad principle laid down in Bradlaugh (1884) LR 12 QBD 271 : 53 LJQB 290 : 50 LT 620 (DC), acknowledging exclusive cognizance of the legislature in England has no application to the system of governance provided by our Constitution wherein no organ is sovereign and each organ is amenable to constitutional checks and controls, in which scheme of things, this Court is entrusted with the duty to be watchdog of and guarantor of the Constitution.”
42. In this regard, we may profitably refer to the authority in Mohd. Saeed Siddiqui v. State of U.P. (2014) 11 SCC 415, wherein a threeJudge Bench while dealing with such a challenge, held that Article 212 precludes the courts from interfering with the presentation of a Bill for assent to the Governor on the ground of noncompliance with the procedure for passing Bills, or from otherwise questioning the Bills passed by the House, for proceedings inside the legislature cannot be called into question on the ground that they have not been carried on in accordance with the Rules of Business.
Thereafter, the Court referring to Article 199(3) ruled that the decision of the Speaker of the Legislative Assembly that the Bill in question was a Money Bill is final and the said decision cannot be disputed nor can the procedure of the State Legislature be questioned by virtue of Article 212. The Court took note of the decision in Raja Ram Pal (supra) wherein it has been held that the proceedings which may be tainted on account of substantive or gross irregularity or unconstitutionality are not protected from 363 judicial scrutiny. Eventually, the Court repelled the challenge.
43. In our considered opinion, the authorities cited by the learned Counsel for the appellants do not render much assistance, for the introduction of a Bill, as has been held in Mohd. Saeed Siddiqui (supra), comes within the concept of “irregularity” and it does come with the realm of substantiality. What has been held in the Special Reference No. 1 of 1964 (supra) has to be appositely understood. The factual matrix therein was totally different than the case at hand as we find that the present controversy is wholly covered by the pronouncement in Mohd. Saeed Siddiqui (supra) and hence, we unhesitatingly hold that there is no merit in the submission so assiduously urged by the learned Counsel for the appellants.”
358. The consideration in the above case indicate that this Court has merely relied on judgment of Three Judge Bench in Mohd. Saeed Siddiqui (supra). The Court based its decision on finality attached to the decision of the Speaker in Article 199(3) as well as bar on challenge of proceeding of the legislature on an irregularity procedure as contained in Article 212.
The question is, where a Speaker certify a Bill as a Money Bill and it is introduced and passed as a Money Bill, this only a question of procedure or not? Article 107 contains provisions as to introduction of 364 passing of bills. Article 107(2) state that subject to the provisions of Articles 108 and 109, a Bill shall not be deemed to have been passed by the Houses of Parliament unless it has been agreed to by both Houses of Parliament. However, the requirement of passing a Bill by both the Houses is not applicable in case of Money Bills. Article 110 defines as to what is the Money Bill. A Money Bill is constitutionally defined and a Bill shall be a Money Bill only if it is covered by Article 110(1). A Bill, which does not fulfill the conditions as enumerated in Article 110(1) and it is certified as Money Bill, whether the Constitutional conditions enumerated in Article 110(1) shall be overridden only by certificate of Speaker?
359. We have noticed the Constitution Bench Judgment in Kihoto Hollohan (supra) and Raja Ram Pal (supra) that finality of the decision of the Speaker is not immuned from Judicial Review. All Bills are required to be passed by both Houses of Parliament. Exception is given in case of Money Bills and in the case of joint sitting of both houses. In event, we accept the 365 submission of learned Attorney General that certification by Speaker is only a matter of procedure and cannot be questioned by virtue of Article 122(1), any Bill, which does not fulfill the essential constitutional condition under Article 110 can be certified as Money Bill byepassing the Upper House.
There is a clear difference between the subject “irregularity of procedure” and “substantive illegality”. When a Bill does not fulfill the essential constitutional condition under Article 110(1), the said requirement cannot be said to be evaporated only on certification by Speaker. Accepting the submission that certification immunes the challenge on the ground of not fulfilling the constitutional condition, Court will be permitting constitutional provisions to be ignored and byepassed. We, thus, are of the view that decision of Speaker certifying the Bill as Money Bill is not only a matter of procedure and in event, any illegality has occurred in the decision and the decision is clearly in breach of the constitutional provisions, the 366 decision is subject to Judicial Review. We are, therefore, of the view that the Three Judge Bench Judgment of this Court in Mohd. Saeed Siddiqui (supra) and Two Judge Bench judgment of this Court in Yogendra Kumar Jaiswal (supra) does not lay down the correct law.
We, thus, conclude that the decision of the Speaker certifying the Aadhaar Bill as Money Bill is not immuned from Judicial Review. 360. We having held that the decision of Speaker certifying the Aadhaar Bill as a Money Bill is open to Judicial Review. We now proceed to examine as to whether Speaker’s decision certifying the Aadhaar Bill as Money Bill contravenes any of the Constitutional provisions, i.e., Whether the decision is vitiated by any Constitutional Illegality? For determining the main issue, which need to be answered is as to whether Aadhaar Bill is covered by any of Clauses (a) to (f) of Article 110(1). That Clause(g) shall be applicable only when any of Clauses (a) to (f) are attracted. Clause (g) which contemplate that any matter incidental to any of the matters specified in sub367 clauses (a) to (f), can be a provision in a Bill presupposes that main provisions have to fall in any of the Clauses (a) to (f). The heart of the Aadhaar Act is Section 7, which is to the following effect:”
7. Proof of Aadhaar number necessary for receipt of certain subsidies, benefits and services, etc.The Central Government or, as the case may be, the State Government may, for the purpose of establishing identity of an individual as a condition for receipt of a subsidy, benefit or service for which the expenditure is incurred from, or the receipt therefrom forms part of, the Consolidated Fund of India, require that such individual undergo authentication, or furnish proof of possession of Aadhaar number or in the case of an individual to whom no Aadhaar number has been assigned, such individual makes an application for enrolment:
Provided that if an Aadhaar number is not assigned to an individual, the individual shall be offered alternate and viable means of identification for delivery of the subsidy, benefit or service.”
361. A condition for receipt of a subsidy, benefit or service for which the expenditure is incurred from, or the receipt therefrom forms part of, the Consolidated Fund of India, has been provided by Section 7, i.e. undergoing of an individual to an authentication. The Preamble of the Act as well as objects and reasons as 368 noticed above also indicate that the Act has been enacted to provide for, as a good governance, efficient, transparent, and targeted delivery of subsidies, benefits and services, the expenditure for which is incurred from the Consolidated Fund of India, to individuals residing in India through assigning of unique identity numbers to such individuals and for matters connected therewith or incidental thereto. Thus, the theme of the Act or main purpose and object of the Act is to bring in place efficient, transparent and targeted deliveries of subsidies, benefits and services, which expenditure is out from the Consolidated Fund of India.
Thus, the above provisions of the Act is clearly covered by Article 110(1)(c) and (e).
362. Shri P. Chidambaram, learned counsel for petitioners has laid much emphasis on the word “only” as occurring in Article 110(1). The word “only” used in Article 110(1) has purpose and meaning. The legislative intendment was that main and substantive provisions should be only any or all of the clauses 369 from (a) to (f). In event, the main and substantive provision of the Act are not covered by Clauses (a) to (f), the said Bill cannot be said to be a Money Bill. It will not be out of place to mention here that in Constituent Assembly, an amendment was moved for deletion of word “only” on 20.05.1949, Hon’ble Shri Ghanshyam Singh Gupta moved the amendment in Draft Article 90. It is useful to extract the above debate, which is to the following effect: The Honourable Shri Ghanshyam Singh Gupta (C.P. & Berar: General): Sir, I beg to move: “That in clause (1) of article 90, the word `only’ be deleted.”
This article is a prototype of Section 37 of the Government of India Act which says that a Bill or amendment providing for imposing or increasing a tax or borrowing money, etc. shall not be introduced or moved except on the recommendation of the GovernorGeneral. This means that the whole Bill need not be a money Bill: it may contain other provisions, but if there is any provision about taxation or borrowing, etc. It will come under this Section37, and the recommendation of the GovernorGeneral is necessary. Now article 90 says that a Bill shall be deemed to be a money Bill if it contains only provisions dealing with the imposition, regulation, etc., of any tax or the borrowing of money, etc.
This can mean that if there is a Bill which has other provisions and also a 370 provision about taxation or borrowing etc., it will not become a money Bill. If that is the intention I have nothing to say; but that if that is not the intention I must say the word “only” is dangerous, because if the Bill does all these things and at the same time does something else also it will not be a money Bill. I do not know what the intention of the Drafting Committee is but I think this aspect of the article should be borne in mind.”
363. After discussion, Mr. Naziruddin Ahmad also suggested that the position of the word “only” in connection with Amendment No.1669 should be specially considered. It is a word which is absolutely misplaced. On that day, the consideration was deferred and again in the debate on 06.06.1949, Constituent Assembly took up the discussion.
The President of the Constituent Assembly placed the amendment for vote on 08.06.1949, which amendment was negativated. Thus, use of word “only” in Article 110(1) has its purpose, which is a clear restriction for a Bill to be certified as a Money Bill.
364. Other provisions of the Act can be said to be incidental to the above matter. The architecture of the Aadhaar Act veer round the Government’s constitutional obligation to provide for subsidies, benefits and services to the individuals, who are entitled for such subsidies, benefits and services. Section 24 contemplates the appropriation made by Parliament by law for grant of sums of money for the purposes of Aadhaar Act.
The disbursement of subsidies, benefits and services from the Consolidated Fund of India is in substance, the main object of the Act for which Aadhaar architecture has been envisaged and other provisions are only to give effect to the above main theme of the Act. Other provisions of the Act are only incidental provisions to main provision. Section 57 on which much attack has been made by the learned counsel for the petitioners that it cannot be covered by any of the provisions from (a) to (f) of Article 110(!). Suffice it to say that Section 57 is a provision which clarifies that nothing contained in Aadhaar Act shall prevent the use of Aadhaar number for establishing the identity of an individual for any purpose, whether by the State or any body corporate or 372 person, pursuant to any law, for the time being in force, or any contract to this effect.
The applicability of the provision of Section 57 comes into play when Aadhaar Number is allocated to an individual after completing the process under the Act. Section 57 is also a incidental provision covered by subclause( g) of Article 110(1). Section 57 is a limitation imposed under the Act on the use of Aadhaar Number by State or any body corporate or any private party. We, thus, are of the view that Aadhaar Bill has rightly been certified as the Money Bill by the Speaker, which decision does not violate any constitutional provision, hence does not call for any interference in this proceeding. Issue No. 16 is answered in the following manner:Ans. 16:Aadhaar Act has been rightly passed as Money Bill.
The decision of Speaker certifying the Aadhaar Bill, 2016 as Money Bill is not immuned from Judicial Review.
Issue No.17
Whether Section 139AA of the Income Tax Act 1961 is unconstitutional in view of the Privacy judgment in Puttaswamy case?
365. Section 139AA was challenged by a bunch of writ petitions, which were decided by this Court in Binoy Viswam Vs. Union of India and Others, (2017) 7 SCC 59. The writ petitions were disposed of upholding the vires of Section 139AA. Para 136 of the judgment contains operative portion, which is to the following effect:”
136. Subject to the aforesaid, these writ petitions are disposed of in the following manner:
136.1 We hold that the Parliament was fully competent to enact Section 139AA of the Act and its authority to make this law was not diluted by the orders of this Court.
136.2. We do not find any conflict between the provisions of the Aadhaar Act and Section 139AA of the Income Tax Act inasmuch as when interpreted harmoniously, they operate in distinct fields.
136.3. Section 139AA of the Act is not discriminatory nor it offends equality Clause enshrined in Article 14 of the Constitution.
136.4. Section 139AA is also not violative of Article 19(1)(g) of the Constitution insofar as it mandates giving of Aadhaar 374 enrollment number for applying for PAN cards, in the income tax returns or notified Aadhaar enrollment number to the designated authorities. Further, the proviso to Subsection (2) thereof has to be read down to mean that it would operate only prospectively.
136.5 The validity of the provision upheld in the aforesaid manner is subject to passing the muster of Article 21 of the Constitution, which is the issue before the Constitution Bench in Writ Petition (Civil) No. 494 of 2012 and other connected matters. Till then, there shall remain a partial stay on the operation of the proviso to Subsection (2) of Section 139AA of the Act, as described above. No cost.”
366. As per the above judgment, the validity of the provisions of Section139AA was upheld subject to passing the muster of Article 21 of the Constitution, which was the issue pending before the Constitution Bench in Writ Petition (C) No. 494 of 2012 and other connected matters. The Constitution Bench Judgment in Puttaswamy was delivered on 24.08.2017. Right of Privacy has been held to be fundamental right, any restriction on such fundamental right has been held to be valid when it passes the muster of threefold test as laid down there. In the lead judgment of Dr. 375 Justice D.Y. Chandrachud, threefold test are:( a) The existence of law; (b) A legitimate State interest and (c) such law should pass the test of proportionality.
367. Dr. Justice Chandrachud has delivered the judgment for himself and three other Hon’ble Judges, Justice Sanjay Kishan Kaul in paragraph 639 has upheld the test of proportionality. As a result, atleast five out of nine Judges requires the proportionality test to be applied. In addition to tests propounded by a Constitution Bench in Puttaswamy case, an additional test as propounded by a Five Judges Constitution Bench of this Court in Shayara Bano Vs. Union of India, (2017) 9 SCC 1, Justice R.F. Nariman has laid down a test of “manifest arbitrariness”. Reading the Nine Judge Bench decision in Puttaswamy case and Five Judge Bench decision in Shayara Bano’s case, the Petitioner can succeed to the challenge to Section 139AA only if they successfully demonstrate the said provision to be violative of Right to Privacy 376 on the basis of the following tests:
(i) Absence of law;
(ii) Absence of Legitimate State Interest;
(iii) The provision being hit by lack of proportionality.
(iv) The provision being manifestly arbitrary, which can be traced to Article 14. [The test to determine “manifest arbitrariness” is to decide whether the enactment is drastically unreasonable and / or capricious, irrational or without adequate determining principle”]
368. The learned Attorney General relies on following interest, which according to him are safeguarded by Section 139AA to satisfy the legitimate State interest:
a. To prevent income tax evasion by requiring, through an amendment to the Income Tax Act, that the Aadhaar number be linked with the PAN; and
b. Prevention, accumulation, circulation and use of black money and money laundering by imposing a requirement by law for linking Aadhaar for opening bank accounts;
c. To prevent terrorism and protect national 377 security and prevention of crime by requiring that Aadhaar number be linked to SIM cards for mobile phones.
369. Binoy Viswam has examined Section 139AA on the Principle of Doctrine of Proportionality in Paragraphs 123 to 125:”
123. Keeping in view the aforesaid parameters and principles in mind, we proceed to discuss as to whether the “restrictions” which would result in terms of the proviso to subsection (2) of Section 139AA of the Act are reasonable or not.
124. Let us revisit the objectives of Aadhaar, and in the process, that of Section 139AA of the Act in particular.
125. By making use of the technology, a method is sought to be devised, in the form of Aadhaar, whereby identity of a person is ascertained in a flawless manner without giving any leeway to any individual to resort to dubious practices of showing multiple identities or fictitious identities. That is why it is given the nomenclature “unique identity”. It is aimed at securing advantages on different levels some of which are described, in brief, below:
125.1. In the first instance, as a welfare and democratic State, it becomes the duty of any responsible Government to come out with welfare schemes for the upliftment of povertystricken and marginalised sections of the society. This is even the ethos of Indian Constitution which casts a duty on the State, in the form of “directive principles of State policy”, to take adequate and effective steps for betterment of such underprivileged classes. State is bound to take adequate measures to provide education, health care, employment and even cultural opportunities and social standing to these deprived and underprivileged classes. It is not that Government has not taken steps in this direction from time to time. At the same time, however, harsh reality is that benefits of these schemes have not reached those persons for whom that are actually meant.
125.1.1. India has achieved significant economic growth since Independence. In particular, rapid economic growth has been achieved in the last 25 years, after the country adopted the policy of liberalisation and entered the era of, what is known as, globalisation. Economic growth in the last decade has been phenomenal and for many years, the Indian economy grew at highest rate in the world. At the same time, it is also a fact that in spite of significant political and economic success which has proved to be sound and sustainable, the benefits thereof have not percolated down to the poor and the poorest. In fact, such benefits are reaped primarily by rich and upper middle classes, resulting into widening the gap between the rich and the poor.
125.1.2. Jean Dreze and Amartya Sen pithily narrate the position as under: “Since India’s recent record of fast economic growth is often celebrated, with good reason, it is extremely important to point to the fact that the 379 societal reach of economic progress in India has been remarkably limited. It is not only that the income distribution has been getting more unequal in recent years (a characteristic that India shares with China), but also that the rapid rise in real wages in China from which the working classes have benefited greatly is not matched at all by India’s relatively stagnant real wages. No less importantly, the public revenue generated by rapid economic growth has not been used to expand the social and physical infrastructure in a determined and wellplanned way (in this India is left far behind by China).
There is also a continued lack of essential social services (from schooling and health care to the provision of safe water and drainage) for a huge part of the population. As we will presently discuss, while India has been overtaking other countries in the progress of its real income, it has been overtaken in terms of social indicators by many of these countries, even within the region of South Asia itself (we go into this question more fully in Chapter 3, ‘India in Comparative Perspective’).
To point to just one contrast, even though India has significantly caught up with China in terms of GDP growth, its progress has been very much slower than China’s in indicators such as longevity, literacy, child undernourishment and maternal mortality. In South Asia itself, the much poorer economy of Bangladesh has caught up with and overtaken India in 380 terms of many social indicators (including life expectancy, immunisation of children, infant mortality, child undernourishment and girls’ schooling).
Even Nepal has been catching up, to the extent that it now has many social indicators similar to India’s, in spite of its per capita GDP being just about one third. Whereas twenty years ago India generally had the second best social indicators among the six South Asian countries (India, Pakistan, Bangladesh, Sri Lanka, Nepal and Bhutan), it now looks second worst (ahead only of problemridden Pakistan). India has been climbing up the ladder of per capita income while slipping down the slope of social indicators.”
125.1.3. It is in this context that not only sustainable development is needed which takes care of integrating growth and development, thereby ensuring that the benefit of economic growth is reaped by every citizen of this country, it also becomes the duty of the Government in a welfare State to come out with various welfare schemes which not only take care of immediate needs of the deprived class but also ensure that adequate opportunities are provided to such persons to enable them to make their lives better, economically as well as socially.
As mentioned above, various welfare schemes are, in fact, devised and floated from time to time by the Government, keeping aside substantial amount of money earmarked for spending on socially and economically backward classes. However, for various reasons including corruption, actual benefit does not reach those who are supposed to receive such benefits. One of the main 381 reasons is failure to identify these persons for lack of means by which identity could be established of such genuine needy class. Resultantly, lots of ghosts and duplicate beneficiaries are able to take undue and impermissible benefits. A former Prime Minister of this country has gone on record to say that out of one rupee spent by the Government for welfare of the downtrodden, only 15 paisa thereof actually reaches those persons for whom it is meant. It cannot be doubted that with UID/Aadhaar much of the malaise in this field can be taken care of.
125.2. Menace of corruption and black money has reached alarming proportion in this country. It is eating into the economic progress which the country is otherwise achieving. It is not necessary to go into the various reasons for this menace. However, it would be pertinent to comment that even as per the observations of the Special Investigation Team (SIT) on black money headed by Justice M.B. Shah, one of the reasons is that persons have the option to quote their PAN or UID or passport number or driving licence or any other proof of identity while entering into financial/business transactions. Because of this multiple methods of giving proofs of identity, there is no mechanism/system at present to collect the data available with each of the independent proofs of ID. For this reason, even SIT suggested that these databases be interconnected. To the same effect is the recommendation of the Committee headed by Chairman, CBDT on measures to tackle black money in India and abroad which also discusses the problem of money laundering being done to evade taxes under the garb of shell companies by the persons who hold multiple bogus PAN numbers under 382 different names or variations of their names. That can be possible if one uniform proof of identity, namely, UID is adopted. It may go a long way to check and minimise the said malaise.
125.3. Thirdly, Aadhaar or UID, which has come to be known as the most advanced and sophisticated infrastructure, may facilitate lawenforcement agencies to take care of problem of terrorism to some extent and may also be helpful in checking the crime and also help investigating agencies in cracking the crimes. No doubt, going by the aforesaid, and may be some other similarly valid considerations, it is the intention of the Government to give fillip to Aadhaar movement and encourage the people of this country to enrol themselves under the Aadhaar Scheme.”
370. In Paragraphs 122 to 125 of Binoy Viswam, it has also been observed that the measures taken may go a long way to check and minimise the malaise of black money.
371. Dr. Justice D.Y. Chandrachud in Puttaswamy case in Paragraph 311 has stated:” 311. ………Prevention and investigation of crime and protection of the revenue are among the legitimate aims of the State. Digital platforms are a vital tool of ensuring good governance in a social welfare State. Information technology – legitimately deployed is a powerful enabler in the spread of innovation and knowledge.”
372. In Puttaswamy case, Justice Sanjay Kishan Kaul has noted the European Union General Data Protection Regulation and observed that restrictions on the right to privacy may be justifiable on the ground of regulation of taxes and financial institutions. In Paragraph 640, Justice Kaul has held:” 640. It would be useful to turn to the European Union Regulation of 2016. Restrictions of the right to privacy may be justifiable in the following circumstances subject to the principle of proportionality:
(a) Other fundamental rights: The right to privacy must be considered in relation to its function in society and be balanced against other fundamental rights.
(b) Legitimate national security interest.
(c) Public interest including scientific or historical research purposes or statistical purposes.
(d) Criminal offences: The need of the competent authorities for prevention investigation, prosecution of criminal offences including safeguards against threat to public security;
(e) The unidentifiable data: The 384 information does not relate to identified or identifiable natural person but remains anonymous. The European Union Regulation of 2016 refers to “pseudonymisation” which means the processing of personal data in such a manner that the personal data can no longer be attributed to a specific data subject without the use of additional information, provided that such additional information is kept separately and is subject to technical and organisational measures to ensure that the personal data are not attributed to an identified or identifiable natural person;
(f) The tax, etc.: The regulatory framework of tax and working of financial institutions, markets may require disclosure of private information. But then this would not entitle the disclosure of the information to all and sundry and there should be data protection rules according to the objectives of the processing. There may however, be processing which is compatible for the purposes for which it is initially collected.”
373. Section 139AA thus clearly enacted to fulfill the legitimate State interest. Section 139A which came into effect w.e.f. 01.04.1989 provide for Permanent Account Number (PAN) and the provision also provided that statutory mandatory provisions as to 385 when “every person” shall quote such number (PAN number) for various purposes as enumerated in Section 139A. Introduction of Section 139AA is an extension and implication of Section 139A. The introduction of Section 139AA was for the purpose of eliminating duplicate PANs from the system with the help of a robust technology solution.
374. The new Section 139AA in the Income Tax Act seeks to remove bogus PAN cards by linking with Aadhaar, expose shell companies and thereby curb the menace of black money, money laundering and tax evasion. The fact that the tax base of India is very narrow and that we are a largely tax noncompliant society is evident from some of the startling figures in the budget speech of the Finance Minister. Linking of PAN with Aadhaar will at least ensure that duplicate and fake PAN cards which are used for the purpose of tax evasion will be eliminated and is one of the many fiscal measures to eliminate black money from the system.
375. The Binoy Viswam has referred to other relevant rationals for enactment of Section 139AA. Section 139AA also cannot be said to be disproportionate. The section has been enacted to achieve the legitimate State aim. Section 139AA is a law framed by Parliament, which require linking of the Aadhaar with PAN. The means which are sought to be achieved by such enactment cannot be said to be disproportionate in any manner. It has been further submitted that Section 139AA unfairly attracts only individual assessees and not other tax paying assessees, who may also be involved in financial frauds.
The above submission need not detain us since Aadhaar number can be obtained by the individuals and not by the entities hence Section139AA can only apply to individuals. In any event, the legislature cannot be expected to address all issues relating to a particular evil at one go. Section 139AA is a required first step to weed out fake PANs for individuals; it is perfectly acceptable for the legislature to weed out fake PANs for other taxpaying entities at a later stage. Such 387 a view is also endorsed in judicial decisions. In Namit Sharma Vs. Union of India, (2013) 1 SCC 745 (per Swatanter Kumar, J.) this Court observed:”
43. The rule of equality or equal protection does not require that a State must choose between attacking every aspect of a problem or not attacking the problem at all, and particularly with respect to social welfare programme. So long as the line drawn by the State is rationally supportable, the courts will not interpose their judgment as to the appropriate stopping point…………” 376.
Thus, the legislature is within its remit to only target individual assessees with Section 139AA, and not every other taxpaying entity. The law does not have to provide for complete coverage of taxpayers who may be indulging in financial fraud but may envisage ‘degrees of harm’ and act on that basis. In this context, the Aadhaar number is being mandated for all individual assessees. This is applicable to natural persons as well as persons who together constitute legal persons (e.g. Partners in a partnership, members of a company etc.) and hence provides significant coverage to weed out duplicate PANs and hence reduce the incidence of financial and 388 tax frauds through these means. Aadhaar’s inclusion into PAN is meant to curb tax evasion, sham transactions, entry providers which are rampantly carried out on account of bogus PANs. Aadhaar’s unique deduplication based on biometric identification has been hailed as the most sophisticated system by the World Bank. Inclusion of Aadhaar into PAN eliminates the inequality between honest tax payers and noncompliant, dishonest ones who get away without paying taxes. Inclusion of Aadhaar into PAN promotes rather than negates equality. It bolsters equality and is consistent with Article 14.
377. In result, Section 139AA is fully compliant of threefold test as laid down in Puttaswamy’s case. Section 139AA, thus does not breach fundamental Right of Privacy of an individual and Section 139AA cannot be struck down on that ground. Ans.17:Section 139AA does not breach fundamental Right of Privacy as per Privacy Judgment in Puttaswamy case.
Issue No. 18
Whether Aadhaar Act violates the Interim Orders passed by this Court in Writ Petition (C) No. 494 of 2012?
378. The petitioners submits that this Court has passed various Interim Orders in Writ Petition (C) No. 494 of 2012 from 23.09.2013 to 15.10.2015. On 23.09.2013, this Court directed “In the meanwhile, no person should suffer not getting the Aadhaar card inspite of the fact that some authority had issued a circular making it mandatory and when any person applies to get the Aadhaar Card voluntarily, it may be checked whether that person is entitled for it under the law and it should not be given to any illegal immigrant”.
379. On 11.08.2015, this Court issued following order:” Having considered the matter, we are of the view that the balance of interest would be best served, till the matter is finally decided by a larger Bench if the Union of India or the UIDA proceed in the following manner:
390
1. The Union of India shall give wide publicity in the electronic and print media including radio and television networks that it is not mandatory for a citizen to obtain an Aadhaar card;
2. The production of an Aadhaar card will not be condition for obtaining any benefits otherwise due to a citizen;
3. The Unique Identification Number or the Aadhaar card will not be used by the respondents for any purpose other than the PDS Scheme and in particular for the purpose of distribution of foodgrains, etc. and cooking fuel, such as kerosene. The Aadhaar card may also be used for the purpose of the LPG Distribution Scheme;
4. The information about an individual obtained by the Unique Identification Authority of India while issuing an Aadhaar card shall not be used for any other purpose, save as above, except as may be directed by a Court for the purpose of criminal investigation.” By subsequent order of 15.10.2015, some more Schemes were included.
380. It is submitted that the Central Government and the State Government issued various notifications numbering 139, requiring Aadhaar authentication for various benefits, subsidies and schemes. The issuance of such orders is in breach of above Interim Orders passed by this Court.
381. In Binoy Viswam (supra) an argument was advanced that enactment of Section 139AA was in breach of the Interim Order passed in Writ Petition (C) No. 494 of 2012. The said argument was considered and in Para 99 it was held as follows:
“99. Main emphasis, however, is on the plea that Parliament or any State Legislature cannot pass a law that overrules a judgment thereby nullifying the said decision, that too without removing the basis of the decision. This argument appears to be attractive inasmuch as few orders are passed by this Court in pending writ petitions which are to the effect that the enrolment of Aadhaar would be voluntary. However, it needs to be kept in mind that the orders have been passed in the petitions where Aadhaar Scheme floated as an executive/administrative measure has been challenged. In those cases, the said orders are not passed in a case where the Court was dealing with a statute passed by Parliament.
Further, these are interim orders as the Court was of the opinion that till the matter is decided finally in the context of right to privacy issue, the implementation of the said Aadhaar Scheme would remain voluntary. In fact, the main issue as to whether Aadhaar card scheme whereby biometric data of an individual is collected violates right to privacy and, therefore, is offensive of Article 21 of the Constitution or not is yet to be decided. In the process, the Constitution Bench is also called upon to decide as to whether right to privacy is a part of Article 21 of the Constitution at all. Therefore, no final decision has been taken. In a situation like this, it cannot be said that Parliament is precluded from or it is rendered incompetent to pass such a law.
That apart, the argument of the petitioners is that the basis on which the aforesaid orders are passed has to be removed, which is not done. According to the petitioners, it could be done only by making the Aadhaar Act compulsory. It is difficult to accept this contention for two reasons: first, when the orders passed by this Court which are relied upon by the petitioners were passed when the Aadhaar Act was not even enacted. Secondly, as already discussed in detail above, the Aadhaar Act and the law contained in Section 139AA of the Income Tax Act deal with two different situations and operate in different fields. This argument of legislative incompetence also, therefore, fails.”
382. We have noticed that the Writ Petition (C) No. 494 of 2012 was filed at the time when Aadhaar Scheme was being implemented on the basis of executive’s instructions dated 28.01.2009. In the Writ Petition filed prior to enactment of Act, 2016, challenge to Aadhaar Scheme was founded on following:i. The requirement of making Aadhaar mandatory for availing benefits under various social service schemes by way of an executive order and ii. Concerns regarding the right to privacy of the individuals, which emanated on 393 account of collection of biometric data under the Aadhaar scheme, which is without any legislative backing.
383. Aadhaar Act, 2016 gives legislative backing to the Aadhaar Scheme. The Act contains specific provisions prohibiting disclosure of core biometric information collected in Aadhaar enrolment. It is submitted that Schemes notified under Section 7 of the Act were on the strength of Aadhaar enactment and cannot be said to be a violation of interim orders of this Court. The submission that interim orders directed the Aadhaar to be voluntary, it is submitted by the respondent that consent was obtained from individuals, who came for enrolment under the Aadhaar Act. It is submitted that all those, who were enrolled under the Statutory Scheme dated 28.01.2009, the consent was given by the individuals in verifying their informations.
384. We, thus, conclude that Aadhaar Act cannot be struck down on the ground that it is in violation of interim orders passed by this Court in Writ Petition (C) No. 494 of 2012. Issue No. 18 is answered in 394 following manner:Ans. 18:The Aadhaar Act does not violate the interim orders passed in Writ Petition (C) No. 494 of 2012 and other Writ Petitions. 385. I had gone through the erudite and scholarly opinion of Justice A.K.Sikri (which opinion is on his own behalf and on behalf of Chief Justice and Justice A.M.Khanwilkar) with which opinion I broadly agree. Rule 9 as amended by PMLA (Second Amendment) Rules, 2017 has been struck down by my esteemed brother which provision has been upheld by me. My reasons and conclusions are on the same line except few where my conclusions are not in conformity with the majority opinion.
CONCLUSIONS:
386. In view of above discussions, we arrive at following conclusions:
(1) The requirement under Aadhaar Act to give one’s demographic and biometric information does not violate fundamental right of 395 privacy.
(2) The provisions of Aadhaar Act requiring demographic and biometric information from a resident for Aadhaar Number pass threefold test as laid down in Puttaswamy (supra) case, hence cannot be said to be unconstitutional.
(3) Collection of data, its storage and use does not violate fundamental Right of Privacy.
(4) Aadhaar Act does not create an architecture for pervasive surveillance.
(5) Aadhaar Act and Regulations provides protection and safety of the data received from individuals.
(6) Section 7 of the Aadhaar is constitutional. The provision does not deserve to be struck down on account of denial in some cases of right to claim on account of failure of authentication.
(7) The State while enlivening right to food, right to shelter etc. envisaged under Article 21 cannot encroach upon the right of privacy of beneficiaries nor former can be given precedence over the latter.
(8) Provisions of Section 29 is constitutional and does not deserves to be struck down.
(9) Section 33 cannot be said to be unconstitutional as it provides for the use of Aadhaar data base for police investigation nor it can be said to violate protection granted under Article 20(3).
(10) Section 47 of the Aadhaar Act cannot be held to be unconstitutional on the ground that it does not allow an individual who finds that there is a violation of Aadhaar Act to initiate any criminal process.
(11) Section 57, to the extent, which permits use of Aadhaar by the State or any body corporate or person, in pursuant to any contract to this effect is unconstitutional and void. Thus, the last phrase in main provision of Section 57, i.e. “or any contract to this effect” is struck down.
(12) Section 59 has validated all actions taken by the Central Government under the notifications dated 28.01.2009 and 12.09.2009 and all actions shall be deemed to have been taken under the Aadhaar Act.
(13) Parental consent for providing biometric information under Regulation 3 & demographic information under Regulation 4 has to be read for enrolment of children between 5 to 18 years to uphold the constitutionality of Regulations 3 & 4 of Aadhaar (Enrolment and Update) Regulations, 2016.
(14) Rule 9 as amended by PMLA (Second Amendment) Rules, 2017 is not unconstitutional and does not violate Articles 14, 19(1)(g), 21 & 300A of the Constitution and Sections 3, 7 & 51 of the Aadhaar Act. Further Rule 9 as amended is not ultra vires to PMLA Act, 2002.
(15) Circular dated 23.03.2017 being unconstitutional is set aside.
(16) Aadhaar Act has been rightly passed as Money Bill. The decision of Speaker certifying the Aadhaar Bill, 2016 as Money Bill is not immuned from Judicial Review.
(17) Section 139AA does not breach fundamental Right of Privacy as per Privacy Judgment in Puttaswamy case.
(18) The Aadhaar Act does not violate the interim orders passed in Writ Petition (C) No. 494 of 2012 and other Writ Petitions. 387. Now, we revert back to the batch of cases, which have come up for consideration before us. 388. We having considered and answered the issues arising in this batch of cases, all the Writ Petitions filed under Article 32 deserves to be disposed of in accordance with our conclusions as noted above. All Transfer Cases/Transfer Petitions are also deserves to be decided accordingly.
389. Now, we come to the Criminal Appeal arising out of S.L.P. (Crl.) No. 2524 of 2014. The above S.L.P. (Crl.) arose out of an order passed by Judicial Magistrate First Class dated 22.10.2013 by which Judicial Magistrate First Class directed DG, UIDAI and Dy. Dg. UIDAI Technology Centre, Bangalore to provide the necessary data to the respondent C.B.I. The said order was challenged in the High Court by means of Criminal Writ Petition, in which the order was passed by the High Court on 26.02.2014 giving rise to S.L.P. (Crl.) No. 2524 of 2014.
390. We have noticed above that according to Aadhaar Act Section 33 disclosure of information can be made as per subsection (1) pursuant to an order of Court, not inferior to that of District Judge. The order directing for disclosure of information having been passed by Judicial Magistrate First Class, in the present case, the order is not in consonance with subsection (1) of Section 33, hence the order passed by Judicial Magistrate, First Class dated 22.10.2013 and order of the High Court passed in reference to the said order deserves to be set aside. Criminal Appeal is allowed accordingly.
391. No case is made out to initiate any contempt proceedings in the contempt applications as prayed for. All the contempt petitions are dismissed.
392. In result, this batch of cases is decided in following manner:
(i) All the Writ Petitions filed under Article 32 as well as Transfer Cases are disposed of as per our conclusions recorded above.
(ii) Criminal Appeal arising out of S.L.P. (Criminal) No. 2524 of 2014 is allowed.
(iii) All the contempt applications are closed.
393. Before we part, we record our deep appreciation for the industry, hard work and eloquence shown by learned counsel for the parties appearing before us, which was amply demonstrated in their respective arguments. Learned counsel have enlightened us with all relevant concerned materials available in this country and abroad. The concern raised by these Public Interest Litigations is a concern shown for little Indian for whom the Society, Government and Court exists. We appreciate the concern and passion expressed before us by learned counsel appearing for both the parties as well as those, who were permitted to intervene in the matter. We close by once more recording of our appreciation for the cause espoused in these cases.
…………………………J. ( ASHOK BHUSHAN )
NEW DELHI,
SEPTEMBER 26, 2018.
![]()
Connected cases :
[Transferred Case (Civil) No. 151 of 2013]
[Transferred Case (Civil) No. 152 of 2013]
[Writ Petition (Civil) No. 833 of 2013]
[Writ Petition (Civil) No. 829 of 2013]
[Transferred Petition (Civil) No. 1797 of 2013]
[Writ Petition (Civil) No. 932 of 2013]
[Transferred Petition (Civil) No. 1796 of 2013]
[Contempt Petition (Civil) No. 144 of 2014 in Writ Petition (Civil) No. 494 of 2012]
[Transferred Petition (Civil) No. 313 of 2014]
[Transferred Petition (Civil) No. 312 of 2014]
[Special Leave Petition (Criminal) No. 2524 of 2014]
[Writ Petition (Civil) No. 37 of 2015]
[Writ Petition (Civil) No. 220 of 2015]
[Contempt Petition (Civil) No. 674 of 2015 in Writ Petition (Civil) No. 829 of 2013]
[Transferred Petition (Civil) No. 921 of 2015]
[Contempt Petition (Civil) No. 470 of 2015 in Writ Petition (Civil) No. 494 of 2012]
[Writ Petition (Civil) No. 231 of 2016]
[Contempt Petition (Civil) No. 444 of 2016 in Writ Petition (Civil) No. 494 of 2012]
[Contempt Petition (Civil) No. 608 of 2016 in Writ Petition (Civil) No. 494 of 2012]
[Writ Petition (Civil) No. 797 of 2016]
[Contempt Petition (Civil) No. 844 of 2017 in Writ Petition (Civil) No. 494 of 2012]
[Writ Petition (Civil) No. 342 of 2017]
[Writ Petition (Civil) No. 372 of 2017]
[Writ Petition (Civil) No. 841 of 2017]
[Writ Petition (Civil) No. 1058 of 2017]
[Writ Petition (Civil) No. 966 of 2017]
[Writ Petition (Civil) No. 1014 of 2017]
[Writ Petition (Civil) No. 1002 of 2017]
[Writ Petition (Civil) No. 1056 of 2017]
[Contempt Petition (Civil) No. 34 of 2018 in Writ Petition (Civil) No. 1014 of 2017]